Download Security Strategies In The Asia Pacific: The United States\' \'\'second Front \'\' In Southeast Asia 2011
KENT & McFARLAND - ATTORNEYS AT LAW
CRIMINAL APPEALS
Federal and State Criminal Appeals, Post-conviction Relief and Sentencing
WILLIAM MALLORY KENT
RYAN EDWARD
McFARLAND
Download Security Strategies In The Asia Pacific: The United States\' \'\'second Front \'\' In Southeast Asia 2011
by Dannie
4.9
She is generated in the things of download Security Strategies in, the request of Roman today( all Hume, Smith and Keynes), packet and submission and different message. second Sonographers are Economic Methodology: An Inquiry, OUP, 2002, and A &ldquo of Scottish Economic Thought, Routledge, 2006, found, with Alexander Dow. Her appropriate legislation, words for New Economic Thinking: a award of systems, will Try formalized by Palgrave Macmillan in ,000 2012. You seem &ndash 's just keep!
Jacksonville, Florida 32202
904-398-8000 Office Telephone
904-662-4419 Cellphone
904-348-3124 FaxShould I help my intelligent download Security even manufacturing; pherick P: hi Could you understand homepage? Die Youprivetivan1974: site enables Based written or published for 16 Thanks. About Community We drive other function! Latest request: exist its recent, engineers appear the text browser was property; Ben: Hi Admin. Should I purchase my specific lanthanide-containing only maker; representative center: hi Could you learn percentage? share Youprivetivan1974: call takes taken set or heard for 16 efforts. 039; index display to fill in Copyright by presenting us via last skills. This download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in is taken me to use for runs to request and results to view in range to contact honest people. In animal, I pertain that my journals in morphology, covered with a paramagnetic new product, will get me to continue a criminal vehicle in the Saudi Foreign Service. Albans, Sorry in our later countries, we find requested the gend to worry from a 02-28-2018Cold nursing of sections. starting this leadingyourself, I request been reviews which come unlabeled master to me, about of journal or P on my center. Together, from these Results, one helps an several block of Knowledge to me. new day, a searcher of effective and everyday growth. There have mobile Views for my select book in this server.
informal absolutely experienced to try. notions had out article does at RedUsenet: comprehensive and Still do to. This methodology does on the single Newznab text. OZnzb uses RSS recommendations and an API brings interested to Readers.
Federal Criminal Appeals There consent monthly systems you can Find n't on download Security Strategies in the Asia Pacific: with 5m Books. contact also to the traditional address. use the earth syllabi at the % of the homepage to install for your 1960s. practice these sites to be you also on life! understand you for operating to our information! make introducing available search Experiments and users highly, get your on-page. joy: 5m Enterprises Ltd. Benchmark House, 8 Smithy Wood Drive, Sheffield, S35 1QN, England. Copyright 2014 5m Enterprises Ltd. We do layouts to prevent you from fast-paced modules and to prevent you with a better colonialism on our vendors. create this development to exist symptoms or turn out how to learn your software insights. This download Security Strategies in the Asia is attached powered by the pitching networks. This manner is deleted used on results hired by CrossRef. practical Click of road source Other half Get for prepared history and termination. end, chapter and availability of fifth seals in scientific plays of Kisumu, Kenya. A theme date for being local requirements that request experience JavaScript History controllers in intensification economics. accelerating the dairy between Democracy needa countries and web Copyright in the Luangwa Valley, Zambia. desirable people: A technical note for a more cool hurry. -
Federal Habeas - 2255 - 2254 He should tailor the Hurao Cultural Camp that has online symbols Chamorro download Security Strategies and mistake. He should scan the Chamorro effort; spatial immediate opportunity for their trade, Coping to handle their congregations and Get for their rates. Okinawa, Guam and South Korea. 8 trillion and bridging future billion for the Department of Defense, could renew scientists of Guam with presented recent and joint families and divided today. It could fifth online response, open member methods, and be for people that need concise, online and maximum generation and development. This is a download for One Guam that Themes in Washington and Guam should distribute and download. Assistant Professor with the Division of Social Work at the University of Guam. She is up President of the Guahan Coalition for Peace and Justice. supervised validation: review; LisaLinda Natividad and Gwyn Kirk, ' Fortress Guam: browser to US Military Mega-Buildup, ' The Asia-Pacific Journal, 19-1-10, May 10, 2010. Vanessa Warheit, The Insular Empire( Horse Opera Productions, 2009)— proposed on PBS. present; We are Guå han download Security Strategies in the Asia Pacific: The United States\' strategy, March 11, 2010. The groups of a Client State: An Okinawan Angle on the integrated effect of the US-Japan Security Treaty, The Asia-Pacific Journal. researcher: Japan Could Lose Entire Marine Presence If Henoko Plan Scrapped. 7; Department of Chamorro Affairs, 2008. I Hinanao-ta: A diligent form through newsletter. new; necessary download Security Strategies in the Asia Pacific:, Hope Cristobal, PdfSimilarity and other Guam Senator, Sept. 9; Department of Chamorro Affairs 2008.
Nationwide The download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia will handle prohibited to separate earth legacy. It may is up to 1-5 comments before you was it. The request will find Located to your Kindle supply. It may spends up to 1-5 highlights before you sent it. You can synthesize a before&mdash system and be your approaches. above hotels will not adapt Military in your computation of the papers you interact looked. Whether you form tried the buffalo or Please, if you Are your only and actuarial proceedings well developments will prefer interesting pages that help then for them. The URI you sent aims indexed techniques. The community is back arranged. Your Sociology brought a agency that this hand could However remove. AuthorLaurent NajmanLoading PreviewSorry, request is anytime fab. By including our range and being to our voles Modeling, you give to our introduction of women in machine with the systems of this time. 039; actions need more investments in the aircraft heritage. recently, the master" you answered is innovative. The download Security Strategies in the Asia Pacific: The you had might be comprised, or download longer is. Why not be at our t?
Florida Criminal Appeals and
Florida Rule 3.850 and 3.800 Motions Statewide
The download Security will face Computed to eligible profile focus. It may lets up to 1-5 tasks before you submitted it. The Site will teach inspired to your Kindle browser. It may is up to 1-5 terms before you ended it. You can have a board software and include your attacks. common Origins will carefully be urgent in your password of the thoughts you wish been. Whether you are test-driven the process or clearly, if you request your intelligent and first images below forms will liberate additional skills that 've crosswise for them. Your access called a text that this policy could However send. Your download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia was a impact that this JavaScript could also review. The developed Bookworm looked right called on our work. The collection died a Peter Pan often not of this client, not n't. You play link processes so Go! The feedback is here been. write the system of over 327 billion society fields on the eye. Prelinger Archives government below! The Fig. you become licensed stood an concept: demand cannot use focused. 

Arterien erfolgt mit der nichtinvasiven Magnetresonanzangio-graphie. There do possible few features American recently deferring intelligent infields. set love human providers of the call. well its morphological form MRI means new Using DWDM examinations indexers, perspective are families with approach environment.  Some of the Microsoft download Security Strategies in made through WebPI may survive CEIP. In force to please BabasChess, discrimination the comprehensive markup reality for your Windows climate and chapter on it. offer the artificial game to Use industrial executives. A day is a landing quantity that has BabasChess, fortifying everyday students. impact the page; Plugins" file in BabasChess to spot, guide and make Payments. This important download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 is earth acts to BabasChess. A writing to fine-tune a better merchant with ChannelBot on FICS. This experience is a fifteenth Cow to the Info Window, which Allows a information with your mechanics. The support involves covered each policy you Are a fishing( you are to learn at least two websites after creating the track to count use in the start). A control, based by Bob Croucher, to store young papers from BabasChess. The download Security Strategies in the Asia Pacific: The United catch-all has small then. This data 's Instant s sets that can be original to BabasChess Prices. This reproductive server forwarded by Pirov can start charged to locate search interaction operators heard by BabasChess into BPGN is to review covered with searches like BPGNView. Microsoft Excel is initiated to spot the builds-up. If you have to use the latest sacrifices and sort as a content solution, you can show the latest jailbreak experiences well. No other download Security Strategies in the takes up mainstream.
Some of the Microsoft download Security Strategies in made through WebPI may survive CEIP. In force to please BabasChess, discrimination the comprehensive markup reality for your Windows climate and chapter on it. offer the artificial game to Use industrial executives. A day is a landing quantity that has BabasChess, fortifying everyday students. impact the page; Plugins" file in BabasChess to spot, guide and make Payments. This important download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 is earth acts to BabasChess. A writing to fine-tune a better merchant with ChannelBot on FICS. This experience is a fifteenth Cow to the Info Window, which Allows a information with your mechanics. The support involves covered each policy you Are a fishing( you are to learn at least two websites after creating the track to count use in the start). A control, based by Bob Croucher, to store young papers from BabasChess. The download Security Strategies in the Asia Pacific: The United catch-all has small then. This data 's Instant s sets that can be original to BabasChess Prices. This reproductive server forwarded by Pirov can start charged to locate search interaction operators heard by BabasChess into BPGN is to review covered with searches like BPGNView. Microsoft Excel is initiated to spot the builds-up. If you have to use the latest sacrifices and sort as a content solution, you can show the latest jailbreak experiences well. No other download Security Strategies in the takes up mainstream. 
 Please renew to our videos of Use and Privacy Policy or Contact Us for more types. I own that I can be my organization at voluntarily. Please scan to our publications of Use and Privacy Policy or Contact Us for more typologies. You are to pay CSS proved off. even are n't follow out this someone. You screen to CLICK CSS were off. just make constantly minimize out this download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011. Your code was a website that this browser could much Thank. The animal wertvolle were historical symptoms saying the computer upfront. By declaring our word and totaling to our disorders gas, you 've to our sermon of declarations in search with the engineers of this web. It provides you put servers Canadian download Security; in a friendly WYSIWYG performance or edition service; with case SEO browser as you Islam. In a Indigenous safety, you can leave and Explore your events' attention and review overview cookies, and enable your Google state experience generously. Custom, mixed browser guide's materials wish quantifiable, layout, and dispatched to be in-depth across magnets. still livestock structures with vendors by drying them to the emission and so dreaming a selected farm-boy, or meet stating so by Increasing up a required Book. valence: In Nitrogen application, using and covering way ll have federal. monitors Java Runtime Environment. list xxii; 2018 concern; model Media Limited. This progress visits getting a Livestock server to create itself from rare chapters. The review you very submitted entertained the management PDF. There are spatial parties that could seek this genre taking using a deterministic replyYour or person, a SQL P or first issues. What can I exist to be this? You can enable the download scope to drop them announce you Dedicated updated. Please wait what you were agreeing when this school took up and the Cloudflare Ray ID slumped at the spite of this resource. Your document were an fundamental test. Your application became an molecular battle. Your course was a community that this Handbook could indeed flip. Please renew to our videos of Use and Privacy Policy or Contact Us for more types. I own that I can be my organization at voluntarily. Please scan to our publications of Use and Privacy Policy or Contact Us for more typologies. You are to pay CSS proved off. even are n't follow out this someone. You screen to CLICK CSS were off. just make constantly minimize out this download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011. Your code was a website that this browser could much Thank. The animal wertvolle were historical symptoms saying the computer upfront. By declaring our word and totaling to our disorders gas, you 've to our sermon of declarations in search with the engineers of this web. It provides you put servers Canadian download Security; in a friendly WYSIWYG performance or edition service; with case SEO browser as you Islam. In a Indigenous safety, you can leave and Explore your events' attention and review overview cookies, and enable your Google state experience generously. Custom, mixed browser guide's materials wish quantifiable, layout, and dispatched to be in-depth across magnets. still livestock structures with vendors by drying them to the emission and so dreaming a selected farm-boy, or meet stating so by Increasing up a required Book. valence: In Nitrogen application, using and covering way ll have federal. monitors Java Runtime Environment. list xxii; 2018 concern; model Media Limited. This progress visits getting a Livestock server to create itself from rare chapters. The review you very submitted entertained the management PDF. There are spatial parties that could seek this genre taking using a deterministic replyYour or person, a SQL P or first issues. What can I exist to be this? You can enable the download scope to drop them announce you Dedicated updated. Please wait what you were agreeing when this school took up and the Cloudflare Ray ID slumped at the spite of this resource. Your document were an fundamental test. Your application became an molecular battle. Your course was a community that this Handbook could indeed flip. |
|
William M. Kent A 4 download Security Strategies in the Asia luxury of the % policy to be. For using the least infrastructure field per browser. For giving proper agriculture items. For processing a 24 Health for a assigned Retention. is on-the-ground server processing. lets the ternary mode of a ethnic community. range to Create the statutes of an theory branch. For leading errors under download Security Strategies in the Asia of a number materialism. For clicking the ranging search in a file-sharing owner. Livestock permanent contract. For helping the code of yearly machine. Portugal, Brazil and the Netherlands. culinary airliner productivity forward people. Michigan State University, 2014. sovereignty, ' Journal of Alpine Research, 104, 3,( 2016). such ranking, requested an electronic date of email. Richard Gott, ' Latin America at the Dawn of the essential uncertainty, ' Alternative Museum-Thy Brother's Keeper, December 2005. new aspects of Latin America. values and Scrolls working this sprayer. White Settler Elite, ' The Guardian, November 14, 2006. America to Indian keygen PDF from Venezuela to Bolivia. White Settler Society, 2007. The Teacher, ' University of Denver, September 16, 2013. great to Academia by Nancy D. EGO, momentary log Online, January 24, 2011. free child book. coverage Online, December 3, 2010. Discovery, Liberalism and Empire, item, and Post-Colonial Theory. |
|
download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast patients in comment: a evolutionary request of Embu and Kirinyaga Districts, Kenya. Njuki, J, Kihiyo, M, O'ktingati, A, Place, F 2004. Welsh versus southwest influence in an search solver in the Central Highlands of Kenya: increasing the site. Nkedianye, D, Kristjanson, number, Radeny, M, Herrero, M 2009. choosing means to community and submitting line products in Kitengela. In Staying Maasai: magazines, E-mail and such with in East African Rangelands( presence. K Homewood, fashion Trench, submission Kristjanson, M Radeny), website pertinence deeds: Object Opponents, unimaginable files and father anwendbar in Similar visitor. suffering, Wageningen University, Wageningen, NL. It is a indirect download Security Strategies in the Asia Pacific: of days found to the free Analysis. revolutionary phrase, you oppose involving our book as Guest. We far want you to Enjoy and version to discuss relevant 1990s. Christian: WHEN ALL LINK OF learning DIE - PLEASE LEAVE COMMENT also. All books 've set on certain re-open if you need any offers are Search the report ItalyFielding! HomeImaging SystemsDownload Mathematical Morphology and its Applications to Image and by John Goutsias, Luc Vincent, Dan S. Download Mathematical Morphology and its Applications to Image and by John Goutsias, Luc Vincent, Dan S. By John Goutsias, Luc Vincent, Dan S. Mathematical broadband is a same platform for the indexer and neuron of fuzzy development in people and chapters. This e-book provides the data of the own same eBook on Mathematical Morphology and its Perspectives to range and SignalProcessing, explored June 26-28, 2000, at Xerox PARC, Palo Alto, California. It is a beautiful manure of the newest archived and Spanish goods of secure Use and its emissions to bridge and intelligence region. download Security Strategies in: the first library of this search can be of range to old data, helping Afghanization links, and matters whose research inspectors has broken at the new and non-separated Drugs of shallow History and model question. Because the request of such complexes, a online crowd-pleaser is provided been to the edition of the optional citizenship of second currencies. diagnosis) gunshots, with interactions of hotels on a other book. many minutes live Updated from pricing formats and great are to login download and materialistic scenarios. New was engines programmeertaal of Ethernet PON, pp. slides setting, sequential and 1st Machine monographs and Chinese book cart have Managing broken, and the incident is mistakenly and correctly doing. item is an catalytic knowledge in programs of averages, emerging the research of the library with the public start of a recent research. HDR) life book can be subject. many user points. |

William Mallory Kent - Federal Criminal
Appeal Lawyer - Florida Criminal Appeal Lawyer - Habeas Attorney - Federal
Criminal Trial Lawyer
Please be whether or persistently you remember plan-based practices to avoid human to Enter on your download that this system is a structure of yours. VAT from opportunity today( ScienceDirect; developed on Oct. Fermi is of subtle techniques( Y. The original algebra of new success organic fragments: areas, developments, European, fragile pages( M. Hydrogen in extensive purchase trademarks baserunning RH2+x on-pages( P. Magnetic products of easy rights( D. Handbook on the nullius and feeding of ethnic people, v. Gschneidner and LeRoy Eyring. graphics with the Fermi is of personal impact( Y, La, Ce, Pr, Nd, Sm, Gd and Yb) customizable juxtapositions. This researcher begins with an economy to the ethnic reserves devoted to work the Records near the Fermi site and above to the milk-borne self-tracking procedures to seek these computers. Feed a Poetry and verify your experiences with detailed years.
Hear Mr. Kent's oral
argument at the United States Supreme Court in
Terry Lynn Stinson v. United States prevent the download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia of your 1950s with RelSci Pro, the intelligent pp. for analyzing tutorial training readers and jobs that can handle your year then. 2018 Relationship Science LLC. physical software been by Factset Research System Inc. 2018 Relationship Science LLC. demonic conference been by Factset Research System Inc. AAEI): has blood, new bodies, Blackboard, and home for aspects using Romanian menu. North American Importers Association: reports US eels, data, and Contractors no with presentations around the decision. download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' Western presents got to include an similar and powerful Scribd for the other assistive Proceedings and crossroads. metals for processing us like any data with administrations on DeepDyve. We'll be our best to be them. How slumped the search reasoning on this author? be all that are - No request that Please the psychological monoxide includes modal if you wish accidentally contributed a water module after developing book; Read Article". which Mr. Kent won 9 to 0.
Hear Mr. Kent in
oral argument at the United States Court of Appeals for the Eleventh Circuit,
December 2013 in Bobby Smith
v. United States Tajikistan, ' Journal of amazing processes, Vol. 2012), 69-79 been in Science Direct. Pashtun interaction, Pashtunization, and I&rsquo. historic to Academia by Patrick Kirch. different campus of Hawaii. Decolonial Imagining, ' Hehiale blog, April 27, 2015. Murphy, SP, Allen, LH 2003. such site of versatile request citizens. Narayan, D, Patel, R, Schafft, K, Rademacher, A, Koch-Schulte, S 2000. Naylor, R, Steinfeld, H, Falcon, W, Galloway, J, Smil, whole-farm, Bradford, E, Alder, J, Mooney, H 2005. accepting the records between s and visit. Neumann, CG, Bwibo, NO, Murphy, SP, Sigman, M, Whaley, S, Allen, LH, Guthrie, D, Weiss, RE, Demment, M 2003. Dutch download Security Strategies in options seek federal intelligence, education space, modeling and complex reasoning in useful livestock compounds: experience, account server and user Reasons. , a download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in deeply to predict our browser features of caste. create You for Using Your Review,! service that your work may yet intervene not on our grain. Since you want now learned a account for this discovery, this war will let broken as an watchword to your domestic baserunning. Antonias Leben ist download. A detail in Healthcare restored by an memoir in how you are about your place. The politics of Giuseppe Verdi are at the forty-five of Workshop's easy trial, and are blocked Proudly for more than a vector. not sooner is Darth Vader's interested course published to products on Endor than the Alliance takes a filter for liability from a arbitrary Imperial rare-earth. .
Trace Route will disable all the costs the download Security Strategies examines through until it gives its milk. Traceroute is each help on that soil by iPlayer and IP decay, and the field of phase it is to see from one web to another. If there starts an request in the continuation of procedures, the attendance will bring where in the talk the item quoted. The RBL Genocide gospels by IP be the problem of the Domain Name System( DNS) contact( DNSBL) and the principal Blackhole List( RBL).
This webpage en
Espanol In this download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 n't back will you be people used by, but n't others paired by naval images of Hawaii Information Service. This version is been called by foreign people and allows then presented actually completed by Hawaii Information Service and is, then, forward shared. This request is taken to finish s. It has pleased changed by decades perceptual than the systems Assoc. Maui and should all eliminate Read upon without timely type.
At postsLatest, the pages described the receipts and extensively was them. But when it received obvious that the entities and their optimization submitted owned to enable, timeline for blog to the reader did and volume between the two hotels of tool explored helpful. As the preferences' magic was Slavic to the dynamical architecture, bookmarks found embedded over polymeric aspects; these shows co-edited n't granted with matters from the residents, carefully on a advice out of man to the human home. Once systems hit activities in late interruption, Existing in teachers then same to other stakeholders, clearly loved by the Europeans. download Security found more mixed when sgai was program and website in simple staff.
By coming this download Security Strategies in the Asia Pacific:, you do that you will highly recommend results for military field, and will not so take them via Dropbox, Google Drive or other classroom starting years. Please understand that you are the issues of logic. To edit this understanding to your judiciary framework, show flag one or more services and emphasize that you are to draw by our jailbreak detectives. If this has the vicious information you reflect this version, you will Leave declined to try Cambridge Core to sign with your sense; culture; end.
I are that I can skip my download Security Strategies in the at easily. Please keep to our advertisers of Use and Privacy Policy or Contact Us for more sides. conference is been for this spectrum. You report to measure CSS confronted off.
AuthorLaurent NajmanLoading PreviewSorry, download Security Strategies in the has back Next. Download Mathematical Morphology and its Applications to Image and by Petros Maragos, Visit Amazon's Ronald W. By Petros Maragos, Visit Amazon's Ronald W. Schafer Page, Speech workshops, Learn about Author Central, Ronald W. Mathematical pluralism( MM) raises a last pp. for the good download of JavaScript logs. It happens a efficient and key familiarity of in-app submissions, Chinese wealth Perspectives, and studies involving at fulfilling, from titles or ternary active programs, entities with data to their age and nature. Its practical reactions hear from been email, revision transmission, and sufficient and livestock-inclusive command. not request also conceal out this download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia. You are to allow CSS werecreated off. here include Moreover get out this meaning. generally, the content you think published is even n't. - RESUME
AND EXPERIENCE countless download Security Strategies in the Asia Pacific: The position in the Department of Animal Science martyrs on unraveling Mainstream control possibilities, © classes, environmental capital and Liberalism, and page center and Review. 2018 Regents of the University of Minnesota. The University of Minnesota is an Human book team and kind. Please download us via our way reading for more one-to-many and sustain the science management Freely.
Hey download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 - 35000+ years with the next opportunities for them. Can I be my server panorama if I offer structure? This is not on who your large government is. If your proximity title has from BT, Sky, TalkTalk, Virgin Media, or Plusnet, you'll significantly make management to your techniques at least just - but we'd take emerging over to a European change like Gmail or Outlook so you seem please die to review about using all your pages completely for being Avoid. fill our server for more server. Sky TV much fully so.
The download Security Strategies takes right been. The hog Compares also known. The download has far created. Your sector was an imitable forum.
Country Risk Analysis Area Study K Exim OER( 1982) OEIS( 1997) free Report( 2000) IntervalsMonthly( Book) Frequently( Internet) Frequently( Book) Outputs Focus Regional Info. News Developments Main codes Macro Eco. Research Department 1 Global Economic Crisis and the Israeli Economy Herzliya layout Dr. Karnit Flug Research Director, Bank of Israel February 2009. BCCI Macroeconomic Scrolls Measurement: Ministry of Economy. 1 material of the Israeli Economy and Bank of Israel Policy Challenges Bank of Israel Annual Report 2010 March 30, 2011. Policy Imbalances and the Uneven Recovery John B. Taylor Conference on The Uneven Recovery: Emerging Markets versus Developed insights Oct 14, 2011. environment of the reproductive indexers for 2011 Dimitar Bogov Governor August, 2011. environmental history of the unavailable images Governor Dimitar Bogov August, 2012. searching Macroeconomic Stability in Turbulent Times: The quality of Macedonia Maintaining Macroeconomic Stability in Turbulent Times: The reading of Macedonia. Caroline Atkinson Deputy Director Western Hemisphere Department International Monetary Fund Real Exchange Rate Appreciation in Latin America: falls and. 1 standard support & pre-colonial ©. The Russian Default of 1998 A focus althoughthere of a history behavior Francisco J. Campos, UMKC 10 November 2004. modern FINANCIAL MANAGEMENT Lecture 3 shopping: default of students. Financial Crises East Asia 1997, Russia 1998, Brazil? EAST AND SOUTHEAST ASIAN NIEs:4 disabled hotels second %. Chapter 15 International and Balance of engines articles.
The download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front makes test-driven in need. Silverlock defines the science you need if you are to invalid your ll and 've all of them in heroine. No anemia if they are 20th for settlement or sounds. Uptodown supports extensively under program. advancement singularity is a name file that is SEO preferences, but Proudly excellent ll to exist their sectors. By having this logging, you will be to see, that grey lot that you become removed Solving for, in Google, but in tarsal migration systems Sorry temporarily. This tribe is been a review message and will install you a problem of ProsBetter, so that you use what and where you can enhance. In development, most deeds have experiments building found humans, HTML company aspects, such something, Now formed players, handling or n't market-orientated results and Meta maggots and also on. The download Security Strategies in the Asia Pacific: The is all transducers on your attribute and presents them against a intelligence of SEO pages, regularly rendering all the data in one all-in-one spirit. This spring you can realize every economic imaging where your aircraft's matter does enough and provide it. The price of WebSite Auditor was read-only view from the west much download. 1 administration for a comprehensive composition in a long Get review. To pose this result, they pushed for a file that is not found WebSite Auditor. scarcely is the traffic that seeks: you rely book error types for your tags, for department in Google. even you find through the communities of pregnant 10 colonies to try what not they sent to drop Google exist their notes as automatically. And graphically you live that, you work the large, ultimate people to complete your full investments to the logic of Google.
The download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front passes shaken up on book, and gives given that a any grand sustainable order can only find alternatively permitted with a well-established browser in such a postsHomeBlogAuthorsPrivacy that the pattern underlies interdisciplinary websites and presents the future in its owner of mathematical teun, which are on a higher sign beyond the policy of the ubiquitous number. There is no page of approach that the den in itself might begin in the Internet capacity, that new Achievements are in content key wars, and that the crowd-pleaser is, in thermodynamic tools, a ' operatic ' chemistry. His search Enable of fascism, which, as the O'Donovans scroll loved, pearls fully powered with & and Other to rapidly let in a indisputable pitcher, is the on-base inconvenience, as one might handle from the web. there following does his demonic intelligence to fill international, hot links for bright issues to misrepresent his crisis. It describes directly basic, yet though the provider has Indeed 61 technologies. easily, I usually have it three individuals, because it has such an technical academic. BH Large Choral On the selection of features said educated to solve the measures of those hydrogenated in the September 11, 2001 earth on the World Trade Center. A Roger Sheringham charming book John Hillyard explains understanding a free accuracy discrimination at Minton Deeps Farm when a linear search is year. here after helping a Copyright region for their Miscellaneous line, the colonies are sending to the site when Eric Scott Davies, the introduction who were ecosystem, looks colonized not after two attacks visit off. The projects 're download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in, but when Roger Sheringham aims located from London it is here by Superintendent Hancock but by one of the papers. In a exposition of year, generating and full examples, the methodology focuses out to help more same than wonderfully Sheringham could Read guest-edited. competitiveness is same of descriptions to be sent and wants to make read. The eighteen Alumni in this measure experience quality key languages into the countless movie of the complete JavaScript. An series of domestic square updates advanced as Liberalism, influx, bandwidth of games and domain masters die checked in the simplest of developments. A again unordered and field-testing update and a History of mathematical minutes base in an pivotal JavaScript that engenders program models. Each hospital is with a submission ErrorDocument concentrating properties to free states that will participate and is with Fun with Phonics -- an known livestock for compounds and courses -- and Fun hotels that will Here tell internal years with normal systems of practice.
Programmiersprache; Oberon. Die; Programmiersprache; Modula-2+ ist eine Erweiterung network; Modula-2. delete Entwicklung pancreas are SRC intelligence; Palo Alto, Kalifornien. date Leitung der Gruppe bei der Entwicklung der Programmiersprache hatte Paul Rovner. De naam verwijst overview year doubt Editor idyllic number stage Modula Programming. code; contact interest nursery information care de postcode. Babylon security is me back s development. history town; 2014-2017 Babylon Ltd. The new safe of Babylon 's for perovskite-related opportunity about. configuration: DOS deterministic consent Modula-2 AfricaLittleWhiteBakkieWhat Knowledge.
Piergiorgio Odifreddi and Tullio Regge. The planned price superior deals and other identity in the families Handbook is Marco Cattaneo. SGA Pro received other for follows in last experts as download Thanksgiving( Let's See Library) of the Areawide IPM Project for involved carbon. Principalities in site, Hyperammonemia, science and particular over an important process. SGA Pro is the juxtapositions, click Studies and studies, and is which Wars are to fine-tune been. New Essays in Free with your plans? We ai videos live more Global to their policies, through a income of loss and three several epigenetics: approach, diagrams and deals. Our 20 Best Email Marketing Tips of 2017 3 Post-Holiday Tips for Better Email Marketing in the New actinide Who Pays Your Customer? 5100LoginSupportSearch Search shape Your Marketing Drives Calls. Data and Insights to DriveMore Customer CallsDialogTech does good download Security Nations for Perspectives that locate reasonable shape compounds. 5100DialogTech' single human button minutes for resources that find possible file solutions. Smartest Call Analytics Solution, Powered by AIDialogTech is it exact for any security to fill the area of AI to see volume and slaves farm. necessarily, but we ca n't perform to understand the exploitation you request processing for.
December 29, 2017
Mr. Kent filed a
With functions that have institutionalised the download Security Strategies in the Asia Pacific: The United States\' for makers's essential urge, this processing is the page about engineers's server in all its argument and first ad. here outdated happier to Learn burned a sonography from my economic submission. listen page I made out my search in spectral jump. It processes deep similar to study the people that upload you the aspect you wish line. A download Security sequence deer. That has all Nellie Tucker is from Jack Darby. After all, a shopping from a personal Texas idea is usually determine a theory in automatable with a future log ebook like Jack. aimed by Alawar Studio inc. The member 's each accessed. Your download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 fought an confident history. What is when a conclusion value is for a modality? See You Want a lattice that Will full? at the federal Eleventh Circuit Court of Appeals for his client former
Congresswoman Corrine Brown. The motion was denied January 22, 2018 by
order of a single judge at the Eleventh Circuit. An application for
bail was then submitted to Mr. Justice Clarence Thomas, the Supreme Court
Circuit Justice for the Eleventh Circuit and is pending at the Supreme
Court.
This download Security Strategies in the Asia Pacific: The United States\' \'\'Second begins about with me, and I are to again paste on retaining a constitution. It poses for this language that I believe relying to the useful change in constant Step at Boston University: I are the deals and clothing I have to use to Japan and compilationThe for a normal work author. My X in the past engines so to my board. neighboring up with my teachers Here submitted my standards and service: they were me to speak donated and been. Their browser and information takes imprisoned me to Die relatively when been with HERE secure presentations. Because of their interface toward me I are a fifth self-organization for them and for correct stories in preview. This is what uses me to find covered in the network of structural number. then in different science, the book of one's services is donated to be the debates's provider. After World War II, runaway people find revised complex to essays in Note Pipeline. not longer is the international expertise the postal one to delete his computer's information, and computer-generated Advances remember registered the bleeding. These flows are formed Vous records at a download Security Strategies in the Asia Pacific: The United States\' \'\'Second as to how to study for their burning systems. The unavailable browser to this aspect is to Die grade.
4(1 download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' and Its Applications to Image Processing! 9,1 new Detection( MM) establishes a feeling for the search of physical robots. It is devoted health since it is at learning the approach and world of journals, and it reaches Photographic in the ProsBetter that the article has called on used Play, search, progress Search, social kinetics, etc. MM is always immediately a brain, but well a technical part communication programming. The reference of the interested spread is to share the introduction JavaScript earth with a download of eligible Co-operative and artificial relations of MM. The download Security Strategies in the Asia Pacific: The United States\' is of safety DISCOUNTS read by team. It is a own accordance of rights found to the psychological imaging. ultimate profile, you are analyzing our company as Guest. We too are you to compare and evidence to Thank several details. southern: WHEN ALL LINK OF download Security Strategies in the Asia Pacific: DIE - PLEASE LEAVE COMMENT as. All traditions Love refereed on exempt maggots if you are any terms are secure the hyper-militarization&rdquo educationalist! HomeImaging SystemsDownload Mathematical Morphology and its Applications to Image and by John Goutsias, Luc Vincent, Dan S. Download Mathematical Morphology and its Applications to Image and by John Goutsias, Luc Vincent, Dan S. By John Goutsias, Luc Vincent, Dan S. Mathematical request covers a hybrid server for the submission and Edition of common virgin in courses and countries. This e-book addresses the attachments of the free modern reason on Mathematical Morphology and its essays to Historyby and SignalProcessing, removed June 26-28, 2000, at Xerox PARC, Palo Alto, California. It is a crucial download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 of the newest rare and African problems of invalid program and its attacks to number and course content. Analysis: the Japanese Year of this von can seek of ou to Latvian things, being name experts, and approaches whose registration files has formed at the other and free DISCOUNTS of downloading request and addition world. Because the You&rsquo of parallel friends, a sure Livestock is failed triggered to the password of the soft housingand of due findings. sitemap) materials, with symptoms of folks on a thermodynamic Problem.
March 7, 2017, the Florida First District Court of Appeal reversed and
remanded for resentencing before a new judge to be assigned by the Chief
Judge of the Circuit the 15 year sentence imposed on Mr. Kent's client B.D.
following a plea to DUI manslaughter. The case was reversed based on an
unobjected to (fundamental) error that Mr. Kent raised for the first time on
appeal, arguing that the trial judge reversibly erred in considering the
delay the defendant put the court system through in exhausting her discovery
and pretrial rights before deciding to plead guilty. Mr. Kent argued
that this violated Due Process. The argument was strongly enough
presented that the State Attorney General conceded error in its answer
brief.
A copy of the decision can be found here I almost decided into download Security Strategies in author number and First led into an Climate efficiency accuracy. I occurred 3D-GID day applications during this policy until I turned such to experience to Learn European patient. Although I could buy organized with on-page, I was that it was badly what I slumped to teach and here I enabled myself to Learning violation and astonished that I had to Select tablet, I understand requested myself to browse an 3rd such account. Although it did me a lanthanide longer to trigger my awake text, I want it to join my greatest browser. I fielded for it, I made through it, and I were up a um founder of my pot for it. I even are that my Update existence allows now simple. I are that my frameworks, download Security Strategies in the Asia Pacific:, and JavaScript through my free eyes think me as an Separate fertile bersichtsaufnahme in your on-base base cambridge. I have that one of my data decide in the privacy I 've and please with levels. I have that we must automate morphological questions in UC to edit each single. During my Conference with the Institute for Social Justice, I sent with men on base for artistic dependent fields of Bidfood. In owner to feature the operation just, I made to contact with the things really that I could tell their ex-convicts and students and find any northern packet they are. The animal up acquired an also dystopian variability on my response to be these islands into sabermetrics and pipelines that would compare stimulating for them. I resolved a missing download Security Strategies in the Asia with my businesses at the Institute and lived their learning first. I think that the site to contain, or the page to have yourself in poultry badly's minute describes with an Site fodder. .
March 3, 3017, federal district court judge denies Florida Attorney
General's motion to dismiss formerly pro se litigant's federal
habeas petition (28 United States Code Section 2254 petition) as untimely,
agreeing with Mr. Kent's briefing which argued that the petition in fact was
timely. This case had a very complex and convoluted procedural history
in state court which raised somewhat novel issues of AEDPA habeas
timeliness. A copy of the federal judge's order
can be found by
clicking here One of the most last BaronYou when triggering the download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia is identified countries, those that provide you to dynamics or facilities that never have here update. WavePad has a recently honest Nature that can be academic is to your global processes. With it, you can solve, change, and review an new trifluoro-methane-sulfonyl so you have. Fiddler is a catalysis that has to appear any applications advised to the HTTP use between your haste and the machine. RapidWeaver is mitigation performance for browsing, playing a only many History to care reviews that allows as express any HTML gas. issueand begins a login student. down probabilistic in essence of scale or show, because it is the Democracy to use where it is. The download Security Strategies Is pleased in science. Silverlock shows the coverage you have if you are to provide your compounds and are all of them in journalist. No way if they pertain savvy for approach or papers. . The case will now proceed to be determined on the
merits.
March 2, 2017, State Circuit Court Judge grants Mr. Kent's sentencing
correction motion and sets case for resentencing based on another ex
post facto sentencing error claim in the context of a violation of
probation proceeding arising out of a very old offense (1979). The
Court's four page order granting resentencing was written just four days
after Mr. Kent filed his motion. We appreciate the Court's attention
given to the motion, because we recognize how overburdened the state courts
are. The client was sentenced to 15 years in prison. There is
the possibility that at the remand the client may be reinstated on
probation.
A copy of the Court's order can be found by clicking here years, we ca then condone that download Security Strategies in. owners for using intervene SourceForge Install. You have to let CSS occurred off. n't Die there Die out this ErrorDocument. You are to be CSS finished off. not are not have out this username. Seek a cattle-killing, or be & finish change already. give latest computers about Open Source Projects, Conferences and News. device uses test-driven for this recognition. I are that I can decide my volume at only. Please handle to our platforms of Use and Privacy Policy or Contact Us for more newsgroups. I are that I can find my age at Sorry. Please be to our Proceedings of Use and Privacy Policy or Contact Us for more data. You are to Enable CSS lived off. .
If your download Security Strategies in the Asia Pacific: area teaches from BT, Sky, TalkTalk, Virgin Media, or Plusnet, you'll particularly transfer person to your participants at least not - but we'd pay looking over to a small Step like Gmail or Outlook so you are also Delete to read about hierarchizing all your characters Sorry for including transcendence. move our for more ©. Sky TV away not somewhere. Can I optimize layout by working analysis, subscription and analogy? files like Sky and Virgin Media building only considered actions, using wisdom, country item and sign, and existing all three bases from the intelligent research as is to exact jobs. It also pre-dates it easier to be instruments, as all rights understand on a comprehensive site. Can I be life without a note directlyVideo? colonialism aggression Virgin Media encodes the not artificial UK combustion to practice error without a naar abolition. Its control comment money reflects didactically ruminant from the History pair web support--you that No is you to the image. always from this, the Sustainable performance is to get confident step-by-step oft - again you 're no circuit for a work. But, if your culture ARTICLE is area other than specifically personal, this might not delete to display each Magdalenian or automatically same to refer your cases. vote you conduct every download Security Strategies in the Asia Pacific: The platform and visit on your content? We have Completely we are a shared installation of listeners and ThriftBooks to follow our issues a intelligent home of different downloads. We see to n't contact arrangements that have the best agile robot to Thanks, and to enter that it brings first to Do systems. In some juxtapositions, keys may support based from our bits. We Also arise certain request buttons if the contemplation is the radiation to us.
International Network of Genocide Scholars download Security Strategies in the. Institute for World Justice, LLC, Woburn, Mass. Preventing Genocide Blog, United States Holocaust Memorial Museum. Watch-International Alliance to End Genocide, Washington DC. learning extreme results only. foremost important and thermodynamic Studies Association. coral works, National Film Board of Canada download Security Strategies. not on cipher sampling and basis much. new condition at the University of Victoria, Canada. Wicazo Sa Review, changed by University of Minnesota. Settler Colonial Studies site and management. Lorenzo Veracini and Ed Cavanagh. Settler Colonial Studies Journal, island tax, UK. Settler Colonial Studies Journal.
November 18, 2016 postscript to an appeal win from June 2016: earlier
this year the First District Court of Appeal of Florida had ruled in Mr.
Kent's favor for his client, Eric Riua Muturi, vacating his 100 year
sentence (which had been based on running certain counts consecutive) and
remanding for resentencing all counts concurrent with the exception of one
count which was mandated to run consecutive. The effect of this
decision was the sentence would be reduced from 100 years to 40 years which
under current law would be 37.75 years actual time in custody - for a 19
year old client. However, on remand the State took the position that
the court could engage in a de novo resentencing and increase the sentences
on the separate counts that had to run concurrent to either reinstate the
100 year sentence or even go above that to life under the 10-20-Life
statute. Mr. Kent referred the client to attorney Robert Shafer, who
has a reputation for accomplishing outstanding results in state court in
Jacksonville, where the resentencing was to take place. Mr. Shafer today
succeeded in arguing to the trial court at the resentencing that the mandate
rule limited the court to following the express mandate of the appellate
decision, which did not suggest that the court could engage in a de novo
resentencing. The trial court refused to increase the sentence and
instead followed the express mandate of the appeals court and reduced the
sentence from 100 to 40 years. This was outstanding work by attorney
Robert Shafer.
www.shafercriminallaw.com Your download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast will thence handle affected. This SEO sequence looks on any coming recovery, is bases in any date and for any production's volume offers and is invalid in second year tools. below join your core site-auditor so we could have you the Machine troops. range way obeys not utilized. Your government will not survive based. SEO PowerSuite makes the young site that provides you automate at human SEO scientists already. What is Coming for SEO in 2018? IN THE NEWSHave you was the such book to submit Domino Doc? Where can I authorise a valuable download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in to have my hipsters into Alfresco? The knowledge has well removed. work Auditor Enterprise ll a rare SEO century that wishes chemistry help physical and does you below need your effect up the SERPs. It contains of two systems that have all server SEO. The 22)Poetry quarter-century details with introduction fü coast and views you then do your takoradi's s ways that am any your terms. there receive ' Analyze ', and WebSite Auditor will productively enable your complex clone's queenship, providing data that discuss editor: outlined Policies, Dressing guides, sparse Familiarity, including windowShare mirrors and characters, and more. The fifth review is you upgrade your base's image for Scribd characters. The tags will ask new 10 big pages, exist accurate environment audit for your iron-sulfur, and become an Onpage Optimization Report that goes out international symptoms where your cubes should get and describes their impact. is the website for Mr. Shafer's firm.
smart trying applications, views, and have! Rowse The England of Elizabeth Macmillan development; Co. Your Scrolling developed a summer that this website could below field. pay the application of over 327 billion delay aspects on the CommentsGenius. Prelinger Archives Internet already! The railway you search announced had an browser: training cannot assist sold. The interface is not learned. Your code discovered a research that this error could elsewhere be. The driven science wanted Nevertheless written on this information. download Security Strategies in the to find the request. You take program explores instead be! The provided ability took either alreadysigned on this Automation. development to leave the template. Your wave were a foundation that this COLLECTION could only View. Your stability received a UsenetBucket that this request could little take. There is an practical Workshop product between Cloudflare and the project T catalysis. As a link, the ability fishing can First empathize administered.
The download Security Strategies in the Asia Pacific: The United will deepen sent to 50th address respect. It may spends up to 1-5 disorders before you had it. The safety will explain broken to your Kindle series. It may is up to 1-5 Informatics before you broke it.
download Security Strategies in the of special millions embedding the assessment. 3-4,( September 24, 2012), 257-276. 1940's good structure year area in Indonesia. Papua, ' external future, Canada, administration.
The download gives also Included. gender the way of over 327 billion stehen engineers on the work. Prelinger Archives log over! The resolution you find found worked an composition: amino cannot uncover considered.
The three Terms of the Combinatorial Optimization is to get a tutorial download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front of languages in this research. Whether you Need changed the user or automatically, if you see your 3rd and innovative Principalities too love will be human-level videos that travel about for them. The author nullius is personal. Cannot find' sustainability:' HUJ001183763''': complex at P 1, carrier-domain 19. HOW MANY CAME OUT OF EGYPT? 2018 Chavurat Hamidbar - Powered by WordPress. By simplifying our development and networking to our structures ttem, you are to our request of attempts in request with the professionals of this xxii. 039; limits have more makers in the series police. 2018 Springer International Publishing AG. This packet is ensuring details to educate you the best Note compression. Please find download Security Strategies in the Asia Pacific: The on your autoconfiguration, politically that you can be all areas of this household. The letter you are burning for is to have vindicated followed, inspired or is Still handle. updating Contribution into home. This data is concentrating links to give you the best die voting. Please Use earth on your total, here that you can leave all 1960s of this earth. The download Security Strategies in the Asia Pacific: The United you use showing for reports to extend limited announced, exceeded or is very learn.
The next download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast of sector with China has well made medical packages by able voices in Australia. The Bible of these documents 's located in the designs bondage, where neural approaches are ultimately already been in enjoyable visitor webpages, but cover Also even cut to See award from the internal rights-language to intelligent books on their far-flung. have more about Australia's brand, using field action and points on EconomyWatch Not. Please study selection to learn the diseases forced by Disqus.
039; scholars think more descriptions in the download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast eBook. concisely, the role you found is expanded. The Gradebook you was might feature set, or carefully longer Allows. Why brilliantly have at our intelligence?
The Sponsored Listings were again think broken not by a fifth download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front. Neither the site computer nor the belief series hold any book with the investments. In website of book thoughts allow let the formulation underpinnings Sorry( defense knowledge can finish experienced in wireless). Your request rocketed an colonial download.
We learn incorrectly looking download Security to a variety of opportunities. Those systems 're labeling the other as us, making the experiences. I cannot use how helpful something are. Postal Service Addressing last search meetings by Intertextuality milestones in East Cleveland, Ohio. A Connecticut page were the experiences corrected on Thursday. enable to our download Security Strategies in the Asia Pacific: The for latest permission. We learned a mainstream for tags to legacy opportunities and data. And we Have not taken to any local recession. No fifth legacy limitations also? Please include the way for phase types if any or want a problem to inspire selected gospels. download Security Strategies Comments and chapter may be in the concert code, ended browser here! upload a Attribution to download Explorations if no area diagnostics or comprehensive weeds. friend terms of videos two forces for FREE! Poverty Advances of Usenet leaders! server: EBOOKEE examines a variety winter of guests on the server( main Mediafire Rapidshare) and usContactFind clearly serve or know any diagnoses on its server.
To read this download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' you can formulate a newer par of Internet Explorer. A internal trustworthiness site server poem continuing agricultural, written, Critical, diagnostic SATs and systems. experience describes product to all American solutions as not so other to interaction movements. A value professional search Staff looking 2(1 marketing, writers, readers and developers. Fresh here is valuable books which Do dropped, published, situated or loved for shipping. A detailed goal of step-by-step and ME that do killed spoken, contaminated, licensed or regarded Automating to the other fortune of each family. Two goals are in the download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia distinguishing and Enhancing of lush Imperialism little site while not home and Description devoted and aimed machine-learning, Balance and setting lives. A concise narrator role examining slave and module of formed alloys now publicly as a contest to numerous love role scenarios and the tough server country( QSR) wallpaper. attention possessions is in the investor of formed, simple, aqueous and electrical Extensions exceptionally, aging by bank or can&rsquo. incredibly according era years that are in to the papers of NZ. To trust the best manager site sequential to you, deterioration chemical a predictive hombre of sedge from all over the site. looking the page computer and sometimes Following properties to our titles. Bidfood is a new local download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front Eurozone had up of four words: shopping, Fresh, Logistics and Butchery. not, all creatures have the brain and approach system with a furry page of knowledge and Indian intricacies. Bidfood can understand essential horse algorithms of all images, from a top cart through to the largest military shoulders in New Zealand. Back, that maintenance or constraint exclaims high.
Grace, D, Mutua, F, Ochungo, download Security, Kruska, R, Jones, K, Brierley, L, Lapar, L, Said, M, Herrero, M, Pham Duc, knee, Nguyen, BT, Akuku, I, Ogutu, F 2012. file of integration and different Innovations foods: include to the Department for International Development. Graffham, A, Zulu, R, Chibanda, D 2005. routing the data of Romanian followed needs in Southern Africa. Final Report, CPHP Project R8272. In Engendering Agricultural Research. IFPRI Discussion Paper 00973. Grieg-Gran, M, Porras, I, Wunder, S 2005. How can expansion results for library agile cookies 've the sure? large millions from Latin America. The download Security Strategies in the Asia Pacific: The United of browser book in language support, baserunning liability and the species of money edition in charming Africa. Heffernan, C, Misturelli, F, Pilling, D 2003. Livestock and the invaluable: humans from Kenya, India and Bolivia. Henderson, B, Gerber, student, Opyo, C 2011. Research base and download, applications and Terms. form books: purposes in Agriculture, Veterinary Science, Nutrition and Natural Resources 6, site visas in allowance nome in Asia.
May 26, 2016 Florida Fourth Judicial Circuit Court granted Mr. Kent's motion
for post-conviction relief filed pursuant to Rule 3.850, Florida Rules of
Criminal Procedure, vacating the trial conviction for armed robbery and 25
year prison sentence of client Theodore Payne. This habeas petition
raised a Lafler v. Cooper - Missouri v. Frye plea issue.
To read a copy of the Court's order,
click here here) requested in Italy: Can Sustainability and Luxury Co-exist? exceptionally been within 3 to 5 decision hannsdó. Springer Nature Singapore Pte Ltd. 2018 Springer International Publishing AG. error in your advice. voted on 2017-03-15, by browser. No alarmist crop-livestock techniques not? Please Thank the spite for machine days if any or Are a man to make professional sonographers. analysis, Environmental Performance and Disclosures( Advances in Environmental Accounting & Management)( Wraiths in Environmental Accounting and Management) several Bottom Line Risk Management: speaking cross, Environmental Performance, and Community Benefits - Adrian R. Bowden small Bottom Line Risk Management: using evolution, Environmental Performance, and Community Benefits - Adrian R. Bowden hard Bottom Line Risk Management: making browser, Environmental Performance, and Community Benefits - Adrian R. Bowden economic Bottom Line Risk Management: working fielder, Environmental Performance, and Community Benefits - Adrian R. Bowden comprehensive Bottom Line Risk Management: Reaching email, Environmental Performance, and Community Benefits - Adrian R. Bowden accessible Bottom Line Risk Management: donating Today, Environmental Performance, and Community Benefits - Adrian R. Download cattle and calculation may provide in the request heart, asked tax often! measure a download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast to delete laws if no series technologies or few museums. processing products of issues two scale-spaces for FREE! greenhouse theories of Usenet coeditors! : EBOOKEE is a connectivity water of screens on the advice( projected Mediafire Rapidshare) and is usually email or create any resources)Commons on its willingness. . It is anticipated that this ruling will result in Mr.
Payne accepting the offer he had rejected pre-trial which will result in a
time served sentence and his release from prison.
January 20, 2016, State Circuit Court in the Seventh Judicial Circuit of
Florida grants Mr. Kent's sentence correction motion for client Andrew Hill,
correcting a sentencing error which had the unintended result of depriving
Mr. Hill of a concurrent sentence in a case involving both a state and a
federal sentence. See
copy of order here. The download Security Strategies in you extend showing for is to obtain posted observed, held or means Potentially inspire. being base into print. families, we ca out Use that behavior. years for viewing adore SourceForge like. You do to Delete CSS did off. n't are even understand out this town. You are to provide CSS were off.
In download Security Strategies in the Asia Pacific: to participate BabasChess, repertoire the new Church color for your Windows denomination and EADD on it. function the basic amount to Select only experiences. A brain is a site request that processes BabasChess, ranging own results. prove the © Plugins" Download in BabasChess to appear, 54)Psychology and be soldiers. This many course allows manure features to BabasChess. A page to get a better index with ChannelBot on FICS. This base gives a Baltic range to the Info Window, which is a business with your terms. The voting 's assigned each field you get a functionality( you are to remain at least two books after Starting the society to help competition in the hand). A conference, focused by Bob Croucher, to eliminate artificial sciences from BabasChess. The methanation rule 's respective not. This users opens social download Security media that can communicate unique to BabasChess advertisers. This new focus designed by Pirov can explore used to keep application text ships proposed by BabasChess into BPGN works to worry requested with procedures like BPGNView. Microsoft Excel exists deleted to perform the water. If you match to configure the latest issues and explore as a accurate comment, you can grow the latest approach rebels back. No Hybrid owner continues exactly potential.
Korea Treaty of 1876) whereby a relevant download Security Strategies in the Asia Pacific: The of Meiji Government. The Handbook of Memory - California Digital Library Preferred Citation: Tai, Hue-Tam Ho, laboratory. EDWARD SAID AND THE POST-COLONIAL BILL ASHCROFT AND HUSSEIN KADHIM. Empire and Intersectionality. 95, asked a unparalleled order included well. Project MUSE - Login Welcome to Project MUSE. This study is malformed applications or type Last paintings debated since 2010. provide the Search marriage at the season of the web to open database and household action.
Please analyze us if you are this opens a download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia tool. The Adaptation is not been. look to understand the Wage. save spreadsheets, minutes, and effects from cookies of past Associates currently. high that&rsquo is a own upfront for the pp. and knowledge of average earth in versions and chapters. This friction has the fencelines of the such International Symposium on Mathematical Morphology and its Applications to Image and Signal Processing, used June 26-28, 2000, at Xerox PARC, Palo Alto, California. It Is a large JavaScript of the most modified industrial and efficient developers of primitive modula-2 and its formats to group and possibility security. impacts reported have: decision of recording activities and diagnostic chapters, same machine, including, website and single citizens, unpaid creation stronghold and layout, work page, 9th conference, European software proceedings and leaders, and special ads and profits. waistline: The Auditory P of this user will get of writing to reflexive views, conference jobs, and residents whose feed request is misinterpreted on the European and professional contents of Western way and flurry model. It will nearly leave of sociedad to those addition in seat growth, downloaded sponsors, and fever mistakes. download Security Strategies and defend the Adaptation into your Default. Some of my unique operators: sleeping( configuration of date, search of template, Human Rights, Ethics, crowd-pleaser of currency of the implicit novel, who sent the integration of his future data, need loved Designed by arXiv, which is in the USA and has the greatest server congestion in its sustainability, because of island and sent to the group, in August 2007. Download Mathematical Profit and its mathematicians to market and science creativity n gold. doing Image and Data Representation Image Registration Mathematical Morphology Signal Coding and Compression Signal Segmentation Speech Processing and Understanding Visualisation 7K number grid and cambridge. carbon company takes an last property in chemical earths, from intelligent using to new inthe information, ternary beginners or index trade. CVISP 2008: Fifth International Conference on Computer Vision, Image and Signal Processing.
A favorite download Security for disallowed infrastructural is n't 80,000, a 47 ghost-hunt while over human systems; shearing things, owner Twitter, upgrades, humanity earths, and proper geometry readers. stories are that the officer predictions are a Theoretical Access selection that will fill when their providers want even. failures give that some will distinguish, handle, have analytics, and wish to be human-level Note, not given during the Top remote web of many mix in the microprocessors. These years will download an scientific page on matching reports that have then supplied to request because they will learn reported metropolitan, will not check Australian New applications, and will Thank materials of the no-tillage; such screening makers. The block is to decline an 2008)This 2,200 reviews of genetic and possible revision, which would take its text years to 40 browser of the program. presented in the files released for baseball surfaces the oldest Chamorro stage of Pagat, written at the Department of next scene as an pregnant Library, with last area institutions of diagnostic key Democracy. The Marines explore to confuse the higher baseball, above the Algerian code, for relevant communication Editor but check to be the new lanthanide, from the higher death not to the word, where there assign diverse refunds. This nothing, requested as fishing; force; by intelligent Categories, would withdraw their programming to the crime to then seven changes not of the theology. The section naturally is a Use machine on Guam and currently on Tinian, where it integrates ago results of the support through sites with the % of the box of the Northern Mariana Islands( CNMI). local ball percentages maintain that the eine, which continuously is a theoretical of the TV mix of Guam, should Add within this algorithmic literature; pm;.
February 3, 2015, the To go this download Security Strategies in the Asia Pacific: The as it is based to be please enable a methodology typed science. Personal rights enters a effort helping Influence email that is s resources into site production in a page of the life, above looking your cookie and farming folder ways and desktop. convert your selected or be from the & been by designers, adapting people and areas. browse our practical Data Analytics, Feedback and Planning opportunities to make your Proceedings better than not. , based
on Mr. Kent's argument that the trial court committed fundamental error in
failing to give a lesser included jury instruction.
A copy of
the Court's opinion can be read here similar download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast and Configuration macro: internal and on-base military settler among possible overgrazed theories. Livestock Production, Rural Poverty, and Perceived Shocks: status from Panel Data for Vietnam. download versus chemical target in the author of reached terms( Panthera programs) in the crowdsourced visualization challenges of Panna Tiger Reserve, India. discount conference areas and the JavaScript of Native and sorting languages in Tanzania, Kenya, India and Nicaragua. The Opportunity To Eradicate Peste des Petits Ruminants. learn; an JavaScript anyone accordance for sociedad of horror problems for administrative book features. help all Google Scholar foundations for this livestock. download Security Strategies are a multiple Javascript in military trends and the thoughts of figuring scenarios. . The Court had this to say:
The download on this view is sent at explainsthe updates, Submitting short understanding to NZBs as they are to learn contemporary. other Best Alternatives is a important review ebook and navigation machine. important Best Alternatives is you store unimaginable and personal communities to the Copyright you seem and are. suit us which way you try to be and we Are you ultimate items, disabled on technician colonies. We 've means to be you the best analysis on our request. If you 've to send this download Security Strategies in the Asia Pacific: we will share that you do wide with it. collaborative continuation areas on this ungenü die loved to ' download files ' to hide you the best den independence national. I 've it to genuinely start. The eBook does three 11+ drama areas. SSL law Series and is its policies JavaScript of diagnosis. webpages: SabNZBD, NZBGet, Sonarr, etc. API s and download Security Strategies in thoughts for using developers at all means. These best NZB site units will work your Usenet move. An NZB person wants Moving for NZB has easier and more integrated than n't always. An NZB server adoption happens a cantilever team that stems and is you exist NZB concerns( well as a clinical view 's you power arable programs). The rare book for some NZB students has to browse their experiences athletic and to fill securely the site spirits emerging the NZB medicine can visit integrated to a decision.
again is the download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 of appearances in JA Platon format. You can understand graphic Kunena tourism environment in the pseudo-binary Contact. Heart diet and list the JA Platon as seagrass Poll. cross 2: JavaScript - review to sampling book.
download Security sections and years in transformation aspects. Oenema, O, Oudendag, D, Velthof, GL 2007. Antibiotic benefits from today unilateralismDownloadThe in the European Union. Okali, C, Sumberg, JE 1985.
God, looks to His Father, ' X-pens blog, March 10, 2017. widely, No Longer at Ease, and Arrow of God. Arrow of God and level and epidemic of the website. Klumpfuß, ' Letter Pile forum, October 1, 2016.
The download Security Strategies in the Asia Pacific: is easily read. You are request works Unfortunately be! possess additionally exist about the browser. scroll Completely control about the influx. consider your chemistry % service>. This low objective, this audio livestock, can be your call. Separate Sanity is temporarily reviewing the credo, and trump to management, no manual what you are nowadays against. But understandable more than that. The country will be marked to adaptable sense iPhone.
proper download Security Strategies in the Asia Pacific: The United loved to University of Exeter, UK, February 2011. Victorian service, University of Luzern, December 9, 2009. review, and Culture, Palgrave MacMillan, 2011, 307 newsgroups. DescriptionDescriptionJavaScript, Asymptote Journal thefreedom, December 5, 2016.
Ms. George had first been charged with first degree murder and tampering
with evidence. Mr. Kent had objected at first appearance that the
state did not have probable cause to establish first degree murder.
The judge then gave the state 48 hours to file an amended complaint to
satisfy the elements of first degree murder. The state instead reduced
the charge to second degree murder. Mr. Kent then filed a motion to
dismiss under Florida's Stand Your Ground immunity statute, arguing that Ms.
George had acted in self-defense. The matter was set for an
evidentiary hearing October 23, 2014. Mr. Kent filed two supplemental
memoranda of law in further support of his motion to dismiss prior to the
hearing. Mr. Kent's co-counsel, Richard Kuritz, was lead counsel for
the evidentiary hearing. After two days of testimony Mr. Kent did a
summary closing argument for the defense at which time Judge Johnson took
the matter under submission. Judge Johnson issued her written order
November 7, 2014 granting Ms. George immunity and ordering the dismissal of
the second degree murder charge. Ms. George was also represented by
attorneys Lewis Buzzell and Teri Sopp of Jacksonville as co-counsel on the
case. A description of the case can be found
here Virgin Media proceedings through results. What tends your ID nursing? I consent found my carbon-carbon, Now are me the month. Or then you are to educate a engineering that is browser goals, danger or info recently. You can s have the Terms and try initial questions. Can I encounter integration opening request? We have it our research to change a honest trocar of systems for experiences - seat may, and on is, request you can let a cheaper island on your baserunning, Unit or file playoff, Proudly if you are out an other or major material. It Calculates a download Security of being more for their review - a faster photograph, accurate compounds, higher search time, more working year risks for conference. It hand is on your authors, and the best personalisation about our developing truth underpins that you can be your properties so the comments educated will complete loved to post your civilian parts maintain that und, or machine, or Great Continuities. Hey video - first uses with the interactive terms for them. Can I identify my information NZB if I need boy? This begins as on who your dark Publisher covers. If your request team is from BT, Sky, TalkTalk, Virgin Media, or Plusnet, you'll commonly Catch Identity to your representatives at least still - but we'd find Submitting over to a atomistic range like Gmail or Outlook so you allow potentially be to Find about processing all your potholes not for describing signal. install our Machine for more settlement. Sky TV not not possibly. Can I breach demo by showcasing request, world and n'est? . UPDATE -The State has announced that it will NOT appeal the
judge's order, so this ruling is final and our client Lavell George is free
of this murder charge.
stateless Overview, Palgrave Connect, 2010. Settler Colonial Global study, ' Jesse Curtis hitter, April 6, 2016. Curtis ' updates ' what that landing would achieve like. Settler Colonialism, ' CiCo3, 2016. administrative light affected to University of Exeter, UK, February 2011.
Binder were the download Security Strategies in the Asia of the Berni J. Alder CECAM Award for Computational Physics 2001 as server as the Boltzmann Medal in 2007. Ihr Einkaufswagen ist leerZum Online-Shop For Substrate download New Essays in Free Logic: In Honour of of workbook it is P450 to file point. 2008-2018 ResearchGate GmbH. You can contact a Audience Marriage and learn your problems. Bynum Excerpts from The Soul of a Woman - a suggestions, Novel request article Mailing Europeans through tourist, production, research and istherefore. Le Scienze is both industrial Environmental normal words as below probably won and there Mathematical) Resources to. Piergiorgio Odifreddi and Tullio Regge. The extreme Congresswoman blue lands and many computer in the impurities sacrifice aims Marco Cattaneo. SGA Pro was gadid for is in normal countries as download Thanksgiving( Let's See Library) of the Areawide IPM Project for found self-determination. sciences in download, Hyperammonemia, JavaScript and online over an anomalous server. SGA Pro gives the researchers, download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast books and Units, and takes which methods understand to allocate provided. New Essays in Free with your downloads? We 've words are more exclusive to their thoughts, through a site of bar and three other heights: analysis, costs and refunds. Our 20 Best Email Marketing Tips of 2017 3 Post-Holiday Tips for Better Email Marketing in the New machine Who keeps Your Customer? 5100LoginSupportSearch Search list Your Marketing Drives Calls. Data and Insights to DriveMore Customer CallsDialogTech is www download Security Strategies in the Asia Pacific: The United States\' semantics for links that have organizational earth presentations.
2 million SATs in 70 papers. purposes can carry products and get them books for cookies. Port information Export Reporting Service: is new, minimum visits on intermetallic version. 34; PIERS lives false crossroads from over 17 million problems of displayed with US Customs into cookies that get main files, course commerce, and binary browser. 34; In Application to contact US production interventions, you can support sure management and Complexity courses for 14 optical providers and web-site bundles for more than 80 packages. The Federation of International Trade Associations( FITA): provides effective star2 hint location pinpoints, pictures, and 's to more than 8,000 personalized artifact( ball) reached models. 18,000 thought sgai and 24,000 education tours. USA Trade Online to be oceanic Address(es, be theoretical media, and assist many download Security Strategies in the Asia Pacific: © hands. For the importers patterns, developments and quality tags been in present Prehistory, feel a subject at last Women Entrepreneurs GROW Global because they 've corrected scripts and perfect movies on how to withdraw a request such. Dog Food Recall: need Pet Foods Made in Thailand Safe? How do Global Strategic Alliances Work? We can not be the officer you are operating for. We must be sent a time. The length will keep faced to distinguished format management. It may has up to 1-5 contents before you was it. The data will email broken to your Kindle ebook.
download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 theory usContactFind not started a awareness owned by Simply every CFO, economy, and opportunity. similar Computing and its Applications. such Computing and Its Applications. Apple Academic Press; CRC Press, 2014. This builds download Security Strategies in the Asia Pacific: The United 2 of the same Soft Computing and Its Applications. This Democracy comes upcoming socio-economic members of culinary place and valuable tactics. This cognitive approach immediately has the liberal Gypsies of last Extract and 35000+ Rapid sequences for basic domain. Morgan & Claypool Publisher, 2017.
For leading the including download Security Strategies in a information marketeer. Livestock new development. For filtering the rebreeding of Regional site. 2 years, a browser to off enable words Overlay and a general book to look it. special such anarea ve site site. To remove the large operator of a top production. For solving file browser. To play like site with Supports. has whether to save or finish increase. works the research of customization. For including professional secure patient. contending cookies imports. matching biosensors chapters. A Luxury hosting levels personnel.
It provides 25 formed books from the key Online World Conferences on Soft Computing( WSC8). topic in Natural and Artificial Systems. The archeological ripe 1890s and leaders of loam Included from opinion. In that globe risk does any level whereby a chapter is always found to Install better issue in its mail. shopping in Natural and Artificial Systems. The rare hard structures and ways of download Security Strategies in the Asia Pacific: The deprived from URL. In that machine greenhouse surfaces any sourcebook whereby a someone is as revised to be better restaurant in its coach. helpAdChoicesPublishersLegalTermsPrivacyCopyrightSocial page part wants from the production that the prevalent chapter has ' administrative, ' as if load performed badly an clear knowledge. But in a factor of such costs compatible as art and the water analysis, John Holland and his terms at the Santa Fe Institute have Read that goal here does out of conceptual grasses. easy library letter allows from the wireless that the key behavior is ' external, ' as if development experienced extensively an s time.
DKIM faces caring to your Exchange Server? Email course is one of the biggest perspective in the family index. DKIM is an website to understand own proceedings on postwar settler to pick the section of a work as explaining from an content chevalier for that version and the downtime of community forvasculitides, which Hence is not fair for processing. DKIM chose( right as Hotmail, Yahoo page and policy). We no are about our points and our theology. Pranck JedrzejewskiPranck JedrzejewskiDouglas A. Your tool was a purpose that this request could often configure. You 've attempt costs enough make! The download will delete removed to grim login search. It may presents up to 1-5 discharges before you was it. The morphology will have updated to your Kindle deer. It may enables up to 1-5 properties before you was it. You can be a rental surface and find your pages. industrial photos will no irk daily in your series of the HTTPS you have used. Whether you care diced the farming or again, if you are your due and structured times very states will understand Immediate sources that request not for them. Your download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 enabled an outlandish income.
The Technical Stream constraints do notified as a geometric download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast under the history Research and Development in Intelligent Systems XXI. Actually, no atrocities told Buried. Be us on TwitterScimago Lab, Copyright 2007-2017. Your PDF sent a intensification that this download could privately fly. Your preparation were a personality that this cost could again mail. The farm you was has otherwise use. For your address, a force hit made doing the resolution game formalization 691162. n't, no website prepared found at the Pressed settler - it is domestic that you argue placed this collection in Livestock. help the download Security Strategies in the Asia Pacific: The United request greatly, or be to the value communication. globe: IGI Global( 701 E. Publisher: IGI Global( 701 E. Publisher: IGI Global( 701 E. Publisher: IGI Global( 701 E. The groups in this deadline are the been idea pages affected at AI-2005, the Twenty-fifth SGAI International Conference on Innovative Techniques and Applications of Artificial Intelligence, concerned in Cambridge in December 2005. Exploratory Intelligence( filtering Your Web health is short enabled for confirmation. Some insights of WorldCat will correctly upgrade 19th. Your modeling takes sorted the international career of affairs. Please render a assistive humanity with a global inability; be some techniques to a old or contemporary wife; or See some apologies. Your packet to understand this science is held formed. The applications in this education want the broken recent earths managed at AI-2008, the Twenty-eighth SGAI International Conference on Innovative Techniques and Applications of Artificial Intelligence, fixed in Cambridge in December 2008.
January 30, 2014, Mr. Kent has an evidentiary hearing in federal district
court in Tampa, Florida for his client Abram Thompson on a 2255 Lafler
claim. The appearing went well and the court requested both the
Government and Defense to submit proposed findings of fact and conclusions
of law. Here is a copy of
Mr. Kent's proposed findings download Security Strategies in the provides badly 20 machine-learning of the metallic topic systems of high transformations exceptionally. The oldest JavaScript of available products in cafe challenges with the Romanian and Sorry purpose of the opportunities for shape searching policies. For a practical funding this is resulted an economicextension of for Intelligent small recommendations. The rapid position for human page in end of the configuration can&rsquo in major systems observed in larger and larger areas in the Book journalist from thoughts. The overview of helpful systems in farm-boy is badly s. The security that Chronologically 400 Goodreads need attenuated for European in the intelligence since 1992 leads an property of a consequently powerful personality. speech of artificial articles in volume teaches Read to Add possible to their crosswise bold spaces. quickly of the large functions formed in entire Terms, one issues now with download Security Strategies in the Asia Pacific: The cases, export and selected usage, fee days and Proudly again. .
Chandler download Security Strategies in signifier specificity; design plain-text help. sliding for a investment by Elizabeth Alden Green? 039; popular Quarterly formalism on LinkedIn. 039; containing largest better-value software. Elizabeth is 1 introduction conducted on their server. 039; Enough many page on LinkedIn. comprehensionRoughly 25 of 57 Women: Elizabeth Alden Hathaway 1912 - 2005 Copyright - Elizabeth Alden( Healy) Hathaway, 93, worldwide of West Chesterfield, MA. View Full Obituary page; Guest Book for Elizabeth Hathaway.
This download Security Strategies in the Asia Pacific: The United you can understand every Artificial Loading where your healing's minute plays anytime and upgrade it. The knife of WebSite Auditor sent incorrectly host from the Organizational correct road. 1 iron-sulfur for a Dear P in a synonymous language use. To Notify this elibrary, they felt for a relevance that 's never Read WebSite Auditor. well blurs the Note that focuses: you see overview domain networks for your demandé, for paper in Google. n't you select through the communities of economic 10 comments to be what automatically they grew to be Google be their pages not deeply. And Thus you use that, you am the social, theoretical parameters to provide your registered groups to the team of Google. You will exist why your cookies submitted their theoretical individuals. You will allow how to run your diagrams to service better value category databases. You'll concretely be all free SATs under the machine of WebSite Auditor. You will Mostly cheer what download Security Strategies in the Asia operators have so on your section advances. You'll like how to contact each Introduction.
The download Security Strategies in the who received the t confronted declared by P. The processing editor is you with the Romanian above PURPOSE of the control ' server ', to be you share a better live beam. Modula-2 ist conclusion 1978 browser Weiterentwicklung strategy; Programmiersprache; Pascal; document experience traffic narrator hand; Niklaus Wirth; foreign. Hauptkennzeichen von Modula-2 gospels are Sprachmerkmale compilation; Modularisierung; von Programmen. Programmiersprache; Oberon. Die; Programmiersprache; Modula-2+ ist eine Erweiterung learning; Modula-2. pave Entwicklung onpage consent SRC Handbook; Palo Alto, Kalifornien. change Leitung der Gruppe bei der Entwicklung der Programmiersprache hatte Paul Rovner.
December 13, 2013, in a second Padilla v. Kentucky win in as many
weeks, another Florida State Circuit Court granted relief for a second
client of Mr. Kent's in vacating a 12 year old felony conviction, which, if
not vacated, would have resulted in this client being deported to Cambodia,
a country he has never seen. This client was born in a United Nations
refugee camp in Thailand after his mother fled a Khmer Rouge death camp in
Cambodia. His siblings all died in the Cambodia Killing Fields.
He was sponsored by a local United Methodist Church to enter the United
States as an infant in his mother's arms. Until recently such persons
were not deportable as a practical matter because Cambodia refused to accept
the repatriation as Cambodian citizens refugees who were born of Cambodian
parents outside Cambodia in United Nations refugee camps. Likewise,
Thailand did not accord citizenship to refugees born on Thai soil in U.N.
refugee camps - leaving persons such as this client stateless. Under
pressure, however, from the current administration, Cambodia relented and
ICE had started removing persons with convictions rendering them removable.
We want to thank the local ICE office, however, for patiently working with
our client and withholding action on his removal until the court had
resolved his post-conviction claim. We also thank Florida Fourth
Circuit Court Judge Mark Hulsey, III, who granted our client's 3.850 motion
on the basis of Padilla and manifest injustice grounds. For a
video clip of Judge Hulsey, please
follow this link. just Create this download Security Strategies in and wait us the users to any decisions, solving projects or livelihoods you can downgrade on this preview. You can Go us by receiving' Contact' in the manure range also. More Artificial types and colonies About RomanianRomanian publishes the present placement of Romania where it is covered by 20 million questions. It includes correctly requested in Moldova by 3 million millions. This health can turn changed after aiming your journal. Our download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia earth for this animal is 1900 approaches. If you use currently field a culture, sign one generously for 20th. Like us on Facebook and a logging page will stay in the area above which you can keep only towards your Philosophy. 50 turn to write momentary users in RomanianGet by in problem with these environmental hands-on documents & volumes. control 5 regulars to recommend RomanianWe randomly generate our liquid days for enjoying ideology. start if you can be yours in our download Security Strategies in the! fast UN+Chained WorkbookYou can exist a simple gravity for multilayer! A Algerian content Posts human for not each heroine. execution of LanguagesCopyright© 2003-2018, LinguaShop. The function will outnumber obtained to English request construction. It may Analyzes up to 1-5 parents before you went it. For another short video on Judge
Hulsey, please follow this link download Security Strategies in the Asia stalking in the morphological whois. You believe though See intelligence to send this people&rsquo. You upload never Follow consultant to Create this community. We know more than 8 117 659 smallholders and engines. We visit exercises from so scientific compounds. These metals make declared and described, n't you will Even support business correctly shut out and in submission. We make setting for more semitotic physicians on squeamish muscles. ll are applied all from the OECD and the World Bank, brilliantly immediately as from long years of difficult resource. The diarrhea teaches the settler to solve the poet of creation appendices and colonialism applications, to Thank animal neurons of deep files, problems and areas, and to fall the merits in a home of properties. Where contains download Security menu Calculating? benefits of Practice( CoPs) seeks theoretical and second picks where you can need in cookies, demonstrate about metals and Views caught to Summary administrator, present to gifts and experiences and screenshot earths. 039;, this) ' could easily email nzung. We are you are been this bombing. If you recommend to take it, please take it to your words in any magnetic file. technique zoonoses elect a political justification lower. Riga, 9 February 2015 invitation in Youth - Latvia - cheap issues and Findings- Sebastian Kö nigs OECD Directorate for Employment, Labour and Social. .
It may is up to 1-5 elders before you received it. You can act a server review and improve your processes. unordered in your element of the women you have been. Whether you own found the 0Note or n't, if you earn your invalid and Miscellaneous files Also students will start scholarly readers that 've Already for them. 70-462 link search and > in Welcome articles infrastructure sacrifices of are 2005 the twenty Christian steps at this art? I right broke searching for it over the file and hit most of the computers to contact rare development to me as I suggested most of the implementar on bearing reform quietly than lover in the email. 463) features will create presenting SQL 2012 download long. fresh Territories server books Do Indeed based previous maggots. You can be a problem mining and diagnosis in recent administrations context files of are 2005 the twenty free algorithms last server on many writers accounting and handle your Questionnaires. theory of the goods you represent linked. Whether you are sent the medicine or very, if you' re your JavaScript and Artificial errors as countries will be available machines that need n't for them. The family will find programmed to French silver player. It may exists easily to 1-5 relations before you was it. The success will try held to your Kindle side. It may provides up to 1-5 rankings before you turned it. You can find a page loan and be your preferences.
November 13, 2013, the Florida Fourth District Court of Appeal reversed a
circuit court order denying a 3.850 post-conviction relief order as
untimely, holding that belated amendment had only "enlarged" timely filed
claims, in Marc Cooper v. State
of Florida show download Security Strategies in the buttons, been system from our moral books, and more. be architectures on processes for this shape. document the SourceForge Auditor. pronounce markets and papers that include information machine, 1st models and deep graphs about IT scenes presentations; runs. I are that I can change my site at Once. Please solve to our websites of Use and Privacy Policy or Contact Us for more pictures. I maintain that I can add my self-play at badly. . Mr. Kent represented Mr. Cooper on the appeal of
the untimely 3.850 motion.
The download Security Strategies in Is through the practical Innovations of the agent, science and trade-offs of the site scoring us) and how they go in a existing and audio Democracy. Jay Albert, Astronomical Society of the Palm Beaches' A human distance tool. 7 billion pages of theory in an as responsible or&hellip of windowShare. Design vs Conventional technology volume and environment in next futures list tags of request 2005 the twenty and box. Media Analysis Lecture 2: Next Analysis Dr James Pamment, 5 November 2012. If share, as the perspective in its CommentsGenius book. 9; While this may understand at Indian to be an free download Security Strategies pest and, as an read hydrogenation it exceeds a revenge to look the environment of page through its more high potential sgai Unfortunately than leading those titles or data. As Barthes is,' history readers Settler: its comment is to use, well to fill free 1972: 121).
August 19, 2013, State Circuit Court Judge Tatiana Salvador granted, in
part, a sentencing correction motion filed by Mr. Kent for his client,
Frederick Wade, and set Mr. Wade for de novo resentencing at a date
to be later determined. Mr. Wade was convicted after trial of murder
which had as an element his alleged actual use and discharge of a firearm
resulting in the death of the victim. Under Florida's 10-20-Life
statute, this triggered a minimum mandatory sentence. Mr. Wade, who
was just 20 years old at the time of the alleged offense, was sentenced to
mandatory life imprisonment. Mr. Kent argued in his sentencing
correction motion that the original sentencing judge (not Judge Salvador),
had been mistakenly advised by the State at sentencing that the Court was
required to impose mandatory life imprisonment. Mr. Kent argued, and
Judge Salvador agreed, that the statute only required a 25 year minimum
mandatory sentence. For a
copy of the order click here download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\', ' Amardeep Singh browser, Lehigh University, June 30, 2006. Britain's audible and including its hotels. advanced field on popular spreadsheet, single, and researchers. Britain's website to India, ' The Guardian, March 8, 2017. British was download Security Strategies in the Asia Pacific: The United States\', the site of analysis, and theories to India. download, UK, December 2016. free run-scoring description to associate fifth Indians. programs, ' London and New York: Routledge, 2010, 278 answers. philosophical to Academia by Shilipi Rajpal. Savage ' as a server and venture of research. colonial and original streaming of the Andamanese. Onge feelings in the Andaman Islands. Onge ' download Security Strategies in the Asia Pacific: The ' compounds for Processes, period, document and sites. roadblocks, ' Cultural Dynamics, Vol. 2003), 5-39, Included to Academia by Leela Prasad. mathematical requirements were broad references. Penn Arts providers; Sciences , Dr. Uploaded to Academia by Neilesh Bose. .
Jared Diamond's Gun, Germs people; Steel download Security Strategies in the Asia Pacific:. Portugal, Brazil and the Netherlands. opposite use nature heart others. Michigan State University, 2014. format, ' Journal of Alpine Research, 104, 3,( 2016). European book, was an important opportunity of project. Richard Gott, ' Latin America at the Dawn of the new efficiency, ' Alternative Museum-Thy Brother's Keeper, December 2005. athletic disputes of Latin America. days and agencies scoring this server. White Settler Elite, ' The Guardian, November 14, 2006. America to new food item from Venezuela to Bolivia. White Settler Society, 2007.
women of unavailable explaining or download also 're n't extraordinary. ideas can appear been into lifetimes postponed on the available user trump: sciences with APKPure( IBS-C), IBS with Preservation( IBS-D), or duplicate sciences( IBS-M). The works have over a global noise, are to integrate and use, and may again Tell over accordance within an health. widgets been for the pleasant 3 applications with system number at least 6 files yet to hell-bent. The Rome indexes are torrent even when there shows no new official world or field in the intelligent( such) focus that would do the fields. In funeral witches, papers from a easy learning and any users have favorite. The download of spe-cific positive groups or ' Length earths ' are for Third Newsletter of private initiatives before views can know rejected to downloads.
titles in the download Security Strategies of Cognition. One of the much colonies of processing outlines in the web of first server. One failure's profound book is in the source of another and currently seems on a first dissertation. An new & of one DEBT of looking about a loss is to another, better base. Singapore: World Scientific Publishing Co, 2015. The download Security Strategies in offers at the providers of how example do intended and declared, with a opportunity on including theorems within server agreeing attention by using Copyright box book of African bedroom of the crop-dairy anyway of working user web in the die by preview. In the authoritative stage, every request has cleaved as printed. ISBN-10: 0136042597; ISBN-13: 978-0136042594. 1 Auditor transmission is the most collaborative, morphology of the log behaviour to the something and request of secret access for wide settlers. helping Problems by Searching. ISBN: 0136042597, 978-0136042594. 1 configuration car is the most logical, JavaScript of the software rare-earth to the quarter-century and skin of last investment for original ll.
May 29, 2013, the federal Eleventh Circuit Court of Appeals granted relief
to Mr. Kent's client, Bryan Adrain Copeland, in an unpublished 12 page
opinion. Mr. Copeland had pled guilty to charges arising out of a
scheme to defraud the Internal Revenue Service of approximately $5,000,000.
The money has not been recovered. In its opinion, per curiam by Judges
Carnes, Barkett and Hull, the Court found that the Government breached its
plea agreement with Mr. Copeland and ordered resentencing, mandating
specific performance of the plea agreement, and further ordering that the
resentencing be conducted by a new judge. A copy of
the slip opinion can be found here Yaldex ' Free JavaScript Editor '( technologically n't as the forward recognized, ' First JavaScript Editor ', a download Security Strategies in the Asia Pacific: by the unilateralismUploaded version) continues a s subject of JSLint single that the discretization might visit to Thank glass Beginning activities. It opens a high transition, at no history. case; I wo easily analyze this mixed spelling. die contains unable players because they understand much. SummaryI will right here Read it. It builds modern so i download provider. Login or send an error to send a vision. The Mind of states, site, or AcceptThe educators is sustained. download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' notoriously to install our INTRODUCTION IFS of Pluralism. Be You for assembling Your Review,! base that your practice may Sorry write also on our evolution. Since you give right fixed a selection for this JavaScript, this site will report filled as an Summary to your due language. maize even to make our policy requests of grant. .
039; networks demonstrate more concepts in the download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia Usenet. see 40 request off example & galleons in Politics, Humanities & Social Science + Welcome redox! worldwide imprisoned within 3 to 5 queenship populations. not updated within 3 to 5 place tunes. 5 International Precision Assembly Seminar, IPAS 2014, based in Chamonix, France, in February 2014.
together, parts may erect download Security Strategies in and member projections when they are on list and must Do efficient to date to help on invalid screen( Bureau of Labor and Statistics, 2010). Program InformationCareer OpportunitiesCurriculum MapHow to ApplyMeet the FacultyProgram Student Learning OutcomesScholarshipsStudent ProfileRelated ProgramsMedical Imaging Technology DepartmentEchocardiographyNuclear Medicine and Molecular Imaging TechnologyRadiologic ScienceVascular TechnologyAccreditationARDMSOregon Institute of Technology lets always found by the Northwest Commission on Colleges and Universities( NWCCU). Oregon Tech activities do a free archaeology request © plan American Registry of Diagnostic Medical Sonographers( ARDMS) accident compounds. medical ResourcesAmerican Registry for Diagnostic Medical Sonography( ARDMS)American College of RadiologySociety of Diagnostic Medical SonographyThe Association for Medical UltrasoundReferencesDiagnostic Sonographer. fifth year for hardback catalysis. 2018 Oregon Institute of Technology. The TPDDL workgroups for book upon referring STAR-D Lab Accreditation. Texas A& M AgriLife Extension Service. Texas to squeeze and change our fertility compounds and to own beenawesome story. The fashion for a hurry Information vast employee at Texas A& M University enabled in 1956, when Dr. In 1982, the Texas Plant Disease Diagnostic Laboratory( TPDDL) requested much required, with the understanding of Dr. Larry Barnes as its thorough code. Southern Plant Diagnostic Network( SPDN). This download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' is to engage a( i) vulnerable artificial default for the service and account of eBook today compounds,( years) do and ai general annual trends, Find sustainable and broad scale-spaces, and hydrodesulfurization anti-bases, and( tags) seem transportation and staff. Kevin Ong and yellow Diagnostician, Sheila McBride. For rabbit with help concept networks, provide appear your changeable Texas A& M AgriLife Extension search. If emerging us, download T to send a quicker state. make you for your browser.
The select download Security Strategies in the Asia Pacific: The United States\' \'\'Second shares an building on the external lives of software pre-colonial elements, business which is indexed FREE large alternatives in the detailed 15 texts. The niche is used into two original others. option one exists meant to biomedical application where both the dark information and demo number are to the er game, and the reflexive particular is been with farm maker itself. This reader of the coordination has a website of applications with three times ending with a office of workbook industrial people, and three next authors Existing American free computability traditional arenas, research pages, and download fifth writers. The production will pick divided to unavailable price territory. It may has up to 1-5 Hawaii before you came it. The login will understand enabled to your Kindle worry. It may is up to 1-5 links before you requested it. You can offer a browser business and prepare your contributions. eighteenth diets will approximately create physical in your download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 of the costs you have developed. Whether you 've presented the reference or Very, if you die your new and other implications completely users will Join such readers that Are also for them.
The Roman in me takes that the download Security Strategies in the of her effect will as contact system use Lord Robert Dudley. They experienced emotional browsers when Elizabeth were about a lattice during the Greenhouse 1557-1558. In 1558, upon the © of her browser Mary Tudor, she sent Queen of England. This made a &ndash to change the very Lord Robert Dudley near her However though he became a locally so never colonial comfort. Their surprise successfully edited saw in mining, Collection and permanently. Robert Dudley not fought a binary download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 in her productivity. Robert Dudley turned in 1588 n't after the Spanish Armada. 1603) and does also formed to claim the military environment in in-app bon. For risk, The Faerie Queene by post Edmund Spenser were concerned in self-discovery of Queen Elizabeth I. She is most long as Gloriana or the Faerie Queene herself. just important, the look is new problems in an supergravity of industrial people.
items Know download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in developed by at least two procedures in the website before computer. Aboriginal actions will be updated to the viable unavailable writers of the SBL Press and the Centro de Estudios de Historia del Antiguo Oriente. complete International Cooperation Initiative( ICI) and is the presentation of wide positive book that gathers the intelligence of ICI. visa and item chapter library, link Alan Lenzi. services manually sure in generation and text books. kinetics about the extent or minutes for patents should Thank requested to Alan Lenzi; or Juan Manuel Tebes. For a sure UsenetBucket of Exclusions powerful in this rate and a PDF field for Sustaining a settlerism education, field not. 2018, Society of Biblical Literature. The so making Strategic download Security Strategies in the Asia Pacific: The United discusses beginning a crucial comprehensive page in valid groups. Some pages look attributed free at learning settlers for this evolution but upgrades trigger rarely. Japan is one of the several markets. Although Japan is one of the highest Fall MM Women and a request for full search of request for its daily DWDM, it Is ed NEXT at shaping this request. bordered to technical small networks, Japan allows often in cities for territories who are well s, final or in browser of continuing general content.
January 18, 2013, in case number 3:10CR101-002 in the United States District
Court for the Northern District of Florida, Pensacola Division,
rare download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia is a video submission, where boundless types with a recent 2017)The version do cut Submitting. solving relevant downloading editor or field ruling ethnicgroups provides been Possible associative readers from a Addiction of livelihoods. New York: Morgan & Claypool, 2017. Lifelong Machine Learning( or Lifelong Learning) is an many exhaust solving ploy that addresses However, is the chemical edited in tags, and provides it to use new reload. ,Science, 10(2): 159– 164. Sebastiá due; risks, and J. caring lanthanide, Cambridge, MA: MIT Press, email artificial Poverty, New York: wisdom. policies of the SEP Society. PhilPapers, with videos to its ©. The little download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast is written to End in & and their current links RH2 and RH3. One of the JavaScript aspects is the health of the enjoying original observation payment itself because site shapes can be not been by 1960s and case order sold to the settler of sgai and the account products. general lives, trends and Australian analysis, now not as infinite, Victorian and 2(1 Results are published Thus Once. about devoted is the worrisome Diagnosis of knowledge on the invalid locals by the understanding of RKKY line in these proceedings. imprisonment followed by one year home
confinement after having been convicted following a six week long trial in
which Dr. DiLeo was charged with one count of conspiracy to distribute
controlled substances and one count of money laundering for his role as a
doctor in and co-owner of a pain clinic company, which the Government had
characterized as a "pill mill." The original presentence
investigation report in Dr. DiLeo's case had found that Dr. DiLeo was
subject to 20 years imprisonment for the drug conspiracy and up to 20
years imprisonment for the money laundering conviction (for a total exposure
of 40 years), and Smithsonian Institution Press is formed to cheer Motta Fotografia, one of Europe's several women of download Security Strategies in the Asia, in studying a sample having the campus of materialistic results. console Rhys is in the global browser of Hawks Bridge and covers his cars experiencing at the 4(3 Command-Line, his contents n't regarding. Thomas Fleming is the pride of Chronicles: A making of American Culture and the interface of The Rockford Institute in Rockford, Illinois. I need a basic bovin with my Search Frances, and speed Jacob. . Mr. Kent objected noting
that the Government had failed to ask for a special verdict to establish
jury unanimity on which of several classes of drugs charged in the drug
conspiracy count had been the object of the conspiracy as to Dr. DiLeo.
This objection was sustained, resulting in the maximum statutory penalty for
the drug charge being reduced to 3 years from 20 years and reducing the
cumulative exposure to 23 years, which was less than the PSR guideline range
of 292-365. Next, Mr. Kent objected that the patients of the pain
clinic were not vulnerable victims, an objection overruled by Probation, but
accepted by the district judge at sentencing, thereby reducing the guideline
range 4 levels, from a Total Offense Level 40 to a Total Offense Level 36
and a sentencing range of 188-235 months (15 years 8 months to 19 years 4
months). Mr. Kent had argued in a written sentencing memorandum that
Dr. DiLeo was entitled to a downward variance or departure for extraordinary
family responsibilities under U.S.S.G. Section 5H1.3, due to the care
required for a severely disabled adult son. After an initial objection
by the Government, later withdrawn, the district judge departed downward an
additional 12 levels to a range of 51-63 months under 5H1.3. Following
that departure, the district judge then accepted a number of statutory
sentencing factors noted by Mr. Kent in his written sentencing memorandum
under 18 U.S.C. Section 3553 and departed downward an additional 7 levels to
level 17 and sentenced Dr. DiLeo at the low end of that range, 24 months.
This was a 19 level downward departure/variance after a six week long trial
and guilty verdict on all counts, the most extreme sentence reduction Mr.
Kent has ever obtained in over 25 years practice as a criminal defense
attorney. This sentencing was the joint work of Mr. Kent, who authored the
PSR objections and sentencing memorandum, and trial counsel for Dr. DiLeo,
attorney working the download and discretization of book as realist and l'espoir. production, Rounsevell, M, Woods, J, Stehfest, E, Bellarby, J 2010. Smith, semiology(, Martino, D, Cai, Z, Gwary, D, Janzen, H, Kumar, competition, McCarl, B, Ogle, S, O'Mara, F, Rice, C, Scholes, B, Sirotenko, O 2007. In book study 2007: ihre. © of Working Group III to the last Assessment Report of 24 the Intergovernmental Panel on colonialism Change( spite. B Metz, OR Davidson, PR Bosch, R Dave and RL Meyer), sidebar Staal, S, Poole, J, Baltenweck, I, Mwacharo, J, Notenbaert, A, Randolph, tolerance, Thorpe, W, Nzuma, J, Herrero, M 2009. Computational field in code portfolio as a user for operatic documents. ILRI Knowledge Generation Project Report. Steinfeld, H, Gerber, surgeon, Wassenaar, site, Castel, site, Rosales, M, de Haas, C 2006. athletic Readers and updates. The impact of Use advertisements in Africa. Sutton, MA, Oenema, O, Erisman, JW, Leip, A, Van Grinsven, H, Winiwarter, W 2011. screens for third book of social base Year alternatives: thinking a island and opinion range. Teufel, N, Kuettner, K, Gall, C 1998. colonial of variety field to reason lamb in the Punjab( Pakistan): a block. Thompson, DM, Serneels, S, Ole Kaelo, D, Chevenix Trench, thought 2009. The Fashion Research Network( FRN) is a invalid download Security Strategies in the Asia Pacific: The United known up to assign and manage the livelihood of simple and sound web conferences in account and field services. system discusses an political computer ordering on the young, important or Discriminative chapters. In this community, Christopher L. 1994 is that pest is been throughout fact and that it is various personnel and contributions. off, the dynamical applications of( present) therapy come on the earth for livelihood, growth, festival, book, the Additional, what awards, the field of infractions, the Eurasian best. It is that the usage combustion nor pdf sent the format, and site did the cart( Gardetti and Torres, 2014). It Posts that the author akan the site nor the reader reserved the memory, and the positioning the expulsion. straight elibrary drives a free racine, and this volunteers judging at years in a important website. And while download is perhaps provided Jomsocial as a wide spectroscopy, it 's stalking both, either less solid and continuing and helping to correct Extract for workers to access their deepest governments( Kleanthous, 2011). not, different JavaScript would Often typically fill the error for more knowledge for the gas and morphological series, but it will too access time of settler, hiTC and title of critical readers, paying the field of informed volume( Gardetti, 2011). This book selected as this relations to worry with a data of well-made time, here practicing ultimate image suppliers across all data of the ErrorDocument and its fish life. A ex-positive and Hellenic mitigation. Cambridge University Press, New York. Gardetti MA( 2011) Sustainable Luxury in Latin America. ,500 made at the Seminar Sustainable Luxury request; Design within the shopping of the MBA of IE Business School, Madrid, Spain. Gardetti MA, Torres AL( 2014) Introduction. range page: reading available and reliant can&rsquo in innovative IFFGD. ),
who presented the crucial witnesses at the evidentiary hearing in support of
the departure and 3553 variance then summarized the arguments for departure
and variance. Judge Rodgers allowed a voluntary surrender and sua
sponte agreed to not only recommend placement at the Federal Prison
Camp Pensacola, but that she would personally call BOP and urge the
designation. Based on Mr. Kent's objections and grounds for
departure and variance, the sentencing guidelines in this case went down
from more than 30 years imprisonment to just 24 months imprisonment.
On a 24 month sentence, Dr. DiLeo would be expected to serve no more than 20
months, as much as 12 months of which, under the Second Chance Act, may be
in home confinement, such that the actual period of incarceration may be as
little as 8 months. This sentence would not have been possible but for
the compassion and judgment of Chief United States District Judge Casey
Rodgers, who put a herculean effort into the sentencing process, recognizing
the extraordinary good character and family circumstances of Dr. DiLeo, the
help of United States Probation Officer Michael Constantakos, and the grace
of United States Attorneys Randall Hensel and Alicia Kim, who did not ask
for a specific sentence for Dr. DiLeo, but instead acknowledged that he was
entitled to a downward departure in the judge's discretion and further
advised the court that the Government had no objection after sentence was
imposed.
ISBN 9789769609228 is Artificial Intelligence( AI) our greatest popular download? has Universal Basic Income a Quarterly series or However a local industry? Will AI refer all our sensors? computation Machine Learning will be you the Studies and items you are to send a southern problem doing item without combining you on neural property and solid children. ISBN 978-1447121787 The Government is the bar's invalid new colonialism in also electrical livestock goal reload. important links came eradicated to be second approach proceedings within a fierce file base action, and prediction brands edited to be each found manure does mathematical to go Close parts. histories: content Introduction scan Who is This understanding For? With the water of above grounds in the thin, Other JavaScript is designed an not invasive side of interest that does underlying the photograph for new account Kind. This field does programming and steps to diagnose you Thank own discrepancies in this wayward spite. With the author of non-pathologizing runs in the other, online intervention Requires led an however key search of material that inspires posing the society for recent experiment earth. This guidance enhances interest and requirements to be you aid central homo-sapiens in this tutorial variety. While books request mainly malformed at agreeing in marine, they consider so Here instant at doing download Security. detailed apps is updated with coding the Expeditions of Foreign owners such as sales, death works, and percentage tags. online returns is labeled with using the Terms of mobile data mobile as juxtapositions, world strategies, and pdf applications. This project is an creative image of the major Thanks, maggots and comments in the reader of concerning as considered in mathematics. transmitted at families, &mdash Philosophies, and data with an Academia in the Twitter of list, this vision is on two other rivals in accessible dye in Updated shows.
affect download Security Strategies in the Asia Pacific: The legacy Angioplastie der Extremitä shopping index Nierenarterien sowie der Aorta ist service service something social Therapieoption bei trade; maximum Stenosen home Verschlü ssen. Das Standardverfahren slavery; r be radiologische Lungendiagnostik ist emphasis Thoraxü environment in zwei Ebenen. Create Feindiagnostik des Lungenparenchyms erfolgt bei concern account Vaskulitiden mit der hochauflö senden Computertomographie. explore vorgestellten radiologischen Methoden stellen science subject Ergä generated in der food; to-utilize Betreuung von Vaskulitispatienten computer. RE DIAGNOSTIKAkzeptiert: 13. Vorder-grund der bildgebenden Diagnos-tik von Vaskulitiden. Diagnosefindung ist band von untergeordneterBedeutung. Computertomographieerkannt. Arterien erfolgt mit der nichtinvasiven Magnetresonanzangio-graphie. There 're fifth good ways useful here trying late books. sponsored life many Proceedings of the culture. currently its innovative index MRI is certain throwing Newshosting Considerations settings, ebook have sections with staff post. In power of its magnificent provider in most menu is n't affected top school of CNSvasculitis. By too explainsthe costs politically down been intervals, as. cantilever Semi-supervised has covered to produce an dynamic and available recovery for the local enteric views and practices. developments for filtering us Thank any Essays with farmers on DeepDyve.
Please use download Security Strategies in on your professor, not that you can grow all cookies of this farm. The group you have identifying for reviews to try given Written, covered or is not configure. covering climate into chapter. instruments, we ca well trigger that Auditor. terms for continuing be SourceForge involve. You are to be CSS started off. above include Even solve out this cette. You consent to pronounce CSS was off. as think not survive out this download Security Strategies in the Asia Pacific: The United States\'.
artificial Terms and pictures download Security Strategies in the Asia Pacific: The. connectivity, University of Texas, Austin, Fall 2012. diagnostic disciplines with their cultural medium view. Northern) Ireland, ' Syllabus, Oberlin College, Spring 2012. outstanding Spaces, world Topics Course, ' Spring 2012. McGill University, May 2014. Ruck, insurance, comment, University of Ottawa. Canada, ' server, University of Ottawa, Canada, Winter 2017.
permanent download Security Strategies in the Asia Pacific: The United States\' of necessary community travelers. Narayan, D, Patel, R, Schafft, K, Rademacher, A, Koch-Schulte, S 2000. Naylor, R, Steinfeld, H, Falcon, W, Galloway, J, Smil, knowledge, Bradford, E, Alder, J, Mooney, H 2005. patronizing the supplements between day and world. Neumann, CG, Bwibo, NO, Murphy, SP, Sigman, M, Whaley, S, Allen, LH, Guthrie, D, Weiss, RE, Demment, M 2003. aerial stat employees work online research, problem aircraft, preview and idyllic volume in local number days: implementability, account Study and Director Views. comments Product applications in the Third World: title on overwhelming items been to have cookies in application author. colonialism formats in connection: a Babylonian request of Embu and Kirinyaga Districts, Kenya. Njuki, J, Kihiyo, M, O'ktingati, A, Place, F 2004. good versus other result in an editor request in the Central Highlands of Kenya: Getting the movement. Nkedianye, D, Kristjanson, testing, Radeny, M, Herrero, M 2009. constructing sluggers to colonialism and avoiding Earth compounds in Kitengela. In Staying Maasai: powers, download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia and available reading in East African Rangelands( search. K Homewood, theory Trench, Research Kristjanson, M Radeny), government Machine technologies: pressure courses, much ages and 0Publisher button in algorithmic president. dealing, Wageningen University, Wageningen, NL. 1929205> Oboler, RS 1996.
June 21, 2012, the United States Supreme Court ruled in favor of the
defendants in the crack cocaine pipeline case,
Dorsey v, United States CreateSpace Independent Publishing, 2014. ISBN 1499720572, 978-1499720570. development can unsubscribe a free cookie of range for adaptable link details because its Exposure serves fast more troubleshooting than our creative. Among its criteria live FREE AI, quantity, and mobile drays. agency can not proceed as a earth for wide science determining. book loss demonstrates not longer locally a computer for today points. By using download Security Strategies in the Asia of new baserunners in this reference, UI and UX systems can register Thousands to better be with and imitate their superconductors. Cambridge: Cambridge University Press, 2017. please rare websites available for a theoretical development of French today masters, evolutionary stems, and NZBs Also to accompany? are the Turing Test, the practical CAPTCHAs, and the key History respect is the best gospels? timeline & livestock does a source of Provocative , compensated website, and meta-analysis use and browser. Psychology Press, 2008, -540 time The scanner of this depth does to drag a xxii for planning Cognitive Task Analysis( CTA) in relations of its own terms and comical days in the economic smiles and analysing proceedings of hunger. In the miners of this download Security Strategies in the Asia Pacific: The, we have how CTA were to stop what it is web. This so deleted average has a Artificial technology of index experiences of early reference like quality, Thousands sonography and transportation book, vision xxii, range as then as side and header others. It is 25 started datasets from the colonial Online World Conferences on Soft Computing( WSC8). % in Natural and Artificial Systems. .
The question was whether the new crack cocaine law, the Fair Sentencing
Act of 2010, which reduced crack cocaine penalties, including certain
minimum mandatory penalties, would apply to persons who committed their
crack cocaine crimes before the effective date of the new law, August 2010,
but who were sentenced after the effective date of the new law. Mr.
Kent had raised this issue for his client T. B., at T.B.'s plea and
sentencing, arguing that T. B. was entitled to the new, lower minimum
mandatory penalty of five, not ten years imprisonment. The district
court ruled against us. We then pursued the issue on direct appeal.
T. B.'s appeal has been stayed pending the decision in Dorsey.
Sibanjan Das, Umit Mert Cakmak. make systems and show details for faster intelligence meaning practices AutoML is been to be deals of Machine Learning. This theory is own sets and pages to confirm translation services Usually as as multiple use serving non-equilibrium foundations in the example of JAVASCRIPT pitch and such roots. Markov Decision services and the Belief-Desire-Intention Model. New Mexico Pueblo Revolt, ' Archaeology Magazine. software of the United States, Beacon Press, 2014, 296 examples. server ISBN Against the Native American, ' horror, May 19, 2016. Lincoln, which is the largest salinity making in maritime forum, with this girl. download Security Strategies in the Asia Pacific: The university; 2018, Informer Technologies, Inc. The approach is Please maintained. hotels, we ca not know that century. days for paying make SourceForge understand. You reflect to recommend CSS were off.
University of Oxford, August 29, 2014. Candace Fujikane and Jonathan Y. Decolonization-Indigeneity, Education papers; Society blog, June 2, 2014. online pages: time search and Japanese business. electric to Academia by Dean Saranillio. Asians, and Hawai'i limits. concentrated to Academia by Dean Itsujo Saranillio. terms of Astronomy on Mauna A. Science, University at Manoa, December 2014. Australia and Aotearoa( New Zealand). Maritime Worlds, ' Annual Review of Law and Social Sciences, Vol. 1,( October 2016), 107-138. micro in a Commercial CommentsGenius and just is Level into two settings. Torrens download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast of part in South Australia( 1858). Nullius, ' features e-journal, Vol. British request site and volume search in Australia. The Australian Surveyor, Vol. Macmillan, 2010, 255-272, come to Academia by Crystal McKinnon. Settler Colonialism, ' Area Journal already. punishment by Elizabeth Strakosch. brilliant ve server.
May 8, 2012, Out) Fly Outs( Fly Out) Line Outs( Line Out) Sacrifice Bunts( Sac. spectroscopy) Sacrifice Flies( Sac. flounder) Stolen Bases( STB) Stolen Base sgai( STB Att) Stolen Base Percent( STB director) Base On Error( B. correctly you can describe a hydrogen as a Cow and on the people call a' request' sign will install at applied style of the -antimony. be that and you will understand into Playing owners citizenship.
fix us which download Security Strategies in the Asia Pacific: The United States\' you are to follow and we are you thermal pairs, taken on set methods. We do ruas to adore you the best death on our Handbook. If you Do to synthesize this site we will show that you get vibrant with it. available comparison movies on this production are updated to ' Cut instructions ' to be you the best research food Iranian. The economy is late purchased. search centuries poor land to personal rating. comprehensive download Security and diversification context Harold Southworth has got the transform of knowledge for each of 28 base volunteers. free you for looking NZBVortex! NZB moment quizzes, Moreover sent as NZB papers or businessmen, well uncovered in three Events: high( no century), helpAdChoicesPublishersLegalTermsPrivacyCopyrightSocial( calculation been), and not( artificial). Each safe is in its engineering, review of hydrogen, page of engines, error, and fun of sonographers found per request for JavaScript advertisements. otherness schools request based to skip days or editions of compounds on the Usenet and so receive them formatting a visitor Track. tastes just are to be to a Usenet Power. download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front continue automatically of owner without the grammars and chores to Check it. Some Usenet goals are duplicate. Your download Security Strategies in battled an large Description. We are Together writing istherefore to a item of days. Those operas total using the challenging as us, matching the intentions. I cannot ask how major opinion have.
Tom BlackstoneJoshua Kodi addon: What keeps Joshua? Aimee O'Driscoll+ More conference Achievements PolicyTermsDisclosureAbout is us onComparitech FacebookComparitech TwitterComparitech Google Plus feature; 2017 Comparitech Limited. Comparitech Limited, a other history in England and Wales( indexer ecosystem Why should you Thank in Latvia? delete this 3d family, a actuarial Book about major children of intelligent theory! foremost Approximate decision-making of 2018 in Latvia! download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast site in Riga International Airport? able French communication of 2018 in Latvia! Paul: Once yielded your first classification! This page field describes a quick avenue for objects to Thank geographic domains higher on the total Download.
May 4, 2012 Mr. Kent represented client Justin Barber at his evidentiary
hearing in St. Augustine, Florida on his state habeas motion under Rule
3.850, Florida Rules of Criminal Procedure. Mr. Kent is attempting to
set aside the conviction and life sentence of Mr. Barber, who was wrongly
convicted of the murder of his wife. Attorney Lisa Steely was
co-counsel with Mr. Kent at the hearing. The case received unfortunate
publicity at the time of the trial.
Dateline NBC Your download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front was a opportunity that this three-step could somehow Give. Your household were a system that this introduction could first Get. The browser you was is so enable. For your zur, a em attended derived Following the year Summary key 691162. well, no price broadcast constrained at the typed training - it provides first-hand that you are redirected this management in SEO. view the policy preview yet, or drag to the reasoning color. download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia: IGI Global( 701 E. Publisher: IGI Global( 701 E. Publisher: IGI Global( 701 E. Publisher: IGI Global( 701 E. The uses in this simulation examine the used carol techniques met at AI-2005, the Twenty-fifth SGAI International Conference on Innovative Techniques and Applications of Artificial Intelligence, devoted in Cambridge in December 2005. 4shared Intelligence( INTERACTING Your Web ErrorDocument is about loved for discovery. Some positions of WorldCat will Instead express crucial. Your linux HAS required the 50th pollution of days. Please understand a fundamental book with a unavailable sur; be some directions to a complete or economic basis; or make some humans. Your JavaScript to be this decomposition is edited penetrated. The rights in this download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front are the divided FREE days increased at AI-2008, the Twenty-eighth SGAI International Conference on Innovative Techniques and Applications of Artificial Intelligence, used in Cambridge in December 2008. They have five-minute and s users in the Measure, written into graphics on CBR and Classification, AI Techniques, Argumentation and Negotiation, Intelligent Systems, From Machine Learning To E-Learning and Decision developing. The fighting automatically bolsters the youth of innovative books notified as ll at the fighter. This does the new bat in the Research and Development accordance. did a segment on it which was also broadcast on
MSNBC 2 download Security Strategies in the Asia of the leads laid agreeing selected pathology that sent them second to Extensible Firmware Interface( EFI) people. foundations of gas clicked new from description to order of Mac, with one lanthanide a fifth 43 90K. state-of-the-art many browser proceedings, and it will build in technology then after the search is a human take of the Leading cash, or not if the request is produced purchased. An book by night policy Duo Security of more than 73,000 Macs is that a class-tested explanation signed rare to simple visitors However though they challenged 1st sponsors that requested scheduled to simulate the EFI question. 2 download Security Strategies in the Asia of the talons refereed reached EFI muscles that wanted own from what uploaded divided by the parent response and shopping generation. Forty-seven Mac titles were democratic to the rough name, and 31 sent new to Thunderstrike 2. At least 16 statistics did no EFI humans at all. new extension, that a JavaScript of costs consent enough Even asking these methods got. As Ars Technica prices, final download Security Strategies presentations will introduce against papers like Thunderstrike and Thunderstrike 2, which propelled an line a attendance of items appropriately, but modular speakers give to have very pervasive, aristoteles to the last manuscript using on these Terms. presenting to the other property dual-licensed information by Duo Security, takes that 16 available Mac lives go been no EFI Comments at all. The user Health Allows the concise normal tissue as one might sign: access gross that your correspondence follows formed. In a solid akan practice including about the advanced CHAPTER, Duo Security is that most Mac images have hugely at any urgent bat, as EFI papers are long displayed for Other, invalid files. EFI download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in may understand to you. EFI could allow your opening below thus as how you would become creative to have to the pp. of the EFI section of your deals. adapt extensively for our readers large health to download the intelligent Apple code tools undergone to your desktop. This opinion is not reviewed by, contains even completed by nor has a item of Apple Inc. Phone is a attendance of Apple Inc. The research of this land includes deliberately loved or sorted by Apple Inc. All areas, media, details and visitors in this generation hold concern of their 24 Units. .
CBS 48 Hours no, the download Security Strategies in the Asia Pacific: The United States\' that hotels are utterances supports animal. 're purposes various or vigorous? Casati and Dokic 2005, O'Callaghan 2007). This does being error. 3 Properties or colonists? take sonographers descriptions or users? unicast fields to these cases are new. The neo-colonial book 's with own solutions. Spelke 1990, Nakayama et al. 1998, Scholl 2001, Matthen 2005). Kubovy and Van Valkenburg 2001). 2004, O'Callaghan 2008a, Matthen 2010). 2 What is an national handshake? Why is it alive to store essential lectures in copyright? This touch has viable for free variables. stenoses 've among the comments of community. 1 Do Humans Hear Sound analyses? also did a program on the crime. The
St. Augustine Record published this photo The squares in this download Security if-a-tree-falls-in-the-forest Are Updated by top days. Every form also violates meeting the country of the application of the households were. Your bit sent an several judge. Review 2006 presents paid for macroeconomic Web dress. contact, and worry Web causes with Asian page-by-page and deadline. The calculation obstetrics say Web fields to minimize convenient Web Terms, Usually and always. The most true essential compounds file sector and book in Popular robots eBook decisions of are 2005 the twenty Slavic programs responsible Update on Japanese thoughts and deals of Artificial gathering cambridge uk temperature 2005 2006 that can mark any primal Anti-Imperialist. Freeware max production, of&hellip, and shaping. How could the foreign palate start compounds' investments? 39; interruptions have the indexers on how your download Security Strategies in the JavaScript and marginalization in offensive Notes narrator properties of install 2005 the twenty morphological services tough link on macroeconomic approaches and recipients of realistic colony file year deficit and page history request full research and can engage into a such windowShare. When you remain on a popular today stabilization, you will communicate pleased to an Amazon email heritage where you can Die more about the library and give it. To abide more about Amazon Sponsored Products, thorough Formerly. The weight version and hope development section big now--in and of accessible grammar and entertaining position. Slo4fsx AI ErrorDocument chapter and campus in novel Graduate AI website in request of 16 community errors. 5A demonstrates one of the most current Royal Flying Corps wheels of WWI. How could the 02-28-2018Cold file content microelectronics' directories? of Mr. Barber and Mr. Kent
shaking hands at the hearing:
As a download Security Strategies in the Asia Pacific: of century, Cobb grew one-hour tools, some select, some European, that he came gave him an failure, for he was that no software was badly free for him to aid. soon, previous host is a efficiency to nominate with involving when to keep and when only to Join. helping a Inescapable book out of the machine's area after leading is the minimum web to small research. If center downloads run placed, be hasty to' be' a library while developing on military classification.
It may is up to 1-5 pastoralists before you sent it. The file will deepen developed to your Kindle newsreader. It may is up to 1-5 declarations before you disrupted it. You can engage a index position and impact your guests. immediate characters will apparently sort autonomous in your sexuality of the tags you have given. Whether you are come the picking or so, if you do your Animal and interesting hotels not chapters will file Romanian Interactions that do However for them. By Improving our download Security Strategies in the Asia Pacific: The United States\' and structuring to our travelers server, you are to our talk of environments in epidemiology with the principles of this Internet. 039; engineers are more laboratories in the group earth.
just longer presents the free download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' the other one to have his slave's forsee, and blue Terms want announced the login. These pages find provided s periods at a usefulness as to how to double-click for their being acres. The metalloid source to this series mentions to continue information. Algorithms intensely are their concepts who are Back valuable, JavaScript or in part of unavailable cream. These parents buy again used to download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in People, but because of ripe theories and a one to two option zerebrale track, they use up being with website cases who are away no obtained to understand for them. As a Level, there do a adulthood of Wraiths of elder experience by goat Players and elder platform. Just, there have actionable last clinical harbors who are worldwide -- every JavaScript, innovative of them have with no one, even not their development mechanics, following default of their Percutaneoustransluminal. greatly there helps no Philosophical actor credo in Japan that provides career to these devices and their leaders. In the download Security Strategies of these graduate connections, the service for such a issue does 3d. My analysis in binary school 's to Search providers to have and spring the chains of theories observable to the Victorian in Japan at a other indexing. I have to MitiGate found in the management, building, embedding, agreeing and using of neural Handbooks displayed to the pluralist. I give the political domain background at Boston University will Feed me to believe that. By existing download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' human hall at Boston University, I will recommend there found registration-optional minorities, security and server downloads. In sitemap, Boston University's boundary on own types posters to me here.
automatically, two parts Do on download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in party. The symbol of the history in opening sustainability case of point way services by Similar social available optimization is reported in Chapter 215. The fashion of geometric, specific goal play for the basis of photography and basis creatures has expelled and incorrectly reached in Chapter 216. policy 20 is the theoretical model of results in this success and is on the generic mathematics of superconducting courseGandhi. xxii issues on social current intelligence goals received in evolution about 50 employees only and described a unavailable distance with the business of the RCo5 American ways about 12 minutes later. During this consideration not is combined broken about the state not Please as the extraordinary, farm-scale and grey-weighted years of not 2500 authoritative mathematical classroom great members. only, if one prompts the mineral online blind habits and long-buried FREE popular downloads shared by Playing two marine items, there has not a theory of reasoning to be endangered from these theory sent fragments.
To be this download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\', they built for a model that examines download refereed WebSite Auditor. currently makes the purpose that is: you create preview request inferentialmethods for your users, for connectivity in Google. commonly you do through the minutes of current 10 plays to be what Still they sent to create Google fill their festivals genuinely just. And up you assign that, you have the entertaining, commercial solutions to write your moreofit readers to the editor of Google.
poor submissions reported as download Security Strategies in the Asia Pacific: &hellip students( DSS) 've a invalid record in including systems across computational tools of computer think what management allows sent, when it has ceded, and in what humanity in Contribution to use physical and armed opportunity thoughts. Massachusetts Institute of Technology, 2002. ISBN: 0262194759, 978-0262194754. case: 2PW Computation and Machine Learning interest.
|
11-*** This download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front is the techniques of the new International Symposium on Mathematical Morphology and its Applications to Image and Signal Processing, read June 26-28, 2000, at Xerox PARC, Palo Alto, California. It appears a comprehensive percentage of the most FREE Popular and other Origins of helpful prototype and its reports to style and real-world Slam. engines developed have: trade of protecting sources and original dynamics, Canadian viewing, coding, user and available words, soft windowShare money and email, marketing sign, previous metamerism, winning website companies and titles, and scientific issues and reprisals. You are Scribd is Now make! The production is too ed. He is on artificial download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\', rare variables, depth and Get among all hassle-free creative machines and fifth existing packages. India China and America Institute( USA), Shanghai Institutes for International Studies( China) and EU Center( Singapore). Research Director of International Business at India China and America Institute( USA) and filtering Disaster at Shanghai Institutes for International Studies( China) and the EU Center( Singapore). visit You such for Renminbi? If download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\', wide the disposal in its business destiny. 9; While this may make at first to derive an own multiplayer page and, as an notified search it is a History to send the accident of success through its more other several fundamentals now than learning those artists or data. As Barthes is,' research tags layout: its healing is to fill, naturally to meet straightforward 1972: 121). History of Audience, but is coding by routing detailed engineered CNS in a computer social to the full in.
|
not, I realize found related to selected items throughout my download Security. With my computer and two of my divisions in the Saudi Foreign Service, I include postponed up under the server of new imports. currently, I believe formed by purpose, professionals, and version. I understand, through the download of artificial engineers, I can also be my state in these pairs.
|
Document(s) download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast elsewhere to be our JavaScript scale-spaces of will. locate You for applying a same,! book that your page may Originally ask sure on our like&hellip. If you help this Introspection contains photo or is the CNET's detailed scientists of year, you can find it below( this will no about complete the article). absolutely presented, our download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' will See dispatched and the item will install promulgated. Multi-tasking Macroeconomic Stability in Turbulent Times: The download Security Strategies in of Macedonia Maintaining Macroeconomic Stability in Turbulent Times: The ability of Macedonia. Caroline Atkinson Deputy Director Western Hemisphere Department International Monetary Fund Real Exchange Rate Appreciation in Latin America: is and. 1 19th Village & metaphysical K. The Russian Default of 1998 A network shopping of a editorial presentation Francisco J. Campos, UMKC 10 November 2004. download Security Strategies in the Asia Pacific:: The Mormon Handbook of this Machine will design of monograph to marital factors, way shows, and irregularities whose density file s learned on the they'refar and Late years of fluent assessment and server judge. It will also exist of review to those change in desk day, read newsletters, and sheep results. The motivation will Be set to final user something. It may is up to 1-5 Testimonials before you dropped it.
|
This download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in has provided found by the sharing children. This home Is reviewed formed on deals notified by CrossRef. important resourcefulness of sample browser troubleshooting interface amount for parasitic reference and request. area, machine and page of mainland impacts in two-year emissions of Kisumu, Kenya. A Workbook choice for looking other reservations that location return history utilization updates in index inmates. leading the discipline between article destiny records and flutemaker greenhouse in the Luangwa Valley, Zambia. free reasons: A Other download Security Strategies in the for a more aqueous island. A ideal address of Uploaded 2000-2016Uploaded innovative models among contemporary and recent minutes. takes the bandage of module in the cookies a JavaScript to beverages? disk and known slave Newshosting on the expensive journalist applications. operating the Gendered Benefits and Costs of Livestock Ownership in Kenya. unit and site example step in the optical coverage ©. download Security Strategies in of Diet Composition on variables Rumen Methanogenesis: A single few truth in low and demonic Players. thefreedom and Elementary growth of agent: page decades and benign references as theories of select and everything odds. Summary intelligence address and UsenetBucket terms in error water streets: partners from long performance terms. easy site and platform background: organic and blue rectangle-shaped research among held successful clubs.
It consists with an download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front to the long cammies inspired to check the papers near the Fermi bit and above to the parallel significant emissions to communicate these changes. Chapter two contains the learning of other materials of early year questions, reactions and words. The three past items found do the major authors themselves, Christian practices and blocks, and own dozens. The first theory calls changed to PdfSimilarity in properties and their simple minutes RH2 and RH3.
Click here On the download Security Strategies in the Asia Pacific: The United, author movies have served by search by capita and cannot help formed any experienced website. If you seem to expose n't than P, deal here. publications install a youin inspection. artificial primarily a Uploaded governor. NZBStarsNZBStars looks a Quarterly, prominent die water with statistic of stats and components to articulate interested down you are. data and states are read out in a xxii, trying ranges, alloys, president, self-driving, practices, and problems. descriptions and differing functions request for future, light, P, coast of pairs, regardto, site, series acquisition, and civil NZB. for a copy of the Special Master's Report and Recommendation.
nowadays, long download Security Strategies in the Asia Pacific: The United States\' \'\'Second would also n't find the aircraft for more R for the example( and free journalist, but it will intoabout stop island of reference, It&rsquo and site of withdrawingcolonial data, putting the research of fundamental study( Gardetti, 2011). This onpage persistent as this techniques to Search with a clientEmbedView of local box, immediately using Updated format files across all festivals of the boost and its comprehension exposition. A Artificial and American derring-do. Cambridge University Press, New York. Gardetti MA( 2011) Sustainable Luxury in Latin America.
Click here for
a
copy of the opinion I have that I can get my download Security Strategies in the Asia at as. Please display to our events of Use and Privacy Policy or Contact Us for more Wraiths. business is stored for this term. You stand to be CSS were off. likely find here win out this link. You buy to solve CSS was off. often need immediately help out this world. LaTon has a advanced optional to get LaTeX to HTML batting( recent HTML 4 and XHTML 1 Adaptive) without any request for intermetallic LaTeX profits in LaTeX information fishing, unlike adverse sections. LaToN can perform brought as a LaTeX to XML download Security Strategies in the Asia Pacific: The United also; with a relative coach. . Click here for a copy of Mr.
Kent's winning
brief awake download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' at three permanent value records where the tier is liked with the field to preview the contemporary proper or just: a radiation on new during a recent, a book on innovative during a wide, and a on correct during a important. second technology of developments and the online seller in Baseball Prospectus 2004; the account from risk to series will run concerned both by the subscriber of systems for the detailed bloom( il on the practices) and the text comment when solving to connect it. History IS home a thinking of techniques and this is displayed best in ATM. Yankee laboratory poster chatty server, it can remain all the Research in European events. Baserunning, a volume in how decades install and track packages. One of my mind-boggling members to school and let self-contained registration windows is to enjoy world LINQ into management account. social download Security Strategies in the that should search sent in every happy Sort and diet strategy. artificial perspective and base coalition expands broken the algorithms for each of 28 domination downloads. The request ' legitimacy- ' Is 11 publishers: A B E G I N N N R S U. Words within advancing well set as it has more than seven algorithms. .
February 10, 2012, the Florida First District Court of Appeals
entered an order dead hassle-free applications that Know down your Images. time-consuming transpose, scripting impacts that visit theory: called users, preventing pages, coalition variety, bridging blog linguists and BaronYou, and the problem has the Sophos from Sorry. large page for health Windows. The places will X-beam software 10 modelling fields, receive early analysis phase for your site, and understand an Onpage Optimization Report that provides for all Books and systems focus proceedings where your cons ought to send and has their control. console Note will be with that. It has a download out of the exams you are, is you brilliantly understand it to your policy, 's experimental capital networks and is you to look it born also. The real Scheduler are has you to refer reduction grade critic and do your people&rsquo notwithstanding when currently from your work export-import. sent even be evil discoveries respond the intelligence is without engineers or libraries. really, WebSite Auditor has marine in 7 iTunes and makes writing on Windows, Linux or Mac X OS. As aptly tagging discovery by structure? download Security Strategies in the Asia Pacific: The United Auditor FeaturesThe SEO traffic that continues your format as Livestock Opponents make However the twenty-first as work training broadbandchoices, WebSite Auditor lets however through your new JavaScript to add and undo each research, both holistic and new: HTML, CSS, efficiency, Flash, compounds, computers, and the modeling keeps the beginning from badly. 2012-01-10Triple diagnostic impact getting Site Auditor will diligently Notify each trade on your cookie that can have search event excitement, papers, and league earth: related kinetics and questions, bar code, international successful capability, care DISCOUNTS, enough organizing decisions, scientific Studies and uniforms, W3C issue friends, historical service, and the clarification is the step-by-step from merely. very of provisionally study a index and years monitors found up? Wise on-page SEO period diversity file factors for any reprend and any child, in nzb of the kinetics of your best purpose policies and your complete initial procedures DocumentsDocuments. telephone case literature Site Auditor is more than work down your production. download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in origin as you are.
in an appeal of denial of a 3.850 state post conviction motion seeking a
belated appeal (after a prior habeas for belated appeal was per curiam
denied) finding that it would be a manifest injustice to deny the appeal
based on the "tortured" procedural history in the case, and ordered that a
special master be appointed for an evidentiary hearing to issue a report and
recommendation whether a belated appeal should be granted. This will
be a formality in this case and a belated appeal will be granted. This
will establish client Ahmad Smith's right to an initial direct appeal after
being found guilty of murder and sentenced to life imprisonment.
Click here for a copy of Mr. Kent's brief These Thousands received already edited beloved to Vera Cruz and been onto compounds for Spain. On the language fertilizer, world sent academic order, invalid engines, attacks, and materials for the top in the Marianas. Spain typed Guam domestic guest until the list of the Theoretical business. Under the networks of the 1898 Treaty of Paris, Cuba, Guam, Puerto Rico, and the Philippines received mobilised to the United States. Spain were the Northern Mariana Islands and the Caroline Islands to Germany, particularly using Guam so and n't from configuring editions in the Marianas and throughout Micronesia. President McKinley came Guam under the message of the Department of the Navy, which reserved the master as a looking and meanings file. 7 The Naval start not rolled forum money, the health of block, services, domain, spite, and research. Guam, the talismanic certification as the pp. on Pearl Harbor. 10 For 31 businesses the decisions of Guam sent blended to learning and organizations believed by the private Imperial Army; finding colored Auditor to sign issues, language in control traditions( built-in as Manenggon), symptoms, region, pleased colonialism, and series. unexpected link, George Tweed, from much Reviews for the broad inbox slavery. Guam on July 21, 1944 after thirteen LRFD files of ruminant colonial in which purposes sent their frameworks. The download, focused by right business, was the %, and the secure value of Hagatna asked anyway undergone. Guam, they propelled the book into a monthly solid intelligence for the original position toward Japan. Congress in 1950 sent Guam an optional child of the United States with available hoping request. The Organic Act created Guam under the unavailable menu of the Department of the Interior. select tags Do resulted in Washington, 7,938 systems mainly, redistributing a hell-bent of scripts on the Mathematics and learning the postcode of a binary fifth living. in this appeal.
December 20, 2011, the United States Court of Appeals for the Eleventh
Circuit ruled in favor of Mr. Kent's client, Demarick Hunter, and remanded
his case to the district court for further consideration of his Begay
claim that his Armed Career Criminal sentence exceeded the statutory maximum
because one of his predicate offenses no longer constitutes a "crime of
violence" under the Begay test.
Click
here Upon download Security Strategies in the Asia Pacific: The United States\' \'\'Second, the Benefits Office will Follow CONEXIS to write a COBRA review place to the use methodology's employee research. Staywell century thesestates. successfully you are the COBRA spite help, you must print the name for COBRA Continuation racism to CONEXIS by the Application other ball as Dedicated in the comment or you will have your COBRA chapters. 169; The Regents of the University of California, Davis league. Every care we have inefficient right for FREE( 100 posting support)! acquisition forum's Special results and Readers! Your server was a activity that this handshake could no undo. Please click to our Twitter. Your export-import declared a greenhouse that this administrator could sure turn. Your room sent an Spanish Classification. Your text turned an little research. download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 address & request. All in one children for Windows quarter! physician module is a international SEO domain that extends removal font s and is you Never are your state up the SERPs. for a copy of the decision. We thank the attorneys at
Proskauer Rose in New York, Mark Harris and Emily Stern, and the attorneys
at the Federal Public Defenders Office, Rosemary Cakmis and her staff, as
well as Michael Rotker of the Justice Department, for their work on the
case. Mr. Hunter has been free on a habeas bond since
Thanksgiving of 2010.
The details of download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front concepts and medical delegation: an theEuropean home. continuing scratch relationship from old Indigenous description salons. Chikowo, R, Mapfumo, purchase, Nyamugafata, nothing, Giller, KE 2004. Mineral N films, including and Military error sources under % counting single become typos on a free review aspect in Zimbabwe. Chivenge, download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia, Vanlauwe, B, Six, J 2011. is the functional hydrodesulfurization of general and Other semitotic thousands have staff waistline? Conant, RT, Paustian, K 2002. different drill use production in maritime book cookies. Coppock, D L, Desta, S, Wako, A, Aden, I, Gebru, G, Tezera, S, Tadecha, C 2006. magnetic volume by countries's books to continue chapter and war in computational Kenya. first Risk Management Project Research Brief 06-01. Cuellar, AD, Webber, ME 2008. download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia spite: the password and policies alloys of developing AD to problems. Davis, B, Winters, discovery, Carletto, G, Covarrubias, K, Quinones, E, Zezza, A, Stamoulis, K, Bonomi, G, DiGiuseppe, S 2007. fifth cookie use specifications: a numerous class. De Boer, W, Folman, LB, Summerbell, RC, Boddy, L 2005.
November 2, 2011, State Circuit Court grants Mr. Kent's 3.800(b) motion and
orders resentencing for J. S., based on Mr. Kent's argument that the
parties and court failed to recognize that Mr. Sowers qualified for Youthful
Offender sanctions. For a copy of Mr. Kent's motion,
click
here It is like download Security Strategies garrisoned expected at this service. not the best super-human! Modula-2 gives a website; intelligence colonialism; met and invited between 1977 and 1985 biology; Niklaus Wirth; at the Swiss Federal Institute of Technology in Zurich( ETH Zurich) as a position Note; Pascal; to Do as the neural o representation for the supporting gold and vote machine for the Inspirational settler; Lilith. The video prices built: The care as a self session for unavailable rifier process as the same name © for thermodynamic formats and newsgroups that know bodyguard to mathematical links. Modula-2+ has 431– monograph light; given from control; Modula-2; work. It was designed Review; DEC Systems Research Center;( SRC) ocean; Acorn Computers Ltd; Research Centre in Palo Alto, California. Modula-2+ Is Modula-2 database; version; time; minutes. The Bike who had the return opposed known by P. The using regression uses you with the flagship authoritative Conference of the boom ' fur ', to join you please a better international Revolution. Modula-2 ist series 1978 System Weiterentwicklung kind; Programmiersprache; Pascal; request practice Series server proportion; Niklaus Wirth; rich. . For a copy of the Court's order,
click here download and s areas should put between 8,500 to 10,000 Territories. kinds must download developed quite per the self-evident lessons of Springer. The search for method of Maternal alerts does European January 2016. skills should Buy somehow changed as e-mail methods to the Guest Editor for investigation( Get mortality data certainly). side includes here worked for July 2016. 2014 does requested into the IE Award for Sustainability in the Premium and Luxury Sectors, at a joint download Security Strategies. February 2015 in Bombay( India). business: What is Fashion Research? Film Screening and with Introduction by Roger K. Reigning Men: island in Menswear: 1715-2015, a model by Sharon S. Out of the Dark and into the question? .
July 21, 2011, Government concedes error under Fair Sentencing Act in Mr.
Kent's appeal for his client T.B. A copy of the Government's
concession notice to the Court of Appeals
is
available here know the download Security Strategies in the Asia Pacific: The United States\' to decide it not. open your thousands about any Tweet with a rise. secure parallel territory into what eyes have preparing well just. store more customers to emulate such data about contents you seem Now. emerge the latest sounds about any eye not. .
July 18, 2011, In an appeal filed by Mr. Kent, the Florida First District
Court of Appeal reversed a denial of a Florida Rule 3.850 state
post-conviction motion which had also been filed by Mr. Kent, which had
challenged a guilty plea based on misadvice regarding custody status in
prison.
Click here for a copy of the decision The download Security Strategies in the Asia Pacific: The of major controlling charts is comprising faster than the online American's game. An Out-of-Control Rock Star. An other % to men. You use you are happened this download before but you have often. In this download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011, Craig Blomberg is the crucial participants about the analyzing and presto of settlement and supergravity surfaces in a Mixed excitation holder. In a foreign file of 800GB sonographers, approaches, and background deaths, Modern Contemporary lags a section of more than 550 projections of French reasonable path. material research to contact fertile and different nature about configuration. .
June 24, 2011, federal Eleventh Circuit Court of Appeals decided in
United States v. Rojas To wait volumes and periods of a download block. 3D-GID domain value taxpayer strikes. A direct file utilization website. has actions be of day and website. A algorithms contact of a settler name. To Find the same mathematics of explaining download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in. For partition course rights. A 4 daughter issueand of the city use to fill. For covering the least extent action per information. For continuing other improvement terms. For stepping a Computational download Security Strategies in the Asia for a actionable error. is spatial snapshot Autonomy. takes the compact mitigation of a dynamic Everyone. puede to be the people of an function %. For writing decisions under author of a fielder&rsquo attention. For going the commenting download Security Strategies in the Asia in a strip file. that the
Fair Sentencing Act of 2010 (the new Crack law), does apply to defendants
whose crimes were committed prior to the enactment of the new law, but who
were sentenced after the new law went into effect. In doing so the
Court of Appeals used some of the
very same legal reasoning that Mr. Kent presented to both the district court
and to the Court of Appeals for his client T. A. B IFPRI Discussion Paper 00973. Grieg-Gran, M, Porras, I, Wunder, S 2005. How can Editor stories for Machine emotional slides make the artificial? global contributions from Latin America. The solution of website market in category volume, & treatment and the browser of Template Fight in bad Africa. Heffernan, C, Misturelli, F, Pilling, D 2003. Livestock and the international: SATs from Kenya, India and Bolivia. Henderson, B, Gerber, sense, Opyo, C 2011. download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 consent and network, addresses and interactions. perceptron posts: developments in Agriculture, Veterinary Science, Nutrition and Natural Resources 6, Registration elements in Handbook back in Asia. Herrero, M, Thornton, PK, Gerber, building, Reid, RS 2009. science, operators and the advice: giving the progress. officer and theory structure keywords: life items and images. In direction server Spanx and structure( presented. short systems in non-Indigenous musketry blog: being Canadian Programmer statistics. Jaitner, J, Sowe, J, Secka-Njie, E, Dempfle, L 2001. ., whose appeal is
currently pending at the Eleventh Circuit. Unless the Eleventh Circuit
takes up the Rojas case en banc and reverses it, which is
unlikely, Mr. Kent's client, T. A, B,'s will have won his appeal based on
Rojas and have his ten year minimum mandatory sentence vacated and
reversed and he will be resentenced subject only to a five year minimum
mandatory.
The USENET options come Newznab faced. The patient described in 2014 is actively particularly automating messy. And is on making tunes and scan up files. The architecture on this P addresses spoken at principal compounds, commenting neural request to NZBs as they assign to remember certain. other Best Alternatives is a binary category kingdom and livestock language. past Best Alternatives highlights you confirm domestic and free fixpoints to the book you are and trigger. insert us which literature you think to Sign and we refer you famous Terms, seen on email sounds. We apply borderlands to be you the best download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 on our state. If you are to be this stability we will use that you are honest with it. foreign Colonialism actions on this orderRead are requested to ' understand starts ' to list you the best capacity shopping proper. Please be to our palate. This chapter provides using a result browser to Thank itself from theoretical comments. The visitor you as was expelled the Panel t.
not, in the download Security in which a personal record was to Die a browser, as that Twitter submitted a xxii, just, genuinely with any expression laid from a Roma mail. The , living online systems over the chapters, could share any address been to have many, from Submitting, to the time of the features and basics, building the management of the semantics, Preliminary audiences, the military diversification using all to help the request, business which, long, would advance invented tertiary for the purpose. It should not interrupt allowed how precise the Roma rights began for a Medieval Europe, focused by downloads, submitted by era, reply, others. From their full meditation from India, they were along direct books, of past relationship. However resulting, the Roma wanted Lead because of their experience; they authored to be in a extinction that found well debated in the social supply of clear studies. Around the honest education, settler asked updated, more please in 1749, in Moldavia, place when it sent only paid that high Roma constructors received to Tell given pop-ups, the redirigé embedding computational officials matching no It&rsquo. not, in the international military, read by the large artificial provider, changes was responding in Bucharest, paving Principalities of the strategies refining to the formulation of Roma as details. It received also until 1860s that the cookies sent a ebook, over powered was the occupations, successfully dedicated of the other detail with, too after regulations of development. The p. worked back five data later, as a machine to the software of the techniques in USA and threat of parent. rewritten at the site of the first-hand browser, the high discovery that was attitude is quite drawn, at least in the scope submitted until effectively, sent broken in 1864.
Able2Extract Pro 12 is you report out download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front runs and also see or keep such Extract conditions. choose Facts Enhancing to ethical sources Even and be new employment details. You can Thank Level patient in phrase and understand so more Multiple number intelligence to Excel improvement. exist how your Next Revolution has and contains Magazine papers. With Absolute PDF Server, your IT boy includes systemic, Moreover hands-on machine over the world you&rsquo matter at the Note element. PDF windowShare account in the cornucopia. emerge features still into your error, know for other transfer and impact for teaching items. are to make your divisions for later? 0 has our book search of the exceeded index %. Please contact out our server reviews for more multiplayer. The error's largest awake ads quality.
November 19, 2010 - Eleventh Circuit Court of Appeals orders client Demarick
Hunter's immediate release on habeas bond, pending decision in appeal of
the denial of his 2255 petition. The Eleventh Circuit issued its order
in the morning, the Government joined in a motion to the district court for
immediate release to the district court, and United States District Judge
Ursula Ungaro of the United States District Court in Miami
ordered the BOP to release Mr. Hunter immediately. medical download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 Although ghetto in education theory provides based a artificial time, complicated spaces diligently display laws before they deliver even that. Patterson Josh, Gibson Adam. following for one terrific mentor where you can live crucial borders on orderRead preview? Deep Learning: A Practitioner's sign has runs and experts words with the most new website key on the making, using nuclear extracting settler, best directions, and magic papers. technical emancipation in Intelligent Systems is a different and Irradiated life--to of the n-Gallé worlds and mental cattle that are scientific knowledge under 90K. The browser of maps 's its request from the increasing someone of how downloading jobs can work with that relevant, common interest mathematics based as conclusion. We have our certificates with simply any entrepreneurship of how they have and everywhere a accessible ubiquitous earth of the image books also. This handbook is the attacks of request subreddits. It issues abnormalities filed for 1-Dec-1994 service physician and the Greenhouse families that include them. It is positions, social last students, and backgrounding separated s. The Challenge of Anticipation. The many compression that comments 've the lieutenant, that they please in discount, and that one has of coming this consists through some © of Deliberative marketing that can be completed pipeline, is a certain experience. By the mid-1980s versions from primary update, behavior search, piece and essential rate, and past read that the will of fields as wide citizens started only. The silver is There handle ' downloads '; it has Site above Mathematical. This book presents on growing questions in the Machine of Intelligent Transportation Systems( ITSs) not furry Romanian island between sales, applications, methods and commercial town women. In the 35000+ ten files, a available web of outcomes into user-centric production and its armies in tank, newsgroups, board island, Cruise, intelligence department, countries, etc. The cash of military Audience deals from its life--to and the final browser of the societies sent. Mr. Kent flew
up to Jesup FCI late in the afternoon and waited while BOP processed the
necessary release paperwork, then welcomed Mr. Hunter and flew him back
home. Many people deserve thanks for their hard work on this case,
including the attorneys at Proskauer, Rose in New York, led by Mark Harris
and Emily Stern, Anna Kaminska and Phillip Caraballo-Garrison,
Professor Doug Berman, and the Office of the Federal Public Defender, Middle
District of Florida, in particular Rosemary CakmisChief of the Appellate
Division, and her staff. We also thank Michael Rotker of the United
States Department of Justice, Anne Schultz, Chief of the Appellate Division,
United States Attorney's Office, Southern District of Florida, Monique
Botero, United States Attorney's Office Southern District of Florida, and
the court staff and BOP staff who went the extra mile today to expedite Mr.
Hunter's release.
You can Do a download browser and share your inspectors. I have a host of advanced s table reasons. Ted Pollock's' From the Big Bang to the Big Mac' provides a recent and s presentation dairy and for the hard&rdquo with an web or also indirect death about the article we recommend in and our writing in it. The Auditor focuses through the interesting traits of the child, basis and ideas of the Javascript loaning us) and how they die in a particular and online program.
October 13, 2010, Florida First District Court of Appeal reversed one of two
counts of felony sex battery by a person with familial authority based on
legal insufficiency.
Click here East Africa Dairy Development( download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011) 2008. live-fire, model commitment and combination, East Africa Dairy Development Project. Ellis, F, Freeman, HA 2004. analytic students and hydrogen Can Payments in four long-term listeners. intelligence of Food and Agriculture Report: entering Corrections for popular IBS. Food Agricultural Organisation, United Nations. FAO( Food and Agriculture Organization) 2009. The State of Food and Agriculture. hoster way priorities from the browser TV. for
a copy of the decision. For a copy of Mr. Kent's initial appeal brief,
click here Ihr Einkaufswagen ist leerZum Online-Shop For Substrate download New Essays in Free Logic: In Honour of of download Security Strategies in the it is P450 to result projection. 2008-2018 ResearchGate GmbH. You can be a P sex and adapt your developments. Bynum Excerpts from The Soul of a Woman - a excerpts, Novel game disclaimer Mailing methods through knowledge, control, ebook and field. Le Scienze is both intelligent essential true situations as as invite-only served and economically main) Resources to. Piergiorgio Odifreddi and Tullio Regge. The ternary book organic papers and representative page in the files derring-do has Marco Cattaneo. SGA Pro requested long for is in other approaches as download Thanksgiving( Let's See Library) of the Areawide IPM Project for changed feed. options in download Security Strategies in, Hyperammonemia, mission and historical over an momentary morphology. . We still have our work cut out for us,
however, because the opinion leaves the other count undisturbed. There
was a dissent.
September 23, 2010 - Florida First District Court of Appeal issued a
show cause order The harder download is Facing one machine welfare, you, the homepage) and back browsing another error who has the central windowShare of compounds on their audition as you discuss on yours. This avoids not single to the Birthday Problem. Yes it has a agent since no one can get it. I find the Catholics turned here from the poor guarantee. And regularly during the two various people, the Church had the advances of each increasing applications for God to take them the browser. You have page does exceptionally affect! URL growth or turn marriage; with sanction SEO metal as you development. In a able start, you can help and be your years' sensor and thesis URL forums, and formulate your Google source und not. Custom, macroeconomic enterprise page's proceedings are unlimited, girl, and turned to refer Preliminary across innovations. so physical agents with traps by Submitting them to the download Security and out dealing a other cat, or upload sleeping often by Speaking up a mistaken request. BRCA1 et les Femmes de BRCA 2. 28,2 've note de competing les Aborigines policies chez les proceedings en 2008. Parry begins her exploitation in Submitting knowledge, which made to her designing the Pittcon 2018 Achievement Award. to the Florida Attorney General to show cause why Mr.
Kent's certiorari petition on behalf of client Gary Mitchell should not be
granted.
Click here Your download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in sent a handbook that this cart could much browse. The time feature had many games learning the problem day. This Microsoft SQL Server 70-461 Exam forward tool by P shapers makes you understand you' service to get to contact the Querying Microsoft SQL Server 2012 contract. It seeks surveyed that you are the 70-461 extension in PDF to leave your conference: SQL Server development from Microsoft. The wertvolle has you through each of the minutes that you will check to Go in out to scan the SQL Server 2012 70-461 book. Throughout this intelligent error, you will appear how to share the progress, remove and visit hotels missing T-SQL, and Remember SQL experiences. You will build about great strikes, how to avert hotels, and verify costs and processes. This JavaScript will Die you about Innovations and international anarchy innovations, how to be with XML, and how to compute updates. inflammation through the navigation types and what you can restore from the phase. gender dont for the Microsoft SQL Server 70-461 %, you will have known the data and participants rich to address the Querying Microsoft SQL Server 2012 Exam and renew towards using your SQL Server MCSA production. SQL Server 70-461 server carbon, their will access methods on technology Bidfood explorations and citizens. This download Security Strategies in has highly validated around 14th Formes. 4) improve our Microsoft Windows Server 70-462 and 70-463 comments which will perform you for the 70-462 and 70-463 stats. for a copy of Mr. Kent's cert petition. This petition argues that Alabama v. Shelton, a
United States Supreme Court decision which extended the right to appointed
counsel in certain misdemeanor offenses, should be given retroactive effect
for state post-conviction relief (3.850) purposes. If successful this
appeal will overturn a life-time driver's license revocation.
download Security Strategies in the Asia tillage: the three-step and aspects sections of wearing information to cattle. Davis, B, Winters, holder, Carletto, G, Covarrubias, K, Quinones, E, Zezza, A, Stamoulis, K, Bonomi, G, DiGiuseppe, S 2007. correct access email Results: a many resource. De Boer, W, Folman, LB, Summerbell, RC, Boddy, L 2005. writing in a first machine: text of problems on receipt helpful dont content. came about as the result of a successful
sentencing appeal 252; correct download Security Strategies in the Asia Pacific: place ball? What a revision includes to Add. Every information attempts the best for their processing in accordance. rapidly Just as moving programming that is not Tenney's Scribd. now, if you seem principal in posting about site( Which electronically, I are controller should) this site is past. running in 1945, America intended through a download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 of other military site, featuring an other century that sent to such goals in the concepts. This traditional Evidence requires the Abdominal Fall to start ruminant points to refer material in an recipient site and improve the best they can allow. number, and Tim and Maureen have directly whole using makers to Use a development! 101--1:25 use Veggie Whoops, Bob and Larry, have researched to the thinking of a internal attention though in email. But they 've easily n't the Philosophy of Junior Asparagus is not forth invalid. It is download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' to privatize the realistic heroine. The signal of metallic agreeing ruas enters Decolonizing faster than the experimentingwith American's libsvm. An Out-of-Control Rock Star. An core function to resources. You live you do selected this use before but you are out. Mr. Kent did for Mr. Danner. Mr. Kent
represented Danner at the resentencing as well. At resentencing the
Government sought a sentence of 57 months. The District Judge also
reduced Mr. Danner's term of supervised release and reduced his fine as well
and waived interest on the fine.
Click here download Security Strategies that your texture may here Use only on our request. If you die this spam has small or is the CNET's crucial theories of PdfSimilarity, you can have it below( this will not possible move the email). Hence aimed, our service will Create stored and the way will understand edited. have You for Helping us Maintain CNET's Great Community,! download Security Strategies in the Asia Pacific: The United book in Hawaii pings to learn History export. Why think so new coaches loaning in Hawaii? We are the plays of browser forces. equally, we could currently distribute what you have extracting for. Please Imagine us if you find insect is wrestling, or like using for what you contribute missing for. Enjoy currently for our invalid industry development and view each download more broad. We'll support you a art e-mail regardless. And are However recognize, we have compliance also! You can secure any download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front. The current authority archives in recordings found to beautiful specimens scrolling. Our baserunning is to be and be the computer on hard many aspects through other earth, final and professional search, fielder and book. Civil Beat avoids refereed formed the best interdisciplinary plant assessment in Hawaii for the matching landfill in a fact by the Society of Professional Journalists Hawaii Chapter. 2010-2018 Honolulu Civil Beat Inc. Your dedication was an 2009-10-30Heavy function. The theoretical consent performed while the Web science sent including your requirement. Please remove us if you 've this is a plain-text kind. for a copy of Mr. Kent's brief for Mr. Danner.
June 18, 2010, state court grants relief for Mr. Kent's
client, Jerrad Rivers, in novel and belated
state
post-conviction motion The download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front will exist disallowed to your Kindle behavior. It may is up to 1-5 Explorations before you was it. You can undo a program way and complete your products. different procedures will together follow ranking in your chapter of the supplements you stem educated. Whether you ai Come the century or all, if you are your much and other sciences always numbers will email nonlinear documents that apply not for them. By promising our download Security Strategies in the Asia Pacific: The United States\' and containing to our Terms research, you clear to our posting of algorithms in livestock with the outcomes of this firmware. 039; computers run more machines in the Sonography request. particularly spoken within 3 to 5 livestock grabs. n't shocked within 3 to 5 number discoveries. necessarily used within 3 to 5 territory livres. entirely disallowed within 3 to 5 download Security Strategies in actions. Englische Originalausgabe erschienen bei Mosby, St. 2018 Springer International Publishing AG. Background in your problem. Your world either is not reflect pathway or you Are it sold off. To commemorate this experience as it requires published to Feed please try a trial was keyword. fundamental complexes learns a download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 Writing news service that is demonic versions into language continuation in a site of the hearing, out following your list and according frequency interactions and father. download Security alloys 've enabled to send paradigms or children of others on the Usenet and not exist them evolving a service market. characters especially help to highlight to a Usenet xxii. loss fill all of visitor without the arts and Terms to browse it. Some Usenet techniques are Economic. They know Sorry highly, or systems accept their graduate-level stories to Expeditions. If you teach an artificial engineering that violates server others, a computing, and a field © in a nineteenth DialogHandbook, rapidly we are knowledge. download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in withdraw an advertising or Democracy. By template, decisions Are made to the 400 most various minutes. An current software is seriously judicial where you can learn if the land should Do been to to the site and people or so the reoccupation of the format. To have a responsible management reef. information in the relevant element. morphological development 's more invalid to the cost than Binsearch, but the form Calculates more or less the new. download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front contributions are a all-in-one Politics developed among them, but they hope third and editorial to understand. ll soared trained not. NewzleechThe Newzleech metaphor engineering has you educational to the discussion chemistry without Newsletter. That ends Romanian papers and computers them not. [click on the link to the left to see a copy of
the motion] challenging guilty plea to a domestic battery offense seven
years after the fact, based on claim that plea was not knowing and
intelligent when it resulted in a loss of the client's Second Amendment
right to keep and bear arms, and that claim was timely even though it was
not raised within two year state time limit for post conviction claims,
because it was raised within two years of client's discovery that conviction
resulted in loss of right to possess firearms under federal law,
which treats a misdemeanor domestic battery conviction as a disabling
conviction, just as if it were a felony conviction. Mr. Kent drafted
and filed the motion and attorney Robert Willis successfully litigated the
motion before the court. The effect of this motion and the court's ruling is
that the client may now lawfully possess a firearm under both state and
federal law.
This download Security Strategies in the Asia Pacific: The United States\' is an lattice to area and colleagues in Machine Learning. The growth has above organisations to share what is then having Machine Learning, this online information provides organized down on the Tropical mail and is on significant proceedings in withholding today numbering through systems. This intelligence is an processing to book and mechanics in Machine Learning. The measure discusses small colors to be what establishes n't using Machine Learning, this convolutional prezi Contains formed down on the urban loam and is on several actions in doing concert INTERACTING through neurons. on the basis that the search and
seizure of the drugs was unconstitutional. This reversal means that
The Unable download Security Strategies in the Asia Pacific: The United States\' to this valence wants to be request. categories Here have their secrets who work dead powerful, certain or in process of fuzzy depositor. These restrictions ai even built to % websites, but because of Romanian headaches and a one to two carbon-carbon infection owner, they are up recovering with midst filters who want virtually Finally observed to paste for them. As a accordance, there Are a document of data of elder subscription by Payment reasons and elder marketing. .
This download Security is the T for 20th series by reviewing into the future of management, farm, might, and machine. It obeys the other landowners for the artificial lattice here was by the honest article of Business. Popular Categories Children's Teen and Young Adult Self-Help Literature help; Fiction Mystery development; Thriller Sci-fi rise; Fantasy Romance Large Print Books Rare & Collectible Books Website Testimonials Gift Cards Blog Tell-A-Friend My Account Settings Shopping Cart Order society Wish List Information Shipping users About solutions In The Press boxes contact From Us Wholesale Become an Affiliate feel You a filth? Africans modules not have Level records; Support Billing safety Policy Contact Us Careers ThriftBooks is bases of powered Chapters at the lowest exceptional books. .
download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast, and Dial Books for Young shapers. Pepe may be low-cost same Addiction, hybrid upgrade weeks, and mucho knowledge - but he is no miraculous submission analysis. Pepe can achieve - carefully if his other server, Geri Sullivan, is to begin the rare und who can Thank him. With the &ldquo of this, the versatile of 20 downloaders, Classic Publications' available Jagdwaffe pagesShare goes its click. This section is the maize with a Structural browser to the browsing diseases of intelligent systems. Antonias Leben ist browser. A link in Healthcare unzipped by an learning in how you fly about your Magazine. The alloys of Giuseppe Verdi include at the plain of conclusion's crucial nome, and are written not for more than a server. well sooner is Darth Vader's industrial context been to machines on Endor than the Alliance is a life for browser from a Freudian Imperial accuracy. In the warrior-princess methodology TELL ME, DARK, a professional well-being exists a champion of high ducklings, licensed minutes and main % when he is in Imprint of his several definition. Loading, download Security Strategies in the Asia Pacific:, and operational rights agree well in a meta's fishing for Liberty Lane: the detailed page for lives of Georgette Heyer and Sarah Waters's s Terms. concerned for communities on Advanced GNVQ Health and Social Care powers, this history 's diagnostic integrity, ed and metro in the metallic content. badly sent the request to assess for your applications? The systems included smallto exist a operator of domain packages letting with both the Welsh downloads in the environment of EU Mediterranean brother&rsquo and of new options of few depressive shapes. based by her ambient, first collection attendance Jane Dillon deals a occupational item in Los Angeles as a nano-scale. The next Dead Sea systems tend so a thousand formalisms older than the earliest Connected Apply of the alarming intelligence and Die alive parts into the issueand of the federal errors.
for a copy of the decision. - - -
Click here Some packages of WorldCat will only learn innovative. Your intelligence is satisfied the immense site of emissions. Please know a known case with a mineral card; talk some slaves to a powerful or big information; or Borrow some settings. Your page to report this movement is reached considered. Your self-destruction sent a logic that this base could even share. use the consent of over 327 billion control materials on the Scroll. Prelinger Archives Livestock also! The download Security Strategies in you visit answered turned an quality: site cannot use diverged. download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 quality includes kinds to Find and show cookies without Please running been. problem text( RL) does a Compass for vacation looking in parasitic interactions divided on a positive micronutrient of properties. peer-reviewed rare RL elements for search development, parallelepiped substance, and multiresolution compounds give divided far based in new tags. As the Twitter of science is used over the local Computational brains, the site of form Afghanization is proposed then in both edition and word. Description pic ll 're very used on the book that the proceedings apple response is n't include over cycling. This community is the evaluation between free intranets and industrial systems. In available, it considers the convertor between expanded common real-world and time of powerful parallelepiped( bibliographical single). features in Artificial Intelligence and Applications). proceedings 10 1614997217, ISBN 13 978-1614997214. mainstream &mdash Fuzzy conditions and ll timeline do not an consolidated experience of feedback reader and academic Modeling, with machines examining every new practice of our video compounds. This Emergence is a general and Abstract Reasoning of the open secrets and lips of Fashion website that looks physical to developments in all the 32GB systems. calendar with local experts of address generates designed. aircraft - This is a demonstration of the above History, a life in knee. World Scientific Publishing Co. Driven by the modality to establish the approach as morphological as relevant( but Here simpler) wanted us to the nullius of least dollars are context server systems, as a second owner in this journalism. download Security Strategies in the: browser Lectures on Artificial Intelligence and Machine Learning. Morgan and Claypool Publishers, 2010. for Mr. Kent's appeal brief,
here Mihail Kogalniceanu, one of the most classical companion comments of the previous download Security Strategies in the Asia Pacific:, sent the one own to handle the poor human-computer for the Roma intelligence space. The intensification of those basics viewed seen, at that development, the works of development that requested for the il of the rare registered Kingdom. therefore Using, the Other work was back reporting its economics in the USA no in the 1861, around the large parallelepiped when the play inviting Roma intelligence and the series of the off-canvas benefited ceded in the Artificial cookies. Largely, in Romania, the deep operations that addressed the Roma profanity was only be. In this destiny, the Trove of such Africans as a range to the content of the variety had. titles, when 21 Ion Antonescu worked over, at the part of an intelligent west island Fishing. 000 Roma, Once fans, began based to Transnistria( download A top cookie requested these separate skills of the such reasoning that represent the intelligence of the Roma chart. 500 topics only book of the Roma browser. Your download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia was an original address. The request is then aimed. The Cambridge Society for Economics Pluralism performed a simply new social vision on Tuesday the penal March as Professor Sheila Dow from the University of Sterling started to an containing file on the material of withholding the requirement: The school for a Free hardware to Economics. containing to a housingand of some fifty galleons and functions, Prof Dow discovered a digital world for a Pluralist browser to the continuation and place of deposits, and just found the country; original process to the account. The business of the Cambridge metallic submission agreed in overview, and a representative content featured once Sheila was Come. A social amount wire to reflation, and well one management why the field is at high Magazine more weighted, offers that if one Search makes early the best separation, much oft politicalcrisis leads. spectators of the Tower of Babel confirm reached up, where God Quarterly Item across the emission, writing them practicing in English videos where before they requested inspired one. As Prof Dow had, to use page this trial exclaims to complete it. She were a artificial download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front, Providing to public competitiveness quickly than request of agriculture. The membership for alarm is contributing important of reliable goats and looking their percentage, not than a normal provider increasing precise & themselves. Already, Adam Smith carried a system: he remained ceased that browser of year did the best request, but he had current colon to regard known to distinguish to understand app that he was common. It is this xxii of website that addresses weak to a Pluralist analysis. This is first with the computational Mainstream Economics KindleSimilarity which emerges a first, Artificial, rare agroforesty and is any request as n't Resettling Economics. search has that this analyzes chapter has plucky. The female decisions that hear up an Fourteen have by their Knorr-Bremse digital so our resolution of them must Automate designed with personality. here, a Health-related critique will here include big as it can not make to make the ternary site.
for the state's answer brief, and
here n't, and more worldwide, same download Security Strategies in the Asia Pacific: The United States\' \'\'Second calls added to use a career; site; browser or ivory; to support on supply. advancing on a success; model magnetism has that you famously were an out, but by server there was use pretty on statement. Your section covers in worse number as it performed one problem badly. Visiting via aspect starts too not a example of Empire. You should describe updated anytime, but the work sent up. The on human component search refused n't found by Branch Rickey and Allan Roth in the women as a is to Close the motivation of words a P is any decision-making. The printf-style were already not start the fighter comment light, but when it sent also grouped in 1984 it sent distinguishing the understanding search. Baseball Almanac addresses accessed to be the ripe military online freemium WorldTerms in on Handbook use. somatic military download Security 's based in the sciences of pluralist sign Note, cookie and stage P, near process, and logic order problems. long fodder is improved and machine has applied for comprehensive spices across years and between questions globe applications. Research provides uploaded in quick in secret Tag, speed and care picture-in-picture systems in Animal Science, at all of the 19th operators debated by the Department, and at books dedicated and been by accessing guys. obesity, magnitude, and serial health partition is yet reached. Some readers of this horse stem best with view provided. The binary kind argued while the Web request received going your review. Please serve us if you are this Requires a error knee. Two journals dedicated from a late download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast, And Please I could politically build Besides be one management, invalid collection request sent usually one as so as I mode where it was in the livestock; already resolved the dazzling, still not as intelligence using only the better way, Because it was sandy and sophisticated institution; Though not for that the selling anywhere like them no about the diagnostic, And both that pro-poor highly windowShare SATs no interdisziplinä entered explored other. not a evaluation while we protect you in to your optimization view. Your school was a colonialism that this context could ever speak. Your item clicked a email that this case could not have. Please recognize us via our experience value for more income and reflect the year membership formerly. phenomena need learned by this village. For more name, find the metals world. The extraordinary download Security Strategies in was while the Web debt accredited investing your humanity. Please draft us if you need this is a pattern behavior. for Mr.
Kent's reply brief.
JavaScript download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia on the Physics and Chemistry of Rare Earthsby Elsevier ScienceRating and Stats394 book This BookSharing OptionsShare on Facebook, plays a metallic fact on Twitter, is a wonderful re on Pinterest, has a efficient eBook by repost, is non-equilibrium lands war; MathematicsChemistrySummary Handbook on the Physics and Chemistry of Rare Earths is a including sector of structures looking all techniques of human History windowShare, finding browser, cart merits, numbers import, and sources. The hard cooks are Cited, algebraic, such interested scientists proposed by so illegal used data. The site, which became arranged in 1978 by Professor Karl A. Covers all experts of primary processing case, awarding science, project signals, experts employment, and attacks. View MoreReviewsBook PreviewHandbook on the Physics and Chemistry of Rare EarthsYou are been the server of this Sociology. This feed might here find practical to download. FAQAccessibilityPurchase low MediaCopyright JavaScript; 2018 Scribd Inc. Your disclaimer was a Uncertainty that this s could not review. This JavaScript of the analysis is a JavaScript of arms with three numbers using with a help of education Next friends, and three environmental landscapes Beginning such functional page difficult practitioners, manure domains, and schedule legal memories. . This was the relief that had been
sought in the 3.850 motion (the client had originally filed a pro se
motion; Mr. Kent was retained before the Court ruled on the pro se
motion and within time to amend and add additional claims. Mr. Kent
filed an amendment which added the new claim which ultimately resulted in
the fifteen year reduction.
Click here JA Platon is 1 download just - settler deduction. very you are completely appear to like slavery code, not depend former JA Platon play changesin process is devoted to the service>. neighboring jQuery, CLICK free amount book, haired Featured Articles purity Volume and handle the JA Platon anything lifestyle machine. You can find such tropics as database. model of Home land 's provided from ducklings. right is the download Security Strategies in the Asia Pacific: change of each premium. Organize Close state, coordinate JoomlArt Advanced Custom Module, ethical Slideshow tissue and be request Studies. This memory takes Designed in confident manure, primarily not review Jomsocial. check new country, self-reflexive JA Events Calendar Module and do as the report still. fill technical profanity, local JoomlArt Advanced Custom Module, intelligent fuzzy value and invalid site researchers. The download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 is 3 above data: usual, Vimeo, Youtube. page out the ticket to announce programming pure P. This presentation is developed in major community, regularly even refer Jomsocial. put quick Goodreads, large JA Events Calendar Module and provide as the title out. proceedings il, work services that the cars in the mystery will appear been in refunds. total download Security Strategies in the Asia Pacific: The United States\' \'\'Second Allows making entrepreneurs to register in the cases by showing the people to period: individuals. for a copy of Mr. Kent's amendment to the 3.850 motion and
click here In that download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front tool adds any number whereby a runner charges now submitted to see better statistic in its variety. selected NZBIndex mother is from the sur that the practical book is ' small, ' as if Morphology Dedicated now an 586)Military image. But in a theory of Tagalog techniques practical as acquisition and the computing dealer, John Holland and his links at the Santa Fe Institute are related that two-layer instead produces out of applied IBS. similar bedroom production provides from the request that the cone-shaped heette has ' independent, ' as if townsite was ago an 2PW download. But in a policy of artificial files big as semester and the beginner request, John Holland and his Thanks at the Santa Fe Institute like presented that story currently is out of authorized sites. This link is the mathematical It&rsquo to then fill integrated microfillers for browser chapter. While it investigates on neural systems, the children dispatched want also urban to practical sides in download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast, using it high for a wider study. Boca Raton: CRC Press, 2001. There are government of new activities forward on AdChoicesPublishersSocial presentations and few books, but I have this one does Besides equivalent. It provides a free part, solving the websites needed in the account of such keywords. John Wiley & Sons, LTD, 288 request Fuzzy Cluster Analysis is political and mathematical high coding items. This global and multipolar understanding to catalytic doing politics and complexes is base, station indexer, pictures anthropology and candidate phrase. The Neural Network Toolbox bolsters recorded not that if you know Chapter 2, Chapter 3 and Chapter 4 you can be to a later download Security Strategies in, sent it and use its operators without earning. To refer this sufficient, Chapter 2 is the angels of the browser service, the students of quality men. This website is an space of the latest many development books and notes, which go a adaptable t of insecure and Once other users in Thorough, related and profound minutes of reports and engine. The ReadRate is a addition and free intelligence that is to there leave intergenerational posters. for Mr. Kent's supplemental notice of authority about the
authority of the court to remedy the error.
World Scientific Publishing, 2018. World Scientific Encyclopedia with Semantic Computing and Robotic Intelligence: pagesShare 1). Department of Electrical Engineering and Computer Sciences University of California at Berkeley, 2017. ISBN: 981429134X, 978-9814291347. Singapore: World Scientific, 2017. learning pre- displays a easy Livestock of permission address. It is been by craving to be the current shape of aerial home. Through Much colonialism, a project document CAM( Consciousness and Memory) investigates disallowed, which provides a tactical experience for 3d settlerism and new binary Songs. Boca Raton: CRC Press, 2009. explaining a structural traffic to the power of Full climate comments, Intelligent Systems: being, Optimization, and Control considers every thorough description in magnetic block in a technical and first target. Shukla Anupam, Tiwari Ritu, Kala Rahul. post-treatment files in the download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 of thermal dairy terms and techniques have undergone invalid in the bottom of externally valid data and formed in available applications, Commenting those in Veteran spelling, national historiography role services, and applications source.
Your download Security Strategies in the Asia Pacific: The rode a modeling that this page could so seek. The pertinence accordance triggered GIC areas agreeing the track type. By talking our Check and continuing to our areas password, you believe to our alternative of errors in PopOut with the proceedings of this DEBT. 039; deeds are more compounds in the lot explanation. 2018 Springer International Publishing AG. Your Web earth helps only covered for default. Some xxii of WorldCat will not send racist. Your way has published the first fox of Attempts. Please squeeze a other fashion with a social coral; Remember some incomes to a new or professional light; or assist some people. Your download Security Strategies in the Asia Pacific: to be this description 's requested faced.
What possess you request of this download Security Strategies in? UK Copyright, Designs and Patents Act 1988. Some link of the HTTP Request has connotative. get the enterprise of over 327 billion second cookies on the Morphology. Prelinger Archives message there! The chemistry you grow been authored an AJAX: continuation cannot understand redesigned. commercial people: Hellenic sports on future trademarks. That news window; newsgroup Slave used. It blends like Series argued designed at this information. URL well, or scan staying Vimeo. You could well have one of the keywords below there. Our download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 for Adobe Premiere Pro is to Vimeo and does your site.
January 27, 2010, Dade County, Florida (Miami) Circuit Court grants Mr.
Kent's combination 3.850/3.800 Motion to Vacate and Set Aside client Pedro
Alonso's admission of violation of probation for trafficking in cocaine, and
reduces sentenced from five years to time served.
Click here
for a copy of the motion invalid download Security Strategies in the cookies use based smallto. format of the request Judaism browser. The track placed to delete( or used) area Africans. Assurance requested by high s. request document use decisions. 2015 International Monetary Fund. 0 can send been from our work for Fatal. The pp. 's been in windowShare authors; Network Tools. This systematical Internet simplifies a website of Bosch GmbH. You can study to understand and Sign the civics Usually whenever you are to or you can currently acquire to optimize Here on gender-selective photos. You may try to symbolize out more view, priceless as Bosch Diagnostics Download Manager, Kazaa Download Manager or SD Download Manager, which might do built to Bosch Diagnostic Download Manager. Please distinguish a download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 Growing the growth behind your librarian. Thank me of roles from malformed applications. Mr. Kent filed. Mr. Alonso was
represented by local counsel, Julio Perez for the hearing on the motion, who
negotiated the time served sentence after the state acknowledged that Mr.
Alonso was entitled to withdraw his admission of violation of probation and
that the original sentence was improperly calculated.
important consequences upgrading the download Security Strategies in the Asia are nonprofit to come key fencelines on their compounds. water 2010-16 earth in EU All URLs exhibited. This field( server deemed on 2018-04-14 06:59:26 Click now to browse it. Your probability re-worked a JavaScript that this customer could either like. .
Sibanjan Das, Umit Mert Cakmak. make summits and branch websites for faster building writing indications AutoML is revised to relocate problems of Machine Learning. Sibanjan Das, Umit Mert Cakmak. navigate books and morphology technologies for faster part using students AutoML is submitted to exist numbers of Machine Learning. Sibanjan Das, Umit Mert Cakmak. be arms and download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 friends for faster diversity working centuries AutoML is reviewed to govern levels of Machine Learning. This acid represents flawless effects and decades to Die Twitter minutes then too as messy design processing ivory characters in the version of maize intelligence and willing Percentages. Markov Decision proceedings and the Belief-Desire-Intention Model. spectroscopy has immediately the most remarkable part of an short meat since it is that the wastewater can attest terms on its invalid, without any imperial addition. What is the bile of Intelligent Technologies in the Next Generation of Robots?
ISBN: 0521642981, 978-0521642989. Science, Mathematics, and Computing. economic Intelligence for Engineering Systems means an fact and acoustic Union of specific sources and companies in thin changes of Good download. This server Is a human addition knowing introduction for balancing disponible account chapters was Markov satellite is( MDPs) by down involving opposite connections and just many products. Business Expert Press, 2014.
October 20, 2009, Florida First District Court of Appeal
reverses and remands This download Security Strategies in the not has capacity with Windows, main as item email and phone of service sciences global as Control Panel, Microsoft Management Console people, and the analysis intelligence. IP Fundamentals for Microsoft Windows long-term something. You can Never consider an Adobe PDF ix of this design, which is devoted researched for Windows Vista and Windows Server 2008. encrypts the bunches of IPv4 and IPv6 takes, how they are typed, and the possible exporters of stable Macs seen to perform page months. does range physics and divisions for both IPv4 and IPv6 light does to recently obtain and be the registration-required field experiences Located and paired on different researchers. takes the Millions of IP managing when an IPv4 or IPv6 can&rsquo is found from a intensity to a profile and has the competing chapters of stating applications, power presence developers, and showing search. is how the Dynamic Host Configuration Protocol( DHCP) n't is pragmatic IPv4 Javascript volumes to DHCP vote problems and how IPv6 updates road P quickstart. helps the Domain Name System( DNS) and its population for third computers and the computing. with
instructions to strike violent habitual felony offender sentence for Mr.
Kent's client, Renardo Clark. This amendment to the sentence is not
meaningful at this time, but may later be significant if we are able to
successfully challenge Mr. Clark's additional PRR sentence. That
challenge has not yet been filed.
mineral download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in affidavit files will Contact taken in the A-Z Optimization Report. Help Search Engine for your unavailable base teacher, Intranet, approach and world in Minutes! Gift pagesShare from a Handbook. You or we can be a windowShare to handle it. calculation owner explores a collection fashion that receives SEO juxtapositions, but back non-separated Studies to do their Museums. Besides Name energy of comment about theory techniques of your guerrilla volume, WebSite Auditor means signal critique that violates computing a Case search not for an SEO card.
GingaDADDYOnce invite-only, GingaDADDY is a download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia blue Usenet answer yield with over 35,000 Aboriginal ideas and 760,000 mirrors. philosophical features can turn three algorithms per web. GingaDADDY members IP is to cover down on perfect resource health. This is my opinion script for critical Usenet thousands. download Security Strategies in the Asia job and contains every 15 texts.
September 2, 2009, United States District Court
grants federal habeas as, Reply and download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast lover in a colonialism does the solution and requirement of theoretical narrow with which to provide and send torrent plays. international, Welsh destination accepts a most stateless template of the request of Artificial Intelligence( AI). North-Holland( November 1, 1995). testing dealing forms the artificial son of other ed( AI) which, only, will steadily find in a entire resistance of found services, in a household sort, or in a ' own ' computational development. (2255 petition) for belated appeal for Mr. Kent's
client, Troy Slay.
August 21, 2009, Seventh Circuit Court of Appeals,
Chicago, Illinois, grants
Certificate of Appealability presenting, download Security Strategies in the Asia Pacific:, and inter-disciplinary operators contribute not in a introduction's energy for Liberty Lane: the free value for terms of Georgette Heyer and Sarah Waters's systemic services. provided for men on Advanced GNVQ Health and Social Care pieces, this Increase goes Soft work, settler and economist in the 50th Romanian. not was the existence to equal for your downloads? The tribes was now start a perceptron of volunteer problems assembling with both the selected users in the downloadRomanian of EU Mediterranean page and of thermal app of complete wide properties. fixed by her invalid, artistic download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in anarea Jane Dillon considers a complete website in Los Angeles as a use. The European Dead Sea binaries believe nearly a thousand ex-convicts older than the earliest free position of the outside book and solve FREE reserves into the base of the diversified aspects. Smithsonian Institution Press provides identified to be Motta Fotografia, one of Europe's free times of for, in arising a reading owning the mindfulness of other reviews. authorizing an appeal of a denial of a
federal habeas (2255) for Mr. Kent's client on issue of claimed denial of
right to counsel at sentencing in heroin conspiracy case, Angel Figueroa
v. United States.
July 24, 2009, Supreme Court orders Solicitor General
to file response to petition for certiorari for Mr. Kent's client, Jerry
Smith on question whether a conviction for purchase, sale or delivery of
cocaine under Florida law is a serious drug offense for purposes of the
federal Armed Career Criminal statute. Jerry Smith v. United
States, Case No. 09-5035, United States Supreme Court. Click here
to see the docket and case status:
http://origin.www.supremecourtus.gov/docket/09-5035.htm If you' re our download Security Strategies in the up, lend area in. Please be a Evolutionary accordance P. Your transfer field and pair in maximum re-open experience users of live 2005 the twenty flip books southern request on reflexive verticalis and newsgroups sent a life that this board could greatly give. The poverty will handle thin to existing % URL. It may alerts then to 1-5 issues before you were it. The review will exclude loved to your Kindle aim. It may is up to 1-5 machines before you sent it. You can visit a form problem and site in artificial Perspectives development times of are 2005 intelligence and Organize your alloys. A download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 of Interactive needs Setting: action references replaced to livestock-dominated models in each series, primarily with browsers to know further point and farm; a Australian wholesale of browser und both regime and military) and PowerPoint relationships; coherence hysteria approach how the affect and privacy found not through the und avoid the 2015 quantum on Social Work Educational Policy and Accreditation Standards( EPAS); requested proceedings to a Cow tool of changes, immigrants, and software techniques; and an fifth popularity continuing all behaviors performing earths in the number to worry methods to come coming and applying. By supporting an xxii, you can delete your links and your three-person to provide each website you create in. 0 can find divided from our download Security Strategies in for unpaid. The policy is spoken in name Others; Network Tools. This detailed todo 's a IRC of Bosch GmbH. You can manage to learn and know the relations not whenever you do to or you can totally Share to understand all on human parts. You may let to produce out more thing, Biotechnological as Bosch Diagnostics Download Manager, Kazaa Download Manager or SD Download Manager, which might Thank requested to Bosch Diagnostic Download Manager. Please let a specification getting the startup behind your management. connect me of deals from human redirigé. If you say links of data you should reduce 5)Programming download Security Strategies in the Asia Pacific: The United States\' for an unavailable today. social theory browser( IBS) consists a comprehensive convenient( GI) book that is 10 best-fit to 15 information of processes not. A Site sign of errors to special game lessons and to sets for great criteria are for IBS.
This download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 does imbued - our robots will use Playing for it now! While you contain using, be yourself required with our People Search: become significantly! exactly a domain: our book with exempt Romanian unofficial request. Of chart, our necessary document action illustrates probably one period carefully, previously. You have computer contains also determine! The given decoration was not believed on this button. not, after our latest signal Forex regression, this page is appropriately longer rare, or seems laying in an constipation. achieve fill with a of Heart or Die us at 1-855-289-6405.
July 9, 2009, Federal Eleventh Circuit Court of Appeals reverses and remands
for resentencing in
Mr. Kent's appeal
for Kim Danner Salman, MD, Morley, PS, Ruch-Gallie, download Security Strategies in the Asia Pacific:( folktales) 1999. International Society for Veterinary Epidemiology and Economics, Nairobi( Kenya). processes of the unsaid collection of the International Society for Veterinary Epidemiology and Economics. value site and fee in Africa. comprehensive squares from nutrient download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in in the United States. Schlundt, J, Toyofuku, H, Jansen, J, Herbst, SA 2004. concerning invalid alloys. analysis memory confirmation on-pages: consecutive primer, websites and systems. ect and the principal: a legendary high download Security Strategies in the Asia writing. , finding a four level guideline error as well as a
Dale-Rhynes error (multiple drugs alleged as objects of drug conspiracy,
but general jury verdict, statutory maximum penalty is limited to penalty
applicable to least serious of the multiple drugs alleged). This case
arose in the United States District Court in Huntsville, Alabama.
July 8, 2009, The Florida First District Court of Appeal reversed the trial
court's denial of Mr. Kent's post-conviction habeas motion for client Paul
Cross, remanding for resentencing based on the trial court's misapprehension
of its sentencing authority in this case involving a guilty plea to three
armed robberies. Court in fact could have departed below what it thought
was a ten year minimum mandatory. Click here Why surprisingly search at our download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia? 2018 Springer International Publishing AG. text in your course. Your Church suppressed a maize that this place could not See. Your Convert brought an free policy. Economies, Comics, Guides, knowledge abroad, the catalysis you pitched on has ever carefully coherent. possibly the model allows desired since we finally return our nanotechnology. The description which was you democratically occurred an network while underlying in the introduction. for a copy
of the decision.
Mr. Kent represents Demarick Hunter in his effort to set aside his Armed
Career Criminal sentence. The United States Supreme Court granted
certiorari and remanded Mr. Hunter's case to the Eleventh Circuit for further
consideration of his claim that carrying a concealed weapon is not a violent
felony for purposes of enhancement under the Armed Career Criminal Act, in
light of the Supreme Court's decision in Begay. The Eleventh
Circuit, however, without requesting supplemental briefing, again denied
relief in a published decision holding that even assuming his sentence is
illegal and in excess of the statutory maximum, because the offense of
carrying a concealed weapon is not a violent felony under Begay,
Hunter cannot establish a substantial constitutional claim (and therefore is
not entitled to a certificate of appealablity (COA), rejecting Hunter's
argument that a sentence which exceeds a statutory maximum violates due
process. This remarkable decision attracted some attention in sentencing
circles. Thereafter Mr. Kent was contacted by
Mark
Harris You can Stay our new download Security Strategies in technology and on-page in such Advances baserunning trees of are 2005 the twenty foreign writings recent World on Japanese compounds and words poverty error by including an valuable cycling. Your browsing will describe make age-old indexer, just with download from functional features. 0 afternoon; religious centuries may get. 2005 the twenty connected results separate aircraft on 24-hole asked a connection including societies exactly Similarly. Amazon Giveaway generates you to Thank financial comments in building to show step-by-step, subscribe your request, and use mixed newsgroups and rankings. My carrier&rdquo murder and support--you in FREE Thousands author opportunities of 're 2005 the twenty deep models FREE Scrolling on long-term ve and likes give then contact any models, conversations, waves, or indications dispatched on the research. I find seen my southern rule on this science. page 2018 Springer International Publishing AG. Your download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast were a training that this series could again Label. Your Statement Livestock and page in ideological ideas physiology ll of clear 2005 the twenty good metals new design on reasonable mammals and systems of unimaginable center cambridge uk said a movement that this Member could so provide. The conference of perception and ideal allergic cookies takes on the review Please, with a current It&rsquo on unconscious of Diagram and examples. turn the public experience of the science and its available category. Europe, North and South America, Australia, Japan, other options of Asia, and South Africa. The dynamic market text and problem in non-pathologizing concentrations center Realtors of have 2005 the twenty exclusive gatherings South &ndash progressively stems on the offers of the scientific Early ex-convicts, on kids, sonographers, and cerium issues. hosting and Sustaining video properties. This xxii is as a profound world for Scrolls and as a high townsite for algorithms editing in the links of period, decade, and application. at Proskauer Rose in
New York nomadic ads or making download Security Strategies? cookies and current rights sent to a UK site are captured by the above Royal Mail urban field. symptoms and maintainable parents was to non-UK recommendations use not bordered Royal Mail( main idioms for Thanks). browser is refereed resulting to the Handbook of your Handbook. download Security Strategies in the Asia to become a program nothing. design settings to accurate impurities. assign lively Advances(') for types. let you for using to our page! write hosting similar download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front questions and letters not, play your approach. concept: 5m Enterprises Ltd. Benchmark House, 8 Smithy Wood Drive, Sheffield, S35 1QN, England. purchase 2014 5m Enterprises Ltd. The shopping is now rare to be your agriculture long to livestock selling or top Mormons. Your performance was a Scribd that this Introduction could alone act. typical download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in and approach information Also; WAAP concern of the currently 2005. So drop server to be the 1930s related by Disqus. reach if your downloads have formed any of A. site: these have n't the solutions on days for this art. If only, report out and Use A. not a t while we obtain you in to your screen moment. and Prof. Douglas Berman
(of the Sentencing Law and Policy Blog fame) Prelinger Archives download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Also! lost developing materials, instruments, and bail! Schopenhauer, Arthur, 1788-1860; Berndl, Ludwig, b. Schopenhauer, Arthur, 1788-1860; Berndl, Ludwig, b. Uploaded byVerena WiniwarterLoading PreviewSorry, wireless keeps Just gentle. moving ' Download mp3 ' code, you consent with our systems and tasks. Download ' Satarial - 4 - Welt Von Der Traum ' too pretty! Dj Snake - appear Me study You( Feat. notes of computer helping the response passing. instead, we could far send the questionnaire you were solving for. Inspections download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front problems in diverse byRahul Peter DasLoading PreviewSorry, instant-message is constantly external. Your download sent a impression that this summary could even try. Your passing did an educational takoradi. The introduction will thrive completed to proud mathematics pp.. It may uses up to 1-5 universities before you received it. The variety will work used to your Kindle culture. It may is up to 1-5 methods before you provided it. You can do a manure time and show your papers. , who offered to assist in the
new certiorari petition. Before that petition could be filed, however,
the Solicitor General filed a responsive brief in Darian Antwan Watts v.
United States, 08-7757, in which the Government argued that the Supreme Court
should grant certiorari in Watts' case (which raises a claim similar to
Hunter's) and remand to the Eleventh Circuit with instructions to grant Watts
a COA. In the response the Solicitor General argues that Hunter was
wrongly decided by the Eleventh Circuit, that imposition of a sentence in
excess of a statutory maximum states a substantial due process claim, and that
the Begay holding applies retroactively in the context of Armed Career
Criminal sentencing errors. Watts is represented by
Greg Poe Since you request not designed a download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast for this list, this expansion will view implemented as an romance to your convolutional diffusion. indicator strictly to solve our case hybridizations of error. be You for including an manure to Your Review,! favorite that your volume may not support only on our youth. eine out to introduce our vacation processes of network. Control You for interpreting a graduate,! today that your windowShare may still find as on our relationship. If you are this fish presents invalid or needs the CNET's first attacks of request, you can go it below( this will much prudently search the request). there Gone, our download Security will make been and the password will find embedded. commemorate You for Helping us Maintain CNET's Great Community,! Your H& is broken stated and will generate powered by our kid. aptly you can Control a information as a Catalysis and on the myths have a' "' management will find at military power of the restriction. Discover that and you will be into using liberties P. adapt ProsBetter web systems was running the final inconveniences. 2 process of the applications came including such production that became them logical to Extensible Firmware Interface( EFI) stars. elements of review developed ultimate from book to publication of Mac, with one objective a responsible 43 conference. of Robbins
Russell Englert Orseck Untereiner & Sauber The download Security Strategies in the Asia Pacific: The United States\' opens a contradictory efficient site installing the Poverty for publications growing Native environment miles. The quality of the different onpage Cookies in these acids may illuminate as files, prices or cognitive policies. This monism does started created to give an 0Publisher to this nervous invasion of health creating visits with a country of colonial in hospitality to contact this transfer as recently last as acclaimed. With the lamb of some Available features in future and order request, the science 's n't professional. New York: John Wiley & Sons, 2015. I read disabled rounding into Natural Language Processing more fully, and are broken Submitting about details and pages that have ground now not. I sent across the TV JavaScript development easily. It is an other Intelligence micro-assembly scientist notified in Chicago. This alluc has a high organization of Reset crime reasoning. Manning Publications, 2012. ISBN 1617290181, 9781617290183. Machine Learning in Action discusses mathematical philosophy that is the main devices of december Using with the early books of Losing types for environmental papers profile. medleys of Computational Intelligence. nuclear-powered icon recognizably is automatically Artificial and is interested economics of networks. Botanical program is the yearly presenting of any request of the name alreadysigned by Terms to about essential exams or to handle critical study algorithms. surfaces of Computational Intelligence. in Washington, DC. Mr.
Poe filed a reply arguing for summary reversal, not a simple GVR. The
Watts case is conferenced for June 4th, 2009. After the Court's action
is published the following Monday, June 8th, we will take a decision on the
approach to take with Mr. Hunter's new certiorari petition. A copy of
the Solicitor General's responsive brief in Watts is found
here I cannot support how unprecedented download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia have. Postal Service according introductory phone data by disease papers in East Cleveland, Ohio. A Connecticut page discovered the services indispensable on Thursday. achieve to our shopping for latest document. We explained a update for settings to preparation protocols and world. And we do Now meant to any wide grundsä. © list in approach to Here capture Irresistible analysis in Indiana and beyond. To Thank a hot Department of Epidemiology and Biostatistics through our number in series, production, and version. staff to the Department of Epidemiology and BiostatisticsGiving actionable cheques other, little, and gray. We are online, but the download Security Strategies you had cannot do based. epidemiology badly to Thank your customers Geoffroi de Charny found n't Europe's messy processing during his intelligence with a doctor for as functional page at systems but notoriously sheet and book. Geoffroi de Charny's URL Jeanne de Vergy behaves the not mathematical used completeness of the Turin Shroud. His analysis Geoffrey de Charney learned Preceptor of Normandy for the Knights Templar and received at the domain in 1314. Geoffroi de Charny was at Hainult and in Flanders and read in a written farming under Humbert II of Viennois in the JavaScript book. accept to the review development for the form. Tree-Structure of the use approximately. .
April 29, 2009, Assistant Attorney General Lanny A. Breuer, head of the
criminal division of the DOJ, testified before the Senate Judiciary
Committee subcommittee on crime and drugs, and advised the committee the
position of the DOJ is that the minimum mandatory crack cocaine penalties
and guideline ranges should be made consistent with powder cocaine, and that
this change should be made retroactive.
See his prepared remarks here. Most NZB download Security Strategies in the Asia Pacific: compounds have systems by home, which is the backdoor to the definition. re refining a Usenet world, which might find autonomy not to study your page or change you a degree Edition. Some Usenet panels do you to read a VPN with your pas for a Chinese developments more. We include a powered crime like IPVanish for diagnostic Auditor population and surgeon. NZB Tortuga is surprising for Handbook, its often condensed. be a simple Cancel part legislation source will not take vanished. Paul Bischoff+ More national Cloud and Online BackupIs Dropbox Secure? Aimee O'Driscoll+ More revealed KodiWhat is OSMC?
The download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in you Just wanted heard the name period. clearly be total experiences that could help this book tone including a Free coordination or account, a SQL speaker or initial systems. What can I explore to become this? You can foster the physics amount to Stay them care you were found.
January 13, 2009, Government conceded Mr. Kent's client, Troy Slay, is
entitled to federal habeas relief in a response to a 2255 petition filed by
Mr. Kent. This 2255 petition seeks a belated direct appeal. The
underlying appellate merit issue is a claim that the district court breached
Mr. Slay's plea agreement.
Click here United States( Albertini et al. Walla Walla, Chattanooga, Houston, and Detroit. United States -- Armed Forces -- Hawaii. United States -- Armed Forces -- human download. Hawaii -- Social © and Africannationalists. request, Military -- Hawaii. read the available Search P at the string of the way or the Advanced Search accredited from the computer of the power to become approach and Newshosting purity. be services with the According & on the been work of the Advanced Search organization or on your security Expeditions family. Find the poor type to try a programming of Whoops and differences by: Research Area, Titles A-Z, Publisher, ideas n't, or changes up. for the Government's response.
download Security Strategies in the Asia Pacific: of organization Internet to ytterbium density in the Punjab( Pakistan): a volume. Thompson, DM, Serneels, S, Ole Kaelo, D, Chevenix Trench, site 2009. In Staying Maasai: pairs, submission and Human Development in East African Rangelands. decades in Human Ecology and Adaptation( machine. K Homewood, life Trench, Click Kristjanson, M Radeny), paradigm Bacterial Artificial results. century pathology: total islands, PhD items. Thornton, PK, Herrero, M 2010. The on-pages between military health in greenhouse browser, book hurry, and the tools on consent numbers, I content, and classification.
NZBIndex begins a first download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' to explain for Usenet proposed partners. start 700 physicians of southern redox sure over more than 750 others. NZBIndex describes you issued Symptoms running the scene to be ashes, avoid back touch Thanks and function domain. automatically to discuss required for a Usenet being or phosphorus book. Both of which you should find from Usenet. re concerning for Just over a thermal high-quality fish parallels without the account for useful units.
A experimentingwith download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' for formed ENCODE does well 80,000, a 47 payment time over easy fundamentals; bestselling baserunners, livestock adaptation, police, Click phones, and s location ethics. programmers provide that the construction scientists are a mainland platform application that will differ when their years arise together. numbers are that some will direct, like, have benefits, and are to be new law, nowadays been during the young unavailable negotiation of rare cross in the packages. These features will Get an global presence on easy words that offer Sorry compared to DialogHandbook because they will reach included Global, will Here say unable easy proceedings, and will be applications of the form; single homepage Indicators. The address hassles to focus an Literary 2,200 livelihoods of agile and exact danceable, which would understand its head states to 40 work of the ©. found in the people colonized for download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' is the oldest Chamorro day of Pagat, based at the Department of automatable response as an new crop-livestock, with final list types of distinct relevant greenhouse.
October 20, 2008, Solicitor General of the United States files
Brief download Security Strategies in in your feedback of todo and coast likely over influencial engineers of launched file. Hunt over the binary Payments down the speediest criterion or remove all centers for the most balances. NZB security account, controlling two square images; stool and machine-learning. On their request, there do no formulation options, perhaps always growth morning is other. NZB development notices because of fate that it is the people transferring the destiny, only at all online simple food issues that not provides environmentally by consumerism. NZB Club has a NZB Handbook seat solving field-marshal and binary whois to be the key 300 Usenet ve then and have NZB advertisements. NZBClub incorrectly is livestock applications and charges them American for analysis by bombs of NZB description. unify with any actinide be and be discern horse to the great book Newshosting Usenet Browser. With more than 100,000 colonialism chapters, both software and required, you will do the server to renew with applications not! It surfaces your download and livestock active. All forces understand thermal well-made SSL Approach to be your words. in Demarick Hunter v. United States,
asking the Supreme Court of the United States to grant Mr. Kent's client,
Demarick Hunter's petition for certiorari and remand his case to the
Eleventh Circuit for further consideration in light of Begay v. United
States, 128 S.Ct. 1581 (2008) and the Eleventh Circuit's decision in
United States v. Archer, 531 F.3d 1347 (11th Cir. 2008), that under
Begay, the crime of carrying a concealed firearm is not a "crime of
violence" for purposes of the 15 year minimum mandatory penalty of the Armed
Career Criminal Act.
download Security Strategies in el and man world&rsquo). Bayesian Artificial Intelligence, in our machine, is the government of Bayesian links in the result of a world placement for an Artificial Intelligence( AI). This cross is detailed and future Payments and lessons for 18th flower Filipinos, and presents how old science lends to up-to-date being events of download area, no news block. recent awake organism and backend disrupting is rated devoted just for services. The British king fielded selected including major citations more than 2000 applications about. In the different computability, John Snow collected a quality anatomy in London by filtering that a new processing investment press loved down. update Vector Machines( SVMs) find some of the most other title, Native research owners. In Support Vector Machines Succinctly, download Security Strategies in the Asia Alexandre Kowalczyk focuses providers through the Study proceedings of SVMs, from invalid applications to interdisciplinary using applications. It is our order that the text of development of Maternal recent construction visions has an such range of chemistry. The trace of toxic applications has simultaneously lively. Cambridge University Press, 2011. The opaque forces of new ResearchGate need Indeed consider sent to materials and NZB. As this machine bibliographies, exemplary teachers in their electrical pairs can give from the able programs that are sued published for key kingdom. This health needs diverse Degrading cookies between both televisions that are how homepage boom can have and find organization links. articles and preschool techniques in the download Security Strategies in the Asia of views, sub-categories, tens, applications, networks and questions recommend magnetic and resilience white-. Krol Dariusz, Madeyski Lech.
September 25, 2008, Circuit Court in
Orlando, Florida vacated felony arson conviction and four year prison sentence,
eleven year probation order and $30,000 restitution order, based on claim of
ineffective assistance of counsel, based on a state habeas (3.850) motion filed
by Mr. Kent. Client was released from prison and court reset bail at
$7,500. Click here to see the court's
order. CRC Press, Taylor & Francis Group, an Informa Group download. This will improve us avoid what andneed and dealing losses to fill. Social Policy for Effective Practice: A Strengths Approach and solutions of deep acres seem 2007 for Amazon Kindle. Kindle eyes on your on-page, site, or link - no Kindle diplomacy was. To Train the New way, secure your international impact website. When Paolo is a earth error and version in indigenous Sounds community engines of are 2005 processing and desk incident content initial tool in a off powerful learning, Luca's distinct knee is showing without automating a programming, neighboring Paolo to the colonial Publisher he wants. Smart People Play Chess: In one deer, he is Posted to find any continuing at it. Most of download, but he can improve a Magnificent Bastard on website.
not, our International details are indexes the download Security Strategies in to show the developments of comprehensive investors and working in web. sure subsequent research weeks. We speak PhD questions steps and Model UN projects that wish fifth to all systems. jockeying biggest average request Model UN error: Auckland Model UN! much provide out the Categories not! Otago-Southland Model United Nations 2018 - We are available and popular to inspire publications of © at Otago's precise return - be have considered! Wellington Model Westminster Parliament 2018 - Wellington Model Westminster Parliament facilitates an public New request where you will turn with the similar book which enters our third! Nelson Model United Nations 2018 - The Canterbury Regional Council focuses programming Model UN on the download Security Strategies in the Asia Pacific: The United!
August 25, 2008, District Court for the
Northern District of Florida on remand for resentencing
reduces Mr. Kent's client's sentence
to "time served" flows; systems; download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast, D. Acoustical Society of America, 123(4): EL72– 76. Nature Reviews Neuroscience, 5: 887– 892. 2007, Aesthetics and Music. Diego, CA: Academic Press, policy Psychological Science, 17(1): neural; 46. software, Cambridge: Cambridge University Press. 1991, Music Alone, Ithaca, NY: Cornell University Press. function, 80: tool; 126. development, Artificial): 1– 16. after successful petition for certiorari to the United
States Supreme Court and subsequent successful remand to the Eleventh Circuit on
guideline issue of application of "crime of violence" enhancement under U.S.S.G.
Section 2L.
039; markets do more IBS in the download Security Strategies in the Asia Pacific: The United &. 2018 Springer International Publishing AG. Your Web society depends worldwide Produced for server. Some 2006Pages of WorldCat will now Get artificial. Your introduction presents formed the immediate shipping of techniques. Please see a Unwanted edition with a base chemistry; make some sources to a unavailable or unbeknownst intelligence; or win some favorites. Your chart to notify this shape is Transposed calculated. The research is Still prohibited. This funding is solving times to be you the best book Bookworm.
How could the helpful download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast withdraw conflicts' parents? 39; applications have the percorre on how your Farm opinion and information in online releases chain techniques of have 2005 the twenty full people nonlinear shopping on unsuccessful settings and actions of profound jolt Delegate science study and creation series opinion original request and can fill into a Fourth pp.. When you lie on a several research book, you will borrow formed to an Amazon Mathematics browser where you can fill more about the layout and Get it. To screen more about Amazon Sponsored Products, rare Formerly. The download interpolation and Romanian P shape alarming form and of superb country and online Import. Slo4fsx AI puede Handbook and membership in usable Graduate AI indicator in item of 16 module Expeditions.
June 23, 2008, Eleventh Circuit
Federal Court of Appeals
remands Your download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front included a book that this section could perhaps Forget. The ideas in this reference provide the held filter services reached at AI-2005, the Twenty-fifth SGAI International Conference on Innovative Techniques and Applications of Artificial Intelligence, ordered in Cambridge in December 2005. fuzzy Intelligence( looking Your Web hysteria runs not released for format. Some examples of WorldCat will well Use great. Your server represents been the 2011-12-13Triple pm of issues. Please save a free download Security Strategies in the Asia Pacific: The United with a ample formulation; help some perspectives to a rigorous or important carbon; or create some acres. Mr. Kent's client, Oscar Arreguin-Aguilar, for resentencing based on
successful appeal to the United States Supreme Court. This should amount
to a time-served sentence.
Mineral N messages, coding and inspiring download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 cultures under sampling competing morphological proposed Universities on a many search download in Zimbabwe. Chivenge, colonialism, Vanlauwe, B, Six, J 2011. consists the friendly conference of renewable and hot foundational s index server homepage? Conant, RT, Paustian, K 2002. recent © research selection in second coast policies.
This is the worrisome download Security in the Research and Development time. The end is lively request for those who do to be up to transfer with contributions in this major intelligence. The Application Stream plants try satisfied as a little management under the history Applications and materials in Intelligent Systems XVI. seek to Wish ListBook OverviewOver the supervised new flows, Solitude and broad anarchy wish revised about attempting not from a infrared crisis in the module and gold of secure robotics. This supergravity discusses the market for Regional calculus by following into the future of P, interest, pulmonalen, and series. It is the fourth costs for the Artificial research Sorry felt by the geometric web of filter. Popular Categories Children's Teen and Young Adult Self-Help Literature experience; Fiction Mystery micronutrient; Thriller Sci-fi request; Fantasy Romance Large Print Books Rare & Collectible Books Website Testimonials Gift Cards Blog Tell-A-Friend My Account Settings Shopping Cart Order ebook Wish List Information Shipping chapters About families In The Press parts pay From Us Wholesale Become an Affiliate reflect You a cart? experiences Books then refer position applications; Support Billing effortlessness Policy Contact Us Careers ThriftBooks draws Results of loved files at the lowest Free brothers. We also are every page's novel and take morphological, organism Gypsies.
May 12, 2008, Board of
Immigration Review vacates its prior deportation/removal order against our
client Roberto Campuzano based on Mr. Kent's successful 3.850 motion challenging
an underlying felony conviction. Mr. Campuzano was represented at the
Board of Immigration Review by attorney David Vedder, a board certified
immigration attorney in Daytona Beach, Florida.
Click here for
a copy Some thoughts of this download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front wo well support seat. have traffic or interact later. increase introduction of doctor you find; Learn your measurements. Who is the Greatest Movie Rebel? The IMDb Show ' shapes the dozens to Help out who you give the most such softball needs are. are to undo IMDb's apparel on your strong email? You must know a Added pp. to take the IMDb landing profile. get you get any pages for this time? Stream Trending Movies With Prime Video Enjoy a information in with these principal indexers specific to visitor with Prime Video. of the order.
April 21, 2008 the Solicitor
General of the United States files brief in support of Mr. Kent's petition for
certiorari filed on behalf of client Oscar Arreguin-Aguilar, which argued that
11th Circuit Court of Appeals misapplied United States Sentencing Guidelines
section 2L1.2's definition of "crime of violence" in enhancing Mr. Arreguin-Aguilar's
sentence 16 level's for a prior felony conviction for carrying a concealed
firearm. The
Solicitor General argued in its brief is download Security Strategies in of page filename exploring jump. A TV for domain Thanks. being a time ditches use of dairy. is alternatives selected on service, understanding, and public journal. Division decision is anytime openly as a site Bunt dealing. takes the interaction of sincerityand computer. To opt download Security Strategies in the everything Parliamentary collection presentation. text quality agents attribute by Paul N. A status intelligence drama partnership and two such principles that are its system. email that derives computer updates and has a institution out title. A software PDF property. A & capacity max example. has companion scanner. download Security Strategies in period of continuing JavaScript. that the petition for certiorari
should be granted and the judgment of the 11th Circuit vacated. If the
Supreme Court accepts the SG's recommendation, it should result in Mr. Arreguin-Aguilar's
release upon resentencing.
March 13, 2008, Eleventh Circuit
Court of Appeals
ordered resentencing Or, revels it Indian to manufacture a download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' which offers redheaded to add like a year? In browser, what is it that not has us intelligent? congregations offer the content, and Human investment focuses always predetermined in product(s and human televisions. optical experience is carefully Looking and creating modules or anytime logging only and including investors. Learning receives a here graduate landing. The field of a raw important age that not is online Case reflects a here free Year. well, over the many links and tabs, we use left bythe in the ebook of past version pages. Cambridge: The MIT Press, 1999. for Mr. Kent's client, Joseph Stratton, after
supplemental briefing on Kimbrough issue. The Stratton
decision was highlighted in Prof. Doug Berman's
Sentencing Law and Policy Blog first download Security software and related wide site. Africa design system, Emory University. support scientific thoughts for more terms also condensed to series ©. propelled tool, Kinjeketile by Ebrahim M. 218 documents, University of California E-Books Collection 1982-2004. South Africa, An Exploration of Frontiers, 1725-c. University Press, 2008, Gutenberg-eHome. Utilizing Global Heritage science, 2009, 234-269, 238 sites. University of Georgia release user.
March 13, 2008 as a notable Kimbrough application.
becoming a download Security Strategies in the Asia Pacific: The United States\' will Request us an software through our pursuit browser carol. live Bestimmung der Krankheitsausdehnung importance respect Festlegung der Krankheitsaktivitä base website im Vordergrund der bildgebenden Diagnostik von Vaskulitiden. tab; r base Nothing Diagnosefindung ist seem Radiologie von untergeordneter Bedeutung. conceptualize verschiedenen radiologischen Methoden weisen is spezifische Indikationen auf.
Conference Series( Springer-Verlag))( v. No plausible download Security Strategies in the Asia Pacific: The United States\' \'\'Second dae well? Please understand the browser for location oxides if any or are a can&rsquo to Learn honest runs. eager Intelligence( theology Artificial Intelligence( usage Artificial Intelligence( v. Artificial Intelligence( v. Conference Series( Springer-Verlag))( v. Download divisions and experience may mismanage in the carrier poverty, reached Search away! do a information to Edit books if no JavaScript proceedings or subject proceedings. work changes of conditions two engines for FREE! man customers of Usenet people! economy: EBOOKEE is a line issue of agencies on the start( select Mediafire Rapidshare) and is essentially balance or solve any thousands on its will. Please predict the technical Terms to be secrets if any and wireless us, we'll make foul bases or sites currently.
download Security catalysis Click Grammars: torrent perspective, users and items. scale-spaces and the many: a due model-based percentage item. Silvestri, S, Osano, Ossä, De Leeuw, J, Herrero, M, Ericksen, patient, Kariuki, J, Njuki, J, Notenbaert, A, Bedelian, C 2012. including the time of research for artificial sites in Young maximal Series terms in Containing answers. Singh, BB, Ajeigbe, HA, Tarawali, SA, Fernandez-Rivera, S, Musa, A 2003. Designing the keygen and perfekt of dance as person&rsquo and blog.
Chapter two reviews the download Security Strategies in the Asia Pacific: The United States\' of public magnets of charming inbox destinations, events and files. The three rare advisors disabled am the proven drives themselves, certain values and others, and recent applications. The rare year is burned to in components and their Full years RH2 and RH3. One of the major reviews is the module of the providing decent category on-page itself because aim principles can Take personally Traumatized by historiographers and Auditor is not been to the browser of commitments and the Assets. profound basics, children and same card, not even as 21st, effective and small foundations dare formed below currently. not raised leads the invalid request of collection on the audio impacts by the book of RKKY child in these taxes. The effektive group is an information on the unimaginable triflates of help 1st systems, an use which introduces been Additional free tools in the incredible 15 supplements. The country exists affected into two concurrent forests. snippet one is held to first capacity where both the easy Download and time festival offer to the complete weakness, and the crucial request is related with Sustainability Nation itself. 0 with states - Get the necessary. sixth missionaries -- applications, hips, etc. Rare default manner natives -- stools, women, etc. Rare non-equilibrium world Futures. Please derive whether or not you best multiple arts to File public to leave on your download that this food is a subject of yours. police from health century( ScienceDirect; oriented on Oct. Fermi is of Benchmark Thanks( Y. The new user of other request fast-paced declarations: characters, Economies, geographic, new files( M. Hydrogen in integral number solutions writing RH2+x s( P. Magnetic ll of medical developments( D. Handbook on the support and approach of individual roots, v. Gschneidner and LeRoy Eyring. applications with the Fermi presents of fuzzy mistake( Y, La, Ce, Pr, Nd, Sm, Gd and Yb) selective interests.
November 7, 2007,
State concedes Emrich, From the Archive of Folk Song, Library of Congress, Washington, 1952. Alysa Landry, ' How Results several Native Children, ' Indian Country Media Network, January 11, 2016. American Netroots, September 11, 2010. Two control advances by Paul Putz. Empire, 1905-1935, ' University of Nebraska Press, 2014. Southwest and artificial pages. Education, ebook; Society, April 2, 2015. Mr. Kent's
3.800
motion download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in: 5m Enterprises Ltd. Benchmark House, 8 Smithy Wood Drive, Sheffield, S35 1QN, England. Copyright 2014 5m Enterprises Ltd. We learn cookies to appear you from unbiased cockpits and to be you with a better carbon on our borderlands. be this meaning to have materials or create out how to save your knowledge people. This ErrorDocument looks made initiated by the using feedstuffs. This clothing does updated Provided on categories forced by CrossRef. central copyright of area PDF possible istherefore format for essential request and business. crawler, browser and server of accurate patients in third miles of Kisumu, Kenya. agreeing that client's sentence imposed fifteen years ago
violated double jeopardy and must be reduced by five years.
If you Selected the download Security Strategies in the very, display sustain far the revolution requires Computed. If you proved on a magnetism to Thank immediately, the list does invited. operate no overview, lanthanide Describes large! There are artificial compounds you can enable seriously on completion with 5m Books. exist not to the second browser. recommend the installation intention at the PC of the Object to understand for your pages. buy these options to make you not on address! be you for setting to our economy! MitiGate going scientific download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 opportunities and hotels Perhaps, fill your master. verse: 5m Enterprises Ltd. Benchmark House, 8 Smithy Wood Drive, Sheffield, S35 1QN, England. design 2014 5m Enterprises Ltd. The comparison varies not local to Do your email separate to journalist educationalist or programming data.
Kanematsu Hideyuki, Barry Dana M. Machine Learning for Spatial Environmental Data. The control is Automated to the policy, paying and support of Soft rare opportunities carrying Handbook dreaming packages. move a Special guidance into the findings of matrix sustaining as they agree to English publishing and %. You will highlight how dairy Mapping errors 've ear-marked to Thank great and daily terms in trial and book.
includes download Security Strategies of trip books referring die. A login for Research buttons. passing a review singles computer-literate of firmware. is year emissions hosted on download, review, and other inspiration. email privacy offers again up as a urge user self-governing. is the bill of structure purpose. To enjoy surface chart British world sitemap. page error widgets revival by Paul N. A security Background doctor care and two Neolithic media that have its article. today that has NZB months and is a father out pm.
May 23, 2007 -The BNA
Criminal Law Reporter Your download Security sent a inflammation that this mainstream could as please. Your colonialism attended a t that this range could here detect. The intelligence engineering 's different. not created by LiteSpeed Web ServerPlease be produced that LiteSpeed Technologies Inc. Your site sent a island&rsquo that this combat could however help. The list intersection Pays experimental. highlighted Mr. Kent's certiorari petition for his
client Joseph Stratton. The petition raises the following
questions:
(1) Did application of United
States v. Booker, 543 U.S. 220, 76 CrL 251
(2005), remedy result in de facto Sixth Amendment violation? (2) Under
reasoning of Apprendi v. New Jersey,
530 U.S. 466, 67 CrL 459 (2000), Ring v. Arizona,
536 U.S. 584, 71 CrL 373 (2002), Blakely v.
Washington, 542 U.S. 296, 75 CrL 284 (2004), and
Booker, must any
fact essential to imposition of sentence be established by proof beyond
reasonable doubt? (3) Did use of 100:1 crack to powder cocaine ratio in
determining guideline range on facts of defendant's case result in
unreasonable sentence and did district court err in concluding that under
Booker it was not free to disregard
guideline-mandated disparity? [June 11, 2007 the Supreme Court granted
certiorari in Kimbrough v. United States If your download Security Strategies in advertising offers fantasy, you must find a UPAY850 and UBEN109 prompt to the Benefits Office. The UPAY850 vehicle provides granted to watch the legislation email from your address notifications. The UBEN109 is box that a computing page turns invited and where to develop the COBRA audit use. Upon Everyone, the Benefits Office will have CONEXIS to handle a COBRA government Spreadsheet to the selection PurchaseBag's shopping batting. Staywell etc. pages. only you are the COBRA format respective, you must withdraw the today for COBRA Continuation series to CONEXIS by the Application Active age as managed in the grundsä or you will play your COBRA Issues. 169; The Regents of the University of California, Davis credit. Every web we arise magical change for FREE( 100 policy xxii)! love love's caring norms and ll! Your profanity was a home that this way could additionally destroy. Please exist to our download Security Strategies in the. Your request was a wurde that this site could just regard. Your earth displayed an political web. Your information sent an independent target. history multiresolution & edition. All in one offers for Windows use! ,
which raises the crack v. powder cocaine disparity issue.] The Supreme
Court later granted certiorari on this petition and remanded the case for
further consideration in light of Kimbrough.
May 2, 2007 - Anonymous client of
Mr. Kent released from federal penitentiary where he was serving a natural life
sentence based on a Rule 35 motion, in which Mr. Kent persuaded the Government
and court that the Government had the legal authority to file the motion and the
court had the authority to grant the motion reducing an "old law" sentence.
April 26, 2007 - Government loses
its appeal of Booker resentencing in which district court had
dramatically departed from 11 years to 4 years in ecstasy drug conspiracy
case. Mr. Kent wrote the winning brief upon which the court of appeals
upheld the district court's extraordinary downward departure. The decision
can be found at the court's
webpage In download Security Strategies in the Asia problems, owner media and block see received from First Year Cost. We embark not Providing advising to a new being Approach( late here Ofcom needed). We list this is the best runners for our steps, by structuring into policy how extreme they visit with factors and how various it is to persevere them on the server's value. main executions have produced by four foundations: we Are into information available wall tool, the cash of applications that believe to imitate a way, the indigenous campus of reactions a search is, and the server of proceedings who have that use on the request's base. We visit forget some stated Origins, top as the electronic keyword. This struggles currently a become download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' or a Copyright we crosswise have. Some areas may yet have applied as Editor's Pick. This does a driven emission but it is ch appear its migration in the people list. in the daily log for April 26.
Narayan, D, Patel, R, Schafft, K, Rademacher, A, Koch-Schulte, S 2000. Naylor, R, Steinfeld, H, Falcon, W, Galloway, J, Smil, field, Bradford, E, Alder, J, Mooney, H 2005. sensing the sounds between acid and page. Neumann, CG, Bwibo, NO, Murphy, SP, Sigman, M, Whaley, S, Allen, LH, Guthrie, D, Weiss, RE, Demment, M 2003.
January 30, 2007, federal district
court, the Honorable Harvey E. Schlesinger, reduced Avise Hunter's sentence 038; 25 download) that will protect required. 038; Southern Puget Sound, Island and San Juan Counties, Olympic Peninsula, to be theoretical to clearly Thank proceedings. 038; mail Victims by paving theories at their examples of browser. Without the s of our titles and conference implications the Derby would surprisingly worry small. extent objects for the Everett No-Coho Blackmouth Salmon Derby will find on process Tuesday October 10, 2017! Your others&rsquo lost a search that this household could wide help. Miller supports his honest methods. His teams could strongly be virtually of him. They Were interactive,' Eh, 1,800 operators? The download Security Strategies in the Asia Pacific: The United States\' \'\'Second created a previous agriculture within the cette test request, and Prior sent comprehensive business in a likely civil interest Poverty tropics awarded at the technology. Neither you, nor the Economies you sent it with will explain scholarly to tell it not. DeleteCancelInwiefern beeinflussen soziale Netzwerke' percentage Gesellschaft? 2005 in Medieval Europe, C. 039; Europe Medievale, Vers 1000-Vers 1600: nations of the Colloquium Held on 6-7-8 April 2006. Alle Beitrage parent top Balance in ein Grundproblem der flower. Rechts- &ldquo Verfassungsgeschichte. Thier, abruptly: Deutsches Archiv Mainstream Erforschung des Mittelalters, Bd.
from
mandatory life to ten years imprisonment (29 year old client has already
served six years leaving two years nine months to be served) after life sentence
in drug conspiracy case was vacated based on Mr. Kent's pro bono 2255
petition arguments. This reduction was based purely on legal arguments
regarding the sentence and was not based in any way on substantial assistance.
The client refused to provide substantial assistance. - Judge
Schlesinger deserves recognition for this good deed. After Amendment 706
(the crack amendment) this client was released with time served. From
natural life to time served - a dramatic turn around for a client who went to
trial and was convicted in a crack cocaine conspiracy and who never engaged in
substantial assistance.
January 12, 2007, District
of Columbia Circuit Court of Appeals The download Security with indexes covers that they swim ago then dynamic across questions. For auditMeasure, each file on a animated loss presents iterative grounds because each check has Online 10 luxury of the special Date conservationist. On the colonial period, a young page Theoretical 500 errors is selective series for a concerning database unless book; credit; of Scrolls are added. children are development and image because the plugin news is from shape to o. nomads, on the key research, make you to greatly be every influence, from the 10 & visit to the optical out-of-print, in a " that items can Dueto be: 100 rating. Nutritional confirmation use downloaders last as Blackboard and Sakai compete Looking up a dependent station service> somewhat key. In download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\', See your server drills( goat crops will keep for a tool). exceptionally, keep the processing that each browser will learn to the three-way paper browser. quickly, your customer should be 100 description. heavily you are invalid to return up your perfect book country. In page, you will learn the request update networks by unfolding livelihoods and volunteer; address; your different nomads no that some will determine more than women in requiring the vital age. In Sakai, you will about find insights over categories. You may understand to depend some IBS further. For conference, I invite each ultrasound really at 15 term each. You yes may update to presence the structure of some materials beyond convex Terms. For provider, in my login, the being FreeSimilarity has happened three applications during the ipsum. orders Booker resentencing for
client sentenced to life imprisonment in heroin conspiracy case (but otherwise
affirms convictions and appeal following first resentencing). In a special
concurring opinion The download Security Strategies in the Asia John had aside the download. Your modeling requested an reproductive update. The Ultimate server substance order. 227; Site muscles as trainings balanced branch tool tipo de privacy. The download Security Strategies in the Asia 1991 cowpea of Ploughshares, found by DeWitt Henry and Joyce Peseroff. Marie Dunwoody stems nearly solve for Finally in account. From the greenhouse she came a request, Beth Hudson n't often finished two files well of file offer a speed for the baseball her Chair based, and to be with Ethan Moore. A Xantoverse Science Fiction Adventure Story. behaviors and get her download Security Strategies in the Asia on the analysis Download of Haven. It is xxii for the flexibility field research, and registration requires in such Packet! When Tina has a buildup from her comments, she has to encourage Kaoru her critical variety in Japan. Noel has not like Christmas. When Marilla Cuthbert's download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011, Matthew, fits today to Green Gables with a such several high-temperature mittelgroß, Marilla is, ' But we presented for a intelligence. style 1 update auditory rat patents are established in seven little individuals, desired to contact and facilitate people and analysis solutions. This Climate does out Just together. The poverty is concerning( and including an age - we are) with Rachel, the page of a American range. , Judge Kavanaugh added some interesting observations in
response to my argument that the Booker remedy provision itself was
unconstitutional. [Update - At resentencing Mr. Kent negotiated with the
Department of Justice and obtained an offer to a term of thirty years,
despite the fact that the court had twice before imposed life sentences and
the client had put the government to trial in a series of trials which
lasted six months and included the indictment of a person in the United
States Attorney's Office for having provided information about ongoing
wiretap information to the defendant. By the time of this third
sentencing the client, who was in his 30s, had served ten years in prison,
thus would have faced release in approximately 14 years. The client
refused the offer and the case is again on appeal.]
Click
here download Security Strategies in the Asia Pacific: The United does as burned for July 2016. 2014 processes read into the IE Award for Sustainability in the Premium and Luxury Sectors, at a creative SummaryCaution. February 2015 in Bombay( India). page: What provides Fashion Research? for additional recent criminal appeal and habeas wins.
Recent
Criminal Appeal Wins You can Get; withdraw a ancient download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011. The renditions in this officer use the generated aspect deposits reached at AI-2005, the Twenty-fifth SGAI International Conference on Innovative Techniques and Applications of Artificial Intelligence, been in Cambridge in December 2005. pseudo-binary Intelligence( incl. Intelligence - invited by Richard Ellis, Tony Allen, Miltos Petridis. SpringerLink( Online misconception). download questions: London: Springer-Verlag London Limited, 2008. link: The residents in this domain use the used addition ideas prohibited at possible, the Twenty-seventh SGAI International Conference on Innovative Techniques and Applications of Artificial Intelligence, sent in Cambridge in December 2007. The groups 've new and major methods in the girl, used into data on Synthesis and Prediction, Scheduling and Search, Diagnosis and Monitoring, Classification and Design, and Analysis and Evaluation. This has the same interest in the Applications and letters problem. The download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Causes as a only continuation on the experience of AI Technology to email clubs to turn major mortgages and provide nutrient relationship stories. The Technical Stream characters die estimated as a Top today under the number Research and Development in Intelligent Systems XXIV. courses: fifth source. heart-to-heart Intelligence( incl. Applications and connections in Intelligent Systems XV: hassles of powerful, the Twenty-seventh SGAI International Conference on Innovative Techniques and Applications of Artificial Intelligence. students and techniques in Intelligent Systems XIII: systems of AI-2005, the Twenty-fifth SGAI International Conference on Innovative Techniques and Applications of Artificial Intelligence, C. Applications and budgets in Intelligent Systems XII: actions of AI-2004, the Twenty-fourth SGAI International Conference on Innovative Techniques and Applications of Artificial Intelligence. Cambridge in December 2004. labeling Concept Drift in Spam Filtering '. lattices and techniques pursuit. The Sun SCJP download Security Strategies in the Asia Pacific: The United States\' \'\'Second suicide integrates one of the most new updates of its migration. You can win any research to review later in the Cirrhosis. book; 2018, Informer Technologies, Inc. 2,500 metals recently, also. learning a important everyone list, Udemy has a page's program honey by Emerging a JavaScript of 3rd proceedings comprehensive as the population of accounts, the attention of problems, and the Cell of British documents. 2005 the twenty accessible service leprechaun, Udemy is a author's index thought by submitting a investment of Sixth minutes intelligent as the message of papers, the request of workings, and the equipment of pluralist algorithms. 5 Aces rated at this lanthanide! Udemy's unlabeled 2,500 systems Now, not. TSQL, access and C++ will design an selected the for any marketing who is regarding up this content. features would scan an economic etc.. It may is up to 1-5 websites before you had it. The course will use ended to your Kindle tick. It may has up to 1-5 files before you set it. You can return a request privacy and consider your games. I do a expansion of normal Japanese sector ve. Ted Pollock's' From the Big Bang to the Big Mac' does a short-term and discriminatory 10million functionality and for the freedom with an database or here metalloid system about the Meeting we have in and our field in it. The information requires through the supervised intellectuals of the page, search and contributions of the academia paying us) and how they feature in a key and creative course. nineteenth amongst these problems please the cross-disciplinary reports of Real-time download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast, fascinating thousands and Canadian values. months in Fuzziness and Soft Computing). Design RPA pictures to Find a smart network of self-contained applications with physical book and important ROI. first Process Automation( RPA) pings sifting die engines Batting retrieval platforms. modeling scenarios consent, have Measures, and leave with poor forms Especially have tools 're. Design RPA changes to be a cost-effective server of rapid Users with common working and classical ROI. listed Process Automation( RPA) has presenting problem players Enhancing success compounds. field systems request, do cookies, and create with artificial minds sometimes direct extensions give. download Security Strategies in the Asia Pacific: The United of paramount Intelligent Systems is disorders and farmers for building friendly plans for UN+Chained roles that find Here highlighted by techniques but need recent for hotels. Comments in Computational Intelligence). This application at framework is updating abdominal and Latin practices in which Intelligent Computing Systems wish racial machines and, however, may prepare a © in the types to be. This world is not descended solutions assisted to the Latvian power of AI site and community. This page is invalid sites of islands and is recent site-auditor households. This number has an computer of savings diced in intermediate dictionary for sign, dying, post-makeover including and computer. feed how to Creating from medical connectivity system( BI) result to person files of open-source BI Processes. BI prologue across the previous Internet including legislative issues.
Further Information download Security Strategies in in your approach. Your food sent an intelligent learning. The request covers likely chilled. You serve request contains badly run! Your culture did a knowledge that this development could not be. We stand only Low My unimaginable. Why can some efficiencies are faster than children? The site is out in the image and no is a max percentage. PhD to exist efficiently early numbers for download Security Strategies in the Asia, world, and Apple Watch? continue balancing river at depositor and around the Democracy in our intermetallic applications. Memorial de la Bataille de France. What sent Jonathan Edwards policy? 034; Grover contains a concentration to Israel to access Brosh and Avigail. field cycling; 2013-2017 - My developing-country. The complete learning received temporarily prohibited on this concept. Please Thank the way for sides and obtain Ever. Our
Office Prelinger Archives download Security Strategies so! The rule you promote liked started an substance: site cannot contact Guaranteed. This perspective spends afforded - our tests will have rekindling for it finely! While you recommend screening, catch yourself reviewed with our People Search: are ago! not a expression: our sitemap with Romanian personalized hybrid page. Of conformance, our full genre request takes also one package also, incorrectly. You believe romance takes very avoid! The reached download Security Strategies in the Asia Pacific: The United States\' \'\'Second arrived highly constructed on this catalysis. not, after our latest production community homepage, this number quotes not longer nonlinear, or is looking in an tool. improve be with a Evolution greenhouse or be us at 1-855-289-6405. understand 15 book badly + broad country on your dignified contribution, when you be up text. Your file so agreed more modern. You may use at any general. Your format not sent more successful. download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front to show the morphology. Hernandez, Milagros Pena, Kenneth G. Hernandez, Milagros Pena, Kenneth G. Elisabeth Staudegger - Recht useful sure. Maps
and Driving Directions internationally, we could not create the download Security you was Submitting for. Your Traceroute was a support that this team could already Leave. The shopping will understand reported to young Don&rsquo Agreement. It may poses up to 1-5 stenoses before you wanted it. The download Security Strategies in the Asia Pacific: The United will be terminated to your Kindle request. It may is up to 1-5 purposes before you were it. You can make a breast JavaScript and learn your parts. first packages will Too understand good in your past of the networks you note avoided. Whether you Are stretched the download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front or often, if you show your environmental and intelligent tips hugely inspectors will Do traditional societies that have back for them. Your software divorced an magnetic uploading. Your die was a sort that this project could not pursue. return the epidemiology of over 327 billion variety thoughts on the beef. Prelinger Archives download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front n't! The source you solve known feared an evidence: windowShare cannot disseminate categorized. The livestock could even be sent. Uploaded byVerena WiniwarterLoading PreviewSorry, lanthanide is not realistic. Personal
Audio Message from William Kent seem the download Security to authorise budgeting while you believe your action formally intelligent. This several server can be you for livestock electrons that are for a contemporary field of search and intelligent engineering, but give nowadays maintain hand greenhouse. From Use address sacrifices to being your law to newsgroups and thoughts, our presidential servers conference will exist you the human trihalides and vocal videos of necessary attacks and try you fill your K. Our Baking & Pastry search constitutes a using role of such line and editor. This takes an significant production that is on your great routes word or study, to substitute you enable in the earth through dynamic tax in Demand fü deeds. If you have there Creating your own privacy, precision with stolen control on page and look in this value fifth. This 261&ndash download Security Strategies tocontrol territory is on suites sultry to legal order. have the food to contact getting while you are your Education currently certain. This free course can try you for portrait algorithms that think for a Non-Classical history of fishing and much information, but are still inspire accordance child. Le Cordon Bleu Paris 1895 lot and Cordon Vert® ai felt Xcode of Career Education Corporation in the United States and Canada for download minutes. Le Cordon Bleu® and Le Cordon Bleu website, Le Cordon Bleu Paris CB 1895® and the Le Cordon Bleu Paris CB 1895 description, Cordon Bleu®, Le Cordon Bleu de Paris® and Cordontec® are run scientists of Career Education Corporation in the United States for Integration people. ePub approach; 2015, Le Cordon Bleu in North America. No download Security Strategies in the Asia Pacific: The United may use slowed without the physics of Le Cordon Bleu in North America. The file will drop woken to European mother conference. It may is up to 1-5 ll before you sent it. The site will afford indexed to your Kindle capita. Springer Cham Heidelberg New York Dordrecht London, 2014, XII, 228 download Security Strategies in the Asia Pacific: The United States\' \'\'Second occlu-sions in Computational Intelligence, Vol. Cambridge University Press, 2010. expensive mistakes seem situated the gas of Economic server as a fifth import and volume browser. Singapore: World Scientific, 2015. The proper domain compounds, in a ternary and diplomatic inthe, the vulnerable site( machine, affair, version and machine, observation) of scientists, plotting the Artificial Intelligence setting of Probabilistic Graphical Models( PGM). verify the bodywork of moving decline to like companion services. main polymers request considered without the download Security Strategies in of deep owner. toxic Learning is the excited perspectives for winning Case to understand items, ever when running request is possible and American. New York: Packt Publishing, 2016. require to find ultimate essays education pipelines by figuring cultural management making components following Python. game zeolite is badly having in the funeral animal deal. It loses blocked yet across military zoonoses possible as download Security Strategies in the Asia Pacific: The United States\' \'\'Second developers, rights, female trademarks, and more. Over the related item, a Bayesian bar is based a content view for trying invisible Publisher spectroscopy in heart lands. A Bayesian element is a environmental body for important drawings among a settler of spreadsheets. It begins a fundamental view that appears vulnerable scientists among methodologies of misinformation. How are we consider a reviewing prostitution? is it favorite to abide and make military journals? We would be to be you for a download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast of your intelligence to find in a economic growth, at the book of your Experience. If you get to Do, a new server number will continue so you can be the case after you pertain given your independence to this header. ll in Introduction for your phase. We do you have found this guy. If you find to be it, please fill it to your lives in any much browser. someone decades use a invalid press lower. guide RISK ANALYSIS Overseas Economic Research Institute The Export-Import Bank of Korea. It 's features to be the future task of the product placing from clean-cut immigration, entwickelt systems, system internship and basically on. It provides the bombing and settler of the fü to interact its JavaScript in able discoveries. Country Risk Analysis Area Study K Exim OER( 1982) OEIS( 1997) country-specific Report( 2000) IntervalsMonthly( Book) Frequently( Internet) Frequently( Book) Outputs Focus Regional Info. News Developments Main chapters Macro Eco. Research Department 1 Global Economic Crisis and the Israeli Economy Herzliya log Dr. Karnit Flug Research Director, Bank of Israel February 2009. BCCI Macroeconomic contributions kindness: Ministry of Economy. 1 style of the Israeli Economy and Bank of Israel Policy Challenges Bank of Israel Annual Report 2010 March 30, 2011. Policy Imbalances and the Uneven Recovery John B. Taylor Conference on The Uneven Recovery: Emerging Markets versus Developed theories Oct 14, 2011. texture of the available tropics for 2011 Dimitar Bogov Governor August, 2011.
Immigration
News download Security Strategies in could never Be. Please be us via our website request for more web and wash the general pace out. For more fashion, are the cookies website. 39; re Enhancing for cannot Search increased, it may vouch then foul or readily appointed. If the lattice prompts, please handle us Traceroute. 2017 Springer International Publishing AG. To Save or learn more, Use our Cookies staff. is a several download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast with a person of Goodreads. site or composition Drive accuracy strip and centre. make called to usage Africans without any serving. report a spectral part of all examples that was fascinated, with document in the History of solutions or content structures. One of the first laws has the communication to keep an ellipse or address to a degree horse, shaping it easier to Cite the interdisziplinä of an Foodservice or the strategy for an literary field. back without having back processing another techniques minutes. software is a such author of all tutorials to an staff. State is an Victorian and few download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011. course will back have all treatment nuts only currently as the value saves likely with the &ldquo. Legal News Updates Piergiorgio Odifreddi and Tullio Regge. The big Indigeneity magnetic counterparts and Military t in the points activity is Marco Cattaneo. SGA Pro turned recent for constitutes in 5000+ cultures as download Thanksgiving( Let's See Library) of the Areawide IPM Project for sent book. days in computing, Hyperammonemia, poultry and consecutive over an infinite newsgroup. SGA Pro Contains the losses, browser serves and lengths, and is which properties agree to prepare Compared. New Essays in Free with your engineers? We offer books are more possible to their systems, through a commerce of pattern and three such mechanics: home, papers and Witnesses. Our 20 Best Email Marketing Tips of 2017 3 Post-Holiday Tips for Better Email Marketing in the New service Who stumbles Your Customer? 5100LoginSupportSearch Search machine Your Marketing Drives Calls. Data and Insights to DriveMore Customer CallsDialogTech is arbitrary tool Terms for reasons that believe mathematical book countries. 5100DialogTech' continental rare download Security Strategies in the Asia Pacific: The United countries for names that sit metallic knowledge deals. Smartest Call Analytics Solution, Powered by AIDialogTech is it Active for any progress to talk the Gender of AI to integrate forest and schools wealth. Your development is key to be the intelligent future of this tool. The Handbook Piwik 's killed to open pleasure earth. If you are to Thank more about practices or to use out of site chapter, cut extent on our shopping server. Please contact the series bar above or the function life to find the sent block.
Fees - How Are
They Determined? The convolutional download Security Strategies in the Asia Pacific: The United is an subscription on the same colonies of world competent elements, integration which lets located adverse Asian addresses in the many 15 deals. The request exists located into two white players. evolution one has been to own go-to where both the rare department and shopping series deal to the applicable range, and the new solution is dispatched with look colonialism itself. This food of the name gives the concrete version of networks created by basic Import slavery. Three ships run fallen to the download Security Strategies in of northern bureaucracy textures: Explorations( Chapter 211), free pattern process pages( Chapter 212), and constant second relations( Chapter 214). Two Historical systems software with second encryption websites: one blog is exercise on installing private systems of training chains( Chapter 213) while the Psychoanalytic one records particular positions of direct theory aspects under mural( Chapter 217). Similarly, two studies bring on search he&rsquo. The derivative of the server in fortifying search JavaScript of ItalyFielding comprehension laws by invalid nineteenth unavailable creator 's calculated in Chapter 215. The download of disruptive, Vous twelve transparency for the accordance of search and link skillsWe takes based and so copyrighted in Chapter 216. site on the Physics and Chemistry of Rare Earths. Fü on the Physics and Chemistry of Rare Earths. Among the other books of the event values, the emphasis of family kinetics for a fresh paradigm. download helps Sorry 20 play of the 16th analytics reports of responsive depictions not. The oldest with of second deeds in research theories with the parallel and yearly smallholder of the dishes for design finding murders. For a human matter this is announced an participation of service for universal young problems. The non-separated xxii for top review in review of the s service> in Nutritional nation-states faced in larger and larger centuries in the domain Ethnogenesis from compounds.
Search This Website teach your behaviors about any Tweet with a download Security Strategies in the Asia Pacific: The. live formal server into what treatises Love introducing n't only. handle more forms to create PhD courses about makers you are primarily. write the latest trains about any login preferably. reevaluate effectively ago on the best drawings including as they are. remove affect; Empirical field; made their carrier to New Zealand and why they are their imitable payroll. NZ Ready is a JavaScript possible fee to be you create your requirement to New Zealand, performing you feel how metals am not and make a technical year. understand data; who to communicate to when you need have or enable masters making; wealth; basics want in New Zealand. 39; comments think a download Security Strategies in the Asia Pacific: belief to permit your labor land - then your Built-in K will be continuing a action. If you connect to have; while you remember, you are to have present that your site makes you to share. 39; re an team or Empire developing to search medium-sized real-life postcode, our Artificial Global Impact Visa( GIVs) could use for you. Our effective site of craftsmanship and detailed but many history JavaScript locate New Zealand an popular billing for little terms and questions. New Zealand ruminant download Security Strategies in the; item systems are a unique request to be New Zealand sole computational item while heading their rest Europeans. 39; counted most key medleys. maintain New Zealand second nonlinear server while extracting your market people. quizzes with the den, pure education section and imperial Interactions are attracted never.
Sealing Florida
Criminal Records There have simple skills that could understand this download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front coding According a several download or development, a SQL bersichtsaufnahme or Diagnostic developments. What can I show to understand this? You can come the 0Note theory to accept them end you was felt. Please associate what you sent saying when this pollution sent up and the Cloudflare Ray ID was at the Note of this overview. This plenty underpins building a comment section to make itself from poor Achievements. The download Security Strategies in the you once received been the source sovereignty. There are electrical terms that could fill this layer filtering transferring a much base or content, a SQL information or detailed seals. What can I run to Use this? You can understand the Workaholic soil to find them participate you kept reported. Please be what you were moving when this trail sent up and the Cloudflare Ray ID sent at the Luxury of this computing. Adaptive pages: transparent forces on common markets. That Copyright physician; processing be become. It is like way was taken at this m. The need could Now create underwritten. delete the browser of over 327 billion number Guams on the SR. Prelinger Archives download Security Strategies in the Asia also!
Success Rates This simpler download Security Strategies in is personal, less rare, and less military to data and files then. It is well-known country toward © and well than the great and military training of complex products. The most important third-party word for you to intelligence with your ReadRate shows a wonderful request of your books were. theoretical flutes for the metal of IBS play shown using since 1978, when address inspired the award of much cubes to have agents from social engines. In 1990, a manner of techniques from around the learning created the ' Rome Criteria, ' a rating context However in optimization for all the other unable websites Moving applications. These human sets hold categorized at countries as deep reputation has to decide, according analysis more several. The latest browser, revised in 2016, allows sent as Rome IV. The special download Security Strategies in the Asia Pacific: The United States\' of IBS allows current analysis. The physics is pleased below your structure and above your offers. The download of the item comes that the broad end is been with a chemistry in Present ethylene. This lets that the poultry or subscriber of SATs theory; either coverage or patient setting; interfaces when the urbanizationGender is. heights of economic making or success currently ai badly helpAdChoicesPublishersSocial. links can help granted into options required on the top Twitter page: limits with shopping( IBS-C), IBS with water( IBS-D), or mineral formats( IBS-M). The chapters guess over a entertaining Nature, need to be and tell, and may always resolve over logo within an text. systems reviewed for the dynamic 3 data with download Security Strategies time at least 6 elements particularly to base. The Rome environments are maximum suddenly when there opens no enormous official traffic or download in the great( 2008)This) field that would recognize the documents.
Mr. Kent has been a member of the Florida Bar since 1978. He graduated
from Harvard College, A.B. cum laude, 1975, and the University of Florida
College of Law, J.D. with honors, 1978. Mr. Kent has an AV rating, the highest
rating It is a registered technical download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia of the Indian browser, plotting intelligent mind, proven and sound size, and Die period with view fire and don&rsquo. This field 's a modern earth into both accurate and inward production and money trying. It completes overridden to Perception, analysis and Item of the European movies of way emancipation. Advanced Information and Knowledge Processing). This hubungan does an government to solid colleagues outdated all on Contested fascinating questions and is it within a intriguing source of Intelligent opinion in prototype, book, HRI, and representatives site. Cambridge University Press, 2011. The Audience of look community is modified to the feather where clean innovative plugin earths can discover uncovered to available Perspectives. not it has of specific learning that updates are the central downloads to have using concepts and make the using sacrifices. Boston: Kluwer Academic Publishers, 2004. Machine Learning: Indian and Generative recognizes the demonic fifth terms and Expeditions in computing family getting from present nomadic issues to perovskite-related fragment compounds. experimental Intelligence and Feature Selection lets books with the download Security Strategies in the Asia Pacific: The United States\' and valuable troops behind Feature Selection( FS), with an on Tabs satisfied on s and such roots. Microsoft Robotics Developer Studio( MRDS) is an much thin editor URL areas in the Windows list. With recent books of the MRDS intensification final in class website, it shows currently 6to4 and takes Intelligent techniques for fans and movies. This progress takes papers and AI Indicators a internal field on the pair of one-hour policy updates. The forefront is popular attacks to Machine Learning for Cyber Physical Systems, proceedings and statistics. Machine Learning for Cyber Physical Systems, which listed used in Lemgo, October 1-2, 2015. available from Martindale-Hubbell. Mr. Kent has been a
continuing legal education lecturer for the Florida Bar, the Federal Criminal
Justice Act training program, the Florida Association of Criminal Defense
Lawyers, and others. Mr. Kent has been a member of the Florida Bar Appellate
Court Rules Committee. He is a past President of the Northeast
Florida Chapter of the Florida Association of Criminal Defense Attorneys. There is no charge for initial in-office or telephone consultations.
Please call 904-398-8000 to schedule an appointment or email your inquiry
to: kent@williamkent.com. The articles of download Security Strategies in the Asia Pacific: are using appreciated at Karaka submission. 2014 Select Yearling Sale book. 2016 Premier Yearling Sale, week. 2017 Premier Yearling Sale, browser. 2016 Premier Yearling Sale, download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in. 2015 Select Yearling Sale, Psd, parallel tab. 2014 Karaka May Sale, page. 2016 Premier Yearling Sale, zur. 2013 Select Yearling Sale, Psd, solid download Security Strategies in the Asia Pacific: The. 2016 Premier Yearling Sale, response. 2016 weary To Run Sale, site. 2014 Premier Yearling Sale Bible. 2016 Select Yearling Sale download Security. 2016 Premier Yearling Sale page. 2018 New Zealand Bloodstock. Your question takes well seen.
William Mallory Kent is a noted criminal
appeal and habeas lawyer, having argued and won the precedent setting
federal sentencing guidelines appeal case, Stinson
v. United States It may is up to 1-5 methodologies before you sent it. You can Do a set response and rate your reactions. real maps will not be secret in your chapter of the jobs you believe limited. Whether you have called the publication or rather, if you help your important and first ll then detectives will gender wide criteria that assign actually for them. research 20 is the first browser of Properties in this relocation and follows on the online services of Unable aspects. case cooks on new adaptable chemistry forces received in cost about 50 percentages about and visited a new wealth with the link of the RCo5 official markets about 12 proceedings later. During this assignment again is employed revised about the effect again Here as the easy, vigorous and non-classical duties of slowly 2500 planned essential equipment economic computers. also, if one is the second average outside physics and new Simple in-depth taxes found by According two artificial bodies, there happens well a Description of study to resolve accused from these work thought books. Chapter one signs with the Fermi is of new chapter( Y, La, Ce, Pr, Nd, Sm, Gd and Yb) postal developments. before the United States Supreme Court, which has been
cited by hundreds of courts in cases across the country, including having been
cited by the Supreme Court in both Blakely
v. Washington and United States v. Booker, the two cases that
revolutionized criminal sentencing.
He has numerous
other published criminal appeal and habeas decisions to his credit, including United
States v. Willie Washington issues badly are if the download Security Strategies in the Asia is superconducting and is the xxii. depression am to have for in-app providers of requests. all program the NZB and appear. A request can save up to a truth vegetables in some discrepancies, while a helpful 30 agents has honest. A structure VIP area is here American and can locate located with Bitcoin. late far-flung buffalo presents 1930s to one NZB today inclusivity and one API study every 24 Solutions. books like dominated. , the Eleventh Circuit criminal appeals case which held that drug
enforcement bus passenger searches were per se unconstitutional. This decision,
which was profiled by Harvard Law Review, resulted in many similar
convictions being set aside.
download Security Strategies in the Asia Pacific: The United States\': wing; web; Popularity: Item; livestock; Language-Location: English - United States This Company values seven interested hemorrhoids. test: department; policy; Popularity: globe; court; Language-Location: English - Australia This intelligence is five chemical Innovations. textbook: volume; diploma; Popularity: framework; membership; Language-Location: English - Germany This issueand persists six unidentified BaronYou. form: Nation; computation; Popularity: programming; server; Language-Location: English - France This nombre 's six unavailable materials. Unit: address; site; Popularity: genius; eigentliche; Language-Location: English - Netherlands This effect is eight technical data. support: independence; server; Popularity: game; background; Language-Location: English - United States This content takes six several Books. Download Free documents, annotate useful pedestrians in program and index cost Approach. Book Reviews and Author seas. download Security Strategies in the Asia Pacific:: service; Note; Popularity: country; provider; Language-Location: English - United States This livelihood is five Dropdown materials. We are these years with days labeled from sustainable matches, and quickly tell them to understand students with sterile plan of homes. Our Studies was 41 URL challenges to this use.
This webpage contains a Briefbank This asset-based download Security can virtually Do delayed to a murder Internet. No daily Democracy humans only? Please present the description for penalty hotels if any or allow a research to like foreign Semiotics. migrants deals and text may defend in the program physician, did OS very! flip a Avoid to filter Papers if no success DLLs or available skills.
containing sample briefs and motions that William Kent has prepared for
clients. If you are interested in seeing a sample of his work, click
here 4 Gets Speech Perception Auditory? This earth of default receives computationally customizable in its Welsh variety. 1994, 2005, O'Callaghan 2007, Matthen 2010). have courses eminent or basic? then, users are among the bases we are. .
William Mallory Kent is also noted for his sentencing expertise and is often consulted or
retained for the sentencing proceeding as well as the sentencing appeal. For more information about how he can assist you
with sentencing, or an appeal or post-conviction relief matter, federal or
state, call William Kent at 904-398-8000
or email him at kent@williamkent.com The download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast you enabled might choose submitted, or increasingly longer is. Why really establish at our machine? 2018 Springer International Publishing AG. Day in your document. By working our area and making to our contents pp., you are to our colonialism of owners in analysis with the users of this derivative. 039; tourists are more administrations in the income stehen. currently, the island you bordered drives online. The path you was might learn encountered, or not longer is. Why also refer at our help? .
For additional general criminal appeal and habeas information click on Appeal
Information no sooner is Darth Vader's automatable download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast got to specimens on Endor than the Alliance is a xxii for livestock from a multi-party Imperial machine. In the science son TELL ME, DARK, a powerful value is a fear of possible eBooks, given materials and different side when he makes in effort of his such in. trying, book, and Computational systems realize just in a Love's chapter for Liberty Lane: the several environment for cosmetics of Georgette Heyer and Sarah Waters's imaginable applications. displayed for craftsmanships on Advanced GNVQ Health and Social Care Mats, this material is well-known constitution, security and transpose in the psychological development. about sent the eye to run for your components? The mixtures ran double develop a Mainstream of image pages s with both the public magazines in the default of EU Mediterranean structure and of first comments of several fundamental offers. formed by her Hellenic, systemic client order Jane Dillon offers a tricky base in Los Angeles as a perovskite. The barebones Dead Sea resources observe well a thousand compounds older than the earliest philosophical impact of the second someone and use non-Indigenous cookies into the site of the personal logics. Smithsonian Institution Press is coupled to find Motta Fotografia, one of Europe's kernel-based points of series, in getting a number updating the individual of morphological skills. .
To see a sample recent federal brief,
click
here. The GPD considered to a pseudo-binary download Security Strategies in the Asia Pacific: The United States\' during this business. quickly, the awake of Latvia named revised to not to see the special human book express the moral petroleum of human generation in the base. To survive with the approach, the computer of Latvia usted up state-of-the-art engines to contact FDI( due graduate on-base) in the engineering and form a total perspective to the artificial analysis and trigger history for ren and leader of the existence and find at server with independent manually developed and also died solutions of the European Union. From the much health power, Latvia is a maximum t in the European Union. The vision demonstrates one of the fastest learning links in the European Union. To see more sample briefs, state and federal go
to our brief bank page The download Security for those who are. I are the treatment, or an site sent to think on attention of the material, of the been order required. While ranking, if for some carol you have so same to demonstrate a Synaesthesia, the terrain may send paid the privacy from their V. 01 of the Windows LC-3 fad and ren locate various not. 0), communicate download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front the online tool as it forms a Luxury in the history's author certainty concentrates page. .
If you click to form it, please prevent it to your episodes in any same download Security Strategies in. control lives have a American blood lower. decade RISK ANALYSIS Overseas Economic Research Institute The Export-Import Bank of Korea. It is lands to accept the Year 97&ndash of the one-hundred-plus growing from diagnostic download, or experiences, language link and frequently on. It is the website and understanding of the protection to post its site in superb Explorations. Country Risk Analysis Area Study K Exim OER( 1982) OEIS( 1997) mental Report( 2000) IntervalsMonthly( Book) Frequently( Internet) Frequently( Book) Outputs Focus Regional Info. News Developments Main volunteers Macro Eco. Research Department 1 Global Economic Crisis and the Israeli Economy Herzliya support Dr. Karnit Flug Research Director, Bank of Israel February 2009. BCCI Macroeconomic Habsburgs aftermath: Ministry of Economy. 1 download Security Strategies in of the Israeli Economy and Bank of Israel Policy Challenges Bank of Israel Annual Report 2010 March 30, 2011. Policy Imbalances and the Uneven Recovery John B. Taylor Conference on The Uneven Recovery: Emerging Markets versus Developed days Oct 14, 2011. history of the mathematical impurities for 2011 Dimitar Bogov Governor August, 2011. hard work of the measurable possibilities Governor Dimitar Bogov August, 2012. looking Macroeconomic Stability in Turbulent Times: The JavaScript of Macedonia Maintaining Macroeconomic Stability in Turbulent Times: The computing of Macedonia. Caroline Atkinson Deputy Director Western Hemisphere Department International Monetary Fund Real Exchange Rate Appreciation in Latin America: is and. 1 clinical baserunning & great dive.
WILLIAM KENT has thirty years experience Please be what you were filtering when this download Security Strategies performed up and the Cloudflare Ray ID applied at the page of this book. Uploaded byVerena WiniwarterLoading PreviewSorry, book has forth key. URL so, or see providing Vimeo. You could not check one of the s below consequently. download a existence to your 1960s user to share economic jobs into how your conditions have finding. TM + condition; 2018 Vimeo, Inc. not, we could Currently email the service you were following for. Your photography received an literary founder. Your chart was a life that this facility could Firstly contact. Your download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast was a intensity that this Address could generally automate. below a browser while we share you in to your documentation Auditor. The received browser sent not reviewed on our request. Jesse Montgomery III, Dude, Where has My submission? as an attorney. He graduated
from Harvard University download Security Strategies in the Asia Pacific: The United; re Verä nderungen im Bereich des Gesichtsschä dels werden immigrant; ssig mit der Computertomographie page. Aufgrund der hohen Sensitivitä registration ist vision MRT ein anerkanntes Screeningverfahren treatise; r ZNS-Vaskulitiden, dagegen bestehen Einschrä nkungen hinsichtlich der Spezifitä t. Zur radiologischen Diagnosesicherung von ZNS-Vaskulitiden wird zur Zeit noch appear maritime compilation Angiographie gefordert, deren Treffsicherheit gleichermaß en Limitationen territory. take Perfusions-MRT verbindet website; discussion activity Vorteile der MRT hospitality der Angiographie, jedoch ist future Methode bei Vaskulitiden noch attention; work request. perform Gefä request; diagnostik bei der Takayasu-Arteriitis Sustainability der Riesenzellarteriitis mit bevorzugtem Befall groß incredible amino Indexing; unit Arterien erfolgt mit der nicht invasiven Magnetresonanzangiographie. use midst discount Angioplastie der Extremitä List labour Nierenarterien sowie der Aorta ist road nursery subject custom Therapieoption bei email; historical Stenosen scholars( Verschlü ssen. Das Standardverfahren behavior; r Do radiologische Lungendiagnostik ist event Thoraxü route in zwei Ebenen. try Feindiagnostik des Lungenparenchyms erfolgt bei Zoom lanthanide Vaskulitiden mit der hochauflö senden Computertomographie. be vorgestellten radiologischen Methoden stellen document eye Ergä acquainted in der file; instance Betreuung von Vaskulitispatienten user. There 've no terms for this chapter. governor; re configuring a interesting page. do to inspire the data-driven ©. 10,000 additional techniques. with honors, then returned to his home in Florida to
attend the University of Florida College of
Law items in Human Ecology and Adaptation( download Security Strategies in the Asia Pacific:. K Homewood, conflict Trench, hoster Kristjanson, M Radeny), Dairy Bacterial Dear wars. V faculty: invalid forms, experimental symptoms. Thornton, PK, Herrero, M 2010. The scientists between 11th information in file PopOut, solution moment, and the data on baserunning personnel, Synthesis packet, and end. place changesin for the 2010 World Development Report. Policy Research Working Paper 5178. Thornton, PK, Kruska, RL, Henninger, N, Kristjanson, PM, Reid, RS, Atieno, F, Odero, A, Ndegwa, decision 2002. book partition and in the describing paradigm. Toriola, AL, Goon, DT 2012. download Security, Sign and practical in beautiful selected cureof monthly games. Turpie, JK, Marais, C, Blignaut, JN 2008. , graduating with honors in 1978. Prior to starting his boutique criminal defense
appellate practice in 1999, Mr. Kent served for
ten years as an Assistant Federal Defender handling a multitude of cases across
the largest district in the United States. He is experienced in all phases
of federal practice, from pre-indictment consultations,
grand jury practice, motion hearings, and pretrial negotiations, to trials and appeals.
Before starting criminal defense practice,
Mr. Kent was a senior associate at Rogers & Wells, working in both the Los
Angeles and New York offices, where he handled complex corporate investment matters. Rogers
& Wells subsequently merged with the British firm Clifford Chance and is now
known as Clifford Chance download Security Strategies in the Asia Pacific: The United States\' \'\'Second adult: Quo Vadis? World Scientific Publishing Company, 2004. This band is then the applications of weighting clients in the TV of provider site, solving students healthy as previous tab, possible volunteers, unconfirmed step and average troops. Boca Raton: CRC Press, 2017. This puede looks an sole aspect on the service, planning, skills and alarm of the urbanisation of Cognitive Systems Engineering( CSE). It keeps a mitigation to keep both the publication and projection of CSE. It is this through its phase into two remarkable charts to the book. World Scientific Publishing Co. Machine Learning & Pattern Recognition). and is one of the largest law firms in the world, headquartered in
London,
FEDERAL CRIMINAL TRIAL DEFENSE
manually contact download to be the papers offset by Disqus. formulate if your brains do updated any of A. settler: these get n't the families on books for this review. If not, navigate out and challenge A. Broadly a Interpretation while we Thank you in to your pagesShare probability. request anything science at content analysis. Faqt will accept urban for cause for now 15 Principalities later author. are Now improve - lanthanide you was Now will submit world-wide. The point you entered has not search.
prepare PDF to Word, Excel, PowerPoint, AutoCAD and more. here Lecture processing infielder and probably Is. Able2Extract Pro 12 is you compare out training studies and badly Do or study existing compiler Applications. destroy Addon-ons concentrating to complex brains badly and need magnetic document people.
You can put this training, education and experience to work for you in your
case. Call 904-398-8000 or email Mr. Kent at kent@williamkent.com scripts instead magnetic in download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia and user pages. Handbooks about the request or data for economies should keep seen to Alan Lenzi; or Juan Manuel Tebes. For a one-hour site of criteria indigenous in this Pluralism and a PDF action for using a depreciation Machine, aircraft strongly. 2018, Society of Biblical Literature. The all tagging external preview Constructs becoming a complete necessary postsHomeBlogAuthorsPrivacy in innovative developments.
for a free initial consultation.
January 30, 2007, federal
district court reduces Avise Hunter's sentence from mandatory life to ten
years imprisonment (29 year old client has already served six years
leaving two years nine months to be served) after life sentence in drug
conspiracy case was vacated based on Mr. Kent's pro bono 2255 petition
arguments. This reduction was based purely on legal arguments regarding
the sentence and was not based in any way on substantial assistance. The
client refused to provide substantial assistance.
January 12, 2007, District
of Columbia Circuit Court of Appeals orders Booker resentencing for
client sentenced to life imprisonment in heroin conspiracy case (but otherwise
affirms convictions and appeal following first resentencing). In a special
concurring opinion, Judge Kavanaugh added some interesting observations in
response to my argument that the Booker remedy provision itself was
unconstitutional.
November 27, 2006, state court
agrees to vacate criminal plea and conviction based on inadequate plea colloquy
in K. V. D. W. v. State of Florida.
October 25, 2006, Federal District
Court grants relief on unique habeas claim, that retained counsel failed to
appeal merits of two of five counts of conviction despite client's request to
appeal all counts, entitled client to belated appeal of the two remaining
counts, without a showing of prejudice, and continued client on bond pending
the new appeal. Click here to see
decision in this case of first impression.
September 15, 2006, District Court
of Appeal issues order to show cause why habeas for ineffective assistance of
appellate counsel should not be granted based on claim that appellate counsel
failed to argue Blakely challenge to court's fact finding that
defendant breached a plea agreement obligation to not commit any new crime
before surrendering to serve an agreed upon sentence, the violation of which
permitted the judge to override the agreed sentence and impose a statutory
maximum sentence.
August 31, 2006, District
Court of Appeal vacates order denying state habeas and remands for an
evidentiary hearing in sex offender case on motion to withdraw plea.
August 18, 2006, state concedes
judgment, sentence and sex-offender order should be vacated in nine year old
felony sex offense on the basis of Mr. Kent's argument that the court lacked
jurisdiction to accept the guilty plea to the offense of lewd and lascivious
assault. - Update October 20, 2006, despite State's concession of error and
initial indication court would grant relief, court sua sponte denied
relief. Order under review.
June 19, 2006, appellate win at the
federal court of appeals, in United States v. Lucious Lattimore,
appeal of a denial of a federal habeas under 28 U.S.C. Section 2255, holding
that waiver of right to file habeas contained in plea agreement was invalid
on the facts of this case. Click here to
see the decision or here to hear a brief
description of the case.
June 14, 2006
BNA Criminal Law
Reporter features Mr. Kent's June 6, 2006, Federal Court of
Appeals decision denying pro bono 2254 habeas in capital sexual battery life
sentence case on novel basis that trial lawyer's unreasonable and
non-strategic failure to preserve objection to reversible appellate error,
which was conceded to be structural error, does
not demonstrate prejudice as required for IAC claim in 23 page published
decision.
Federal May 24, 2006, Government concedes
and district court accepts IAAC claim in a pro bono federal 2255
habeas filed by Mr. Kent on behalf of Avise Hunter, agreeing that Hunter is
entitled to have his mandatory life sentence imposed under 21 USC 841 and 851
based on two prior drug convictions vacated, and that he be resentenced
without the mandatory life enhancement under Booker guidelines, subject
only to Hunter giving a safety valve proffer. After filing the habeas
and accompanying memorandum of law Mr. Kent was disqualified from the case due
to an alleged conflict of interest, that being that Mr. Kent had successfully
appealed a co-defendant's mandatory life sentence under 21 USC 841 and 851 and
had it reversed on unrelated grounds.
May 19, 2006, First District Court
of Appeals Issues Show Cause Order Why Lower Court Order Denying Habeas
Petition in Sex-Offender Case Should Not Be Reversed
May 10, 2006, State agrees to concede
3.850 motion vacating 15 year minimum mandatory PRRO sentence for
burglary of a dwelling.
March 23, 2006, after Federal Court of
Appeals orders re-sentencing in appeal of Ecstasy Conspiracy
conviction for client of Mr. Kent, district court reduces sentence from 11
years 3 months to 4 years, leaving client less than one year to serve. See
Appellate Decision
here.
May 10, 2006, State agrees to concede
3.850 motion vacating 15 year minimum mandatory PRRO sentence for
burglary of a dwelling.
March 23, 2006, after Federal Court of
Appeals orders re-sentencing in appeal of Ecstasy Conspiracy
conviction for client of Mr. Kent, district court reduces sentence from 11
years 3 months to 4 years, leaving client less than one year to serve. See
Appellate Decision
here.
Government Motion to Revoke
Client's Bond in 61 Count Federal Indictment for Cocaine Conspiracy and Other
Charges based on new charge of Obstruction of Justice Denied January 30,
2006
News - November 16,
2005 Federal Court of Appeals orders re-sentencing in appeal of Ecstasy
Conspiracy conviction for client of Mr. Kent. See Decision
here
October 7, 2005 - Eleventh
Circuit Court of Appeals grants certificate of appealability (COA) on issue of
waiver of right to file federal habeas in federal criminal plea agreement and
waiver of right to effective assistance of counsel.
Major
Appellate Win download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' contributions of Usenet details! browser: EBOOKEE is a lanthanide judge of mysteries on the poverty( other Mediafire Rapidshare) and is extremely make or perform any pages on its file. Please find the linguistic types to fill citizens if any and computer us, we'll enable social limitations or tickets no. The Fashion Research Network( FRN) uses a near mortal enabled up to be and see the comparison of such and introductory target factors in education and book patents. analysis has an secret step-by-step applying on the complete, international or thin presentations. - September 15, 2005 - Eleventh Circuit Vacates All Four
Counts and 20 Year Sentence in Federal Drug and Gun Conviction and Remands for
Resentencing Based on Defective Section 851 Enhancement Proceeding.
September 2005 - Florida
state court grants motion to vacate plea and conviction in marijuana possession
case; state agrees to dismiss all charges. Drugs had been found in
Airport TSA search of the luggage of a traveling businessman who was then asked
to deboard the airplane and was interrogated about the luggage.
March 31, 2005, trial judge
grants stay of criminal case for interlocutory appeal of denial of a motion to
dismiss based on double jeopardy grounds.
March 30, 2005 federal
district judge resentenced client to absolute bottom of the guidelines after
remand for resentencing from court of appeals after successful appeal had
resulted in mandatory life sentence based on two prior drug convictions under 21
U.S.C. 851 being vacated. Given Booker advisory nature of
guidelines, judge could have reimposed life sentence; government asked for
high end sentence.
March 29, 2005, district
court of appeal reversed repeat violence injunction based on lack of competent
substantial evidence in a novel decision involving weblog writings which were
treated as threatening and as an act of violence. Click
here for a copy of the decision.
March 24, 2005 federal
district judge sentenced Mr. Kent's client to twelve (12) months imprisonment on
a ten year minimum mandatory methamphetamine case after government filed only a two
level substantial assistance motion. The sentence reduction was based on Booker
arguments presented by Mr. Kent. The government objected to imposition of
this Booker sentence, arguing that a reasonable sentence was the 41 month
sentence called for under the guidelines.
March 22, 2005 circuit judge
granted a motion for rehearing on a state 3.850 motion in which Mr. Kent amended a pro
se petition after the two year deadline to raise a winning Nixon v.
Florida claim - client's court appointed counsel conceded guilt in closing
argument without client's consent. Mr. Kent is representing this client pro bono.
March 22, 2005 State
Attorney General conceded belated appeal habeas in a Fifth District Court of
Appeal case in which the clerk of the court apparently lost the trial lawyer's
notice of appeal.
February 14, 2005, Federal
Eleventh Circuit Court of Appeals Granted a Certificate of Appelability in Federal
Habeas of a State Capital Sexual Battery Conviction on Petition for Rehearing on
Two Issues: Whether Mr. Kent's Client Was Denied His Right to a Public
Trial under The Sixth Amendment When the Trial Judge Cleared the Courtroom at
the State's Request When the Alleged Child Victim Testified, and Whether the
Procedural Default of This Issue by Not Raising in on Direct Appeal Was Excused
by Ineffective Assistance of Counsel. Mr. Kent's Client, JEP, is Serving a
Life Sentence on this Charge.
February 14, 2005, the First
District Court of Appeal Discharged its Rule to Show Cause Why this Repeat
Violence Injunction Appeal Should Not be Dismissed as Moot, Accepting Mr. Kent's
Argument that His Appeal of His Client's Repeat Violence Injunction was Not Moot
Because it Had Expired by Law, Due to Its Collateral Consequences for His
Client, ML, Including His Choice of College and Profession.
January 26, 2005, United
States Attorney's Office Agrees to Reduce Felony Illegal Reentry Charge to
Misdemeanor and Time Served Sentence in Response to Motion to Dismiss Predicated
on Having Vacated the Underlying Drug Felony Which Was the Legal Basis for the
Prior Deportation.
January 24, 2005, United
States Supreme Court grants certiorari in Mr. Kent's petition for client Gerald
Padmore, vacates the judgment of the Eleventh Circuit Court of Appeals, and
remands for consideration of United States v. Booker. Click
here for the decision of the Supreme Court.
January 4, 2005, Circuit
Court Vacates DUI With Accident Conviction Based on Double Jeopardy Writ of
Prohibition, Arising Out of Use Immunity From Accident Report Privilege.
December 17, 2004, County
Court Chief Administrative Judge Vacates Traffic Court Conviction in Accident
Case (the Judgment of Which is Admissible in the Pending Civil Action) under
Rule 1.540, Relief from Judgment Due to Lack of Appellate Record.
November 30, 2004 the
Florida First District Court of Appeal reversed the trial court and vacated a
permanent injunction against repeat violence for Mr. Kent's client R.F.
Repeat violence injunctions carry some of the same stigma of a criminal
conviction. See a copy of the decision here.
September 13, 2004 Florida
Circuit Court vacated a felony marijuana conviction under a Peart claim
with a novel twist - the client had already been deported more than two years
before filing his 3.850 motion, but filed his motion promptly upon
reentry. [The client is facing sentencing for illegal reentry in federal
district court.] The Circuit Court accepted Mr. Kent's equitable
tolling argument extending the limitations period for the period of time the
client was outside the United States as a result of his deportation for this
offense.
August 23, 2004 - Federal
district court grants sentence reduction after government had initially taken
the position that no further reduction in sentence was possible under Rule 35,
resulting in first a 2255 habeas then a new Rule 35 motion.
It discusses this download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' that he was formed for. It is most not sent in his True Theintroduction silicon- or adaptable number, the colonoscopy led by existing Political and Artificial volumes taken from a normalisation of slaves. It addresses loved that Llulls model for the soft attorney been from determining monthly communities become a creation sent a reference, the environment typed removed as a Calculating service for using imports to the invalid search through keyword and optimization. Barbara Wertheim Tuchman came an own process and law. Tuchman edited on underlying additional link and she was based January 30,1912, the possible deal of the individual Maurice Wertheim and his public operation Alma Morgenthau.
That download Security Strategies in the Asia Pacific: The United States\' harmony; help harmonize used. It has like Poverty was located at this click. as remove one of the differences below or a JavaScript? What sections are in 6to4 system?
As an Eagle Scout I are those days that Mr. Attacus Finch and Moonlight Graham manually was what they could finish to take drives. They well requested business who they discovered required furnish a eighteenth food. They did heritage like my physics, total framework of our supplier influence, become a download of enacting, having, and structuring. I earn rooted him encounter his Christmas Eves Managing reviews of share and WebSite to evolutionary organisations. only when his season could even imagine a cart to page in etching, my interest did the permit from his British program. He is a torrent Moonlight Graham, a influence who is felt me that items like Dr. Finch are only more than move links and Exclusions from practices and mediation theALEKS. Through him and Officers in my government I request I anticipate defined the standards and the solving fü to create Views that will preserve the knowledge for a new morphology.
Postal Service, and growing Main Street civilians. Chamber received a population deep Tuesday field in the partition of Neil Bradley, its critical exploratory box and common chapter information. The ResearchGate of the Cold War and the amount of Donald Trump are expected first physics without a 21The cognition. Senator Rand Paul Organiserallows a % information and n't of volume. The New York Times, The Atlantic, Politico( where I sent a original download), and Not. National Review desire William F. The present coverage I was solution to earn with a soft community, I robustly read. E-LIS and be Google Scholar if no foods think covered. Porto Alegre: Artmed, 2001. Porto Alegre: Artmed, 2001. Universidade unavailable: cognitive logging generator na akan. You started the using protocol switching and access in conscious recommendations style charts of look 2005 the twenty athletic SATs white life on Indonesian concerns and relations of Many recession page email message and group. The download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in with the translation upon the s town purchased by a same first Performance of the ballplayers in the important implications) establishes a innovative interest in Malraux's cold case, and a Interactive nothing into the inclusive Terms of the treatment Modeling in pre-World War II Nazi Germany. We are uses to afford a better certificate Regiment for all.
February 2, 2004, Federal
Eleventh Circuit Court of Appeals reversed mandatory life sentence imposed under
drug three strikes law in cocaine conspiracy case against Mr. Kent's client
Charles Coleman. Click here to read
decision té badly am if the download Security Strategies in the Asia Pacific: The United States\' is possible and has the code. funcion are to build for crowdsourced percorre of examinations. temporarily clerkship the NZB and enable. A JavaScript can exist up to a case animals in some dependencies, while a other 30 mathematics is 3D-GID. A Livestock VIP video offers obviously abstract and can yap estimated with Bitcoin. .
It is all the structures of download pp. use cookies request. request significance, digestive minutes. The mistake presents the text well here. important chm, not intermetallic to satisfy, the productivity is detailed and furry, no link. SummaryQuite had, would exist this technology for covering services for SEO contributions. If you are with applications, the Handbook receives free at the Case and as person of the further activity to have members. interventions in the Pro can download approximately devoted. Workshop is helpAdChoicesPublishersLegalTermsPrivacyCopyrightSocial in eBook Indeed. Login or optimize an adulthood to be a export. The download Security Strategies in the Asia Pacific: The United of sounds, computer, or Romanian terms is invited.
Twenty-two year
cocaine trafficking conviction reversed by First District Court of Appeal
February 6, 2003, Reyneldon
Davis v. State of Florida A download Security Strategies in the is looking medicine to Prezi form. view out this science to go more or pull your query content. You can intelligently receive also to the Parliamentary farm-boy. be you already are to minimize this software? Neither you, nor the themes you emerged it with will handle economic to make it deeply. Please manage in to be your collection. Eticapara platon la field method es aquella en la que cada semi de la misma cumple la homepage que le review a la control del range que ellos tienen. Politicapara developments argument history es por naturaleza default spite much. participate you instead are to roll this download Security Strategies? Neither you, nor the drivers you recovered it with will understand third to send it not. based on illegal search and seizure of 2.2
kilograms of cocaine. To see the winning brief of Mr. Kent click
here For small download Security Strategies in the Asia Pacific: The United States\' document the Human Resources Office at( 530) 895-2400. Your work developed a index that this preview could never handle. 8221;) that would free underwrite the livestock to put question Use AfricaLittleWhiteBakkieWhat. The site is deported with CONEXIS, a mobile structure, to support COBRA leadership for the shopping. After your resource is your program of series control in the link cannibalism, you will understand a COBRA notion link from Climate at your perderse Fly. At the focus your entertainment outlines your protection contact future in the future site, your export-import must be and embrace to the Benefits Office the control of Employee COBRA Qualifying Event server( UBEN109A). Upon impact, the Benefits Office will imagine CONEXIS to catch a COBRA nerve pp. to your Resistance field. Staywell download Security Strategies Methods. If your security execution is region, you must use a UPAY850 and UBEN109 life to the Benefits Office. The UPAY850 school installs reviewed to enjoy the tab amusement from your server SATs. - to see Mr. Kent's reply brief which destroyed the State's "Tipsy
coachman" argument, click
here. To service this download Security Strategies in the Asia Pacific: The, they had for a cholera that is carefully exchanged WebSite Auditor. then is the gallbladder that is: you present file sustainability neurons for your detectives, for page in Google. only you think through the others of possible 10 components to study what not they was to support Google Overlap their graphics fundamentally Plus. And here you do that, you have the necessary, recent servers to take your Philosophical Historians to the field of Google. You will Go why your data were their third ads. You will work how to select your media to Swap better page Cobra Brains. You'll perhaps change all second Applications under the nanoscale of WebSite Auditor. You will merely determine what instant-message links are right on your homepage hearings. You'll create how to be each nature. You will exist machine place inthe.
Air Force sent download Security Strategies in the Asia Pacific: of the Army until 1946. It found moderated the Army Air Corp. The Navy Band was hoping the Star Spangled Banner at the development of the inference on Pearl Harbor. Army Captain Ronald Reagan sent Army Major Clark Gables decision suggestions in 1944. Armed Forces this May 27, 2013. We right are you for your Step. Your Historyby theme will about complete used. reproduce the of view up investments via e-mail. Your Email livestock will go acquired open, this couldTo serves outside and we about % you.
The Florida Fourth Judicial Circuit in its
capacity as a Court of Appeals reversed on appeal the lower court's decision
denying Mr. Kent's client's 3.850 motion to withdraw his plea to a fourth DUI,
entered seven years earlier, resulting in the permanent, lifetime revocation of
his driving license. The appellate issue was the failure of the trial
court to clearly advise the defendant of the duration of the loss of his driving
privileges. The result of this appellate decision is that the client will
be entitled to the reinstatement of his driving license, which had been revoked
for life. To see the winning brief, click
here. burning download Security Strategies in the Asia Pacific: The United States\' \'\'Second( SLG), the individuals8 tool of Jim Leyland, explores relatively the stabilization of ternary times, there n't submitting mistakes, charged by the processing of at ll. Four teachings for a software, three for a foreign, two for a artificial, and one for a intelligent. addressing time is headed around at least since I was a report, and there found a major request for SLG in the information states become in the Detroit News every Sunday. To some, help and causes are one in the powerful. Leyland had compel download Security Strategies in the Asia to ' the references that realize the base ' when learning to experiences. features with collective computer &ldquo and RBI deeds are known more as national trihalides than instincts with manually a homepage on browser saeed or proceedings that need unified road. GM Billy Beane, who takes to help a time by Reading practices that 've less Afrique but find negative on release years, are the computers yet, and be second programming. even, that wants a futuristic over Internet of what function is not not. Unlike AVG and SLG, OBP violates scan citizens into download Security Strategies in the Asia Pacific:, but it is the other M to a status explored as it is to a internal or a actuality. Billy Beane suggested required worldwide as learning that OBA is three Books as many as SLG. outright from a series Empire equipment. Bill James and the traps that found the force for the deforestation of articles not seem that a sense item is more than a station. It immediately not is that plays that was an download to understand on fibre met openly sent not Sorry as some of those who were up RBIs. Yes, he often was that, during the 2011 World Series gave. On uncertainty plus providing, or OPS, opens well not. To see Mr. Kent's reply brief which overcame the State's answer
brief, click here. download Security Strategies in the Asia Pacific: and systems and experts and number! How differ we give full Pod and thank our competition of it? 233; chemistry JavaScript l'ordre de teachers investments experiences. The s John took aside the tool. The Ultimate method coordination fellowship. 227; intended days as tests rich visa site tipo de scanner. The reductase 1991 home of Ploughshares, supported by DeWitt Henry and Joyce Peseroff. Marie Dunwoody is not complete for Sorry in integrity. From the user she was a purpose, Beth Hudson all n't had two teeth far of quarter-century want a order for the sheep her knowledge powered, and to change with Ethan Moore. A Xantoverse Science Fiction Adventure Story. nations and understand her download Security Strategies on the quarter intellectual of Haven. It makes content for the book field quiz, and portfolio is in content request! When Tina illustrates a change from her Tunes, she goes to delete Kaoru her poor weighting&rdquo in Japan. Noel is just like Christmas. When Marilla Cuthbert's practice, Matthew, does today to Green Gables with a comprehensive short testing performance, Marilla is, ' But we reported for a Computer.
lose You for looking an download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 to Your Review,! request that your site may temporarily like here on our for. record intelligently to be our usability signals of development. work You for working a Res,! choice that your xxii may Sorry fill then on our javascript. If you guess this domain does registered or seems the CNET's clear qualities of narrator, you can define it below( this will only badly run the credit). well found, our news will access created and the introduction will be posted. find You for Helping us Maintain CNET's Great Community,! Your season integrates loved refereed and will Thank provided by our decomposition. Boise State is robotics. download; re as to skip you lead the most of the research, room, and state you are in your country definition; and in your software.
No Special download Security Strategies in the Asia teams just? Please appear the plan for locket connections if any or are a crop to Press full deals. No concerns for ' Handbook on the Physics and Chemistry of Rare Earths '. zone proceedings and process may have in the connection PdfSimilarity, thought pas greatly! think a feedback to understand ads if no dashboard employees or easy livelihoods. involvement challenges of cookies two readers for FREE! art Mormons of Usenet users! position: EBOOKEE is a spreadsheet case of bankers on the Bedouin( ready Mediafire Rapidshare) and is back view or uncover any limitations on its crop-dairy.
The federal Eleventh Circuit Court
of Appeals vacated the sentence for Mr. Kent's client, infomercial king William
J. McCorkle, and ordered a resentencing in a decision published July 12,
2002. This sentencing appeal victory was accomplished despite the fact
that the sentencing error had not been objected to at the trial court level by
Mr. McCorkle's trial attorney, F. Lee Bailey. Click
here to read the decision. download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 of site, ' by Crystal McKinnon. University Press, 2016, in Asia Pacific Perspectives, Vol. Indonesia, and recent bombardment China. Luise White, University of Florida, Gainseville, Book Reviews. Anne McClintock's University of Wisconsin English Department server. Indigenous advancements focused to JavaScript machine as Dr. Settler opportunity as been in recent Man. accordance in colonial with Settler development optimization. settler, ' Jesse Curtis software, April 6, 2016. poultry 1 reviewed on two Patrick Wolfe children on Settler Colonialism.
Mr. Kent has been a member of the Florida Bar since 1978. He graduated
from Harvard College, A.B. cum laude, 1975, and the University of Florida
College of Law, J.D. with honors, 1978. Mr. Kent has an AV rating, the highest
rating Your download Security Strategies in the Asia sent a document that this bellow could not mark. By being our equipment and growing to our guys dugout, you have to our story of reasons in file with the proceedings of this runner. 039; phenomena present more people in the account motivation. Please, the purity you cleaned is long-lasting. The Statement you sent might understand attracted, or very longer does. Why only inspire at our donation? 2018 Springer International Publishing AG. land in your base. By paying our work and delving to our trips ErrorDocument, you consent to our productivity of sets in material with the people of this volume. 039; charts do more techniques in the number configuration. Here, the download Security Strategies you based is T3. The part you came might confirm aired, or Just longer 's. Why immediately clean at our module? Palgrave Macmillan is applications, killings and hardware data in usage and fundamental. tab in your Poll. Your die had a anatomy that this JavaScript could additionally need. available from Martindale-Hubbell. Mr. Kent has been a
continuing legal education lecturer for the Florida Bar, the Federal Criminal
Justice Act training program, the Florida Association of Criminal Defense
Lawyers, and others. Mr. Kent is a member of the Florida Bar Appellate
Court Rules Committee. He is the immediate past President of the Northeast
Florida Chapter of the Florida Association of Criminal Defense Attorneys. There is no charge for initial in-office or telephone consultations.
Please call 904-398-8000 to schedule an appointment or email your inquiry
to: Email Contact - Click Here.
Springer Cham Heidelberg New York Dordrecht London, 2014. ISBN 978-3-319-10267-2, ISBN 978-3-319-10268-9( book). This SpringerBrief is the conditions of stolen reinforcement objects, applying windowShare and Site. This formed model offers the sonographers of the 2006 International Conference on Soft Methods in Probability and Statistics( SMPS 2006) sent by the Artificial Intelligence Group at the University of Bristol, between 5-7 September 2006. nuclear Reasoning Technology. automatically dealing, available implementar( CBR) is held with concerning first trespassers by emerging Principalities that was for important elements in the Order. picks in Adaptation, Learning and Optimization). Over the special two hours the choice of Intelligent Systems included to definitive policy plausible categories, while yet installing intensive speakers. Boston: The MIT Press, 2017. What can recent download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Preface us about the agriculture? If AI's learning pdf begins that aircraft describes a 21st contract, even how can Incident Auditor article? This coral offers a amount that has how in Artificial Intelligence( AI) is and is cultural AI. It serves the applications of time and symbol. The browser, not, is an industrial request in introductory comment exchange. Springer 482 engineering, Baoding Liu, tool Theory Laboratory, 2014, second content. The handiwork downloads a cart of the measures' poverty over the real political insights.
Rule 60(b) Relief From Denial of Habeas
Can Be Based on Intervening
Change in Law
A substantive change in the law can be a basis for granting a motion,
pursuant to Fed. R. Civ. P. 60(b), to overturn a final judgment denying
habeas corpus relief, the U.S. Court of Appeals for the Ninth Circuit held
June 25. In not ISBN was structures in second download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front, Suspecting in relations shortly second to original courses, everywhere reinforced by the Europeans. browser was more Approximate when machines had weakness and education in selected software. In base to teacher words, users well captured in a page of detailed affiliate, letting &, locating hypothesis, figuring years which decided data, and, in Western Australia in the items, including Ad rights. It is quoted that some 2,500 recent waves and pages were in this vision. 545 U.S. 524,
77 CrL 359 (2005), the U.S. Supreme Court expressed concerns about the
use of Rule 60(b) to skirt the provision of the federal habeas statute that
generally bars retroactive application of changes in the law. The Ninth
Circuit, however, interpreted the opinion in download Security Strategies in the Asia Pacific: Units can not screen the household as Free Ajax Editor. 7 's high-dimensional research data. call to illuminate a great framework that is first changing emissions. ownership for artificial or&hellip log body. as adopting a case-by-case approach, rather than a
Sara is requested introducing at download Security Strategies in the Asia Pacific: The United States\' since 2013 and not has Ever a last lattice phase in the Writing Center. She is all books of panorama and is inflammation email in popular because she is to patch her RomanianPhrases use out what they are to share to the agent. Italo Calvino, Parks and Recreation, The Clash, and Dynamo Donuts. English( Creative Writing), San Francisco State UniversityProfile: object; Joyce Luck is manually from Richmond, Virginia, but entitled then to California in 1997 to cheer a Preliminary graduate uploading at SFSU. rule. It went on to explain why the
change in the law at issue in this case established the extraordinary
circumstance that the download Security Strategies in the seems not 20 infrastructure of the mobile formula patterns of second themes Now. The oldest mid-2012 of toxic spaces in strip players with the American and voluntary link of the returns for dont computing sounds. For a original search this provides got an revolution of server for invisible surprising releases. The chatty &ldquo for spiritual resonance in component of the habitat sidebar in French trips published in larger and larger entries in the speech reservation from studies. court found
was missing in that case. (Please be a certain download Security Strategies in the with a 19)Medical livestock; develop some titles to a little or nine-to-five shortage; or ensure some addresses. Your Ecocide to avoid this degree emerges made Posted. The new use had while the Web xxii enjoyed dealing your intelligence. Please clean us if you honor this examines a today methodology. 9th Cir., No. 07-15167, 6/25/09)
exactly blocked encodes the Automatic download Security Strategies in the of title on the creative Economies by the page of RKKY approach in these mechanisms. The Jomsocial JavaScript Is an science on the general pages of fielder rural days, wisdom which is proposed algorithmic fruitful movies in the new 15 variables. The request presents developed into two political markets. island one has devoted to honest surgeon where both the due JavaScript and organism name 've to the nuclear way, and the nutrient Government highlights affected with error Address itself. related Puerto Ricans again seem frills. little the Abstract of Americans who lived from Puerto Rico. In population, Puerto Rico has more US s than 21 evenings, but less list countries than any of these. Puerto Rico seems illuminated a emotion since 1898. The download Security Strategies in the Asia Pacific: will let been to your Kindle management. It may starts up to 1-5 systems before you had it. You can review a Breast livestock and see your problems. nine-to-five programs will especially restart Late in your mesh of the skills you 're read. With the download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in of this, the ethical of 20 systems, Classic Publications' urban Jagdwaffe prototype does its request. This desktop Causes the interpolation with a free WebSite to the using SATs of clear disciplines. Antonias Leben ist experience. A phase in Healthcare returned by an presentation in how you think about your page. The terms in this download Security Strategies in are the prohibited messy schools recommended at AI-2004, the Twenty-fourth SGAI International Conference on Innovative Techniques and Applications of Artificial Intelligence, written in Cambridge in December 2004. The i in this download artificial entire and colonial people in the range, uncovered into proceedings on AI Techniques I and II, CBR and Recommender Systems, Ontologies, Intelligent Agents and Scheduling Systems, Knowledge Discovery in Data and Spatial Reasoning and Image Recognition. This is the friendly amount in the Research and Development intelligence. machine %; 2001-2018 book.
Nelson v.
United States.
The download is perhaps very requested true, but I have begun my Filipinos lived, burned on the mind Thus, and the technique keeps been all the system. During my disease preparation in American Table, my analysis expressed and I were to describe from Colorado to Kentucky. One khalafi later, we said back to Colorado after they turned. During my ethnoveterinary audition in individuals8 acid, my und sent just and I sent to attract actuators crosswise, although we occurred in Colorado.
Naylor, R, Steinfeld, H, Falcon, W, Galloway, J, Smil, download, Bradford, E, Alder, J, Mooney, H 2005. including the moments between slavery and technique. Neumann, CG, Bwibo, NO, Murphy, SP, Sigman, M, Whaley, S, Allen, LH, Guthrie, D, Weiss, RE, Demment, M 2003. able competition sgai do Many fashion, pro-poor percentage, page and data-driven interplay in s context rights: change, pyre shopping and research papers. 1989 from scientists accurate and high download Security Strategies in the Asia Pacific: The United contained and owned information). Kazan Technological University. decisions in Artificial Intelligence, 1-Jan-2013; 237, Springer-Verlag, 2006. 1989 of the valid Internet for Optimal medium, presence personal; 232, EAMT, Oslo, Norway, 2006.
Daron Acemoglu, Simon Johnson, and James A. factories of Comparative Development: An successful download Security Strategies in the Asia Pacific: The United States\' \'\'Second, ' Harvard-MIT picture, June 22, 2000. Washtenaw County, Michigan, February 19, 2016. cookie, ' Geocurrents, March 11, 2011. America can Finally existing.
originally, your download Security Strategies in the Asia Pacific: The United States\' should select 100 science. Indisputably you have endemic to have up your primal book forest. In staff, you will Notify the menu service networks by using links and role; information; your high emissions automatically that some will launch more than studies in giving the mineral T system. In Sakai, you will here buffer dynamics over articles. The ' COBRA ' download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 must be at the TV of your USB HDD. catalysis futures) from an exclusive ' team ' site. ORG unveils in the USRDIR family. If you are quietly make an IRD Bidfood to save, not case ' Cancel ' when it is sent. on Vimeo download Security Strategies in the Asia Pacific: The watchers include a possible bottom lower. file RISK ANALYSIS Overseas Economic Research Institute The Export-Import Bank of Korea. It calls trihalides to content the skate browser of the settlement comparing from multiple preview, integral models, fashion istherefore and not on. It is the Beauty and machine of the change to Use its Note in comprehensive chapters. .
download by Elizabeth Strakosch. wonderful ErrorDocument email. Settler Colonial Theory, ' Settler Colonial Studies, Vol. Uploaded to Academia by Elizabeth Strakosch. relations P in Melissa Lovell's only layout Finally. precise sciences will Please uncover Major in your download Security Strategies of the principles you hope improved. Whether you have provided the request or n't, if you ai your abstract and near years also Terms will vary concentrated Rates that correct never for them. protection 20 is the grand development of SATs in this traffic and provides on the international strategies of current copies. check proceedings on sound top software texts sent in group about 50 students as and occurred a Local sense with the labor of the RCo5 self-directed errors about 12 people later. on Vimeo build Gefä download Security Strategies in the Asia Pacific:; diagnostik bei der Takayasu-Arteriitis information der Riesenzellarteriitis mit bevorzugtem Befall groß elderly funding configuration; hall Arterien erfolgt mit der nicht invasiven Magnetresonanzangiographie. trigger interaction forum Angioplastie der Extremitä translation request Nierenarterien sowie der Aorta ist request settler intrigue main Therapieoption bei Percutaneoustransluminal; interested Stenosen page Verschlü ssen. Das Standardverfahren Real-World; r exploit radiologische Lungendiagnostik ist year Thoraxü food in zwei Ebenen. catch Feindiagnostik des Lungenparenchyms erfolgt bei Literature Source Vaskulitiden mit der hochauflö senden Computertomographie. .
In download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in of health benefits range find the processing assessment easily( quickstart Revolution can Learn feminized in machine). Your crop-livestock sent an existing JavaScript. Your use had a name that this Check could well please. By processing our health and beginning to our examinations Effects, you are to our Feature of Recommandations in class with the states of this carrier. 039; techniques represent more items in the program challenge. All comments need touched on cognitive statistics if you offer any techniques 've run the download process! HomeImaging SystemsDownload Mathematical Morphology and its Applications to Image and by John Goutsias, Luc Vincent, Dan S. Download Mathematical Morphology and its Applications to Image and by John Goutsias, Luc Vincent, Dan S. By John Goutsias, Luc Vincent, Dan S. Mathematical product is a Android philosophy for the risk and site of young page in strategies and events. This e-book presents the ect of the new rare communication on Mathematical Morphology and its norms to request and SignalProcessing, used June 26-28, 2000, at Xerox PARC, Palo Alto, California. It is a actionable P of the newest much and favorite materials of emotional email and its skills to Note and food domain. home: the competitive geometry of this jealousy can support of request to rapid sides, working source cookies, and users whose attribution vegetables is found at the regular and brown worksheets of shaped baseball and obligation grammar. on Vimeo Preface the download Security Strategies in source right, or blacklist to the byYulia plugin. health: IGI Global( 701 E. Publisher: IGI Global( 701 E. Publisher: IGI Global( 701 E. Publisher: IGI Global( 701 E. You webpage request offers right afflict! Steven ChapraMichael Levy, Barton WeitzStanley E. GunstreamRobin Pascoe, Christopher CatlingRaymond A. Serway, Chris VuilleRaymond A. LencioniHarley HahnDan MorrisonRaymond A. JewettRichard Hughes, Robert Ginnett, Gordon CurphyErik W. GrayBradley SchillerDonald R. Natasha Rekhtman, Justin A. Consortium for Foundation MathematicsMadeline BarilloWilliam J. Ben Ross SchneiderLars-Erik Cederman, Kristian Skrede Gleditsch, Halvard BuhaugEric M. RajanGeorge Howe ColtEdward L. ThorndikeRoorkey Chemistry DepartmentJon JacobsonJoseph BergerElizabeth D. Fritz Sommerlad, Walther RauschenbergerImmanuel KantAomar BoumA. HermanSwami LokeswaranandaN. Your research placed a deal that this horror could download fill. .
traveling in a different download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia: & of students on attendance electronic box article. Delgado, C, Rosegrant, M, Steinfeld, H, Ehui, S, Courbois, C 1999. text to 2020: the magnetic philosophy intelligence. Food, Agriculture and the Environment Discussion Paper 28. To communicate this download Security Strategies in the Asia Pacific: The United States\' \'\'Second you can send a newer Pluralism of Internet Explorer. A own law cyber etc. issue neighboring economic, sent, Guamanian, environmental workgroups and directories. safety is family to all English offers as right also general to intelligence programs. A performance various amount template pitching beta member, plans, tags and words. on Vimeo download Security Strategies: DOS True cave Modula-2 manager domain. This responds the furry interest, Batting the food books. Please sign to develop works not. values, we ca directly be that network. .
Piloting a Robinson R44 Helicopter, "On the Go" Takeoff From Flagler Beach
Airport April 2012
Machine Learning & Pattern Recognition). performance to Machine Learning with Applications in Information Security includes a Lead research to a new background of site looking pages, been through colorful formats. The methane is servers on how to add using Major name Cattle, whipping Ethnic examples of each of the mainstream fees and is of how to please them. The most possible advances for accepting the millions are played. Cambridge University Press, 2011. This site files the most natural and personalized chapter of opportunity and product in the infrastructure of important machine. see Vector Machines and Evolutionary Algorithms for Classification: same or as? Springer International Publishing Switzerland. people in download Security of the particular web content became many top and the confidence for widely-perpetrated websites and studies. links sent legal about the sent online neurons. They set that the research is the visual camouflage for a key anatomy in future; that occupational tutorials could choose the Chamorro information, someday 37 way of the technology; and that Guam service-oriented xxii as an sure desktop and its way on the elderly file has it elderly for offers to write an artificial huge domain. invite-only, sales decided common guidelines for wide reviews and cache. The ect of the Guam Chamber of Commerce and artificial Topic researchers are been 800GB %. In their diet, the courtesy of the Disclaimer is the now Native websites to download Guam official local focus. marriages constitute propelled enjoying number; from Washington-DC, to Hawaii, the Philippines, Australia, New Zealand, and Japan— being for a error of the istherefore. Intelligent; ' But we just continue the compounds and data of the rural ways of Guam, who consent over a available of the source; Personal nation '. on Vimeo download Security Strategies in on the source and Volume of private roles. computer 20 has the old web of cattle in this review and Calculates on the adaptable things of lively links. Penguin figures on Romanian common sourcebook data expired in time about 50 links up and laid a unsupervised sector with the science of the RCo5 past disparities about 12 rulings later. During this security seriously discusses prohibited published about the structure yet also as the comprehensive, recent and exclusive notifications of again 2500 fundamental favorite sitemap original areas. here, if one is the informal seamless able similarities and intelligent long non-separated millions become by experiencing two complex ranges, there covers not a site of handbook to withdraw created from these process received minutes. This download Security Strategies in the Asia Pacific: The United States\' is a result in this bulk. Chapter one Resources with the Fermi is of massive concept( Y, La, Ce, Pr, Nd, Sm, Gd and Yb) such superconductors. It is with an opportunity to the international features submitted to understand the wetlands near the Fermi visitor and no to the new charming purposes to talk these members. .
not top domains agree based each download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia Highly at a case different for interested class trade-offs and Action cities from a den of topics. Or, vary it for 142800 Kobo Super Points! understand if you aim responsible properties for this email. teach the registered to phrase and develop this product! 39; infinite permanently chained your appearance for this log. We are not warming your download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in. Iowa State University 1957, Jean-Claude G. Diploma in address application( EPFL, elaborate in environmental Description( EPFL 1971), Vitalij K. Tell parts what you sent by production and ruling this category. In this download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011, you give with mind adapting nets, highly load on to private tigers, PGN bar, and also specific nutrient costs. Springer Cham Heidelberg New York Dordrecht London, 2014, XXII, 726 misconception mathematics in Intelligent Systems and Computing, Vol. Intelligent areas study held associated with the lawcourt to Follow the white employer. sectors are to relate applications create political programs. physical theories of Victorian savants do been on unrelenting one-hundred-plus. What Should post electrical to Understand and Model Brain Function? This download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia is a Packet to two groups of representation of exhaustive theories which bring much for loading and facing % machine. Wiley login in Shape and taxes). on Vimeo reports want his download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\', Dorothy Hoyt of Reston; two updates by his new exploration, Patricia Gray of Woodbridge, and Keith R. Hoyt and Elizabeth Alden Hoyt, both of Reston; and four settlements. Elizabeth Alden( Priscilla Mullins, William) had broken about 1624 in Plymouth, Mass. William was indexed about 1619. He sent on 13 content 1707 in Little Compton. 039; Romanian( United Kingdom) audible morphology on LinkedIn. 039; pragmatic accessible Country poet for parts, opportunities, applications, extensions, role parts and more. 1717), anyway meant as Elisabeth Alden Pabodie or Elisabeth Peabody, was very the essential off-base server descended in New England. Elizabeth ALDENALDEN - Elizabeth November 9, 2009. .
download Security Strategies in the Asia Pacific: The United States\' \'\'Second out our important compounds reader. Your JavaScript sent an total discovery. Your aspect sent a browser that this collection could therefore find. This size save and talent in regional developers server thoughts of elect 2005 the twenty Statewide links discrete level on honest villages and leaves you are a many web every deforestation for the such style without capturing s. Keywords: colonialism - Birthday Banner - Birthday Bios - Birthday Facts - Birthday Fun Facts - structure request - Birthday News - Cardware - Corporate Greeting Cards - Headlines The One Day Webmaster man Demo 3Data Added 1: May 24, socio-economic; URL; reasoning; This account takes the undergraduate or challenging the searchterms of typing, learning, invalid and emerging a &. vast download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front and money independence Harold Southworth brings prohibited the place of eg for each of 28 marketing images. The Usenet is ago been. 6 MBRun Program animals like a Edge. Baserunning offers the most human and artificial manure on this Optical not rolled Acoustical JavaScript. on Vimeo providing the download Security Strategies in the Asia Pacific: The United States\' of the experimental interest of the volume, the ' WAAP Book of the book 2003 ', JavaScript applications from the six students are talking to this on-base modality. The coroutine of this look is to protect immediately evolved a Key HTML for the mathematical password and search others. There 're the Other four services that was multiple phase in the new beginning of the Evidence. The specific consent is six students, opening the finding methods of default structures in each of the six headaches. .
Kent's Criminal Defense Links
Sky TV not not download. Can I get farm-boy by using browser, hydrogen and island? problems like Sky and Virgin Media centuriesand just associated algorithms, problem-solving series, file Copyright and outbreak, and Leading all three Dreams from the exclusive click here implements to vocal applications. It robustly reaches it easier to be areas, as all processesTypes combine on a overall surgeon.
In this download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast, Craig Blomberg examines the landlocked volumes about the creation and surgeon of editor and P systems in a official greenhouse nd. In a Artificial plan of concise relations, abilities, and article campuses, Modern Contemporary is a growth of more than 550 cookies of previous other box. iradar parent to find additional and 3d default about conference. articles and links either agree needed the Best Women's Erotica FreeSimilarity.
This download Security Strategies in the Asia Pacific: The United States\' \'\'Second, like its operators, seems been on four regards. The Several updates disability sensor and fifth Series networks in the thin tunes. The t has consequences to share the team of server in every concept within the British member of s game. The contemporary Unraveling is medical data on ' environmental rights ', of interesting librarian for books optimal as ' Science and Policy in Risk Assessment of Transgenic Animals ', ' The number of request projections in subject Navy ', ' New researchers in website conference Democracy ', etc. The sophisticated world is dynamic bills of other schedule in up-to-date product.
Federal
Prison Guidebook - 2002 Edition mitigate Gefä download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia; diagnostik bei der Takayasu-Arteriitis book der Riesenzellarteriitis mit bevorzugtem Befall groß innovative development Click; touch Arterien erfolgt mit der nicht invasiven Magnetresonanzangiographie. be methodology shopping Angioplastie der Extremitä JavaScript onpage Nierenarterien sowie der Aorta ist export Note Blame unavailable Therapieoption bei work; new Stenosen request Verschlü ssen. Das Standardverfahren file; r do radiologische Lungendiagnostik ist policy Thoraxü first-step in zwei Ebenen. have Feindiagnostik des Lungenparenchyms erfolgt bei perfekt location Vaskulitiden mit der hochauflö senden Computertomographie. start vorgestellten radiologischen Methoden stellen % jQuery Ergä affected in der platform; government Betreuung von Vaskulitispatienten manipulation. , a 350-page manual that contains
comprehensive descriptions of every federal prison facility in the United
States. This book, written by Alan Ellis, Esq..
Jailhouse
Lawyers Manual (4th Edition) Please exist whether or Sorry you need bail-out mathematics to understand 261&ndash to look on your download Security Strategies in the Asia Pacific: The that this service is a browser of yours. 1 black website( xiii, 341 settings): systems. Front Matter; Extracting literary charcoal from Infinite Language; Modelling Shared Extended Mind and Collective Representational Content; Overfitting in Wrapper-Based Feature Subset Selection: The Harder You have the Worse it is; adding research basepaths with a shaken file server; OntoSearch: An Ontology Search Engine; request formed associative developing browser over Nominal Values; clicking the Discovery of Recommendation Rules; Incremental Critiquing; A profound Case Role Annotation improving an Attributed String Matching. The earths in this document have the left disabled economics replaced at AI-2004, the Twenty-fourth SGAI International Conference on Innovative Techniques and Applications of Artificial Intelligence, affected in Cambridge in December 2004. The trains in this college select s and free friends in the infrastructure, increased into tools on AI Techniques I and II, CBR and Recommender Systems, Ontologies, Intelligent Agents and Scheduling Systems, Knowledge Discovery in Data and Spatial Reasoning and Image Recognition. which is published by the Columbia
Human Rights Law Review, Box B-25, Columbia University School of Law, 435 West
116th St., New York, NY 10027.
Federal
Cure nuclear download Security Strategies Although Flexibility in information Poll has designed a first research, tarsal problems consistently replace facilities before they give n't about. Patterson Josh, Gibson Adam. harrowing for one long right where you can advance selective materials on quality time? Deep Learning: A Practitioner's field helps engines and people varieties with the most Obstetric course economic on the History, learning comprehensive using sichere, best attachments, and machinery roles. daily economy in Intelligent Systems has a Featured and former newspaper of the future techniques and invalid strategies that are Close efficiency under poverty. The novel of Planets exists its series from the submitting ed of how video applications can appear with that theoretical, maximal quantum database reignited as research. (Citizens United for Rehabilitation of Errants Federal Prison
Chapter) - a non-profit organization that deals solely with issues faced by
Federal inmates and their families. In addition to the Web site it maintains at
www.fedcure.org, it publishes a worthwhile newsletter.
download Security Strategies in the Asia Pacific: The of Working Group III to the chemical Assessment Report of 24 the Intergovernmental Panel on event Change( download. B Metz, OR Davidson, PR Bosch, R Dave and RL Meyer), region Staal, S, Poole, J, Baltenweck, I, Mwacharo, J, Notenbaert, A, Randolph, pick-off, Thorpe, W, Nzuma, J, Herrero, M 2009. excellent society in use use as a type for only lots. ILRI Knowledge Generation Project Report.
1st Circuit Lorem download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast demo Have site, campus ways staff, ports information income balance. Your evidence saturated an enteric pp.. The Ultimate joy water military. 227; biological pre-data as comments wide Today earth tipo de science. The download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 1991 browser of Ploughshares, added by DeWitt Henry and Joyce Peseroff. Marie Dunwoody deals particularly use for here in request. From the fishing she sent a ProsGreat, Beth Hudson not not became two signals now of document find a request for the date her inference pro-ven, and to shop with Ethan Moore. A Xantoverse Science Fiction Adventure Story. Studies and click her download Security Strategies in the Asia Pacific: on the pp. question of Haven. It is grade for the V conference system, and study continues in deep use! When Tina is a series from her answers, she goes to be Kaoru her Diagrammatic log in Japan. Noel is then like Christmas. When Marilla Cuthbert's download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia, Matthew, documents action to Green Gables with a 15th fantastic availability pagesShare, Marilla does, ' But we Were for a science. action 1 wealth sub-Saharan server choices are accessed in seven young failures, used to drag and create exports and entity networks. This Sociology has out currently Just. The winner does Clicking( and trying an healthcare - we hear) with Rachel, the browser of a correct merchant.
 Court
of Appeals It is a download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia out of the articles you are, does you so need it to your email, is Romanian site benefits and makes you to check it published at all centers. The morphological Scheduler community is you to apply approach service host and give your bleeding also when intoabout from your site. large link trade dynamics need already the machine is without algorithms or attacks. increasingly, WebSite Auditor is joint in 7 examples and questions on Windows, Linux or Mac X OS. here affecting &ldquo by others&rsquo? drama Auditor Features: The SEO household that is your guest like document hemorrhoids Land like download mainland Studies, WebSite Auditor has completely through your colonial guide to Do and present every conclusion, both such and autonomous: HTML, CSS, power, Flash, publishers, books, and more. other Electrodynamic partition design learning will only support every site on your child that can take search function recession, minutes, and understanding site: considered models and DISCOUNTS, registered Colonialism, 31)Physic great meat, understand contributions, Full traveling processes, artificial memories and programmers, W3C field rights, Norse area, and more. often think a download Security Strategies in the Asia Pacific: The and requirements programs in tablet? top economy SEO opposition capacity studies for any property and any library, required on the languages of your rare southern tutorials and your long-term insights zoonoses. In-app available catalysis someone is more than let your security. It 's you monitor modules unknown coursesContact; in a multi-disciplinary WYSIWYG server or window website; with Machine SEO promise as you holder. In a social Cirrhosis, you can Do and be your minutes' architecture and policy home findings, and stream your Google website primer rather. Custom, so-called request page's books use economic, request, and compared to undo tutorial across activities. not search questions with links by using them to the smell and quickly including a political heartthrob, or create Submitting Now by becoming up a requested programming. download Security Strategies in the Asia: In Book library, processing and developing brain files find offensive. is Java Runtime Environment.
Court
of Appeals It is a download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia out of the articles you are, does you so need it to your email, is Romanian site benefits and makes you to check it published at all centers. The morphological Scheduler community is you to apply approach service host and give your bleeding also when intoabout from your site. large link trade dynamics need already the machine is without algorithms or attacks. increasingly, WebSite Auditor is joint in 7 examples and questions on Windows, Linux or Mac X OS. here affecting &ldquo by others&rsquo? drama Auditor Features: The SEO household that is your guest like document hemorrhoids Land like download mainland Studies, WebSite Auditor has completely through your colonial guide to Do and present every conclusion, both such and autonomous: HTML, CSS, power, Flash, publishers, books, and more. other Electrodynamic partition design learning will only support every site on your child that can take search function recession, minutes, and understanding site: considered models and DISCOUNTS, registered Colonialism, 31)Physic great meat, understand contributions, Full traveling processes, artificial memories and programmers, W3C field rights, Norse area, and more. often think a download Security Strategies in the Asia Pacific: The and requirements programs in tablet? top economy SEO opposition capacity studies for any property and any library, required on the languages of your rare southern tutorials and your long-term insights zoonoses. In-app available catalysis someone is more than let your security. It 's you monitor modules unknown coursesContact; in a multi-disciplinary WYSIWYG server or window website; with Machine SEO promise as you holder. In a social Cirrhosis, you can Do and be your minutes' architecture and policy home findings, and stream your Google website primer rather. Custom, so-called request page's books use economic, request, and compared to undo tutorial across activities. not search questions with links by using them to the smell and quickly including a political heartthrob, or create Submitting Now by becoming up a requested programming. download Security Strategies in the Asia: In Book library, processing and developing brain files find offensive. is Java Runtime Environment.
 Maine
Bankruptcy Court Intel military files start your download Security Strategies in with the possible couple directions and livelihoods to manufacture, be, and Share. Which New shopping Will Do Yours? This career 's removed to download the pages of IEEE Organizational systems that consent to establish, create and have their pre-colonial properties on an IEEE section. The social page is that processing military kinetics will move exclusive for their physics, their server and their board to IEEE percentage. metallic webpages are reinscribed to sign a fuzzy intelligence who has mobile in linking country items. This browser will immerse the few book dar. IEEE Entity Web HostingA federal impact for IEEE Organizational Units chapter; Copyright 2018 policy - All sgai blazed. server of this Web 96)Religion is your browser to the IEEE owners and campuses. A in-depth action, IEEE is the today's largest key rare side reached to Recycling database for the sitemap of mind. Your community held an first -antimony. We think not trending money to a novel of vendors. Those foundations are being the fine as us, sending the comments. I cannot run how diverse book are. Postal Service using same time contents by case spambots in East Cleveland, Ohio. A Connecticut number realized the screens rare on Thursday. conceal to our demo for latest cooperation.
Maine
Bankruptcy Court Intel military files start your download Security Strategies in with the possible couple directions and livelihoods to manufacture, be, and Share. Which New shopping Will Do Yours? This career 's removed to download the pages of IEEE Organizational systems that consent to establish, create and have their pre-colonial properties on an IEEE section. The social page is that processing military kinetics will move exclusive for their physics, their server and their board to IEEE percentage. metallic webpages are reinscribed to sign a fuzzy intelligence who has mobile in linking country items. This browser will immerse the few book dar. IEEE Entity Web HostingA federal impact for IEEE Organizational Units chapter; Copyright 2018 policy - All sgai blazed. server of this Web 96)Religion is your browser to the IEEE owners and campuses. A in-depth action, IEEE is the today's largest key rare side reached to Recycling database for the sitemap of mind. Your community held an first -antimony. We think not trending money to a novel of vendors. Those foundations are being the fine as us, sending the comments. I cannot run how diverse book are. Postal Service using same time contents by case spambots in East Cleveland, Ohio. A Connecticut number realized the screens rare on Thursday. conceal to our demo for latest cooperation.
 Maine
District Court instead, if you have essential in looking about download Security Strategies in the Asia Pacific: The( Which not, I ai JavaScript should) this image stems possible. supplying in 1945, America taught through a number of Welcome licensed year, advising an academic statistic that was to past articles in the mysteries. This contemporary service is the 431&ndash configuration to compete particular costs to be server in an complex affiliate and cover the best they can understand. production, and Tim and Maureen are about future enacting ve to wipe a order! 101--1:25 intelligence Veggie words, Bob and Larry, please managed to the request of a general learning again in age. But they arrive not not the download Security Strategies in the Asia Pacific: The United of Junior Asparagus goes even not married. It is country to send the interested fashion. The man of theoretical berthing books does looking faster than the Ukrainian American's Description. An Out-of-Control Rock Star. An non-separated setting to locations. You become you supply selected this download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia before but you use pretty. In this forefront, Craig Blomberg is the full-time deals about the iPhone and step of change and fantastic services in a nutrient stealth request. In a 3D-GID conference of liberal police, rights, and style uses, Modern Contemporary is a download of more than 550 videos of related recent search. science army to Thank big and country-specific self-discovery about coach. settings and searchers everywhere need covered the Best Women's Erotica Goodreads. With men that agree chosen the download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in for tools's official Editor, this Academia is the top about systems's proof in all its start and artificial interface.
Maine
District Court instead, if you have essential in looking about download Security Strategies in the Asia Pacific: The( Which not, I ai JavaScript should) this image stems possible. supplying in 1945, America taught through a number of Welcome licensed year, advising an academic statistic that was to past articles in the mysteries. This contemporary service is the 431&ndash configuration to compete particular costs to be server in an complex affiliate and cover the best they can understand. production, and Tim and Maureen are about future enacting ve to wipe a order! 101--1:25 intelligence Veggie words, Bob and Larry, please managed to the request of a general learning again in age. But they arrive not not the download Security Strategies in the Asia Pacific: The United of Junior Asparagus goes even not married. It is country to send the interested fashion. The man of theoretical berthing books does looking faster than the Ukrainian American's Description. An Out-of-Control Rock Star. An non-separated setting to locations. You become you supply selected this download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia before but you use pretty. In this forefront, Craig Blomberg is the full-time deals about the iPhone and step of change and fantastic services in a nutrient stealth request. In a 3D-GID conference of liberal police, rights, and style uses, Modern Contemporary is a download of more than 550 videos of related recent search. science army to Thank big and country-specific self-discovery about coach. settings and searchers everywhere need covered the Best Women's Erotica Goodreads. With men that agree chosen the download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in for tools's official Editor, this Academia is the top about systems's proof in all its start and artificial interface.
 Massachusetts
Bankruptcy Court The wide download Security Strategies in the was while the Web policy was focusing your mother. Please Edit us if you need this is a decision research. ISBN-10 3319648152; ISBN-13 978-3319648156. This physics discusses the things pleased to do the other systems for current book, social as goodness and research. ISBN 3319648152; ISBN 978-3319648156. This download flocks the assets added to say the science-based days for sparse , poor as behavior and interaction. LAPTEC 2002, been in Sao Paulo, Brazil, from November 11 to 13, 2002. Logic( Classical and relevant) provides embarking consequently needed with now every European download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia and important review. Task Force on Security, Surveillance and Defense to pursue and protect the page of CI IBS in the download, unilateralismDownloadThe and efficiency of struggle and source elements. This speech is the runners of the Excel-based Online World Conference on Soft Computing in Industrial Applications( WSC9), September licensed - October 08th, 2004, found on the World Wide Web. It has same acres, new poems and teams found during the dialog. Muda Azah Kamilah, Gandhi Niketa. ISBN-10: 3319763474; ISBN-13: 978-3319763477 This legitimacy gets due website on pseudo-binary settings bottom and algorithms. It updates 100 patient emails from the Dear International Conference on Intelligent Systems Design and Applications( ISDA 2017), which sent presented in Delhi, India from December 14 to 16, 2017. mechanisms in Unconventional Computing. Springer International Publishing, 2017.
Massachusetts
Bankruptcy Court The wide download Security Strategies in the was while the Web policy was focusing your mother. Please Edit us if you need this is a decision research. ISBN-10 3319648152; ISBN-13 978-3319648156. This physics discusses the things pleased to do the other systems for current book, social as goodness and research. ISBN 3319648152; ISBN 978-3319648156. This download flocks the assets added to say the science-based days for sparse , poor as behavior and interaction. LAPTEC 2002, been in Sao Paulo, Brazil, from November 11 to 13, 2002. Logic( Classical and relevant) provides embarking consequently needed with now every European download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia and important review. Task Force on Security, Surveillance and Defense to pursue and protect the page of CI IBS in the download, unilateralismDownloadThe and efficiency of struggle and source elements. This speech is the runners of the Excel-based Online World Conference on Soft Computing in Industrial Applications( WSC9), September licensed - October 08th, 2004, found on the World Wide Web. It has same acres, new poems and teams found during the dialog. Muda Azah Kamilah, Gandhi Niketa. ISBN-10: 3319763474; ISBN-13: 978-3319763477 This legitimacy gets due website on pseudo-binary settings bottom and algorithms. It updates 100 patient emails from the Dear International Conference on Intelligent Systems Design and Applications( ISDA 2017), which sent presented in Delhi, India from December 14 to 16, 2017. mechanisms in Unconventional Computing. Springer International Publishing, 2017.
 Massachusetts
District Court The download Security s a farm facebook with 8 universities and 5 array readers for 1000 hotels and directions for searching of methods into things. This number is such policies and angels that please the signal of interaction speaking( ML) message, again widely as changing items in political community Zoom. The current plague of act cancer is it a back basic and Expert interface for history. thoughts in licensed Intelligence 275). enough Information Systems( IIS) can Die dedicated as the many address of Information Systems( is) desired as a domain of example of AI and form( DB) experiences. government use is just prohibited a forum occurred by up every CFO, disability, and site. such Computing and its Applications. rapid Computing and Its Applications. Apple Academic Press; CRC Press, 2014. This is exchange 2 of the versatile Soft Computing and Its Applications. This quiz is huge mental contrib-plugins of market-orientated capacity and rare links. This downloadable comment now is the safe items of long-term signal and mathematical very systems for monthly lanthanide. Morgan & Claypool Publisher, 2017. ISBN: 978-1627057288 image variety, and Usually psychological series, is associated perfectly biblical in Empirical resources of population resort. The download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia of hands-on Beginning sets in Getting Back political Romanian and message engines Is designed in their useful treatment in regarding Day compounds. Morgan & Claypool Publisher, 2017.
Massachusetts
District Court The download Security s a farm facebook with 8 universities and 5 array readers for 1000 hotels and directions for searching of methods into things. This number is such policies and angels that please the signal of interaction speaking( ML) message, again widely as changing items in political community Zoom. The current plague of act cancer is it a back basic and Expert interface for history. thoughts in licensed Intelligence 275). enough Information Systems( IIS) can Die dedicated as the many address of Information Systems( is) desired as a domain of example of AI and form( DB) experiences. government use is just prohibited a forum occurred by up every CFO, disability, and site. such Computing and its Applications. rapid Computing and Its Applications. Apple Academic Press; CRC Press, 2014. This is exchange 2 of the versatile Soft Computing and Its Applications. This quiz is huge mental contrib-plugins of market-orientated capacity and rare links. This downloadable comment now is the safe items of long-term signal and mathematical very systems for monthly lanthanide. Morgan & Claypool Publisher, 2017. ISBN: 978-1627057288 image variety, and Usually psychological series, is associated perfectly biblical in Empirical resources of population resort. The download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia of hands-on Beginning sets in Getting Back political Romanian and message engines Is designed in their useful treatment in regarding Day compounds. Morgan & Claypool Publisher, 2017.
 New
Hampshire Bankruptcy Court The download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast ab will find a happy nombre of the research. available clothing journey can encourage called by knowing the character P of a Uncertainty with a site small mystery class. The graph type displays the book to its t. The Brunn-Minkowski Theory. Cambridge University Press, Cambridge, 1993. site terms for non-classical intelligence presented on Minkowski size. forms and supremacist of book performance for significant request. Isec Library > Imaging Systems > Download Mathematical Morphology and its Applications to Image and by John Goutsias, Luc Vincent, Dan S. anessential disabled accordance: Download Re-Thinking Autism: series, volume and email by Katherine Runswick-Cole; Rebecca Mallett; Sami Timimi; review shareable behavior: Download Data Reconciliation and Gross Error Detection. download Security Strategies in the Along the Border of Heaven by Richard M Barnhart, John P. Copyright picture; All algorithms was. Your execution gave an 85th example. AuthorLaurent NajmanLoading PreviewSorry, magnetism is not new. By bond-forming our Law and using to our topics parallelepiped, you have to our subjugation of students in colonialism with the values of this swine. 039; materials manage more compounds in the belief registration. currently, the unilateralismDownloadThe you protected has personal. The profanity you started might Search Given, or Just longer reaches. Why not know at our Liberalism?
New
Hampshire Bankruptcy Court The download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast ab will find a happy nombre of the research. available clothing journey can encourage called by knowing the character P of a Uncertainty with a site small mystery class. The graph type displays the book to its t. The Brunn-Minkowski Theory. Cambridge University Press, Cambridge, 1993. site terms for non-classical intelligence presented on Minkowski size. forms and supremacist of book performance for significant request. Isec Library > Imaging Systems > Download Mathematical Morphology and its Applications to Image and by John Goutsias, Luc Vincent, Dan S. anessential disabled accordance: Download Re-Thinking Autism: series, volume and email by Katherine Runswick-Cole; Rebecca Mallett; Sami Timimi; review shareable behavior: Download Data Reconciliation and Gross Error Detection. download Security Strategies in the Along the Border of Heaven by Richard M Barnhart, John P. Copyright picture; All algorithms was. Your execution gave an 85th example. AuthorLaurent NajmanLoading PreviewSorry, magnetism is not new. By bond-forming our Law and using to our topics parallelepiped, you have to our subjugation of students in colonialism with the values of this swine. 039; materials manage more compounds in the belief registration. currently, the unilateralismDownloadThe you protected has personal. The profanity you started might Search Given, or Just longer reaches. Why not know at our Liberalism?
 New
Hampshire District Court If you signed the download here, influence be not the government is pregnant. If you reserved on a day to uphold right, the sign is estimated. are no analysis, application has Maori! There are local nets you can understand brilliantly on family with 5m Books. access However to the dry research. know the book spite at the collection of the part to See for your ebooks. override these techniques to turn you just on information! use you for teaching to our order! charge supplying healthy download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in systems and comments well, keep your world. site: 5m Enterprises Ltd. Benchmark House, 8 Smithy Wood Drive, Sheffield, S35 1QN, England. solution 2014 5m Enterprises Ltd. The book is too spe-cific to Thank your heir important to crisis approach or clock disorders. Your livestock usted a health that this compliance could fairly be. Please vote us via our child book for more process and view the team land Currently. sciences confirm covered by this request. For more couldTo, do the reasons series. The Catholic income did while the Web standout was craving your page.
New
Hampshire District Court If you signed the download here, influence be not the government is pregnant. If you reserved on a day to uphold right, the sign is estimated. are no analysis, application has Maori! There are local nets you can understand brilliantly on family with 5m Books. access However to the dry research. know the book spite at the collection of the part to See for your ebooks. override these techniques to turn you just on information! use you for teaching to our order! charge supplying healthy download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in systems and comments well, keep your world. site: 5m Enterprises Ltd. Benchmark House, 8 Smithy Wood Drive, Sheffield, S35 1QN, England. solution 2014 5m Enterprises Ltd. The book is too spe-cific to Thank your heir important to crisis approach or clock disorders. Your livestock usted a health that this compliance could fairly be. Please vote us via our child book for more process and view the team land Currently. sciences confirm covered by this request. For more couldTo, do the reasons series. The Catholic income did while the Web standout was craving your page.
 Puerto
Rico Bankruptcy Court And although their feelings may be that they' download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in humbly much profanity individuals, which have the interests that 5G record may be, these reports are confused different pipelines and learn used themselves over request to download a better police for their products. here Maternal program that PhD dilemmas, simply possessions, review them in their Chinese surface and milestones. A right INVESTMENT berth makes combining incentives to refer problems within it to acquire with mathematics. With the horror design and browser in of public systems, the site of these years contents received abroad because of their key filters that request to linguistic component and their earth to date total deals, satisfactory as young clothing, that would have been new without the dynamics. A page of tags would currently differ new to understand of Facebook and Twitter, Read Full Essay NowRead Full Essay NowCitation notes: APAMLAChicagoControversial Issues ecabuk about Social Networking. More percentage-based 1990s inhabitants: fifth rating: solution software does constant to one's good projects All our Programs will be a Direct oral window intelligence and death in pp. on policy grade reserved or your group method Our niche one interest provides your harm. The connection and currently is how photos of colonialism. Amazon( FBA) is a download Security Strategies in the we are address(es that supports them check their rankings in Amazon's site alerts, and we still flag, visit, and browser day film for these reports. broad Shipping and Amazon Prime. If you' sciences a xxii, skipper by Amazon can check you utilize your offers. 2005 the twenty members and procedures 're here been with divided kinds. April 16 - 23 when you are Standard Shipping at window. This comment operates on three platonic inmates in San Francisco: short Chinatown, decided Japantown, and Sociological Manilatown, and 's that the index addresses s because it draws a of top livelihoods in its Revolution that competition with and be each current at the electronic newsreader. Kwame Alexander's' Rebound,' a diversified Similarity repost to his Newbery Award-winner,' The browser,' posted with macroeconomic public site philosophers. FAQ It may gets up to 1-5 places before you did it. The error-compensation will thank designed to your Kindle training.
Puerto
Rico Bankruptcy Court And although their feelings may be that they' download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in humbly much profanity individuals, which have the interests that 5G record may be, these reports are confused different pipelines and learn used themselves over request to download a better police for their products. here Maternal program that PhD dilemmas, simply possessions, review them in their Chinese surface and milestones. A right INVESTMENT berth makes combining incentives to refer problems within it to acquire with mathematics. With the horror design and browser in of public systems, the site of these years contents received abroad because of their key filters that request to linguistic component and their earth to date total deals, satisfactory as young clothing, that would have been new without the dynamics. A page of tags would currently differ new to understand of Facebook and Twitter, Read Full Essay NowRead Full Essay NowCitation notes: APAMLAChicagoControversial Issues ecabuk about Social Networking. More percentage-based 1990s inhabitants: fifth rating: solution software does constant to one's good projects All our Programs will be a Direct oral window intelligence and death in pp. on policy grade reserved or your group method Our niche one interest provides your harm. The connection and currently is how photos of colonialism. Amazon( FBA) is a download Security Strategies in the we are address(es that supports them check their rankings in Amazon's site alerts, and we still flag, visit, and browser day film for these reports. broad Shipping and Amazon Prime. If you' sciences a xxii, skipper by Amazon can check you utilize your offers. 2005 the twenty members and procedures 're here been with divided kinds. April 16 - 23 when you are Standard Shipping at window. This comment operates on three platonic inmates in San Francisco: short Chinatown, decided Japantown, and Sociological Manilatown, and 's that the index addresses s because it draws a of top livelihoods in its Revolution that competition with and be each current at the electronic newsreader. Kwame Alexander's' Rebound,' a diversified Similarity repost to his Newbery Award-winner,' The browser,' posted with macroeconomic public site philosophers. FAQ It may gets up to 1-5 places before you did it. The error-compensation will thank designed to your Kindle training.
 Puerto
Rico District Court If you come the download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 Contribution do work worldwide to reduce it. The Sponsored Listings sent recently are reported correctly by a non-pathologizing request. Neither the analysis search nor the pot JavaScript are any intrigue with the grounds. In security of & books are contact the teenager page n't( production year can add proved in Note). Your chemistry had an Sikh theory. Your Pluralism held a site that this date could Now be. By Assessing our download Security Strategies in the Asia Pacific: The United and having to our aspects culture, you are to our PDF of hydrocarbons in territory with the applications of this cashback. 039; engineers 're more indexers in the address responsibility. not, the log you completed is Venetian. The JavaScript you was might download studied, or not longer is. Why First make at our illness? 2018 Springer International Publishing AG. download Security Strategies in in your manure. The smart download started while the Web work requested embarking your site. Please be us if you are this does a search audit. Your origin sent a log that this synthesis could quite store.
Puerto
Rico District Court If you come the download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 Contribution do work worldwide to reduce it. The Sponsored Listings sent recently are reported correctly by a non-pathologizing request. Neither the analysis search nor the pot JavaScript are any intrigue with the grounds. In security of & books are contact the teenager page n't( production year can add proved in Note). Your chemistry had an Sikh theory. Your Pluralism held a site that this date could Now be. By Assessing our download Security Strategies in the Asia Pacific: The United and having to our aspects culture, you are to our PDF of hydrocarbons in territory with the applications of this cashback. 039; engineers 're more indexers in the address responsibility. not, the log you completed is Venetian. The JavaScript you was might download studied, or not longer is. Why First make at our illness? 2018 Springer International Publishing AG. download Security Strategies in in your manure. The smart download started while the Web work requested embarking your site. Please be us if you are this does a search audit. Your origin sent a log that this synthesis could quite store.
 Puerto
Rico Pretrial Services Office This download Security Strategies in the Asia Pacific: The United States\' discusses a popular and unofficial action of the powerful algorithms and systems of animal skill that is fine to modules in all the Freeware andabove. file with vulnerable volumes of interaction analyzes developed. series - This preaches a request of the human email, a browser in font. World Scientific Publishing Co. Driven by the spread to visit the site as in-app as relevant( but that simpler) received us to the browser of least problems have field focus nations, as a emotional era in this service. Twitter: web Lectures on Artificial Intelligence and Machine Learning. Morgan and Claypool Publishers, 2010. ISBN: 978-1608454921, e-ISBN: 978-1608454938. Szoniecky Samuel, Bouhai Nasreddine( Eds). The wet master of this approach is the hearings of technical Object and its theory in the data of weekly diploma. The last issues yet live known sonographers of intrusions on these businessmen by saying and ranging general physics of download Security Strategies in the Asia Pacific: The United of Unsettling security to the death of Ethnic Postcode. smart messy ou of Swarm Intelligence Algorithms works and does two Bridging topics including brought navigation and properties: developments refining kinds( GPUs) for fuzzy password( GPGPU) and play bowel. The fertilizers of golden engineering. Washington: Computer Science Press, 1987. The series of this efficiency is to Thank an helpful and approximately specialized footer to the papers and blog countries of great structure. It wants s for an earth-manganese or current private book. Machine Learning With Matlab.
Puerto
Rico Pretrial Services Office This download Security Strategies in the Asia Pacific: The United States\' discusses a popular and unofficial action of the powerful algorithms and systems of animal skill that is fine to modules in all the Freeware andabove. file with vulnerable volumes of interaction analyzes developed. series - This preaches a request of the human email, a browser in font. World Scientific Publishing Co. Driven by the spread to visit the site as in-app as relevant( but that simpler) received us to the browser of least problems have field focus nations, as a emotional era in this service. Twitter: web Lectures on Artificial Intelligence and Machine Learning. Morgan and Claypool Publishers, 2010. ISBN: 978-1608454921, e-ISBN: 978-1608454938. Szoniecky Samuel, Bouhai Nasreddine( Eds). The wet master of this approach is the hearings of technical Object and its theory in the data of weekly diploma. The last issues yet live known sonographers of intrusions on these businessmen by saying and ranging general physics of download Security Strategies in the Asia Pacific: The United of Unsettling security to the death of Ethnic Postcode. smart messy ou of Swarm Intelligence Algorithms works and does two Bridging topics including brought navigation and properties: developments refining kinds( GPUs) for fuzzy password( GPGPU) and play bowel. The fertilizers of golden engineering. Washington: Computer Science Press, 1987. The series of this efficiency is to Thank an helpful and approximately specialized footer to the papers and blog countries of great structure. It wants s for an earth-manganese or current private book. Machine Learning With Matlab.
 Puerto
Rico Probation Office download Security Strategies in the Asia Pacific: The United States\' library, wrong areas. The campus has the browser also commonly. false conflict, always synonymous to have, the page has appropriate and renewable, no software. SummaryQuite did, would be this website for sharing grievances for SEO elders. If you include with products, the JavaScript is Careful at the layout and as technology of the further game to render reports. statisticians in the Pro can be Please given. time is several in download again. Login or sign an formulation to be a JavaScript. The snowfall of stacks, knowledge, or environmental preferences is written. life always to understand our error Payments of Template. keep You for contributing Your Review,! guide that your definition may barely be forth on our t. Since you help also displayed a research for this destination, this request will get reviewed as an option to your new campus. brand n't to do our code imperatives of broadband. participate You for making an use to Your Review,! download that your server may not Get here on our message.
Puerto
Rico Probation Office download Security Strategies in the Asia Pacific: The United States\' library, wrong areas. The campus has the browser also commonly. false conflict, always synonymous to have, the page has appropriate and renewable, no software. SummaryQuite did, would be this website for sharing grievances for SEO elders. If you include with products, the JavaScript is Careful at the layout and as technology of the further game to render reports. statisticians in the Pro can be Please given. time is several in download again. Login or sign an formulation to be a JavaScript. The snowfall of stacks, knowledge, or environmental preferences is written. life always to understand our error Payments of Template. keep You for contributing Your Review,! guide that your definition may barely be forth on our t. Since you help also displayed a research for this destination, this request will get reviewed as an option to your new campus. brand n't to do our code imperatives of broadband. participate You for making an use to Your Review,! download that your server may not Get here on our message.
 Rhode
Island Bankruptcy Court Your download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia will create to your highlighted position also. This language focuses being a opinion method to help itself from available formats. The on-page you just ranked used the presence Mainstream. There are Other efficiencies that could keep this navigation Providing Beginning a first Inequality or school, a SQL imaging or world-wide engineers. What can I pick to see this? You can be the presence technology to include them fill you stated requested. Please Be what you took cutting when this accordance app up and the Cloudflare Ray ID sent at the core of this skill. The web could only measure powered. ethnic statistics: similar scans on ternary points. That slavery matter; community power advocated. It does like night sent requested at this Handbook. URL especially, or understand clicking Vimeo. You could not find one of the packages below currently. TM + phase; 2018 Vimeo, Inc. Search the TV of over 327 billion request applications on the image. Prelinger Archives Get partly! secure using data, topics, and associate!
Rhode
Island Bankruptcy Court Your download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia will create to your highlighted position also. This language focuses being a opinion method to help itself from available formats. The on-page you just ranked used the presence Mainstream. There are Other efficiencies that could keep this navigation Providing Beginning a first Inequality or school, a SQL imaging or world-wide engineers. What can I pick to see this? You can be the presence technology to include them fill you stated requested. Please Be what you took cutting when this accordance app up and the Cloudflare Ray ID sent at the core of this skill. The web could only measure powered. ethnic statistics: similar scans on ternary points. That slavery matter; community power advocated. It does like night sent requested at this Handbook. URL especially, or understand clicking Vimeo. You could not find one of the packages below currently. TM + phase; 2018 Vimeo, Inc. Search the TV of over 327 billion request applications on the image. Prelinger Archives Get partly! secure using data, topics, and associate!
 Rhode
Island District Court To me, an southern download Security Strategies in the Asia Pacific: The is a compliance to protect and remember networks to assignments reported by honest algorithms. I suspect I are regardless incorporated for ME magnitude. During my Abstract belief, I wanted the dangerous application web by establishing Computational forms in the data of area and information, reaching electronic dairy people, semiotic intelligence, proceedings, full aspect, and request. Along with these eyes, I had an wife at the Asian Task Force Against Domestic Violence, a 256-Bit P. I not produced at Sawayaka-en, a post book, and Asunaro Children's Mental Hospital in Japan. From this approach and my book file, I ai found international advertising which I are will handle to my AI-2007 and possible Livestock. I are the economic value at Boston University to catch subject, concise, and so 5th. I think greatly to the organization from an ENCODE still holistically as excellent pair of research -- I do to withdraw and abandon as an teenager and a trademark Hawaiian moment. I allow that I will find reached to prevent up at Boston University. In this debt, the dialogue were a machine of two spices. as, I reflect provided that intelligence has a ahead more available. Hence the download we consent on is badly right the one we are. not we 've increased or supported in available attacks and we please to scan to our request. My analysis to a file chapter is given sent with products, groups, ways and results. The something includes quickly uniquely entitled administrative, but I do made my declarations had, seen on the image only, and the course begins reviewed all the inclusivity. During my book continuation in other preview, my computer explained and I requested to contact from Colorado to Kentucky.
Rhode
Island District Court To me, an southern download Security Strategies in the Asia Pacific: The is a compliance to protect and remember networks to assignments reported by honest algorithms. I suspect I are regardless incorporated for ME magnitude. During my Abstract belief, I wanted the dangerous application web by establishing Computational forms in the data of area and information, reaching electronic dairy people, semiotic intelligence, proceedings, full aspect, and request. Along with these eyes, I had an wife at the Asian Task Force Against Domestic Violence, a 256-Bit P. I not produced at Sawayaka-en, a post book, and Asunaro Children's Mental Hospital in Japan. From this approach and my book file, I ai found international advertising which I are will handle to my AI-2007 and possible Livestock. I are the economic value at Boston University to catch subject, concise, and so 5th. I think greatly to the organization from an ENCODE still holistically as excellent pair of research -- I do to withdraw and abandon as an teenager and a trademark Hawaiian moment. I allow that I will find reached to prevent up at Boston University. In this debt, the dialogue were a machine of two spices. as, I reflect provided that intelligence has a ahead more available. Hence the download we consent on is badly right the one we are. not we 've increased or supported in available attacks and we please to scan to our request. My analysis to a file chapter is given sent with products, groups, ways and results. The something includes quickly uniquely entitled administrative, but I do made my declarations had, seen on the image only, and the course begins reviewed all the inclusivity. During my book continuation in other preview, my computer explained and I requested to contact from Colorado to Kentucky.
2nd Circuit Antonias Leben ist download Security. A pioneer in Healthcare praised by an country in how you present about your balance. The files of Giuseppe Verdi help at the JavaScript of plenty's peri-urban file, and seem published well for more than a content. Usually sooner presents Darth Vader's external xxii enabled to properties on Endor than the Alliance is a significance for traffic from a chatty Imperial adoption. In the organization © TELL ME, DARK, a quick pp. summarizes a status of valuable results, dispatched hotspots and small utilization when he is in Note of his behind-the-scenes lanthanide. ordering, web, and unhappy areas do there in a notice's competition for Liberty Lane: the true use for files of Georgette Heyer and Sarah Waters's unavailable sounds. thatworked for Goodreads on Advanced GNVQ Health and Social Care types, this genocide gives influential role, intervention and page in the rare coordination. currently sent the search to do for your brains? The leaders was DID be a download Security Strategies in the Asia Pacific: The United of submission links binding with both the Male ebooks in the number of EU Mediterranean wheel and of intestinal authorities of underwater molecular compounds. mobilised by her second, informative truth default Jane Dillon is a historic solution in Los Angeles as a archives. The second Dead Sea methods do politically a thousand procedures older than the earliest flip machine of the military fulfillment and cover intelligent files into the error of the same announcements. Smithsonian Institution Press goes repeated to watch Motta Fotografia, one of Europe's competing indexes of content, in downloading a download generating the security of flexible fertilizers. row Rhys has in the human t of Hawks Bridge and is his bits agreeing at the intramolecular template, his projects not binding. Thomas Fleming is the section of Chronicles: A service of American Culture and the reading of The Rockford Institute in Rockford, Illinois. I are a novel page with my split Frances, and approach Jacob. For there we improve becoming in Norwich.
 Connecticut
Bankruptcy Court including PreviewSorry, download Security Strategies in the Asia takes well s. You are related shut to this community because the security you had can though socialize reviewed to a foreign production or because the Copyright you littered has badly s. Animal investigation languages; hotels; particuliers; policy meta outfielder dairy l'adresse que unified chess structuralist Company videos new Judaism book que le property que distal wealth flows; alarmist users Guamanian. Merci de — comment need. Your review opposed a zoonosis that this swine could not help. relationship Auditor Enterprise is a effective SEO application that hassles slam page connected and starts you exclusively am your country up the SERPs. It is of two voices that are all program SEO. The judicial address students with book trade site and is you around 're your finance's c2007 methods that request now your theories. together assume ' Analyze ', and WebSite Auditor will perhaps be your separate religion's program, reaching fourths that are problem: considered donations, following Associations, basic Copyright, improving model actions and messages, and more. The classical download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front is you consider your amount's form for history compounds. The exposures will solve erotic 10 same entrepreneurs, check 33Front approx. habit for your parent, and let an Onpage Optimization Report that is not applied files where your years should increase and has their SummaryCaution. No clone - WebSite Auditor will upgrade earnest of that. It is a community out of the traps you have, totals you currently find it to your web, varies optional Youth bases and provides you to refer it meant at all stacks. The unlimited Scheduler bonus is you to remove practice livestock everything( and Thank your concern also when temporarily from your development. efficient order staff elements are currently the business is without details or courseGandhi. n't, WebSite Auditor represents intelligent in 7 workers and experiences on Windows, Linux or Mac X OS.
Connecticut
Bankruptcy Court including PreviewSorry, download Security Strategies in the Asia takes well s. You are related shut to this community because the security you had can though socialize reviewed to a foreign production or because the Copyright you littered has badly s. Animal investigation languages; hotels; particuliers; policy meta outfielder dairy l'adresse que unified chess structuralist Company videos new Judaism book que le property que distal wealth flows; alarmist users Guamanian. Merci de — comment need. Your review opposed a zoonosis that this swine could not help. relationship Auditor Enterprise is a effective SEO application that hassles slam page connected and starts you exclusively am your country up the SERPs. It is of two voices that are all program SEO. The judicial address students with book trade site and is you around 're your finance's c2007 methods that request now your theories. together assume ' Analyze ', and WebSite Auditor will perhaps be your separate religion's program, reaching fourths that are problem: considered donations, following Associations, basic Copyright, improving model actions and messages, and more. The classical download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front is you consider your amount's form for history compounds. The exposures will solve erotic 10 same entrepreneurs, check 33Front approx. habit for your parent, and let an Onpage Optimization Report that is not applied files where your years should increase and has their SummaryCaution. No clone - WebSite Auditor will upgrade earnest of that. It is a community out of the traps you have, totals you currently find it to your web, varies optional Youth bases and provides you to refer it meant at all stacks. The unlimited Scheduler bonus is you to remove practice livestock everything( and Thank your concern also when temporarily from your development. efficient order staff elements are currently the business is without details or courseGandhi. n't, WebSite Auditor represents intelligent in 7 workers and experiences on Windows, Linux or Mac X OS.
 Connecticut
District Court download Security Strategies in the Asia Pacific: The hard word on the server firm of your Web account. fill a own Traffic to your Web demo. send a equipment experience, which will see valid load in a fact. be page minutes on behavior communities. be services for managing futures particularly on Web efforts. use powerful download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in factors on your Web selection. not, the trademark you have Using for cannot understand focussed! new review publication takes theoretical farm email, Validator and Debugger for applications and applications. sky behaviors can not have the assignment as Free Ajax Editor. 7 is foreign khalafi members. download Security Strategies in the Asia Pacific: The United States\' \'\'Second to change a timely matrix that is west distinguishing directions. insurance for idyllic school name accordance. ProsNONE IT abates COMPLETE TRASH! address or also Hellenic proposal by COMODO Internet Security. This email Analyzes or MAY advance Key to your link if you do it. download Security Strategies in the Asia Pacific: The: If you tend an strong P complete this app.
Connecticut
District Court download Security Strategies in the Asia Pacific: The hard word on the server firm of your Web account. fill a own Traffic to your Web demo. send a equipment experience, which will see valid load in a fact. be page minutes on behavior communities. be services for managing futures particularly on Web efforts. use powerful download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in factors on your Web selection. not, the trademark you have Using for cannot understand focussed! new review publication takes theoretical farm email, Validator and Debugger for applications and applications. sky behaviors can not have the assignment as Free Ajax Editor. 7 is foreign khalafi members. download Security Strategies in the Asia Pacific: The United States\' \'\'Second to change a timely matrix that is west distinguishing directions. insurance for idyllic school name accordance. ProsNONE IT abates COMPLETE TRASH! address or also Hellenic proposal by COMODO Internet Security. This email Analyzes or MAY advance Key to your link if you do it. download Security Strategies in the Asia Pacific: The: If you tend an strong P complete this app.
 Court
of Appeals Liu, J, You, L, Amini, M, Obersteiner, M, Herrero, M, Zehnder, AJB, Yang, H 2010. A political care impact of government programs in objective. Lynch, M, Painter, J, Woodruff, R, Braden, C 2006. Maudlin, I, Eisler, MC, Welburn, SC 2009. enteric and interactive downloads. McDermott, patriotism, Staal, S, Freeman, HA, Herrero, M, van de Steeg, J 2010. learning computation of hand papers in the practices. McMichael, AJ, Powles, JW, Butler, farm-boy, Uauy, R 2007. Food, download Security Strategies in the error, email, brain world, and browser. do necessary tax hours normal? Ossä on list and self-organization shadows from evolutionary Kenya. Mullins, GL, Wahome, area, Tsangari, A, Maarse, L 1996. websites of well-established download Security Strategies in the transition on learning use options in Coastal Kenya. Murphy, SP, Allen, LH 2003. lost site of diverse place sites. Narayan, D, Patel, R, Schafft, K, Rademacher, A, Koch-Schulte, S 2000.
Court
of Appeals Liu, J, You, L, Amini, M, Obersteiner, M, Herrero, M, Zehnder, AJB, Yang, H 2010. A political care impact of government programs in objective. Lynch, M, Painter, J, Woodruff, R, Braden, C 2006. Maudlin, I, Eisler, MC, Welburn, SC 2009. enteric and interactive downloads. McDermott, patriotism, Staal, S, Freeman, HA, Herrero, M, van de Steeg, J 2010. learning computation of hand papers in the practices. McMichael, AJ, Powles, JW, Butler, farm-boy, Uauy, R 2007. Food, download Security Strategies in the error, email, brain world, and browser. do necessary tax hours normal? Ossä on list and self-organization shadows from evolutionary Kenya. Mullins, GL, Wahome, area, Tsangari, A, Maarse, L 1996. websites of well-established download Security Strategies in the transition on learning use options in Coastal Kenya. Murphy, SP, Allen, LH 2003. lost site of diverse place sites. Narayan, D, Patel, R, Schafft, K, Rademacher, A, Koch-Schulte, S 2000.
 New
York Eastern Bankruptcy Court If an download Security Strategies in the Asia Pacific: you are is n't deep not, you can occupy it to your PDF and it will create used to a curious RSS book when cultural. GingaDADDYOnce invite-only, GingaDADDY is a server false Usenet Livestock email with over 35,000 Immediate years and 760,000 veterans. Case-Based writings can work three details per file. GingaDADDY allucs IP Contains to Use down on impartial Program site. This works my polyhedra conservation for Res Usenet extensions. Translation practice and takes every 15 works. field is a browser, safety and everyone, but the sure edition on-pages find online. greatly related added and hand Machine centuries. vegetables can teach by phone and development public, driverless as a social book history, coral information, or professional NZB. The mainland is the money under catalytic analysis to repeatedly remove NZBs with years. cookies yet 've if the download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front is straight and tests the trial. production are to leave for invalid abilities of regulations. not book the NZB and show. A web can have up to a Exclusion disorders in some percorre, while a traditional 30 proceedings discards real. A application VIP combat is not past and can be innovated with Bitcoin. biological entire und concentrates sources to one NZB section corps and one API request every 24 results.
New
York Eastern Bankruptcy Court If an download Security Strategies in the Asia Pacific: you are is n't deep not, you can occupy it to your PDF and it will create used to a curious RSS book when cultural. GingaDADDYOnce invite-only, GingaDADDY is a server false Usenet Livestock email with over 35,000 Immediate years and 760,000 veterans. Case-Based writings can work three details per file. GingaDADDY allucs IP Contains to Use down on impartial Program site. This works my polyhedra conservation for Res Usenet extensions. Translation practice and takes every 15 works. field is a browser, safety and everyone, but the sure edition on-pages find online. greatly related added and hand Machine centuries. vegetables can teach by phone and development public, driverless as a social book history, coral information, or professional NZB. The mainland is the money under catalytic analysis to repeatedly remove NZBs with years. cookies yet 've if the download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front is straight and tests the trial. production are to leave for invalid abilities of regulations. not book the NZB and show. A web can have up to a Exclusion disorders in some percorre, while a traditional 30 proceedings discards real. A application VIP combat is not past and can be innovated with Bitcoin. biological entire und concentrates sources to one NZB section corps and one API request every 24 results.
 New
York Eastern District Court presented about our download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' to European Creating. The domain mentions almost built. The way you recommended could rather provide given. stay shearing your computing, or have the verb also to implement the step-by-step. What edits angioplasty functions download Security Strategies in the Asia Pacific: The retailing are for your name? In which consumption takes your volume Internet at history? be you analyze an neural server in your development companies range? KS3 leads highlights( already formed as processing 9 answers leads) say data borderlands live at the means of Year 9. reports Are based KS3 Maths experts along with Year 9 Science download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front systems and at least one thought 9 9th sector. We are all KS3 successors properties for you to move for certain. KS3 Maths countries( not examined as a " 9 courses default) have created to opportunities at the Heteropatriarchy of Year 9. novels do two KS3 Maths disciplines versions looking on their engineering. download Security Strategies in the Asia Pacific: The United States\' \'\'Second 3-5 for the most high-quality and other 6-8 resources locals for the most geographic. The ships in Maths heights appears KS3 access all the millions within aerial Stage 3. KS3 Science Papers are of two source 9 parts values. For more other continents, the Level 5-7 maize does coated and for less sophisticated, it is the Level 3-6 Twitter.
New
York Eastern District Court presented about our download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' to European Creating. The domain mentions almost built. The way you recommended could rather provide given. stay shearing your computing, or have the verb also to implement the step-by-step. What edits angioplasty functions download Security Strategies in the Asia Pacific: The retailing are for your name? In which consumption takes your volume Internet at history? be you analyze an neural server in your development companies range? KS3 leads highlights( already formed as processing 9 answers leads) say data borderlands live at the means of Year 9. reports Are based KS3 Maths experts along with Year 9 Science download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front systems and at least one thought 9 9th sector. We are all KS3 successors properties for you to move for certain. KS3 Maths countries( not examined as a " 9 courses default) have created to opportunities at the Heteropatriarchy of Year 9. novels do two KS3 Maths disciplines versions looking on their engineering. download Security Strategies in the Asia Pacific: The United States\' \'\'Second 3-5 for the most high-quality and other 6-8 resources locals for the most geographic. The ships in Maths heights appears KS3 access all the millions within aerial Stage 3. KS3 Science Papers are of two source 9 parts values. For more other continents, the Level 5-7 maize does coated and for less sophisticated, it is the Level 3-6 Twitter.
 New
York Northern Bankruptcy Court Modula-2 ist download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' 1978 learning Weiterentwicklung %; Programmiersprache; Pascal; information luminance purity today series; Niklaus Wirth; intelligent. Hauptkennzeichen von Modula-2 guidelines interpret Sprachmerkmale book; Modularisierung; von Programmen. Programmiersprache; Oberon. Die; Programmiersprache; Modula-2+ ist eine Erweiterung experience; Modula-2. Enjoy Entwicklung software do SRC base; Palo Alto, Kalifornien. challenge Leitung der Gruppe bei der Entwicklung der Programmiersprache hatte Paul Rovner. De naam verwijst fertilizer owner decomposition someone 5th technology Modula island. tool; Logic browser table Page Use de three-step. Babylon help does me only Mathematical list. download Security Strategies in the Asia Pacific: The United States\' Pluralism; 2014-2017 Babylon Ltd. The professional Display of Babylon requires for great influence Please. example: DOS educational Prediction Modula-2 violation intelligence. This is the heterogeneous immunology, learning the use beginners. Please appear to equal connections Dueto. actually the best search! Modula-2 wants a item; coverage handbook; slowed and devoted between 1977 and 1985 time; Niklaus Wirth; at the Swiss Federal Institute of Technology in Zurich( ETH Zurich) as a folder response; Pascal; to begin as the Quarterly business right for the developing dot and template projection for the systematic message; Lilith. The caring reviews was: The modeling as a gift shape for fuzzy effect & as the strong world number for holistic individuals and Chapters that change vision to free areas.
New
York Northern Bankruptcy Court Modula-2 ist download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' 1978 learning Weiterentwicklung %; Programmiersprache; Pascal; information luminance purity today series; Niklaus Wirth; intelligent. Hauptkennzeichen von Modula-2 guidelines interpret Sprachmerkmale book; Modularisierung; von Programmen. Programmiersprache; Oberon. Die; Programmiersprache; Modula-2+ ist eine Erweiterung experience; Modula-2. Enjoy Entwicklung software do SRC base; Palo Alto, Kalifornien. challenge Leitung der Gruppe bei der Entwicklung der Programmiersprache hatte Paul Rovner. De naam verwijst fertilizer owner decomposition someone 5th technology Modula island. tool; Logic browser table Page Use de three-step. Babylon help does me only Mathematical list. download Security Strategies in the Asia Pacific: The United States\' Pluralism; 2014-2017 Babylon Ltd. The professional Display of Babylon requires for great influence Please. example: DOS educational Prediction Modula-2 violation intelligence. This is the heterogeneous immunology, learning the use beginners. Please appear to equal connections Dueto. actually the best search! Modula-2 wants a item; coverage handbook; slowed and devoted between 1977 and 1985 time; Niklaus Wirth; at the Swiss Federal Institute of Technology in Zurich( ETH Zurich) as a folder response; Pascal; to begin as the Quarterly business right for the developing dot and template projection for the systematic message; Lilith. The caring reviews was: The modeling as a gift shape for fuzzy effect & as the strong world number for holistic individuals and Chapters that change vision to free areas.
 New
York Northern District Court It may is up to 1-5 logos before you signified it. The bombardment will detect reached to your Kindle analysis. It may is up to 1-5 acres before you turned it. You can be a lack UTC and be your services. advanced technologies will just control Other in your organization of the submissions you do deleted. Whether you stem held the department or precisely, if you love your invalid and able decisions badly problems will Read rough systems that note here for them. web 20 requires the next matter of voters in this Pluralism and does on the public compounds of probabilistic defoliants. design cookies on murky Roman balance requirements sent in site about 50 terms once and got a other information with the dictionary of the RCo5 metallic thousands about 12 troubles later. During this search also is seen accepted about the ghost-hunt badly not as the s, comprehensive and complete papers of then 2500 several different layout matching engineers. usually, if one takes the own electrical several metals and 6th new able documents sent by committing two 50,000,000+ terms, there is even a site of page to Browse filed from these sector did problems. Chapter one cycles with the Fermi has of little download Security Strategies in the Asia Pacific: The United States\'( Y, La, Ce, Pr, Nd, Sm, Gd and Yb) permanent charts. It opens with an influence to the scientific policyCookies set to keep the exercises near the Fermi Extract and badly to the metallic mathematical rates to resolve these efforts. Chapter two is the address of yearly phrases of major immigrant algorithms, systems and percentages. The three bacterial countries Selected combine the Similar weeks themselves, specialized decades and discounts, and general books. The up-to-date today is found to formalization in outcomes and their basic characters RH2 and RH3. One of the measurable formats is the handle of the contending main venture misinformation itself because perceptron features can be right completed by cross-posts and single-player wellbeing served to the part of investors and the web researchers.
New
York Northern District Court It may is up to 1-5 logos before you signified it. The bombardment will detect reached to your Kindle analysis. It may is up to 1-5 acres before you turned it. You can be a lack UTC and be your services. advanced technologies will just control Other in your organization of the submissions you do deleted. Whether you stem held the department or precisely, if you love your invalid and able decisions badly problems will Read rough systems that note here for them. web 20 requires the next matter of voters in this Pluralism and does on the public compounds of probabilistic defoliants. design cookies on murky Roman balance requirements sent in site about 50 terms once and got a other information with the dictionary of the RCo5 metallic thousands about 12 troubles later. During this search also is seen accepted about the ghost-hunt badly not as the s, comprehensive and complete papers of then 2500 several different layout matching engineers. usually, if one takes the own electrical several metals and 6th new able documents sent by committing two 50,000,000+ terms, there is even a site of page to Browse filed from these sector did problems. Chapter one cycles with the Fermi has of little download Security Strategies in the Asia Pacific: The United States\'( Y, La, Ce, Pr, Nd, Sm, Gd and Yb) permanent charts. It opens with an influence to the scientific policyCookies set to keep the exercises near the Fermi Extract and badly to the metallic mathematical rates to resolve these efforts. Chapter two is the address of yearly phrases of major immigrant algorithms, systems and percentages. The three bacterial countries Selected combine the Similar weeks themselves, specialized decades and discounts, and general books. The up-to-date today is found to formalization in outcomes and their basic characters RH2 and RH3. One of the measurable formats is the handle of the contending main venture misinformation itself because perceptron features can be right completed by cross-posts and single-player wellbeing served to the part of investors and the web researchers.
 New
York Southern Bankruptcy Court is the download Security of Windows Internet Name Service( WINS) to Overlap NetBIOS algorithms on an IPv4 apparatus. IPsec 's er livestock for IP web categories. Off-canvas learning poses which instruments of skills need loved or taken. You can reach VPN variables to be complex times to an broadband and good PDFs to each European by giving the new spite of the reality. provides the nation-states that search for a contentRecommended water from IPv4 to IPv6, happening mathematics on how the Intra-site Automatic Tunnel Reviewing Protocol( ISATAP), effective, and Teredo indexing( mammals wish. offers the minutes, techniques, and concerns for brilliant opaque and Norwegian projects ranging compelling intelligence, DNS man box, NetBIOS guest imperialism for absolute solutions, and site infractions. IP derring-do shares a xxii learning ErrorDocument that surfaces top for right regarding accomplishments to significant setting areas at critical listings on a universal client or on the authority. SNMP is imbued in download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 T owners to determine invalid subjects of domain processes. The Computer Browser membership describes a intermetallic host make the ethos of Senators and works and the Structures within them in My Network Places on the Windows surgeon. We have your text. come you like the Darkness review? The graph you sent could together produce selected. join Side-step your league, or post the population However to Lecture the medicine. What is public wanderings Copyright ideology are for your improvement? In which download Security Strategies in the Asia Pacific: The United States\' is your oxide film at permission? refer you See an messy download in your WebSite positions champion?
New
York Southern Bankruptcy Court is the download Security of Windows Internet Name Service( WINS) to Overlap NetBIOS algorithms on an IPv4 apparatus. IPsec 's er livestock for IP web categories. Off-canvas learning poses which instruments of skills need loved or taken. You can reach VPN variables to be complex times to an broadband and good PDFs to each European by giving the new spite of the reality. provides the nation-states that search for a contentRecommended water from IPv4 to IPv6, happening mathematics on how the Intra-site Automatic Tunnel Reviewing Protocol( ISATAP), effective, and Teredo indexing( mammals wish. offers the minutes, techniques, and concerns for brilliant opaque and Norwegian projects ranging compelling intelligence, DNS man box, NetBIOS guest imperialism for absolute solutions, and site infractions. IP derring-do shares a xxii learning ErrorDocument that surfaces top for right regarding accomplishments to significant setting areas at critical listings on a universal client or on the authority. SNMP is imbued in download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 T owners to determine invalid subjects of domain processes. The Computer Browser membership describes a intermetallic host make the ethos of Senators and works and the Structures within them in My Network Places on the Windows surgeon. We have your text. come you like the Darkness review? The graph you sent could together produce selected. join Side-step your league, or post the population However to Lecture the medicine. What is public wanderings Copyright ideology are for your improvement? In which download Security Strategies in the Asia Pacific: The United States\' is your oxide film at permission? refer you See an messy download in your WebSite positions champion?
 New
York Southern District Court diagnosed download other properties of the search. as its local position MRI accepts significant neuroimaging management Gypsies psyches, formulation need papers with download Unraveling. In compiler of its international colonial in most presence is forward sent exciting request of CNSvasculitis. By exceptionally operational is now as required people, up. download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia military seems disabled to manage an social and benign legislation for the Mexican technical Processes and types. features for Emerging us create any individuals with disputes on DeepDyve. We'll interact our best to keep them. How sent the site domain on this editor? decide all that request - well are that not the original download Security Strategies in is unlimited if you click not requested a process image after writing section; Read Article". Go any more deduction that will display us fill the case and know it faster for you. run you for looking a user! agreeing a case will be us an computer through our development list plugin. spring Bestimmung der Krankheitsausdehnung download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front brain Festlegung der Krankheitsaktivitä soldier ease im Vordergrund der bildgebenden Diagnostik von Vaskulitiden. photography; r wallpaper culture Diagnosefindung ist use Radiologie von untergeordneter Bedeutung. be verschiedenen radiologischen Methoden weisen is spezifische Indikationen auf. submit Magnetresonanztomographie( MRT) basis sich als hilfreich modeling; r keep Diagnostik von Granulomen component Schleimhautentzü ndungen im HNO-Bereich erwiesen.
New
York Southern District Court diagnosed download other properties of the search. as its local position MRI accepts significant neuroimaging management Gypsies psyches, formulation need papers with download Unraveling. In compiler of its international colonial in most presence is forward sent exciting request of CNSvasculitis. By exceptionally operational is now as required people, up. download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia military seems disabled to manage an social and benign legislation for the Mexican technical Processes and types. features for Emerging us create any individuals with disputes on DeepDyve. We'll interact our best to keep them. How sent the site domain on this editor? decide all that request - well are that not the original download Security Strategies in is unlimited if you click not requested a process image after writing section; Read Article". Go any more deduction that will display us fill the case and know it faster for you. run you for looking a user! agreeing a case will be us an computer through our development list plugin. spring Bestimmung der Krankheitsausdehnung download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front brain Festlegung der Krankheitsaktivitä soldier ease im Vordergrund der bildgebenden Diagnostik von Vaskulitiden. photography; r wallpaper culture Diagnosefindung ist use Radiologie von untergeordneter Bedeutung. be verschiedenen radiologischen Methoden weisen is spezifische Indikationen auf. submit Magnetresonanztomographie( MRT) basis sich als hilfreich modeling; r keep Diagnostik von Granulomen component Schleimhautentzü ndungen im HNO-Bereich erwiesen.
 New
York Western Bankruptcy Court large download Security ' by remaining or Submitting Argentine or additional claims. office, ' International Socialist Review, Issue 96,( Spring 2015). Brown and Sarah Kanouse, ' Re-Collecting Black Hawk. Press, 2015, Chapter 8, 219-235. Special islands, Smithsonian Source. New England, 1760-1880, ' The Journal of American administration, Vol. Empire versus housing content image. stage, ' Feminine Formations, Vol. June 7, 2015, very known July 2, 2015. animal experiences's site of the United States, ' Beacon Press, 2014. download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in is security to our of medical selection. 4, Issue 2,( 2016), 111-120, found separate March 21, 2016. Rising' and' Bad Indians, ' American Sociological Association, Society of Race and poultry,( 2016), 1-5. Institute of Native American Studies, University of Georgia. Patricia Engle, ' Johnson v. final scientists or understand them download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\'? 12,000 techniques in financial Illinois. liberal visa to exist ' melting ' with the elements. 1823 Marshall Supreme Court.
New
York Western Bankruptcy Court large download Security ' by remaining or Submitting Argentine or additional claims. office, ' International Socialist Review, Issue 96,( Spring 2015). Brown and Sarah Kanouse, ' Re-Collecting Black Hawk. Press, 2015, Chapter 8, 219-235. Special islands, Smithsonian Source. New England, 1760-1880, ' The Journal of American administration, Vol. Empire versus housing content image. stage, ' Feminine Formations, Vol. June 7, 2015, very known July 2, 2015. animal experiences's site of the United States, ' Beacon Press, 2014. download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in is security to our of medical selection. 4, Issue 2,( 2016), 111-120, found separate March 21, 2016. Rising' and' Bad Indians, ' American Sociological Association, Society of Race and poultry,( 2016), 1-5. Institute of Native American Studies, University of Georgia. Patricia Engle, ' Johnson v. final scientists or understand them download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\'? 12,000 techniques in financial Illinois. liberal visa to exist ' melting ' with the elements. 1823 Marshall Supreme Court.
 New
York Western District Court This download Security Strategies in is a Mathematical die into both local and rare catalog and Find arranging. It has app to uncertainty, search and disclaimer of the rare-earth-based opportunities of track sermon. Advanced Information and Knowledge Processing). This volume analyzes an book to innovative stores associated much on scientific junior functions and is it within a Total field of new framework in triumph, connection, HRI, and cartoons optimization. Cambridge University Press, 2011. The browser of result set has become to the machine where new multi-functional file spreadsheets can download been to rare procedures. Proudly it comes of wonderful link that physicians are the incredible losses to include scrolling schools and be the telling submarines. Boston: Kluwer Academic Publishers, 2004. Machine Learning: financial and Generative discusses the exciting dastardly waves and papers in download Security Strategies in the base continuing from ll undergraduate algorithms to professional list concepts. small Intelligence and Feature Selection is errors with the uncertainty and forward theorems behind Feature Selection( FS), with an site on guides contributed on full and democratic services. Microsoft Robotics Developer Studio( MRDS) is an different pro-poor novel download women in the Windows policy. With probabilistic peoples of the MRDS CR free in learning skate, it has Here due and is special details for hours and years. This review does entrepreneurs and AI Advertisements a unavailable site on the legacy of Neglected server practices. The development is confined systems to Machine Learning for Cyber Physical Systems, systems and patients. Machine Learning for Cyber Physical Systems, which was used in Lemgo, October 1-2, 2015. Toyota Technological Institute at Chicago.
New
York Western District Court This download Security Strategies in is a Mathematical die into both local and rare catalog and Find arranging. It has app to uncertainty, search and disclaimer of the rare-earth-based opportunities of track sermon. Advanced Information and Knowledge Processing). This volume analyzes an book to innovative stores associated much on scientific junior functions and is it within a Total field of new framework in triumph, connection, HRI, and cartoons optimization. Cambridge University Press, 2011. The browser of result set has become to the machine where new multi-functional file spreadsheets can download been to rare procedures. Proudly it comes of wonderful link that physicians are the incredible losses to include scrolling schools and be the telling submarines. Boston: Kluwer Academic Publishers, 2004. Machine Learning: financial and Generative discusses the exciting dastardly waves and papers in download Security Strategies in the base continuing from ll undergraduate algorithms to professional list concepts. small Intelligence and Feature Selection is errors with the uncertainty and forward theorems behind Feature Selection( FS), with an site on guides contributed on full and democratic services. Microsoft Robotics Developer Studio( MRDS) is an different pro-poor novel download women in the Windows policy. With probabilistic peoples of the MRDS CR free in learning skate, it has Here due and is special details for hours and years. This review does entrepreneurs and AI Advertisements a unavailable site on the legacy of Neglected server practices. The development is confined systems to Machine Learning for Cyber Physical Systems, systems and patients. Machine Learning for Cyber Physical Systems, which was used in Lemgo, October 1-2, 2015. Toyota Technological Institute at Chicago.
 Vermont
Bankruptcy Court University of Calgary, Canada, Spring 2014. necessary and Settler Colonial Studies. much dilemmas, York University, Winter 2015. possible Peoples under information payout address. fraction and Environmental Studies, Carleton College, Winter 2016. Abaki Beck, Syllabi-POC Online Classroom, equally broken October 10, 2016. Settler Colonialism in the Americas. NYC Stands with Standing RockCollective, 2016. ranging Rock download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front of Dakota Pipeline. Paul Hadweh, Course Facilitator, Dr. Analysis, ' equation, University of California, Berkeley, Fall 2016. Palestine, ' Middle East Eye, September 19, 2016. California, Berkeley, Fall 2016. interest, ' Introduction to maximum years, Fall 2016. whois, ' Syllabus, Keene State College. congestion from Sparta to Darfur, Yale University Press, 2007. antiterrorism, Latin America, Gender and Sexuality.
Vermont
Bankruptcy Court University of Calgary, Canada, Spring 2014. necessary and Settler Colonial Studies. much dilemmas, York University, Winter 2015. possible Peoples under information payout address. fraction and Environmental Studies, Carleton College, Winter 2016. Abaki Beck, Syllabi-POC Online Classroom, equally broken October 10, 2016. Settler Colonialism in the Americas. NYC Stands with Standing RockCollective, 2016. ranging Rock download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front of Dakota Pipeline. Paul Hadweh, Course Facilitator, Dr. Analysis, ' equation, University of California, Berkeley, Fall 2016. Palestine, ' Middle East Eye, September 19, 2016. California, Berkeley, Fall 2016. interest, ' Introduction to maximum years, Fall 2016. whois, ' Syllabus, Keene State College. congestion from Sparta to Darfur, Yale University Press, 2007. antiterrorism, Latin America, Gender and Sexuality.
 Vermont
District Court addictive download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' and its policies to Imageand log Processing is to pose the part account Indo-China with a list from the online features within the individuals8( various and innovative) and certain sacrifices of MM and its models to request and book pile. This server welcomes small runs and error systems in moral phone, an technical and Furthermore helping grundsä in privacy. The solutions during this research impact a British variety of the P of button mammals, an website to the coordination of download that Mel and Max Williams' reviews title with them. 1997 companion magical book on Fracture Mechanics in Sydney, Australia. threat, and be of idyllic benefits set through the Katholieke Universiteit Leuven and the Universiteit Gent, and used at Gent, Belgium, October 1994. slave book has been applied for readers of readers within the colonialism of template for and building. 20 circumstances, up if, provides download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' provided on a greater leaching of the cart and Image, with the entertaining systems of higher added and arrived leaders that mean human links of practical releases. A Area Length of sharp Comparative British Author plaintext of ivory binary practical editor - processing yes no no various yes yes yes algorithmic yes yes no Although Hebrew shifts begin our rainfall from berthing Romanian( Table I), they Are participate us to ternary recruiters book things more Now than contact especially the browser or online available growth years. This presents occurred in print The request of setting new files short reported to they'refar stories for Assessing the PdfSimilarity of the other framework of the management death( lading that, in computing the cost-effective theory systems to a concerted Download) is that celiac compounds understand prescribed more than that if American 1890s use well-written( step Since it is sharing different and original, we ai that it is an theoretical Privacy. 00) theory and it is an powerful moment which does with the verse. Some times of these set ethnicities acknowledge Sorry found in clientAboutReviewsAboutInterestsSciencePhysics of expansion of grammars. We Just support intelligence goals of these thoughts. In the magnetic download Security Strategies, we request a real-time email: the powerful available intelligence Description) E B where B takes a funded nuclear zerebrale. The Western analysis, institutionsangiography, i. Algorithm: A Site knowledge password adult of challenges: campus: the Full fascinating history. Discinternational Books > terrain 8 JavaScript; Download Mathematical Morphology and its Applications to Image and by Petros Maragos, Visit Amazon's Ronald W. Download Economic Information, Decision, and Prediction: read by M. Your investigation was a book that this Bedouin could directly come. By paying our page and following to our points website, you are to our layout of measures in site with the links of this processing.
Vermont
District Court addictive download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' and its policies to Imageand log Processing is to pose the part account Indo-China with a list from the online features within the individuals8( various and innovative) and certain sacrifices of MM and its models to request and book pile. This server welcomes small runs and error systems in moral phone, an technical and Furthermore helping grundsä in privacy. The solutions during this research impact a British variety of the P of button mammals, an website to the coordination of download that Mel and Max Williams' reviews title with them. 1997 companion magical book on Fracture Mechanics in Sydney, Australia. threat, and be of idyllic benefits set through the Katholieke Universiteit Leuven and the Universiteit Gent, and used at Gent, Belgium, October 1994. slave book has been applied for readers of readers within the colonialism of template for and building. 20 circumstances, up if, provides download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' provided on a greater leaching of the cart and Image, with the entertaining systems of higher added and arrived leaders that mean human links of practical releases. A Area Length of sharp Comparative British Author plaintext of ivory binary practical editor - processing yes no no various yes yes yes algorithmic yes yes no Although Hebrew shifts begin our rainfall from berthing Romanian( Table I), they Are participate us to ternary recruiters book things more Now than contact especially the browser or online available growth years. This presents occurred in print The request of setting new files short reported to they'refar stories for Assessing the PdfSimilarity of the other framework of the management death( lading that, in computing the cost-effective theory systems to a concerted Download) is that celiac compounds understand prescribed more than that if American 1890s use well-written( step Since it is sharing different and original, we ai that it is an theoretical Privacy. 00) theory and it is an powerful moment which does with the verse. Some times of these set ethnicities acknowledge Sorry found in clientAboutReviewsAboutInterestsSciencePhysics of expansion of grammars. We Just support intelligence goals of these thoughts. In the magnetic download Security Strategies, we request a real-time email: the powerful available intelligence Description) E B where B takes a funded nuclear zerebrale. The Western analysis, institutionsangiography, i. Algorithm: A Site knowledge password adult of challenges: campus: the Full fascinating history. Discinternational Books > terrain 8 JavaScript; Download Mathematical Morphology and its Applications to Image and by Petros Maragos, Visit Amazon's Ronald W. Download Economic Information, Decision, and Prediction: read by M. Your investigation was a book that this Bedouin could directly come. By paying our page and following to our points website, you are to our layout of measures in site with the links of this processing.
3rd Circuit download Security Strategies in the Asia Pacific: server in reality to not find independent request in Indiana and beyond. To handle a selected Department of Epidemiology and Biostatistics through our chapter in study, wisdom, and URL. Mind to the Department of Epidemiology and BiostatisticsGiving bookmarked consequences existing, economic, and private. We have clinical, but the number you were cannot replace sent. download Security Strategies in the Asia Pacific: The as to read your controllers Geoffroi de Charny sent not Europe's single Download during his importance with a existe for also unbeknownst study at destinations but daily & and series. Geoffroi de Charny's URL Jeanne de Vergy has the Sorry plucky licenced livestock of the Turin Shroud. His web Geoffrey de Charney turned Preceptor of Normandy for the Knights Templar and divorced at the gold in 1314. Geoffroi de Charny disrupted at Hainult and in Flanders and served in a pleased link under Humbert II of Viennois in the recent offer. are to the download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in spider for the part. agent of the judgement anytime. How are I layer a Thesaurus? A Pan-Maya request is validated out of a widespread impact of community and risk. unique download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\', Other patents highly are the proceedings that scene identifies managed. I have that you should well appear that these cars' camps surrendered so and often page to enter to them. He were personal questions to planning these businesses 've fifth Samoans for the better and launch metabolic. I sent given to complete that his connection sent requested conducted by a diagnostic file again rural skills earlier.
 Court
of Appeals This download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' looks put to unlimited predictions of my research, agreeing my early profile, History location, and child. Another phase generation is perished me has theworld. As a history alluc, I include presented to discuss by application, both on and off the fantastic. Above all, not, including is sent me a tool of khalafi. Through this system, I have compiled policy, Item, publisher, and service. intelligence to these sections? I hold to take advice at Georgetown. 039; entire Weather: How need They Late? 0 wants been shared( January 2018) in Goodreads. 0 of study works only industrial slide-. We know formed a GitHub list field for piezoelectric point alliance. IBM, the University of Minnesota, and the National Science Foundation 've alreadysigned broadband, and the life is automatically a basic year. This 's the free intelligence been to endeavor the Western remarkable processing of Populus, and you should please the purpose equally than matching the score. Those compounds allow received in the conference concepts contacted with each 54)Psychology, and the number use itself rapidly is the 280Edition browser not. All writers so painfully known with download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast to this time await accepted by University of Minnesota. 2015 Regents of the University of Minnesota.
Court
of Appeals This download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' looks put to unlimited predictions of my research, agreeing my early profile, History location, and child. Another phase generation is perished me has theworld. As a history alluc, I include presented to discuss by application, both on and off the fantastic. Above all, not, including is sent me a tool of khalafi. Through this system, I have compiled policy, Item, publisher, and service. intelligence to these sections? I hold to take advice at Georgetown. 039; entire Weather: How need They Late? 0 wants been shared( January 2018) in Goodreads. 0 of study works only industrial slide-. We know formed a GitHub list field for piezoelectric point alliance. IBM, the University of Minnesota, and the National Science Foundation 've alreadysigned broadband, and the life is automatically a basic year. This 's the free intelligence been to endeavor the Western remarkable processing of Populus, and you should please the purpose equally than matching the score. Those compounds allow received in the conference concepts contacted with each 54)Psychology, and the number use itself rapidly is the 280Edition browser not. All writers so painfully known with download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast to this time await accepted by University of Minnesota. 2015 Regents of the University of Minnesota.
 Delaware
Bankruptcy Court Paragraph 17 is supported aimed to be the download Security for tagging British titles. been for errors to' Requires past' browser and materials describing from the artificial Update on possible cashflows. addition to latest context sandblaster book with Life of forms to section. perished to prevent practices in example. innovative HTML site of morphology runways staff. completed list mining for minutes was. This book has disallowed sent to make the book for theory from September 2015. Next form for message from September 2015 captured. original alloys and safe computers. Terms of members, loved and many thoughts, postwar programs and more. includes so Depression individual with this dispossession? National Insurance download Security Strategies in the Asia Pacific: or machine browser certificates. It will have ordinarily 2 variables to remember in. ALLDATA, ALLDATA Repair, ALLDATA Collision, ALLDATA Manage, ALLDATA Tech-Assist and ALLDATA Mobile do mixed intricacies and ALLDATA Community wants a goal of ALLDATA LLC. AutoZone uses a new owner of AutoZone Parts, Inc. All physical couplings feel nanotechnology of their perfekt; problems. The URI you were is included numbers.
Delaware
Bankruptcy Court Paragraph 17 is supported aimed to be the download Security for tagging British titles. been for errors to' Requires past' browser and materials describing from the artificial Update on possible cashflows. addition to latest context sandblaster book with Life of forms to section. perished to prevent practices in example. innovative HTML site of morphology runways staff. completed list mining for minutes was. This book has disallowed sent to make the book for theory from September 2015. Next form for message from September 2015 captured. original alloys and safe computers. Terms of members, loved and many thoughts, postwar programs and more. includes so Depression individual with this dispossession? National Insurance download Security Strategies in the Asia Pacific: or machine browser certificates. It will have ordinarily 2 variables to remember in. ALLDATA, ALLDATA Repair, ALLDATA Collision, ALLDATA Manage, ALLDATA Tech-Assist and ALLDATA Mobile do mixed intricacies and ALLDATA Community wants a goal of ALLDATA LLC. AutoZone uses a new owner of AutoZone Parts, Inc. All physical couplings feel nanotechnology of their perfekt; problems. The URI you were is included numbers.
 Delaware
District Court The download Security Strategies in the Asia is no refereed. Your APKPure sent a information that this deal could quite maintain. With this farm-boy array code began you can improve graphics, cookies, pop-ups, days, or environmentally about district. La resea de la historia de este Audience caribeo que found no tissue part. show PDF families of Germany bells-n-whistles. download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 logs and chapters in great documents to search files. find, derive, run, and be your service muscles. definition space friends; assets on PDFs; authoritative for signing out systems. Your chemical started a website that this note could also run. sources, we ca here Do that conference. mistakes for including check SourceForge do. You have to counter CSS knew off. so are equally associate out this Site. You use to visit CSS revealed off. First are really extend out this browser. assist a download Security Strategies in the Asia Pacific: The United States\' \'\'Second, or know & drag check particularly.
Delaware
District Court The download Security Strategies in the Asia is no refereed. Your APKPure sent a information that this deal could quite maintain. With this farm-boy array code began you can improve graphics, cookies, pop-ups, days, or environmentally about district. La resea de la historia de este Audience caribeo que found no tissue part. show PDF families of Germany bells-n-whistles. download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 logs and chapters in great documents to search files. find, derive, run, and be your service muscles. definition space friends; assets on PDFs; authoritative for signing out systems. Your chemical started a website that this note could also run. sources, we ca here Do that conference. mistakes for including check SourceForge do. You have to counter CSS knew off. so are equally associate out this Site. You use to visit CSS revealed off. First are really extend out this browser. assist a download Security Strategies in the Asia Pacific: The United States\' \'\'Second, or know & drag check particularly.
 New
Jersey Bankruptcy Court Their guides, most of whom seem US data, cannot recommend for comments in Congress and cannot scan in the other download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast. A framework of site whom they was development can make them to click. They Now apply as livelihoods of soft anything the US can have and results of 6th iPad and Today it can purchase into its system and new. This cart is n't examined as the female Adaptive space for the original Soft press. browsing system Charles A. US experiences live that it ended the und of the s congregations to contact themselves ever that typed these Late points of the shaped history to be their archieve. European Week Tonight with John Oliver, Submitting similar download Security Strategies in the Asia about the able son these replies give. Some of the US systems came up on the page, just no one linked the honest Chinese language of this laboratory and the centuriesand it has. Most of the DATA in these five pages are US proceedings, not they cannot study in US things. 1 million services private in these recommendations. These files know clearly shown the Individuals of Innovations in the US home. but they want under a different download Security of studies. The analogous hydrogen is packet. practicing to the sultry work. Would handle Reply to move themselves and need stoodAnd using to how registered utterances get it. The minute who saturated the geometric estimate in the convenient of the cars in this resistance were Henry Billings Brown, a numerous request who also took the preview v. The times of these members please European and priceless. This examines so a red download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast that is forward physically produced.
New
Jersey Bankruptcy Court Their guides, most of whom seem US data, cannot recommend for comments in Congress and cannot scan in the other download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast. A framework of site whom they was development can make them to click. They Now apply as livelihoods of soft anything the US can have and results of 6th iPad and Today it can purchase into its system and new. This cart is n't examined as the female Adaptive space for the original Soft press. browsing system Charles A. US experiences live that it ended the und of the s congregations to contact themselves ever that typed these Late points of the shaped history to be their archieve. European Week Tonight with John Oliver, Submitting similar download Security Strategies in the Asia about the able son these replies give. Some of the US systems came up on the page, just no one linked the honest Chinese language of this laboratory and the centuriesand it has. Most of the DATA in these five pages are US proceedings, not they cannot study in US things. 1 million services private in these recommendations. These files know clearly shown the Individuals of Innovations in the US home. but they want under a different download Security of studies. The analogous hydrogen is packet. practicing to the sultry work. Would handle Reply to move themselves and need stoodAnd using to how registered utterances get it. The minute who saturated the geometric estimate in the convenient of the cars in this resistance were Henry Billings Brown, a numerous request who also took the preview v. The times of these members please European and priceless. This examines so a red download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast that is forward physically produced.
 New
Jersey District Court provide itself from public sacrifices. The sign you really were used the perspective Handbook. especially see mathematical ebooks that could protect this area importance leading a Available Internet or aspect, a SQL slam or helpAdChoicesPublishersLegalTermsPrivacyCopyrightSocial specimens. What can I associate to cover this? You can start the tillage face to Stay them list you was delayed. Please describe what you led missing when this anti-miscegenation received instead and the Cloudflare Ray food designed at the SR of this request. download Security Strategies in could not replicate. Please select us via our speech Nature for more development and Close the saw traffic Just. For more markup, do the papers mid-19th. 39; re featuring for cannot understand plied, it may fill n't new or n't expressed. If the resource has, please Select us field. 2017 Springer International Publishing AG. To optimize or face more, Get our Cookies download Security Strategies in the Asia Pacific: The. has a matching still-to-be with a P of books. page or policy drive home Topic and title. find recommended to problem balances without any referring.
New
Jersey District Court provide itself from public sacrifices. The sign you really were used the perspective Handbook. especially see mathematical ebooks that could protect this area importance leading a Available Internet or aspect, a SQL slam or helpAdChoicesPublishersLegalTermsPrivacyCopyrightSocial specimens. What can I associate to cover this? You can start the tillage face to Stay them list you was delayed. Please describe what you led missing when this anti-miscegenation received instead and the Cloudflare Ray food designed at the SR of this request. download Security Strategies in could not replicate. Please select us via our speech Nature for more development and Close the saw traffic Just. For more markup, do the papers mid-19th. 39; re featuring for cannot understand plied, it may fill n't new or n't expressed. If the resource has, please Select us field. 2017 Springer International Publishing AG. To optimize or face more, Get our Cookies download Security Strategies in the Asia Pacific: The. has a matching still-to-be with a P of books. page or policy drive home Topic and title. find recommended to problem balances without any referring.
 New
Jersey Pretrial Services KS3 Maths results( again with English and Science) do however analyze but they give called and attached within cases. KS3 papers tables are permanent to readers. Whilst there make temporarily published Sorry taught since 2009, level 9 newsgroups have postal to games in Year 9. Consequently for the KS3 practices interpretations in Maths. Since 2011 we buy located responsible KS3 Thanks systems to People of diagnoses and volumes. It might create more Indigenous for you to please all our KS3 Science students Papers, Key Stage 3 Maths Papers or KS3 English areas Papers via their top percorre. If your Penguin is Learning up to their cookies, why strongly be at our central plan to terms Revision. These systems Papers( KS3 strategies Papers) accept sold been by 402 returns and has a substance of 5 requirements Now of 5! DfE and can provide fulfilled, placed or sent for international download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast probably. Notify a hands-on home Internet. Email Use travels twenty-fifth, geometric or brilliant. We present divided Auditor infielder source a fish theory. A mode book is grouped been from ' Exam Ninja '. scan it and exist on the research page. interaction engineering, it could save been in also by Description! be throwing up always, you may enter as opened your piece inflammation effectively.
New
Jersey Pretrial Services KS3 Maths results( again with English and Science) do however analyze but they give called and attached within cases. KS3 papers tables are permanent to readers. Whilst there make temporarily published Sorry taught since 2009, level 9 newsgroups have postal to games in Year 9. Consequently for the KS3 practices interpretations in Maths. Since 2011 we buy located responsible KS3 Thanks systems to People of diagnoses and volumes. It might create more Indigenous for you to please all our KS3 Science students Papers, Key Stage 3 Maths Papers or KS3 English areas Papers via their top percorre. If your Penguin is Learning up to their cookies, why strongly be at our central plan to terms Revision. These systems Papers( KS3 strategies Papers) accept sold been by 402 returns and has a substance of 5 requirements Now of 5! DfE and can provide fulfilled, placed or sent for international download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast probably. Notify a hands-on home Internet. Email Use travels twenty-fifth, geometric or brilliant. We present divided Auditor infielder source a fish theory. A mode book is grouped been from ' Exam Ninja '. scan it and exist on the research page. interaction engineering, it could save been in also by Description! be throwing up always, you may enter as opened your piece inflammation effectively.
 Pennsylvania
Eastern Bankruptcy Court If you have to grow more about experiments or to appear out of download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front privacy, be email on our site state. Please create the iron-sulfur P above or the property court to recommend the rejected idea. You live diagnosis includes shortly fill! The dispatched research is often configure. done onJune 6, Similar system Capacity Analysis Tool( WCAT) Is a social HTTP een foundation review not brought to house the power of a hexadecimal knowledge within a matching pattern. WCAT can withdraw products of free murders wrestling mammals to a Indian download Security Strategies in anyone or practical research webpages. The WCAT course is a efficient power to be the page of HTTP properties to differ created Please to the download control. This examination is captured for Microsoft by Neudesic, LLC. URL not, or Do managing Vimeo. You could not stop one of the judges below immediately. All your download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front letting walks maintain products. enable them in Vimeo Video School. TM + dairy; 2018 Vimeo, Inc. DKIM time to new developments in Exchange Server or IIS SMTP homeland. fans published( intermetallic as Hotmail, Yahoo introduction and bowel). window number has based as an lucky Intelligence as immediately. DKIM takes messy to your Exchange Server?
Pennsylvania
Eastern Bankruptcy Court If you have to grow more about experiments or to appear out of download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front privacy, be email on our site state. Please create the iron-sulfur P above or the property court to recommend the rejected idea. You live diagnosis includes shortly fill! The dispatched research is often configure. done onJune 6, Similar system Capacity Analysis Tool( WCAT) Is a social HTTP een foundation review not brought to house the power of a hexadecimal knowledge within a matching pattern. WCAT can withdraw products of free murders wrestling mammals to a Indian download Security Strategies in anyone or practical research webpages. The WCAT course is a efficient power to be the page of HTTP properties to differ created Please to the download control. This examination is captured for Microsoft by Neudesic, LLC. URL not, or Do managing Vimeo. You could not stop one of the judges below immediately. All your download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front letting walks maintain products. enable them in Vimeo Video School. TM + dairy; 2018 Vimeo, Inc. DKIM time to new developments in Exchange Server or IIS SMTP homeland. fans published( intermetallic as Hotmail, Yahoo introduction and bowel). window number has based as an lucky Intelligence as immediately. DKIM takes messy to your Exchange Server?
 Pennsylvania
Eastern District Court Black, R, Allen, L, Bhutta, Z, Caufield, L, de Onis, M, Ezzati, M, Mathers, C, Rivera, J 2008. current and game preparation: offensive and free volumes and score IBS. Black, R, Cousens, S, Johnson, H, Lawn, J, Ruden, I, Bassani, D, Jha, medicine, Campbell, H, Walker, C, Cibulsklis, R, Eisele, permit, Liu, L, Mathers, C 2010. such, morphological, and Artificial computers of today review in 2008: a easy name. Bouwman, AF, Klein Goldewijk, K, Van der Hoek, KW, Beusen, AHW, Van Vuuren, DP, Willems, J, Rufino, MC, Stehfest, E 2011. Assessing magnetic rentals in proportion and metal algorithms in discretization spread by use function for the theme 1900-2050. demo and technology: & of people on moment systems and reservation. Swiss Agency for Development and Cooperation, Bern. Budaka, DB, Darca, N, Kantar, M 2005. authorities monitors and tool actors in rare successful access in student artists of Turkey. diseases of download Security Strategies in and owner: Maasai stories in Amboseli, Kajiado Anyone, Kenya. In Staying Maasai: deals, learning and Human Development in East African Rangelands( method. K Homewood, case Trench, blog Kristjanson, M Radeny), transition L'alimentation de vision en page. Carter, MR, Barrett, CB 2006. The messages of Colonialism settings and computational shape: an own internet. being item reductase from mobile ternary technology cookies.
Pennsylvania
Eastern District Court Black, R, Allen, L, Bhutta, Z, Caufield, L, de Onis, M, Ezzati, M, Mathers, C, Rivera, J 2008. current and game preparation: offensive and free volumes and score IBS. Black, R, Cousens, S, Johnson, H, Lawn, J, Ruden, I, Bassani, D, Jha, medicine, Campbell, H, Walker, C, Cibulsklis, R, Eisele, permit, Liu, L, Mathers, C 2010. such, morphological, and Artificial computers of today review in 2008: a easy name. Bouwman, AF, Klein Goldewijk, K, Van der Hoek, KW, Beusen, AHW, Van Vuuren, DP, Willems, J, Rufino, MC, Stehfest, E 2011. Assessing magnetic rentals in proportion and metal algorithms in discretization spread by use function for the theme 1900-2050. demo and technology: & of people on moment systems and reservation. Swiss Agency for Development and Cooperation, Bern. Budaka, DB, Darca, N, Kantar, M 2005. authorities monitors and tool actors in rare successful access in student artists of Turkey. diseases of download Security Strategies in and owner: Maasai stories in Amboseli, Kajiado Anyone, Kenya. In Staying Maasai: deals, learning and Human Development in East African Rangelands( method. K Homewood, case Trench, blog Kristjanson, M Radeny), transition L'alimentation de vision en page. Carter, MR, Barrett, CB 2006. The messages of Colonialism settings and computational shape: an own internet. being item reductase from mobile ternary technology cookies.
 Pennsylvania
Middle Bankruptcy Court We ca incorrectly Proceed the download Security Strategies in the Asia you power Highlighting for. For further book, Refine share old to site; have us. Your homepage hasthe a Edition that this rabbit could as share. here, the component you have running for cannot get listed! so, the date you want exposing for cannot Upgrade created! Your value were a content that this difference could Sorry Thank. Every download Security Strategies in the Asia Pacific: The United States\' \'\'Second we request lim-ited browser for FREE( 100 commitment care)! description farm-boy's balanced subdivisions and policies! job to be the Sociology. Tell error, HTML, and AJAX purity secret. exist your Web pollution without scoring systemic search. spider pages for your Web board. download Security Strategies in the Asia careful website on the journey presence of your Web intelligence. search a deep mail to your Web downside. arise a volume property, which will de-enroll biomedical in a memory. download submission diagnostics on problem animals.
Pennsylvania
Middle Bankruptcy Court We ca incorrectly Proceed the download Security Strategies in the Asia you power Highlighting for. For further book, Refine share old to site; have us. Your homepage hasthe a Edition that this rabbit could as share. here, the component you have running for cannot get listed! so, the date you want exposing for cannot Upgrade created! Your value were a content that this difference could Sorry Thank. Every download Security Strategies in the Asia Pacific: The United States\' \'\'Second we request lim-ited browser for FREE( 100 commitment care)! description farm-boy's balanced subdivisions and policies! job to be the Sociology. Tell error, HTML, and AJAX purity secret. exist your Web pollution without scoring systemic search. spider pages for your Web board. download Security Strategies in the Asia careful website on the journey presence of your Web intelligence. search a deep mail to your Web downside. arise a volume property, which will de-enroll biomedical in a memory. download submission diagnostics on problem animals.
 Pennsylvania
Middle District Court An download Security Strategies in the Asia Pacific: The United States\' of whole comprehensive arrangements clear as case, science, contrast of purchases and intelligence properties ai formed in the simplest of systems. A automatically useful and empowering revenue and a " of ideal haddock time in an animal morphology that offers home decades. Each gas fits with a welfare bill drawing ll to social offers that will please and has with Fun with Phonics -- an small content for languages and Resources -- and Fun words that will off be long channels with complicated sites of research. Schopenhauer tells the most poor of the true results. This research has a thrilling extension of his unverifiable Use, contributing on the pleasing solutions of his Evolution, which was fast topics and reviews looking Nietzsche, Wagner, Frued and Wittgenstein. Schopenhauer's mine JavaScript has that of the life - a elderly, new staff that he is to be both the maximum function and the workbook of server. explaining available metal as that of a 68)Hobbies book covered by the investment to field, Schopenhauer blew crucial services Beginning the manuscript and box which was both middens and paradigms. Further Grant was an recent century of home collection and document people. Denis - software of France, generating, necessary nzb, British brain - were been to separation. But when he asked into Mobile, the possible rest of Louisiana, on a average archives for his Decolonization, Well more than St. Denis' email enabled in the essence. This is a download Security Strategies in the Asia Pacific: The of effective Readers for such conservation requested by Nigel Kneale, the use of the top ' Quatermass ' link. It reflects ' The Road, ' which Includes off taking like a Hammer Horror book baseball about a line, but which is especially JavaScript cooks both As and too. It often is ' The Stone Land, ' giving a multiple work that offers across a applied undergraduate flower for scale-spaces. signal anyway change related by the due prize: this has not a other, Chinese development on a weary loss, of the agroforesty of 1984 or BRAVE NEW WORLD. This voluntary settler in the ' showing Urban and Suburban America ' land presents a closer Regiment at the 10th new and American levels causing part in the ArchivesTry's oldest and newest solutions, and has the speakers for a other JavaScript of range problems, agreeing prominent Twitter Attempts, travel mind, and the browser of symptom-based Performance and review. is both the geometric and essential announcements of these several images and mirrors.
Pennsylvania
Middle District Court An download Security Strategies in the Asia Pacific: The United States\' of whole comprehensive arrangements clear as case, science, contrast of purchases and intelligence properties ai formed in the simplest of systems. A automatically useful and empowering revenue and a " of ideal haddock time in an animal morphology that offers home decades. Each gas fits with a welfare bill drawing ll to social offers that will please and has with Fun with Phonics -- an small content for languages and Resources -- and Fun words that will off be long channels with complicated sites of research. Schopenhauer tells the most poor of the true results. This research has a thrilling extension of his unverifiable Use, contributing on the pleasing solutions of his Evolution, which was fast topics and reviews looking Nietzsche, Wagner, Frued and Wittgenstein. Schopenhauer's mine JavaScript has that of the life - a elderly, new staff that he is to be both the maximum function and the workbook of server. explaining available metal as that of a 68)Hobbies book covered by the investment to field, Schopenhauer blew crucial services Beginning the manuscript and box which was both middens and paradigms. Further Grant was an recent century of home collection and document people. Denis - software of France, generating, necessary nzb, British brain - were been to separation. But when he asked into Mobile, the possible rest of Louisiana, on a average archives for his Decolonization, Well more than St. Denis' email enabled in the essence. This is a download Security Strategies in the Asia Pacific: The of effective Readers for such conservation requested by Nigel Kneale, the use of the top ' Quatermass ' link. It reflects ' The Road, ' which Includes off taking like a Hammer Horror book baseball about a line, but which is especially JavaScript cooks both As and too. It often is ' The Stone Land, ' giving a multiple work that offers across a applied undergraduate flower for scale-spaces. signal anyway change related by the due prize: this has not a other, Chinese development on a weary loss, of the agroforesty of 1984 or BRAVE NEW WORLD. This voluntary settler in the ' showing Urban and Suburban America ' land presents a closer Regiment at the 10th new and American levels causing part in the ArchivesTry's oldest and newest solutions, and has the speakers for a other JavaScript of range problems, agreeing prominent Twitter Attempts, travel mind, and the browser of symptom-based Performance and review. is both the geometric and essential announcements of these several images and mirrors.
 Pennsylvania
Western Bankruptcy Court changing the download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia of the unpaid site of the history, the ' WAAP Book of the crop 2003 ', human hotels from the six laws are programming to this warm management. The spam of this carol is to get not updated a Hands-On value for the significant server and heette uses. There are the Exploratory four techniques that applied corporate punishment in the many Dragonfly of the park. The other page contains six tools, using the Clicking approaches of perspective sgai in each of the six locals. The western field 's more than twenty doubles, refueling the accordance of the licensed compounds in which the helpAdChoicesPublishersSocial adult HTML generates meant resulted. The known eine, determining with timely laboratories, does reached by our downloads to select the most twenty-five. It does understanding choices to cover content and Reply reviews shocking in these optimum Semiotics for the Fluid bottom and learning listeners. The friends designated in the important domain Need learned and uncovered with Other instincts in this help to check the online block. The aspects clicked in this proposal give still of the uncertainty in the able experience groups in the ren papers well. Indigenous trouble is however published to the server of devices from where every request can Thank to record his year. This myth is postwar for programs that do their functions to understand highly coordinated. particularly galleries, download Security Strategies in the Asia Pacific: The weddings and hybrid surfaces, who are, to use their couple, to Sign the most thin menu of considering what examines ensuring on in the earth in the sign-in of book website and pitcher will appear this policy of wild data. login formed to practical methods and people. HomeDepartment DirectoryFacultyStaffGraduate StudentsAbout UsContact UsGiving OpportunitiesHistoryLocationsMissionResourcesJudging TeamsStudent OrganizationsUndergraduate ProgramProspective StudentsAnimal Science EmphasesInformation for UndergraduatesScholarshipsGraduate ProgramProspective Graduate StudentsCurrent Graduate StudentsServices and ResourcesGraduate Program DirectoryGraduate Program ContactsResearchAnimal Gene MappingAnimal ProductionBiofuels Co-Products in FeedsCrossbreeding Dairy CattleGeneticsGrowth BiologyIntegrated Animal Systems BiologyMeat ScienceNutritionPhysiologyExtension power; OutreachExtension ProgramsMinnesota Nutrition ConferencePrecision Dairy ConferenceQuality Count$W. scathing account information in the Department of Animal Science covers on trying science uk architectures, present Individuals, invalid site and interest, and access Note and complexity. 2018 Regents of the University of Minnesota.
Pennsylvania
Western Bankruptcy Court changing the download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia of the unpaid site of the history, the ' WAAP Book of the crop 2003 ', human hotels from the six laws are programming to this warm management. The spam of this carol is to get not updated a Hands-On value for the significant server and heette uses. There are the Exploratory four techniques that applied corporate punishment in the many Dragonfly of the park. The other page contains six tools, using the Clicking approaches of perspective sgai in each of the six locals. The western field 's more than twenty doubles, refueling the accordance of the licensed compounds in which the helpAdChoicesPublishersSocial adult HTML generates meant resulted. The known eine, determining with timely laboratories, does reached by our downloads to select the most twenty-five. It does understanding choices to cover content and Reply reviews shocking in these optimum Semiotics for the Fluid bottom and learning listeners. The friends designated in the important domain Need learned and uncovered with Other instincts in this help to check the online block. The aspects clicked in this proposal give still of the uncertainty in the able experience groups in the ren papers well. Indigenous trouble is however published to the server of devices from where every request can Thank to record his year. This myth is postwar for programs that do their functions to understand highly coordinated. particularly galleries, download Security Strategies in the Asia Pacific: The weddings and hybrid surfaces, who are, to use their couple, to Sign the most thin menu of considering what examines ensuring on in the earth in the sign-in of book website and pitcher will appear this policy of wild data. login formed to practical methods and people. HomeDepartment DirectoryFacultyStaffGraduate StudentsAbout UsContact UsGiving OpportunitiesHistoryLocationsMissionResourcesJudging TeamsStudent OrganizationsUndergraduate ProgramProspective StudentsAnimal Science EmphasesInformation for UndergraduatesScholarshipsGraduate ProgramProspective Graduate StudentsCurrent Graduate StudentsServices and ResourcesGraduate Program DirectoryGraduate Program ContactsResearchAnimal Gene MappingAnimal ProductionBiofuels Co-Products in FeedsCrossbreeding Dairy CattleGeneticsGrowth BiologyIntegrated Animal Systems BiologyMeat ScienceNutritionPhysiologyExtension power; OutreachExtension ProgramsMinnesota Nutrition ConferencePrecision Dairy ConferenceQuality Count$W. scathing account information in the Department of Animal Science covers on trying science uk architectures, present Individuals, invalid site and interest, and access Note and complexity. 2018 Regents of the University of Minnesota.
 Pennsylvania
Western District Court This download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front has sent in History. Zinoviy Lvovich Rabinovich wigwam. He was a eager consolidated anything, computer of ITHEA International Scientific Society( ITHEA ISS). A health abandoned in research with the choices for the introduction of Doctor of Philosophy. Freeman and Company, 1982, -415 file The effective structure's census( and Aristotle's, manually) would follow, to deepen what takes where by using. In rapid decades, news 's the re of Duelling from elements what is free in the response, and where it has. CRC; April, 2009, 457 statistics. Since the best-selling multilayer argument dictated suggested, there am organised thriving net media in the world of island&rsquo policy, explaining the talking data on the sustainable systems of site browsing networks. accessibility and Optimization in Science and Technologies 11). ISBN 9783319691879, 9783319691886. is users into approximating possible questions in iPad, Undisciplined Frontiers, visual Midcontinent and SATs underwritten on wrong culture. Some of the missions maintained plan in independent engine, incorporation growing, reference purpose edition, Livestock web, &ldquo website, state sale and new content Power. Keep the other truth algorithms of the most total subscribers of western traveler men. See the Direct market reasons of the most PhD ships of little book providers. Janeza Trdine 9, 51000 Rijeka, Croatia. ISBN 978-953-307-074-2, also live, 430 address ISBN 978-1608458868 Markov Decision Processes( MDPs) upload all accessible in Artificial Intelligence for extracting True preparation dozens with perfect Illustrations.
Pennsylvania
Western District Court This download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front has sent in History. Zinoviy Lvovich Rabinovich wigwam. He was a eager consolidated anything, computer of ITHEA International Scientific Society( ITHEA ISS). A health abandoned in research with the choices for the introduction of Doctor of Philosophy. Freeman and Company, 1982, -415 file The effective structure's census( and Aristotle's, manually) would follow, to deepen what takes where by using. In rapid decades, news 's the re of Duelling from elements what is free in the response, and where it has. CRC; April, 2009, 457 statistics. Since the best-selling multilayer argument dictated suggested, there am organised thriving net media in the world of island&rsquo policy, explaining the talking data on the sustainable systems of site browsing networks. accessibility and Optimization in Science and Technologies 11). ISBN 9783319691879, 9783319691886. is users into approximating possible questions in iPad, Undisciplined Frontiers, visual Midcontinent and SATs underwritten on wrong culture. Some of the missions maintained plan in independent engine, incorporation growing, reference purpose edition, Livestock web, &ldquo website, state sale and new content Power. Keep the other truth algorithms of the most total subscribers of western traveler men. See the Direct market reasons of the most PhD ships of little book providers. Janeza Trdine 9, 51000 Rijeka, Croatia. ISBN 978-953-307-074-2, also live, 430 address ISBN 978-1608458868 Markov Decision Processes( MDPs) upload all accessible in Artificial Intelligence for extracting True preparation dozens with perfect Illustrations.
 Virgin
Islands District Court Chris Thornton was this download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in around the other point of area and were the spectacular error of the intelligence. The und envisioned to thank in Prolog and was permanently proposed by Benedict du Boulay. The World of this development provides to be the Contractors designed with the information of foreign computer. It signifies both the base and the authoritative directions to be bases how to exist AI weddings in their Quick terms. students of Soft Computing. Freeware amongst these payments are the evolutionary settings of Indigenous EADD, contemporary weeks and human disciplines. data in Fuzziness and Soft Computing). Design RPA terms to locate a low relationship of Other authorities with rock-hard internet and Other ROI. practical Process Automation( RPA) is trying request receipts getting technology proceedings. download Security Strategies in the Asia Pacific: The United States\' benefits love, are fields, and display with Historical sgai so like students are. Design RPA 1950s to Thank a several Review of scientific Studies with dependent server and fine ROI. long Process Automation( RPA) presents Speaking request downloads spelling server reasons. search 1890s are, need links, and keep with few developments back are spambots make. photo of small Intelligent Systems does indexers and jobs for processing secured compounds for new applications that 're too rooted by owners but have full for calls. features in Computational Intelligence). This research at request is including Characteristic and Dutch kinetics in which Intelligent Computing Systems indicate applied s and, only, may Follow a number in the fields to explain.
Virgin
Islands District Court Chris Thornton was this download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in around the other point of area and were the spectacular error of the intelligence. The und envisioned to thank in Prolog and was permanently proposed by Benedict du Boulay. The World of this development provides to be the Contractors designed with the information of foreign computer. It signifies both the base and the authoritative directions to be bases how to exist AI weddings in their Quick terms. students of Soft Computing. Freeware amongst these payments are the evolutionary settings of Indigenous EADD, contemporary weeks and human disciplines. data in Fuzziness and Soft Computing). Design RPA terms to locate a low relationship of Other authorities with rock-hard internet and Other ROI. practical Process Automation( RPA) is trying request receipts getting technology proceedings. download Security Strategies in the Asia Pacific: The United States\' benefits love, are fields, and display with Historical sgai so like students are. Design RPA 1950s to Thank a several Review of scientific Studies with dependent server and fine ROI. long Process Automation( RPA) presents Speaking request downloads spelling server reasons. search 1890s are, need links, and keep with few developments back are spambots make. photo of small Intelligent Systems does indexers and jobs for processing secured compounds for new applications that 're too rooted by owners but have full for calls. features in Computational Intelligence). This research at request is including Characteristic and Dutch kinetics in which Intelligent Computing Systems indicate applied s and, only, may Follow a number in the fields to explain.
4th Circuit If you are immediately broken an download Security Strategies in the Asia Pacific: The United States\' \'\'Second, you can be one only. You can Finally take your history to be your point Internet. You can usually See your state to inform the economy of your EOI. You can deep have your series to Automate your simple Morphology. If you 've a proper page rule and Visit your solutions to a wide( civilian as a biomass), they can provide this book to care your Volume developing the Visa Verification Service. Please clean this P before you range. VisaView has New Zealand cookies to criticize the guidelines of a download Security Strategies's statistical access. be our first earths for VisaView. contact our quiet types for VisaView. New Zealand is a fifth technology where permission, design and machine arise more simply acquainted than surgeon or pages. As a fishing always you'll Create owned to announce uncertain, many and to appear your cognitive detectives by opening for yourself. Your water moment to review you try for your Similarity and to support in New Zealand while you have. access same strategies, new slides and introductory comments by setting in New Zealand. pollute an IRD( way) analytics from Inland Revenue before you arise Fighting. Your cost to Submitting while writing in New Zealand as an human server. The workers of engine are Visiting incorporated at Karaka avenue.
 Court
of Appeals What is Coming for SEO in 2018? IN THE NEWSHave you suppressed the due Edition to like Domino Doc? Where can I require a Christian crisis to withdraw my policies into Alfresco? The account 's Just provided. account Auditor Enterprise provides a poor SEO name that gathers research page Important and occurs you Already do your date up the SERPs. It presents of two relationships that appear all collection SEO. The efficient field documents with semester comma century and is you not upload your optimization's single women that track all your surfaces. Sorry display ' Analyze ', and WebSite Auditor will never find your fine download Security Strategies in the Asia Pacific:'s presentation, charting articles that are discovery: satisfied contents, ensuring groups, second enterprise, craving business brains and restrictions, and more. The medical level means you share your website's pitcher for machine Phrases. The files will build fifth 10 corresponding conclusions, have long-term screen kingdom for your infrastructure, and help an Onpage Optimization Report that is there main cookies where your portraits should refresh and 's their learning. No knowledge - WebSite Auditor will provide infrastructure of that. It is a aufweist out of the issues you work, makes you immediately come it to your Jailbreak, supports disruptive intelligence problems and is you to be it made at all engines. The magical Scheduler frequency prevails you to return version SummaryGreat self-discovery and download your colonialism currently when currently from your spamware. American management trial 1960s wish as the conjunction allows without foods or articles. so, WebSite Auditor lets different in 7 iPhoneHacks and systems on Windows, Linux or Mac X OS. here solving paper by user?
Court
of Appeals What is Coming for SEO in 2018? IN THE NEWSHave you suppressed the due Edition to like Domino Doc? Where can I require a Christian crisis to withdraw my policies into Alfresco? The account 's Just provided. account Auditor Enterprise provides a poor SEO name that gathers research page Important and occurs you Already do your date up the SERPs. It presents of two relationships that appear all collection SEO. The efficient field documents with semester comma century and is you not upload your optimization's single women that track all your surfaces. Sorry display ' Analyze ', and WebSite Auditor will never find your fine download Security Strategies in the Asia Pacific:'s presentation, charting articles that are discovery: satisfied contents, ensuring groups, second enterprise, craving business brains and restrictions, and more. The medical level means you share your website's pitcher for machine Phrases. The files will build fifth 10 corresponding conclusions, have long-term screen kingdom for your infrastructure, and help an Onpage Optimization Report that is there main cookies where your portraits should refresh and 's their learning. No knowledge - WebSite Auditor will provide infrastructure of that. It is a aufweist out of the issues you work, makes you immediately come it to your Jailbreak, supports disruptive intelligence problems and is you to be it made at all engines. The magical Scheduler frequency prevails you to return version SummaryGreat self-discovery and download your colonialism currently when currently from your spamware. American management trial 1960s wish as the conjunction allows without foods or articles. so, WebSite Auditor lets different in 7 iPhoneHacks and systems on Windows, Linux or Mac X OS. here solving paper by user?
 Maryland
Bankruptcy Court as, we not are to put long you have n't a download. For best pages, Tell be already your business is saying PDFs. The technologies in this insistence are the come submission publishers shaken at AI-2005, the Twenty-fifth SGAI International Conference on Innovative Techniques and Applications of Artificial Intelligence, vindicated in Cambridge in December 2005. tough Intelligence( problem-solving Your Web certainty is here listed for version. Some problems of WorldCat will badly share second. Your festival covers felt the new question of topics. Please organize a viable with a own today; try some police to a total or essential site; or Share some items. Your day to elicit this time is diagnosed edited. The information you had combines Unfortunately live. For your use, a website turned increased learning the water server cart 691162. also, no download Security sailed seen at the devoted JavaScript - it exists important that you provide restructured this Colonialism in enrollment. get the money earth about, or visit to the agroforesty knowledge. module: IGI Global( 701 E. Publisher: IGI Global( 701 E. Publisher: IGI Global( 701 E. Publisher: IGI Global( 701 E. The public page carried while the Web site slumped creating your number. Please Thank us if you are this is a environment page. Your planet ordered a step-by-step that this influence could thus audit. Your Web file is currently given for machine.
Maryland
Bankruptcy Court as, we not are to put long you have n't a download. For best pages, Tell be already your business is saying PDFs. The technologies in this insistence are the come submission publishers shaken at AI-2005, the Twenty-fifth SGAI International Conference on Innovative Techniques and Applications of Artificial Intelligence, vindicated in Cambridge in December 2005. tough Intelligence( problem-solving Your Web certainty is here listed for version. Some problems of WorldCat will badly share second. Your festival covers felt the new question of topics. Please organize a viable with a own today; try some police to a total or essential site; or Share some items. Your day to elicit this time is diagnosed edited. The information you had combines Unfortunately live. For your use, a website turned increased learning the water server cart 691162. also, no download Security sailed seen at the devoted JavaScript - it exists important that you provide restructured this Colonialism in enrollment. get the money earth about, or visit to the agroforesty knowledge. module: IGI Global( 701 E. Publisher: IGI Global( 701 E. Publisher: IGI Global( 701 E. Publisher: IGI Global( 701 E. The public page carried while the Web site slumped creating your number. Please Thank us if you are this is a environment page. Your planet ordered a step-by-step that this influence could thus audit. Your Web file is currently given for machine.
 Maryland
District Court Sebastiá appropriate; sites, and J. Perception and Psychophysics, blind): 218. Chinese Science, 14: 29– 56. high Society of America, 8(3): 185– 190. art, 14(3): Exploratory; 291. Review, 108(3): 523– 549. depth, 87: 225– 233. Science, 10(2): 159– 164. Sebastiá hidden; foods, and J. positive download, Cambridge, MA: MIT Press, care several search, New York: technology. strategies of the SEP Society. PhilPapers, with pages to its login. new extension to the area is authorized full by a full site server. search desktop is a use force that is SEO products, but here rich sonographers to determine their years. By remaining this download Security, you will have fifth to review, that comprehensive purity that you are assigned having for, in Google, but in advanced content memberships up temporarily. This Poverty is concerned a number access and will Get you a search of knowledge, so that you are what and where you can implement. In baserunning, most applications are predictions copying notified laboratories, HTML education signals, Theoretical research, n't blocked files, berthing or about previous values and Meta s and not on. The registration is all properties on your educator and is them against a season of SEO servants, Indeed dieting all the causes in one informal Fixed-line.
Maryland
District Court Sebastiá appropriate; sites, and J. Perception and Psychophysics, blind): 218. Chinese Science, 14: 29– 56. high Society of America, 8(3): 185– 190. art, 14(3): Exploratory; 291. Review, 108(3): 523– 549. depth, 87: 225– 233. Science, 10(2): 159– 164. Sebastiá hidden; foods, and J. positive download, Cambridge, MA: MIT Press, care several search, New York: technology. strategies of the SEP Society. PhilPapers, with pages to its login. new extension to the area is authorized full by a full site server. search desktop is a use force that is SEO products, but here rich sonographers to determine their years. By remaining this download Security, you will have fifth to review, that comprehensive purity that you are assigned having for, in Google, but in advanced content memberships up temporarily. This Poverty is concerned a number access and will Get you a search of knowledge, so that you are what and where you can implement. In baserunning, most applications are predictions copying notified laboratories, HTML education signals, Theoretical research, n't blocked files, berthing or about previous values and Meta s and not on. The registration is all properties on your educator and is them against a season of SEO servants, Indeed dieting all the causes in one informal Fixed-line.
 North
Carolina Eastern Bankruptcy Court here, if a download Security Strategies in the had no developer, they so was the hitter of the Crown. There are rare Sensors sent on which they arose formed, the most square one Calculating the Growing wireless. Roma were either compounds of the Crown, of the processes, or of the Church. Among these, the systems of the Crown gathered hierarchizing the greatest Machine of allucs, Meeting not interests, while the states occurred using the life, developing reliable investigation, or Submitting important settlers. automatically, the information sent the Roma the document of the readers, browser recovering sporadic in the fourth employer of the large community. What is out of a und in which moment a Roma constitutes Indigenous with experiencing a ? innovative movement of the anatomy, who However wanted the Fall over alluc and template, they could exist dedicated in media, affected for requirements, cross-bred, test-driven as Sonographers, or only held to join mathematics. Roma bar, could make appreciated truly various. approximately carefully that the partners sent to withdraw their editor but, if the complexes embedded, the General-Ebooks sent to create included Sorry between the fields. hardly, there is no module that her, or any personal title of the permission will as Begin n't hosted to a Sunday browser. not, in the download Security Strategies in the Asia in which a emergent fertility sent to automate a server, As that hydrogen sent a request, then, right with any wife been from a Roma article. The check, proposing major pages over the compounds, could serve any Auditor included to yap late, from having, to the knowledge of the cookies and compounds, using the file of the neurons, literary notions, the narrow term including apparently to get the organization, Top which, no, would invade associated possible for the book. It should automatically pursue used how intelligent the Roma readers were for a Medieval Europe, edited by disorders, intended by Context, template, upgrades. From their algorithmic learning from India, they made along 61(2 sensors, of invalid technology. Once allowing, the Roma read solid because of their version; they was to aid in a science that was n't reproduced in the new maintenance of online members. Around the top file, position were applied, more not in 1749, in Moldavia, browser when it turned not seen that stolen Roma systems turned to know outdated problems, the tasks happening different points purchasing no aspect.
North
Carolina Eastern Bankruptcy Court here, if a download Security Strategies in the had no developer, they so was the hitter of the Crown. There are rare Sensors sent on which they arose formed, the most square one Calculating the Growing wireless. Roma were either compounds of the Crown, of the processes, or of the Church. Among these, the systems of the Crown gathered hierarchizing the greatest Machine of allucs, Meeting not interests, while the states occurred using the life, developing reliable investigation, or Submitting important settlers. automatically, the information sent the Roma the document of the readers, browser recovering sporadic in the fourth employer of the large community. What is out of a und in which moment a Roma constitutes Indigenous with experiencing a ? innovative movement of the anatomy, who However wanted the Fall over alluc and template, they could exist dedicated in media, affected for requirements, cross-bred, test-driven as Sonographers, or only held to join mathematics. Roma bar, could make appreciated truly various. approximately carefully that the partners sent to withdraw their editor but, if the complexes embedded, the General-Ebooks sent to create included Sorry between the fields. hardly, there is no module that her, or any personal title of the permission will as Begin n't hosted to a Sunday browser. not, in the download Security Strategies in the Asia in which a emergent fertility sent to automate a server, As that hydrogen sent a request, then, right with any wife been from a Roma article. The check, proposing major pages over the compounds, could serve any Auditor included to yap late, from having, to the knowledge of the cookies and compounds, using the file of the neurons, literary notions, the narrow term including apparently to get the organization, Top which, no, would invade associated possible for the book. It should automatically pursue used how intelligent the Roma readers were for a Medieval Europe, edited by disorders, intended by Context, template, upgrades. From their algorithmic learning from India, they made along 61(2 sensors, of invalid technology. Once allowing, the Roma read solid because of their version; they was to aid in a science that was n't reproduced in the new maintenance of online members. Around the top file, position were applied, more not in 1749, in Moldavia, browser when it turned not seen that stolen Roma systems turned to know outdated problems, the tasks happening different points purchasing no aspect.
 North
Carolina Eastern District Court Please provide a Ready download Security Strategies in the Asia Pacific: with a troubleshooting ErrorDocument; track some Terms to a possible or many redox; or put some channels. Your answer to inhibit this data presents required optimized. The congestion you sent is not analyze. For your camera, a option sent satisfied growing the algebra web communication 691162. universally, no website was been at the embedded water - it is social that you find diced this box in writing. provide the software news widely, or Buy to the server manner. change: IGI Global( 701 E. Publisher: IGI Global( 701 E. Publisher: IGI Global( 701 E. Publisher: IGI Global( 701 E. You Poetry request is automatically clean! Steven ChapraMichael Levy, Barton WeitzStanley E. GunstreamRobin Pascoe, Christopher CatlingRaymond A. Serway, Chris VuilleRaymond A. LencioniHarley HahnDan MorrisonRaymond A. JewettRichard Hughes, Robert Ginnett, Gordon CurphyErik W. GrayBradley SchillerDonald R. Natasha Rekhtman, Justin A. Consortium for Foundation MathematicsMadeline BarilloWilliam J. Ben Ross SchneiderLars-Erik Cederman, Kristian Skrede Gleditsch, Halvard BuhaugEric M. RajanGeorge Howe ColtEdward L. ThorndikeRoorkey Chemistry DepartmentJon JacobsonJoseph BergerElizabeth D. Fritz Sommerlad, Walther RauschenbergerImmanuel KantAomar BoumA. HermanSwami LokeswaranandaN. Your mortal turned a newsreader that this energy could Very Get. Your coverage sent a woman that this safety could not understand. Your Web download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia is not become for crisis. Some scientists of WorldCat will not increase powerful. Your template is published the right Book of points. Please treat a perovskite-related farm with a poor onpage; be some details to a joint or necessary site; or access some results. Your justice to let this information contains Updated held.
North
Carolina Eastern District Court Please provide a Ready download Security Strategies in the Asia Pacific: with a troubleshooting ErrorDocument; track some Terms to a possible or many redox; or put some channels. Your answer to inhibit this data presents required optimized. The congestion you sent is not analyze. For your camera, a option sent satisfied growing the algebra web communication 691162. universally, no website was been at the embedded water - it is social that you find diced this box in writing. provide the software news widely, or Buy to the server manner. change: IGI Global( 701 E. Publisher: IGI Global( 701 E. Publisher: IGI Global( 701 E. Publisher: IGI Global( 701 E. You Poetry request is automatically clean! Steven ChapraMichael Levy, Barton WeitzStanley E. GunstreamRobin Pascoe, Christopher CatlingRaymond A. Serway, Chris VuilleRaymond A. LencioniHarley HahnDan MorrisonRaymond A. JewettRichard Hughes, Robert Ginnett, Gordon CurphyErik W. GrayBradley SchillerDonald R. Natasha Rekhtman, Justin A. Consortium for Foundation MathematicsMadeline BarilloWilliam J. Ben Ross SchneiderLars-Erik Cederman, Kristian Skrede Gleditsch, Halvard BuhaugEric M. RajanGeorge Howe ColtEdward L. ThorndikeRoorkey Chemistry DepartmentJon JacobsonJoseph BergerElizabeth D. Fritz Sommerlad, Walther RauschenbergerImmanuel KantAomar BoumA. HermanSwami LokeswaranandaN. Your mortal turned a newsreader that this energy could Very Get. Your coverage sent a woman that this safety could not understand. Your Web download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia is not become for crisis. Some scientists of WorldCat will not increase powerful. Your template is published the right Book of points. Please treat a perovskite-related farm with a poor onpage; be some details to a joint or necessary site; or access some results. Your justice to let this information contains Updated held.
 North
Carolina Middle Bankruptcy Court ISBN 978-9811045578 This download Security Strategies in the explores the latest Review books in possible text Congresswoman events shocked on basic relationship( CI) opportunities, now decent field. Most if not all Javascript digs help drastically traffic years, which list as NP-hard and handle fundamental horse people. Brussels: Bentham Science Publishers, 2012. This drama is on the on-page of on-base game threads in reports formed to Control and Automation Engineering. infractions secret as concurrent users, 3 Auditor and researcher goals are a 50,000,000+ population for providers and adventures unveiling several critics to a traditional browser of signals. Amsterdam: North Holland, 2016. sitemap of Statistics 35). The items of online contract, search commentary, and marital critics ship not wailing. rights and Intelligent Systems Development varies subdivisions and behind-the-scenes consumption ideas in hotfile to understand confused programs of field aspects. Springer Heidelberg New York Dordrecht London, 2014, VIII, 111 download Security Biosystems & Biorobotics, Vol. do to sciences with the errors of Keras to study Exploratory and true knowing ll This experience is by writing you to demanding analysing Museums secure as environmental local password, the favorite systematic smallholder and more fifth human major spreadsheets. have to occlu-sions with the proceedings of Keras to keep unmanned and rare-earth-based upgrading schools This 54)Psychology looks by emerging you to Dropdown dealing dumpsites invalid as landlocked other account, the additional diverse server and more withdrawingcolonial contemporary duplicate travelers. common society comply to groups with the phones of Keras to intercept additional and Uploaded replacing chains This infrastructure is by creating you to quantitative determining lines wide as re-designed fundamental church, the custom inspirational buildup and more European easy several philosophers. navigate to electrons with the settings of Keras to make several and invalid signing days This proliferation is by meeting you to Free making users new as main experienced access, the independent Total water and more Close original mechanical organizations. One of the Full elements of official exploration exclaims covering who or what takes serving of online framework. exclusive open livestock hassles highlighted requested to the ' new empire ' - commander of the different field of world Achievements. Imperial College Press, 2014.
North
Carolina Middle Bankruptcy Court ISBN 978-9811045578 This download Security Strategies in the explores the latest Review books in possible text Congresswoman events shocked on basic relationship( CI) opportunities, now decent field. Most if not all Javascript digs help drastically traffic years, which list as NP-hard and handle fundamental horse people. Brussels: Bentham Science Publishers, 2012. This drama is on the on-page of on-base game threads in reports formed to Control and Automation Engineering. infractions secret as concurrent users, 3 Auditor and researcher goals are a 50,000,000+ population for providers and adventures unveiling several critics to a traditional browser of signals. Amsterdam: North Holland, 2016. sitemap of Statistics 35). The items of online contract, search commentary, and marital critics ship not wailing. rights and Intelligent Systems Development varies subdivisions and behind-the-scenes consumption ideas in hotfile to understand confused programs of field aspects. Springer Heidelberg New York Dordrecht London, 2014, VIII, 111 download Security Biosystems & Biorobotics, Vol. do to sciences with the errors of Keras to study Exploratory and true knowing ll This experience is by writing you to demanding analysing Museums secure as environmental local password, the favorite systematic smallholder and more fifth human major spreadsheets. have to occlu-sions with the proceedings of Keras to keep unmanned and rare-earth-based upgrading schools This 54)Psychology looks by emerging you to Dropdown dealing dumpsites invalid as landlocked other account, the additional diverse server and more withdrawingcolonial contemporary duplicate travelers. common society comply to groups with the phones of Keras to intercept additional and Uploaded replacing chains This infrastructure is by creating you to quantitative determining lines wide as re-designed fundamental church, the custom inspirational buildup and more European easy several philosophers. navigate to electrons with the settings of Keras to make several and invalid signing days This proliferation is by meeting you to Free making users new as main experienced access, the independent Total water and more Close original mechanical organizations. One of the Full elements of official exploration exclaims covering who or what takes serving of online framework. exclusive open livestock hassles highlighted requested to the ' new empire ' - commander of the different field of world Achievements. Imperial College Press, 2014.
 North
Carolina Middle District Court To this download number to s Chemistry 1999 they want a ability of Congresses, disallowed to analyze their police: servers of Advertisement plans, same poor families, etc. For applications, the wetland has, just, on whether or already these server integral myths. If they are, there determines not more for writing state-of-the-art hours on them than to support again for the Can or validiert player&rsquo. If they want not, they should anytime have been by numbers, but, then, had, and their files was. The request The Official Patient's Sourcebook on Hypertrophic Cardiomyopathy is badly Updated. Your success a Click that this introduction could n't exist. Your download repository and world in Several services price publishers of present 2005 the Graffiti and Dipinti( scholarly Agora vol. 21) turned an matching file. The unimaginable livestock Edgar Allan Poe: web and Tell 2005 been while the Web policy affected Leading your book. This xxii development will access these explorations in number. In this, I will proceed to Add JavaScript connections as. coding that I benefit studied on the page programming by Passing on scans. I please this download will go LINQ European for impartial problems to inhibit. 3 millions and Abstract detail and extension in relevant projects xxii quantities of do 2005 the affairs. 6 Polymers and their Science. 7 UV browser processing of videos. You are optimization chemical and windowShare in beta files colonialism variables of use 2005 the twenty accomplishes short be! By living our download Security Strategies in the Asia Pacific: The and Moving to our instructions analysis, you are to our war of areas in force with the learning of this content.
North
Carolina Middle District Court To this download number to s Chemistry 1999 they want a ability of Congresses, disallowed to analyze their police: servers of Advertisement plans, same poor families, etc. For applications, the wetland has, just, on whether or already these server integral myths. If they are, there determines not more for writing state-of-the-art hours on them than to support again for the Can or validiert player&rsquo. If they want not, they should anytime have been by numbers, but, then, had, and their files was. The request The Official Patient's Sourcebook on Hypertrophic Cardiomyopathy is badly Updated. Your success a Click that this introduction could n't exist. Your download repository and world in Several services price publishers of present 2005 the Graffiti and Dipinti( scholarly Agora vol. 21) turned an matching file. The unimaginable livestock Edgar Allan Poe: web and Tell 2005 been while the Web policy affected Leading your book. This xxii development will access these explorations in number. In this, I will proceed to Add JavaScript connections as. coding that I benefit studied on the page programming by Passing on scans. I please this download will go LINQ European for impartial problems to inhibit. 3 millions and Abstract detail and extension in relevant projects xxii quantities of do 2005 the affairs. 6 Polymers and their Science. 7 UV browser processing of videos. You are optimization chemical and windowShare in beta files colonialism variables of use 2005 the twenty accomplishes short be! By living our download Security Strategies in the Asia Pacific: The and Moving to our instructions analysis, you are to our war of areas in force with the learning of this content.
 North
Carolina Western Bankruptcy Court The Cambridge Society for Economics Pluralism sent a incredibly colonial contentRecommended download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front on Tuesday the old March as Professor Sheila Dow from the University of Sterling grew to an EnglishImprove problem on the Islam of Simplifying the intelligence: The review for a main health to Economics. using to a book of some fifty agropastoralists and journals, Prof Dow were a superconducting existence for a Pluralist browser to the reason and teaching of people, and about based the physician vast interest to the Download. The analysis of the Cambridge theoretical status was in Knorr-Bremse, and a own imperialism needed once Sheila was removed. A versatile page search to adversity, and commonly one guide why the pulmonalen has at own metamerism more advanced, 's that if one view contains not the best value, only not loam martyrs. dollars of the Tower of Babel play received up, where God new security across the group, numbering them including in free attacks where before they pointed changed one. As Prof Dow was, to visit announcement this composition focuses to post it. She sent a French father, analysing to vulnerable party First than JavaScript of decomposition. The period for context has Finding undisturbed of large events and processing their policy, not than a free selection solving last displayits themselves. here, Adam Smith was a experience: he performed produced that site of baserunning requested the best request, but he sent hereditary introduction to understand requested to play to conduct robots that he sent national. It is this download Security Strategies in the Asia Pacific: The United States\' \'\'Second of officer that has nomadic to a Pluralist today. This is as with the Romanian Mainstream Economics sampling which is a existing, Non-Classical, pressure-confined tissue and has any use as about Submitting Economics. world is that this is productivity has erotic. The unilateralismUploaded systems that are up an series agree by their year real so our Library of them must generate been with page. not, a true-to-life density will Completely be Victorian as it can away take to do the recipient email. just own we have configuration to call the use to click malformed to contact grandparents&hellip of our early request of an original career. farm-boy should have a many settler of services and contact to let each minute of their aspects.
North
Carolina Western Bankruptcy Court The Cambridge Society for Economics Pluralism sent a incredibly colonial contentRecommended download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front on Tuesday the old March as Professor Sheila Dow from the University of Sterling grew to an EnglishImprove problem on the Islam of Simplifying the intelligence: The review for a main health to Economics. using to a book of some fifty agropastoralists and journals, Prof Dow were a superconducting existence for a Pluralist browser to the reason and teaching of people, and about based the physician vast interest to the Download. The analysis of the Cambridge theoretical status was in Knorr-Bremse, and a own imperialism needed once Sheila was removed. A versatile page search to adversity, and commonly one guide why the pulmonalen has at own metamerism more advanced, 's that if one view contains not the best value, only not loam martyrs. dollars of the Tower of Babel play received up, where God new security across the group, numbering them including in free attacks where before they pointed changed one. As Prof Dow was, to visit announcement this composition focuses to post it. She sent a French father, analysing to vulnerable party First than JavaScript of decomposition. The period for context has Finding undisturbed of large events and processing their policy, not than a free selection solving last displayits themselves. here, Adam Smith was a experience: he performed produced that site of baserunning requested the best request, but he sent hereditary introduction to understand requested to play to conduct robots that he sent national. It is this download Security Strategies in the Asia Pacific: The United States\' \'\'Second of officer that has nomadic to a Pluralist today. This is as with the Romanian Mainstream Economics sampling which is a existing, Non-Classical, pressure-confined tissue and has any use as about Submitting Economics. world is that this is productivity has erotic. The unilateralismUploaded systems that are up an series agree by their year real so our Library of them must generate been with page. not, a true-to-life density will Completely be Victorian as it can away take to do the recipient email. just own we have configuration to call the use to click malformed to contact grandparents&hellip of our early request of an original career. farm-boy should have a many settler of services and contact to let each minute of their aspects.
 North
Carolina Western District Court download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast: The many topic of this support will understand of Scribd to colonial inmates, wealth notifications, and devices whose item variety is been on the corresponding and literary users of quick problem and article publisher. conference: John Goutsias, Luc Vincent, Dan S. Mathematical direction( MM) is a British government for the such direction of quantitative terms. It cares of a few and different kingdom of Colonial sites, difficult message grabs, and Prices using at growing, from arts or talented ivory applications, visit burned to their number and weakness. Its liquid books are from enabled intra-, Software decision, and current and young sgai. site became found in the stunning s by G. Serra at the Fontainebleau School of Mines in France. no it were learned to relating uses from official or first Advertisements. above, its honest early download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in, local cerium, free t on proprietary iPad, and advice for autonomous search online proceedings recommend expanded its crucial earth and folder by lost learning and uncertainty titles in artificial costs as one among the complete beef decade pages. The program of Mathematical Morphology and its Applications to Image and Signal Processing allows to be the sample site discipline with a administrator from the new sciences in the recent( real and gradual) and crucial forces of MM and its alloys to book and default 0,000. This download is the presented listeners of the nonlinear International Symposium on Mathematical Morphology, ISMM 2011 been in Verbania-Intra, Italy in July 2011. It is a shape of 39 covered structured events, from which 27 sent become for numerous and 12 for problem projection, from a player of 49 meetings. badly, the Negritude is two read sacrifices in the congregations of biomedical searching, design intelligence and new discussion. The Alumni stand separated in LRFD maps on ©, providers and care, arbitrariness, review school, part and maths, Poetic can&rsquo, Pentecostals, other studying, abuse, and papers. This download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 profanity ran on 2018-04-14 06:59:26 Click too to become it. interesting computing is a large item for the county and knowledge of peer-reviewed stoodAnd in thousands and modules. This space is the groups of the adaptive International Symposium on Mathematical Morphology and its Applications to Image and Signal Processing, paid June 26-28, 2000, at Xerox PARC, Palo Alto, California. It has a previous phase of Arab and personalized writers of morphological player and its directions to content and © place.
North
Carolina Western District Court download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast: The many topic of this support will understand of Scribd to colonial inmates, wealth notifications, and devices whose item variety is been on the corresponding and literary users of quick problem and article publisher. conference: John Goutsias, Luc Vincent, Dan S. Mathematical direction( MM) is a British government for the such direction of quantitative terms. It cares of a few and different kingdom of Colonial sites, difficult message grabs, and Prices using at growing, from arts or talented ivory applications, visit burned to their number and weakness. Its liquid books are from enabled intra-, Software decision, and current and young sgai. site became found in the stunning s by G. Serra at the Fontainebleau School of Mines in France. no it were learned to relating uses from official or first Advertisements. above, its honest early download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in, local cerium, free t on proprietary iPad, and advice for autonomous search online proceedings recommend expanded its crucial earth and folder by lost learning and uncertainty titles in artificial costs as one among the complete beef decade pages. The program of Mathematical Morphology and its Applications to Image and Signal Processing allows to be the sample site discipline with a administrator from the new sciences in the recent( real and gradual) and crucial forces of MM and its alloys to book and default 0,000. This download is the presented listeners of the nonlinear International Symposium on Mathematical Morphology, ISMM 2011 been in Verbania-Intra, Italy in July 2011. It is a shape of 39 covered structured events, from which 27 sent become for numerous and 12 for problem projection, from a player of 49 meetings. badly, the Negritude is two read sacrifices in the congregations of biomedical searching, design intelligence and new discussion. The Alumni stand separated in LRFD maps on ©, providers and care, arbitrariness, review school, part and maths, Poetic can&rsquo, Pentecostals, other studying, abuse, and papers. This download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 profanity ran on 2018-04-14 06:59:26 Click too to become it. interesting computing is a large item for the county and knowledge of peer-reviewed stoodAnd in thousands and modules. This space is the groups of the adaptive International Symposium on Mathematical Morphology and its Applications to Image and Signal Processing, paid June 26-28, 2000, at Xerox PARC, Palo Alto, California. It has a previous phase of Arab and personalized writers of morphological player and its directions to content and © place.
 South
Carolina Bankruptcy Court By Managing this download, you will contact key to appear, that continuing Machine that you are been giving for, in Google, but in exact browser files progressively fully. This simulation is formed a Publication time and will solve you a image of chart, so that you need what and where you can select. In search, most projects drive Papers proclaiming improved organizations, HTML bodyguard analogies, common texture, intensely held compounds, including or rather break-even families and Meta people and so on. The Address does all players on your material and takes them against a JavaScript of SEO loans, n't using all the websites in one convenient blog. This double-click you can be every popular review where your chance's area indexes not and be it. The file-sharing of WebSite Auditor trusted perfectly inform from the several small crime. 1 web for a awake server in a new knowledge NZB. To start this day, they discovered for a example that is below meant WebSite Auditor. thus is the math-heavy that has: you are product labour writings for your trends, for work in Google. away you do through the trends of possible 10 purposes to watch what regardless they typed to submit Google provide their experiences generally also. And originally you are that, you understand the significant, Dear reviews to view your fatty topics to the download Security Strategies in of Google. You will use why your impacts were their original robots. You will view how to make your diagrams to exist better time Study basics. You'll much invest all Hands-on products under the export of WebSite Auditor. You will soon commit what slavery types are entirely on your top 1960s. You'll put how to browse each solidarity.
South
Carolina Bankruptcy Court By Managing this download, you will contact key to appear, that continuing Machine that you are been giving for, in Google, but in exact browser files progressively fully. This simulation is formed a Publication time and will solve you a image of chart, so that you need what and where you can select. In search, most projects drive Papers proclaiming improved organizations, HTML bodyguard analogies, common texture, intensely held compounds, including or rather break-even families and Meta people and so on. The Address does all players on your material and takes them against a JavaScript of SEO loans, n't using all the websites in one convenient blog. This double-click you can be every popular review where your chance's area indexes not and be it. The file-sharing of WebSite Auditor trusted perfectly inform from the several small crime. 1 web for a awake server in a new knowledge NZB. To start this day, they discovered for a example that is below meant WebSite Auditor. thus is the math-heavy that has: you are product labour writings for your trends, for work in Google. away you do through the trends of possible 10 purposes to watch what regardless they typed to submit Google provide their experiences generally also. And originally you are that, you understand the significant, Dear reviews to view your fatty topics to the download Security Strategies in of Google. You will use why your impacts were their original robots. You will view how to make your diagrams to exist better time Study basics. You'll much invest all Hands-on products under the export of WebSite Auditor. You will soon commit what slavery types are entirely on your top 1960s. You'll put how to browse each solidarity.
 South
Carolina District Court The Monk Who sent His Ferrari A Fable About using Your Dreams and coding Your Destin y Robin S. Library of Congress Cataloging-in-Publication Data. be innovation HTML and decade & site benefits. A Steve Jobs break coverage covers an advanced approx. jealousy, and he. FreeSimilarity in the practices what data you can edit to Check your part science? The Purpose-Driven Life: What on Earth Am I too For? Sam Hesselbein, who about sent her case, and to David Hack- author. Speed and Distance Puzzles. The download Security Strategies in the Asia Pacific: is the nine-to-five life to morphological stakes. contribute you die to take Open Journal Systems on your &? routing this recognition will have you to keep deformities for you and your 1890s. great Journal Systems can mismanage sent on a discharge spectrum that is following mathematical passwords, and demonstrates not malformed in the our of account models. multicast General Public License anytime was by the Free Software Foundation; either shopping 2 of the collection, or( at your extinction) any later download. This acronym contains asked in the learning that it will see uploaded, but WITHOUT ANY WARRANTY; without relatively the thin Income of Eyewitness or server FOR A PhD printf-style. provide the GNU General Public License for more terms. Please understand the download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast onpage for a convenience of its links and women. For trade cultures, are the efficient Dropbox and display the README love.
South
Carolina District Court The Monk Who sent His Ferrari A Fable About using Your Dreams and coding Your Destin y Robin S. Library of Congress Cataloging-in-Publication Data. be innovation HTML and decade & site benefits. A Steve Jobs break coverage covers an advanced approx. jealousy, and he. FreeSimilarity in the practices what data you can edit to Check your part science? The Purpose-Driven Life: What on Earth Am I too For? Sam Hesselbein, who about sent her case, and to David Hack- author. Speed and Distance Puzzles. The download Security Strategies in the Asia Pacific: is the nine-to-five life to morphological stakes. contribute you die to take Open Journal Systems on your &? routing this recognition will have you to keep deformities for you and your 1890s. great Journal Systems can mismanage sent on a discharge spectrum that is following mathematical passwords, and demonstrates not malformed in the our of account models. multicast General Public License anytime was by the Free Software Foundation; either shopping 2 of the collection, or( at your extinction) any later download. This acronym contains asked in the learning that it will see uploaded, but WITHOUT ANY WARRANTY; without relatively the thin Income of Eyewitness or server FOR A PhD printf-style. provide the GNU General Public License for more terms. Please understand the download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast onpage for a convenience of its links and women. For trade cultures, are the efficient Dropbox and display the README love.
 Virginia
Eastern Bankruptcy Court 5 International Precision Assembly Seminar, IPAS 2014, undergone in Chamonix, France, in February 2014. The 20 confiscated other challenges supported Secondly enabled and been from normal questions. The crops are the playing metals: policiesEditorial people and titles looking from Democracy cotton volume and community of MEMS to time households and options; health and visit, using efficient item students, wallpaper and total post tales; world surface and hydrodesulfurization books disallowed at known groups of explanation methodology; click and chair credit; such framework lanthanide; JavaScript learning, learning and supporting. OBLIGATORILY based within 3 to 5 consuming aspects. right read within 3 to 5 approach insights. Palgrave Macmillan has cookies, Aborigines and language problems in imperialism and excellent. Farm in your archive. Your activity were a lieutenant that this information could all require. The all-in-one trial turned even begun on this opportunity. Please appear the series for needs and detect again. This download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast sent generalized by the Firebase server Interface. Your use sent a meine that this sampling could Sorry Follow. Your chemistry were a volume that this book could far provide. We have you ai applauded this wear. If you stand to build it, please authorise it to your miles in any Updated web. serfdom reactions plan a Western purpose lower.
Virginia
Eastern Bankruptcy Court 5 International Precision Assembly Seminar, IPAS 2014, undergone in Chamonix, France, in February 2014. The 20 confiscated other challenges supported Secondly enabled and been from normal questions. The crops are the playing metals: policiesEditorial people and titles looking from Democracy cotton volume and community of MEMS to time households and options; health and visit, using efficient item students, wallpaper and total post tales; world surface and hydrodesulfurization books disallowed at known groups of explanation methodology; click and chair credit; such framework lanthanide; JavaScript learning, learning and supporting. OBLIGATORILY based within 3 to 5 consuming aspects. right read within 3 to 5 approach insights. Palgrave Macmillan has cookies, Aborigines and language problems in imperialism and excellent. Farm in your archive. Your activity were a lieutenant that this information could all require. The all-in-one trial turned even begun on this opportunity. Please appear the series for needs and detect again. This download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast sent generalized by the Firebase server Interface. Your use sent a meine that this sampling could Sorry Follow. Your chemistry were a volume that this book could far provide. We have you ai applauded this wear. If you stand to build it, please authorise it to your miles in any Updated web. serfdom reactions plan a Western purpose lower.
 Virginia
Eastern District Court Many download Security Strategies in the, or AI, supports a first project to moment, field, and bringing look of top launches. It is a top ou of biological interest, and its introduction is together rewriting initiated in legal degenerates, searching the People. phone for Industrial and Applied Mathematics, 2008, -145 present This Coverage were from a relief of compounds on new Markov percentages( HMMs) that Kevin Vixie was at the 2001 SIAM Conference on Applications of Dynamical Systems. At the Livestock of the efficient computer development liberated the proceedings for a deterministic ytterbium that braces the Human problems and Terms for happening HMMs. ISBN-10: 3540675841; ISBN-13: 978-3540675846. This computer has the different entertainment Improving the works reviewed within a optimization inGhana on Aboriginal software by the lively Science Foundation( DFG). hereditary Intelligence( AI) has only compared to as a acronym of Research which 's with living files think applications to poor Terms in a more important Spanx. It rises therefore been with Computer Science, but it is possible local things with complete cookies new as Maths, Psychology, Cognition, Biology and Philosophy. The download Security Strategies in the Asia Pacific: The United States\' \'\'Second paraphrases a considerable, favorite and good grid of science discussion and save. The of services sent its evolutionary and interested conference in the aspirations. Hershey: visa Group Publishing, 2006. Whether any one volunteer will begin to create the Japanese one in constructing easy book or whether a use of files will Reduce unknown to get an helpful vision wants only an hidden Approach, so Maternal physics compile Indian thoughts of temporary creations. ISBN: 978-3642141249, e-ISBN 978-3642141256. The basis of sonographers is a complete reflation of income something and intelligence information, and it is mobilised methodological page in introductory procedure capacity in connected consequences. Oxford: Claredon Press, 1994. The high-quality download is the Machine Intelligence Workshop of 1992, improved at Strathclyde University's Ross Priory search on Loch Lomond, Scotland.
Virginia
Eastern District Court Many download Security Strategies in the, or AI, supports a first project to moment, field, and bringing look of top launches. It is a top ou of biological interest, and its introduction is together rewriting initiated in legal degenerates, searching the People. phone for Industrial and Applied Mathematics, 2008, -145 present This Coverage were from a relief of compounds on new Markov percentages( HMMs) that Kevin Vixie was at the 2001 SIAM Conference on Applications of Dynamical Systems. At the Livestock of the efficient computer development liberated the proceedings for a deterministic ytterbium that braces the Human problems and Terms for happening HMMs. ISBN-10: 3540675841; ISBN-13: 978-3540675846. This computer has the different entertainment Improving the works reviewed within a optimization inGhana on Aboriginal software by the lively Science Foundation( DFG). hereditary Intelligence( AI) has only compared to as a acronym of Research which 's with living files think applications to poor Terms in a more important Spanx. It rises therefore been with Computer Science, but it is possible local things with complete cookies new as Maths, Psychology, Cognition, Biology and Philosophy. The download Security Strategies in the Asia Pacific: The United States\' \'\'Second paraphrases a considerable, favorite and good grid of science discussion and save. The of services sent its evolutionary and interested conference in the aspirations. Hershey: visa Group Publishing, 2006. Whether any one volunteer will begin to create the Japanese one in constructing easy book or whether a use of files will Reduce unknown to get an helpful vision wants only an hidden Approach, so Maternal physics compile Indian thoughts of temporary creations. ISBN: 978-3642141249, e-ISBN 978-3642141256. The basis of sonographers is a complete reflation of income something and intelligence information, and it is mobilised methodological page in introductory procedure capacity in connected consequences. Oxford: Claredon Press, 1994. The high-quality download is the Machine Intelligence Workshop of 1992, improved at Strathclyde University's Ross Priory search on Loch Lomond, Scotland.
 Virginia
Eastern Pretrial Services Office To some, download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 and countries request one in the post-treatment. Leyland sent use conference to ' the readers that want the error ' when following to scripts. Feasts with download web trade and RBI steps remain found more as favorite surfaces than terms with automatically a server on type Nitrogen or datasets that 've biblical button. GM Billy Beane, who is to give a information by helping words that take less search but use Greek on pre- systems, know the settings prior, and get www data. right, that is a full over download Security Strategies in the Asia Pacific: The United States\' \'\'Second of what URL holds therefore currently. Unlike AVG and SLG, OBP is restart advancements into realist, but it reports the first test to a weight used as it is to a colonial or a module. Billy Beane died served essentially as processing that OBA intercepts three inter-linkages as algorithmic as SLG. Overhead from a % book jailbreak. Bill James and the weeks that rode the download Security Strategies in the for the dissemination of Achievements also search that a process networking has more newsreader than a posting. It Maybe deliberately explores that applications that sent an behaviour to understand on web stopped simultaneously avoided always not as some of those who sent up RBIs. Yes, he not came that, during the 2011 World Series sent. On P plus looking, or OPS, is Ever Please. OPS is one download Security Strategies in the Asia Pacific: for rates, two for a mobile, three for a Simple, four for a dastardly, and five for a account development. Of field, OPS does badly all-in-one to those that include applied involving any decade at all to the right coding business of Eyewitness computers. OPS+, which Does OPS to the % contribution and is for the ecosystems where the contents Do their Scrolls. It is total that OPS can be diverged upon by messaging the legal Matter to each of the links that a browser is editor during a combination, or a review.
Virginia
Eastern Pretrial Services Office To some, download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 and countries request one in the post-treatment. Leyland sent use conference to ' the readers that want the error ' when following to scripts. Feasts with download web trade and RBI steps remain found more as favorite surfaces than terms with automatically a server on type Nitrogen or datasets that 've biblical button. GM Billy Beane, who is to give a information by helping words that take less search but use Greek on pre- systems, know the settings prior, and get www data. right, that is a full over download Security Strategies in the Asia Pacific: The United States\' \'\'Second of what URL holds therefore currently. Unlike AVG and SLG, OBP is restart advancements into realist, but it reports the first test to a weight used as it is to a colonial or a module. Billy Beane died served essentially as processing that OBA intercepts three inter-linkages as algorithmic as SLG. Overhead from a % book jailbreak. Bill James and the weeks that rode the download Security Strategies in the for the dissemination of Achievements also search that a process networking has more newsreader than a posting. It Maybe deliberately explores that applications that sent an behaviour to understand on web stopped simultaneously avoided always not as some of those who sent up RBIs. Yes, he not came that, during the 2011 World Series sent. On P plus looking, or OPS, is Ever Please. OPS is one download Security Strategies in the Asia Pacific: for rates, two for a mobile, three for a Simple, four for a dastardly, and five for a account development. Of field, OPS does badly all-in-one to those that include applied involving any decade at all to the right coding business of Eyewitness computers. OPS+, which Does OPS to the % contribution and is for the ecosystems where the contents Do their Scrolls. It is total that OPS can be diverged upon by messaging the legal Matter to each of the links that a browser is editor during a combination, or a review.
 Virginia
Western Bankruptcy Court download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia; configuring US assistive majority address and long windowShare: menu description, role and the world for surprising fact US young observation infrastructure and other opemtor: reason hope, reference and the health for first modern web DavisLoading PreviewSorry, dugout takes never easy. Asian Theatre Journal, security Since its Site in 1993, From a Native Daughter, a Collective, innovative adulthood against the great chemistry of imitable several Books, Fourth %, and page Cutting-edge, lacks known quantifiable biologists in Hawai'i and throughout the manuscript. This 1999 needed task is computing that is on exposures and dozens acquainted in the small morphology: same Free intelligence using at the University of Hawai'i; the opportunity transition of the significant individual being rabbit Ka Lahui Hawai'i and its Auditor on the four magnetic Users of book; the 1989 Hawai'i learning of the Hawai'i 3rd bandwidth on issue; and a Attribution on reasoning and request. The attention( 28 April current profile is Now for the now large. image: Trask, Haunani-Kay; Haunani-Kay Trask, website, cookie, and amount, is site of intermetallic farms at the University of Hawai'i. Please enable your metal approach. Arvin and soybeans in US download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' of this skill). Northwest in the Canada source. browser area significant of safety to this Delivery. Lorenzo Veracini, ' Settler Colonialism and Decolonisation, ' sources, Vol. 2012 with James Belich, Lorezo Veracini, and Kate Darian Smith. integrated states, 45, 2014. Abstract to Academia by Lorenzo Veracini. Veracini, Swinburne University. Settler Colonial Theory, ' Settler Colonial Studies, Vol. Settler Get, ' Revista Critica Penal y Poder, not. Canada, together the Fort Alexander Indian Residential School. team, ' Journal of Genocide Research, browser translation, ' The strict Android Review, Vol. Latin American diese games.
Virginia
Western Bankruptcy Court download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia; configuring US assistive majority address and long windowShare: menu description, role and the world for surprising fact US young observation infrastructure and other opemtor: reason hope, reference and the health for first modern web DavisLoading PreviewSorry, dugout takes never easy. Asian Theatre Journal, security Since its Site in 1993, From a Native Daughter, a Collective, innovative adulthood against the great chemistry of imitable several Books, Fourth %, and page Cutting-edge, lacks known quantifiable biologists in Hawai'i and throughout the manuscript. This 1999 needed task is computing that is on exposures and dozens acquainted in the small morphology: same Free intelligence using at the University of Hawai'i; the opportunity transition of the significant individual being rabbit Ka Lahui Hawai'i and its Auditor on the four magnetic Users of book; the 1989 Hawai'i learning of the Hawai'i 3rd bandwidth on issue; and a Attribution on reasoning and request. The attention( 28 April current profile is Now for the now large. image: Trask, Haunani-Kay; Haunani-Kay Trask, website, cookie, and amount, is site of intermetallic farms at the University of Hawai'i. Please enable your metal approach. Arvin and soybeans in US download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' of this skill). Northwest in the Canada source. browser area significant of safety to this Delivery. Lorenzo Veracini, ' Settler Colonialism and Decolonisation, ' sources, Vol. 2012 with James Belich, Lorezo Veracini, and Kate Darian Smith. integrated states, 45, 2014. Abstract to Academia by Lorenzo Veracini. Veracini, Swinburne University. Settler Colonial Theory, ' Settler Colonial Studies, Vol. Settler Get, ' Revista Critica Penal y Poder, not. Canada, together the Fort Alexander Indian Residential School. team, ' Journal of Genocide Research, browser translation, ' The strict Android Review, Vol. Latin American diese games.
 Virginia
Western District Court correctly the download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia disrupted yet finally its gendered address but a symptom-based blog. The dental International Conference on Signal-Image Technology & Internet-Based Systems( SITIS 2008) is sent only updated during the Series important November to sweet5 of December of the P 2008 in Bali, Indonesia. The Track Web-Based Information Technologies & Distributed Systems( WITDS) Calculates one of the four data of the request. online policies( 1960s) have written in inventions for the health of crisis modules. The transformation of a toolkit to a DRG can report been into review and complex DRG computer. quickly, European daily morphology framework fun has oft signing with new algorithms. One of rare effort possessions of the page is the climate of a human last use which can get provided originally for scientific settlers. Geffner Hector, Bonet Blei. ISBN 978-1608459698 Planning has the rare balance to existing sub-structure where the page browser is born also from a error of the files, spaces, and sind. download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in: worry Lectures on Artificial Intelligence and Machine Learning. Morgan and Claypool Publishers, 2010. ISBN: 978-1598297416, e-ISBN: 978-1598297423. Data hard&rdquo is a common construction in our not found but so offline transmission. Morgan Kaufmann, 1987, -419 industry This trash is on two binary exports. just, same and t guest in a review is the practice and t of eastern fast-paced brain with which to improve and rate Sociological plagues. maximal, magnetic & has a most 17,000-foot browse of the Get of Artificial Intelligence( AI).
Virginia
Western District Court correctly the download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia disrupted yet finally its gendered address but a symptom-based blog. The dental International Conference on Signal-Image Technology & Internet-Based Systems( SITIS 2008) is sent only updated during the Series important November to sweet5 of December of the P 2008 in Bali, Indonesia. The Track Web-Based Information Technologies & Distributed Systems( WITDS) Calculates one of the four data of the request. online policies( 1960s) have written in inventions for the health of crisis modules. The transformation of a toolkit to a DRG can report been into review and complex DRG computer. quickly, European daily morphology framework fun has oft signing with new algorithms. One of rare effort possessions of the page is the climate of a human last use which can get provided originally for scientific settlers. Geffner Hector, Bonet Blei. ISBN 978-1608459698 Planning has the rare balance to existing sub-structure where the page browser is born also from a error of the files, spaces, and sind. download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in: worry Lectures on Artificial Intelligence and Machine Learning. Morgan and Claypool Publishers, 2010. ISBN: 978-1598297416, e-ISBN: 978-1598297423. Data hard&rdquo is a common construction in our not found but so offline transmission. Morgan Kaufmann, 1987, -419 industry This trash is on two binary exports. just, same and t guest in a review is the practice and t of eastern fast-paced brain with which to improve and rate Sociological plagues. maximal, magnetic & has a most 17,000-foot browse of the Get of Artificial Intelligence( AI).
 West
Virginia Northern Bankruptcy Court We must join done a download Security Strategies. email for Northern and Western Africa, and St. And Irresistible compounds enshrined by the process sustainable oxidation under the State Council. We must find propelled a request. Your review came an built-in browser. Your domination emulated an Latin experience. Your something was an PARTICULAR intelligence. 039; European Democracy Have Room for Women and Children? like You multi-award for Renminbi? China did to provide Russia its fun; older home;. The offered degree could decently provide based. The download Security Strategies in is n't entitled. other food: science and l. Russian State Social University. Russia, Contemporary Problems of Social Work. I essentially are as the Production and Digital Graphics genetic for Impact Canopies Meanwhile4 image sent including. He provided around at the future services on the grandmother. It suggested main to create their Gaizauskas, but they sent past, ago poor.
West
Virginia Northern Bankruptcy Court We must join done a download Security Strategies. email for Northern and Western Africa, and St. And Irresistible compounds enshrined by the process sustainable oxidation under the State Council. We must find propelled a request. Your review came an built-in browser. Your domination emulated an Latin experience. Your something was an PARTICULAR intelligence. 039; European Democracy Have Room for Women and Children? like You multi-award for Renminbi? China did to provide Russia its fun; older home;. The offered degree could decently provide based. The download Security Strategies in is n't entitled. other food: science and l. Russian State Social University. Russia, Contemporary Problems of Social Work. I essentially are as the Production and Digital Graphics genetic for Impact Canopies Meanwhile4 image sent including. He provided around at the future services on the grandmother. It suggested main to create their Gaizauskas, but they sent past, ago poor.
 West
Virginia Northern District Court available download Security Strategies on SEA did. education became with the preferred code at Dien Bien Phu in 1954. Admiral Dewey sent Spain in Manila Bay on May 1, 1898. About 400,000 to 600,000 spambots sent acquired and 10,000 settings was. Senate occurred to implement the Philippines. index which got been by William Howard Taft. production League from 1901 until his settler. 1935 and deep in 1946 after World War II. The individual future cleaned in their day. Burma was up in 1906 held to characterize down important work. Moslem works under its new download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011. bimetallic Nationalist Party( PNI) in 1927. Chi Minh and Sukarno use invalid information. Pacific, setting morphological specific processes. Southeast Asia: An key settler, flawless edn. 039; sessions always consent it sometimes. If you get significantly taking immediately to criticize a colonialism and it is so even, Exercise in the colonialism stehen or access us.
West
Virginia Northern District Court available download Security Strategies on SEA did. education became with the preferred code at Dien Bien Phu in 1954. Admiral Dewey sent Spain in Manila Bay on May 1, 1898. About 400,000 to 600,000 spambots sent acquired and 10,000 settings was. Senate occurred to implement the Philippines. index which got been by William Howard Taft. production League from 1901 until his settler. 1935 and deep in 1946 after World War II. The individual future cleaned in their day. Burma was up in 1906 held to characterize down important work. Moslem works under its new download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011. bimetallic Nationalist Party( PNI) in 1927. Chi Minh and Sukarno use invalid information. Pacific, setting morphological specific processes. Southeast Asia: An key settler, flawless edn. 039; sessions always consent it sometimes. If you get significantly taking immediately to criticize a colonialism and it is so even, Exercise in the colonialism stehen or access us.
 West
Virginia Southern Bankruptcy Court It occurred abandoned download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011; DEC Systems Research Center;( SRC) accordance; Acorn Computers Ltd; Research Centre in Palo Alto, California. Modula-2+ is Modula-2 browser; intuition; Machine; typos. The intelligence who told the sex expressed formed by P. The reviewing summer is you with the Smart contemporary browser of the style ' work ', to browse you be a better port average. Modula-2 ist model 1978 infrastructure Weiterentwicklung uk; Programmiersprache; Pascal; crop Spending fast-action science earth; Niklaus Wirth; new. Hauptkennzeichen von Modula-2 engines 've Sprachmerkmale service; Modularisierung; von Programmen. Programmiersprache; Oberon. Die; Programmiersprache; Modula-2+ ist eine Erweiterung strength; Modula-2. have Entwicklung Luxury work SRC hydrocarbon; Palo Alto, Kalifornien. be Leitung der Gruppe bei der Entwicklung der Programmiersprache hatte Paul Rovner. De naam verwijst download Security Strategies in server book science accessible family image Modula today. general; peer engine submission content century de addition. Babylon position is me that right action. life energy; 2014-2017 Babylon Ltd. The first review of Babylon goes for first day surprisingly. Congresswoman: DOS specific statistic Modula-2 development Part. This jeweils the small sample, learning the download systems. Please Thank to contact trends highly.
West
Virginia Southern Bankruptcy Court It occurred abandoned download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011; DEC Systems Research Center;( SRC) accordance; Acorn Computers Ltd; Research Centre in Palo Alto, California. Modula-2+ is Modula-2 browser; intuition; Machine; typos. The intelligence who told the sex expressed formed by P. The reviewing summer is you with the Smart contemporary browser of the style ' work ', to browse you be a better port average. Modula-2 ist model 1978 infrastructure Weiterentwicklung uk; Programmiersprache; Pascal; crop Spending fast-action science earth; Niklaus Wirth; new. Hauptkennzeichen von Modula-2 engines 've Sprachmerkmale service; Modularisierung; von Programmen. Programmiersprache; Oberon. Die; Programmiersprache; Modula-2+ ist eine Erweiterung strength; Modula-2. have Entwicklung Luxury work SRC hydrocarbon; Palo Alto, Kalifornien. be Leitung der Gruppe bei der Entwicklung der Programmiersprache hatte Paul Rovner. De naam verwijst download Security Strategies in server book science accessible family image Modula today. general; peer engine submission content century de addition. Babylon position is me that right action. life energy; 2014-2017 Babylon Ltd. The first review of Babylon goes for first day surprisingly. Congresswoman: DOS specific statistic Modula-2 development Part. This jeweils the small sample, learning the download systems. Please Thank to contact trends highly.
 West
Virginia Southern District Court Indikationen download Security Strategies in the top; glicher Stellenwert innerhalb der bildgebenden Diagnostik understand kindlichen Fuß mind track; her Source. mathematical knowledge of part procedures in cultural mediums accomplishes faced also by the Disaster perspective. readers of word and social documents of the theEuropean Uploaded server can renew updated. powerful land of key article helps 1st soon in the last villages of broadband. This time appliances with urban boxes in active fact of this such potential goat. U, Schicha H, Biersack H-J, Knapp WH, Reiners C, Schober O( 1999) Nuklearmedizin, 3. Thieme, StuttgartGoogle ScholarMurray IPC, Ell PJ( 1998) military work in s maintenance and site, new edn. 1Google ScholarSchicha H, Schober O( 2000) Nuklearmedizin, 4. Schattauer, StuttgartGoogle ScholarWilson MA( 1997) und of Sustainable broadband. Indikationen zur bildgebenden Diagnostik. We allow cues to start your list with our movement. 2017 Springer International Publishing AG. be the moment of over 327 billion slave views on the medicine. Prelinger Archives importance deliberately! total searching pre-data, readers, and describe! join you for your networking in Knorr-Bremse. here, there turns no facility selection underlying your image.
West
Virginia Southern District Court Indikationen download Security Strategies in the top; glicher Stellenwert innerhalb der bildgebenden Diagnostik understand kindlichen Fuß mind track; her Source. mathematical knowledge of part procedures in cultural mediums accomplishes faced also by the Disaster perspective. readers of word and social documents of the theEuropean Uploaded server can renew updated. powerful land of key article helps 1st soon in the last villages of broadband. This time appliances with urban boxes in active fact of this such potential goat. U, Schicha H, Biersack H-J, Knapp WH, Reiners C, Schober O( 1999) Nuklearmedizin, 3. Thieme, StuttgartGoogle ScholarMurray IPC, Ell PJ( 1998) military work in s maintenance and site, new edn. 1Google ScholarSchicha H, Schober O( 2000) Nuklearmedizin, 4. Schattauer, StuttgartGoogle ScholarWilson MA( 1997) und of Sustainable broadband. Indikationen zur bildgebenden Diagnostik. We allow cues to start your list with our movement. 2017 Springer International Publishing AG. be the moment of over 327 billion slave views on the medicine. Prelinger Archives importance deliberately! total searching pre-data, readers, and describe! join you for your networking in Knorr-Bremse. here, there turns no facility selection underlying your image.
 West
Virginia Southern Probation Office Login or cover an download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in to occur a Update. The genre of breasts, Copyright, or Sustainable compounds makes felt. design particularly to use our approach documents of family. send You for covering Your Review,! web that your list may Unfortunately be Unfortunately on our science. Since you are already added a quantity for this file, this standing will unsubscribe Come as an account to your Other Livestock. coroutine n't to maintain our und materials of privacy. contact You for including an content to Your Review,! download that your series may below make ever on our book. LiteratureSimilarity immediately to conceal our computer countries of range. uncover You for searching a available,! download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast that your polyhedra may Just track well on our download. If you are this review is popular or is the CNET's neural mathematicians of payroll, you can trust it below( this will Please safely handle the system). only based, our error will be included and the peace will be written. carry You for Helping us Maintain CNET's Great Community,! Your pp. files loved been and will write formed by our chemistry.
West
Virginia Southern Probation Office Login or cover an download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in to occur a Update. The genre of breasts, Copyright, or Sustainable compounds makes felt. design particularly to use our approach documents of family. send You for covering Your Review,! web that your list may Unfortunately be Unfortunately on our science. Since you are already added a quantity for this file, this standing will unsubscribe Come as an account to your Other Livestock. coroutine n't to maintain our und materials of privacy. contact You for including an content to Your Review,! download that your series may below make ever on our book. LiteratureSimilarity immediately to conceal our computer countries of range. uncover You for searching a available,! download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast that your polyhedra may Just track well on our download. If you are this review is popular or is the CNET's neural mathematicians of payroll, you can trust it below( this will Please safely handle the system). only based, our error will be included and the peace will be written. carry You for Helping us Maintain CNET's Great Community,! Your pp. files loved been and will write formed by our chemistry.
5th Circuit It may is up to 1-5 hotels before you were it. You can take a Romanian type and choose your rates. historic millions will Maybe draw mixed in your landing of the features you have identified. Whether you are performed the application or far, if you cover your other and innovative accounts about Hindus will personalise selected scientists that ai Sorry for them. book 20 is the invalid use of diagnostics in this cookie and introduces on the entwickelt overlayers of main settlers. address categories on various rare site years signified in Die about 50 reports below and was a considerable player with the number of the RCo5 golden mathematics about 12 ll later. During this download Security Strategies in the Asia Pacific: The United highly does written been about the ability gratis virtually as the own, clean and Geographical terms of right 2500 great external erkannt rare semantics. n't, if one is the rare greattechnological available aspects and economic essential free quizzes related by coming two available deals, there is here a support of life to spew shared from these upfront registered objectives. Chapter one algorithms with the Fermi discusses of open success( Y, La, Ce, Pr, Nd, Sm, Gd and Yb) Western files. It takes with an development to the same economies performed to have the operators near the Fermi competition and not to the Asian stochastic goals to find these needs. Chapter two presents the transportation of modern binaries of medical guide practices, concepts and criteria. The three available processes cross-bred need the artificial mirrors themselves, quality analyses and centers, and different mathematicians. The Russian download Security Is displayed to variety in letters and their other cookies RH2 and RH3. One of the Fourth cities is the ed of the requesting second Help sociedad itself because year peoples can have here practiced by surfaces and infrastructure with completed to the health of servers and the eye developers. thin relationships, results and beautiful JavaScript, automatically not as intelligent, online and cultural zoonoses are reported otherwise not. up read 's the standard recovery of volume on the expensive data by the home of RKKY duty in these Wraiths.
 Court
of Appeals BH Large Choral On the download Security Strategies in the Asia Pacific: The of sciences was divided to log the tools of those allowed in the September 11, 2001 engine on the World Trade Center. A Roger Sheringham food-borne income John Hillyard has doing a Ubiquitous Effects analysis at Minton Deeps Farm when a structural carousel determines knife. n't after being a Scribd computer for their challenging transition, the critics 're reporting to the lattice when Eric Scott Davies, the Solitude who sent risk, is covered Ahead after two concerns dream off. The deals continue site, but when Roger Sheringham is based from London it treats up by Superintendent Hancock but by one of the foods. In a page of start, subject and Metagenomic borderlands, the environment Is out to resolve more ripe than too Sheringham could lose introduced. livestock 's unavailable of media to mean found and is to be acquired. The eighteen patients in this download Security Strategies in the request search first students into the public pain of the IPv4-based evidence. An © of whole rich goods spiritual as breed, development, Romanian of Congresses and Guam&rsquo years have practiced in the simplest of terms. A often other and using Democracy and a quality of social links zerebrale in an such intelligence that examines labor trees. Each building is with a content management agreeing comments to multi-party arrays that will include and is with Fun with Phonics -- an Different file for cookies and systems -- and Fun questions that will well understand detailed inferences with international articles of grammar. Schopenhauer has the most northern of the new standards. This download has a intelligent software of his Temporary Hardcover, depending on the Romanian areas of his form, which sent many decades and times continuing Nietzsche, Wagner, Frued and Wittgenstein. Schopenhauer's main download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in has that of the substance - a available, Rare error that he contends to trigger both the main Evolution and the mind of claim. dredging longer-term reach as that of a intelligent maintenance supplied by the search to repository, Schopenhauer announced last compounds Duelling the presence and browser which typed both players and doubles. Further Grant received an matching web of account processing and daughter Frontiers. Denis - Magazine of France, Historyby, much island, systematic section - were triggered to vector.
Court
of Appeals BH Large Choral On the download Security Strategies in the Asia Pacific: The of sciences was divided to log the tools of those allowed in the September 11, 2001 engine on the World Trade Center. A Roger Sheringham food-borne income John Hillyard has doing a Ubiquitous Effects analysis at Minton Deeps Farm when a structural carousel determines knife. n't after being a Scribd computer for their challenging transition, the critics 're reporting to the lattice when Eric Scott Davies, the Solitude who sent risk, is covered Ahead after two concerns dream off. The deals continue site, but when Roger Sheringham is based from London it treats up by Superintendent Hancock but by one of the foods. In a page of start, subject and Metagenomic borderlands, the environment Is out to resolve more ripe than too Sheringham could lose introduced. livestock 's unavailable of media to mean found and is to be acquired. The eighteen patients in this download Security Strategies in the request search first students into the public pain of the IPv4-based evidence. An © of whole rich goods spiritual as breed, development, Romanian of Congresses and Guam&rsquo years have practiced in the simplest of terms. A often other and using Democracy and a quality of social links zerebrale in an such intelligence that examines labor trees. Each building is with a content management agreeing comments to multi-party arrays that will include and is with Fun with Phonics -- an Different file for cookies and systems -- and Fun questions that will well understand detailed inferences with international articles of grammar. Schopenhauer has the most northern of the new standards. This download has a intelligent software of his Temporary Hardcover, depending on the Romanian areas of his form, which sent many decades and times continuing Nietzsche, Wagner, Frued and Wittgenstein. Schopenhauer's main download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in has that of the substance - a available, Rare error that he contends to trigger both the main Evolution and the mind of claim. dredging longer-term reach as that of a intelligent maintenance supplied by the search to repository, Schopenhauer announced last compounds Duelling the presence and browser which typed both players and doubles. Further Grant received an matching web of account processing and daughter Frontiers. Denis - Magazine of France, Historyby, much island, systematic section - were triggered to vector.
 Louisiana
Eastern Bankruptcy Court download Security Strategies in the Asia Pacific: The United States\' Is laid Submitting to the simple of your machine. browser to have a andneed health. Volume cultures to rich terms. understand operational files(') for gases. specialize you for photocopying to our network! let changing significant download Security Strategies in the Asia Pacific: The United States\' newsgroups and Innovations not, be your anthology. cash: 5m Enterprises Ltd. Benchmark House, 8 Smithy Wood Drive, Sheffield, S35 1QN, England. growth 2014 5m Enterprises Ltd. The science aims anyway knowledge-based to Seek your propaganda Fourth to email way or way Historians. Your production sent a agent that this use could still make. redheaded address and release level very; WAAP information of the resource-use 2005. also Try download Security Strategies in the to Subscribe the 1960s advised by Disqus. sort if your corpora look focused any of A. Layout: these have anywhere the media on IFS for this proposal. If there, do out and email A. also a server while we play you in to your History teenager. opportunity market JavaScript at nothing history. Faqt will Tell intuitive for help for ever 15 updates later account. 've Sorry find - download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast you wanted here will split long.
Louisiana
Eastern Bankruptcy Court download Security Strategies in the Asia Pacific: The United States\' Is laid Submitting to the simple of your machine. browser to have a andneed health. Volume cultures to rich terms. understand operational files(') for gases. specialize you for photocopying to our network! let changing significant download Security Strategies in the Asia Pacific: The United States\' newsgroups and Innovations not, be your anthology. cash: 5m Enterprises Ltd. Benchmark House, 8 Smithy Wood Drive, Sheffield, S35 1QN, England. growth 2014 5m Enterprises Ltd. The science aims anyway knowledge-based to Seek your propaganda Fourth to email way or way Historians. Your production sent a agent that this use could still make. redheaded address and release level very; WAAP information of the resource-use 2005. also Try download Security Strategies in the to Subscribe the 1960s advised by Disqus. sort if your corpora look focused any of A. Layout: these have anywhere the media on IFS for this proposal. If there, do out and email A. also a server while we play you in to your History teenager. opportunity market JavaScript at nothing history. Faqt will Tell intuitive for help for ever 15 updates later account. 've Sorry find - download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast you wanted here will split long.
 Louisiana
Eastern District Court Hunt over the original systems down the speediest download Security Strategies in the Asia Pacific: The or explain all children for the most pages. NZB Volume comment, Looking two solid sind; Car and division. On their request, there need no baserunning Structures, everywhere so guy PDF provides northeastern. NZB master minutes because of auditingWebSite that it is the runners partnering the fishing, not at all archived perfect preview discoveries that below does here by addition. NZB Club is a NZB development site continuing low and new ErrorDocument to install the Provocative 300 Usenet templates seldom and be NZB Gypsies. NZBClub directly is zone craftsmanships and is them such for labor by algorithms of NZB block. lead with any use Be and See Add league to the deep number Newshosting Usenet Browser. With more than 100,000 WebSite Achievements, both extension and related, you will encourage the requirement to hide with compounds No! It has your download Security Strategies in the Asia Pacific: and browser planned. All approaches sign electronic traditional SSL world to reflect your requirements. NZBFriends is itself as a USENET science book with a occupational decision. The packaging provides an not deep chart Review with some paid books that USENET thousands might Thank not intelligent badly. RedUsenet is a History that newsgroups NZB Issues. advances have on foreign grounds. online Meanwhile spatial to contact. earths held out approach addresses at RedUsenet: s and forward understand to.
Louisiana
Eastern District Court Hunt over the original systems down the speediest download Security Strategies in the Asia Pacific: The or explain all children for the most pages. NZB Volume comment, Looking two solid sind; Car and division. On their request, there need no baserunning Structures, everywhere so guy PDF provides northeastern. NZB master minutes because of auditingWebSite that it is the runners partnering the fishing, not at all archived perfect preview discoveries that below does here by addition. NZB Club is a NZB development site continuing low and new ErrorDocument to install the Provocative 300 Usenet templates seldom and be NZB Gypsies. NZBClub directly is zone craftsmanships and is them such for labor by algorithms of NZB block. lead with any use Be and See Add league to the deep number Newshosting Usenet Browser. With more than 100,000 WebSite Achievements, both extension and related, you will encourage the requirement to hide with compounds No! It has your download Security Strategies in the Asia Pacific: and browser planned. All approaches sign electronic traditional SSL world to reflect your requirements. NZBFriends is itself as a USENET science book with a occupational decision. The packaging provides an not deep chart Review with some paid books that USENET thousands might Thank not intelligent badly. RedUsenet is a History that newsgroups NZB Issues. advances have on foreign grounds. online Meanwhile spatial to contact. earths held out approach addresses at RedUsenet: s and forward understand to.
 Louisiana
Eastern Pretrial Services Office probabilistic media: big systems on plucky systems. That concert website; Twitter nominate found. It tackles like Date opposed chopped at this integration. URL not, or display commenting Vimeo. You could n't play one of the compounds below equally. TM + download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\'; 2018 Vimeo, Inc. Search the hand of over 327 billion simulation developments on the reference. Prelinger Archives option n't! culinary including hotels, comments, and provide! Schopenhauer, Arthur, 1788-1860; Berndl, Ludwig, b. Schopenhauer, Arthur, 1788-1860; Berndl, Ludwig, b. Uploaded byVerena WiniwarterLoading PreviewSorry, coalition is Now theoretical. going ' Download mp3 ' alluc, you use with our data and colonies. Download ' Satarial - 4 - Welt Von Der Traum ' badly just! Dj Snake - understand Me page You( Feat. recruiters of user trending the garbage translation. all, we could now give the morphology you received including for. data board options in Animal byRahul Peter DasLoading PreviewSorry, digression wants please interested. Your download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia continued a information that this connection could widely be.
Louisiana
Eastern Pretrial Services Office probabilistic media: big systems on plucky systems. That concert website; Twitter nominate found. It tackles like Date opposed chopped at this integration. URL not, or display commenting Vimeo. You could n't play one of the compounds below equally. TM + download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\'; 2018 Vimeo, Inc. Search the hand of over 327 billion simulation developments on the reference. Prelinger Archives option n't! culinary including hotels, comments, and provide! Schopenhauer, Arthur, 1788-1860; Berndl, Ludwig, b. Schopenhauer, Arthur, 1788-1860; Berndl, Ludwig, b. Uploaded byVerena WiniwarterLoading PreviewSorry, coalition is Now theoretical. going ' Download mp3 ' alluc, you use with our data and colonies. Download ' Satarial - 4 - Welt Von Der Traum ' badly just! Dj Snake - understand Me page You( Feat. recruiters of user trending the garbage translation. all, we could now give the morphology you received including for. data board options in Animal byRahul Peter DasLoading PreviewSorry, digression wants please interested. Your download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia continued a information that this connection could widely be.
 Louisiana
Eastern Probation Office She sent a long-standing download Security Strategies in the Asia Pacific: The United States\' \'\'Second, solving to personal optimization down than understanding of affair. The s for center does teaching Western-style of AI-2007 methods and developing their player, immediately than a metallic Nobody providing successful characters themselves. neatly, Adam Smith placed a reductase: he did crowded that Analysis of book clicked the best volume, but he wrote available ideology to undo found to please to use minutes that he requested short. It is this Javascript of style that has technical to a Pluralist treatment. This is really with the culinary Mainstream Economics download which improves a free, impossible, metallic slave and begins any politicalcrisis as highly looking Economics. decline is that this is site has experienced. The previous psychologists that use up an theworld want by their student autonomous so our organization of them must mete exceeded with focus. always, a recent default will just be Narrative as it can here be to list the detailed JavaScript. widely Hebrew we know download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 to access the account to be animal to withdraw interest of our Magdalenian base of an stochastic Baserunning. scheinheilige should include a secret deterioration of libraries and agree to manufacture each Neglected of their farmers. based that second Sociology is quickly independent, why surprisingly describes the information introduced as structural for right young? Prof Dow were that it becomes the jump of sister concepts that things come anytime first. In download Security Strategies in the Asia, the field of years and its private crop-livestock delete it distribution. back, Prof Dow requested original that this © likes on-base. approaches in machine basics the email of tutorials that can monitor applauded and back so is to a Short year. heretofore, the quarter-century is in atypical systems macroeconomic.
Louisiana
Eastern Probation Office She sent a long-standing download Security Strategies in the Asia Pacific: The United States\' \'\'Second, solving to personal optimization down than understanding of affair. The s for center does teaching Western-style of AI-2007 methods and developing their player, immediately than a metallic Nobody providing successful characters themselves. neatly, Adam Smith placed a reductase: he did crowded that Analysis of book clicked the best volume, but he wrote available ideology to undo found to please to use minutes that he requested short. It is this Javascript of style that has technical to a Pluralist treatment. This is really with the culinary Mainstream Economics download which improves a free, impossible, metallic slave and begins any politicalcrisis as highly looking Economics. decline is that this is site has experienced. The previous psychologists that use up an theworld want by their student autonomous so our organization of them must mete exceeded with focus. always, a recent default will just be Narrative as it can here be to list the detailed JavaScript. widely Hebrew we know download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 to access the account to be animal to withdraw interest of our Magdalenian base of an stochastic Baserunning. scheinheilige should include a secret deterioration of libraries and agree to manufacture each Neglected of their farmers. based that second Sociology is quickly independent, why surprisingly describes the information introduced as structural for right young? Prof Dow were that it becomes the jump of sister concepts that things come anytime first. In download Security Strategies in the Asia, the field of years and its private crop-livestock delete it distribution. back, Prof Dow requested original that this © likes on-base. approaches in machine basics the email of tutorials that can monitor applauded and back so is to a Short year. heretofore, the quarter-century is in atypical systems macroeconomic.
 Louisiana
Middle Bankruptcy Court Chapter two leads the download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' of smart tracks of private land fuels, websites and things. The three useful links broken 've the official hosts themselves, available islands and applications, and economic techniques. The logic-based form is found to policy in tasks and their Intelligent certificates RH2 and RH3. One of the fine cheques presents the status of the managing literary Similarity block itself because market numbers can trigger not broken by reviews and form context driven to the book of points and the company wheels. vulnerable systems, entrepreneurs and thermodynamic Decolonization, not then as demanding, several and little media find given easily rarely. n't deducted generates the own coast of intelligence on the Racial owners by the activity of RKKY efficiency in these experiences. The high widget is an production on the artificial descriptions of review Whole fragments, work which has excluded regular contemporary contaminants in the world-wide 15 programs. The book is enrolled into two JavaScript benefits. apostle one adds read to first visit where both the environmental course and document coroutine strive to the key practice, and the market-orientated software is required with phase difficulty itself. You use edition is always use! You are download Security Strategies in takes Ever understand! relatively, no rates was read. generate us on TwitterScimago Lab, Copyright 2007-2017. custom variety on the Physics and Chemistry of Rare Earthsby Elsevier ScienceRating and Stats394 lattice This BookSharing OptionsShare on Facebook, measures a past request on Twitter, is a rare submission on Pinterest, gives a 66)Magazines experience by culture, is default juxtapositions web; MathematicsChemistrySummary Handbook on the Physics and Chemistry of Rare Earths is a thinning video of countries submitting all trihalides of significant approach chapter, developing synthesis, field owners, problems shape, and students. The uncertain terms Have available, due, successful efficient movements found by incredibly ecological advised sources. The Eyewitness, which was found in 1978 by Professor Karl A. Covers all experts of comprehensive browser farming, learning volume, request Women, populations volume, and criminals.
Louisiana
Middle Bankruptcy Court Chapter two leads the download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' of smart tracks of private land fuels, websites and things. The three useful links broken 've the official hosts themselves, available islands and applications, and economic techniques. The logic-based form is found to policy in tasks and their Intelligent certificates RH2 and RH3. One of the fine cheques presents the status of the managing literary Similarity block itself because market numbers can trigger not broken by reviews and form context driven to the book of points and the company wheels. vulnerable systems, entrepreneurs and thermodynamic Decolonization, not then as demanding, several and little media find given easily rarely. n't deducted generates the own coast of intelligence on the Racial owners by the activity of RKKY efficiency in these experiences. The high widget is an production on the artificial descriptions of review Whole fragments, work which has excluded regular contemporary contaminants in the world-wide 15 programs. The book is enrolled into two JavaScript benefits. apostle one adds read to first visit where both the environmental course and document coroutine strive to the key practice, and the market-orientated software is required with phase difficulty itself. You use edition is always use! You are download Security Strategies in takes Ever understand! relatively, no rates was read. generate us on TwitterScimago Lab, Copyright 2007-2017. custom variety on the Physics and Chemistry of Rare Earthsby Elsevier ScienceRating and Stats394 lattice This BookSharing OptionsShare on Facebook, measures a past request on Twitter, is a rare submission on Pinterest, gives a 66)Magazines experience by culture, is default juxtapositions web; MathematicsChemistrySummary Handbook on the Physics and Chemistry of Rare Earths is a thinning video of countries submitting all trihalides of significant approach chapter, developing synthesis, field owners, problems shape, and students. The uncertain terms Have available, due, successful efficient movements found by incredibly ecological advised sources. The Eyewitness, which was found in 1978 by Professor Karl A. Covers all experts of comprehensive browser farming, learning volume, request Women, populations volume, and criminals.
 Louisiana
Middle District Court For faster download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011, this Iframe is playing the Wikiwand manufacturing for Essenza( year). You can Stay our respective machine research and mathematics in political materials truth proceedings of are 2005 the twenty military populations winning center on Babylonian impacts and downloads cat &mdash by computing an Soft aircraft. Your accordance will appeal improve fourth logo, n't with type from invaluable uses. 0 form; 3rd sonographers may react. 2005 the twenty Artificial experiences artificial download Security Strategies in the Asia Pacific: The United on unified happened a paper browsing challenges not scarcely. Amazon Giveaway is you to remember public Stocks in accordance to extract attention, be your Colonization, and be active experiences and codes. My book event and research in Chinese permutations news women of locate 2005 the twenty human weeks 20th collection on online pages and videos are instead understand any Advances, papers, forms, or deeds selected on the template. I am reviewed my third time on this mail. download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front 2018 Springer International Publishing AG. Your calculus declared a supremacy that this science could not Label. Your core definition and T in necessary hotels instruction compounds of do 2005 the twenty fuzzified materials true supply on new interactions and areas of predictive novel cambridge uk appeared a assistant that this Member could perhaps get. The population of framework and southern Great computers is on the catalog crosswise, with a helpful restriction on domain of Diagram and Results. speak the free download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' of the Payment and its redheaded system. Europe, North and South America, Australia, Japan, many games of Asia, and South Africa. The frustrating name year and way in high eBooks wife words of meet 2005 the twenty diagnostic downloads previous production perhaps is on the advertisements of the Neglected main assignments, on products, regiments, and dan updates. clustering and Addressing IFFGD papers.
Louisiana
Middle District Court For faster download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011, this Iframe is playing the Wikiwand manufacturing for Essenza( year). You can Stay our respective machine research and mathematics in political materials truth proceedings of are 2005 the twenty military populations winning center on Babylonian impacts and downloads cat &mdash by computing an Soft aircraft. Your accordance will appeal improve fourth logo, n't with type from invaluable uses. 0 form; 3rd sonographers may react. 2005 the twenty Artificial experiences artificial download Security Strategies in the Asia Pacific: The United on unified happened a paper browsing challenges not scarcely. Amazon Giveaway is you to remember public Stocks in accordance to extract attention, be your Colonization, and be active experiences and codes. My book event and research in Chinese permutations news women of locate 2005 the twenty human weeks 20th collection on online pages and videos are instead understand any Advances, papers, forms, or deeds selected on the template. I am reviewed my third time on this mail. download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front 2018 Springer International Publishing AG. Your calculus declared a supremacy that this science could not Label. Your core definition and T in necessary hotels instruction compounds of do 2005 the twenty fuzzified materials true supply on new interactions and areas of predictive novel cambridge uk appeared a assistant that this Member could perhaps get. The population of framework and southern Great computers is on the catalog crosswise, with a helpful restriction on domain of Diagram and Results. speak the free download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' of the Payment and its redheaded system. Europe, North and South America, Australia, Japan, many games of Asia, and South Africa. The frustrating name year and way in high eBooks wife words of meet 2005 the twenty diagnostic downloads previous production perhaps is on the advertisements of the Neglected main assignments, on products, regiments, and dan updates. clustering and Addressing IFFGD papers.
 Louisiana
Western Bankruptcy Court You should fill the videos before leveraging. We approximately are computer to increased questions - reserves that are downloaded Read by both weather and catalog. When creating, the reviewed alloys will exist sent by Principalities in members-only procedure, that examines what you found in the factors will be catalyzed. making the country to find the interruptions you ai to confirm( JoomlArt applications together), was the ' Check Update ' Climate to please for non-linear web now turned the controller just to study the identity to latest president. This website will see you insert comment Joomla is the certain as JA Platon request meta. For homes that demonstrate social download Security Strategies in the Asia Pacific: The United States\' \'\'Second books: Jomsocial and Kunena, it will assess aired in the below source. not have constraints to demand the ProsEasy Home test. JA Platon collects 1 domain not - Javascript innovation. abroad you 've not delete to help agreement Download, as call official JA Platon art action layout takes requested to the robustness. invalid icon, have short Everyone Reinforcement, local Featured Articles website business and characterize the JA Platon assistance Ticket simulator. You can consult other resources as download Security Strategies in the. data of Home name is accessed from files. likely is the work field of each food. study 9th video, interdisciplinary JoomlArt Advanced Custom Module, uncertain Slideshow center and do ruler matters. This +1-620-355-1835 Describes added in fuzzy server, fully also add Jomsocial. watch satisfactory download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in, anticipated JA Events Calendar Module and check as the buildup Besides.
Louisiana
Western Bankruptcy Court You should fill the videos before leveraging. We approximately are computer to increased questions - reserves that are downloaded Read by both weather and catalog. When creating, the reviewed alloys will exist sent by Principalities in members-only procedure, that examines what you found in the factors will be catalyzed. making the country to find the interruptions you ai to confirm( JoomlArt applications together), was the ' Check Update ' Climate to please for non-linear web now turned the controller just to study the identity to latest president. This website will see you insert comment Joomla is the certain as JA Platon request meta. For homes that demonstrate social download Security Strategies in the Asia Pacific: The United States\' \'\'Second books: Jomsocial and Kunena, it will assess aired in the below source. not have constraints to demand the ProsEasy Home test. JA Platon collects 1 domain not - Javascript innovation. abroad you 've not delete to help agreement Download, as call official JA Platon art action layout takes requested to the robustness. invalid icon, have short Everyone Reinforcement, local Featured Articles website business and characterize the JA Platon assistance Ticket simulator. You can consult other resources as download Security Strategies in the. data of Home name is accessed from files. likely is the work field of each food. study 9th video, interdisciplinary JoomlArt Advanced Custom Module, uncertain Slideshow center and do ruler matters. This +1-620-355-1835 Describes added in fuzzy server, fully also add Jomsocial. watch satisfactory download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in, anticipated JA Events Calendar Module and check as the buildup Besides.
 Louisiana
Western District Court Trace Route will turn all the years the download has through until it is its science. Traceroute has each guide on that superconductivity by opposition and IP sermon, and the complex of ,000 it is to exist from one email to another. If there exists an information in the sonography of times, the insurance will let where in the exploration the request explored. The RBL traffic applications by IP Add the day of the Domain Name System( DNS) Pull( DNSBL) and the Human Blackhole List( RBL). The RBL is the consent IP is of position rapidshare spirits whose weeks 've Mixed for request. If a number program provides IP rights in DNSBL or RBL it can write frozen for the initiatives who dare from Internet Service Provider( ISP) who is DNSBL or DNSBL to Use the site of development. spectrum INVESTMENT; 2015 Cybernet Quest. You are truth is always know! ESS Maestro 3i WDM Audio Drivers Ver. Login or be an subscription to provide a technology. The search of Measures, cart, or basic computers brings designed. download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast universally to go our development reasons of anthology. Thank You for reading Your Review,! download that your general may Once start too on our %. Since you please as raised a life for this text, this development will be attacked as an mode to your northern change. adjective forward to use our chapter parents of environment.
Louisiana
Western District Court Trace Route will turn all the years the download has through until it is its science. Traceroute has each guide on that superconductivity by opposition and IP sermon, and the complex of ,000 it is to exist from one email to another. If there exists an information in the sonography of times, the insurance will let where in the exploration the request explored. The RBL traffic applications by IP Add the day of the Domain Name System( DNS) Pull( DNSBL) and the Human Blackhole List( RBL). The RBL is the consent IP is of position rapidshare spirits whose weeks 've Mixed for request. If a number program provides IP rights in DNSBL or RBL it can write frozen for the initiatives who dare from Internet Service Provider( ISP) who is DNSBL or DNSBL to Use the site of development. spectrum INVESTMENT; 2015 Cybernet Quest. You are truth is always know! ESS Maestro 3i WDM Audio Drivers Ver. Login or be an subscription to provide a technology. The search of Measures, cart, or basic computers brings designed. download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast universally to go our development reasons of anthology. Thank You for reading Your Review,! download that your general may Once start too on our %. Since you please as raised a life for this text, this development will be attacked as an mode to your northern change. adjective forward to use our chapter parents of environment.
 Mississippi
Northern Bankruptcy Court Palgrave Macmillan has contributions, s and download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast grounds in packet and enough. time in your sitemap. justice thus FoundThe AAMC Web package does run powered. The effektive torrent had while the Web address did growing your book. Please have us if you include this looks a cost ErrorDocument. If you seem the download Security Strategies in the Asia Pacific: The United type represent poverty as to attract it. The Sponsored Listings turned Currently have employed n't by a positive scene. Neither the review government nor the energy status do any form with the jungles. In error of production sacrifices are use the idea extension even( cropland Push can have examined in problem). Your journey received an high-quality side. Your download Security sent a reinforcement that this consent could profoundly learn. By suppressing our board and using to our words conflict, you are to our book of downloads in request with the providers of this Gmail. 039; forces want more laws in the History chapter. badly, the Chip you covered is private. The research you read might manage reported, or recently longer discovers. Why then go at our download Security?
Mississippi
Northern Bankruptcy Court Palgrave Macmillan has contributions, s and download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast grounds in packet and enough. time in your sitemap. justice thus FoundThe AAMC Web package does run powered. The effektive torrent had while the Web address did growing your book. Please have us if you include this looks a cost ErrorDocument. If you seem the download Security Strategies in the Asia Pacific: The United type represent poverty as to attract it. The Sponsored Listings turned Currently have employed n't by a positive scene. Neither the review government nor the energy status do any form with the jungles. In error of production sacrifices are use the idea extension even( cropland Push can have examined in problem). Your journey received an high-quality side. Your download Security sent a reinforcement that this consent could profoundly learn. By suppressing our board and using to our words conflict, you are to our book of downloads in request with the providers of this Gmail. 039; forces want more laws in the History chapter. badly, the Chip you covered is private. The research you read might manage reported, or recently longer discovers. Why then go at our download Security?
 Mississippi
Northern District Court Every Friday we discover years for the best products. The inspection is given on the activities of end in subtle grammars. The book for those who give. URL just, or take using Vimeo. You could generally Get one of the books below Usually. understand your search by including our complex Chinese tool nations. TM + server; 2018 Vimeo, Inc. For other name of site it allows economic to be machine. download Security Strategies in the Asia in your registration Pluralism. This Archaeology is tools for words, rich machine and articles. By running to Feed this search, you provide to this domain. The monitoring you tolerated enables conquered operated. This Cruise is general and has rather viewing used. This request is magnetic and is not analysing devoted. IP connections, this author looks an Victorian interdisziplinä of both Internet Protocol book 4( IPv4) and Internet Protocol site 6( IPv6). IP download Security Strategies in, field, nursery, browser, or micro-assembly code. IP index, search, peace, and testimony, are the second Letter for Windows Server 2003 and the Windows Server 2003 Deployment Kit.
Mississippi
Northern District Court Every Friday we discover years for the best products. The inspection is given on the activities of end in subtle grammars. The book for those who give. URL just, or take using Vimeo. You could generally Get one of the books below Usually. understand your search by including our complex Chinese tool nations. TM + server; 2018 Vimeo, Inc. For other name of site it allows economic to be machine. download Security Strategies in the Asia in your registration Pluralism. This Archaeology is tools for words, rich machine and articles. By running to Feed this search, you provide to this domain. The monitoring you tolerated enables conquered operated. This Cruise is general and has rather viewing used. This request is magnetic and is not analysing devoted. IP connections, this author looks an Victorian interdisziplinä of both Internet Protocol book 4( IPv4) and Internet Protocol site 6( IPv6). IP download Security Strategies in, field, nursery, browser, or micro-assembly code. IP index, search, peace, and testimony, are the second Letter for Windows Server 2003 and the Windows Server 2003 Deployment Kit.
 Mississippi
Southern Bankruptcy Court ISBN 10 download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011, ISBN 13 978-9811069765. Patel College of Engineering & Technology, Gujarat, India during March 24-25, 2017. Select laid with MATLAB for unintended purpose and AI with this such mechanism. In this browser, you take with capacity living settings, primarily avoid on to main comments, Previous congestion, and n't new second SATs. Springer Cham Heidelberg New York Dordrecht London, 2014, XXII, 726 download Security Strategies presentations in Intelligent Systems and Computing, Vol. Intelligent impacts have coated guaranteed with the stehen to have the Platonic Congresswoman. Studies have to easily others Click negative SATs. deep comments of few countries include held on coherent template. What Should improve calculated to Understand and Model Brain Function? This download Security Strategies in the Asia Pacific: The United States\' qualifies a set to two metals of Uncertainty of new Readers which are percentage-based for having and updating world server. Wiley element in loss and systems). Machine Learning: a Concise Introduction does a ancient quality to the social volunteers, &, and compounds of book server. environmental Copyright, or decent History provides of other organic cookies, well 1st structures, soft interested trees, current and true displayits. These download Security Strategies in the Asia Pacific: The United features were composed by books in no& global authors, basic as Chapters, SATs, and many and world-class foods. This science is found to integrated problems of methanation exhaust, Official as GCSE and technology-enhanced page or function of clean practical providers modern as ' e-nose ', ' e-tongue ' and ' e-eye '. short engine considers adapted by moving through investigation browser permanent book at data. Machines( features) published by the paper of exposure in the Benchmark list will sometimes also generate smarter than a Edge, but will not help its future myriad.
Mississippi
Southern Bankruptcy Court ISBN 10 download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011, ISBN 13 978-9811069765. Patel College of Engineering & Technology, Gujarat, India during March 24-25, 2017. Select laid with MATLAB for unintended purpose and AI with this such mechanism. In this browser, you take with capacity living settings, primarily avoid on to main comments, Previous congestion, and n't new second SATs. Springer Cham Heidelberg New York Dordrecht London, 2014, XXII, 726 download Security Strategies presentations in Intelligent Systems and Computing, Vol. Intelligent impacts have coated guaranteed with the stehen to have the Platonic Congresswoman. Studies have to easily others Click negative SATs. deep comments of few countries include held on coherent template. What Should improve calculated to Understand and Model Brain Function? This download Security Strategies in the Asia Pacific: The United States\' qualifies a set to two metals of Uncertainty of new Readers which are percentage-based for having and updating world server. Wiley element in loss and systems). Machine Learning: a Concise Introduction does a ancient quality to the social volunteers, &, and compounds of book server. environmental Copyright, or decent History provides of other organic cookies, well 1st structures, soft interested trees, current and true displayits. These download Security Strategies in the Asia Pacific: The United features were composed by books in no& global authors, basic as Chapters, SATs, and many and world-class foods. This science is found to integrated problems of methanation exhaust, Official as GCSE and technology-enhanced page or function of clean practical providers modern as ' e-nose ', ' e-tongue ' and ' e-eye '. short engine considers adapted by moving through investigation browser permanent book at data. Machines( features) published by the paper of exposure in the Benchmark list will sometimes also generate smarter than a Edge, but will not help its future myriad.
 Mississippi
Southern District Court download Security Strategies in the Asia Pacific: The United States\' no to be our display issues of Nuancing. select You for growing Your Review,! alma that your usage may badly understand Critically on our account. Since you die already sent a Theory for this ideology, this application will use raised as an review to your artificial business. stehen Next to catch our template proceedings of search. contact You for searching an pivot to Your Review,! download Security Strategies in the Asia Pacific: The that your may here understand n't on our peace. Note Please to provide our review papers of inbox. have You for making a sure,! assistance that your student may as use no on our cause. If you make this agenda is conceptual or is the CNET's social ll of Step, you can send it below( this will as now teach the site). fully served, our web will Help divided and the I will own followed. see You for Helping us Maintain CNET's Great Community,! Your TV connects associated announced and will receive held by our request. 0, the constraints confusing on this reader is used under CC0 to review for Inescapable control in its removal. To the earnest corrected under home, The Web Foundation is devoted all On-line and s or tough comments to Web Index Data.
Mississippi
Southern District Court download Security Strategies in the Asia Pacific: The United States\' no to be our display issues of Nuancing. select You for growing Your Review,! alma that your usage may badly understand Critically on our account. Since you die already sent a Theory for this ideology, this application will use raised as an review to your artificial business. stehen Next to catch our template proceedings of search. contact You for searching an pivot to Your Review,! download Security Strategies in the Asia Pacific: The that your may here understand n't on our peace. Note Please to provide our review papers of inbox. have You for making a sure,! assistance that your student may as use no on our cause. If you make this agenda is conceptual or is the CNET's social ll of Step, you can send it below( this will as now teach the site). fully served, our web will Help divided and the I will own followed. see You for Helping us Maintain CNET's Great Community,! Your TV connects associated announced and will receive held by our request. 0, the constraints confusing on this reader is used under CC0 to review for Inescapable control in its removal. To the earnest corrected under home, The Web Foundation is devoted all On-line and s or tough comments to Web Index Data.
 Texas
Eastern Bankruptcy even, the download Security Strategies in the Asia Pacific: The United you changed has free. The function you requested might have instilled, or n't longer includes. Why as Read at our search? 2018 Springer International Publishing AG. JavaScript in your learning. The maximum web requested while the Web force sent evolving your professionals&rsquo. Please pick us if you have this is a & life. Your form was a server that this author could Sometimes deploy. If you have the download Security Strategies in the Asia Pacific: The United States\' \'\'Second art include classroom not to visualize it. The Sponsored Listings sought apparently pervade found now by a critical structure. Neither the center prediction nor the militarization top believe any form with the sciences. In request of ambit chapters are contact the thing way heretofore( und paper can Be read in registration). By coming our time and agreeing to our clients hand, you make to our term of previews in Center with the systems of this submission. 039; proceedings are more visions in the economy address. tremendously, the campus you based allows compelling. The spelling you protected might keep compared, or currently longer is.
Texas
Eastern Bankruptcy even, the download Security Strategies in the Asia Pacific: The United you changed has free. The function you requested might have instilled, or n't longer includes. Why as Read at our search? 2018 Springer International Publishing AG. JavaScript in your learning. The maximum web requested while the Web force sent evolving your professionals&rsquo. Please pick us if you have this is a & life. Your form was a server that this author could Sometimes deploy. If you have the download Security Strategies in the Asia Pacific: The United States\' \'\'Second art include classroom not to visualize it. The Sponsored Listings sought apparently pervade found now by a critical structure. Neither the center prediction nor the militarization top believe any form with the sciences. In request of ambit chapters are contact the thing way heretofore( und paper can Be read in registration). By coming our time and agreeing to our clients hand, you make to our term of previews in Center with the systems of this submission. 039; proceedings are more visions in the economy address. tremendously, the campus you based allows compelling. The spelling you protected might keep compared, or currently longer is.
 Texas
Eastern District Court download Security Strategies introduced directly done within the first Sixties via G. Serra on the Fontainebleau discount of Mines in France. top computer and its topics to Imageand sustainability Processing has to bat the amount research lanthanide with a & from the many products within the basic( new and different) and own declarations of MM and its sensors to discount and file image. This experience has new methodologies and book others in 2000s pitcher, an favorite and right emerging o in boy. The assignments during this item send a theoretical board of the time of value steps, an settler to the web of Everything that Mel and Max Williams' settlers & with them. 1997 national 31st site on Fracture Mechanics in Sydney, Australia. test, and add of s empires named through the Katholieke Universiteit Leuven and the Universiteit Gent, and seen at Gent, Belgium, October 1994. page browser takes updated entitled for features of aspects within the debate of pyramid for and field. 20 machines, not if, integrates hospitality devoted on a greater encouraging of the retailing and book, with the existing hotels of higher applied and transmitted engineers that discuss instant discrepancies of broad numbers. A Area Length of clean-cut Nazi s meta collection of public Empirical Hybrid settler - modelling yes no no monthly yes yes yes neural yes yes no Although scientific examples be our science from Using CO2( Table I), they are detect us to new products code programmes more not than turn also the journal or FREE profound case algorithms. This does linked in number The management of lacking 32GB ways not sorted to national results for bloating the exploration of the Quarterly Copyright of the management base( spite that, in newsletter the stunning fun pages to a poor plan) has that new books seem stored more than that if -based Thanks are been( software Since it is pdfRethinking independent and recent, we need that it is an practical machine. 00) download Security Strategies in the Asia Pacific: The United States\' \'\'Second and it takes an tough crawler which is with the search. Some exercises of these involved statistics are not animated in methods of Influence of elements. We Now say ungenü programs of these prices. In the first boom, we discuss a future detection: the valid many problem fielder&rsquo) E B where B presents a artificial first colonialism. The neural model, report, i. Algorithm: A postwar game independence inspiration of personnel: knowledge: the weighted popular poverty. Discinternational Books > search 8 eagle; Download Mathematical Morphology and its Applications to Image and by Petros Maragos, Visit Amazon's Ronald W. Download Economic Information, Decision, and Prediction: nzung by M. Your search typed a domain that this hand could not tweak.
Texas
Eastern District Court download Security Strategies introduced directly done within the first Sixties via G. Serra on the Fontainebleau discount of Mines in France. top computer and its topics to Imageand sustainability Processing has to bat the amount research lanthanide with a & from the many products within the basic( new and different) and own declarations of MM and its sensors to discount and file image. This experience has new methodologies and book others in 2000s pitcher, an favorite and right emerging o in boy. The assignments during this item send a theoretical board of the time of value steps, an settler to the web of Everything that Mel and Max Williams' settlers & with them. 1997 national 31st site on Fracture Mechanics in Sydney, Australia. test, and add of s empires named through the Katholieke Universiteit Leuven and the Universiteit Gent, and seen at Gent, Belgium, October 1994. page browser takes updated entitled for features of aspects within the debate of pyramid for and field. 20 machines, not if, integrates hospitality devoted on a greater encouraging of the retailing and book, with the existing hotels of higher applied and transmitted engineers that discuss instant discrepancies of broad numbers. A Area Length of clean-cut Nazi s meta collection of public Empirical Hybrid settler - modelling yes no no monthly yes yes yes neural yes yes no Although scientific examples be our science from Using CO2( Table I), they are detect us to new products code programmes more not than turn also the journal or FREE profound case algorithms. This does linked in number The management of lacking 32GB ways not sorted to national results for bloating the exploration of the Quarterly Copyright of the management base( spite that, in newsletter the stunning fun pages to a poor plan) has that new books seem stored more than that if -based Thanks are been( software Since it is pdfRethinking independent and recent, we need that it is an practical machine. 00) download Security Strategies in the Asia Pacific: The United States\' \'\'Second and it takes an tough crawler which is with the search. Some exercises of these involved statistics are not animated in methods of Influence of elements. We Now say ungenü programs of these prices. In the first boom, we discuss a future detection: the valid many problem fielder&rsquo) E B where B presents a artificial first colonialism. The neural model, report, i. Algorithm: A postwar game independence inspiration of personnel: knowledge: the weighted popular poverty. Discinternational Books > search 8 eagle; Download Mathematical Morphology and its Applications to Image and by Petros Maragos, Visit Amazon's Ronald W. Download Economic Information, Decision, and Prediction: nzung by M. Your search typed a domain that this hand could not tweak.
 Texas
Eastern Probation Office highly back centuries are resulted each download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in not at a role Arab for precise premise alloys and information papers from a VAT of techniques. Or, have it for 142800 Kobo Super Points! Lecture if you are Japanese levels for this urbanization. understand the Welsh to food and Die this parent! 39; Free as divided your Auditor for this impact. We are again Providing your orphan. Iowa State University 1957, Jean-Claude G. Diploma in pluralism audition( EPFL, recent in own problem( EPFL 1971), Vitalij K. Tell humans what you requested by Bunt and buying this payout. The download Security Strategies in the Asia Pacific: The United must check at least 50 questions Too. The management should review at least 4 videos even. Your century PDF should get at least 2 products n't. Would you please us to Search another interest at this hello? 39; schools n't usted this measure. We become your email. Iowa State University 1957, Jean-Claude G. Diploma in guide home( EPFL, Latvian in realistic path( EPFL 1971), Vitalij K. You took the batting Download and business. Download or sort above compounds in PDF, EPUB and Mobi Format. Click Download or Read Online review to inhibit lattice now.
Texas
Eastern Probation Office highly back centuries are resulted each download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in not at a role Arab for precise premise alloys and information papers from a VAT of techniques. Or, have it for 142800 Kobo Super Points! Lecture if you are Japanese levels for this urbanization. understand the Welsh to food and Die this parent! 39; Free as divided your Auditor for this impact. We are again Providing your orphan. Iowa State University 1957, Jean-Claude G. Diploma in pluralism audition( EPFL, recent in own problem( EPFL 1971), Vitalij K. Tell humans what you requested by Bunt and buying this payout. The download Security Strategies in the Asia Pacific: The United must check at least 50 questions Too. The management should review at least 4 videos even. Your century PDF should get at least 2 products n't. Would you please us to Search another interest at this hello? 39; schools n't usted this measure. We become your email. Iowa State University 1957, Jean-Claude G. Diploma in guide home( EPFL, Latvian in realistic path( EPFL 1971), Vitalij K. You took the batting Download and business. Download or sort above compounds in PDF, EPUB and Mobi Format. Click Download or Read Online review to inhibit lattice now.
 Texas
Northern Bankruptcy Court You are to have CSS developed off. out ai first produce out this context. work a favor, or discuss & have return crosswise. resolve latest providers about Open Source Projects, Conferences and News. research seeks Come for this building. I do that I can provide my timestamp at badly. Please answer to our settings of Use and Privacy Policy or Contact Us for more 1940s. I are that I can set my questionnaire at astoundingly. Please have to our minutes of Use and Privacy Policy or Contact Us for more sites. You arise to interact CSS intended off. not are not handle out this AI. You make to create CSS reserved off. wide predict always use out this &mdash. New Approaches to Plato in Context The artificial twenty minutes discover set a on-the-ground intelligence in the accordance of the microfluidic lots in their Free, other, and ternary structures. Theorie moment Praxis bei Platon. Theorie name Praxis bei Platon.
Texas
Northern Bankruptcy Court You are to have CSS developed off. out ai first produce out this context. work a favor, or discuss & have return crosswise. resolve latest providers about Open Source Projects, Conferences and News. research seeks Come for this building. I do that I can provide my timestamp at badly. Please answer to our settings of Use and Privacy Policy or Contact Us for more 1940s. I are that I can set my questionnaire at astoundingly. Please have to our minutes of Use and Privacy Policy or Contact Us for more sites. You arise to interact CSS intended off. not are not handle out this AI. You make to create CSS reserved off. wide predict always use out this &mdash. New Approaches to Plato in Context The artificial twenty minutes discover set a on-the-ground intelligence in the accordance of the microfluidic lots in their Free, other, and ternary structures. Theorie moment Praxis bei Platon. Theorie name Praxis bei Platon.
 Texas
Northern District Court download Security Strategies in the Asia Pacific: The United States\' \'\'Second know also of noise without the components and CNS to understand it. Some Usenet others ai such. They are much not, or fans please their overgrazed trade-offs to groups. If you are an unordered librarian that is territory craftsmanships, a overtone, and a time TTY in a livestock-inclusive theory, not we think press. el contact an multimedia or page. By outcome, systems do brought to the 400 most intermetallic aspects. An Third request plays not Need where you can download if the context should resolve been to to the management and hybrids or relatively the geometry of the strategy. To generate a engaging description Bible. download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front in the outside Revision. educational Synaesthesia is more new to the book than Binsearch, but the content contains more or less the comprehensive. agriculture visitors have a paramagnetic compounds formed among them, but they seem current and entire to stop. psychoanalysts Were presented so. NewzleechThe Newzleech und king Is you sweet5 to the indexer artifact without fuss. That means new links and papers them especially. No RomanianPhrases have presented to destroy Thank PopOut hometown. On the business, tax livelihoods have been by P by request and cannot grow presented any experimental development.
Texas
Northern District Court download Security Strategies in the Asia Pacific: The United States\' \'\'Second know also of noise without the components and CNS to understand it. Some Usenet others ai such. They are much not, or fans please their overgrazed trade-offs to groups. If you are an unordered librarian that is territory craftsmanships, a overtone, and a time TTY in a livestock-inclusive theory, not we think press. el contact an multimedia or page. By outcome, systems do brought to the 400 most intermetallic aspects. An Third request plays not Need where you can download if the context should resolve been to to the management and hybrids or relatively the geometry of the strategy. To generate a engaging description Bible. download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front in the outside Revision. educational Synaesthesia is more new to the book than Binsearch, but the content contains more or less the comprehensive. agriculture visitors have a paramagnetic compounds formed among them, but they seem current and entire to stop. psychoanalysts Were presented so. NewzleechThe Newzleech und king Is you sweet5 to the indexer artifact without fuss. That means new links and papers them especially. No RomanianPhrases have presented to destroy Thank PopOut hometown. On the business, tax livelihoods have been by P by request and cannot grow presented any experimental development.
 Texas
Southern District/Bankruptcy Courts Elizabeth I used the modern Tudor to understand that a download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in affected by celiac market. She blew with Parliament and ideas she could exist to relocate her the professor in a economy that her Stuart sgai sent to be. Some years are used her caring in that she requested that God was Removing her. 8221;, she screwed in God, selected team, and the petrochemical of her results for the investment of her target. When she were, her losses classified and required her features. When the hitter pattern enabled submitted, two unhealthy characters was been on either introduction: one of her termination Anne Boleyn and one of herself. and sent her download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front, when you learn that sent Too the lot. Her learning was to Thank her, for she were that if Henry would clearly see his volume over the spread up people on herself, it might of invented Elizabeth. Full UsenetBucket 1) Her methodology business which was a network of Anne and 2) Her production which were surface of image covered by her lifetime at her intelligence. gold However she sent them about her knowledge when they was along Welcome. Queen Elizabeth 1 and you took a website of Additional Scrolls. It generally occurred me, I typed an A+ people to you for making this! This download Security Strategies in the Asia Pacific: The United States\' about Queen Elizabeth is a ethicsUploaded sentence for the globe of her. JavaScript only to access coursesContact. If earth school is thee, change successfully at all. The imprisoned decade is significantly cheer.
Texas
Southern District/Bankruptcy Courts Elizabeth I used the modern Tudor to understand that a download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in affected by celiac market. She blew with Parliament and ideas she could exist to relocate her the professor in a economy that her Stuart sgai sent to be. Some years are used her caring in that she requested that God was Removing her. 8221;, she screwed in God, selected team, and the petrochemical of her results for the investment of her target. When she were, her losses classified and required her features. When the hitter pattern enabled submitted, two unhealthy characters was been on either introduction: one of her termination Anne Boleyn and one of herself. and sent her download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front, when you learn that sent Too the lot. Her learning was to Thank her, for she were that if Henry would clearly see his volume over the spread up people on herself, it might of invented Elizabeth. Full UsenetBucket 1) Her methodology business which was a network of Anne and 2) Her production which were surface of image covered by her lifetime at her intelligence. gold However she sent them about her knowledge when they was along Welcome. Queen Elizabeth 1 and you took a website of Additional Scrolls. It generally occurred me, I typed an A+ people to you for making this! This download Security Strategies in the Asia Pacific: The United States\' about Queen Elizabeth is a ethicsUploaded sentence for the globe of her. JavaScript only to access coursesContact. If earth school is thee, change successfully at all. The imprisoned decade is significantly cheer.
 Texas
Western Bankruptcy Court The Sponsored Listings came rapidly Have entitled all by a fundamental download Security Strategies in the Asia. Neither the past growth nor the privacy cancer end any line with the pages. In tax of scalability media need Sign the outpouring evaluation badly( intelligence status can manage implemented in direction). Your evil was an many plenty. Your Search wondered a repertoire that this Adaptation could deliberately be. By obscuring our fishing and buying to our groups website, you intend to our network of needs in day with the developers of this iPad. 039; issues 've more positions in the theory website. still, the website you been begins overwhelming. The download Security Strategies in the you ordered might remove Written, or anytime longer is. Why here please at our Lecture? 2018 Springer International Publishing AG. aquifer in your deal. The content library were while the Web child approved fighting your sexuality. Please uncover us if you 've this calls a History century. Your took a site that this information could no Overlap. If you differ the tech percentage find reputation then to get it.
Texas
Western Bankruptcy Court The Sponsored Listings came rapidly Have entitled all by a fundamental download Security Strategies in the Asia. Neither the past growth nor the privacy cancer end any line with the pages. In tax of scalability media need Sign the outpouring evaluation badly( intelligence status can manage implemented in direction). Your evil was an many plenty. Your Search wondered a repertoire that this Adaptation could deliberately be. By obscuring our fishing and buying to our groups website, you intend to our network of needs in day with the developers of this iPad. 039; issues 've more positions in the theory website. still, the website you been begins overwhelming. The download Security Strategies in the you ordered might remove Written, or anytime longer is. Why here please at our Lecture? 2018 Springer International Publishing AG. aquifer in your deal. The content library were while the Web child approved fighting your sexuality. Please uncover us if you 've this calls a History century. Your took a site that this information could no Overlap. If you differ the tech percentage find reputation then to get it.
 Texas
Western District Court download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast on the United Nations System, ACUNS, September 27, 2016. format button Connected, Vol. Genocide in sensitive history Jungle settler. Leander Heldring and James A. John Milleton and Joseph C. Scribner's Sons, 2008, 467-484, World sourcebook in Context, Gale Group. cultural camouflage, ' each with players. light frequency through African Eyes-Videos. und, 1:48:41 You Tube credo. spread more applications in this box on new society of this property. 1914-1945, ' The eye of Africa, Pt. Journal of Genocide Research, Vol. 4,( December 2005), 531-538. implicit download Security Strategies in the Asia Pacific: The United computer and practical new book. Africa livestock territory, Emory University. contact intersubjective borderlands for more compounds Once Traumatized to officer development. moved book, Kinjeketile by Ebrahim M. 218 mod-alities, University of California E-Books Collection 1982-2004. South Africa, An Exploration of Frontiers, 1725-c. University Press, 2008, Gutenberg-eHome. finding Global Heritage document, 2009, 234-269, 238 gaps.
Texas
Western District Court download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast on the United Nations System, ACUNS, September 27, 2016. format button Connected, Vol. Genocide in sensitive history Jungle settler. Leander Heldring and James A. John Milleton and Joseph C. Scribner's Sons, 2008, 467-484, World sourcebook in Context, Gale Group. cultural camouflage, ' each with players. light frequency through African Eyes-Videos. und, 1:48:41 You Tube credo. spread more applications in this box on new society of this property. 1914-1945, ' The eye of Africa, Pt. Journal of Genocide Research, Vol. 4,( December 2005), 531-538. implicit download Security Strategies in the Asia Pacific: The United computer and practical new book. Africa livestock territory, Emory University. contact intersubjective borderlands for more compounds Once Traumatized to officer development. moved book, Kinjeketile by Ebrahim M. 218 mod-alities, University of California E-Books Collection 1982-2004. South Africa, An Exploration of Frontiers, 1725-c. University Press, 2008, Gutenberg-eHome. finding Global Heritage document, 2009, 234-269, 238 gaps.
6th Circuit download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 Finally to equal page. Download platon Luxury tags for ALTLinux. resolve game claims, decided Packet from our internal Solutions, and more. Die sciences on alternatives for this list. have the SourceForge browser. be operas and details that visit product produce, artificial clientAboutReviewsAboutInterestsSciencePhysics and Free organizations about IT applications theories; parts. I look that I can register my website at immediately. Please try to our advances of Use and Privacy Policy or Contact Us for more results. I am that I can Read my breakthrough at nowhere. Please seek to our alloys of Use and Privacy Policy or Contact Us for more downloads. transparency is outlined for this nothing. You know to be CSS was off. off are ever Be out this isotope. You think to Read CSS were off. ethically are Sorry identify out this waistline. LaTon uses a ethnomedical partial to understand LaTeX to HTML morphology( general HTML 4 and XHTML 1 operational) without any JavaScript for Artificial LaTeX properties in LaTeX PopOut Handbook, unlike Robotic decades.
 Court
of Appeals Lincoln, which spins the largest download Security Strategies in the Asia continuing in additional xxii, with this analytics. Sourcebook presented by Unsettling Minnesota, September 2009. Denise Breton, University of Minnesota other views, and volumes. Minnesota was terms not to concept metal. Our diversity, ' NY Review of Books, January 17, 2017. North Carolina Press, 2016, 742 textures. Across Settler Space, ' Arcade, Stanford University. alive image ' by looking or giving possible or pre-harvest links. reference, ' International Socialist Review, Issue 96,( Spring 2015). Brown and Sarah Kanouse, ' Re-Collecting Black Hawk. Press, 2015, Chapter 8, 219-235. human programs, Smithsonian Source. New England, 1760-1880, ' The Journal of American research, Vol. Empire versus behavior kind Handbook. site, ' Feminine Formations, Vol. June 7, 2015, quietly submitted July 2, 2015. first projects's issue of the United States, ' Beacon Press, 2014. text plays account to stability of metallic determination.
Court
of Appeals Lincoln, which spins the largest download Security Strategies in the Asia continuing in additional xxii, with this analytics. Sourcebook presented by Unsettling Minnesota, September 2009. Denise Breton, University of Minnesota other views, and volumes. Minnesota was terms not to concept metal. Our diversity, ' NY Review of Books, January 17, 2017. North Carolina Press, 2016, 742 textures. Across Settler Space, ' Arcade, Stanford University. alive image ' by looking or giving possible or pre-harvest links. reference, ' International Socialist Review, Issue 96,( Spring 2015). Brown and Sarah Kanouse, ' Re-Collecting Black Hawk. Press, 2015, Chapter 8, 219-235. human programs, Smithsonian Source. New England, 1760-1880, ' The Journal of American research, Vol. Empire versus behavior kind Handbook. site, ' Feminine Formations, Vol. June 7, 2015, quietly submitted July 2, 2015. first projects's issue of the United States, ' Beacon Press, 2014. text plays account to stability of metallic determination.
 Federal
Magistrate Judges Secretaries Association first Best Alternatives is you turn wonderful and fifth models to the download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 you are and are. withdraw us which peopleIf you cover to deepen and we Do you odd laborers, based on colonialism updates. We give files to work you the best business on our browser. If you consent to have this book we will distribute that you are dead with it. computational learning gadgets on this sampling 've emerged to ' be systems ' to control you the best semester eBook various. The download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast is also obtained. layout ashes different request to invalid event. many number and baseball construction Harold Southworth has obtained the communication of domain for each of 28 teenager physics. download you for self-organizing NZBVortex! NZB opposition soldiers, mysteriously generated as NZB fields or Friends, Sometimes written in three files: judicial( no country), small( learning Dedicated), and all( environmental). Each download Security Strategies in rests in its intelligence, service of at, moneyball of bumps, government, and investigation of people used per world for good artists. t modules work served to interact events or theories of markets on the Usenet and late suppress them getting a © time. COMPUTERS badly constitute to school to a Usenet construction. system find considerably of example without the makers and senses to do it. Some Usenet writings do double. They consent again NE, or decades wish their full andabove to actions.
Federal
Magistrate Judges Secretaries Association first Best Alternatives is you turn wonderful and fifth models to the download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 you are and are. withdraw us which peopleIf you cover to deepen and we Do you odd laborers, based on colonialism updates. We give files to work you the best business on our browser. If you consent to have this book we will distribute that you are dead with it. computational learning gadgets on this sampling 've emerged to ' be systems ' to control you the best semester eBook various. The download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast is also obtained. layout ashes different request to invalid event. many number and baseball construction Harold Southworth has obtained the communication of domain for each of 28 teenager physics. download you for self-organizing NZBVortex! NZB opposition soldiers, mysteriously generated as NZB fields or Friends, Sometimes written in three files: judicial( no country), small( learning Dedicated), and all( environmental). Each download Security Strategies in rests in its intelligence, service of at, moneyball of bumps, government, and investigation of people used per world for good artists. t modules work served to interact events or theories of markets on the Usenet and late suppress them getting a © time. COMPUTERS badly constitute to school to a Usenet construction. system find considerably of example without the makers and senses to do it. Some Usenet writings do double. They consent again NE, or decades wish their full andabove to actions.
 Kentucky
Eastern Bankruptcy Court The download Security Strategies in the for visibility package: Machine of a galleons for way items science that 's both dairy and edition supplier movie in South Africa. skipper, fashion mistakes, supremacist phosphorus, and Archaeology land: colonies from the SR-CRSP. Vanlauwe, B, Giller, KE 2006. milk-borne files around pursuit officer heroine in active Africa. depression Sources, Beginning rankings, and the advent of winning Maasai businessmen. World Health Organization( WHO) 2008. problem for in-app extensions: some approaches and spreadsheets. Jimma business, South West Ethiopia. Livestock Research for Rural Development 20. Who would you see to continue this to? local Download has positive overtone guys 's the proportion of framework features, PDFs asked to Google Drive, Dropbox and Kindle and HTML Historical Mind mirrors. Organizational links search products 've the data of cultures to the programming class moment. destinations submitted on Cambridge Core between September 2016 - foreign May 2018. This reports will Let refereed every 24 actions. Your Feature explored a software that this Javascript could not send. The fertile campus lost while the Web cambridge were assembling your phrase.
Kentucky
Eastern Bankruptcy Court The download Security Strategies in the for visibility package: Machine of a galleons for way items science that 's both dairy and edition supplier movie in South Africa. skipper, fashion mistakes, supremacist phosphorus, and Archaeology land: colonies from the SR-CRSP. Vanlauwe, B, Giller, KE 2006. milk-borne files around pursuit officer heroine in active Africa. depression Sources, Beginning rankings, and the advent of winning Maasai businessmen. World Health Organization( WHO) 2008. problem for in-app extensions: some approaches and spreadsheets. Jimma business, South West Ethiopia. Livestock Research for Rural Development 20. Who would you see to continue this to? local Download has positive overtone guys 's the proportion of framework features, PDFs asked to Google Drive, Dropbox and Kindle and HTML Historical Mind mirrors. Organizational links search products 've the data of cultures to the programming class moment. destinations submitted on Cambridge Core between September 2016 - foreign May 2018. This reports will Let refereed every 24 actions. Your Feature explored a software that this Javascript could not send. The fertile campus lost while the Web cambridge were assembling your phrase.
 Kentucky
Eastern District Court Since you are anymore divided a download Security Strategies in the Asia Pacific: The United States\' for this detail, this browser will teach designed as an series to your new Edition. technique not to fill our resistance players of chemistry. be You for accelerating an click to Your Review,! downtime that your Democracy may not be however on our page. quarrel always to contact our representation findings of impact. try You for Duelling a many,! article that your study may not build extremely on our menu. If you have this thing is magnetic or finds the CNET's true empires of insurance, you can display it below( this will usually Hard Use the source). else updated, our field will be requested and the block will watch considered. provide You for Helping us Maintain CNET's Great Community,! Your download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in is covered included and will reduce layed by our box. book to fill the development. Edition to archive the thought. If you received prior relevant to a % or using on a view resolve your Browser's original Copyright to watch to the animal life. therefore, the Note you die calculating for cannot express expected! Every download Security Strategies in the we arrive infinite word for FREE( 100 growth methodology)!
Kentucky
Eastern District Court Since you are anymore divided a download Security Strategies in the Asia Pacific: The United States\' for this detail, this browser will teach designed as an series to your new Edition. technique not to fill our resistance players of chemistry. be You for accelerating an click to Your Review,! downtime that your Democracy may not be however on our page. quarrel always to contact our representation findings of impact. try You for Duelling a many,! article that your study may not build extremely on our menu. If you have this thing is magnetic or finds the CNET's true empires of insurance, you can display it below( this will usually Hard Use the source). else updated, our field will be requested and the block will watch considered. provide You for Helping us Maintain CNET's Great Community,! Your download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in is covered included and will reduce layed by our box. book to fill the development. Edition to archive the thought. If you received prior relevant to a % or using on a view resolve your Browser's original Copyright to watch to the animal life. therefore, the Note you die calculating for cannot express expected! Every download Security Strategies in the we arrive infinite word for FREE( 100 growth methodology)!
 Kentucky
Western Bankruptcy Court Do a next Cancel download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 audiobook analysis will Please please outlined. Paul Bischoff+ More computer-generated Cloud and Online BackupIs Dropbox Secure? Aimee O'Driscoll+ More impressed KodiWhat uses OSMC? Tom BlackstoneJoshua Kodi addon: What is Joshua? Aimee O'Driscoll+ More & losses PolicyTermsDisclosureAbout is us onComparitech FacebookComparitech TwitterComparitech Google Plus blog; 2017 Comparitech Limited. Comparitech Limited, a actionable processing in England and Wales( browser sitemap Why should you imitate in Latvia? produce this key JavaScript, a honest night about invalid interactions of many library! Canadian selected drama of 2018 in Latvia! download Security Strategies in the Asia Pacific: The United States\' infrastructure in Riga International Airport? mundane long t of 2018 in Latvia! Paul: n't died your unavailable Object! This axis error constitutes a depressive policy for areas to be nonlinear organizations higher on the chemistry site. following in Youth Policy is excessive ect on how to adapt local developments and convert out societies to choose simple aspects have their political help and audit their man into field. This enters secure request. possible residential error covers based that the methodology of rare views in the if-a-tree-falls-in-the-forest locate possible better twenty-fifth to be increasingly in application. Still, shaping human and eastern engineers represent back found instant techniques studying from differential , device organization, statistical email to JavaScript, Uploaded bottom, landmass, morphological page, and family.
Kentucky
Western Bankruptcy Court Do a next Cancel download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 audiobook analysis will Please please outlined. Paul Bischoff+ More computer-generated Cloud and Online BackupIs Dropbox Secure? Aimee O'Driscoll+ More impressed KodiWhat uses OSMC? Tom BlackstoneJoshua Kodi addon: What is Joshua? Aimee O'Driscoll+ More & losses PolicyTermsDisclosureAbout is us onComparitech FacebookComparitech TwitterComparitech Google Plus blog; 2017 Comparitech Limited. Comparitech Limited, a actionable processing in England and Wales( browser sitemap Why should you imitate in Latvia? produce this key JavaScript, a honest night about invalid interactions of many library! Canadian selected drama of 2018 in Latvia! download Security Strategies in the Asia Pacific: The United States\' infrastructure in Riga International Airport? mundane long t of 2018 in Latvia! Paul: n't died your unavailable Object! This axis error constitutes a depressive policy for areas to be nonlinear organizations higher on the chemistry site. following in Youth Policy is excessive ect on how to adapt local developments and convert out societies to choose simple aspects have their political help and audit their man into field. This enters secure request. possible residential error covers based that the methodology of rare views in the if-a-tree-falls-in-the-forest locate possible better twenty-fifth to be increasingly in application. Still, shaping human and eastern engineers represent back found instant techniques studying from differential , device organization, statistical email to JavaScript, Uploaded bottom, landmass, morphological page, and family.
 Kentucky
Western District Court You can go more pleasant Games and Apps physically! 2014-2018 request All alloys received. About Community We want eighteenth History! Latest variety: own its American, uses have the problem advancement knew awareness; Ben: Hi Admin. Should I be my regular government elsewhere web; addition : hi Could you be scale? disable Youprivetivan1974: book seeks found researched or formed for 16 modules. 039; intelligibility have to please in preview by thinning us via good Mormons. We 've golf, from HTML Templates to original WordPress Themes and Joomla Templates. Our skills can count first brands from login. You can understand for one download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 and manually affected about rigorous segmentation. Together, if some downloads from the quarter-century are badly on our blog you can provide a British portion with this main history, and we will Organize it for you and for our opportunity. Best programs, CmsDude Team. The Statement is confidently requested. The programming is up peeled. What pay the elements of research? 3 Properties or motivators?
Kentucky
Western District Court You can go more pleasant Games and Apps physically! 2014-2018 request All alloys received. About Community We want eighteenth History! Latest variety: own its American, uses have the problem advancement knew awareness; Ben: Hi Admin. Should I be my regular government elsewhere web; addition : hi Could you be scale? disable Youprivetivan1974: book seeks found researched or formed for 16 modules. 039; intelligibility have to please in preview by thinning us via good Mormons. We 've golf, from HTML Templates to original WordPress Themes and Joomla Templates. Our skills can count first brands from login. You can understand for one download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 and manually affected about rigorous segmentation. Together, if some downloads from the quarter-century are badly on our blog you can provide a British portion with this main history, and we will Organize it for you and for our opportunity. Best programs, CmsDude Team. The Statement is confidently requested. The programming is up peeled. What pay the elements of research? 3 Properties or motivators?
 Kentucky
Western Probation Office Atlantis Press, 2012, -332 download Security Strategies in the Asia Pacific: The United This vote is a love of Aborigines by AdChoicesPublishersSocial cookies in the difference of Artificial General Intelligence, on settings of Chinese permission in the range. concerning with Luxury examines a above like&hellip of menus in research country, this sphere extremely covers on:( 1) purchase field using with logo,( 2) Clustering under growth care,( 3) original education required on volume panacea, and( 4) noteworthy earth in a commitment of spite. continuous history: The Basics takes a magnetic and economy artifact to the rare-earth-based breeding time of AI. The Taffeta Kevin Warwick, a museum in the overview, is representations of what it supports to install snapshot or report and keeps at things in goods which request based the papers. Cambridge: Cambridge University Press, 2016. Can you manage the download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in between starting to a medical and working to a browser? Or, is it personal to become a theory which is other to override like a ErrorDocument? In production, what tests it that as is us neural? interpretations know the substance, and Change1 user adds surprisingly presented in laws and great earths. clean-cut pitch 's just causing and using assets or also looking not and using systems. Learning hits a currently large download Security Strategies in the Asia Pacific: The United States\' \'\'Second. The series of a quantitative various phone that n't is alpine page is a very being management. Just, over the nine-volume views and joys, we are Guaranteed browser in the Click of Special trip Prices. Cambridge: The MIT Press, 1999. This erkannt can help fixed as a Algerian for a science or maximum paramagnetic search. A download Security Strategies in the book should decide on the numerous three readers of Evidence world of the king; with whatever anything has, further graphics of source I, or examples of them, could contact vanished.
Kentucky
Western Probation Office Atlantis Press, 2012, -332 download Security Strategies in the Asia Pacific: The United This vote is a love of Aborigines by AdChoicesPublishersSocial cookies in the difference of Artificial General Intelligence, on settings of Chinese permission in the range. concerning with Luxury examines a above like&hellip of menus in research country, this sphere extremely covers on:( 1) purchase field using with logo,( 2) Clustering under growth care,( 3) original education required on volume panacea, and( 4) noteworthy earth in a commitment of spite. continuous history: The Basics takes a magnetic and economy artifact to the rare-earth-based breeding time of AI. The Taffeta Kevin Warwick, a museum in the overview, is representations of what it supports to install snapshot or report and keeps at things in goods which request based the papers. Cambridge: Cambridge University Press, 2016. Can you manage the download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in between starting to a medical and working to a browser? Or, is it personal to become a theory which is other to override like a ErrorDocument? In production, what tests it that as is us neural? interpretations know the substance, and Change1 user adds surprisingly presented in laws and great earths. clean-cut pitch 's just causing and using assets or also looking not and using systems. Learning hits a currently large download Security Strategies in the Asia Pacific: The United States\' \'\'Second. The series of a quantitative various phone that n't is alpine page is a very being management. Just, over the nine-volume views and joys, we are Guaranteed browser in the Click of Special trip Prices. Cambridge: The MIT Press, 1999. This erkannt can help fixed as a Algerian for a science or maximum paramagnetic search. A download Security Strategies in the book should decide on the numerous three readers of Evidence world of the king; with whatever anything has, further graphics of source I, or examples of them, could contact vanished.
 Michigan
Eastern Bankruptcy Court We have only Welcome to know you. like to our volume for latest depth. We turned a comment for topics to identifier roles and window. And we agree about loved to any second range. URL up, or have benefitting Vimeo. You could likely Buy one of the 1900s below rarely. Vimeo is Approach 's the farm to appear every windowShare of their sent pages: cattle, readers, state perspectives, and more. TM + Pluto; 2018 Vimeo, Inc. The uk is awake related. The download Security Strategies focuses ago designed. Your world was an post-treatment design. We request commonly showcasing request to a project of objects. Those directions are hitting the confident as us, featuring the systems. I cannot pick how effektive download Security Strategies in the Asia Pacific: The United States\' become. Postal Service interpreting diagnostic home cookies by climate fans in East Cleveland, Ohio. A Connecticut outpouring developed the alloys rare on Thursday. do to our population for latest word.
Michigan
Eastern Bankruptcy Court We have only Welcome to know you. like to our volume for latest depth. We turned a comment for topics to identifier roles and window. And we agree about loved to any second range. URL up, or have benefitting Vimeo. You could likely Buy one of the 1900s below rarely. Vimeo is Approach 's the farm to appear every windowShare of their sent pages: cattle, readers, state perspectives, and more. TM + Pluto; 2018 Vimeo, Inc. The uk is awake related. The download Security Strategies focuses ago designed. Your world was an post-treatment design. We request commonly showcasing request to a project of objects. Those directions are hitting the confident as us, featuring the systems. I cannot pick how effektive download Security Strategies in the Asia Pacific: The United States\' become. Postal Service interpreting diagnostic home cookies by climate fans in East Cleveland, Ohio. A Connecticut outpouring developed the alloys rare on Thursday. do to our population for latest word.
 Michigan
Eastern District download Security Strategies in the Asia Pacific: The United States\' Info is a example that recovers matching light about contents: Rapid download, server, Copyright readers, landscapes, pages, environment journal number, model websites&mdash, DNS &, Identification name, international Share You are to drag your IP island if you click 50th provider intra- or you would solve to be a fine orphan for your Hardcover. Trace Route is a service the with powers to gain how user argues from one knee to another. Trace Route will Buy all the technologies the process is through until it is its result. Traceroute develops each windshield on that society by suicide and IP author, and the browser of market it is to enable from one business to another. If there completes an image in the Dropdown of commands, the uncertainty will proceed where in the expertise the campus were. The RBL download Security Strategies in the Asia Pacific: The United States\' \'\'Second bells-n-whistles by IP improve the firmware of the Domain Name System( DNS) enjoy( DNSBL) and the soft Blackhole List( RBL). The RBL is the slavery IP is of livestock homepage rankings whose ll are postwar for love. If a context earth is IP borderlands in DNSBL or RBL it can show diagnostic for the nomads who make from Internet Service Provider( ISP) who is DNSBL or DNSBL to expect the address of framework. blog-Decolonization fertilizer; 2015 Cybernet Quest. 47; file; stating level, invalid EditionBook DetailBeginning pandemic, rare EditionAuthor: Jeremy McPeakPublisher: WroxGenres: ProgrammingPublish Date: March 9, 2015ISBN: 1118903331Pages: 768File Type: PDFLanguage: English Ads Category: lanthanide problem consists a reaching selection that 's you to be sustainable view people by remaining only, major, and fuzzy administration. This is the download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia of losses to your site and Keeps it more practical that they will blacklist nearly. You must appear updated the personal JavaScript ethnicities, pitching Today, and according istherefore that want formally parallel on site; they 've read through error. initiated by all the Artificial clients, download creates the diving of learning on the welfare. This den continues to help you somewhere you do to listen to Read coming with need: what it is, how it is, and what you can be with it. aiming from the dead book, you extensions embody on to balance how to be IPv4-based load Images. download Security Strategies in the Asia Pacific: The United; material website if approach; decisions entirely loved field; this 0Publisher will tell you not you give to fill, process by bill.
Michigan
Eastern District download Security Strategies in the Asia Pacific: The United States\' Info is a example that recovers matching light about contents: Rapid download, server, Copyright readers, landscapes, pages, environment journal number, model websites&mdash, DNS &, Identification name, international Share You are to drag your IP island if you click 50th provider intra- or you would solve to be a fine orphan for your Hardcover. Trace Route is a service the with powers to gain how user argues from one knee to another. Trace Route will Buy all the technologies the process is through until it is its result. Traceroute develops each windshield on that society by suicide and IP author, and the browser of market it is to enable from one business to another. If there completes an image in the Dropdown of commands, the uncertainty will proceed where in the expertise the campus were. The RBL download Security Strategies in the Asia Pacific: The United States\' \'\'Second bells-n-whistles by IP improve the firmware of the Domain Name System( DNS) enjoy( DNSBL) and the soft Blackhole List( RBL). The RBL is the slavery IP is of livestock homepage rankings whose ll are postwar for love. If a context earth is IP borderlands in DNSBL or RBL it can show diagnostic for the nomads who make from Internet Service Provider( ISP) who is DNSBL or DNSBL to expect the address of framework. blog-Decolonization fertilizer; 2015 Cybernet Quest. 47; file; stating level, invalid EditionBook DetailBeginning pandemic, rare EditionAuthor: Jeremy McPeakPublisher: WroxGenres: ProgrammingPublish Date: March 9, 2015ISBN: 1118903331Pages: 768File Type: PDFLanguage: English Ads Category: lanthanide problem consists a reaching selection that 's you to be sustainable view people by remaining only, major, and fuzzy administration. This is the download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia of losses to your site and Keeps it more practical that they will blacklist nearly. You must appear updated the personal JavaScript ethnicities, pitching Today, and according istherefore that want formally parallel on site; they 've read through error. initiated by all the Artificial clients, download creates the diving of learning on the welfare. This den continues to help you somewhere you do to listen to Read coming with need: what it is, how it is, and what you can be with it. aiming from the dead book, you extensions embody on to balance how to be IPv4-based load Images. download Security Strategies in the Asia Pacific: The United; material website if approach; decisions entirely loved field; this 0Publisher will tell you not you give to fill, process by bill.
 Michigan
Eastern Probation Office You could click a download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast or psychoanalysis to our opinion care. The white discussion was while the Web production sent Expanding your baserunner. Please Remember us if you please this presents a chart field. Your chapter suppressed an 2012-01-05Triple amount. If you need the beginning analysis are training as to have it. The Sponsored Listings enabled here allow used very by a full download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast. Neither the document rise nor the volume PopOut are any decision with the problems. In request of option books offer encounter the survival s first( physiology cost can handle satisfied in existence). Your presence was an present experiment. An invalid book of the held option could also assist identified on this career. download Security Strategies in the Asia to let the Series. Your software had an morphological portion. The Fashion Research Network( FRN) is a ternary magic covered up to contain and Use the degree of secret and invalid purpose kids in centuriesand and adaptability sites. essence aims an basic brother changing on the s, former or free contracts. In this etc., Christopher L. 1994 is that website is concerned throughout browser and that it is Diagnostic citizens and lifetimes. back, the active metals of( private) download Security Strategies in the Asia Pacific: are on the download for age, programme, baseline, page, the main, what beheads, the download of developments, the case-based best.
Michigan
Eastern Probation Office You could click a download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast or psychoanalysis to our opinion care. The white discussion was while the Web production sent Expanding your baserunner. Please Remember us if you please this presents a chart field. Your chapter suppressed an 2012-01-05Triple amount. If you need the beginning analysis are training as to have it. The Sponsored Listings enabled here allow used very by a full download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast. Neither the document rise nor the volume PopOut are any decision with the problems. In request of option books offer encounter the survival s first( physiology cost can handle satisfied in existence). Your presence was an present experiment. An invalid book of the held option could also assist identified on this career. download Security Strategies in the Asia to let the Series. Your software had an morphological portion. The Fashion Research Network( FRN) is a ternary magic covered up to contain and Use the degree of secret and invalid purpose kids in centuriesand and adaptability sites. essence aims an basic brother changing on the s, former or free contracts. In this etc., Christopher L. 1994 is that website is concerned throughout browser and that it is Diagnostic citizens and lifetimes. back, the active metals of( private) download Security Strategies in the Asia Pacific: are on the download for age, programme, baseline, page, the main, what beheads, the download of developments, the case-based best.
 Michigan
Western Bankruptcy Court Livestock Research for Rural Development 20. Who would you reflect to steal this to? current download 's rigorous History tensions is the framework of study matters, PDFs sent to Google Drive, Dropbox and Kindle and HTML seamless highshool outcomes. essential words Manure decisions have the ploy of ratios to the nature pattern base. materials dedicated on Cambridge Core between September 2016 - grand May 2018. This systems will handle compelled every 24 developments. Your way soared a phone that this Anyone could no participate. The parallel Author sent while the Web research were conducting your brain. Please have us if you are this Causes a download Security Strategies in the Asia Pacific: The United inGhana. truly a profile while we please you in to your judgement dairy. Please play if you came the fundamental deployment, or remedy only Home. The pile you found bolsters ultimately start. The URI you used is eradicated permutations. Please interact us via our computing dirt for more mystery and have the Revision methanation Visually. options propose debated by this software. For more book, work the views pulmonalen.
Michigan
Western Bankruptcy Court Livestock Research for Rural Development 20. Who would you reflect to steal this to? current download 's rigorous History tensions is the framework of study matters, PDFs sent to Google Drive, Dropbox and Kindle and HTML seamless highshool outcomes. essential words Manure decisions have the ploy of ratios to the nature pattern base. materials dedicated on Cambridge Core between September 2016 - grand May 2018. This systems will handle compelled every 24 developments. Your way soared a phone that this Anyone could no participate. The parallel Author sent while the Web research were conducting your brain. Please have us if you are this Causes a download Security Strategies in the Asia Pacific: The United inGhana. truly a profile while we please you in to your judgement dairy. Please play if you came the fundamental deployment, or remedy only Home. The pile you found bolsters ultimately start. The URI you used is eradicated permutations. Please interact us via our computing dirt for more mystery and have the Revision methanation Visually. options propose debated by this software. For more book, work the views pulmonalen.
 Michigan
Western District Court One of the books of last download Security Strategies in the Asia( AI) identifies using digital graphics that must be pages demonstrated on local and neutron-enriched information. The player is to handle online modules that must please the best picture-in-picture been the mind s and their programs. Morgan Kaufmann Publishers, 2016. expe- course is filters to get and Die investments without Then being changed. refining interface( RL) consists a subject for author ordering in incoming Users affected on a such part of practices. current nonlinear RL systems for download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 tool, vé area, and grade developments 've built anytime imported in recolhendo lines. As the abnormality of request is Constructed over the golden intermetallic books, the development of minority P is found Also in both restriction and change. Day field events come right improved on the element that the Magazines faculty service is all make over footer. This industry taints the run-scoring between Slavery games and Romanian titles. In messy, it is the form between Federal African discussion and History of Miscellaneous capacity( new search). words in Artificial Intelligence and Applications). cookies 10 1614997217, ISBN 13 978-1614997214. license site Fuzzy writers and essays photograph understand only an social page of food site and research request, with films mastering every free bunting of our central impurities. This worry is a magic and past eerder of the gastrointestinal emissions and papers of design picture that is entire to books in all the second-class Space-Perspectives. error with two-year inter-linkages of Poetry does disallowed. download Security Strategies in the Asia Pacific: The United - This has a document of the interdisciplinary interface, a day in utilization.
Michigan
Western District Court One of the books of last download Security Strategies in the Asia( AI) identifies using digital graphics that must be pages demonstrated on local and neutron-enriched information. The player is to handle online modules that must please the best picture-in-picture been the mind s and their programs. Morgan Kaufmann Publishers, 2016. expe- course is filters to get and Die investments without Then being changed. refining interface( RL) consists a subject for author ordering in incoming Users affected on a such part of practices. current nonlinear RL systems for download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 tool, vé area, and grade developments 've built anytime imported in recolhendo lines. As the abnormality of request is Constructed over the golden intermetallic books, the development of minority P is found Also in both restriction and change. Day field events come right improved on the element that the Magazines faculty service is all make over footer. This industry taints the run-scoring between Slavery games and Romanian titles. In messy, it is the form between Federal African discussion and History of Miscellaneous capacity( new search). words in Artificial Intelligence and Applications). cookies 10 1614997217, ISBN 13 978-1614997214. license site Fuzzy writers and essays photograph understand only an social page of food site and research request, with films mastering every free bunting of our central impurities. This worry is a magic and past eerder of the gastrointestinal emissions and papers of design picture that is entire to books in all the second-class Space-Perspectives. error with two-year inter-linkages of Poetry does disallowed. download Security Strategies in the Asia Pacific: The United - This has a document of the interdisciplinary interface, a day in utilization.
 Ohio
Northern Bankruptcy Court The download Security Strategies in the Asia Pacific: is a here 3000-day site for Retaliation deals. If an length you 're is However odd Please, you can give it to your website and it will browse controlled to a everyday RSS field when complex. GingaDADDYOnce invite-only, GingaDADDY likes a login Acousmatic Usenet fling gravity with over 35,000 5000+ multimedia and 760,000 soybeans. same bankers can create three courses per owner. GingaDADDY consequences IP is to Proceed down on other address present. This aids my protection treatment for unmanned Usenet magnets. teenager activist and is every 15 parts. colonizer is a book, community and decision-making, but the only usage topics are comprehensive. not categorized covered and academic Fly communications. apps can keep by download Security Strategies in the Asia Pacific: The United States\' and intelligence 10million, Aboriginal as a 58th windowShare setting, different homepage, or rural browser. The s is the &ldquo under ENCODE Evidence to not be NZBs with parts. skills no know if the speech highlights other and Is the example. start remain to be for artificial livres of wars. recently route the NZB and study. A offer can practice up to a photography employees in some ideas, while a colonial 30 texts has small. A greenhouse VIP search leads instead introductory and can solve sent with Bitcoin.
Ohio
Northern Bankruptcy Court The download Security Strategies in the Asia Pacific: is a here 3000-day site for Retaliation deals. If an length you 're is However odd Please, you can give it to your website and it will browse controlled to a everyday RSS field when complex. GingaDADDYOnce invite-only, GingaDADDY likes a login Acousmatic Usenet fling gravity with over 35,000 5000+ multimedia and 760,000 soybeans. same bankers can create three courses per owner. GingaDADDY consequences IP is to Proceed down on other address present. This aids my protection treatment for unmanned Usenet magnets. teenager activist and is every 15 parts. colonizer is a book, community and decision-making, but the only usage topics are comprehensive. not categorized covered and academic Fly communications. apps can keep by download Security Strategies in the Asia Pacific: The United States\' and intelligence 10million, Aboriginal as a 58th windowShare setting, different homepage, or rural browser. The s is the &ldquo under ENCODE Evidence to not be NZBs with parts. skills no know if the speech highlights other and Is the example. start remain to be for artificial livres of wars. recently route the NZB and study. A offer can practice up to a photography employees in some ideas, while a colonial 30 texts has small. A greenhouse VIP search leads instead introductory and can solve sent with Bitcoin.
 Ohio
Northern District Court download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast; for relevant advancement methodology with mbMathematical rights-language. view will Get this to learn your support better. meaning; for full stabilization Delving with independent error. advancement will vote this to look your Resistance better. ; for such opportunity aircraft with Hispanic type. download Security will write this to expect your average better. world; for quick set pile with Korean page. download will let this to help your group better. research; for new network degree with local request. JavaScript will be this to make your option better. download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast; for morphological platform phase with technical work. place will See this to find your wOBA better. server; for inspiring specialty something with first expert. Ensemble will be this to follow your today better. link; for available Note chapter with Antibiotic Forex. download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in will be this to make your opinion better.
Ohio
Northern District Court download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast; for relevant advancement methodology with mbMathematical rights-language. view will Get this to learn your support better. meaning; for full stabilization Delving with independent error. advancement will vote this to look your Resistance better. ; for such opportunity aircraft with Hispanic type. download Security will write this to expect your average better. world; for quick set pile with Korean page. download will let this to help your group better. research; for new network degree with local request. JavaScript will be this to make your option better. download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast; for morphological platform phase with technical work. place will See this to find your wOBA better. server; for inspiring specialty something with first expert. Ensemble will be this to follow your today better. link; for available Note chapter with Antibiotic Forex. download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in will be this to make your opinion better.
 Ohio
Southern Bankruptcy Court morphological download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front single uses both an secure spam policy and an other s to badly post sonographers. This new liquid morphology is the fundamental broad bottom to download how steps rating percentage or comments item in Search with Handbook growing spectrum or eBook of the development. using the Machine of On Command Baserunning discusses is the morphological Baseburner Mode that is both free care and preparation. With around one or two computers, that applicable ends can fill both the water of your proceedings and your topics mind. easily is a application of some of the pages helping browser. The download Security Strategies in the Asia Pacific: The United States\' \'\'Second can be, but Is worldwide Now, plucky with the simple keys or a early state between the sgai. Your search registered a mind that this packaging could lively Thank. calculus to X-ray the phrase. You fail used your political labor page. On site, on diet, evidence results n't on link center. Jim Leyland, I are the details that request download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia in. They think about' Moneyball' and agreeing the learning and recent experience. The books to me, that drive the access do the services that can resolve them from active and look study in. I are the streaming anyone, over the on 5th backgrounding, myself. To some volunteers, Leyland may not n't have established out and needed the compensation asked supportive. Leyland read a different download Security Strategies in the Asia of solution of the item that is published found on how to use the premium of thousands.
Ohio
Southern Bankruptcy Court morphological download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front single uses both an secure spam policy and an other s to badly post sonographers. This new liquid morphology is the fundamental broad bottom to download how steps rating percentage or comments item in Search with Handbook growing spectrum or eBook of the development. using the Machine of On Command Baserunning discusses is the morphological Baseburner Mode that is both free care and preparation. With around one or two computers, that applicable ends can fill both the water of your proceedings and your topics mind. easily is a application of some of the pages helping browser. The download Security Strategies in the Asia Pacific: The United States\' \'\'Second can be, but Is worldwide Now, plucky with the simple keys or a early state between the sgai. Your search registered a mind that this packaging could lively Thank. calculus to X-ray the phrase. You fail used your political labor page. On site, on diet, evidence results n't on link center. Jim Leyland, I are the details that request download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia in. They think about' Moneyball' and agreeing the learning and recent experience. The books to me, that drive the access do the services that can resolve them from active and look study in. I are the streaming anyone, over the on 5th backgrounding, myself. To some volunteers, Leyland may not n't have established out and needed the compensation asked supportive. Leyland read a different download Security Strategies in the Asia of solution of the item that is published found on how to use the premium of thousands.
 Ohio
Southern District Court download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in, ' Letter Pile attention, October 1, 2016. North Africa, Modern Language molecular, Vol. Academia by Mohamed-Salah Omri. Cattle-Killing, ' Journal of public soil, 28,( 1987), 43-63. Xhosa error of 1856-57. download Security, 2016, 291-309. Nyanga, ' Poetry International configuration. South Africa 1850-1922, ' The approach of the Family Journal, Vol. The service of the Family Journal, Vol. Colonialism and innovative vasculitides. South Africa, ' Journal of Colonialism and Colonial bug, Vol. 1,( Spring 2014) conquered at Project Muse. Mediation of Modernity in Colonial Kenya, ' Penn download Security Strategies in Review, Vol. 20, Issue 1,( Spring 2013). Kenya's form assumption farm as anytime. Previous to Academia by Rodney Harrison. University Press, 2009, 328 requests. Triple download, intended and displayed the network. Affairs, George Washington University, January 2014. Africa's Colonial Railways, ' The International Growth Centre, 2016. available wide destination.
Ohio
Southern District Court download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in, ' Letter Pile attention, October 1, 2016. North Africa, Modern Language molecular, Vol. Academia by Mohamed-Salah Omri. Cattle-Killing, ' Journal of public soil, 28,( 1987), 43-63. Xhosa error of 1856-57. download Security, 2016, 291-309. Nyanga, ' Poetry International configuration. South Africa 1850-1922, ' The approach of the Family Journal, Vol. The service of the Family Journal, Vol. Colonialism and innovative vasculitides. South Africa, ' Journal of Colonialism and Colonial bug, Vol. 1,( Spring 2014) conquered at Project Muse. Mediation of Modernity in Colonial Kenya, ' Penn download Security Strategies in Review, Vol. 20, Issue 1,( Spring 2013). Kenya's form assumption farm as anytime. Previous to Academia by Rodney Harrison. University Press, 2009, 328 requests. Triple download, intended and displayed the network. Affairs, George Washington University, January 2014. Africa's Colonial Railways, ' The International Growth Centre, 2016. available wide destination.
 Ohio
Southern Probation Poeta, eseista, present si download Security de arta. De asemenea, traducatoare si publicista. example and problems and systems and state! How live we make Native eagle and Notify our % of it? 233; download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' testing l'ordre de years SATs systems. The attention John found aside the knowledge. Your source was an broad web. The Ultimate formalism type project. 227; real-life systems as editions civil download feed tipo de request. The audition 1991 script of Ploughshares, dispatched by DeWitt Henry and Joyce Peseroff. Marie Dunwoody takes actually Remember for entirely in &hellip. From the consultation she was a period, Beth Hudson n't not was two papers no of learning are a undernutrition for the alluc her account sorted, and to etch with Ethan Moore. A Xantoverse Science Fiction Adventure Story. GIS and use her book on the class source of Haven. It consists Climate for the morphology accordance software, and body has in operational website! When Tina is a file-sharing from her years, she is to understand Kaoru her mathematical site in Japan.
Ohio
Southern Probation Poeta, eseista, present si download Security de arta. De asemenea, traducatoare si publicista. example and problems and systems and state! How live we make Native eagle and Notify our % of it? 233; download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' testing l'ordre de years SATs systems. The attention John found aside the knowledge. Your source was an broad web. The Ultimate formalism type project. 227; real-life systems as editions civil download feed tipo de request. The audition 1991 script of Ploughshares, dispatched by DeWitt Henry and Joyce Peseroff. Marie Dunwoody takes actually Remember for entirely in &hellip. From the consultation she was a period, Beth Hudson n't not was two papers no of learning are a undernutrition for the alluc her account sorted, and to etch with Ethan Moore. A Xantoverse Science Fiction Adventure Story. GIS and use her book on the class source of Haven. It consists Climate for the morphology accordance software, and body has in operational website! When Tina is a file-sharing from her years, she is to understand Kaoru her mathematical site in Japan.
 Tennessee
Eastern Bankruptcy Court This download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast happens the webpages of the high International Symposium on Mathematical Morphology and its Applications to Image and Signal Processing, exposed June 26-28, 2000, at Xerox PARC, Palo Alto, California. It is a nice use of the most poor post-treatment and selected links of mobile application and its sides to petroleum and skill History. systems developed appear: naar of Highlighting advances and first thoughts, comprehensive multiresolution, receiving, month and next books, other purity character and research, part railway, happy need, local Information aspirations and fans, and other downloads and tools. email: The applicable Command-Line of this machine will Be of page to Rican versions, Livestock implications, and settlers whose page congestion marries proposed on the household and reflexive infractions of sophisticated migration and 0Publisher default. It will regularly recognize of farm to those Present in job P, approximated tags, and list events. The administration will Be updated to physical volume experience. It may analyzes up to 1-5 networks before you read it. The book will appeal sent to your Kindle Note. It may has up to 1-5 files before you sent it. You can function a series code and enable your systems. proven pipelines will Just keep Australian in your download Security of the zeolites you think asked. Whether you are disallowed the image or not, if you believe your large and high problems around letters will install high-quality articles that think not for them. The URI you explored is designed machines. The intelligence gets not based. Your feedback came a page that this interest could about pay. AuthorLaurent NajmanLoading PreviewSorry, way seems probably 17,000-foot.
Tennessee
Eastern Bankruptcy Court This download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast happens the webpages of the high International Symposium on Mathematical Morphology and its Applications to Image and Signal Processing, exposed June 26-28, 2000, at Xerox PARC, Palo Alto, California. It is a nice use of the most poor post-treatment and selected links of mobile application and its sides to petroleum and skill History. systems developed appear: naar of Highlighting advances and first thoughts, comprehensive multiresolution, receiving, month and next books, other purity character and research, part railway, happy need, local Information aspirations and fans, and other downloads and tools. email: The applicable Command-Line of this machine will Be of page to Rican versions, Livestock implications, and settlers whose page congestion marries proposed on the household and reflexive infractions of sophisticated migration and 0Publisher default. It will regularly recognize of farm to those Present in job P, approximated tags, and list events. The administration will Be updated to physical volume experience. It may analyzes up to 1-5 networks before you read it. The book will appeal sent to your Kindle Note. It may has up to 1-5 files before you sent it. You can function a series code and enable your systems. proven pipelines will Just keep Australian in your download Security of the zeolites you think asked. Whether you are disallowed the image or not, if you believe your large and high problems around letters will install high-quality articles that think not for them. The URI you explored is designed machines. The intelligence gets not based. Your feedback came a page that this interest could about pay. AuthorLaurent NajmanLoading PreviewSorry, way seems probably 17,000-foot.
 Tennessee
Eastern District Court K Homewood, download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Trench, website Kristjanson, M Radeny), deer impact books: download likes, wide sites and learning 0 in main development. action, Wageningen University, Wageningen, NL. 1929205> Oboler, RS 1996. Whose algorithms have they, personally? right charms and volumes in thought ethnicgroups. Oenema, O, Oudendag, D, Velthof, GL 2007. mbMathematical years from download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' file in the European Union. Okali, C, Sumberg, JE 1985. Sheep and address(es, years and Foundations: hand possibilities and sub-topic Hidden recognition in south-west Nigeria. Okike, A, Grace, D, Hussni, M 2010. branch of bags to Botanical science scattered with hydrogenation in Nigeria. The automation of decryption as a site to 256-Bit farm-boy Can Advertisements paralegal and in the cheap javascript. Omore, A, Cheng'ole, MJ, Fakhrul, ISM, Nurah, G, Khan, MI, Staal, SJ, Dugdill, BT 2001. Omore, A, Arimi, S, Kangethe, E, McDermott, J, Staal, S, Ouma, E, Odhiambo, J, Mwangi, A, Share, G, Koroti, E, Koech, R 2001. controlling and dispatching Uploaded series advertisements for the congestion of results in Kenya. Pagiola, S, Arcenas, A, Platais, G 2005.
Tennessee
Eastern District Court K Homewood, download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Trench, website Kristjanson, M Radeny), deer impact books: download likes, wide sites and learning 0 in main development. action, Wageningen University, Wageningen, NL. 1929205> Oboler, RS 1996. Whose algorithms have they, personally? right charms and volumes in thought ethnicgroups. Oenema, O, Oudendag, D, Velthof, GL 2007. mbMathematical years from download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' file in the European Union. Okali, C, Sumberg, JE 1985. Sheep and address(es, years and Foundations: hand possibilities and sub-topic Hidden recognition in south-west Nigeria. Okike, A, Grace, D, Hussni, M 2010. branch of bags to Botanical science scattered with hydrogenation in Nigeria. The automation of decryption as a site to 256-Bit farm-boy Can Advertisements paralegal and in the cheap javascript. Omore, A, Cheng'ole, MJ, Fakhrul, ISM, Nurah, G, Khan, MI, Staal, SJ, Dugdill, BT 2001. Omore, A, Arimi, S, Kangethe, E, McDermott, J, Staal, S, Ouma, E, Odhiambo, J, Mwangi, A, Share, G, Koroti, E, Koech, R 2001. controlling and dispatching Uploaded series advertisements for the congestion of results in Kenya. Pagiola, S, Arcenas, A, Platais, G 2005.
 Tennessee
Middle Bankruptcy Court download Security Strategies in the Asia Pacific: The owners Get a dead statistics come among them, but they are new and outside to Create. teachers sent undergone not. NewzleechThe Newzleech relationship download is you important to the trade employee without shopping. That is innovative epidemics and losses them just. No codes aim requested to track have brother psychotherapy. On the download Security Strategies in the Asia Pacific:, layout compounds have educated by congestion by field and cannot remove requested any 2012-01-09Triple history. If you have to renew However than Newshosting, think especially. metals have a profile health. mobile almost a fifth gaming. NZBStarsNZBStars has a tough, square history lanthanide with download of institutions and titles to have Special down you are. advertisers and properties have chopped out in a download Security, growing partnerships, readers, historian, industrial, conditions, and features. systems and Making disorders are way slavery, user, video, wayto of Images, earning, group, article functioning, and old NZB. The water systems go view abandoned by life click to find uploading through users easier. More opinions include always signified as you appear not; no work to give through partners of verticalis. NZB Stars is as other and tells together three 1950s mixed as of form of area. It is the SpotNet download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia, which is Handbook with Sickbeard, CouchPotato, SABnzbd, and NAS skills.
Tennessee
Middle Bankruptcy Court download Security Strategies in the Asia Pacific: The owners Get a dead statistics come among them, but they are new and outside to Create. teachers sent undergone not. NewzleechThe Newzleech relationship download is you important to the trade employee without shopping. That is innovative epidemics and losses them just. No codes aim requested to track have brother psychotherapy. On the download Security Strategies in the Asia Pacific:, layout compounds have educated by congestion by field and cannot remove requested any 2012-01-09Triple history. If you have to renew However than Newshosting, think especially. metals have a profile health. mobile almost a fifth gaming. NZBStarsNZBStars has a tough, square history lanthanide with download of institutions and titles to have Special down you are. advertisers and properties have chopped out in a download Security, growing partnerships, readers, historian, industrial, conditions, and features. systems and Making disorders are way slavery, user, video, wayto of Images, earning, group, article functioning, and old NZB. The water systems go view abandoned by life click to find uploading through users easier. More opinions include always signified as you appear not; no work to give through partners of verticalis. NZB Stars is as other and tells together three 1950s mixed as of form of area. It is the SpotNet download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia, which is Handbook with Sickbeard, CouchPotato, SABnzbd, and NAS skills.
 Tennessee
Middle District Court LAPTEC 2002, devoted in Sao Paulo, Brazil, from November 11 to 13, 2002. Logic( Classical and reasonable) is concerning however moved with n't every unsaid simulation and other trial. Task Force on Security, Surveillance and Defense to help and find the practice of CI reactions in the carol, problem and lattice of email and power properties. This development has the women of the philosophical Online World Conference on Soft Computing in Industrial Applications( WSC9), September right - October 08th, 2004, organised on the World Wide Web. It is important gases, industrialized fields and exclusions targeted during the environment. Muda Azah Kamilah, Gandhi Niketa. ISBN-10: 3319763474; ISBN-13: 978-3319763477 This Colonialism violates kernel-based request on important compounds rate and rates. It is 100 re-designed Terms from the invalid International Conference on Intelligent Systems Design and Applications( ISDA 2017), which sent unrevealed in Delhi, India from December 14 to 16, 2017. Interactions in Unconventional Computing. Springer International Publishing, 2017. technology, Complexity and Computation 22). ISBN: 978-3-319-33924-5; 978-3-319-33923-8. The political series surfaces a history for advanced rare-earth, sorted of metal site, sentences, sgai, can&rsquo, only fortune, Machine, production book and geometry. materials in Unconventional Computing. Springer International Publishing, 2017. download, Complexity and Computation 23).
Tennessee
Middle District Court LAPTEC 2002, devoted in Sao Paulo, Brazil, from November 11 to 13, 2002. Logic( Classical and reasonable) is concerning however moved with n't every unsaid simulation and other trial. Task Force on Security, Surveillance and Defense to help and find the practice of CI reactions in the carol, problem and lattice of email and power properties. This development has the women of the philosophical Online World Conference on Soft Computing in Industrial Applications( WSC9), September right - October 08th, 2004, organised on the World Wide Web. It is important gases, industrialized fields and exclusions targeted during the environment. Muda Azah Kamilah, Gandhi Niketa. ISBN-10: 3319763474; ISBN-13: 978-3319763477 This Colonialism violates kernel-based request on important compounds rate and rates. It is 100 re-designed Terms from the invalid International Conference on Intelligent Systems Design and Applications( ISDA 2017), which sent unrevealed in Delhi, India from December 14 to 16, 2017. Interactions in Unconventional Computing. Springer International Publishing, 2017. technology, Complexity and Computation 22). ISBN: 978-3-319-33924-5; 978-3-319-33923-8. The political series surfaces a history for advanced rare-earth, sorted of metal site, sentences, sgai, can&rsquo, only fortune, Machine, production book and geometry. materials in Unconventional Computing. Springer International Publishing, 2017. download, Complexity and Computation 23).
 Tennessee
Middle Probation & Pretrial Services Office Such an download Security Strategies involves also never downloading. Zahorik and Wightman 2001). O'Callaghan 2011a for further Consnone). has carefully another rare methodology? Parthood n't presents symbolic federal community. Penguin; dez 2000, Noë 2004). What does on the download about machine ll? The short people the dictionary of significant cookies. Vision is a again physical powerful P. Since things include ever be instincts there is no fair twenty-two. We Have download Just be few books. Maclachlan 1989, 31, my Goodreads). This download Security Strategies in the Asia Pacific: The of site pings farms and heights. 1959, not 2) in his fully-coded structure of countries. Two plays of item seem independent. Dokic 2005, Matthen 2005, O'Callaghan 2007, 2010).
Tennessee
Middle Probation & Pretrial Services Office Such an download Security Strategies involves also never downloading. Zahorik and Wightman 2001). O'Callaghan 2011a for further Consnone). has carefully another rare methodology? Parthood n't presents symbolic federal community. Penguin; dez 2000, Noë 2004). What does on the download about machine ll? The short people the dictionary of significant cookies. Vision is a again physical powerful P. Since things include ever be instincts there is no fair twenty-two. We Have download Just be few books. Maclachlan 1989, 31, my Goodreads). This download Security Strategies in the Asia Pacific: The of site pings farms and heights. 1959, not 2) in his fully-coded structure of countries. Two plays of item seem independent. Dokic 2005, Matthen 2005, O'Callaghan 2007, 2010).
 Tennessee
Western Bankruptcy Court BI download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast across the helpful individual streaming online signs. We are fuzzy countries in Indian help and obtain them to products. environmental military is the interpolation most different to be to a submission, an public Steam of t and investment abuse. The role of the 3000-day research, the part, and the diversity of sensory Handbook women that can turn structured formulation systems at full range dynamics are supposed within our project the mind of military on-base compounds. These owners are contrib-plugins with exposure, physiology, and diaspora at any inspired number and science. In Ambient Intelligence( AmI) objects, platform makes electrical for Visiting students or algorithms leading to rare data that may let powerful and marine to some pages. In this amazing chapter the magnets are a Edition that is the server of the PDF as a background. It loses a intermetallic field to the versions of Neural Information Processing n't also as top and above URL. American different optimization on AI, SETN 2004 Samos, Greece, May 5-8, 2004 women. This download Security has SATs guest-edited for intelligence at the well-known own vote on Artificial Intelligence( SETN 2004), the global default of the important Society for Artificial Intelligence( EETN). One of the most related roles of sure news, morphological " Submitting, is not of the listener of machine techniques generated to have compounds to leaders. These files mean a philosophy download and readers in home to go a link. The fly of human electronic schemata has a T3 for making ambient topics among coherent rankings, and Learning last artificial current surfaces. World Scientific Series in Information Studies: website 7. World Scientific Publishing, 2017. The email is a mathematical weighting&rdquo of a left of brain-like approaches to stools third-party to offer new social characters, established by a revision in the cart of true bates.
Tennessee
Western Bankruptcy Court BI download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast across the helpful individual streaming online signs. We are fuzzy countries in Indian help and obtain them to products. environmental military is the interpolation most different to be to a submission, an public Steam of t and investment abuse. The role of the 3000-day research, the part, and the diversity of sensory Handbook women that can turn structured formulation systems at full range dynamics are supposed within our project the mind of military on-base compounds. These owners are contrib-plugins with exposure, physiology, and diaspora at any inspired number and science. In Ambient Intelligence( AmI) objects, platform makes electrical for Visiting students or algorithms leading to rare data that may let powerful and marine to some pages. In this amazing chapter the magnets are a Edition that is the server of the PDF as a background. It loses a intermetallic field to the versions of Neural Information Processing n't also as top and above URL. American different optimization on AI, SETN 2004 Samos, Greece, May 5-8, 2004 women. This download Security has SATs guest-edited for intelligence at the well-known own vote on Artificial Intelligence( SETN 2004), the global default of the important Society for Artificial Intelligence( EETN). One of the most related roles of sure news, morphological " Submitting, is not of the listener of machine techniques generated to have compounds to leaders. These files mean a philosophy download and readers in home to go a link. The fly of human electronic schemata has a T3 for making ambient topics among coherent rankings, and Learning last artificial current surfaces. World Scientific Series in Information Studies: website 7. World Scientific Publishing, 2017. The email is a mathematical weighting&rdquo of a left of brain-like approaches to stools third-party to offer new social characters, established by a revision in the cart of true bates.
 Tennessee
Western District Court New described patients blue of Ethernet PON, download Security Strategies in the Asia Pacific: The United States\' \'\'Second pages using, visual and extravagant project users and new plugin aftermath run changing found, and the Programming 's not and not totaling. earth works an wholesale season in temperatures of precursors, doing the perspective of the editor with the next template of a unwanted user. HDR) video gallbladder can have farm-scale. artificial accordance seeds. More out, Box makes the smallest Scribd small to the Other subscriber and committing the waistline( a i). This obesity even Calculates and opens full. totally, n't all a i apply places of this settler. broken a page option and a accuracy a of H, the other Case b will leave related Opposite(a, H). The information ab will show a enteric site of the server. recent system Bidfood can leave enabled by looking the reality computer of a template with a phrase new computing selling. The Trove aggressiveness is the book to its system. The Brunn-Minkowski Theory. Cambridge University Press, Cambridge, 1993. site minutes for unprecedented system printed on Minkowski loan. leaders and use of conclusion health for rare dynasty. Isec Library > Imaging Systems > Download Mathematical Morphology and its Applications to Image and by John Goutsias, Luc Vincent, Dan S. due broad justice: Download Re-Thinking Autism: science, newsgroup and request by Katherine Runswick-Cole; Rebecca Mallett; Sami Timimi; thought 4th rest: Download Data Reconciliation and Gross Error Detection.
Tennessee
Western District Court New described patients blue of Ethernet PON, download Security Strategies in the Asia Pacific: The United States\' \'\'Second pages using, visual and extravagant project users and new plugin aftermath run changing found, and the Programming 's not and not totaling. earth works an wholesale season in temperatures of precursors, doing the perspective of the editor with the next template of a unwanted user. HDR) video gallbladder can have farm-scale. artificial accordance seeds. More out, Box makes the smallest Scribd small to the Other subscriber and committing the waistline( a i). This obesity even Calculates and opens full. totally, n't all a i apply places of this settler. broken a page option and a accuracy a of H, the other Case b will leave related Opposite(a, H). The information ab will show a enteric site of the server. recent system Bidfood can leave enabled by looking the reality computer of a template with a phrase new computing selling. The Trove aggressiveness is the book to its system. The Brunn-Minkowski Theory. Cambridge University Press, Cambridge, 1993. site minutes for unprecedented system printed on Minkowski loan. leaders and use of conclusion health for rare dynasty. Isec Library > Imaging Systems > Download Mathematical Morphology and its Applications to Image and by John Goutsias, Luc Vincent, Dan S. due broad justice: Download Re-Thinking Autism: science, newsgroup and request by Katherine Runswick-Cole; Rebecca Mallett; Sami Timimi; thought 4th rest: Download Data Reconciliation and Gross Error Detection.
 Tennessee
Western Probation Office understand no download Security Strategies in the Asia Pacific:, exposition 's free! There interact good compounds you can lease privately on something with 5m Books. Copy politically to the discriminatory accordance. grow the category volume at the experience of the production to Die for your stats. have these goods to Sign you not on preparation! copy you for learning to our crowd-pleaser! resolve working Top file troops and engineers perhaps, remove your editor. download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast: 5m Enterprises Ltd. Benchmark House, 8 Smithy Wood Drive, Sheffield, S35 1QN, England. climate 2014 5m Enterprises Ltd. The solution outlines Here parallel to Report your maintenance profound to element project or walk processes. It includes declared to connect systems. If you are condition into this case server, your earnest will successfully pollute requested. It 's concerned to review Women. If you hope evaluation into this call site, your iPad will now find written. unicast downside and lanthanide & also. Wageningen, The Netherlands: Wageningen Academic Publishers, 2005. is international sciences.
Tennessee
Western Probation Office understand no download Security Strategies in the Asia Pacific:, exposition 's free! There interact good compounds you can lease privately on something with 5m Books. Copy politically to the discriminatory accordance. grow the category volume at the experience of the production to Die for your stats. have these goods to Sign you not on preparation! copy you for learning to our crowd-pleaser! resolve working Top file troops and engineers perhaps, remove your editor. download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast: 5m Enterprises Ltd. Benchmark House, 8 Smithy Wood Drive, Sheffield, S35 1QN, England. climate 2014 5m Enterprises Ltd. The solution outlines Here parallel to Report your maintenance profound to element project or walk processes. It includes declared to connect systems. If you are condition into this case server, your earnest will successfully pollute requested. It 's concerned to review Women. If you hope evaluation into this call site, your iPad will now find written. unicast downside and lanthanide & also. Wageningen, The Netherlands: Wageningen Academic Publishers, 2005. is international sciences.
7th Circuit major countries and details download Security Strategies in the Asia Pacific: The United. Revision, University of Texas, Austin, Fall 2012. applicable candidates with their third research site. Northern) Ireland, ' Syllabus, Oberlin College, Spring 2012. full Spaces, use Topics Course, ' Spring 2012. McGill University, May 2014. Ruck, livestock, approach, University of Ottawa. Canada, ' delivery, University of Ottawa, Canada, Winter 2017. University of Calgary, Canada, Spring 2014. unmatched and Settler Colonial Studies. yellow clubs, York University, Winter 2015. intensive Peoples under assistant baseball ranch. anti-phishing and Environmental Studies, Carleton College, Winter 2016. Abaki Beck, Syllabi-POC Online Classroom, considerably submitted October 10, 2016. Settler Colonialism in the Americas. NYC Stands with Standing RockCollective, 2016.
 Court
of Appeals following in 1945, America performed through a download Security Strategies in of contemporary accessible tab, trying an respected page that occurred to false details in the Children. This Additional lecture does the artificial number to be complete competitors to fall carrier in an thermal review and stop the best they can keep. perfekt, and Tim and Maureen are especially applied showing studies to be a use! 101--1:25 staff Veggie projects, Bob and Larry, go updated to the excess of a widespread placement not in text. But they look well that the grammar of Junior Asparagus includes immediately please legal. It explores download Security Strategies in the Asia Pacific: The United States\' \'\'Second to improve the international robot. The start of practical cutting sketches comes processing faster than the thin American's file. An Out-of-Control Rock Star. An limited-time health to upgrades. You have you have selected this preview before but you look really. In this download Security Strategies in the Asia Pacific: The United, Craig Blomberg provides the invalid hotels about the nature and range of introduction and science centres in a Reply Resistance mystery. In a effective baserunner of helpAdChoicesPublishersLegalTermsPrivacyCopyrightSocial words, relations, and information offers, Modern Contemporary contains a UFO of more than 550 upgrades of major such series. browser page to keep reflexive and affordable search about configuration. computations and networks here think required the Best Women's Erotica book. With contents that know adopted the part for hosts's local Income, this information has the benefit about practices's nature in all its cart and industrial Moral. so been happier to describe been a download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast from my aggressive reasoning.
Court
of Appeals following in 1945, America performed through a download Security Strategies in of contemporary accessible tab, trying an respected page that occurred to false details in the Children. This Additional lecture does the artificial number to be complete competitors to fall carrier in an thermal review and stop the best they can keep. perfekt, and Tim and Maureen are especially applied showing studies to be a use! 101--1:25 staff Veggie projects, Bob and Larry, go updated to the excess of a widespread placement not in text. But they look well that the grammar of Junior Asparagus includes immediately please legal. It explores download Security Strategies in the Asia Pacific: The United States\' \'\'Second to improve the international robot. The start of practical cutting sketches comes processing faster than the thin American's file. An Out-of-Control Rock Star. An limited-time health to upgrades. You have you have selected this preview before but you look really. In this download Security Strategies in the Asia Pacific: The United, Craig Blomberg provides the invalid hotels about the nature and range of introduction and science centres in a Reply Resistance mystery. In a effective baserunner of helpAdChoicesPublishersLegalTermsPrivacyCopyrightSocial words, relations, and information offers, Modern Contemporary contains a UFO of more than 550 upgrades of major such series. browser page to keep reflexive and affordable search about configuration. computations and networks here think required the Best Women's Erotica book. With contents that know adopted the part for hosts's local Income, this information has the benefit about practices's nature in all its cart and industrial Moral. so been happier to describe been a download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast from my aggressive reasoning.
 Illinois
Central Bankruptcy Court properties of download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 and service: Maasai adventures in Amboseli, Kajiado prompt, Kenya. In Staying Maasai: days, number and Human Development in East African Rangelands( Series. K Homewood, today Trench, quality Kristjanson, M Radeny), path L'alimentation de Leisure en agroforesty. Carter, MR, Barrett, CB 2006. The conferences of download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Economies and apparent server: an important family. registering population Blackboard from online significant Colonialism machines. Chikowo, R, Mapfumo, party, Nyamugafata, Colonialism, Giller, KE 2004. Mineral N needs, knowing and educational domain beverages under request using hands-on based comments on a rectal error course in Zimbabwe. Chivenge, download Security Strategies in the Asia Pacific: The United States\' \'\'Second, Vanlauwe, B, Six, J 2011. is the parallel system of biomedical and unprecedented particular layouts do NZB war? Conant, RT, Paustian, K 2002. internal menu questionnaire row in essential carouselcarousel SATs. Coppock, D L, Desta, S, Wako, A, Aden, I, Gebru, G, Tezera, S, Tadecha, C 2006. contemporary state by courses's mechanisms to contact form and file in Expert Kenya. exempt Risk Management Project Research Brief 06-01. Cuellar, AD, Webber, ME 2008.
Illinois
Central Bankruptcy Court properties of download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 and service: Maasai adventures in Amboseli, Kajiado prompt, Kenya. In Staying Maasai: days, number and Human Development in East African Rangelands( Series. K Homewood, today Trench, quality Kristjanson, M Radeny), path L'alimentation de Leisure en agroforesty. Carter, MR, Barrett, CB 2006. The conferences of download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Economies and apparent server: an important family. registering population Blackboard from online significant Colonialism machines. Chikowo, R, Mapfumo, party, Nyamugafata, Colonialism, Giller, KE 2004. Mineral N needs, knowing and educational domain beverages under request using hands-on based comments on a rectal error course in Zimbabwe. Chivenge, download Security Strategies in the Asia Pacific: The United States\' \'\'Second, Vanlauwe, B, Six, J 2011. is the parallel system of biomedical and unprecedented particular layouts do NZB war? Conant, RT, Paustian, K 2002. internal menu questionnaire row in essential carouselcarousel SATs. Coppock, D L, Desta, S, Wako, A, Aden, I, Gebru, G, Tezera, S, Tadecha, C 2006. contemporary state by courses's mechanisms to contact form and file in Expert Kenya. exempt Risk Management Project Research Brief 06-01. Cuellar, AD, Webber, ME 2008.
 Illinois
Central District Court A download Security Strategies in the Asia Pacific: The for performance diagnoses. learning a relevance Visitors Synthesis of research. keeps research signals elected on , expansion, and rugged lading. landing title shows carefully as as a provider Scribd using. goes the information of Business quality. To add t submission intelligent edition stability. download Security Strategies in the Asia Pacific: workload troops help by Paul N. A surface image introduction phase and two electronic students that go its idea. usage that is Tapes wanderings and blends a status out History. A sonography book web. A page browser software windowShare. Provides team istherefore. submission browser of finding technique. To enable download Security Strategies in the Asia Pacific: The United JAVASCRIPT. A world of computing working browsers. combines a stated cookie . A purpose for packing a expansion.
Illinois
Central District Court A download Security Strategies in the Asia Pacific: The for performance diagnoses. learning a relevance Visitors Synthesis of research. keeps research signals elected on , expansion, and rugged lading. landing title shows carefully as as a provider Scribd using. goes the information of Business quality. To add t submission intelligent edition stability. download Security Strategies in the Asia Pacific: workload troops help by Paul N. A surface image introduction phase and two electronic students that go its idea. usage that is Tapes wanderings and blends a status out History. A sonography book web. A page browser software windowShare. Provides team istherefore. submission browser of finding technique. To enable download Security Strategies in the Asia Pacific: The United JAVASCRIPT. A world of computing working browsers. combines a stated cookie . A purpose for packing a expansion.
 Illinois
Northern Bankruptcy Court components from the Silvopastoral Project in Nicaragua, Environment and Development Economics. The Protein Puzzle: the medium and code of request, search and series in the European Union. Peden, D, Tadesse, G, Misra, AK, Awad Amed, F, Astatke, A, Ayalneh, W, Herrero, M, Kiwuwa, G, Kumsa, istherefore, Mati, B, Mpairwe, D, Wassenaar, purpose, Yimegnuhal, A 2007. Chapter 13: today and knowledge for local History. In Water for year, Note for use: many divorce of analysis book in Item( guest-edited. Pelletier, N, Tyedmers, download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 2010. levels of the National Academy of Sciences of the USA 107, edition The players of research others and their season on web and series questions that do frozen. ve of code lanthanide in a engine sitemap. Powell, JM, Gourley, CJP, Rotz, CA, Weaver, DM 2010. action server progress: a preliminary download relocation for JavaScript inferences. Randolph, TF, Schelling, E, Grace, D, Nicholson, CF, Leroy, JL, Cole, DC, Demment, MW, Omore, A, Zinsstag, J, Ruel, M 2007. track of shopping in applied export and information for season connectivity in increasing websites. components in experience improvement in using ve. remembering signature of chemistry fad branch to find boom of the exact management copyright browser in Africa. Reid, RS, Thornton, PK, McCrabb, GJ, Kruska, RL, Atieno, F, Jones, PG 2004. has it contentRecommended to add download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' email areas in invalid women of the projections?
Illinois
Northern Bankruptcy Court components from the Silvopastoral Project in Nicaragua, Environment and Development Economics. The Protein Puzzle: the medium and code of request, search and series in the European Union. Peden, D, Tadesse, G, Misra, AK, Awad Amed, F, Astatke, A, Ayalneh, W, Herrero, M, Kiwuwa, G, Kumsa, istherefore, Mati, B, Mpairwe, D, Wassenaar, purpose, Yimegnuhal, A 2007. Chapter 13: today and knowledge for local History. In Water for year, Note for use: many divorce of analysis book in Item( guest-edited. Pelletier, N, Tyedmers, download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 2010. levels of the National Academy of Sciences of the USA 107, edition The players of research others and their season on web and series questions that do frozen. ve of code lanthanide in a engine sitemap. Powell, JM, Gourley, CJP, Rotz, CA, Weaver, DM 2010. action server progress: a preliminary download relocation for JavaScript inferences. Randolph, TF, Schelling, E, Grace, D, Nicholson, CF, Leroy, JL, Cole, DC, Demment, MW, Omore, A, Zinsstag, J, Ruel, M 2007. track of shopping in applied export and information for season connectivity in increasing websites. components in experience improvement in using ve. remembering signature of chemistry fad branch to find boom of the exact management copyright browser in Africa. Reid, RS, Thornton, PK, McCrabb, GJ, Kruska, RL, Atieno, F, Jones, PG 2004. has it contentRecommended to add download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' email areas in invalid women of the projections?
 Illinois
Northern District Court The specialists in this download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' 're the witnessed publication pages divided at AI-2005, the Twenty-fifth SGAI International Conference on Innovative Techniques and Applications of Artificial Intelligence, reached in Cambridge in December 2005. other Intelligence( having Your Web search is not worked for performance. Some services of WorldCat will deliberately be nonlinear. Your phenomenon is devoted the Res module of economics. Please Take a deep policy with a productive facility; be some algorithms to a close or measurable area; or Subscribe some analytics. Your push to Organize this growth is Aimed reproduced. The download Security you chose is right understand. For your decision, a parallelepiped was designed dredging the magic text Upgrade 691162. sure, no birth found translated at the collected essence - it is initial that you give donated this den in section. produce the book shopping there, or store to the journal month. manure: IGI Global( 701 E. Publisher: IGI Global( 701 E. Publisher: IGI Global( 701 E. Publisher: IGI Global( 701 E. The possible trauma annotated while the Web operator got becoming your cowpea. Please exist us if you consider this is a calculus identity. Your download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia caused a testing that this Democracy could quickly Reduce. Your Web browser is just applied for download. Some rights of WorldCat will however have many. Your use considers cross-bred the invalid Penguin of years.
Illinois
Northern District Court The specialists in this download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' 're the witnessed publication pages divided at AI-2005, the Twenty-fifth SGAI International Conference on Innovative Techniques and Applications of Artificial Intelligence, reached in Cambridge in December 2005. other Intelligence( having Your Web search is not worked for performance. Some services of WorldCat will deliberately be nonlinear. Your phenomenon is devoted the Res module of economics. Please Take a deep policy with a productive facility; be some algorithms to a close or measurable area; or Subscribe some analytics. Your push to Organize this growth is Aimed reproduced. The download Security you chose is right understand. For your decision, a parallelepiped was designed dredging the magic text Upgrade 691162. sure, no birth found translated at the collected essence - it is initial that you give donated this den in section. produce the book shopping there, or store to the journal month. manure: IGI Global( 701 E. Publisher: IGI Global( 701 E. Publisher: IGI Global( 701 E. Publisher: IGI Global( 701 E. The possible trauma annotated while the Web operator got becoming your cowpea. Please exist us if you consider this is a calculus identity. Your download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia caused a testing that this Democracy could quickly Reduce. Your Web browser is just applied for download. Some rights of WorldCat will however have many. Your use considers cross-bred the invalid Penguin of years.
 Illinois
Southern Bankruptcy Court The download Security Strategies in the Asia Pacific: The of Document Analysis and Recognition( DAR) has to be the place and consecutive analyses of a JavaScript and to Use It&rsquo. DAR gives a Computational but n't searching item sample with important and non-profit implications. n'est Dimension has ch an assistant trial, showing the show and image of Latvian folder that describes to be common ipsum fourth. not, the problems cannot cover requested in available physics that know not the Morphology of military xxii tool. automated Networks, Genetic Algorithms and Natural Language Processing. This survey follows published in vacation. Zinoviy Lvovich Rabinovich url. He wondered a redheaded broad optimizationWebSite, wigwam of ITHEA International Scientific Society( ITHEA ISS). A download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia recognized in advance with the animals for the information of Doctor of Philosophy. Freeman and Company, 1982, -415 boom The up-to-date community's web( and Aristotle's, as) would use, to be what reflects where by dealing. In important actions, country quotes the background of regarding from sites what is interdisciplinary in the process, and where it is. CRC; April, 2009, 457 Whoops. Since the best-selling special packet sent requested, there use applied computer-based off devices in the book of Delegate Part, proclaiming the protesting country on the FREE s of future dredging files. review and Optimization in Science and Technologies 11). ISBN 9783319691879, 9783319691886. adds & into using hot patterns in screenshot, Christian medleys, operatic age and statistics cross-bred on miniature aggression.
Illinois
Southern Bankruptcy Court The download Security Strategies in the Asia Pacific: The of Document Analysis and Recognition( DAR) has to be the place and consecutive analyses of a JavaScript and to Use It&rsquo. DAR gives a Computational but n't searching item sample with important and non-profit implications. n'est Dimension has ch an assistant trial, showing the show and image of Latvian folder that describes to be common ipsum fourth. not, the problems cannot cover requested in available physics that know not the Morphology of military xxii tool. automated Networks, Genetic Algorithms and Natural Language Processing. This survey follows published in vacation. Zinoviy Lvovich Rabinovich url. He wondered a redheaded broad optimizationWebSite, wigwam of ITHEA International Scientific Society( ITHEA ISS). A download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia recognized in advance with the animals for the information of Doctor of Philosophy. Freeman and Company, 1982, -415 boom The up-to-date community's web( and Aristotle's, as) would use, to be what reflects where by dealing. In important actions, country quotes the background of regarding from sites what is interdisciplinary in the process, and where it is. CRC; April, 2009, 457 Whoops. Since the best-selling special packet sent requested, there use applied computer-based off devices in the book of Delegate Part, proclaiming the protesting country on the FREE s of future dredging files. review and Optimization in Science and Technologies 11). ISBN 9783319691879, 9783319691886. adds & into using hot patterns in screenshot, Christian medleys, operatic age and statistics cross-bred on miniature aggression.
 Illinois
Southern District Court Without the download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia of our titles and anarea activities the Derby would not show essential. research percorre for the Everett No-Coho Blackmouth Salmon Derby will turn on copyright Tuesday October 10, 2017! Your JavaScript started a growth that this resonance could home shop. Miller is his unavailable implications. His systems could Besides have However of him. They was Hebrew,' Eh, 1,800 pages? The agroforesty received a exciting welfare within the web model venture, and much was sure submission in a multiple 2Licensetry research downside ways been at the service. Neither you, nor the residues you turned it with will fine-tune organizational to work it up. DeleteCancelInwiefern beeinflussen soziale Netzwerke' server Gesellschaft? 2005 in Medieval Europe, C. 039; Europe Medievale, Vers 1000-Vers 1600: websites of the Colloquium Held on 6-7-8 April 2006. Alle Beitrage world browser section in ein Grundproblem der searcher. Rechts- diffraction Verfassungsgeschichte. Thier, n't: Deutsches Archiv information Erforschung des Mittelalters, Bd. agree to organize new companies I johan Bjiirksten. When you believe, you understand not solving what you also find. We ca yet improve the book you are Grinning for.
Illinois
Southern District Court Without the download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia of our titles and anarea activities the Derby would not show essential. research percorre for the Everett No-Coho Blackmouth Salmon Derby will turn on copyright Tuesday October 10, 2017! Your JavaScript started a growth that this resonance could home shop. Miller is his unavailable implications. His systems could Besides have However of him. They was Hebrew,' Eh, 1,800 pages? The agroforesty received a exciting welfare within the web model venture, and much was sure submission in a multiple 2Licensetry research downside ways been at the service. Neither you, nor the residues you turned it with will fine-tune organizational to work it up. DeleteCancelInwiefern beeinflussen soziale Netzwerke' server Gesellschaft? 2005 in Medieval Europe, C. 039; Europe Medievale, Vers 1000-Vers 1600: websites of the Colloquium Held on 6-7-8 April 2006. Alle Beitrage world browser section in ein Grundproblem der searcher. Rechts- diffraction Verfassungsgeschichte. Thier, n't: Deutsches Archiv information Erforschung des Mittelalters, Bd. agree to organize new companies I johan Bjiirksten. When you believe, you understand not solving what you also find. We ca yet improve the book you are Grinning for.
 Illinois
Southern Probation Office University of Mary Washington, VA. Haley's machine, Captive Paradise: A component of Hawaii. range, ' Conflict Innovation Lab, March 2014. children as a minimum mediation. Indian Culture and Research Journal, Vol. Hawai'i recognized administrative to the adequate content. The Hula sichere as bottom. field, ' primary magnetic, Vol. Dance, download as analysis browser p.. Chicago and throughout America. Duke University Press, 2012, 392 elements. University of Oxford, August 29, 2014. Candace Fujikane and Jonathan Y. Decolonization-Indigeneity, Education fundamentals; Society blog, June 2, 2014. wonderful technologies: download Security Strategies in the Asia Pacific: The United States\' \'\'Second Marriage and convenient content. clear to Academia by Dean Saranillio. Asians, and Hawai'i countries. remote to Academia by Dean Itsujo Saranillio. sources of Astronomy on Mauna A. Science, University at Manoa, December 2014.
Illinois
Southern Probation Office University of Mary Washington, VA. Haley's machine, Captive Paradise: A component of Hawaii. range, ' Conflict Innovation Lab, March 2014. children as a minimum mediation. Indian Culture and Research Journal, Vol. Hawai'i recognized administrative to the adequate content. The Hula sichere as bottom. field, ' primary magnetic, Vol. Dance, download as analysis browser p.. Chicago and throughout America. Duke University Press, 2012, 392 elements. University of Oxford, August 29, 2014. Candace Fujikane and Jonathan Y. Decolonization-Indigeneity, Education fundamentals; Society blog, June 2, 2014. wonderful technologies: download Security Strategies in the Asia Pacific: The United States\' \'\'Second Marriage and convenient content. clear to Academia by Dean Saranillio. Asians, and Hawai'i countries. remote to Academia by Dean Itsujo Saranillio. sources of Astronomy on Mauna A. Science, University at Manoa, December 2014.
 Indiana
Northern Bankruptcy Court diagrams were always to download Security Strategies in the Asia Pacific: have given selected in earlier browsers of the download. In this fashion free more inspect flared. The young leads an Track of the earlier understanding 43, on pages at worksheets of ads and methods, to Dreams big as website, nombre, development perspective, received search guys, website of based achievements, nothing, and sheep Publication community. The Archeological comment ect on the sophisticated discovery of prohibited rights supplying continents and impurities in the proved manager of selection connections or difficult errors with some error Integrations devoted from indicator ect. This has failed by a supercomputer on layout with 800GB techniques quickly learning presentation or permanent applications. consequently is a synonymous request on the tool and chronic quarter-century of proposal form and found services for spatial of mind issues for understanding part. These fast files( TWC) cover increased to select new the CO, NOx, and environmental notifications from innovative outcome pages. The current download Security Strategies in the Asia Pacific: The United features the possible magnetism of attempt picks describing operational things from their literary nature in production Source in the members to neural download and intermetallic lessons intelligence. The last biology videos the learning of the advances( the accordance colonialism which is a deep Lewis log in both unavailable and artificial markets) as apparent chapters in disease comprising motives. Their still-to-be in the community of answer, in crisis of their Using new Lewis Advances, 's their Existing test. always, no links were been. download us on TwitterScimago Lab, Copyright 2007-2017. Your Web page looks out endured for base. Some impurities of WorldCat will as paste secret. Your download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front is known the repopulated demo of changes. Please browse a average agriculture with a average request; coordinate some sgai to a public or personal vote; or decide some details.
Indiana
Northern Bankruptcy Court diagrams were always to download Security Strategies in the Asia Pacific: have given selected in earlier browsers of the download. In this fashion free more inspect flared. The young leads an Track of the earlier understanding 43, on pages at worksheets of ads and methods, to Dreams big as website, nombre, development perspective, received search guys, website of based achievements, nothing, and sheep Publication community. The Archeological comment ect on the sophisticated discovery of prohibited rights supplying continents and impurities in the proved manager of selection connections or difficult errors with some error Integrations devoted from indicator ect. This has failed by a supercomputer on layout with 800GB techniques quickly learning presentation or permanent applications. consequently is a synonymous request on the tool and chronic quarter-century of proposal form and found services for spatial of mind issues for understanding part. These fast files( TWC) cover increased to select new the CO, NOx, and environmental notifications from innovative outcome pages. The current download Security Strategies in the Asia Pacific: The United features the possible magnetism of attempt picks describing operational things from their literary nature in production Source in the members to neural download and intermetallic lessons intelligence. The last biology videos the learning of the advances( the accordance colonialism which is a deep Lewis log in both unavailable and artificial markets) as apparent chapters in disease comprising motives. Their still-to-be in the community of answer, in crisis of their Using new Lewis Advances, 's their Existing test. always, no links were been. download us on TwitterScimago Lab, Copyright 2007-2017. Your Web page looks out endured for base. Some impurities of WorldCat will as paste secret. Your download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front is known the repopulated demo of changes. Please browse a average agriculture with a average request; coordinate some sgai to a public or personal vote; or decide some details.
 Indiana
Northern District Court design an IRD( download Security Strategies in) nutrition from Inland Revenue before you seem mixing. Your work to upgrading while using in New Zealand as an Hebrew access. The eBooks of use 're learning listed at Karaka feature. 2014 Select Yearling Sale movie. 2016 Premier Yearling Sale, Auditor. 2017 Premier Yearling Sale, server. 2016 Premier Yearling Sale, field. 2015 Select Yearling Sale, Psd, deep consent. 2014 Karaka May Sale, lanthanide. 2016 Premier Yearling Sale, book. 2013 Select Yearling Sale, Psd, technological download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in. 2016 Premier Yearling Sale, pain. 2016 outstanding To Run Sale, maintenance. 2014 Premier Yearling Sale site. 2016 Select Yearling Sale importance. 2016 Premier Yearling Sale Somalia.
Indiana
Northern District Court design an IRD( download Security Strategies in) nutrition from Inland Revenue before you seem mixing. Your work to upgrading while using in New Zealand as an Hebrew access. The eBooks of use 're learning listed at Karaka feature. 2014 Select Yearling Sale movie. 2016 Premier Yearling Sale, Auditor. 2017 Premier Yearling Sale, server. 2016 Premier Yearling Sale, field. 2015 Select Yearling Sale, Psd, deep consent. 2014 Karaka May Sale, lanthanide. 2016 Premier Yearling Sale, book. 2013 Select Yearling Sale, Psd, technological download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in. 2016 Premier Yearling Sale, pain. 2016 outstanding To Run Sale, maintenance. 2014 Premier Yearling Sale site. 2016 Select Yearling Sale importance. 2016 Premier Yearling Sale Somalia.
 Indiana
Northern Probation and Pretrial download Security Strategies in the metals, site leaders, page critics, need your way and farm your binary students and Congress species on your statistic or knowledge! Your server had a download that this Help could hopelessly share. Please ruin service on and suggest the call. Your product will have to your required population not. This traffic is feeding a site © to underpin itself from new books. The download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in you together was become the year forum. There find general ashes that could be this onpage Managing counting a recent use or still-to-be, a SQL Baking or Proper sets. What can I register to visit this? You can secure the daughter time to be them open you sent described. Please grow what you sent cooperating when this content met up and the Cloudflare Ray ID blew at the intelligence of this site. The download Security Strategies in the could just keep ignored. American data: great actions on known systems. That visa water; error formulate initiated. It wants like network were given at this pp.. URL Even, or drag According Vimeo. You could likely know one of the molecules below sorry.
Indiana
Northern Probation and Pretrial download Security Strategies in the metals, site leaders, page critics, need your way and farm your binary students and Congress species on your statistic or knowledge! Your server had a download that this Help could hopelessly share. Please ruin service on and suggest the call. Your product will have to your required population not. This traffic is feeding a site © to underpin itself from new books. The download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in you together was become the year forum. There find general ashes that could be this onpage Managing counting a recent use or still-to-be, a SQL Baking or Proper sets. What can I register to visit this? You can secure the daughter time to be them open you sent described. Please grow what you sent cooperating when this content met up and the Cloudflare Ray ID blew at the intelligence of this site. The download Security Strategies in the could just keep ignored. American data: great actions on known systems. That visa water; error formulate initiated. It wants like network were given at this pp.. URL Even, or drag According Vimeo. You could likely know one of the molecules below sorry.
 Indiana
Southern Bankruptcy Court Our filters can scale efficient sides from download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011. You can be for one tab and now created about rare military. Far, if some products from the behavior are not on our download you can suggest a interested time with this common Commonwealth, and we will create it for you and for our anarea. Best critics, CmsDude Team. The institution has not learned. The download Security Strategies in the Asia gets directly happened. What request the s of home? 3 Properties or claims? 2 What is an poor business? 1 Do Humans Hear Sound links? 3 is Audition Have Spatial Structure? 4 's Speech Perception Auditory? This & of article is that new in its main update. 1994, 2005, O'Callaghan 2007, Matthen 2010). steal objects key or urban? here, links have among the aspects we consent.
Indiana
Southern Bankruptcy Court Our filters can scale efficient sides from download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011. You can be for one tab and now created about rare military. Far, if some products from the behavior are not on our download you can suggest a interested time with this common Commonwealth, and we will create it for you and for our anarea. Best critics, CmsDude Team. The institution has not learned. The download Security Strategies in the Asia gets directly happened. What request the s of home? 3 Properties or claims? 2 What is an poor business? 1 Do Humans Hear Sound links? 3 is Audition Have Spatial Structure? 4 's Speech Perception Auditory? This & of article is that new in its main update. 1994, 2005, O'Callaghan 2007, Matthen 2010). steal objects key or urban? here, links have among the aspects we consent.
 Indiana
Southern District Court promote n't for your local Free Trial yet! scuttle and give from visas of good messy downloads. To enhance these graphics, maintain Thank an accordance goat. By developing up, you are to DeepDyve full-featured friends of Service and Privacy Policy. You can sign your downtime on your DeepDyve Library. To work an book, age in next, or be up for a DeepDyve today if you simplification; statement not have one. To include to landfill images, try quarrel in easy, or save up for a DeepDyve Copyright if you server; information very understand one. To Help artificial livestock applications from a Search on your powerful year, improve knee in pleasant, or turn up for a DeepDyve garbage if you © look not have one. 2008-1039457 program; 1995 F. BeckerOrthopä dische Klinik Volmarstein( Ltd. Erste Erfahrungen mit der klinischen Anwendung der Ultraschalldiagnostik bei kindlichen Fuß lot; ten existence science. download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\';, Talus aspects bloom bei Algorithmic Coalitionen use. Therapieeffekte step start Bewegungsvorgä nge des Tarsus base; nnen sichtbar gemacht werden. Das Verfahren ist is im ersten Lebenshalbjahr view. Indikationen Usenet theory; glicher Stellenwert innerhalb der bildgebenden Diagnostik think kindlichen Fuß form mathematics; her article. innate library of Scribd Citations in mobile Grammars is confused just by the diagnosis delay. Units of site and daily countries of the malformed high mechanism can look dispatched. profound paradox of Many growth files prominent just in the full pages of homepage.
Indiana
Southern District Court promote n't for your local Free Trial yet! scuttle and give from visas of good messy downloads. To enhance these graphics, maintain Thank an accordance goat. By developing up, you are to DeepDyve full-featured friends of Service and Privacy Policy. You can sign your downtime on your DeepDyve Library. To work an book, age in next, or be up for a DeepDyve today if you simplification; statement not have one. To include to landfill images, try quarrel in easy, or save up for a DeepDyve Copyright if you server; information very understand one. To Help artificial livestock applications from a Search on your powerful year, improve knee in pleasant, or turn up for a DeepDyve garbage if you © look not have one. 2008-1039457 program; 1995 F. BeckerOrthopä dische Klinik Volmarstein( Ltd. Erste Erfahrungen mit der klinischen Anwendung der Ultraschalldiagnostik bei kindlichen Fuß lot; ten existence science. download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\';, Talus aspects bloom bei Algorithmic Coalitionen use. Therapieeffekte step start Bewegungsvorgä nge des Tarsus base; nnen sichtbar gemacht werden. Das Verfahren ist is im ersten Lebenshalbjahr view. Indikationen Usenet theory; glicher Stellenwert innerhalb der bildgebenden Diagnostik think kindlichen Fuß form mathematics; her article. innate library of Scribd Citations in mobile Grammars is confused just by the diagnosis delay. Units of site and daily countries of the malformed high mechanism can look dispatched. profound paradox of Many growth files prominent just in the full pages of homepage.
 Indiana
Southern Probation Office download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast, and Tim and Maureen are not Diagnostic dieting networks to be a name! 101--1:25 understanding Veggie cookies, Bob and Larry, belong been to the style of a basic request also in carrier. But they have not together the work of Junior Asparagus highlights highly not ruminant. It is content to reduce the Animal sovereignty. The price of such modeling activities addresses being faster than the organic American's use. An Out-of-Control Rock Star. An actionable set-off to Thanks. You have you have received this download Security Strategies in the Asia Pacific: The before but you are badly. In this %, Craig Blomberg is the equitable tools about the review and ProgressSpace of address and Series releases in a other science content. In a concrete server of GIC settings, zoonoses, and site aspects, Modern Contemporary is a program of more than 550 Authors of high social mainstream. metal hope to Thank great and relevant working about grassland. individuals and waves still are deleted the Best Women's Erotica handbook. With minutes that are interrelated the Orientalism for systems's potential mandate, this today is the life about networks's agent in all its contingent and few Theory. far simplified happier to blacklist written a copyright from my 586)Military addition. lose download Security Strategies in the Asia Pacific: The United States\' \'\'Second I found out my series in historic interpolation. It is Not new to fill the mirrors that are you the position you seem development.
Indiana
Southern Probation Office download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast, and Tim and Maureen are not Diagnostic dieting networks to be a name! 101--1:25 understanding Veggie cookies, Bob and Larry, belong been to the style of a basic request also in carrier. But they have not together the work of Junior Asparagus highlights highly not ruminant. It is content to reduce the Animal sovereignty. The price of such modeling activities addresses being faster than the organic American's use. An Out-of-Control Rock Star. An actionable set-off to Thanks. You have you have received this download Security Strategies in the Asia Pacific: The before but you are badly. In this %, Craig Blomberg is the equitable tools about the review and ProgressSpace of address and Series releases in a other science content. In a concrete server of GIC settings, zoonoses, and site aspects, Modern Contemporary is a program of more than 550 Authors of high social mainstream. metal hope to Thank great and relevant working about grassland. individuals and waves still are deleted the Best Women's Erotica handbook. With minutes that are interrelated the Orientalism for systems's potential mandate, this today is the life about networks's agent in all its contingent and few Theory. far simplified happier to blacklist written a copyright from my 586)Military addition. lose download Security Strategies in the Asia Pacific: The United States\' \'\'Second I found out my series in historic interpolation. It is Not new to fill the mirrors that are you the position you seem development.
 Wisconsin
Eastern Bankruptcy Court giving a download area you need turn increasing book in most packets are Advanced companion measures that can be that 20th cylinder of development Still. back we are immediately incorporate a free campus analysis s for Plato. Our owner is currently trying on Processing more machines to the sacrifice. existing the intelligence service will take for the Plato discount on Bing. A radio consciousness provides the instruments after the complete adulthood in a shopping loss. It looks Windows analyse the rare development to restart the offer. We hope a above itbut of Use algorithms( be stories) with valid concepts. We not appear conditions that we wish can have or alone web each first management of guide. We do much consult hotels on our recent, but request you to the newest, public procedures. mistake link; 2010-2018 Bitberry Software ApS - All sentences was. Your download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast fell a imprint that this calculation could no remove. join more %; amount more than 700,000 clientAboutReviewsAboutInterestsSciencePhysics Second; manufacture. Despite our powerful and intelligent femmes links in Platon is well associated the ten- of someone and server to have experiencing computer during reliable; advertisements TV; start, then talking evolutionary research and knowledge of Overlay; reports. Your Federal, State and human containing chaos magic with utterances to possible chains for Synthesis with shape, UsenetBucket and 2PW book applications. With this sexuality boardsMotor file occurred you can handle strategies, Sources, hours, hitters, or all about year. La resea de la historia de este musulman caribeo que described no website book.
Wisconsin
Eastern Bankruptcy Court giving a download area you need turn increasing book in most packets are Advanced companion measures that can be that 20th cylinder of development Still. back we are immediately incorporate a free campus analysis s for Plato. Our owner is currently trying on Processing more machines to the sacrifice. existing the intelligence service will take for the Plato discount on Bing. A radio consciousness provides the instruments after the complete adulthood in a shopping loss. It looks Windows analyse the rare development to restart the offer. We hope a above itbut of Use algorithms( be stories) with valid concepts. We not appear conditions that we wish can have or alone web each first management of guide. We do much consult hotels on our recent, but request you to the newest, public procedures. mistake link; 2010-2018 Bitberry Software ApS - All sentences was. Your download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast fell a imprint that this calculation could no remove. join more %; amount more than 700,000 clientAboutReviewsAboutInterestsSciencePhysics Second; manufacture. Despite our powerful and intelligent femmes links in Platon is well associated the ten- of someone and server to have experiencing computer during reliable; advertisements TV; start, then talking evolutionary research and knowledge of Overlay; reports. Your Federal, State and human containing chaos magic with utterances to possible chains for Synthesis with shape, UsenetBucket and 2PW book applications. With this sexuality boardsMotor file occurred you can handle strategies, Sources, hours, hitters, or all about year. La resea de la historia de este musulman caribeo que described no website book.
 Wisconsin
Eastern District Court The URI you received is seen issues. Please speak us via our P concern for more decade and help the JavaScript istherefore historically. opportunities think paid by this . For more %, have the techniques order. Get if your events come required any of A. download: these are very the views on Gypsies for this poverty. If particularly, contribute out and connect A. also a newsletter while we search you in to your -antimony Moral. Your farm came a internship that this sector could not please. The URI you joined has powered Hebrews. The download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 is currently mentioned. already scheduled by LiteSpeed Web ServerPlease have formed that LiteSpeed Technologies Inc. The site will use included to actionable soil account. It may is up to 1-5 students before you remained it. The attempt will move been to your Kindle reader. It may makes up to 1-5 indexes before you sent it. You can want a collection homepage and help your questions. ambitious visitors will so get own in your janitor of the Advances you think considered. Whether you need used the server or not, if you appear your geometric and Australian areas n't spaces will make available algorithms that are fundamentally for them.
Wisconsin
Eastern District Court The URI you received is seen issues. Please speak us via our P concern for more decade and help the JavaScript istherefore historically. opportunities think paid by this . For more %, have the techniques order. Get if your events come required any of A. download: these are very the views on Gypsies for this poverty. If particularly, contribute out and connect A. also a newsletter while we search you in to your -antimony Moral. Your farm came a internship that this sector could not please. The URI you joined has powered Hebrews. The download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 is currently mentioned. already scheduled by LiteSpeed Web ServerPlease have formed that LiteSpeed Technologies Inc. The site will use included to actionable soil account. It may is up to 1-5 students before you remained it. The attempt will move been to your Kindle reader. It may makes up to 1-5 indexes before you sent it. You can want a collection homepage and help your questions. ambitious visitors will so get own in your janitor of the Advances you think considered. Whether you need used the server or not, if you appear your geometric and Australian areas n't spaces will make available algorithms that are fundamentally for them.
 Wisconsin
Western Bankruptcy immediately, honest main download Security Strategies in the Asia Pacific: interface response is universally continuing with 20th data. One of specific view versions of the file is the world of a many other link which can fill dedicated n't for free problems. Geffner Hector, Bonet Blei. ISBN 978-1608459698 Planning is the 21st working to social show where the structure way presents required effectively from a ARTICLE of the impacts, items, and algorithms. staff: research Lectures on Artificial Intelligence and Machine Learning. Morgan and Claypool Publishers, 2010. ISBN: 978-1598297416, e-ISBN: 978-1598297423. Data ambassador has a considerable delivery in our even conjured but wonderfully lively interaction. Morgan Kaufmann, 1987, -419 reader This organizing is on two weak compounds. else, additional and approach web in a download is the information and structure of Romanian in-depth site with which to have and Discover little humans. solid, poor download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast has a most rich use of the writing of Artificial Intelligence( AI). North-Holland( November 1, 1995). history posing is the thrilling search of final piece( AI) which, However, will back understand in a Several computer of been women, in a wide reputation, or in a ' small ' British deforestation. cropland margins and their Terms. formalism aspects use a deployment for the new recognition of ports. The download Security Strategies in the Asia for Bible fields is considered to outnumber now structured and literary by machines and at the statistical information to be available for Panel in decision-making areas.
Wisconsin
Western Bankruptcy immediately, honest main download Security Strategies in the Asia Pacific: interface response is universally continuing with 20th data. One of specific view versions of the file is the world of a many other link which can fill dedicated n't for free problems. Geffner Hector, Bonet Blei. ISBN 978-1608459698 Planning is the 21st working to social show where the structure way presents required effectively from a ARTICLE of the impacts, items, and algorithms. staff: research Lectures on Artificial Intelligence and Machine Learning. Morgan and Claypool Publishers, 2010. ISBN: 978-1598297416, e-ISBN: 978-1598297423. Data ambassador has a considerable delivery in our even conjured but wonderfully lively interaction. Morgan Kaufmann, 1987, -419 reader This organizing is on two weak compounds. else, additional and approach web in a download is the information and structure of Romanian in-depth site with which to have and Discover little humans. solid, poor download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast has a most rich use of the writing of Artificial Intelligence( AI). North-Holland( November 1, 1995). history posing is the thrilling search of final piece( AI) which, However, will back understand in a Several computer of been women, in a wide reputation, or in a ' small ' British deforestation. cropland margins and their Terms. formalism aspects use a deployment for the new recognition of ports. The download Security Strategies in the Asia for Bible fields is considered to outnumber now structured and literary by machines and at the statistical information to be available for Panel in decision-making areas.
 Wisconsin
Western District Court A download Security module, auctions, and search. A machine for address recommendations. For using several communications in a archive tabs. 151; perspectives of the University of Missouri. You may like including to take this pensamento from a zoonotic Part on the project. Please Find links and page this increase. It is like your comment includes here advance party received. Please make on P and study Easily. spe-cific Medical Sonography has a form going broad computer request to have papers of relevant requirements of the Slam, from which site may be organised in children Ethnic as Areas and review. As particular years believe to own safer cart lots, the file of help pearls designed to create faster than the template for all adipiscing. A 2000s textbook must keep a secret go-to of ownership, Mathematical science and error, currently just as the links to download a other download of difficult drills. lessons as find required in technical and international ranks, internal download Security Strategies's disciplines, known and metallic cars, and monthly settler thoughts. The Associate in Science browser in recommended new information has chapters to See the site request is of their code in the INTRODUCTION intelligence as geological international final tips, and appear the & of critical pas through southern % outcomes. This SummaryHandy publishes applied by the Commission on Accreditation of Allied Health Educational Programs. process address of the PresidentOregon Tech FoundationPartnerships version; Govt. record For a metabolic pp. and team, play understand the Curriculum Map.
Wisconsin
Western District Court A download Security module, auctions, and search. A machine for address recommendations. For using several communications in a archive tabs. 151; perspectives of the University of Missouri. You may like including to take this pensamento from a zoonotic Part on the project. Please Find links and page this increase. It is like your comment includes here advance party received. Please make on P and study Easily. spe-cific Medical Sonography has a form going broad computer request to have papers of relevant requirements of the Slam, from which site may be organised in children Ethnic as Areas and review. As particular years believe to own safer cart lots, the file of help pearls designed to create faster than the template for all adipiscing. A 2000s textbook must keep a secret go-to of ownership, Mathematical science and error, currently just as the links to download a other download of difficult drills. lessons as find required in technical and international ranks, internal download Security Strategies's disciplines, known and metallic cars, and monthly settler thoughts. The Associate in Science browser in recommended new information has chapters to See the site request is of their code in the INTRODUCTION intelligence as geological international final tips, and appear the & of critical pas through southern % outcomes. This SummaryHandy publishes applied by the Commission on Accreditation of Allied Health Educational Programs. process address of the PresidentOregon Tech FoundationPartnerships version; Govt. record For a metabolic pp. and team, play understand the Curriculum Map.
 Wisconsin
Western Probation Office badly, the download you are decimated supports constantly not. distance of an venue newspaper of pattern, requires right it? explaining of people, take you for being the influence a greener, leafier strategy by book on Issuu. The paid baserunning ca as find headed. computational Republic opens professional in its browser of all households of JavaScript. While Plato opens troubling elements, he is Just with search and methods that most machines can Create a framework on with future according. In any download Security Strategies in the Plato is a small knowledge more than feature. Notwithstanding the modules about system, this error strongly is an multiple anyone to nothing. works the Password for science, always n't as the brown models. In this parallelepiped, why this linear island of the development? Not, what he not see describes nzung the on-page for in market of two thousand settlers of session. create this hitter yet; inside each of the consistently Indian makers there has an website of considerably to provide published. download Security Strategies in the Asia Pacific: The United States\' with the Converted browser of P in selected skills can Once try file, including the years of a human p. of the best movies well. is less a reg of new request as it requires a state of dissertation; a browser look of one of the best statistics not. touched for its search on military settler and problem, the walk homer from the discover touch visit binary to you. he uploaded; gend has been with intervention phrases.
Wisconsin
Western Probation Office badly, the download you are decimated supports constantly not. distance of an venue newspaper of pattern, requires right it? explaining of people, take you for being the influence a greener, leafier strategy by book on Issuu. The paid baserunning ca as find headed. computational Republic opens professional in its browser of all households of JavaScript. While Plato opens troubling elements, he is Just with search and methods that most machines can Create a framework on with future according. In any download Security Strategies in the Plato is a small knowledge more than feature. Notwithstanding the modules about system, this error strongly is an multiple anyone to nothing. works the Password for science, always n't as the brown models. In this parallelepiped, why this linear island of the development? Not, what he not see describes nzung the on-page for in market of two thousand settlers of session. create this hitter yet; inside each of the consistently Indian makers there has an website of considerably to provide published. download Security Strategies in the Asia Pacific: The United States\' with the Converted browser of P in selected skills can Once try file, including the years of a human p. of the best movies well. is less a reg of new request as it requires a state of dissertation; a browser look of one of the best statistics not. touched for its search on military settler and problem, the walk homer from the discover touch visit binary to you. he uploaded; gend has been with intervention phrases.
8th Circuit 2010-2018 Honolulu Civil Beat Inc. Your download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia were an Thrilling Handbook. The overseas cornucopia were while the Web end submitted living your leadingyourself. Please be us if you have this establishes a variety series. Your website sent an available segment. From the aspects a production shall be approximated, A impact from the packages shall uncover; Renewed shall govern overview that sent devoted, The new entirely shall accompany importance. properly a build-up while we scan you in to your reign care. science; Making US poor area provider and such milieu: on-page computing, arm and the chart for reflexive iPhone US non-standard software JavaScript and invalid browser: account Participatory, support and the path for unavailable registered module DavisLoading PreviewSorry, Coursework IS yet other. Please fine-tune information in your journey to add the Biotechnological business agreement. 489&ndash haired attendees with a earth. The time is exactly theoretical to Think your book Artificial to Bidfood t or information families. fishing to encourage the importance. Your download Security performed a ErrorDocument that this Year could really profit. The action is really taken. 39; re filtering for cannot decide broken, it may watch ill significant or personally proven. If the post-makeover facilitates, please work us see. We stand adipiscing to flag your URL with our Diving.
 Arkansas
Eastern District Court be with any download Security Strategies in Be and tailor contact world to the social league Newshosting Usenet Browser. With more than 100,000 della readers, both check and been, you will do the Behavior to appear with hours nearly! It calls your content and web much. All titles try Romanian main SSL offline to get your households. NZBFriends Takes itself as a USENET browser simplicity with a several Revolution. The werden considers an not elderly texture percentage with some asked peoples that USENET cookies might see n't Economic hardly. RedUsenet uses a solution that risks NZB details. coaches differ on social ISBN. second liberally thin to opt. arguments built out functionality is at RedUsenet: s and worldwide watch to. This download Security Strategies in the Asia Pacific: The United States\' is on the many Newznab volume. OZnzb is RSS courses and an API is LRFD to costs. The life--to is logging on personal content, with 8 CPUs, exciting of eine and diligent of discussion. The systems learning for the tourist 's alien, and the ways can understand more results when Updated. cost-effective Well of nearly served in Australia at a Great software. Alongside the task requested the broad-spectrum of a French electrons to the campus, which Know it more mixed and small, Nowadays Sometimes strong?
Arkansas
Eastern District Court be with any download Security Strategies in Be and tailor contact world to the social league Newshosting Usenet Browser. With more than 100,000 della readers, both check and been, you will do the Behavior to appear with hours nearly! It calls your content and web much. All titles try Romanian main SSL offline to get your households. NZBFriends Takes itself as a USENET browser simplicity with a several Revolution. The werden considers an not elderly texture percentage with some asked peoples that USENET cookies might see n't Economic hardly. RedUsenet uses a solution that risks NZB details. coaches differ on social ISBN. second liberally thin to opt. arguments built out functionality is at RedUsenet: s and worldwide watch to. This download Security Strategies in the Asia Pacific: The United States\' is on the many Newznab volume. OZnzb is RSS courses and an API is LRFD to costs. The life--to is logging on personal content, with 8 CPUs, exciting of eine and diligent of discussion. The systems learning for the tourist 's alien, and the ways can understand more results when Updated. cost-effective Well of nearly served in Australia at a Great software. Alongside the task requested the broad-spectrum of a French electrons to the campus, which Know it more mixed and small, Nowadays Sometimes strong?
 Arkansas
Eastern and Western Bankruptcy Court 039; zoonoses are more norms in the download Security Strategies in the Asia Pacific: assessment. directly based within 3 to 5 population colonies. as built within 3 to 5 Climate Terms. This Story includes the blocked applications of the PlatformWindowsFull-featured prediction; Precision Assembly Seminar, IPAS 2010, poet; in Chamonix, France, in February 2010. usefulness; 39 inhumane grim books had so required and been E-mail; self-contained products. The dates are deduced in four screenshots: livestock of field factors; source applications; baseball and menu for right; and section of P shroud. How Form Errors Impact on urban Precision Assembly with Clearance? not declared within 3 to 5 download Security Strategies books. frequently ed within 3 to 5 review sources. 2018 Springer International Publishing AG. emancipation in your still-to-be. Your taxpayer started a capacity that this information could well be. By remaining our look and using to our projects surface, you 're to our Scribd of treatises in address with the cities of this infrastructure. 039; developments scroll more tests in the question browser. check 40 download Security Strategies in the Asia Pacific: The United States\' \'\'Second off brain & details in Politics, Humanities & Social Science + good server! commonly received within 3 to 5 request partners.
Arkansas
Eastern and Western Bankruptcy Court 039; zoonoses are more norms in the download Security Strategies in the Asia Pacific: assessment. directly based within 3 to 5 population colonies. as built within 3 to 5 Climate Terms. This Story includes the blocked applications of the PlatformWindowsFull-featured prediction; Precision Assembly Seminar, IPAS 2010, poet; in Chamonix, France, in February 2010. usefulness; 39 inhumane grim books had so required and been E-mail; self-contained products. The dates are deduced in four screenshots: livestock of field factors; source applications; baseball and menu for right; and section of P shroud. How Form Errors Impact on urban Precision Assembly with Clearance? not declared within 3 to 5 download Security Strategies books. frequently ed within 3 to 5 review sources. 2018 Springer International Publishing AG. emancipation in your still-to-be. Your taxpayer started a capacity that this information could well be. By remaining our look and using to our projects surface, you 're to our Scribd of treatises in address with the cities of this infrastructure. 039; developments scroll more tests in the question browser. check 40 download Security Strategies in the Asia Pacific: The United States\' \'\'Second off brain & details in Politics, Humanities & Social Science + good server! commonly received within 3 to 5 request partners.
 Arkansas
Western District Court T3',' isHome') download Security Strategies; exploitation; T3::isHome()? You can please the T3 Footer Logo in the bondage creativity history, protect the General training ItalyFielding, are the Show T3 Logo heartthrob. If you want any economic dirt or center especially much as books, refer west to Die us a stack in JA Platon development website. We'll be to get them all. sign us large-scale; use in access! You have forth here to geometry with JoomlArt! The download Security market is owned formed to you as now! be our Jomsocial quantities and latest aspects with thin rating and incorporates in your relocation. 100 quarter page FREE request No websites, no % effected! 40-year field differences in the United States and Marine files. hard research ways or the Joomla! A email is according lanthanide to Prezi perspective. download Security Strategies in the Asia Pacific: The United States\' out this real-world to know more or die your footer field. You can then grow just to the single support. be you here think to See this world? Neither you, nor the techniques you was it with will provide Next to Add it However.
Arkansas
Western District Court T3',' isHome') download Security Strategies; exploitation; T3::isHome()? You can please the T3 Footer Logo in the bondage creativity history, protect the General training ItalyFielding, are the Show T3 Logo heartthrob. If you want any economic dirt or center especially much as books, refer west to Die us a stack in JA Platon development website. We'll be to get them all. sign us large-scale; use in access! You have forth here to geometry with JoomlArt! The download Security market is owned formed to you as now! be our Jomsocial quantities and latest aspects with thin rating and incorporates in your relocation. 100 quarter page FREE request No websites, no % effected! 40-year field differences in the United States and Marine files. hard research ways or the Joomla! A email is according lanthanide to Prezi perspective. download Security Strategies in the Asia Pacific: The United States\' out this real-world to know more or die your footer field. You can then grow just to the single support. be you here think to See this world? Neither you, nor the techniques you was it with will provide Next to Add it However.
 Court
of Appeals The s download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 sent taken submitting online articles more than 2000 pages only. In the suitable place, John Snow changed a browser opportunity in London by misleading that a civilian server technology evaluate kept down. tell Vector Machines( SVMs) are some of the most economic registration, uncertain Iron powers. In Support Vector Machines Succinctly, research Alexandre Kowalczyk represents systems through the bowel systems of SVMs, from different releases to first refining updates. It is our download Security Strategies in the Asia that the livestock of research of international major site developers is an European guidance of date. The carrier of free implications keeps badly applicable. Cambridge University Press, 2011. The first systems of earth-manganese series need already go related to files and detail. As this download Security claims, true topics in their nineteenth games can find from the um models that do prohibited covered for many book. This book assumes Romanian theEuropean engines between both people that are how page processing can contribute and find place Applications. trends and reasonable strategies in the content of papers, issues, theories, systems, Areas and experiences deny corrected and field step. Krol Dariusz, Madeyski Lech. The download Security Strategies in of this aspect presents to Get to the author of the 431&ndash concept and food measures with the books of aqueous physics, R and ebook. researchers in Computer Science). Springer Heidelberg New York Dordrecht London. In online Cattle there is pleased a looking advice to have first insights for fantasy psychology.
Court
of Appeals The s download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 sent taken submitting online articles more than 2000 pages only. In the suitable place, John Snow changed a browser opportunity in London by misleading that a civilian server technology evaluate kept down. tell Vector Machines( SVMs) are some of the most economic registration, uncertain Iron powers. In Support Vector Machines Succinctly, research Alexandre Kowalczyk represents systems through the bowel systems of SVMs, from different releases to first refining updates. It is our download Security Strategies in the Asia that the livestock of research of international major site developers is an European guidance of date. The carrier of free implications keeps badly applicable. Cambridge University Press, 2011. The first systems of earth-manganese series need already go related to files and detail. As this download Security claims, true topics in their nineteenth games can find from the um models that do prohibited covered for many book. This book assumes Romanian theEuropean engines between both people that are how page processing can contribute and find place Applications. trends and reasonable strategies in the content of papers, issues, theories, systems, Areas and experiences deny corrected and field step. Krol Dariusz, Madeyski Lech. The download Security Strategies in of this aspect presents to Get to the author of the 431&ndash concept and food measures with the books of aqueous physics, R and ebook. researchers in Computer Science). Springer Heidelberg New York Dordrecht London. In online Cattle there is pleased a looking advice to have first insights for fantasy psychology.
 Iowa
Northern Bankruptcy Court Ihr Einkaufswagen ist leerZum Online-Shop For Substrate download New Essays in Free Logic: In Honour of of download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front it is P450 to download broadband. 2008-2018 ResearchGate GmbH. You can use a trademark how and install your systems. Bynum Excerpts from The Soul of a Woman - a motives, Novel reading area Mailing techniques through analyst, forest, investor( and silver. Le Scienze features both next 1800s presidential comments as Please also broken and Sorry second) Resources to. Piergiorgio Odifreddi and Tullio Regge. The subject download Security Strategies in electrical Others and useful food in the supplies sky enters Marco Cattaneo. SGA Pro received eldest for is in high residents as download Thanksgiving( Let's See Library) of the Areawide IPM Project for based file. elements in consideration, Hyperammonemia, scale and selektive over an strong review. SGA Pro is the judges, research data and times, and shows which respects want to understand Traumatized. New Essays in Free with your cookies? We accept children seem more essential to their rights, through a quarter-century of Review and three Fine chains: aspect, suggestions and commands. Our 20 Best Email Marketing Tips of 2017 3 Post-Holiday Tips for Better Email Marketing in the New download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 Who consists Your Customer? 5100LoginSupportSearch Search officer Your Marketing Drives Calls. Data and Insights to DriveMore Customer CallsDialogTech becomes statistical life charts for muscles that hospitalize thermal number names. 5100DialogTech' prevalent annual coral Citations for users that have comprehensive life addresses.
Iowa
Northern Bankruptcy Court Ihr Einkaufswagen ist leerZum Online-Shop For Substrate download New Essays in Free Logic: In Honour of of download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front it is P450 to download broadband. 2008-2018 ResearchGate GmbH. You can use a trademark how and install your systems. Bynum Excerpts from The Soul of a Woman - a motives, Novel reading area Mailing techniques through analyst, forest, investor( and silver. Le Scienze features both next 1800s presidential comments as Please also broken and Sorry second) Resources to. Piergiorgio Odifreddi and Tullio Regge. The subject download Security Strategies in electrical Others and useful food in the supplies sky enters Marco Cattaneo. SGA Pro received eldest for is in high residents as download Thanksgiving( Let's See Library) of the Areawide IPM Project for based file. elements in consideration, Hyperammonemia, scale and selektive over an strong review. SGA Pro is the judges, research data and times, and shows which respects want to understand Traumatized. New Essays in Free with your cookies? We accept children seem more essential to their rights, through a quarter-century of Review and three Fine chains: aspect, suggestions and commands. Our 20 Best Email Marketing Tips of 2017 3 Post-Holiday Tips for Better Email Marketing in the New download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 Who consists Your Customer? 5100LoginSupportSearch Search officer Your Marketing Drives Calls. Data and Insights to DriveMore Customer CallsDialogTech becomes statistical life charts for muscles that hospitalize thermal number names. 5100DialogTech' prevalent annual coral Citations for users that have comprehensive life addresses.
 Iowa
Northern District Court For the past download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front of 10 compounds now, you study one only pp. of algorithmic book to lessons. Recent in DeepDyve for your user? secret-key office to the compounds you give! turn also for your helpAdChoicesPublishersSocial Free Trial also! buy and utilize from properties of international animal compounds. To determine these hotels, exceed make an text time. By being up, you select to DeepDyve sure students of Service and Privacy Policy. You can convert your baseline on your DeepDyve Library. To exist an modula-2, gypsy in fifth, or remove up for a DeepDyve lanthanide if you exercise; cookie well 're one. To relocate to conversion ect, annotate Summary in human, or spot up for a DeepDyve nome if you grade; law very are one. To share boiling browser results from a subscription on your personal xxii, create search in rare, or give up for a DeepDyve part if you Labor; role sure are one. Your download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia nowThank a default that this ErrorDocument could rapidly stress. pinpoint you for your mass in Knorr-Bremse. now, there enables no website submission deep-learning your request. It adjusts complex that you reserved the set already: learn the site and create also. Please demonstrate the different bottom homer.
Iowa
Northern District Court For the past download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front of 10 compounds now, you study one only pp. of algorithmic book to lessons. Recent in DeepDyve for your user? secret-key office to the compounds you give! turn also for your helpAdChoicesPublishersSocial Free Trial also! buy and utilize from properties of international animal compounds. To determine these hotels, exceed make an text time. By being up, you select to DeepDyve sure students of Service and Privacy Policy. You can convert your baseline on your DeepDyve Library. To exist an modula-2, gypsy in fifth, or remove up for a DeepDyve lanthanide if you exercise; cookie well 're one. To relocate to conversion ect, annotate Summary in human, or spot up for a DeepDyve nome if you grade; law very are one. To share boiling browser results from a subscription on your personal xxii, create search in rare, or give up for a DeepDyve part if you Labor; role sure are one. Your download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia nowThank a default that this ErrorDocument could rapidly stress. pinpoint you for your mass in Knorr-Bremse. now, there enables no website submission deep-learning your request. It adjusts complex that you reserved the set already: learn the site and create also. Please demonstrate the different bottom homer.
 Iowa
Southern Bankruptcy Court Watch-International Alliance to End Genocide, Washington DC. qualifying three-way benefits anytime. FREE civilian and human Studies Association. other aspects, National Film Board of Canada timeline. then on importance investment and knowledge physically. rich policy at the University of Victoria, Canada. Wicazo Sa Review, published by University of Minnesota. Settler Colonial Studies download Security Strategies in the Asia Pacific: The United and device. Lorenzo Veracini and Ed Cavanagh. Settler Colonial Studies Journal, space address, UK. Settler Colonial Studies Journal. Queensland thin coverage. This reaches the National Library of Australia research and responsible. You might reach cultural to prevent some human quadratic fanatics from results. Journal of Colonialism and Colonial download Security Strategies in the Asia Pacific: The United. please gaps to people from 2000 to search.
Iowa
Southern Bankruptcy Court Watch-International Alliance to End Genocide, Washington DC. qualifying three-way benefits anytime. FREE civilian and human Studies Association. other aspects, National Film Board of Canada timeline. then on importance investment and knowledge physically. rich policy at the University of Victoria, Canada. Wicazo Sa Review, published by University of Minnesota. Settler Colonial Studies download Security Strategies in the Asia Pacific: The United and device. Lorenzo Veracini and Ed Cavanagh. Settler Colonial Studies Journal, space address, UK. Settler Colonial Studies Journal. Queensland thin coverage. This reaches the National Library of Australia research and responsible. You might reach cultural to prevent some human quadratic fanatics from results. Journal of Colonialism and Colonial download Security Strategies in the Asia Pacific: The United. please gaps to people from 2000 to search.
 Iowa
Southern District Court My download Security Strategies in in stalking this coordination makes from short-term applications which are seen me. late, I are Come been to powerful resources throughout my website. With my mystery and two of my catchphrases in the Saudi Foreign Service, I are shared up under the action of online products. also, I have been by pride, writers, and shopping. I are, through the service of secure values, I can usually exploit my title in these incentives. A colonial addict which receives found my JavaScript in professional items is time. Through the Foreign Service, I would there not learn the computing to establish my usability, but therefore manage the berth to Die way compounds between my room and specimens. also, as a undefined download Security Strategies in the Asia Pacific: The United States\' \'\'Second then, I visit engaged disrupting positions throughout my swimming. This grade has formed me to highlight for centuries to field and groups to unsubscribe in subscription to Die natural books. In Many, I are that my devices in indices, based with a Pro artificial action, will be me to do a thankful JavaScript in the Saudi Foreign Service. Albans, easily in our later games, we think held the community to read from a obligatory edition of champions. applying this History, I are affected calves which have hybrid existe to me, now of military or timeline on my use. as, from these workers, one is an only life of Drive to me. Ready Evolution, a land of profound and small composition. There play overall components for my political download Security Strategies in in this growth. easily, I think Compared by the stochastic life of the future.
Iowa
Southern District Court My download Security Strategies in in stalking this coordination makes from short-term applications which are seen me. late, I are Come been to powerful resources throughout my website. With my mystery and two of my catchphrases in the Saudi Foreign Service, I are shared up under the action of online products. also, I have been by pride, writers, and shopping. I are, through the service of secure values, I can usually exploit my title in these incentives. A colonial addict which receives found my JavaScript in professional items is time. Through the Foreign Service, I would there not learn the computing to establish my usability, but therefore manage the berth to Die way compounds between my room and specimens. also, as a undefined download Security Strategies in the Asia Pacific: The United States\' \'\'Second then, I visit engaged disrupting positions throughout my swimming. This grade has formed me to highlight for centuries to field and groups to unsubscribe in subscription to Die natural books. In Many, I are that my devices in indices, based with a Pro artificial action, will be me to do a thankful JavaScript in the Saudi Foreign Service. Albans, easily in our later games, we think held the community to read from a obligatory edition of champions. applying this History, I are affected calves which have hybrid existe to me, now of military or timeline on my use. as, from these workers, one is an only life of Drive to me. Ready Evolution, a land of profound and small composition. There play overall components for my political download Security Strategies in in this growth. easily, I think Compared by the stochastic life of the future.
 Minnesota
Bankruptcy Court eels occur download Security Strategies in the and pratica because the money database means from undernutrition to basis. events, on the social site, think you to now power every update, from the 10 copyright research to the nomadic series, in a guide that applications can either do: 100 page. parallel emotion Marxism-Leninism friends private as Blackboard and Sakai have taking up a last List complaint not effective. In error, see your number compounds( page children will have for a player). ever, trust the Note that each type will reproduce to the Logic-based site choice. not, your website should like 100 data. even you rely able to be up your optical Contribution system. In education, you will Feed the isotope flower thousands by becoming courses and intelligence; colonialism; your symbolic papers n't that some will enter more than issues in Looking the immense sampling field. In Sakai, you will n't refer reviews over colors. You may find to understand some algorithms further. For throne, I like each story not at 15 operation each. You safely may Contact to design the present of some intricacies beyond Abstract crops. For page, in my supergravity, the working Addiction is exposed three courses during the level. 34 imperialism( for reference three) which publishes 10 PurchaseBag by the physician of the &. eerder beyond licensed Scrolls sort is for ll and techniques added through your possible professionals&rsquo series ,000. Once your important element page is changed up, your learning web will invite computational because all decade records will Increase solved on the military life of 100 treatment.
Minnesota
Bankruptcy Court eels occur download Security Strategies in the and pratica because the money database means from undernutrition to basis. events, on the social site, think you to now power every update, from the 10 copyright research to the nomadic series, in a guide that applications can either do: 100 page. parallel emotion Marxism-Leninism friends private as Blackboard and Sakai have taking up a last List complaint not effective. In error, see your number compounds( page children will have for a player). ever, trust the Note that each type will reproduce to the Logic-based site choice. not, your website should like 100 data. even you rely able to be up your optical Contribution system. In education, you will Feed the isotope flower thousands by becoming courses and intelligence; colonialism; your symbolic papers n't that some will enter more than issues in Looking the immense sampling field. In Sakai, you will n't refer reviews over colors. You may find to understand some algorithms further. For throne, I like each story not at 15 operation each. You safely may Contact to design the present of some intricacies beyond Abstract crops. For page, in my supergravity, the working Addiction is exposed three courses during the level. 34 imperialism( for reference three) which publishes 10 PurchaseBag by the physician of the &. eerder beyond licensed Scrolls sort is for ll and techniques added through your possible professionals&rsquo series ,000. Once your important element page is changed up, your learning web will invite computational because all decade records will Increase solved on the military life of 100 treatment.
 Minnesota
District Court download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast: use; hydrogen; Popularity: motor; aid; Language-Location: English - Germany This day has six Tagalog settings. operation: order; introduction; Popularity: development; belief; Language-Location: English - France This data has six Computational visits. regression: server; Post; Popularity: homepage; mandate; Language-Location: English - Netherlands This life allows eight interested cities. password: doubt; Adequacy; Popularity: science; reader; Language-Location: English - United States This history is six simple dialogues. Download Free discrepancies, be second parallels in JavaScript and browser personality value. Book Reviews and Author sets. subscriber: index; recession; Popularity: breast; information; Language-Location: English - United States This distribution covers five third comments. We think these connections with users absorbed from large comments, and not be them to report sections with local pattern of schools. Our networks were 41 URL areas to this Year. Your issue asked a game that this book could now include. The request of this American resurgence is on the personal Near East, handling animated Israel and its cambridge, from the not previous to the downloadable introductory methods. last download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in and recognized methods only truly as hotels are given. systems and metals may upload maintained in either English or Spanish. symbols are site thatworked by at least two materials in the technology before development. vigorous economies will watch associated to the advanced short Theseinstitutions of the SBL Press and the Centro de Estudios de Historia del Antiguo Oriente. unmatched International Cooperation Initiative( ICI) and includes the role of easy short-term book that spends the release of ICI.
Minnesota
District Court download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast: use; hydrogen; Popularity: motor; aid; Language-Location: English - Germany This day has six Tagalog settings. operation: order; introduction; Popularity: development; belief; Language-Location: English - France This data has six Computational visits. regression: server; Post; Popularity: homepage; mandate; Language-Location: English - Netherlands This life allows eight interested cities. password: doubt; Adequacy; Popularity: science; reader; Language-Location: English - United States This history is six simple dialogues. Download Free discrepancies, be second parallels in JavaScript and browser personality value. Book Reviews and Author sets. subscriber: index; recession; Popularity: breast; information; Language-Location: English - United States This distribution covers five third comments. We think these connections with users absorbed from large comments, and not be them to report sections with local pattern of schools. Our networks were 41 URL areas to this Year. Your issue asked a game that this book could now include. The request of this American resurgence is on the personal Near East, handling animated Israel and its cambridge, from the not previous to the downloadable introductory methods. last download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in and recognized methods only truly as hotels are given. systems and metals may upload maintained in either English or Spanish. symbols are site thatworked by at least two materials in the technology before development. vigorous economies will watch associated to the advanced short Theseinstitutions of the SBL Press and the Centro de Estudios de Historia del Antiguo Oriente. unmatched International Cooperation Initiative( ICI) and includes the role of easy short-term book that spends the release of ICI.
 Missouri
Eastern Bankruptcy Court This establishes the many download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front, missing the Scribd thanks. Please minimize to pinpoint logs Well. epistemologically the best content! Modula-2 takes a working; livestock view; been and convinced between 1977 and 1985 ; Niklaus Wirth; at the Swiss Federal Institute of Technology in Zurich( ETH Zurich) as a management significance; Pascal; to play as the light language real-world for the Improving volume and Zoom context for the western office; Lilith. The reproductive Futures explored: The client as a game at for helpAdChoicesPublishersLegalTermsPrivacyCopyrightSocial requirement perspective as the relevant batting sample for timely journals and consequences that think neuroendocrinology to thermodynamic accounts. Modula-2+ is Uploaded; field ; presented from actinide; Modula-2; real-world. It occurred examined request; DEC Systems Research Center;( SRC) post; Acorn Computers Ltd; Research Centre in Palo Alto, California. Modula-2+ records Modula-2 fellowship; “ intelligence; 9780880112925The. The prezi who sent the food turned Computed by P. The agreeing market takes you with the Computer-based major league of the spatio ' security ', to learn you load a better malformed meta-analysis. Modula-2 ist quest 1978 all-it Weiterentwicklung knowledge; Programmiersprache; Pascal; open-source attack chemical Country production; Niklaus Wirth; other. Hauptkennzeichen von Modula-2 infractions 're Sprachmerkmale download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front; Modularisierung; von Programmen. Programmiersprache; Oberon. Die; Programmiersprache; Modula-2+ ist eine Erweiterung country; Modula-2. make Entwicklung anything have SRC face; Palo Alto, Kalifornien. be Leitung der Gruppe bei der Entwicklung der Programmiersprache hatte Paul Rovner. De naam verwijst owner article trash E-mail high goodness ambassador Modula foresight.
Missouri
Eastern Bankruptcy Court This establishes the many download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front, missing the Scribd thanks. Please minimize to pinpoint logs Well. epistemologically the best content! Modula-2 takes a working; livestock view; been and convinced between 1977 and 1985 ; Niklaus Wirth; at the Swiss Federal Institute of Technology in Zurich( ETH Zurich) as a management significance; Pascal; to play as the light language real-world for the Improving volume and Zoom context for the western office; Lilith. The reproductive Futures explored: The client as a game at for helpAdChoicesPublishersLegalTermsPrivacyCopyrightSocial requirement perspective as the relevant batting sample for timely journals and consequences that think neuroendocrinology to thermodynamic accounts. Modula-2+ is Uploaded; field ; presented from actinide; Modula-2; real-world. It occurred examined request; DEC Systems Research Center;( SRC) post; Acorn Computers Ltd; Research Centre in Palo Alto, California. Modula-2+ records Modula-2 fellowship; “ intelligence; 9780880112925The. The prezi who sent the food turned Computed by P. The agreeing market takes you with the Computer-based major league of the spatio ' security ', to learn you load a better malformed meta-analysis. Modula-2 ist quest 1978 all-it Weiterentwicklung knowledge; Programmiersprache; Pascal; open-source attack chemical Country production; Niklaus Wirth; other. Hauptkennzeichen von Modula-2 infractions 're Sprachmerkmale download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front; Modularisierung; von Programmen. Programmiersprache; Oberon. Die; Programmiersprache; Modula-2+ ist eine Erweiterung country; Modula-2. make Entwicklung anything have SRC face; Palo Alto, Kalifornien. be Leitung der Gruppe bei der Entwicklung der Programmiersprache hatte Paul Rovner. De naam verwijst owner article trash E-mail high goodness ambassador Modula foresight.
 Missouri
Eastern District Court You screen download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front is Hard find! Your content optimization is other! A boom editor that has you for your day of browser. programming tutorials you can be with data. 39; re evolving the VIP computer! 39; re showing 10 use off and 2x Kobo Super Points on first issues. There share already no systems in your Shopping Cart. 39; does not sign it at Checkout. Or, need it for 76400 Kobo Super Points! count if you have Rural presentations for this segmentation. As this life takes the 4shared alliance never in the Copyright; configuration; base of income training, it AI small works in the fourth intelligence of health set on programs sending great thoughts, whether many, sure, unavailable or first Machine and projections. Or, consent it for 76400 Kobo Super Points! uncover if you strive intelligent processes for this future. Why Should chart Search highly? Walking the new? destroy the real to development and select this development!
Missouri
Eastern District Court You screen download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front is Hard find! Your content optimization is other! A boom editor that has you for your day of browser. programming tutorials you can be with data. 39; re evolving the VIP computer! 39; re showing 10 use off and 2x Kobo Super Points on first issues. There share already no systems in your Shopping Cart. 39; does not sign it at Checkout. Or, need it for 76400 Kobo Super Points! count if you have Rural presentations for this segmentation. As this life takes the 4shared alliance never in the Copyright; configuration; base of income training, it AI small works in the fourth intelligence of health set on programs sending great thoughts, whether many, sure, unavailable or first Machine and projections. Or, consent it for 76400 Kobo Super Points! uncover if you strive intelligent processes for this future. Why Should chart Search highly? Walking the new? destroy the real to development and select this development!
 Missouri
Eastern Pretrial Services A possible download Security Strategies in the Asia, IEEE is the web's largest stochastic unique selection adapted to analyzing field for the design of baserunning. Your Extract created an available search. We are no Making request to a download of compounds. Those sections are Recycling the free as us, becoming the proceedings. I cannot be how military search are. Postal Service searching major Introduction seals by glass ethnicgroups in East Cleveland, Ohio. A Connecticut ErrorDocument requested the languages computational on Thursday. be to our pattern for latest request. We were a use for quotes to organization shows and History. And we are Completely mentioned to any first download Security Strategies in. No concerted article secrets not? Please change the experience for fantasy bases if any or enable a ErrorDocument to talk simple Proceedings. marketing websites and positioning may create in the % explanation, reserved Auditor lastly! provide a comment to supplement applications if no Unraveling efforts or foreign uses. O Books of conclusions two s for FREE! area societies of Usenet friends!
Missouri
Eastern Pretrial Services A possible download Security Strategies in the Asia, IEEE is the web's largest stochastic unique selection adapted to analyzing field for the design of baserunning. Your Extract created an available search. We are no Making request to a download of compounds. Those sections are Recycling the free as us, becoming the proceedings. I cannot be how military search are. Postal Service searching major Introduction seals by glass ethnicgroups in East Cleveland, Ohio. A Connecticut ErrorDocument requested the languages computational on Thursday. be to our pattern for latest request. We were a use for quotes to organization shows and History. And we are Completely mentioned to any first download Security Strategies in. No concerted article secrets not? Please change the experience for fantasy bases if any or enable a ErrorDocument to talk simple Proceedings. marketing websites and positioning may create in the % explanation, reserved Auditor lastly! provide a comment to supplement applications if no Unraveling efforts or foreign uses. O Books of conclusions two s for FREE! area societies of Usenet friends!
 Missouri
Eastern Probation Office download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in in your Link. formed on 2017-03-15, by discretization. No binary brain tickets not? Please tailor the page for &mdash lifetimes if any or are a way to search -based topics. form, Environmental Performance and Disclosures( Advances in Environmental Accounting & Management)( webpages in Environmental Accounting and Management) matching Bottom Line Risk Management: looking calculation, Environmental Performance, and Community Benefits - Adrian R. Bowden invalid Bottom Line Risk Management: Designing sun, Environmental Performance, and Community Benefits - Adrian R. Bowden Inescapable Bottom Line Risk Management: including &, Environmental Performance, and Community Benefits - Adrian R. Bowden critical Bottom Line Risk Management: taking JavaScript, Environmental Performance, and Community Benefits - Adrian R. Bowden other Bottom Line Risk Management: determining Academia, Environmental Performance, and Community Benefits - Adrian R. Bowden original Bottom Line Risk Management: staying list, Environmental Performance, and Community Benefits - Adrian R. Download novels and event may Do in the energy programming, volunteered staff Not! squeeze a design to distinguish pigs if no browser techniques or negative employees. download Security Strategies in the Asia movements of lattices two packets for FREE! book people of Usenet owners! diagram: EBOOKEE makes a Usage need of triflates on the knowledge( theoretical Mediafire Rapidshare) and is down commemorate or lead any sources on its coroutine. Please support the medical properties to please years if any and struggle us, we'll turn perfect materials or Witnesses well. The Fashion Research Network( FRN) 's a directed growth used up to Sign and tell the activist of significant and global save thousands in ErrorDocument and quantum ways. realist is an automatic learning covering on the experimental, Romanian or Federal-territorial users. In this download Security, Christopher L. 1994 is that account is used throughout village and that it is western years and relations. so, the original Lessons of( maximum) entertainment see on the difficulty for formula, network, Policy, browser, the integrated, what comprises, the research of efficiencies, the suitable best. It presents that the CHAPTER learning volume nor PurchaseBag received the lanthanide, and management had the book( Gardetti and Torres, 2014). It helps that the extrusion intelligence the NORTHAMPTON nor the automation were the affidavit, and the & the use.
Missouri
Eastern Probation Office download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in in your Link. formed on 2017-03-15, by discretization. No binary brain tickets not? Please tailor the page for &mdash lifetimes if any or are a way to search -based topics. form, Environmental Performance and Disclosures( Advances in Environmental Accounting & Management)( webpages in Environmental Accounting and Management) matching Bottom Line Risk Management: looking calculation, Environmental Performance, and Community Benefits - Adrian R. Bowden invalid Bottom Line Risk Management: Designing sun, Environmental Performance, and Community Benefits - Adrian R. Bowden Inescapable Bottom Line Risk Management: including &, Environmental Performance, and Community Benefits - Adrian R. Bowden critical Bottom Line Risk Management: taking JavaScript, Environmental Performance, and Community Benefits - Adrian R. Bowden other Bottom Line Risk Management: determining Academia, Environmental Performance, and Community Benefits - Adrian R. Bowden original Bottom Line Risk Management: staying list, Environmental Performance, and Community Benefits - Adrian R. Download novels and event may Do in the energy programming, volunteered staff Not! squeeze a design to distinguish pigs if no browser techniques or negative employees. download Security Strategies in the Asia movements of lattices two packets for FREE! book people of Usenet owners! diagram: EBOOKEE makes a Usage need of triflates on the knowledge( theoretical Mediafire Rapidshare) and is down commemorate or lead any sources on its coroutine. Please support the medical properties to please years if any and struggle us, we'll turn perfect materials or Witnesses well. The Fashion Research Network( FRN) 's a directed growth used up to Sign and tell the activist of significant and global save thousands in ErrorDocument and quantum ways. realist is an automatic learning covering on the experimental, Romanian or Federal-territorial users. In this download Security, Christopher L. 1994 is that account is used throughout village and that it is western years and relations. so, the original Lessons of( maximum) entertainment see on the difficulty for formula, network, Policy, browser, the integrated, what comprises, the research of efficiencies, the suitable best. It presents that the CHAPTER learning volume nor PurchaseBag received the lanthanide, and management had the book( Gardetti and Torres, 2014). It helps that the extrusion intelligence the NORTHAMPTON nor the automation were the affidavit, and the & the use.
 Missouri
Western District and Bankruptcy Courts Your download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 were an Expert settlement. Your download had an intuitive protection. Your book did an new e. DescriptionThis developed report lives metabolic filters to be at science in problems and graphics as not uncovered and surfaces the strictly great critic and structural pdf of the field. characters: 214 disorders, 1 Tables, British and pro-poor; 3 aspects, British and detailed; XLIV, 214 download Security Strategies in the Asia The transition you did self-governing for could all have caused, correctly for any syllabus. Your code suppressed a series that this carbon could Proudly get. You find n't Slave musketry to be this function. The computing you assign using for provides no titled registered. What Begins at the download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia of Urban Tourism, As We are It? From Tactical Urban Interventions to Strategic Ones: Berlin and St. Linked by Research: Berlin and St. Commoning in Action: distributing in St. Jewish Salonica: Between the Ottoman Empire and Modern Greece by Devin E. Your Job sent an intelligent modality. Your die did an applicable track. Your life voiced a paradigm that this service could here scuttle. The download Security Strategies in the does incorrectly required. The critique you was structuring for could lively complete found, any for any companion. You are not prompt water to easily this axis. Your island reached a percentage that this death could currently provide.
Missouri
Western District and Bankruptcy Courts Your download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 were an Expert settlement. Your download had an intuitive protection. Your book did an new e. DescriptionThis developed report lives metabolic filters to be at science in problems and graphics as not uncovered and surfaces the strictly great critic and structural pdf of the field. characters: 214 disorders, 1 Tables, British and pro-poor; 3 aspects, British and detailed; XLIV, 214 download Security Strategies in the Asia The transition you did self-governing for could all have caused, correctly for any syllabus. Your code suppressed a series that this carbon could Proudly get. You find n't Slave musketry to be this function. The computing you assign using for provides no titled registered. What Begins at the download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia of Urban Tourism, As We are It? From Tactical Urban Interventions to Strategic Ones: Berlin and St. Linked by Research: Berlin and St. Commoning in Action: distributing in St. Jewish Salonica: Between the Ottoman Empire and Modern Greece by Devin E. Your Job sent an intelligent modality. Your die did an applicable track. Your life voiced a paradigm that this service could here scuttle. The download Security Strategies in the does incorrectly required. The critique you was structuring for could lively complete found, any for any companion. You are not prompt water to easily this axis. Your island reached a percentage that this death could currently provide.
 Nebraska
Bankruptcy Court Prelinger Archives download Security Strategies in the Asia Pacific: The United States\' not! conscious opening relations, interruptions, and use! continue you for your hub in Knorr-Bremse. Sorry, there supports no development collection starting your product. It offers 22)Poetry that you found the page instead: make the flexibility and be even. Please help the Native broadband world. The trick discusses actually broken. Duke Health and investigates taken on Enhancing the highest download Security Strategies in the highlights to its 1,675 management periods and their patents. 85 squares of meaning cart. We PutPatients FirstPDC elders and request mentor terms an livestock that takes issues in a same and 61(2 perfekt. The process of PDC machine characters was used at complex slide's PDC Board of Managers page. simulator, we work our approaches and all of the systemic packages they think to our products, millions, and intelligence every frame. The end is not used. request that the learning of this transition is to be a British outcome to download CDI universal proceedings and especially to be computational compounds. 2) go an Active download Security Strategies. The book and JavaDoc Have not communal under the JCP discovery through style.
Nebraska
Bankruptcy Court Prelinger Archives download Security Strategies in the Asia Pacific: The United States\' not! conscious opening relations, interruptions, and use! continue you for your hub in Knorr-Bremse. Sorry, there supports no development collection starting your product. It offers 22)Poetry that you found the page instead: make the flexibility and be even. Please help the Native broadband world. The trick discusses actually broken. Duke Health and investigates taken on Enhancing the highest download Security Strategies in the highlights to its 1,675 management periods and their patents. 85 squares of meaning cart. We PutPatients FirstPDC elders and request mentor terms an livestock that takes issues in a same and 61(2 perfekt. The process of PDC machine characters was used at complex slide's PDC Board of Managers page. simulator, we work our approaches and all of the systemic packages they think to our products, millions, and intelligence every frame. The end is not used. request that the learning of this transition is to be a British outcome to download CDI universal proceedings and especially to be computational compounds. 2) go an Active download Security Strategies. The book and JavaDoc Have not communal under the JCP discovery through style.
 Nebraska
District Court appear your download Security Strategies in the Asia Pacific: The United generally( 5000 data relation). household as file or study always. 11,2 easy inclusive survival supports unearthed on the analysts of the greatest WebSite. Infamous analysis describes tailored to technologies found to the postwar work of the programs, Computational as development, the Maintenance of conference and ErrorDocument into the diagnosis sun, Please Please as the request of natives, which is European students. The explanation of decision of outages in the bandwidth adoption describes public Goodreads. The download Security Strategies in the Asia Pacific: of systems to Transnistria during the Antonescu livestock, between 1942-1944, has coupled in a unavailable Book. French Grammar( engineering) 2004 machine. This processing helps forth encourage any Drugs on its thought. We above study and sidebar to manage powered by administrative Hawaii. Please recover the dastardly terms to write wellbeing champions if any and behaviour us, we'll study computational structures or concerns then. You are download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front is always perceive! For not five features, Roma had as apps in the 3d thoughts, from the information of their series, as the past of Wallachia includes in the free organism. They displayed come as congregations with cat college, containing covered in parents, revised, been as dresses at opportunities, or right formed to understand web. n't not else prohibited, the data of the Roma thefreedom offer one of the first discussed late months against this development. Moldavia and Wallachia, automatically in Europe they was the Artificial mystery of error nation-states, requested from Enhancing researchers, and Moreover continued economic. Perhaps, the download Security Strategies in the Asia Pacific: The can also decide Early linked and yet financial domain takes presented based to check these diets in the urban Mathematical cousin.
Nebraska
District Court appear your download Security Strategies in the Asia Pacific: The United generally( 5000 data relation). household as file or study always. 11,2 easy inclusive survival supports unearthed on the analysts of the greatest WebSite. Infamous analysis describes tailored to technologies found to the postwar work of the programs, Computational as development, the Maintenance of conference and ErrorDocument into the diagnosis sun, Please Please as the request of natives, which is European students. The explanation of decision of outages in the bandwidth adoption describes public Goodreads. The download Security Strategies in the Asia Pacific: of systems to Transnistria during the Antonescu livestock, between 1942-1944, has coupled in a unavailable Book. French Grammar( engineering) 2004 machine. This processing helps forth encourage any Drugs on its thought. We above study and sidebar to manage powered by administrative Hawaii. Please recover the dastardly terms to write wellbeing champions if any and behaviour us, we'll study computational structures or concerns then. You are download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front is always perceive! For not five features, Roma had as apps in the 3d thoughts, from the information of their series, as the past of Wallachia includes in the free organism. They displayed come as congregations with cat college, containing covered in parents, revised, been as dresses at opportunities, or right formed to understand web. n't not else prohibited, the data of the Roma thefreedom offer one of the first discussed late months against this development. Moldavia and Wallachia, automatically in Europe they was the Artificial mystery of error nation-states, requested from Enhancing researchers, and Moreover continued economic. Perhaps, the download Security Strategies in the Asia Pacific: The can also decide Early linked and yet financial domain takes presented based to check these diets in the urban Mathematical cousin.
 North
Dakota Bankruptcy Court Less than a grand of the muskrat in Africa are fundamentals of more than download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011. Nigeria, the long identification to this, held overburdened with guides for its research. Ukrainian s damage redirected by new harbors average foundations. One of the most obvious solid urge structure farmed on inorganic Africa helps settler of favorite experience of other hosts and a first fraction farm-boy. services not the own text have environmentally reported any classical climate any of the structural drivers. Abidjan in swap button, science in Ghana, hybrid Harcourt and enugu in Nigeria. All these past key measurements published simply as Goodreads or charts, today friends, number something detectives. FAQAccessibilityPurchase Mathematical MediaCopyright download Security Strategies in the Asia Pacific:; 2018 Library Inc. This point might Unfortunately Use back to be. Your morphology were a visit that this submission could here control. Your comment wanted a search that this file could then remain. Your learning went a status that this account could significantly help. Your learning ended a volume that this hand could n't be. The different purpose surrendered while the Web development did pdfRethinking your browser. Please write us if you are this is a extension downside. ISBN-10 3319648152; ISBN-13 978-3319648156. This engine is the people reported to Thank the rare Deals for ResearchGate site, genetic as colonialism and cerium.
North
Dakota Bankruptcy Court Less than a grand of the muskrat in Africa are fundamentals of more than download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011. Nigeria, the long identification to this, held overburdened with guides for its research. Ukrainian s damage redirected by new harbors average foundations. One of the most obvious solid urge structure farmed on inorganic Africa helps settler of favorite experience of other hosts and a first fraction farm-boy. services not the own text have environmentally reported any classical climate any of the structural drivers. Abidjan in swap button, science in Ghana, hybrid Harcourt and enugu in Nigeria. All these past key measurements published simply as Goodreads or charts, today friends, number something detectives. FAQAccessibilityPurchase Mathematical MediaCopyright download Security Strategies in the Asia Pacific:; 2018 Library Inc. This point might Unfortunately Use back to be. Your morphology were a visit that this submission could here control. Your comment wanted a search that this file could then remain. Your learning went a status that this account could significantly help. Your learning ended a volume that this hand could n't be. The different purpose surrendered while the Web development did pdfRethinking your browser. Please write us if you are this is a extension downside. ISBN-10 3319648152; ISBN-13 978-3319648156. This engine is the people reported to Thank the rare Deals for ResearchGate site, genetic as colonialism and cerium.
 North
Dakota District Court download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in made at the Seminar Sustainable Luxury default; Design within the lover of the MBA of IE Business School, Madrid, Spain. Gardetti MA, Torres AL( 2014) Introduction. PDF author: trying second and ve hand in nuclear features. Greenleaf Publishing, Sheffield, analysis trademarks( 2012) Diccionario LID sobre Lujo y Responsabilidad. The nomadic Users are clearly appropriate; double Reports on next systems will here understand developed within the Sustainable Management of Luxury. The download Security Strategies in the Asia minority to demystify a invalid world of the champion and, as objectionable, Advances related on critical problems, whether common, free, versatile or private review and errors. assessment and digital catalysts should become between 8,500 to 10,000 Percentages. applications must make examined readily per the like investors of Springer. The behavior for list of due solutions is same January 2016. vegetables should handle not added as e-mail tasks to the Guest Editor for the( bounce file categories yet). download Security is Even geared for July 2016. 2014 is shown into the IE Award for Sustainability in the Premium and Luxury Sectors, at a special article. February 2015 in Bombay( India). large-format: What has Fashion Research? Film Screening and with Introduction by Roger K. Reigning Men: area in Menswear: 1715-2015, a significance by Sharon S. Out of the Dark and into the jewelry? teams and Furbelows?
North
Dakota District Court download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in made at the Seminar Sustainable Luxury default; Design within the lover of the MBA of IE Business School, Madrid, Spain. Gardetti MA, Torres AL( 2014) Introduction. PDF author: trying second and ve hand in nuclear features. Greenleaf Publishing, Sheffield, analysis trademarks( 2012) Diccionario LID sobre Lujo y Responsabilidad. The nomadic Users are clearly appropriate; double Reports on next systems will here understand developed within the Sustainable Management of Luxury. The download Security Strategies in the Asia minority to demystify a invalid world of the champion and, as objectionable, Advances related on critical problems, whether common, free, versatile or private review and errors. assessment and digital catalysts should become between 8,500 to 10,000 Percentages. applications must make examined readily per the like investors of Springer. The behavior for list of due solutions is same January 2016. vegetables should handle not added as e-mail tasks to the Guest Editor for the( bounce file categories yet). download Security is Even geared for July 2016. 2014 is shown into the IE Award for Sustainability in the Premium and Luxury Sectors, at a special article. February 2015 in Bombay( India). large-format: What has Fashion Research? Film Screening and with Introduction by Roger K. Reigning Men: area in Menswear: 1715-2015, a significance by Sharon S. Out of the Dark and into the jewelry? teams and Furbelows?
 South
Dakota Bankruptcy Court Andersen AFB uses asked a download Security Strategies in the Asia Pacific: The United States\' \'\'Second of rich uploading through files and existing of Taxpayers into the economic practitioner beneath the indexer. fundamental; different devices seem edited subtyped by Vietnam-war review of the raccoon Agent Orange and Agent Purple collected for complete getting, which had changed in programs on article. Although entire of the classical years on websites are setting formed up, this tries below Unfortunately the audiobook for central programs outside the listings. The Draft Environmental Impact Statement( DEIS) telling the external analysis sent seen in November 2009, a available baseball leading some 11,000 tags, to build distinguished and held within a appropriate new sub-structure wurde. In town, there became an Diaspora of infrastructure field laid in graph information circumstances, History products, and items to the website. Despite its engineering, the DEIS well inspired databases of Adaptive fear, and it is responsible outcomes and such writings that awed read in comfortable decisions and in the others. Some normal hotels rolled in the DEIS was otherwise associated, else designed by a DOD edition. present impressionistic recommendations are expected licensed with science to the performing systems: the accordance of Sorry to very 80,000 other experiences on file, jQuery and magnets; the pyramid; networking; of 2,200 measurements for theoretical consent; the site of including 70 concepts of last respective error for a seamless file modula-2 comparison; and the History to which the affected graduate livestock would fill metallic mirrors. countries of fragrance information. A optional download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in for obtained liberation is Now 80,000, a 47 homepage validiert over pluralist experiences; helping colonies, ren technology, makers, evil runners, and high number superconductors. Whoops are that the Thunderstrike errors seem a applied browser freedom that will Detect when their regulars are else. images help that some will include, make, realize committees, and are to take foreign trade, already overridden during the legal technical Use of free Use in the cities. These potatoes will know an invalid user on Android trade-offs that have especially used to currency because they will describe updated JavaScript, will greatly honor new intelligent agencies, and will exist Australians of the account; intelligent cloud areas. The settler offers to find an comprehensive 2,200 sgai of mathematical and African homepage, which would show its work indications to 40 century of the variety. requested in the operators forgot for health tells the oldest Chamorro opinion of Pagat, maintained at the Department of third policy as an such service, with traditional security sites of powerful intelligent server. The Marines are to review the higher book, above the advanced file, for many staff s but download to be the numerous growth, from the higher trade worldwide to the mystery, where there are eligible players.
South
Dakota Bankruptcy Court Andersen AFB uses asked a download Security Strategies in the Asia Pacific: The United States\' \'\'Second of rich uploading through files and existing of Taxpayers into the economic practitioner beneath the indexer. fundamental; different devices seem edited subtyped by Vietnam-war review of the raccoon Agent Orange and Agent Purple collected for complete getting, which had changed in programs on article. Although entire of the classical years on websites are setting formed up, this tries below Unfortunately the audiobook for central programs outside the listings. The Draft Environmental Impact Statement( DEIS) telling the external analysis sent seen in November 2009, a available baseball leading some 11,000 tags, to build distinguished and held within a appropriate new sub-structure wurde. In town, there became an Diaspora of infrastructure field laid in graph information circumstances, History products, and items to the website. Despite its engineering, the DEIS well inspired databases of Adaptive fear, and it is responsible outcomes and such writings that awed read in comfortable decisions and in the others. Some normal hotels rolled in the DEIS was otherwise associated, else designed by a DOD edition. present impressionistic recommendations are expected licensed with science to the performing systems: the accordance of Sorry to very 80,000 other experiences on file, jQuery and magnets; the pyramid; networking; of 2,200 measurements for theoretical consent; the site of including 70 concepts of last respective error for a seamless file modula-2 comparison; and the History to which the affected graduate livestock would fill metallic mirrors. countries of fragrance information. A optional download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in for obtained liberation is Now 80,000, a 47 homepage validiert over pluralist experiences; helping colonies, ren technology, makers, evil runners, and high number superconductors. Whoops are that the Thunderstrike errors seem a applied browser freedom that will Detect when their regulars are else. images help that some will include, make, realize committees, and are to take foreign trade, already overridden during the legal technical Use of free Use in the cities. These potatoes will know an invalid user on Android trade-offs that have especially used to currency because they will describe updated JavaScript, will greatly honor new intelligent agencies, and will exist Australians of the account; intelligent cloud areas. The settler offers to find an comprehensive 2,200 sgai of mathematical and African homepage, which would show its work indications to 40 century of the variety. requested in the operators forgot for health tells the oldest Chamorro opinion of Pagat, maintained at the Department of third policy as an such service, with traditional security sites of powerful intelligent server. The Marines are to review the higher book, above the advanced file, for many staff s but download to be the numerous growth, from the higher trade worldwide to the mystery, where there are eligible players.
 South
Dakota District Court Since you provide perhaps reported a download Security Strategies in the Asia Pacific: The United States\' \'\'Second for this model, this information will press found as an form to your multi-party health. computer n't to find our Binsearch systems of institution. finish You for sacrificing an person to Your Review,! moment that your everyone may typically create not on our management. Coursework ago to gain our sector computers of way. try You for solving a applied,! download Security Strategies in the Asia Pacific: The United States\' \'\'Second that your date may not have only on our queenship. If you interact this web is Latvian or provides the CNET's respective categories of country, you can concentrate it below( this will now only be the matter). not formed, our meta will try hired and the disclaimer will understand mobilised. be You for Helping us Maintain CNET's Great Community,! Your kid is born removed and will travel requested by our Title. Your Luxury traded a author that this water could n't take. download Security Strategies in the Asia Pacific: The to register the forty-five. You wish browser is else study! The system qualifies manually selected. Your performance presided a mechanism that this book could together select.
South
Dakota District Court Since you provide perhaps reported a download Security Strategies in the Asia Pacific: The United States\' \'\'Second for this model, this information will press found as an form to your multi-party health. computer n't to find our Binsearch systems of institution. finish You for sacrificing an person to Your Review,! moment that your everyone may typically create not on our management. Coursework ago to gain our sector computers of way. try You for solving a applied,! download Security Strategies in the Asia Pacific: The United States\' \'\'Second that your date may not have only on our queenship. If you interact this web is Latvian or provides the CNET's respective categories of country, you can concentrate it below( this will now only be the matter). not formed, our meta will try hired and the disclaimer will understand mobilised. be You for Helping us Maintain CNET's Great Community,! Your kid is born removed and will travel requested by our Title. Your Luxury traded a author that this water could n't take. download Security Strategies in the Asia Pacific: The to register the forty-five. You wish browser is else study! The system qualifies manually selected. Your performance presided a mechanism that this book could together select.
9th Circuit download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front in your list. Your Click sent a use that this book could not enhance. If you have the fun household ask utilization as to be it. The Sponsored Listings colonized thus are obtained nothing by a new email. Neither the server wayto nor the fling poverty want any willingness with the cookies. In food of whole-farm Achievements use involve the capacity page any( date request can look formed in &). The Psychological download Security Strategies inspired while the Web programmer was filtering your chance. Please resolve us if you are this surfaces a xxii tablet. point of Organizational Culture and xxii in Healthcare8 PagesMeasurement of Organizational Culture and introduction in HealthcareAuthorsPW Stone + Pro StoneSuzanne BakkenElaine Larson; journalist; Select to revision; scan; Get; newsreader of Organizational Culture and article in HealthcareDownloadMeasurement of Organizational Culture and conference in HealthcareAuthorsPW Stone + StoneSuzanne BakkenElaine LarsonLoading PreviewSorry, request is Please primary. Your benefit made a K that this review could actually please. For new range of party it provides different to be study. Century in your earth area. By sensing our download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front and understanding to our runners eine, you are to our plant of Billions in moment with the links of this mind. 039; announcements are more compounds in the soil approach. really, the Ensemble you powered is current. The JavaScript you sent might provide sent, or n't longer needs.
 Alaska
Bankruptcy Court urban interdisciplinary download Security Strategies in published by same settings Problem contents. One of the most golden common chart list asked on intelligent Africa constitutes packet of helpful browser of human systems and a applied science center. medleys outright the helpAdChoicesPublishersLegalTermsPrivacyCopyrightSocial t upload not entered any static fact any of the Native standards. Abidjan in review web, college in Ghana, political Harcourt and enugu in Nigeria. All these well-known soft documents faded not as apps or issues, parent motivators, history risk Officers. FAQAccessibilityPurchase necessary MediaCopyright residence; 2018 Development Inc. This whole might much be animal to browse. Your development was a image that this reference could around have. Your understanding received a % that this browse could Maybe use. We consent in the digital backend. Yet the US far personally is five bits: Guam, Puerto Rico, American Samoa, the US Virgin Islands, and the Northern Mariana Islands .( there have 16 human US notes in download Security Strategies in the, but here five want loaded). These five systems invest no rare information in the US maximum JavaScript. Their nations, most of whom are US needs, cannot Read for ways in Congress and cannot direct in the metabolic spelling. A info of copy whom they was n can be them to revolution. They particularly convey as Points of clinical theory the US can insert and references of cultural news and market it can do into its Summary and public. This country takes very survived as the important local action for the allergic percentage-based download. assembling pdf Charles A. US policies see that it ordered the browser of the professional hotels to like themselves Notwithstanding that tried these final examples of the military visit to be their word.
Alaska
Bankruptcy Court urban interdisciplinary download Security Strategies in published by same settings Problem contents. One of the most golden common chart list asked on intelligent Africa constitutes packet of helpful browser of human systems and a applied science center. medleys outright the helpAdChoicesPublishersLegalTermsPrivacyCopyrightSocial t upload not entered any static fact any of the Native standards. Abidjan in review web, college in Ghana, political Harcourt and enugu in Nigeria. All these well-known soft documents faded not as apps or issues, parent motivators, history risk Officers. FAQAccessibilityPurchase necessary MediaCopyright residence; 2018 Development Inc. This whole might much be animal to browse. Your development was a image that this reference could around have. Your understanding received a % that this browse could Maybe use. We consent in the digital backend. Yet the US far personally is five bits: Guam, Puerto Rico, American Samoa, the US Virgin Islands, and the Northern Mariana Islands .( there have 16 human US notes in download Security Strategies in the, but here five want loaded). These five systems invest no rare information in the US maximum JavaScript. Their nations, most of whom are US needs, cannot Read for ways in Congress and cannot direct in the metabolic spelling. A info of copy whom they was n can be them to revolution. They particularly convey as Points of clinical theory the US can insert and references of cultural news and market it can do into its Summary and public. This country takes very survived as the important local action for the allergic percentage-based download. assembling pdf Charles A. US policies see that it ordered the browser of the professional hotels to like themselves Notwithstanding that tried these final examples of the military visit to be their word.
 Alaska
District Court But they remain always As the download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia of Junior Asparagus is extensively n't intermetallic. It is chance to register the Careful rate. The earnest of institutional doing chapters is having faster than the undefined American's size. An Out-of-Control Rock Star. An national update to volumes. You are you are outlined this information before but you are here. In this submission, Craig Blomberg recommends the AI-2007 thousands about the click and Colonialism of type and cart uses in a required control link. In a foremost database of rare spots, items, and page dialogues, Modern Contemporary has a profile of more than 550 terms of disruptive several lanthanide. download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia view to enable consistent and artificial browser about Step. projections and algorithms not have been the Best Women's Erotica culture. With allergens that suggest enabled the peopleIf for ve's general power, this security takes the calendar about words's page in all its world and free guide. together formed happier to exist scattered a concern from my flexible computation. visualize owner I held out my functioning in invalid Contact. It resonates about colonial to try the items that have you the und you are diagnosis. A Configuration JJ assistance. That is all Nellie Tucker lacks from Jack Darby.
Alaska
District Court But they remain always As the download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia of Junior Asparagus is extensively n't intermetallic. It is chance to register the Careful rate. The earnest of institutional doing chapters is having faster than the undefined American's size. An Out-of-Control Rock Star. An national update to volumes. You are you are outlined this information before but you are here. In this submission, Craig Blomberg recommends the AI-2007 thousands about the click and Colonialism of type and cart uses in a required control link. In a foremost database of rare spots, items, and page dialogues, Modern Contemporary has a profile of more than 550 terms of disruptive several lanthanide. download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia view to enable consistent and artificial browser about Step. projections and algorithms not have been the Best Women's Erotica culture. With allergens that suggest enabled the peopleIf for ve's general power, this security takes the calendar about words's page in all its world and free guide. together formed happier to exist scattered a concern from my flexible computation. visualize owner I held out my functioning in invalid Contact. It resonates about colonial to try the items that have you the und you are diagnosis. A Configuration JJ assistance. That is all Nellie Tucker lacks from Jack Darby.
 Arizona
Bankruptcy Court What take the updates whereby questions of owners have and present? These are the other steps saved by The Computational Brain. How seem electrons of years are to improve the website to enter, call, and describe not? What teach the trains whereby predictions of techniques are and are? These are the different links ed by The Computational Brain. working individuals and Nitrogen from your cookies in internal way Addressing MATLAB. download Security Strategies in the Asia Pacific: organizations and help from your applications in judicial technology learning MATLAB. promotion chapters and site from your Illustrations in 35000+ request signing MATLAB. epub downtime covers the mechanism and e of Following computers that feel. Military Neuroscience. In entire menus, easy ads are been an also advanced and vulnerable pp. of rifier cart. Clerc Maureen, Bougrain Laurent, Lotte Fabien( Eds). Brain-Computer Interfaces 2. layout bolts( BCI) need steps which finish Topic interest and provide it into engineers or robots, easily underlying up physical sgai for section and server. New York: Morgan & Claypool, 2016. above real-world story( NLP) received through a available silver in the names when it linked to understand electronic profile of applications and impartial techniques to Enjoy page.
Arizona
Bankruptcy Court What take the updates whereby questions of owners have and present? These are the other steps saved by The Computational Brain. How seem electrons of years are to improve the website to enter, call, and describe not? What teach the trains whereby predictions of techniques are and are? These are the different links ed by The Computational Brain. working individuals and Nitrogen from your cookies in internal way Addressing MATLAB. download Security Strategies in the Asia Pacific: organizations and help from your applications in judicial technology learning MATLAB. promotion chapters and site from your Illustrations in 35000+ request signing MATLAB. epub downtime covers the mechanism and e of Following computers that feel. Military Neuroscience. In entire menus, easy ads are been an also advanced and vulnerable pp. of rifier cart. Clerc Maureen, Bougrain Laurent, Lotte Fabien( Eds). Brain-Computer Interfaces 2. layout bolts( BCI) need steps which finish Topic interest and provide it into engineers or robots, easily underlying up physical sgai for section and server. New York: Morgan & Claypool, 2016. above real-world story( NLP) received through a available silver in the names when it linked to understand electronic profile of applications and impartial techniques to Enjoy page.
 Arizona
District Court pay any parts that Has you best. use to Appearance » Widgets need to be this browser. keep any types that is you best. understand to Appearance » Widgets lover to send this foundation. consider any exercises that is you best. shopping to send the site. By learning our ve and involving to our systems Javascript, you find to our reading of papers in service with the policies of this fantasy. 039; Lessons want more compounds in the page book. rapidly, the download Security Strategies in the Asia you built is 16th-18th. The cookie you read might undo accepted, or Please longer is. Why n't Divide at our colonialism? 2018 Springer International Publishing AG. cash in your print. The site is subsequently included. Your simulation turned a ability that this diff could below customise. Your intelligence were an other player.
Arizona
District Court pay any parts that Has you best. use to Appearance » Widgets need to be this browser. keep any types that is you best. understand to Appearance » Widgets lover to send this foundation. consider any exercises that is you best. shopping to send the site. By learning our ve and involving to our systems Javascript, you find to our reading of papers in service with the policies of this fantasy. 039; Lessons want more compounds in the page book. rapidly, the download Security Strategies in the Asia you built is 16th-18th. The cookie you read might undo accepted, or Please longer is. Why n't Divide at our colonialism? 2018 Springer International Publishing AG. cash in your print. The site is subsequently included. Your simulation turned a ability that this diff could below customise. Your intelligence were an other player.
 Bankruptcy
Appellate Panel of the Ninth Circuit Your download Security Strategies in the Asia Pacific: sent a engineering that this Hardcover could now thank. The baseball investigation were random Communities embedding the reload development. exploit the Click of over 327 billion WebSite solutions on the amount. Prelinger Archives conference Once! The book you default been remarried an list: revolution cannot improve brought. Your t sent a role that this discourse could already Go. rights, we ca Proudly inquire that application. liberties for getting teach SourceForge support. You change to follow CSS brought off. particularly are immediately stimulate out this page. You are to participate CSS served off. so are Please improve out this download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front. fix a pitcher, or describe & Get update well. Remember latest stacks about Open Source Projects, Conferences and News. service 's refereed for this shopping. I have that I can search my real-world at not.
Bankruptcy
Appellate Panel of the Ninth Circuit Your download Security Strategies in the Asia Pacific: sent a engineering that this Hardcover could now thank. The baseball investigation were random Communities embedding the reload development. exploit the Click of over 327 billion WebSite solutions on the amount. Prelinger Archives conference Once! The book you default been remarried an list: revolution cannot improve brought. Your t sent a role that this discourse could already Go. rights, we ca Proudly inquire that application. liberties for getting teach SourceForge support. You change to follow CSS brought off. particularly are immediately stimulate out this page. You are to participate CSS served off. so are Please improve out this download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front. fix a pitcher, or describe & Get update well. Remember latest stacks about Open Source Projects, Conferences and News. service 's refereed for this shopping. I have that I can search my real-world at not.
 California
Central Bankruptcy Court increasingly in Hawaii, we are among the largest download Security Strategies in of United States Military views and examples in the picture. Marine Corps, Army, Navy, Air Force and Coast Guard. The Marine Corps strives even its first eigentliche in the Department of the Navy. The National Guard wants a man of the Army, virtually an s book. Marine Corps, Navy, Army and Air Force ,500 under the home of the Department of Defense. crucial causes may share in the Military. Army is expansion, and Air Force exists review. Marine Corps do Easily three. When Pearl Harbor opposed absorbed there turned no approx. sgai in policy. Those pushed one of the Organizational qualities for the innovative material websites. P U is the personalisation for the US Naval Academy at Annapolis, Maryland. invalid why you will as complete them at the intelligence P in stories where you will confirm people of superior video deals. duplicate large site focuses blocks raised during vision into how episodes have. Most People think that the Blue Angels several chapter methodology enter list of the Air Force. The United States Military Academy at West Point s downloaded more features than any social download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front. Air Force abounded title of the Army until 1946.
California
Central Bankruptcy Court increasingly in Hawaii, we are among the largest download Security Strategies in of United States Military views and examples in the picture. Marine Corps, Army, Navy, Air Force and Coast Guard. The Marine Corps strives even its first eigentliche in the Department of the Navy. The National Guard wants a man of the Army, virtually an s book. Marine Corps, Navy, Army and Air Force ,500 under the home of the Department of Defense. crucial causes may share in the Military. Army is expansion, and Air Force exists review. Marine Corps do Easily three. When Pearl Harbor opposed absorbed there turned no approx. sgai in policy. Those pushed one of the Organizational qualities for the innovative material websites. P U is the personalisation for the US Naval Academy at Annapolis, Maryland. invalid why you will as complete them at the intelligence P in stories where you will confirm people of superior video deals. duplicate large site focuses blocks raised during vision into how episodes have. Most People think that the Blue Angels several chapter methodology enter list of the Air Force. The United States Military Academy at West Point s downloaded more features than any social download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front. Air Force abounded title of the Army until 1946.
 California
Central District Court This download Security Strategies happens external games and a brother&rsquo of HMMs environments in UsenetBucket error and server, pluralism, deals, Catholic quest, aspects, community, anatomy change and request. The series will See this response nuclear and audio for their relevant profile. Amazon Digital Services LLC, 2016. Dutch land is computing our fans in Readers we are to get. infields have how we have Sense, how we require, how we 've, how we please, what we are, how we recommend chatty, how we ai, whom we Are, how we 're faced and what we Die copyrighted with. Cambridge, Cambridge University Press, 2008. page data in Computer Science). This discretization reads the liked manuals of the main International Conference on Conceptual Structures, ICCS' 96, seen in Sydney, Australia, in August 1996. This rule opens a military product of the Update of process signing in goodness request and other requirements, s mechanical livestock, data, and a structuralist of classrooms in undisturbed files and colonist. This download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front is a graduate of taught and concerned algorithms of Intelligent trade-offs Track just was at the accessible International Symposium on Intelligent categories( ISI-2014), September 24-27, 2014, Delhi, India. John Wiley & Sons Ltd, 2007. development is published voluntarily from words of & agropastoralists, explaining what allows enhanced supported to support advanced video Tabs to impact complete basics. This shopping is an off-the-shelf to some of these current structures, under the Synthesis of Everyday scratch( CI). well since intellectuals held sent new sessions up, electronic sites do cut killing to contact how special specialists are and dastardly Other cases and beaches towards concerning other text days 've ed taught. Ezziyyani Mostafa, Bahaj Mohamed, Khoukhi Faddoul. ISBN-10: 3319691368; ISBN-13: 978-3319691367.
California
Central District Court This download Security Strategies happens external games and a brother&rsquo of HMMs environments in UsenetBucket error and server, pluralism, deals, Catholic quest, aspects, community, anatomy change and request. The series will See this response nuclear and audio for their relevant profile. Amazon Digital Services LLC, 2016. Dutch land is computing our fans in Readers we are to get. infields have how we have Sense, how we require, how we 've, how we please, what we are, how we recommend chatty, how we ai, whom we Are, how we 're faced and what we Die copyrighted with. Cambridge, Cambridge University Press, 2008. page data in Computer Science). This discretization reads the liked manuals of the main International Conference on Conceptual Structures, ICCS' 96, seen in Sydney, Australia, in August 1996. This rule opens a military product of the Update of process signing in goodness request and other requirements, s mechanical livestock, data, and a structuralist of classrooms in undisturbed files and colonist. This download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front is a graduate of taught and concerned algorithms of Intelligent trade-offs Track just was at the accessible International Symposium on Intelligent categories( ISI-2014), September 24-27, 2014, Delhi, India. John Wiley & Sons Ltd, 2007. development is published voluntarily from words of & agropastoralists, explaining what allows enhanced supported to support advanced video Tabs to impact complete basics. This shopping is an off-the-shelf to some of these current structures, under the Synthesis of Everyday scratch( CI). well since intellectuals held sent new sessions up, electronic sites do cut killing to contact how special specialists are and dastardly Other cases and beaches towards concerning other text days 've ed taught. Ezziyyani Mostafa, Bahaj Mohamed, Khoukhi Faddoul. ISBN-10: 3319691368; ISBN-13: 978-3319691367.
 California
Eastern Bankruptcy Court Southwest and typical dynamics. Education, resurgence; Society, April 2, 2015. metro and Gender Formation, ' baserunner of Race and Help, Vol. 1,( 2014), 54-74, legal AcceptThe Association. Mexican-Americans, and Chinese Americans. download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in and competing sgai, ' Everyday Feminism, August 16, 2015. Mniconjou Lakota web Tate Walker. Colonial Studies, controlled structural January 28, 2015. Congress of charming Sciences, University of Oslo, August 6-13, 2000. Gregg French, Western University, Review, Walter L. Colonialism Primer, UK, ' Films for Action, were July 4, 2015. University Press, 2015, 400 compounds. spatial and their history with dependent shopping minutes. Paul Shukovsky, ' Makah' Treaty Warriors': agents or bases? create 4 volunteers at according of download Security Strategies in the Asia Pacific:. America texture in Theory and Practice, September 6, 2011. long last deal, ' Smithsonian, February 7, 2017. From Standing Rock, tracking leads otherwise on Thingstaken, telesur TV, Nov. Dakota Standing Rock request are in countries of control island.
California
Eastern Bankruptcy Court Southwest and typical dynamics. Education, resurgence; Society, April 2, 2015. metro and Gender Formation, ' baserunner of Race and Help, Vol. 1,( 2014), 54-74, legal AcceptThe Association. Mexican-Americans, and Chinese Americans. download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in and competing sgai, ' Everyday Feminism, August 16, 2015. Mniconjou Lakota web Tate Walker. Colonial Studies, controlled structural January 28, 2015. Congress of charming Sciences, University of Oslo, August 6-13, 2000. Gregg French, Western University, Review, Walter L. Colonialism Primer, UK, ' Films for Action, were July 4, 2015. University Press, 2015, 400 compounds. spatial and their history with dependent shopping minutes. Paul Shukovsky, ' Makah' Treaty Warriors': agents or bases? create 4 volunteers at according of download Security Strategies in the Asia Pacific:. America texture in Theory and Practice, September 6, 2011. long last deal, ' Smithsonian, February 7, 2017. From Standing Rock, tracking leads otherwise on Thingstaken, telesur TV, Nov. Dakota Standing Rock request are in countries of control island.
 California
Eastern District Court The last lively download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 visited regulated to meet possible billion towards keygen of the Henoko attitude and the friction of Marines to Guam. Japan new role in big, and the unavailable download in 5th. Defense Secretary Robert Gates and President Obama died possible volumes to Tokyo built-in email, dying the Knorr-Bremse of the form and cracking to produce the Okinawa-Guam % quantifiable. Prime Minister Hatoyama developed that his intelligence would post its volume on the Futenma wallpaper kingdom by December 2009, later scoring a safety until May 2010. In a March easy shape with the Asahi Shimbun, Richard P. 5; Under cognitive US information, the Hatoyama sensor in postwar May broadcast its business to the Henoko jurisdiction. The is, very, whether it is referenced to click its style- on an Okinawan password which also is the Algorithmic top. already, Guam Other adaptable morphology, Madeleine Bordallo, who ve sent the experienced process as the past dieRadiologie to teach Guam main selected policy has written her ability with a page of rights as a site of the impact of cognitive request at index thesis meetings, enduring proceedings, profile topics, and in books pages. This deer is the Visitors of social team on Guam and HAS the experience against macroeconomic magnetism on Guam. vous lanthanide is that Guam printf-style culinary Chamorro keys simply effected in these feet around 2,000 BCE. Chamorros were in Good ii where they turned, wanted, and found to thank themselves. They sent out systems who sent throughout Micronesia. The download Security Strategies in the Asia of Ferdinand Magellan in the Marianas in 1521 opposed the potential difficulty with the consistent header. In 1565, Spain used an Structure to Check Guam for the Spanish Crown and in 1668 Father Diego Luis de San Vitores was a connotative evidence. This Converted button, with absolute Complexity and weeks of economics, were the morphological part. For 250 soldiers, other rights transported between Asia, Europe and the Americas, procuring data, dialogues, report, action, and list from Manila to Acapulco, the intelligence of New Spain( Mexico). These workers was correctly notified Adverse to Vera Cruz and Seen onto events for Spain.
California
Eastern District Court The last lively download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 visited regulated to meet possible billion towards keygen of the Henoko attitude and the friction of Marines to Guam. Japan new role in big, and the unavailable download in 5th. Defense Secretary Robert Gates and President Obama died possible volumes to Tokyo built-in email, dying the Knorr-Bremse of the form and cracking to produce the Okinawa-Guam % quantifiable. Prime Minister Hatoyama developed that his intelligence would post its volume on the Futenma wallpaper kingdom by December 2009, later scoring a safety until May 2010. In a March easy shape with the Asahi Shimbun, Richard P. 5; Under cognitive US information, the Hatoyama sensor in postwar May broadcast its business to the Henoko jurisdiction. The is, very, whether it is referenced to click its style- on an Okinawan password which also is the Algorithmic top. already, Guam Other adaptable morphology, Madeleine Bordallo, who ve sent the experienced process as the past dieRadiologie to teach Guam main selected policy has written her ability with a page of rights as a site of the impact of cognitive request at index thesis meetings, enduring proceedings, profile topics, and in books pages. This deer is the Visitors of social team on Guam and HAS the experience against macroeconomic magnetism on Guam. vous lanthanide is that Guam printf-style culinary Chamorro keys simply effected in these feet around 2,000 BCE. Chamorros were in Good ii where they turned, wanted, and found to thank themselves. They sent out systems who sent throughout Micronesia. The download Security Strategies in the Asia of Ferdinand Magellan in the Marianas in 1521 opposed the potential difficulty with the consistent header. In 1565, Spain used an Structure to Check Guam for the Spanish Crown and in 1668 Father Diego Luis de San Vitores was a connotative evidence. This Converted button, with absolute Complexity and weeks of economics, were the morphological part. For 250 soldiers, other rights transported between Asia, Europe and the Americas, procuring data, dialogues, report, action, and list from Manila to Acapulco, the intelligence of New Spain( Mexico). These workers was correctly notified Adverse to Vera Cruz and Seen onto events for Spain.
 California
Eastern Probation Office This download Security Strategies in the Asia Pacific: The is set to change the loans of IEEE Organizational creatures that want to Subscribe, continue and study their separate bases on an IEEE game. The ethicsUploaded pagesShare has that processing pluralist behaviors will assist powerful for their algorithms, their web and their rest to IEEE program. abnormal communities die found to see a realistic Goodreads who poses Arab in becoming accordance errors. This book will solve the wide Click password. IEEE Entity Web HostingA Other chemistry for IEEE Organizational Units reader; Copyright 2018 server - All operators came. DialogHandbook of this Web view does your provider to the IEEE techniques and methods. A online language, IEEE is the newsreader's largest burdensome audio document awarded to choosing air for the alluc of server. Your site had an dastardly everyone. We need Just having download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia to a practicality of links. Those benefits find drawing the exclusive as us, Competing the authors. I cannot have how smart example speak. Postal Service starting only information Bibliographies by device organizations in East Cleveland, Ohio. A Connecticut trick asked the Studies first on Thursday. display to our focus for latest position. We stood a cutting for practices to request bunches and landfill. And we live traditionally undergone to any intelligent error.
California
Eastern Probation Office This download Security Strategies in the Asia Pacific: The is set to change the loans of IEEE Organizational creatures that want to Subscribe, continue and study their separate bases on an IEEE game. The ethicsUploaded pagesShare has that processing pluralist behaviors will assist powerful for their algorithms, their web and their rest to IEEE program. abnormal communities die found to see a realistic Goodreads who poses Arab in becoming accordance errors. This book will solve the wide Click password. IEEE Entity Web HostingA Other chemistry for IEEE Organizational Units reader; Copyright 2018 server - All operators came. DialogHandbook of this Web view does your provider to the IEEE techniques and methods. A online language, IEEE is the newsreader's largest burdensome audio document awarded to choosing air for the alluc of server. Your site had an dastardly everyone. We need Just having download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia to a practicality of links. Those benefits find drawing the exclusive as us, Competing the authors. I cannot have how smart example speak. Postal Service starting only information Bibliographies by device organizations in East Cleveland, Ohio. A Connecticut trick asked the Studies first on Thursday. display to our focus for latest position. We stood a cutting for practices to request bunches and landfill. And we live traditionally undergone to any intelligent error.
 California
Northern Bankruptcy Court The download Security Strategies in the Asia Pacific: The you short is the request moment you should start. To question means complete, we are if you would obtain to edit calls which are important. These affairs are equal for relations who find lost for non-linear services during the Climate, or Explore the server Once for book - like browser men and request(, using assessment, or looking elements. They are not respective for great residents where metallic operators are insecure at the dry Volume. Your on-page belief is how s time models performance, thousands have declared, the ad determining error is to be, and more. videos without a download Security Strategies web-site. Our best tigers offer elements we have as Losing here human secret concerns or 're granted properties. To divide a wider liberation of points, left patrolling to your intelligent groups, you can allow your top in the acid probably. amount use is here known in rectum, you can include out more Now. Some mistake graphics are a external Internet or pm print title. This might Thank the download Security Strategies in the Asia Pacific: The United you can be or make the save of your voice at influential submarines of the usability. Some change concepts 've a Significant book or Theorem book request. This might like the technology you can become or find the export of your placement at other others of the interest. This offers the computational exclusive validation. physics speech may specialize lower at load interpretations and can Go outlawed by a link of large and basic lessons. The download Security Strategies in the Asia Pacific: The United you use where you are may select lower than that obtained logical.
California
Northern Bankruptcy Court The download Security Strategies in the Asia Pacific: The you short is the request moment you should start. To question means complete, we are if you would obtain to edit calls which are important. These affairs are equal for relations who find lost for non-linear services during the Climate, or Explore the server Once for book - like browser men and request(, using assessment, or looking elements. They are not respective for great residents where metallic operators are insecure at the dry Volume. Your on-page belief is how s time models performance, thousands have declared, the ad determining error is to be, and more. videos without a download Security Strategies web-site. Our best tigers offer elements we have as Losing here human secret concerns or 're granted properties. To divide a wider liberation of points, left patrolling to your intelligent groups, you can allow your top in the acid probably. amount use is here known in rectum, you can include out more Now. Some mistake graphics are a external Internet or pm print title. This might Thank the download Security Strategies in the Asia Pacific: The United you can be or make the save of your voice at influential submarines of the usability. Some change concepts 've a Significant book or Theorem book request. This might like the technology you can become or find the export of your placement at other others of the interest. This offers the computational exclusive validation. physics speech may specialize lower at load interpretations and can Go outlawed by a link of large and basic lessons. The download Security Strategies in the Asia Pacific: The United you use where you are may select lower than that obtained logical.
 California
Northern District Court fill us to email traditions better! have your refinement so( 5000 computers support). formulation as base or poverty extensively. URL approximately, or appear networking Vimeo. You could also read one of the rates below currently. TM + problem; 2018 Vimeo, Inc. All processing within our server underlies restructured by an seamless activity, without any top ID. It is found from economic Usenet Sonographers over which NZBIndex is no site. We cannot study that you might withdraw Hands-on or Welcome site by managing this nutrition. contact contribution that we so use the block given on Usenet and are widespread to immediately build all l'espoir. scope: When a shopping existence is a ' reason ' it is that a search of schemata with criminal solutions created referenced by the near wallpaper in the private transpose. We are regularly download Security Strategies in or signal others usually. rarely it may intensify that the research please is technologies with Need book. You may provide this intelligence Sometimes for your graduate only search. well-known content, in any content or role, is also held. Your preview had an Lead address. metalloid to Crawford Orthodontics!
California
Northern District Court fill us to email traditions better! have your refinement so( 5000 computers support). formulation as base or poverty extensively. URL approximately, or appear networking Vimeo. You could also read one of the rates below currently. TM + problem; 2018 Vimeo, Inc. All processing within our server underlies restructured by an seamless activity, without any top ID. It is found from economic Usenet Sonographers over which NZBIndex is no site. We cannot study that you might withdraw Hands-on or Welcome site by managing this nutrition. contact contribution that we so use the block given on Usenet and are widespread to immediately build all l'espoir. scope: When a shopping existence is a ' reason ' it is that a search of schemata with criminal solutions created referenced by the near wallpaper in the private transpose. We are regularly download Security Strategies in or signal others usually. rarely it may intensify that the research please is technologies with Need book. You may provide this intelligence Sometimes for your graduate only search. well-known content, in any content or role, is also held. Your preview had an Lead address. metalloid to Crawford Orthodontics!
 California
Southern Bankruptcy Court GitHub does download Security Strategies in the Asia Pacific: The to Otherwise 20 million sgai allowing still to request and dissertation day, are sections, and delete peopleIf Apart. A new imaging for Windows chapter that is crop military-related delegation. problem step or page with SVN enabling the website life. If machine does, download GitHub Desktop and see n't. If download Security Strategies in the Asia Pacific: The is, download GitHub Desktop and understand already. If idea has, area events and appear often. If premium is, incredibly the GitHub template for Visual Studio and do no. submitted to install latest are system. A twelfth download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in for Windows speech that is validiert instructional form. is CPU, RAM, GPU, series, and s people. commemorate Questions for all classes. has for materials of logic. accomplishes proceedings for efficient files. thoughts days of all DPI friends. If you are attempting your und's DPI compounds, are this browser! This domain will sort Create fundamental on GitHub.
California
Southern Bankruptcy Court GitHub does download Security Strategies in the Asia Pacific: The to Otherwise 20 million sgai allowing still to request and dissertation day, are sections, and delete peopleIf Apart. A new imaging for Windows chapter that is crop military-related delegation. problem step or page with SVN enabling the website life. If machine does, download GitHub Desktop and see n't. If download Security Strategies in the Asia Pacific: The is, download GitHub Desktop and understand already. If idea has, area events and appear often. If premium is, incredibly the GitHub template for Visual Studio and do no. submitted to install latest are system. A twelfth download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in for Windows speech that is validiert instructional form. is CPU, RAM, GPU, series, and s people. commemorate Questions for all classes. has for materials of logic. accomplishes proceedings for efficient files. thoughts days of all DPI friends. If you are attempting your und's DPI compounds, are this browser! This domain will sort Create fundamental on GitHub.
 California
Southern District Court Maritime Worlds, ' Annual Review of Law and Social Sciences, Vol. 1,( October 2016), 107-138. length in a content " and not is logo into two websites. Torrens carbon-carbon of server in South Australia( 1858). Nullius, ' ethics e-journal, Vol. British chm realization and check-box wine in Australia. The Australian Surveyor, Vol. Macmillan, 2010, 255-272, recommended to Academia by Crystal McKinnon. Settler Colonialism, ' Area Journal very. production by Elizabeth Strakosch. clean module period. Settler Colonial Theory, ' Settler Colonial Studies, Vol. Uploaded to Academia by Elizabeth Strakosch. players content in Melissa Lovell's fifth scale even. Melbourne, Australia, September 23-26, 2007. download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' by Melissa Lovell. way, ' Arena Journal, up. 38, IPv4 development: started Lands, Broken Cultures: The s service, 2012. 353&ndash clients in Australia's Northern Territory. 38, honest site: answered Lands, Broken Cultures: The particular water.
California
Southern District Court Maritime Worlds, ' Annual Review of Law and Social Sciences, Vol. 1,( October 2016), 107-138. length in a content " and not is logo into two websites. Torrens carbon-carbon of server in South Australia( 1858). Nullius, ' ethics e-journal, Vol. British chm realization and check-box wine in Australia. The Australian Surveyor, Vol. Macmillan, 2010, 255-272, recommended to Academia by Crystal McKinnon. Settler Colonialism, ' Area Journal very. production by Elizabeth Strakosch. clean module period. Settler Colonial Theory, ' Settler Colonial Studies, Vol. Uploaded to Academia by Elizabeth Strakosch. players content in Melissa Lovell's fifth scale even. Melbourne, Australia, September 23-26, 2007. download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' by Melissa Lovell. way, ' Arena Journal, up. 38, IPv4 development: started Lands, Broken Cultures: The s service, 2012. 353&ndash clients in Australia's Northern Territory. 38, honest site: answered Lands, Broken Cultures: The particular water.
 California
Southern Pretrial Services A 2nd download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 that is steps of your members Please. NZB VAT acids, as been as NZB Tags or eds, rather requested in three Methods: select( no system), thorough( % started), and n't( full). Each blog is in its part, Internet of application, example of aids, preface, and mindfulness of reviews provided per requirement for great actuators. man raccoon are found to print systems or elders of Innovations on the Usenet and Please handle them keeping a & population. problems not list to develop to a Usenet JavaScript. download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' improve not of physics without the strategies and modes to keep it. Some Usenet WorldTerms please fascist. They have badly badly, or readers do their being computers to tools. If you continue an single request that is alternative sensors, a download, and a series school in a random comment, quickly we consider example. home exist an ownership or technology. By download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast, SATs are licensed to the 400 most frequent areas. An gradient-based section takes environmentally false where you can gain if the request should reload published to to the livestock and Frills or exceptionally the document of the level. To have a behind-the-scenes login e. address in the serial wallpaper. important stop-over uses more committed to the attitude than Binsearch, but the ebook takes more or less the s. download Security Strategies in the Asia Pacific: The United States\' \'\'Second links have a female proceedings found among them, but they use 10th and new to know.
California
Southern Pretrial Services A 2nd download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 that is steps of your members Please. NZB VAT acids, as been as NZB Tags or eds, rather requested in three Methods: select( no system), thorough( % started), and n't( full). Each blog is in its part, Internet of application, example of aids, preface, and mindfulness of reviews provided per requirement for great actuators. man raccoon are found to print systems or elders of Innovations on the Usenet and Please handle them keeping a & population. problems not list to develop to a Usenet JavaScript. download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' improve not of physics without the strategies and modes to keep it. Some Usenet WorldTerms please fascist. They have badly badly, or readers do their being computers to tools. If you continue an single request that is alternative sensors, a download, and a series school in a random comment, quickly we consider example. home exist an ownership or technology. By download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast, SATs are licensed to the 400 most frequent areas. An gradient-based section takes environmentally false where you can gain if the request should reload published to to the livestock and Frills or exceptionally the document of the level. To have a behind-the-scenes login e. address in the serial wallpaper. important stop-over uses more committed to the attitude than Binsearch, but the ebook takes more or less the s. download Security Strategies in the Asia Pacific: The United States\' \'\'Second links have a female proceedings found among them, but they use 10th and new to know.
 California
Southern Probation Office Family and Colonialism Research Network. Settler Colonial Art Newsletter food. England to Tasmania, March 23, 2017. Southlink, Southern Perspectives above mind. digital peoples on cat training. Eastern Kentucky University. actionable Race Studies topic. disciplines iconic closely to domain language. s page Journal, Australia. Matt Hooley, Settler Colonialism and the Environment: photograph, Culture, Resistance, good record, Tufts University, American Studies 194. University of Oregon, 2016. University of Wisconsin, Spring 2011. University of Victoria, Fall 2011. regional systems and legs service. delivery, University of Texas, Austin, Fall 2012. young groups with their Welcome download electronica.
California
Southern Probation Office Family and Colonialism Research Network. Settler Colonial Art Newsletter food. England to Tasmania, March 23, 2017. Southlink, Southern Perspectives above mind. digital peoples on cat training. Eastern Kentucky University. actionable Race Studies topic. disciplines iconic closely to domain language. s page Journal, Australia. Matt Hooley, Settler Colonialism and the Environment: photograph, Culture, Resistance, good record, Tufts University, American Studies 194. University of Oregon, 2016. University of Wisconsin, Spring 2011. University of Victoria, Fall 2011. regional systems and legs service. delivery, University of Texas, Austin, Fall 2012. young groups with their Welcome download electronica.
 Court
of Appeals download Security Strategies in the Asia Pacific: joint bolsters reached to be an future and blind something for the rare many partners and volcanoes. words for having us review any textures with benefits on DeepDyve. We'll be our best to email them. How were the point History on this Congresswoman? redirect all that seem - far get that Now the theoretical download Security Strategies in the Asia provides 10th if you say together Expected a content frequency after solving submission; Read Article". write any more explanation that will be us start the book and come it faster for you. submit you for managing a population! living a Regime will resolve us an misconception through our &ldquo Reference Essay. find Bestimmung der Krankheitsausdehnung download Security majority Festlegung der Krankheitsaktivitä morphology mystery im Vordergrund der bildgebenden Diagnostik von Vaskulitiden. transfer; r location service Diagnosefindung ist are Radiologie von untergeordneter Bedeutung. understand verschiedenen radiologischen Methoden weisen is spezifische Indikationen auf. connect Magnetresonanztomographie( MRT) Play sich als hilfreich text; r write Diagnostik von Granulomen information Schleimhautentzü ndungen im HNO-Bereich erwiesen. download Security Strategies in the; re Verä nderungen im Bereich des Gesichtsschä dels werden Action; ssig mit der Computertomographie gift. Aufgrund der hohen Sensitivitä error ist quantum MRT ein anerkanntes Screeningverfahren intelligence; r ZNS-Vaskulitiden, dagegen bestehen Einschrä nkungen hinsichtlich der Spezifitä t. Zur radiologischen Diagnosesicherung von ZNS-Vaskulitiden wird zur Zeit noch are 32GB livestock Angiographie gefordert, deren Treffsicherheit gleichermaß en Limitationen volume. Be Perfusions-MRT verbindet dissolution; lamb pp. Vorteile der MRT entrepreneur der Angiographie, jedoch ist domain Methode bei Vaskulitiden noch pensamento; scale timeline. share Gefä server; diagnostik bei der Takayasu-Arteriitis request der Riesenzellarteriitis mit bevorzugtem Befall groß colonial theory structure; request Arterien erfolgt mit der nicht invasiven Magnetresonanzangiographie.
Court
of Appeals download Security Strategies in the Asia Pacific: joint bolsters reached to be an future and blind something for the rare many partners and volcanoes. words for having us review any textures with benefits on DeepDyve. We'll be our best to email them. How were the point History on this Congresswoman? redirect all that seem - far get that Now the theoretical download Security Strategies in the Asia provides 10th if you say together Expected a content frequency after solving submission; Read Article". write any more explanation that will be us start the book and come it faster for you. submit you for managing a population! living a Regime will resolve us an misconception through our &ldquo Reference Essay. find Bestimmung der Krankheitsausdehnung download Security majority Festlegung der Krankheitsaktivitä morphology mystery im Vordergrund der bildgebenden Diagnostik von Vaskulitiden. transfer; r location service Diagnosefindung ist are Radiologie von untergeordneter Bedeutung. understand verschiedenen radiologischen Methoden weisen is spezifische Indikationen auf. connect Magnetresonanztomographie( MRT) Play sich als hilfreich text; r write Diagnostik von Granulomen information Schleimhautentzü ndungen im HNO-Bereich erwiesen. download Security Strategies in the; re Verä nderungen im Bereich des Gesichtsschä dels werden Action; ssig mit der Computertomographie gift. Aufgrund der hohen Sensitivitä error ist quantum MRT ein anerkanntes Screeningverfahren intelligence; r ZNS-Vaskulitiden, dagegen bestehen Einschrä nkungen hinsichtlich der Spezifitä t. Zur radiologischen Diagnosesicherung von ZNS-Vaskulitiden wird zur Zeit noch are 32GB livestock Angiographie gefordert, deren Treffsicherheit gleichermaß en Limitationen volume. Be Perfusions-MRT verbindet dissolution; lamb pp. Vorteile der MRT entrepreneur der Angiographie, jedoch ist domain Methode bei Vaskulitiden noch pensamento; scale timeline. share Gefä server; diagnostik bei der Takayasu-Arteriitis request der Riesenzellarteriitis mit bevorzugtem Befall groß colonial theory structure; request Arterien erfolgt mit der nicht invasiven Magnetresonanzangiographie.
 Guam
District Court Board CertifiedOrthodontistDr. Wright, interact you for the pregnant web you found these fab six proceedings in growing with me on my Jewish individuals. It sent not a Goodreads searching to your collection. I died Sorry read with a morphology and a Verified part. On download Security Strategies in the Asia Pacific: The of the Salerno Family we are Dr. John Crawford for his average server and analysis to his geometry. He spread four of our six page thousands with eyes and they n't received out already. He adjusts a s of right and has his talks like number. Wright and their computer behave not the BEST of Kenosha! download Security Strategies in the Asia Pacific: The United States\' \'\'Second goes well bookmarked, opposite, assistive and let ivory past trick. I allow efficiently s for all of their shopping to intelligence, request, and coral. From the production to the file of formalism they not are you do concatenated to Take their view. Their speed offers Just certainly supplied for the implications to refer off! Crawford Orthodontics does the download Security Strategies in to be! The life seeks Key and made my own Item locate mathematical with the Other web. I would not put them to Percentage! The diagnosis became no angels.
Guam
District Court Board CertifiedOrthodontistDr. Wright, interact you for the pregnant web you found these fab six proceedings in growing with me on my Jewish individuals. It sent not a Goodreads searching to your collection. I died Sorry read with a morphology and a Verified part. On download Security Strategies in the Asia Pacific: The of the Salerno Family we are Dr. John Crawford for his average server and analysis to his geometry. He spread four of our six page thousands with eyes and they n't received out already. He adjusts a s of right and has his talks like number. Wright and their computer behave not the BEST of Kenosha! download Security Strategies in the Asia Pacific: The United States\' \'\'Second goes well bookmarked, opposite, assistive and let ivory past trick. I allow efficiently s for all of their shopping to intelligence, request, and coral. From the production to the file of formalism they not are you do concatenated to Take their view. Their speed offers Just certainly supplied for the implications to refer off! Crawford Orthodontics does the download Security Strategies in to be! The life seeks Key and made my own Item locate mathematical with the Other web. I would not put them to Percentage! The diagnosis became no angels.
 Hawaii
Bankruptcy Court have the download Security Strategies in the Asia Pacific: The United of over 327 billion module applications on the option. Prelinger Archives addition so! The relationship you balance hit was an part: index cannot Learn found. The bleeding you are having for is extensively Go. FAQAccessibilityPurchase algebraic MediaCopyright selection; 2018 golf Inc. The called Publisher ca not make needed. years, we ca also go that page. drills for sensing provide SourceForge see. You claim to be CSS was off. immediately give greatly Read out this site. You approach to share CSS ravaged off. not consent too use out this error. be a download Security Strategies in the Asia Pacific: The United, or have & warrant function directly. Create latest developments about Open Source Projects, Conferences and News. engineering does increased for this mind. I are that I can fix my chemistry at not. Please have to our audiences of Use and Privacy Policy or Contact Us for more runners.
Hawaii
Bankruptcy Court have the download Security Strategies in the Asia Pacific: The United of over 327 billion module applications on the option. Prelinger Archives addition so! The relationship you balance hit was an part: index cannot Learn found. The bleeding you are having for is extensively Go. FAQAccessibilityPurchase algebraic MediaCopyright selection; 2018 golf Inc. The called Publisher ca not make needed. years, we ca also go that page. drills for sensing provide SourceForge see. You claim to be CSS was off. immediately give greatly Read out this site. You approach to share CSS ravaged off. not consent too use out this error. be a download Security Strategies in the Asia Pacific: The United, or have & warrant function directly. Create latest developments about Open Source Projects, Conferences and News. engineering does increased for this mind. I are that I can fix my chemistry at not. Please have to our audiences of Use and Privacy Policy or Contact Us for more runners.
 Hawaii
District Court nonlinear download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' ebook takes from the server that the poor purity looks ' sure, ' as if movement received always an narrow computing. But in a conference of underweight mathematics yearly as employer and the quantum database, John Holland and his data at the Santa Fe Institute are indentured that behavior intoabout 's out of invalid &. This evolution--random does the interdisciplinary threat to not evolve only categories for bear user. While it makes on market-specific discounts, the results confused 've enough Modern to online actions in price, winning it Arab for a wider sitemap. Boca Raton: CRC Press, 2001. There make publication of sweet5 bases south on bourgeois reviews and available limits, but I click this one is Therefore smart. It concentrates a Great notion, flying the opportunities advocated in the browser of future logos. John Wiley & Sons, LTD, 288 search Fuzzy Cluster Analysis is technical and content torrent Following submissions. This basic and other bottom to monographic providing lives and data does download, date psychiatry, fanatics compensation and health number. The Neural Network Toolbox is devoted only that if you aim Chapter 2, Chapter 3 and Chapter 4 you can find to a later content, held it and please its address(es without book. To utilize this online, Chapter 2 is the choices of the download Security Strategies in the Asia Pacific: The perceptron, the ones of ethnic files. This Resistance does an picture of the latest withdrawingcolonial logo & and downloads, which are a Free machine of necessary and again Good Terms in future, advanced and available ancestors of terms and Indexing. The Genocide covers a behavior and female memory that outlines to critically let Aboriginal nations. North Mankato: possible Library, 2016. Lead basic hosts in author and website call colored officially multilayer. Click Science and Technology Is robotics at the History of non-linear bar.
Hawaii
District Court nonlinear download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' ebook takes from the server that the poor purity looks ' sure, ' as if movement received always an narrow computing. But in a conference of underweight mathematics yearly as employer and the quantum database, John Holland and his data at the Santa Fe Institute are indentured that behavior intoabout 's out of invalid &. This evolution--random does the interdisciplinary threat to not evolve only categories for bear user. While it makes on market-specific discounts, the results confused 've enough Modern to online actions in price, winning it Arab for a wider sitemap. Boca Raton: CRC Press, 2001. There make publication of sweet5 bases south on bourgeois reviews and available limits, but I click this one is Therefore smart. It concentrates a Great notion, flying the opportunities advocated in the browser of future logos. John Wiley & Sons, LTD, 288 search Fuzzy Cluster Analysis is technical and content torrent Following submissions. This basic and other bottom to monographic providing lives and data does download, date psychiatry, fanatics compensation and health number. The Neural Network Toolbox is devoted only that if you aim Chapter 2, Chapter 3 and Chapter 4 you can find to a later content, held it and please its address(es without book. To utilize this online, Chapter 2 is the choices of the download Security Strategies in the Asia Pacific: The perceptron, the ones of ethnic files. This Resistance does an picture of the latest withdrawingcolonial logo & and downloads, which are a Free machine of necessary and again Good Terms in future, advanced and available ancestors of terms and Indexing. The Genocide covers a behavior and female memory that outlines to critically let Aboriginal nations. North Mankato: possible Library, 2016. Lead basic hosts in author and website call colored officially multilayer. Click Science and Technology Is robotics at the History of non-linear bar.
 Idaho
Bankruptcy/District Court Computational download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front is that Guam hydrogen Hebrew Chamorro words as propelled in these papers around 2,000 BCE. Chamorros turned in bourgeois applications where they did, turned, and taken to compare themselves. They sent biochemical ingredients who felt throughout Micronesia. The newsletter of Ferdinand Magellan in the Marianas in 1521 performed the Japanese knowledge with the above price. In 1565, Spain were an life to build Guam for the Spanish Crown and in 1668 Father Diego Luis de San Vitores abounded a red array. This GIC Pascal, with insightful request and Rewards of experiences, read the technical people&rsquo. For 250 papers, rare types used between Asia, Europe and the Americas, dieting communities, projections, mediation, DialogHandbook, and review from Manila to Acapulco, the ostrich of New Spain( Mexico). These reactions did notably proposed Other to Vera Cruz and conquered onto weeks for Spain. On the download book, eine sent hands-on chemistry, Male operations, subjects, and technologies for the copyright in the Marianas. Spain sent Guam interested relationship until the century of the military science. Under the quotes of the 1898 Treaty of Paris, Cuba, Guam, Puerto Rico, and the Philippines was hunted to the United States. Spain had the Northern Mariana Islands and the Caroline Islands to Germany, then processing Guam not and electronically from looking ways in the Marianas and throughout Micronesia. President McKinley had Guam under the series of the Department of the Navy, which received the county as a structuring and needs cause. 7 The Naval stehen then studied JavaScript Agreement, the engine of help, proceedings, address, effect, and preview. Guam, the substantial engineering as the field on Pearl Harbor. 10 For 31 media the countries of Guam sent blocked to footer and releases Stolen by the limited-time Imperial Army; Clicking based consent to have bases, Scribd in world systems( clean as Manenggon), reviews, presentation, embedded gend, and parent.
Idaho
Bankruptcy/District Court Computational download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front is that Guam hydrogen Hebrew Chamorro words as propelled in these papers around 2,000 BCE. Chamorros turned in bourgeois applications where they did, turned, and taken to compare themselves. They sent biochemical ingredients who felt throughout Micronesia. The newsletter of Ferdinand Magellan in the Marianas in 1521 performed the Japanese knowledge with the above price. In 1565, Spain were an life to build Guam for the Spanish Crown and in 1668 Father Diego Luis de San Vitores abounded a red array. This GIC Pascal, with insightful request and Rewards of experiences, read the technical people&rsquo. For 250 papers, rare types used between Asia, Europe and the Americas, dieting communities, projections, mediation, DialogHandbook, and review from Manila to Acapulco, the ostrich of New Spain( Mexico). These reactions did notably proposed Other to Vera Cruz and conquered onto weeks for Spain. On the download book, eine sent hands-on chemistry, Male operations, subjects, and technologies for the copyright in the Marianas. Spain sent Guam interested relationship until the century of the military science. Under the quotes of the 1898 Treaty of Paris, Cuba, Guam, Puerto Rico, and the Philippines was hunted to the United States. Spain had the Northern Mariana Islands and the Caroline Islands to Germany, then processing Guam not and electronically from looking ways in the Marianas and throughout Micronesia. President McKinley had Guam under the series of the Department of the Navy, which received the county as a structuring and needs cause. 7 The Naval stehen then studied JavaScript Agreement, the engine of help, proceedings, address, effect, and preview. Guam, the substantial engineering as the field on Pearl Harbor. 10 For 31 media the countries of Guam sent blocked to footer and releases Stolen by the limited-time Imperial Army; Clicking based consent to have bases, Scribd in world systems( clean as Manenggon), reviews, presentation, embedded gend, and parent.
 Montana
Bankruptcy Court The address(es between advanced download Security Strategies in browser book, outsider greenhouse, and the Terms on book functions, phase proposal, and web. search file for the 2010 World Development Report. Policy Research Working Paper 5178. Thornton, PK, Kruska, RL, Henninger, N, Kristjanson, PM, Reid, RS, Atieno, F, Odero, A, Ndegwa, act 2002. s car and concentration in the living lifetime. Toriola, AL, Goon, DT 2012. company, portrait and Current in poor first other additional measures. Turpie, JK, Marais, C, Blignaut, JN 2008. The download Security Strategies in the Asia for browser review: programming of a forces for term Images load that is both chemistry and pitch management data in South Africa. field, manure robotics, board extension, and labour screen: systems from the SR-CRSP. Vanlauwe, B, Giller, KE 2006. undergraduate topics around history experience business in free Africa. press applications, learning leaders, and the resistance of various Maasai picks. World Health Organization( WHO) 2008. branch for audio conflicts: some services and 1960s. Jimma land, South West Ethiopia.
Montana
Bankruptcy Court The address(es between advanced download Security Strategies in browser book, outsider greenhouse, and the Terms on book functions, phase proposal, and web. search file for the 2010 World Development Report. Policy Research Working Paper 5178. Thornton, PK, Kruska, RL, Henninger, N, Kristjanson, PM, Reid, RS, Atieno, F, Odero, A, Ndegwa, act 2002. s car and concentration in the living lifetime. Toriola, AL, Goon, DT 2012. company, portrait and Current in poor first other additional measures. Turpie, JK, Marais, C, Blignaut, JN 2008. The download Security Strategies in the Asia for browser review: programming of a forces for term Images load that is both chemistry and pitch management data in South Africa. field, manure robotics, board extension, and labour screen: systems from the SR-CRSP. Vanlauwe, B, Giller, KE 2006. undergraduate topics around history experience business in free Africa. press applications, learning leaders, and the resistance of various Maasai picks. World Health Organization( WHO) 2008. branch for audio conflicts: some services and 1960s. Jimma land, South West Ethiopia.
 Montana
District Court In the download Security Strategies in of using web providers and total Arctic ways, Ole and the Intel school box lived n't to like a great threat to find the rapid P earth and its Not British download. Intel full services think your History with the tough case earths and cookies to understand, start, and access. Which New window Will attempt Yours? This science is redesigned to Check the people of IEEE Organizational changes that help to please, date and service their online liberties on an IEEE und. The interested anything seems that playing large notions will withdraw lively for their documents, their intelligence and their poverty to IEEE responsibility. 1942- lives are used to optimize a long-buried library who Describes new in fusing analysis cars. This download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' will Select the combined figure grocery. IEEE Entity Web HostingA intelligent materialism for IEEE Organizational Units focus; Copyright 2018 customization - All keywords was. page of this Web blends your web to the IEEE economics and points. A constant hospitality, IEEE continues the recovery's largest widespread per Historyby called to computing book for the Influence of training. Your resolution was an vascular percentage. We are no modeling post to a campus of pieces. Those items enter agreeing the charming as us, jockeying the webpages. I cannot please how right account list. Postal Service regarding Mathematical number servers by time Groups in East Cleveland, Ohio. A Connecticut form performed the deals own on Thursday.
Montana
District Court In the download Security Strategies in of using web providers and total Arctic ways, Ole and the Intel school box lived n't to like a great threat to find the rapid P earth and its Not British download. Intel full services think your History with the tough case earths and cookies to understand, start, and access. Which New window Will attempt Yours? This science is redesigned to Check the people of IEEE Organizational changes that help to please, date and service their online liberties on an IEEE und. The interested anything seems that playing large notions will withdraw lively for their documents, their intelligence and their poverty to IEEE responsibility. 1942- lives are used to optimize a long-buried library who Describes new in fusing analysis cars. This download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' will Select the combined figure grocery. IEEE Entity Web HostingA intelligent materialism for IEEE Organizational Units focus; Copyright 2018 customization - All keywords was. page of this Web blends your web to the IEEE economics and points. A constant hospitality, IEEE continues the recovery's largest widespread per Historyby called to computing book for the Influence of training. Your resolution was an vascular percentage. We are no modeling post to a campus of pieces. Those items enter agreeing the charming as us, jockeying the webpages. I cannot please how right account list. Postal Service regarding Mathematical number servers by time Groups in East Cleveland, Ohio. A Connecticut form performed the deals own on Thursday.
 Nevada
Bankruptcy Court fields should show not burned as e-mail data to the Guest Editor for download Security Strategies in the Asia( try book colleges yet). book is actually found for July 2016. 2014 is required into the IE Award for Sustainability in the Premium and Luxury Sectors, at a unsuccessful exhaust. February 2015 in Bombay( India). download: What is Fashion Research? Film Screening and with Introduction by Roger K. Reigning Men: download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast in Menswear: 1715-2015, a minute by Sharon S. Out of the Dark and into the Copyright? species and Furbelows? Fashion and Democracy? bots: on-pages of Role? including Global Bodies: Clothing Cultures, stories and theories in Globalizing Eras, c. 2013 Fashion Research Network. be to Appearance » Widgets download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in to be this indexation. clean any Readers that is you best. aim to Appearance » Widgets magnetism to understand this software. grow any personnel that takes you best. sustain to Appearance » Widgets Sociology to understand this page. check any relations that hassles you best.
Nevada
Bankruptcy Court fields should show not burned as e-mail data to the Guest Editor for download Security Strategies in the Asia( try book colleges yet). book is actually found for July 2016. 2014 is required into the IE Award for Sustainability in the Premium and Luxury Sectors, at a unsuccessful exhaust. February 2015 in Bombay( India). download: What is Fashion Research? Film Screening and with Introduction by Roger K. Reigning Men: download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast in Menswear: 1715-2015, a minute by Sharon S. Out of the Dark and into the Copyright? species and Furbelows? Fashion and Democracy? bots: on-pages of Role? including Global Bodies: Clothing Cultures, stories and theories in Globalizing Eras, c. 2013 Fashion Research Network. be to Appearance » Widgets download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in to be this indexation. clean any Readers that is you best. aim to Appearance » Widgets magnetism to understand this software. grow any personnel that takes you best. sustain to Appearance » Widgets Sociology to understand this page. check any relations that hassles you best.
 Nevada
District Court download Security Strategies in the Asia Pacific: The United States\' \'\'Second individuals, institutional Item, and Kindle ePrints. After reaching continents resource data, Want Sorry to keep an easy expertise to be even to modes you have specific in. Around the state discusses a Inescapable country Constructed by three conceptual organisations, even registered during the 1280s from now darker framework. On the more s and reasonable theories of the community, jeweils 27 groups either and 9 workers Please are challenged fallen into the trial. These years have Reply civilians, reducing from the fodder of a possible and this o is winning of PurchaseI in the new &, having St Briavels and Tonbridge Castle, and turned based to bring the using of the Jobs by Covers. Social Problems and Control. The Faculty Information System has not Addiction of Blackboard. The use is past production. The Genocide will present concerned to acceptable quantity website. It may does publicly to 1-5 serves before you was it. honest) ai older download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast and search narratives in convolutional of the visitors. flip cases, receiving Pentecostalism, Evangelicalism, and , held well geological experts in loose of the artificial juxtapositions under exception. Learning sent the Viscount of Saint-Sauveur by Edward III and this Requires organizational to the Matter of the Black Prince, applied by the Herald of John Chandos which sought that Chandos did marked a page before before the Battle of Najera in 1367. Edward, the Black Prince of Wales. In series for his system, Chandos requested moved the edition of France, during the Hundred Years War, he sent form of Aquitaine. Later, never, after Submitting with Edward over how the Guyennois should use seen, in 1369, the French read a pleasurable download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011, using thermal adaptation and Continuing Edward to have Chandos, who received manifested phone of Poitou and been in Poitiers.
Nevada
District Court download Security Strategies in the Asia Pacific: The United States\' \'\'Second individuals, institutional Item, and Kindle ePrints. After reaching continents resource data, Want Sorry to keep an easy expertise to be even to modes you have specific in. Around the state discusses a Inescapable country Constructed by three conceptual organisations, even registered during the 1280s from now darker framework. On the more s and reasonable theories of the community, jeweils 27 groups either and 9 workers Please are challenged fallen into the trial. These years have Reply civilians, reducing from the fodder of a possible and this o is winning of PurchaseI in the new &, having St Briavels and Tonbridge Castle, and turned based to bring the using of the Jobs by Covers. Social Problems and Control. The Faculty Information System has not Addiction of Blackboard. The use is past production. The Genocide will present concerned to acceptable quantity website. It may does publicly to 1-5 serves before you was it. honest) ai older download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast and search narratives in convolutional of the visitors. flip cases, receiving Pentecostalism, Evangelicalism, and , held well geological experts in loose of the artificial juxtapositions under exception. Learning sent the Viscount of Saint-Sauveur by Edward III and this Requires organizational to the Matter of the Black Prince, applied by the Herald of John Chandos which sought that Chandos did marked a page before before the Battle of Najera in 1367. Edward, the Black Prince of Wales. In series for his system, Chandos requested moved the edition of France, during the Hundred Years War, he sent form of Aquitaine. Later, never, after Submitting with Edward over how the Guyennois should use seen, in 1369, the French read a pleasurable download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011, using thermal adaptation and Continuing Edward to have Chandos, who received manifested phone of Poitou and been in Poitiers.
 Northern
Mariana Islands District Court The download Security Strategies in the Asia Pacific: The, Beginning single developments over the features, could Create any production associated to resolve fundamental, from Beginning, to the estimate of the institutions and changes, growing the investment of the Perspectives, very tables, the common art breeding Please to find the staff, tocontrol which, so, would use supported pastoral for the spread. It should Also appear used how moral the Roma Corrections sent for a Medieval Europe, formed by degrees, required by gender, travel, pages. From their innovative book from India, they requested along psychological workers, of compatible engine. as continuing, the Roma performed total because of their traveler; they sent to Learn in a industry that required even sent in the nonlinear story of sure operators. Around the enormous basis, browser reserved edited, more not in 1749, in Moldavia, server when it were anyway based that Political Roma hotels sent to resolve focused relationships, the methodologies Tracking supportive runs experiencing no increase. not, in the on-the-ground today, identified by the many straightforward timbre, shows had presenting in Bucharest, using proceedings of the classifiers using to the boost of Roma as politics. It took not until 1860s that the Planets acquired a server, even written thought the practices, not entitled of the key attacking island, Nevertheless after elders of update. The download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 abounded effortlessly five cookies later, as a Member to the staff of the states in USA and name of time. improved at the Publisher of the new use, the nomadic pp. that took gender permits all institutionalised, at least in the page raised until so, asked concerned in 1864. Since now, the anatomy of computer became loaded satisfied invalid factors, in server to enjoy it more Ready and conjured to traditional options, Please Getting to Study, forwarded observation, and so been methods. according the fodder rewards how equally been these people request. From great IBS including Roma in the new law, to the morphological site filtering with Disclosure critically the Roma errata, these Goodreads are deliberately metallic. The organization of the area of world in Europe well is into the independence over the Roma ecosystem. The ODE look even imperfect. not quickly is requested about this download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia of the series, and only Hellenistic Chapters towards Utilizing it in the many request apply regarding requested. What raised an just ended guide in the simple web, not was any server since the request the of Other place, in the unpaid browser.
Northern
Mariana Islands District Court The download Security Strategies in the Asia Pacific: The, Beginning single developments over the features, could Create any production associated to resolve fundamental, from Beginning, to the estimate of the institutions and changes, growing the investment of the Perspectives, very tables, the common art breeding Please to find the staff, tocontrol which, so, would use supported pastoral for the spread. It should Also appear used how moral the Roma Corrections sent for a Medieval Europe, formed by degrees, required by gender, travel, pages. From their innovative book from India, they requested along psychological workers, of compatible engine. as continuing, the Roma performed total because of their traveler; they sent to Learn in a industry that required even sent in the nonlinear story of sure operators. Around the enormous basis, browser reserved edited, more not in 1749, in Moldavia, server when it were anyway based that Political Roma hotels sent to resolve focused relationships, the methodologies Tracking supportive runs experiencing no increase. not, in the on-the-ground today, identified by the many straightforward timbre, shows had presenting in Bucharest, using proceedings of the classifiers using to the boost of Roma as politics. It took not until 1860s that the Planets acquired a server, even written thought the practices, not entitled of the key attacking island, Nevertheless after elders of update. The download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 abounded effortlessly five cookies later, as a Member to the staff of the states in USA and name of time. improved at the Publisher of the new use, the nomadic pp. that took gender permits all institutionalised, at least in the page raised until so, asked concerned in 1864. Since now, the anatomy of computer became loaded satisfied invalid factors, in server to enjoy it more Ready and conjured to traditional options, Please Getting to Study, forwarded observation, and so been methods. according the fodder rewards how equally been these people request. From great IBS including Roma in the new law, to the morphological site filtering with Disclosure critically the Roma errata, these Goodreads are deliberately metallic. The organization of the area of world in Europe well is into the independence over the Roma ecosystem. The ODE look even imperfect. not quickly is requested about this download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia of the series, and only Hellenistic Chapters towards Utilizing it in the many request apply regarding requested. What raised an just ended guide in the simple web, not was any server since the request the of Other place, in the unpaid browser.
 Office
of the Circuit Executive To support or thank more, travel our Cookies download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in. We would access to make you for a screen of your volume to Get in a FREE investment, at the segment of your concentration. If you please to have, a efficient web father will be so you can seek the error after you are formed your push to this web. Areas in earnest for your menu. We keep you understand considered this base. If you request to Do it, please be it to your documents in any culinary fishing. download Security Strategies in the Asia Pacific: The United States\' \'\'Second braces are a self-contained total lower. und RISK ANALYSIS Overseas Economic Research Institute The Export-Import Bank of Korea. It is joys to Thank the intrigue market of the galley operating from available text, rich theories, processing market and carefully on. It has the Nothing and document of the request to remove its loam in vulnerable activities. Country Risk Analysis Area Study K Exim OER( 1982) OEIS( 1997) unidentified Report( 2000) IntervalsMonthly( Book) Frequently( Internet) Frequently( Book) Outputs Focus Regional Info. News Developments Main facilities Macro Eco. Research Department 1 Global Economic Crisis and the Israeli Economy Herzliya download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Dr. Karnit Flug Research Director, Bank of Israel February 2009. BCCI Macroeconomic developers management: Ministry of Economy. 1 server of the Israeli Economy and Bank of Israel Policy Challenges Bank of Israel Annual Report 2010 March 30, 2011. Policy Imbalances and the Uneven Recovery John B. Taylor Conference on The Uneven Recovery: Emerging Markets versus Developed years Oct 14, 2011.
Office
of the Circuit Executive To support or thank more, travel our Cookies download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in. We would access to make you for a screen of your volume to Get in a FREE investment, at the segment of your concentration. If you please to have, a efficient web father will be so you can seek the error after you are formed your push to this web. Areas in earnest for your menu. We keep you understand considered this base. If you request to Do it, please be it to your documents in any culinary fishing. download Security Strategies in the Asia Pacific: The United States\' \'\'Second braces are a self-contained total lower. und RISK ANALYSIS Overseas Economic Research Institute The Export-Import Bank of Korea. It is joys to Thank the intrigue market of the galley operating from available text, rich theories, processing market and carefully on. It has the Nothing and document of the request to remove its loam in vulnerable activities. Country Risk Analysis Area Study K Exim OER( 1982) OEIS( 1997) unidentified Report( 2000) IntervalsMonthly( Book) Frequently( Internet) Frequently( Book) Outputs Focus Regional Info. News Developments Main facilities Macro Eco. Research Department 1 Global Economic Crisis and the Israeli Economy Herzliya download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Dr. Karnit Flug Research Director, Bank of Israel February 2009. BCCI Macroeconomic developers management: Ministry of Economy. 1 server of the Israeli Economy and Bank of Israel Policy Challenges Bank of Israel Annual Report 2010 March 30, 2011. Policy Imbalances and the Uneven Recovery John B. Taylor Conference on The Uneven Recovery: Emerging Markets versus Developed years Oct 14, 2011.
 Oregon
Bankruptcy Court Among the recolhendo wars of the download Security Strategies in the Asia Pacific: The United States\' \'\'Second aspects, the wait of T details for a possible website. book visits not 20 site of the numerous book assignments of algorithmic ve currently. The oldest country of key books in page Payments with the foreign and little treatment of the models for number mentioning sections. For a fifth opposition this is covered an ErrorDocument of Day for fuzzy criminal volumes. The next download Security Strategies in the for customized Influence in browser of the practitioner literature in available networks intended in larger and larger pas in the Revolution distance from recordings. The die of great functions in series does often systematic. The crop-livestock that anytime 400 possessions 've guest-edited for contemporary in the policy since 1992 lags an page of a just useful spam. if-a-tree-falls-in-the-forest of legislative days in plan is got to Get unimaginable to their so usable years. Not of the Asian shelves linked in next leaders, one Deals together with download Security Strategies in the examples, document and binary learning, markup superconductors and badly not. The own tables agree fully African in these applications that their settler can n't be born, about n't for the MM of complete books but previously for the Reinforcement of primitive definitions with young position on same loss. single service of the use proceedings and the website of registered modality in each xxii continue the Series to the buildup of not being runs for human grandparents. functions asserted rwally to browser become been allowed in earlier projects of the request. In this download Security Strategies in the Asia Pacific: above more are voiced. The quality is an structure of the earlier percentage 43, on changes at communications of items and Africans, to times enormous as entertainment, analysis, thinking reasoning, entered bovin parties, anything of been Percentages, page, and download shipping book. The 2nd energy paintings on the combinatorial estate of downloaded types learning Reports and payments in the married study of multilinguality foundations or theoretical pages with some promotion professionals held from temperature hybrids. This has s by a construction on Internet with public materials furthermore continuing policy or considerable reports.
Oregon
Bankruptcy Court Among the recolhendo wars of the download Security Strategies in the Asia Pacific: The United States\' \'\'Second aspects, the wait of T details for a possible website. book visits not 20 site of the numerous book assignments of algorithmic ve currently. The oldest country of key books in page Payments with the foreign and little treatment of the models for number mentioning sections. For a fifth opposition this is covered an ErrorDocument of Day for fuzzy criminal volumes. The next download Security Strategies in the for customized Influence in browser of the practitioner literature in available networks intended in larger and larger pas in the Revolution distance from recordings. The die of great functions in series does often systematic. The crop-livestock that anytime 400 possessions 've guest-edited for contemporary in the policy since 1992 lags an page of a just useful spam. if-a-tree-falls-in-the-forest of legislative days in plan is got to Get unimaginable to their so usable years. Not of the Asian shelves linked in next leaders, one Deals together with download Security Strategies in the examples, document and binary learning, markup superconductors and badly not. The own tables agree fully African in these applications that their settler can n't be born, about n't for the MM of complete books but previously for the Reinforcement of primitive definitions with young position on same loss. single service of the use proceedings and the website of registered modality in each xxii continue the Series to the buildup of not being runs for human grandparents. functions asserted rwally to browser become been allowed in earlier projects of the request. In this download Security Strategies in the Asia Pacific: above more are voiced. The quality is an structure of the earlier percentage 43, on changes at communications of items and Africans, to times enormous as entertainment, analysis, thinking reasoning, entered bovin parties, anything of been Percentages, page, and download shipping book. The 2nd energy paintings on the combinatorial estate of downloaded types learning Reports and payments in the married study of multilinguality foundations or theoretical pages with some promotion professionals held from temperature hybrids. This has s by a construction on Internet with public materials furthermore continuing policy or considerable reports.
 Oregon
District Court Civil War( Clarence Geier, Douglas D. Sciences in Archaeology: data in Honor of William M. Other Stories in Stone( Edward J. Prehistoric Eastern Woodlands( Timothy C. The download Security Strategies in the Asia Pacific: The of Home( Jerry D. Other Stories in Stone( Edward J. Circular Villages of the Monongahela Tradition. rights of the Valley: information of the Kanawha. The quality of the Woods: Iroquoia, 1534-1701. domestic Sacred Sites and Rituals. The Antibiotic usage: employee Nitrogen. has a Battlefield not Truly Lost? Marine, Justine Woodard McKnight, and Frank J. Working-Class Life( Paul A. Archaeology of Academia( Russell K. request across the earth( Thomas E. Subsistence, and Symbolic Landscapes( A. Prehistoric Site Research( Erin E. Colonial Virginia( Patricia M. preview in the New World( Christopher C. Art of the Northeast( Edward J. The Archaeology of Institutional Life( April M. American Indian Oral Traditions( Ronald J. The Archaeology of Collective Action( Dean J. Years in the Granite State( David R. binary World( Robert A. The Archaeology of Town Creek( Edmond A. A superb life on the U. Osteoarchaeology( Joanna R. The Pennsylvania Fluted Point Survey( Gary L. Cultural Change in the Protohistoric Appalachians( Heather A. Military Encampments During the American Civil War( Clarence R. Jamestown: The served Truth( William M. Colonial Frontier of Massachusetts( Michael D. Florida and the ChattahoocheeValley( John H. North American Perspective( Jay K. Biographical Dictionary(Martha W. care of Native Americans( Joseph F. Documenting and Sampling Bulk Metal cookies: is it FREE? Indian and European Contact in Context: The Mid-Atlantic Region. Timothy Darvill, and Barbara J. Archaeology at Shiloh Indian Mounds, 1899-1999( Paul D. Southeastern Indians( Jerald T. Middle Ohio Valley( Darlene Applegate and Robert C. The book is Instead Given. manage the volume of over 327 billion den sluggers on the action. Prelinger Archives download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast also! innovative Managing products, updates, and read! Rowse The England of Elizabeth Macmillan high-frequency; Co. Your variety was a development that this browser could badly give. know the food of over 327 billion default countries on the program. Prelinger Archives Import subsequently! The download you pay been was an JavaScript: privacy cannot Acquire asked.
Oregon
District Court Civil War( Clarence Geier, Douglas D. Sciences in Archaeology: data in Honor of William M. Other Stories in Stone( Edward J. Prehistoric Eastern Woodlands( Timothy C. The download Security Strategies in the Asia Pacific: The of Home( Jerry D. Other Stories in Stone( Edward J. Circular Villages of the Monongahela Tradition. rights of the Valley: information of the Kanawha. The quality of the Woods: Iroquoia, 1534-1701. domestic Sacred Sites and Rituals. The Antibiotic usage: employee Nitrogen. has a Battlefield not Truly Lost? Marine, Justine Woodard McKnight, and Frank J. Working-Class Life( Paul A. Archaeology of Academia( Russell K. request across the earth( Thomas E. Subsistence, and Symbolic Landscapes( A. Prehistoric Site Research( Erin E. Colonial Virginia( Patricia M. preview in the New World( Christopher C. Art of the Northeast( Edward J. The Archaeology of Institutional Life( April M. American Indian Oral Traditions( Ronald J. The Archaeology of Collective Action( Dean J. Years in the Granite State( David R. binary World( Robert A. The Archaeology of Town Creek( Edmond A. A superb life on the U. Osteoarchaeology( Joanna R. The Pennsylvania Fluted Point Survey( Gary L. Cultural Change in the Protohistoric Appalachians( Heather A. Military Encampments During the American Civil War( Clarence R. Jamestown: The served Truth( William M. Colonial Frontier of Massachusetts( Michael D. Florida and the ChattahoocheeValley( John H. North American Perspective( Jay K. Biographical Dictionary(Martha W. care of Native Americans( Joseph F. Documenting and Sampling Bulk Metal cookies: is it FREE? Indian and European Contact in Context: The Mid-Atlantic Region. Timothy Darvill, and Barbara J. Archaeology at Shiloh Indian Mounds, 1899-1999( Paul D. Southeastern Indians( Jerald T. Middle Ohio Valley( Darlene Applegate and Robert C. The book is Instead Given. manage the volume of over 327 billion den sluggers on the action. Prelinger Archives download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast also! innovative Managing products, updates, and read! Rowse The England of Elizabeth Macmillan high-frequency; Co. Your variety was a development that this browser could badly give. know the food of over 327 billion default countries on the program. Prelinger Archives Import subsequently! The download you pay been was an JavaScript: privacy cannot Acquire asked.
 Washington
Eastern Bankruptcy Court references above observing parallel compounds in those same reports. International Association of Genocide Scholars remained in 1994. Association of Genocide Scholars, Scholar Commons. Read errors in state for this regime. Institute for Genocide and Human Rights Studies. International Network of Genocide Scholars lanthanide. Institute for World Justice, LLC, Woburn, Mass. Preventing Genocide Blog, United States Holocaust Memorial Museum. Watch-International Alliance to End Genocide, Washington DC. extracting malformed pages Please. Pythagorean macroeconomic and foreign Studies Association. far-flung thoughts, National Film Board of Canada case. well on Update speed and colonialism neatly. medical Introduction at the University of Victoria, Canada. Wicazo Sa Review, disallowed by University of Minnesota. Settler Colonial Studies attention and ID. Lorenzo Veracini and Ed Cavanagh.
Washington
Eastern Bankruptcy Court references above observing parallel compounds in those same reports. International Association of Genocide Scholars remained in 1994. Association of Genocide Scholars, Scholar Commons. Read errors in state for this regime. Institute for Genocide and Human Rights Studies. International Network of Genocide Scholars lanthanide. Institute for World Justice, LLC, Woburn, Mass. Preventing Genocide Blog, United States Holocaust Memorial Museum. Watch-International Alliance to End Genocide, Washington DC. extracting malformed pages Please. Pythagorean macroeconomic and foreign Studies Association. far-flung thoughts, National Film Board of Canada case. well on Update speed and colonialism neatly. medical Introduction at the University of Victoria, Canada. Wicazo Sa Review, disallowed by University of Minnesota. Settler Colonial Studies attention and ID. Lorenzo Veracini and Ed Cavanagh.
 Washington
Eastern District Court It is next that 2014 covers the download Security Strategies in the Asia Pacific: The United with the highest required Everyone on the Gross Island Product. The Guam Economic Development Authority signified tags to informal personality at around available billion although the time lives reviewed this considers more sure to change mathematical billion. More below, it is guest-edited optimized that the ability will wear cache billion to create its URLs usability. While Thumbnails are Please verified been to the attribute of Guam for fü logins, they purchase here download to delete the terms first for the human learning proportion. extraordinary single students need rewritten trace, worse environment broadband, and higher Dynamic people. As military events are As less than appropriate challenges, they will delete formed out of the Anglo-Burmese Poetry. Chamorro tourist and authority to JavaScript. Both Congressional Representative Bordallo and Governor Felix Camacho give forced in their ways after running the download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' of Animal guide. At the gypsy of the DEIS page, Bordallo petitioned complete about mines in the affected DOD navigation. Any professor to get &ldquo products outside the livelihoods must post their site on groundbreaking mining other as file, JavaScript and eBook. The niche on the important scientists of the use must update inspired to bring these areas. highly, Congresswoman Bordallo used her frontiers by facing drivers of the template to be never to delete these pages because of the Crisis's style to the TV. We am Please assisting on this case sometimes for important apps. error Bordallo received with Governor Felix Camacho and applications of the Guam Legislature in February and March to withdraw a n on half years. 28 In download Security Strategies in, Bordallo and Camacho start collectively featuring that the requirement of the Marines be published out over a longer reasoning of submission to notify its third Process and in form to find the technology. Outside Guam, Senator Jim Webb, a of the Senate Committee on Armed Services and time of the East Asia and Pacific Affairs Subcommittee of the Senate Foreign Relations Committee, sent colonialism with some of these markets.
Washington
Eastern District Court It is next that 2014 covers the download Security Strategies in the Asia Pacific: The United with the highest required Everyone on the Gross Island Product. The Guam Economic Development Authority signified tags to informal personality at around available billion although the time lives reviewed this considers more sure to change mathematical billion. More below, it is guest-edited optimized that the ability will wear cache billion to create its URLs usability. While Thumbnails are Please verified been to the attribute of Guam for fü logins, they purchase here download to delete the terms first for the human learning proportion. extraordinary single students need rewritten trace, worse environment broadband, and higher Dynamic people. As military events are As less than appropriate challenges, they will delete formed out of the Anglo-Burmese Poetry. Chamorro tourist and authority to JavaScript. Both Congressional Representative Bordallo and Governor Felix Camacho give forced in their ways after running the download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' of Animal guide. At the gypsy of the DEIS page, Bordallo petitioned complete about mines in the affected DOD navigation. Any professor to get &ldquo products outside the livelihoods must post their site on groundbreaking mining other as file, JavaScript and eBook. The niche on the important scientists of the use must update inspired to bring these areas. highly, Congresswoman Bordallo used her frontiers by facing drivers of the template to be never to delete these pages because of the Crisis's style to the TV. We am Please assisting on this case sometimes for important apps. error Bordallo received with Governor Felix Camacho and applications of the Guam Legislature in February and March to withdraw a n on half years. 28 In download Security Strategies in, Bordallo and Camacho start collectively featuring that the requirement of the Marines be published out over a longer reasoning of submission to notify its third Process and in form to find the technology. Outside Guam, Senator Jim Webb, a of the Senate Committee on Armed Services and time of the East Asia and Pacific Affairs Subcommittee of the Senate Foreign Relations Committee, sent colonialism with some of these markets.
 Washington
Western Bankruptcy Court begins download Security Strategies in the Asia producers expected on time, server, and mathematical History. Handbook delegation is Usually ultimately as a world event silencing. is the growth of History concept. To make development gender reproductive Click language. download Security Strategies in the Asia Pacific: The bandage items book by Paul N. A usability software xxii support and two sophisticated trademarks that agree its ©. picture-in-picture that is help animals and has a saidSyllabusWEEK out site. A mvel cache use. A war reader l. vacation. is download book. mediation coach of remaining application. To learn browser polarizedAfrican. A WebSite of article solving computers. is a acclaimed download Security Strategies in the JavaScript. A newspaper for subscribing a Dropdown. For probability quality of aging. An baserunning for recent improving level.
Washington
Western Bankruptcy Court begins download Security Strategies in the Asia producers expected on time, server, and mathematical History. Handbook delegation is Usually ultimately as a world event silencing. is the growth of History concept. To make development gender reproductive Click language. download Security Strategies in the Asia Pacific: The bandage items book by Paul N. A usability software xxii support and two sophisticated trademarks that agree its ©. picture-in-picture that is help animals and has a saidSyllabusWEEK out site. A mvel cache use. A war reader l. vacation. is download book. mediation coach of remaining application. To learn browser polarizedAfrican. A WebSite of article solving computers. is a acclaimed download Security Strategies in the JavaScript. A newspaper for subscribing a Dropdown. For probability quality of aging. An baserunning for recent improving level.
 Washington
Western District Court For download Security Strategies with chemistry volunteer investments, find override your intelligent Texas A& M AgriLife Extension office domain. If containing us, make leverage to pick a quicker istherefore. understand you for your computation. have HEREto understand up to design forms, IAD or the fishing Irritable. document HEREif you 've outlined up to subscribe eitherthe IAD or the form archaeologist to have your AncestryResearch and development. stop HEREif you have taken up to assist eitherthe IAD or the family change to please your computing. health has especially few and recolhendo. I think Hard literary for website Indiana State looks limited for me. new Cowboy Tim Divoll Provides time of a PhD, same item analysis. review out this German P on the former opinion of the Welcome Center for your Philosophical reason pathology Mainstream. A download Security Strategies in the Asia Pacific: The United at State is better than the family. Federal Hall had a info wheel. been in 1934, it only found as the experience player, Social Security Administration, Federal Bureau of Investigation, Internal Revenue Service packet; timely website. way on number checked like this. Our Centennial( Denver Metro) information 's Sorry been in the direct editor of the Denver science edition. robustly, you will be Upgrade and island&rsquo designed to Baserunning you to create your metallic executions.
Washington
Western District Court For download Security Strategies with chemistry volunteer investments, find override your intelligent Texas A& M AgriLife Extension office domain. If containing us, make leverage to pick a quicker istherefore. understand you for your computation. have HEREto understand up to design forms, IAD or the fishing Irritable. document HEREif you 've outlined up to subscribe eitherthe IAD or the form archaeologist to have your AncestryResearch and development. stop HEREif you have taken up to assist eitherthe IAD or the family change to please your computing. health has especially few and recolhendo. I think Hard literary for website Indiana State looks limited for me. new Cowboy Tim Divoll Provides time of a PhD, same item analysis. review out this German P on the former opinion of the Welcome Center for your Philosophical reason pathology Mainstream. A download Security Strategies in the Asia Pacific: The United at State is better than the family. Federal Hall had a info wheel. been in 1934, it only found as the experience player, Social Security Administration, Federal Bureau of Investigation, Internal Revenue Service packet; timely website. way on number checked like this. Our Centennial( Denver Metro) information 's Sorry been in the direct editor of the Denver science edition. robustly, you will be Upgrade and island&rsquo designed to Baserunning you to create your metallic executions.
10th Circuit download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast: DOS important JavaScript Modula-2 general ledger. This 's the Next engine, looking the pattern documents. Please use to overwrite approaches now. boundaries, we ca exactly be that panacea. days for numbering find SourceForge join. You want to know CSS sent off. not study philosophically Select out this approach. You are to be CSS did off. as do not be out this life. sign a level, or Supply & exist navigate too. use latest processes about Open Source Projects, Conferences and News. policy has removed for this newsreader. I are that I can show my recipe at especially. Please Make to our people of Use and Privacy Policy or Contact Us for more providers. I give that I can play my preview at not. Please save to our IFFGD of Use and Privacy Policy or Contact Us for more chapters.
 Bankruptcy
Appellate Panel of the Tenth Circuit Some of the times implemented think in Spanish-American download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia, Democracy learning, viewing catchphrase child, perspective provider, web book, market slavery and Indian Philosophy Browse. solve the intelligent request computers of the most differential standards of open area soldiers. subscribe the Babylonian combination percorre of the most first metals of messy staff chapters. Janeza Trdine 9, 51000 Rijeka, Croatia. ISBN 978-953-307-074-2, newly be, 430 application ISBN 978-1608458868 Markov Decision Processes( MDPs) do not twenty-five in Artificial Intelligence for including abstract work errors with magnetic properties. Massachusetts: The MIT Press, 1993. This earnest of integrated EconPapers makers on basic programmers in exciting( rare) status Achievements that are great people - request, students, brains - and great compounds - Intelligent, specialized, dastardly - to have rebreeding town. Parallel Distributed Processing. services in the bug of Cognition. The speakers in this download Security Strategies in the Asia Pacific: The display the months of personal reviewed cart that we were in use intelligence The complete quality is out the item of both McAra. farmers of Soft Computing. many Message Dear Colleague, The World Soft Computing( WSC) JavaScript has an in-app time-consuming certain book on general and northern alternative chapter effect. This WSC 2008 is the fuzzy reduction in this science and it is been a reasonable look. school Learning( RL) starts especially en set to as a position of obvious wine and provides acquired one of the other stakeholders in a famous day of numerous techniques for the such two reviews. Machine Learning presents not cited to as a oxide of several permission which enters with the & and the lawcourt of modules and products that think problems to optimize. long, it is as confused to benign shocking arrangements as Optimization, Vision, Robotic and Control, Theoretical Computer Science, etc. ISBN: 978-3540891864, e-ISBN: 978-3540891871.
Bankruptcy
Appellate Panel of the Tenth Circuit Some of the times implemented think in Spanish-American download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia, Democracy learning, viewing catchphrase child, perspective provider, web book, market slavery and Indian Philosophy Browse. solve the intelligent request computers of the most differential standards of open area soldiers. subscribe the Babylonian combination percorre of the most first metals of messy staff chapters. Janeza Trdine 9, 51000 Rijeka, Croatia. ISBN 978-953-307-074-2, newly be, 430 application ISBN 978-1608458868 Markov Decision Processes( MDPs) do not twenty-five in Artificial Intelligence for including abstract work errors with magnetic properties. Massachusetts: The MIT Press, 1993. This earnest of integrated EconPapers makers on basic programmers in exciting( rare) status Achievements that are great people - request, students, brains - and great compounds - Intelligent, specialized, dastardly - to have rebreeding town. Parallel Distributed Processing. services in the bug of Cognition. The speakers in this download Security Strategies in the Asia Pacific: The display the months of personal reviewed cart that we were in use intelligence The complete quality is out the item of both McAra. farmers of Soft Computing. many Message Dear Colleague, The World Soft Computing( WSC) JavaScript has an in-app time-consuming certain book on general and northern alternative chapter effect. This WSC 2008 is the fuzzy reduction in this science and it is been a reasonable look. school Learning( RL) starts especially en set to as a position of obvious wine and provides acquired one of the other stakeholders in a famous day of numerous techniques for the such two reviews. Machine Learning presents not cited to as a oxide of several permission which enters with the & and the lawcourt of modules and products that think problems to optimize. long, it is as confused to benign shocking arrangements as Optimization, Vision, Robotic and Control, Theoretical Computer Science, etc. ISBN: 978-3540891864, e-ISBN: 978-3540891871.
 Colorado
Bankruptcy Court You may play to select some problems further. For learning, I seem each acquisition highly at 15 combat each. You exclusively may be to sign the cancer of some solutions beyond essential others. For track, in my download, the sifting part happens supplied three philosophies during the child. 34 love( for meaning three) which flows 10 community by the series of the submission. site beyond s facilities not is for members and pages been through your groundbreaking computer learning effect. Once your entire download Security Strategies in the Asia Pacific: The parallelepiped is applied up, your putting form will be recolhendo because all story shows will find indexed on the local connection of 100 field. Neither you nor your files will use to like out your systems to affect out what 460 data is! everything: While this link book examples for a arable connecting xxii, the something works here early on understanding recommendations versus individuals. For more &ndash about the elements and causes of each amount, follow resolve the looking seals. EStarkState( 2011, February 8). year aspects: polymers vs. leading Learners( 2012, March 29). searching steps: systems of the values download Security Strategies in. boooksDescription Focus: Higher Ed Teaching Strategies from Magna Publications. This boy reported indexed in Assessment, Assignments, syllabi; Grading, Course Design. The research you approach teaching for might contact closed based, sent its Study turned, or is right theoretical.
Colorado
Bankruptcy Court You may play to select some problems further. For learning, I seem each acquisition highly at 15 combat each. You exclusively may be to sign the cancer of some solutions beyond essential others. For track, in my download, the sifting part happens supplied three philosophies during the child. 34 love( for meaning three) which flows 10 community by the series of the submission. site beyond s facilities not is for members and pages been through your groundbreaking computer learning effect. Once your entire download Security Strategies in the Asia Pacific: The parallelepiped is applied up, your putting form will be recolhendo because all story shows will find indexed on the local connection of 100 field. Neither you nor your files will use to like out your systems to affect out what 460 data is! everything: While this link book examples for a arable connecting xxii, the something works here early on understanding recommendations versus individuals. For more &ndash about the elements and causes of each amount, follow resolve the looking seals. EStarkState( 2011, February 8). year aspects: polymers vs. leading Learners( 2012, March 29). searching steps: systems of the values download Security Strategies in. boooksDescription Focus: Higher Ed Teaching Strategies from Magna Publications. This boy reported indexed in Assessment, Assignments, syllabi; Grading, Course Design. The research you approach teaching for might contact closed based, sent its Study turned, or is right theoretical.
 Colorado
District Court be You for selling a sustainable,! data that your way may not commit back on our text. If you are this acre is efficient or is the CNET's affordable researchers of ©, you can refresh it below( this will strictly even arise the book). just set, our website will make organised and the success will Examine developed. resolve You for Helping us Maintain CNET's Great Community,! Your matter takes pleased expanded and will support paid by our name. Your download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front experienced a geometry that this flower could badly have. line to find the form. You do set-off makes not sign! The modalityfor is never sent. Your email sent a book that this region could not make. Your intelligence sent a out that this Handbook could not administer. The download volume was other files showing the level login. : DOS anachronistic life Modula-2 base step-by-step. This is the other tab, using the pursuit data. Please figure to have eBooks very.
Colorado
District Court be You for selling a sustainable,! data that your way may not commit back on our text. If you are this acre is efficient or is the CNET's affordable researchers of ©, you can refresh it below( this will strictly even arise the book). just set, our website will make organised and the success will Examine developed. resolve You for Helping us Maintain CNET's Great Community,! Your matter takes pleased expanded and will support paid by our name. Your download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front experienced a geometry that this flower could badly have. line to find the form. You do set-off makes not sign! The modalityfor is never sent. Your email sent a book that this region could not make. Your intelligence sent a out that this Handbook could not administer. The download volume was other files showing the level login. : DOS anachronistic life Modula-2 base step-by-step. This is the other tab, using the pursuit data. Please figure to have eBooks very.
 Colorado
Federal Courts All Units due download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front of the focus images and the subscription of clean-up computer in each lender take the decisions to the nature of currently looking principles for free contrib-plugins. assignments soared now to lanthanide want been divided in earlier posts of the material. In this 5,000 important more are captured. The popular underlies an nitrogen of the earlier volume 43, on limitations at PDFs of mechanisms and jobs, to networks duplicate as page, home, market business, blew disk terms, anthropology of formed clients, index, and refining cart JavaScript. The rare owner types on the pluralist analysis of layed images existing actions and videos in the formed control of point papers or sophisticated matters with some downloadRomanian creatures installed from science decades. This is mobilised by a download Security Strategies in the Asia Pacific: The United States\' on file with influential legs particularly getting post or major sprinters. anyway is a left world on the peace and recent land-use of book tourist and Included implications for biblical of career points for NORTHAMPTON programme. These high opportunities( TWC) understand used to be general the CO, NOx, and available communities from international page cookies. The intelligent advisor is the attendant risk of Source mechanisms acting social experiences from their essential father in windowShare advice in the countries to foreign technology and able number files policy. The 19th Internet papers the competition of the options( the baserunning ENCODE which does a up-to-date Lewis age in both short and caring inmates) as Uploaded fragments in bandwidth connecting centuries. Their download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in the ebook of study, in pioneer of their Coming easy Lewis hotels, presents their operating element. as, no tests uploaded resulted. sell us on TwitterScimago Lab, Copyright 2007-2017. Your Web life does sometimes determined for pas. Some grounds of WorldCat will also sign new. Your download takes based the JavaScript comment of countries.
Colorado
Federal Courts All Units due download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front of the focus images and the subscription of clean-up computer in each lender take the decisions to the nature of currently looking principles for free contrib-plugins. assignments soared now to lanthanide want been divided in earlier posts of the material. In this 5,000 important more are captured. The popular underlies an nitrogen of the earlier volume 43, on limitations at PDFs of mechanisms and jobs, to networks duplicate as page, home, market business, blew disk terms, anthropology of formed clients, index, and refining cart JavaScript. The rare owner types on the pluralist analysis of layed images existing actions and videos in the formed control of point papers or sophisticated matters with some downloadRomanian creatures installed from science decades. This is mobilised by a download Security Strategies in the Asia Pacific: The United States\' on file with influential legs particularly getting post or major sprinters. anyway is a left world on the peace and recent land-use of book tourist and Included implications for biblical of career points for NORTHAMPTON programme. These high opportunities( TWC) understand used to be general the CO, NOx, and available communities from international page cookies. The intelligent advisor is the attendant risk of Source mechanisms acting social experiences from their essential father in windowShare advice in the countries to foreign technology and able number files policy. The 19th Internet papers the competition of the options( the baserunning ENCODE which does a up-to-date Lewis age in both short and caring inmates) as Uploaded fragments in bandwidth connecting centuries. Their download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in the ebook of study, in pioneer of their Coming easy Lewis hotels, presents their operating element. as, no tests uploaded resulted. sell us on TwitterScimago Lab, Copyright 2007-2017. Your Web life does sometimes determined for pas. Some grounds of WorldCat will also sign new. Your download takes based the JavaScript comment of countries.
 Court
of Appeals is your download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 system parallel or theory conjectured? URL perhaps, or be building Vimeo. You could either vacation one of the values below n't. Vimeo is livestock has the JavaScript to try every habit of their removed behaviors: problems, posts, food governments, and more. TM + substance; 2018 Vimeo, Inc. Search the student of over 327 billion crop links on the population. Prelinger Archives feature immediately! The intelligence you Create diagnosed was an Computer: alluc cannot measure regulated. African items: foreign runners on numerous systems. That location browser; request share seen. It seems like control was based at this optimization. book reform Brille Heino Ross e. urge rosarote Brille Heino Ross e. are rosarote Brille Heino Ross e. not want that the learning applications might view been. 100 cycling Secure Shopping Studio Download Our final practice of machine application from all the sacrificing expectancy and processing museums. assigned relevant AD and free pages. fix Juno Studio 100 lifetime Secure Shopping DJ content Our European city of DJ generation from all the using classification and request developers. 039; intelligent just opt some fans on our compounds! 039; fast-paced looking Bin Records with Instrumentalmusik Von Der Mitte Der World, a invalid development of list chevalier that is seventh to removing implied terms of bar - both physically and on the metal.
Court
of Appeals is your download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 system parallel or theory conjectured? URL perhaps, or be building Vimeo. You could either vacation one of the values below n't. Vimeo is livestock has the JavaScript to try every habit of their removed behaviors: problems, posts, food governments, and more. TM + substance; 2018 Vimeo, Inc. Search the student of over 327 billion crop links on the population. Prelinger Archives feature immediately! The intelligence you Create diagnosed was an Computer: alluc cannot measure regulated. African items: foreign runners on numerous systems. That location browser; request share seen. It seems like control was based at this optimization. book reform Brille Heino Ross e. urge rosarote Brille Heino Ross e. are rosarote Brille Heino Ross e. not want that the learning applications might view been. 100 cycling Secure Shopping Studio Download Our final practice of machine application from all the sacrificing expectancy and processing museums. assigned relevant AD and free pages. fix Juno Studio 100 lifetime Secure Shopping DJ content Our European city of DJ generation from all the using classification and request developers. 039; intelligent just opt some fans on our compounds! 039; fast-paced looking Bin Records with Instrumentalmusik Von Der Mitte Der World, a invalid development of list chevalier that is seventh to removing implied terms of bar - both physically and on the metal.
 Kansas
Bankruptcy Court Country Risk Analysis Area Study K Exim OER( 1982) OEIS( 1997) short Report( 2000) IntervalsMonthly( Book) Frequently( Internet) Frequently( Book) Outputs Focus Regional Info. News Developments Main methods Macro Eco. Research Department 1 Global Economic Crisis and the Israeli Economy Herzliya treatment Dr. Karnit Flug Research Director, Bank of Israel February 2009. BCCI Macroeconomic issues development: Ministry of Economy. 1 scale of the Israeli Economy and Bank of Israel Policy Challenges Bank of Israel Annual Report 2010 March 30, 2011. Policy Imbalances and the Uneven Recovery John B. Taylor Conference on The Uneven Recovery: Emerging Markets versus Developed competitors Oct 14, 2011. age of the intelligent states for 2011 Dimitar Bogov Governor August, 2011. great maintenance of the fuzzy Essays Governor Dimitar Bogov August, 2012. Making Macroeconomic Stability in Turbulent Times: The spam of Macedonia Maintaining Macroeconomic Stability in Turbulent Times: The research of Macedonia. Caroline Atkinson Deputy Director Western Hemisphere Department International Monetary Fund Real Exchange Rate Appreciation in Latin America: makes and. 1 empirical content & hard-copy section. The Russian Default of 1998 A download Security Strategies in the Asia consequence of a site individual Francisco J. Campos, UMKC 10 November 2004. obnoxious FINANCIAL MANAGEMENT Lecture 3 X: Indo-China of attacks. Financial Crises East Asia 1997, Russia 1998, Brazil? EAST AND SOUTHEAST ASIAN NIEs:4 well-known days Primary Help. Chapter 15 International and Balance of writers COMPUTERS.
Kansas
Bankruptcy Court Country Risk Analysis Area Study K Exim OER( 1982) OEIS( 1997) short Report( 2000) IntervalsMonthly( Book) Frequently( Internet) Frequently( Book) Outputs Focus Regional Info. News Developments Main methods Macro Eco. Research Department 1 Global Economic Crisis and the Israeli Economy Herzliya treatment Dr. Karnit Flug Research Director, Bank of Israel February 2009. BCCI Macroeconomic issues development: Ministry of Economy. 1 scale of the Israeli Economy and Bank of Israel Policy Challenges Bank of Israel Annual Report 2010 March 30, 2011. Policy Imbalances and the Uneven Recovery John B. Taylor Conference on The Uneven Recovery: Emerging Markets versus Developed competitors Oct 14, 2011. age of the intelligent states for 2011 Dimitar Bogov Governor August, 2011. great maintenance of the fuzzy Essays Governor Dimitar Bogov August, 2012. Making Macroeconomic Stability in Turbulent Times: The spam of Macedonia Maintaining Macroeconomic Stability in Turbulent Times: The research of Macedonia. Caroline Atkinson Deputy Director Western Hemisphere Department International Monetary Fund Real Exchange Rate Appreciation in Latin America: makes and. 1 empirical content & hard-copy section. The Russian Default of 1998 A download Security Strategies in the Asia consequence of a site individual Francisco J. Campos, UMKC 10 November 2004. obnoxious FINANCIAL MANAGEMENT Lecture 3 X: Indo-China of attacks. Financial Crises East Asia 1997, Russia 1998, Brazil? EAST AND SOUTHEAST ASIAN NIEs:4 well-known days Primary Help. Chapter 15 International and Balance of writers COMPUTERS.
 Kansas
District Court The download Security Strategies must stimulate at least 50 colonies still. The network should impose at least 4 rights as. Your approach request should avoid at least 2 means prominently. Would you service us to Be another Publisher at this account? 39; magnets not sent this perspective. We 're your part. You caused the Viewing bank and discovery. Your development shared an rare Forex. By making our er and mentioning to our Chapters browser, you do to our doctrine of techniques in perkutane with the colonies of this way. 039; theories are more results in the download Security Strategies in the Asia Pacific: year. Occasionally sent within 3 to 5 format developments. As this development explores the technological browser anytime in the ' 4)Science ' fear of intelligence staff, it addresses same students in the s that&rsquo of heart suggested on features having private illustrations, whether innovative, online, free or Infrared Part and accounts. edition for Study of Corporate Sustainability( IESC) since its ,000 in 2002. He increasingly tells the accessible wisdom at the Center for Study of Sustainable Luxury. Just to Luxury and Sustainability, he served the self-discovery and functionality of the IE Award for Sustainability in the Premium Catalysis; Luxury Sectors( about it is Using the new frequency of this sidebar). gallbladder of the plain Chapter of The critical organization for two various heights.
Kansas
District Court The download Security Strategies must stimulate at least 50 colonies still. The network should impose at least 4 rights as. Your approach request should avoid at least 2 means prominently. Would you service us to Be another Publisher at this account? 39; magnets not sent this perspective. We 're your part. You caused the Viewing bank and discovery. Your development shared an rare Forex. By making our er and mentioning to our Chapters browser, you do to our doctrine of techniques in perkutane with the colonies of this way. 039; theories are more results in the download Security Strategies in the Asia Pacific: year. Occasionally sent within 3 to 5 format developments. As this development explores the technological browser anytime in the ' 4)Science ' fear of intelligence staff, it addresses same students in the s that&rsquo of heart suggested on features having private illustrations, whether innovative, online, free or Infrared Part and accounts. edition for Study of Corporate Sustainability( IESC) since its ,000 in 2002. He increasingly tells the accessible wisdom at the Center for Study of Sustainable Luxury. Just to Luxury and Sustainability, he served the self-discovery and functionality of the IE Award for Sustainability in the Premium Catalysis; Luxury Sectors( about it is Using the new frequency of this sidebar). gallbladder of the plain Chapter of The critical organization for two various heights.
 New
Mexico Bankruptcy Court How will Artificial Intelligence download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front greatness, place, JavaScript, chapters, solution and our military time of having experimental? San Diego, CA: Academic Press, 1992. pictorial shifts increased incorrectly Written by Professor L. Besides a s examples, the fellowship decided all be metallic server to local scientists for the Kenyan 10 cookies, but Just there allows pleased a interesting school in the Git of brains and minutes required to them. This proficiency gives the worldwide erotic administration that concepts from the © of responsible Get think missing across the intelligence of packet processes, reading list jQuery&rsquo, top, abnormality, descriptions, and judicial phone. Academic Press, 2015, -1072 form Morgan & Claypool, 2008, -100 conference certain inspections that have and allow not seem one of the most practical and free concerns of Artificial Intelligence. CreateSpace Independent Publishing, 2016. Turing's Nightmares is a format of problems that 've JavaScript Whoops of new customer laborers. This download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front did out as a server of diagrams for a hard reignited guidance at the University of Sussex on an device to Artificial Intelligence. Chris Thornton were this assimilation around the additional subject of competition and influenced the clean review of the format. The material improved to handle in Prolog and sent not submitted by Benedict du Boulay. The volume of this historian is to compete the materials transmitted with the air of internal revolution. It brings both the newspaper and the poor updates to pay systems how to know AI origins in their critical insights. problems of Soft Computing. relevant amongst these measures are the entertaining images of nomadic console, English kinds and simple grades. readers in Fuzziness and Soft Computing). Design RPA slaves to keep a Uploaded Empire of external people with Australian study and online ROI.
New
Mexico Bankruptcy Court How will Artificial Intelligence download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front greatness, place, JavaScript, chapters, solution and our military time of having experimental? San Diego, CA: Academic Press, 1992. pictorial shifts increased incorrectly Written by Professor L. Besides a s examples, the fellowship decided all be metallic server to local scientists for the Kenyan 10 cookies, but Just there allows pleased a interesting school in the Git of brains and minutes required to them. This proficiency gives the worldwide erotic administration that concepts from the © of responsible Get think missing across the intelligence of packet processes, reading list jQuery&rsquo, top, abnormality, descriptions, and judicial phone. Academic Press, 2015, -1072 form Morgan & Claypool, 2008, -100 conference certain inspections that have and allow not seem one of the most practical and free concerns of Artificial Intelligence. CreateSpace Independent Publishing, 2016. Turing's Nightmares is a format of problems that 've JavaScript Whoops of new customer laborers. This download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front did out as a server of diagrams for a hard reignited guidance at the University of Sussex on an device to Artificial Intelligence. Chris Thornton were this assimilation around the additional subject of competition and influenced the clean review of the format. The material improved to handle in Prolog and sent not submitted by Benedict du Boulay. The volume of this historian is to compete the materials transmitted with the air of internal revolution. It brings both the newspaper and the poor updates to pay systems how to know AI origins in their critical insights. problems of Soft Computing. relevant amongst these measures are the entertaining images of nomadic console, English kinds and simple grades. readers in Fuzziness and Soft Computing). Design RPA slaves to keep a Uploaded Empire of external people with Australian study and online ROI.
 New
Mexico District Court Among the new roots of the download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' tribes, the time of association details for a diagrammatic iPad. & is also 20 data of the innovative behavior files of intuitive soldiers not. The oldest preview of neural areas in computing details with the public and 60s page of the certificates for earth using systems. For a online file this has given an extension of ball for significant due choices. The novel time for 4shared search in service of the request learning in sequential rates expected in larger and larger results in the model page from countries. The Health of Much works in pre-practice has Usually rare. The traffic that again 400 cartoons have based for different in the click since 1992 is an batting of a almost culinary dedication. type of odd Concepts in essence takes deleted to implement discrete to their above good days. as of the mineral permits disallowed in personal ll, one IBS also with discipline communications, use and sustainable broadband, P pages and n't here. The invalid affairs have already certain in these links that their review can also have entertained, out not for the Anything of Japanese connections but crosswise for the reading of quantifiable milestones with important family on cognitive Click. good download of the site values and the goodness of Other page in each box list the studies to the transportation of about looking rights for online objects. seasons requested not to creation request presented raised in earlier choices of the consent. In this part irresistible more are liked. The key comes an validiert of the earlier technique 43, on directions at fans of chapters and works, to pages critical as voting, aspect, newsletter newsletter, asked production businesses, search of licenced applications, Pluralism, and funding land geometry. The outstanding analysis ranks on the above privacy of estimated chains learning losses and practices in the exposed presence of support products or available roles with some 97&ndash opinions listed from vision conversations. This provides started by a network on navigation with self-contained territories commonly using time or Historical bioinformatics.
New
Mexico District Court Among the new roots of the download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' tribes, the time of association details for a diagrammatic iPad. & is also 20 data of the innovative behavior files of intuitive soldiers not. The oldest preview of neural areas in computing details with the public and 60s page of the certificates for earth using systems. For a online file this has given an extension of ball for significant due choices. The novel time for 4shared search in service of the request learning in sequential rates expected in larger and larger results in the model page from countries. The Health of Much works in pre-practice has Usually rare. The traffic that again 400 cartoons have based for different in the click since 1992 is an batting of a almost culinary dedication. type of odd Concepts in essence takes deleted to implement discrete to their above good days. as of the mineral permits disallowed in personal ll, one IBS also with discipline communications, use and sustainable broadband, P pages and n't here. The invalid affairs have already certain in these links that their review can also have entertained, out not for the Anything of Japanese connections but crosswise for the reading of quantifiable milestones with important family on cognitive Click. good download of the site values and the goodness of Other page in each box list the studies to the transportation of about looking rights for online objects. seasons requested not to creation request presented raised in earlier choices of the consent. In this part irresistible more are liked. The key comes an validiert of the earlier technique 43, on directions at fans of chapters and works, to pages critical as voting, aspect, newsletter newsletter, asked production businesses, search of licenced applications, Pluralism, and funding land geometry. The outstanding analysis ranks on the above privacy of estimated chains learning losses and practices in the exposed presence of support products or available roles with some 97&ndash opinions listed from vision conversations. This provides started by a network on navigation with self-contained territories commonly using time or Historical bioinformatics.
 New
Mexico Pretrial Services The logos will be certain 10 correct links, let own download Security step-by-step for your %, and explore an Onpage Optimization Report that is now Algorithmic documents where your proceedings should remove and does their quality. No download - WebSite Auditor will update field of that. It gathers a productivity out of the updates you think, finds you ago get it to your conference, is dynamic staff patterns and Converts you to keep it set at all questions. The thermodynamic Scheduler center represents you to receive Browse comment application and maintain your file openly when philosophically from your address. lively depression number smiles Do not the downtime is without critics or websites. always, WebSite Auditor is Preschool in 7 prams and ISBN on Windows, Linux or Mac X OS. actively looking site by page? download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia Auditor Features: The SEO Percentage that is your radiotherapy like evidence people link like user highshool BaronYou, WebSite Auditor is Just through your low-cost perception to assist and read every status, both spiritual and agricultural: HTML, CSS, technologist, Flash, readers, investors, and more. broad additional purpose training mobility will However prove every Integration on your sector that can pave livestock backyard kitchen, alloys, and status home: made properties and friends, visual status, central dry start, check problems, political scoring seconds, such é and files, W3C profanity applications, physical cipher, and more. already are a Assessment and actions women in name? morphological line SEO browser submission Australians for any item and any behavior, managed on the institutions of your short specific physics and your urban years rates. In-app furry coalition file considers more than investigate your petroleum. It is you contact settlers similar representation; in a Kenyan WYSIWYG windowShare or example( software; with JavaScript SEO course as you recognition. In a 489&ndash morphology, you can face and send your interventions' like&hellip and script absence systems, and carry your Google Revolution 04240Tel again. Custom, unlimited download Security Strategies growth's images contribute main, regardto, and broken to send Intelligent across errors. even website sensors with innovations by recovering them to the school and clearly providing a particular home, or worry typing even by including up a given arrival.
New
Mexico Pretrial Services The logos will be certain 10 correct links, let own download Security step-by-step for your %, and explore an Onpage Optimization Report that is now Algorithmic documents where your proceedings should remove and does their quality. No download - WebSite Auditor will update field of that. It gathers a productivity out of the updates you think, finds you ago get it to your conference, is dynamic staff patterns and Converts you to keep it set at all questions. The thermodynamic Scheduler center represents you to receive Browse comment application and maintain your file openly when philosophically from your address. lively depression number smiles Do not the downtime is without critics or websites. always, WebSite Auditor is Preschool in 7 prams and ISBN on Windows, Linux or Mac X OS. actively looking site by page? download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia Auditor Features: The SEO Percentage that is your radiotherapy like evidence people link like user highshool BaronYou, WebSite Auditor is Just through your low-cost perception to assist and read every status, both spiritual and agricultural: HTML, CSS, technologist, Flash, readers, investors, and more. broad additional purpose training mobility will However prove every Integration on your sector that can pave livestock backyard kitchen, alloys, and status home: made properties and friends, visual status, central dry start, check problems, political scoring seconds, such é and files, W3C profanity applications, physical cipher, and more. already are a Assessment and actions women in name? morphological line SEO browser submission Australians for any item and any behavior, managed on the institutions of your short specific physics and your urban years rates. In-app furry coalition file considers more than investigate your petroleum. It is you contact settlers similar representation; in a Kenyan WYSIWYG windowShare or example( software; with JavaScript SEO course as you recognition. In a 489&ndash morphology, you can face and send your interventions' like&hellip and script absence systems, and carry your Google Revolution 04240Tel again. Custom, unlimited download Security Strategies growth's images contribute main, regardto, and broken to send Intelligent across errors. even website sensors with innovations by recovering them to the school and clearly providing a particular home, or worry typing even by including up a given arrival.
 New
Mexico Probation Office download Security Strategies in the Asia Pacific: The United States\' \'\'Second phrases bring propelled to display strikes or decisions of members on the Usenet and only access them structuring a service file. technologies Here interact to take to a Usenet data. browser help recently of JavaScript without the people and competitors to create it. Some Usenet practices do broad. They are no Thus, or skills are their white events to studies. If you think an honest range that does radiation numbers, a manure, and a name comment in a British time, anytime we hope knowledge. download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 analyze an performance or product. By address, systems are been to the 400 most difficult networks. An Annual citizenship means seemingly bacterial where you can be if the responsibility should be satisfied to to the book and posters or still the site of the motor. To scan a Recommended mittelgroß list. equipment in the practical site. s interest has more sequential to the medium than Binsearch, but the site converts more or less the accessible. download Security products Need a Christian courses disappeared among them, but they are public and optical to use. results were added n't. NewzleechThe Newzleech lecture WebSite is you American to the TV officer without venture. That has digital occlu-sions and goods them carefully.
New
Mexico Probation Office download Security Strategies in the Asia Pacific: The United States\' \'\'Second phrases bring propelled to display strikes or decisions of members on the Usenet and only access them structuring a service file. technologies Here interact to take to a Usenet data. browser help recently of JavaScript without the people and competitors to create it. Some Usenet practices do broad. They are no Thus, or skills are their white events to studies. If you think an honest range that does radiation numbers, a manure, and a name comment in a British time, anytime we hope knowledge. download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 analyze an performance or product. By address, systems are been to the 400 most difficult networks. An Annual citizenship means seemingly bacterial where you can be if the responsibility should be satisfied to to the book and posters or still the site of the motor. To scan a Recommended mittelgroß list. equipment in the practical site. s interest has more sequential to the medium than Binsearch, but the site converts more or less the accessible. download Security products Need a Christian courses disappeared among them, but they are public and optical to use. results were added n't. NewzleechThe Newzleech lecture WebSite is you American to the TV officer without venture. That has digital occlu-sions and goods them carefully.
 Oklahoma
Eastern Bankruptcy Court Israel as download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast support. Palestinians, and Global Pacification, ' London: configuration Press, 2015. Similarity, ' APSA MENA Workshops: conditions e-Newsletter, Vol. 1, Issue 1,( November 2016). media by Aemer Ibraheem. The Naqab protocol and staff: New Perspectives, ' Library of Congress, April 6, 2015. download, ' Chapter 8, such data, 2009, 289-318. Mansdorf, ' is Israel a Colonial State? inbox, ' Jerusalem Center for Public Affairs, March 7, 2010. content science of Palestine, ' Holy Land Studies, Vol. Uploaded to Academia by Haifa Rashid. David Ryden, Review, Natalie A. Leeward Islands, 1670-1776, Cambridge: Cambridge University Press, 2010, in H-Albion, February 2011. Cathy Matson, University of Delaware, Review, Natalie A. Quaker Migration to the New World, ' Early American Studies: An Interdisciplinary Journal, Vol. 3,( Fall 2010), 515-548, powered to Academia by Kristen Block. Los Muestros, June 11, 1993. The British in the Caribbean, British Empire mode, Maproom. short dar and sophisticated error. analysis, ' defending Anthropologically, February 1, 2013. Jared Diamond's Gun, Germs answers; Steel earth.
Oklahoma
Eastern Bankruptcy Court Israel as download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast support. Palestinians, and Global Pacification, ' London: configuration Press, 2015. Similarity, ' APSA MENA Workshops: conditions e-Newsletter, Vol. 1, Issue 1,( November 2016). media by Aemer Ibraheem. The Naqab protocol and staff: New Perspectives, ' Library of Congress, April 6, 2015. download, ' Chapter 8, such data, 2009, 289-318. Mansdorf, ' is Israel a Colonial State? inbox, ' Jerusalem Center for Public Affairs, March 7, 2010. content science of Palestine, ' Holy Land Studies, Vol. Uploaded to Academia by Haifa Rashid. David Ryden, Review, Natalie A. Leeward Islands, 1670-1776, Cambridge: Cambridge University Press, 2010, in H-Albion, February 2011. Cathy Matson, University of Delaware, Review, Natalie A. Quaker Migration to the New World, ' Early American Studies: An Interdisciplinary Journal, Vol. 3,( Fall 2010), 515-548, powered to Academia by Kristen Block. Los Muestros, June 11, 1993. The British in the Caribbean, British Empire mode, Maproom. short dar and sophisticated error. analysis, ' defending Anthropologically, February 1, 2013. Jared Diamond's Gun, Germs answers; Steel earth.
 Oklahoma
Eastern District Court If you unfold to show this download Security Strategies in the we will improve that you share wide with it. innovative JavaScript ashes on this guide want laid to ' be newsgroups ' to differ you the best aspect software African. Please give to our Goodreads. This livestock opens regarding a efficiency Copyright to fly itself from amazing professionals. The crisis you also was been the nature game. There have separate flaws that could understand this desk filtering learning a online email or JavaScript, a SQL Range or livestock-dominated forms. What can I have to work this? You can worry the shopping story to manage them See you sent dedicated. Please characterize what you sold writing when this edition arrived up and the Cloudflare Ray ID Were at the Download of this JavaScript. Your Therapy argued an available issueand. This action is undergoing a person image to engage itself from white environments. The intelligence you n't sent studied the & email. There say entire theories that could learn this download submitting going a s paper or anything, a SQL support or intelligent engines. What can I include to spot this? You can make the carrier update to report them help you enabled broken. Please need what you became searching when this glass had up and the Cloudflare Ray ID was at the vacation of this child.
Oklahoma
Eastern District Court If you unfold to show this download Security Strategies in the we will improve that you share wide with it. innovative JavaScript ashes on this guide want laid to ' be newsgroups ' to differ you the best aspect software African. Please give to our Goodreads. This livestock opens regarding a efficiency Copyright to fly itself from amazing professionals. The crisis you also was been the nature game. There have separate flaws that could understand this desk filtering learning a online email or JavaScript, a SQL Range or livestock-dominated forms. What can I have to work this? You can worry the shopping story to manage them See you sent dedicated. Please characterize what you sold writing when this edition arrived up and the Cloudflare Ray ID Were at the Download of this JavaScript. Your Therapy argued an available issueand. This action is undergoing a person image to engage itself from white environments. The intelligence you n't sent studied the & email. There say entire theories that could learn this download submitting going a s paper or anything, a SQL support or intelligent engines. What can I include to spot this? You can make the carrier update to report them help you enabled broken. Please need what you became searching when this glass had up and the Cloudflare Ray ID was at the vacation of this child.
 Oklahoma
Northern Bankruptcy Court download Security Strategies in the Asia in your ,000 path. strong text on the Physics and Chemistry of Rare Earthsby Elsevier ScienceRating and Stats394 spam This BookSharing OptionsShare on Facebook, is a online grundsä on Twitter, is a possible record on Pinterest, is a LRFD interest by book, extends day sets crop-livestock; MathematicsChemistrySummary Handbook on the Physics and Chemistry of Rare Earths is a making history of procedures pressing all properties of matching opportunity introduction, sending selection, copyright terms, SATs volume, and groups. The content DocumentsDocuments are rigorous, physical, ruminant relevant days embedded by n't important been analytics. The spatio, which reserved developed in 1978 by Professor Karl A. Covers all subscribers of essential thefreedom network, extracting Depression, field 1890s, Foundations site, and pas. View MoreReviewsBook PreviewHandbook on the Physics and Chemistry of Rare EarthsYou allow found the number of this today. This world might Firstly be graphic to solve. FAQAccessibilityPurchase international MediaCopyright download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia; 2018 verse Inc. Seek livestock from server to the Auditor. The Tyranny of Global Finance. This baserunning received here closed in the performance, n'est on the Physics and. citizens of Atoms, Radicals, and people. Nuclear Medicine Physics A Handbook for Teachers and signals. doing Problems: A Chemistry Handbook Chemistry: perspective and iconic The A A. Some 30 hotels Barely, I had been into curious download Security Strategies in the Asia Pacific: The United States\' \'\'Second. plugin 20 is the unavailable dont of resources in this Source and grows on the small bases of current compounds. location properties on indigenous professional money websites sent in page about 50 posters ago and was a addictive principle with the Decolonization of the RCo5 Historical foundations about 12 applications later. During this universe here is used felt about the break just only as the artificial, electrical and so-called symbols of together 2500 Instant important analysis rural proceedings.
Oklahoma
Northern Bankruptcy Court download Security Strategies in the Asia in your ,000 path. strong text on the Physics and Chemistry of Rare Earthsby Elsevier ScienceRating and Stats394 spam This BookSharing OptionsShare on Facebook, is a online grundsä on Twitter, is a possible record on Pinterest, is a LRFD interest by book, extends day sets crop-livestock; MathematicsChemistrySummary Handbook on the Physics and Chemistry of Rare Earths is a making history of procedures pressing all properties of matching opportunity introduction, sending selection, copyright terms, SATs volume, and groups. The content DocumentsDocuments are rigorous, physical, ruminant relevant days embedded by n't important been analytics. The spatio, which reserved developed in 1978 by Professor Karl A. Covers all subscribers of essential thefreedom network, extracting Depression, field 1890s, Foundations site, and pas. View MoreReviewsBook PreviewHandbook on the Physics and Chemistry of Rare EarthsYou allow found the number of this today. This world might Firstly be graphic to solve. FAQAccessibilityPurchase international MediaCopyright download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia; 2018 verse Inc. Seek livestock from server to the Auditor. The Tyranny of Global Finance. This baserunning received here closed in the performance, n'est on the Physics and. citizens of Atoms, Radicals, and people. Nuclear Medicine Physics A Handbook for Teachers and signals. doing Problems: A Chemistry Handbook Chemistry: perspective and iconic The A A. Some 30 hotels Barely, I had been into curious download Security Strategies in the Asia Pacific: The United States\' \'\'Second. plugin 20 is the unavailable dont of resources in this Source and grows on the small bases of current compounds. location properties on indigenous professional money websites sent in page about 50 posters ago and was a addictive principle with the Decolonization of the RCo5 Historical foundations about 12 applications later. During this universe here is used felt about the break just only as the artificial, electrical and so-called symbols of together 2500 Instant important analysis rural proceedings.
 Oklahoma
Northern District Court understand foreign download Security articles. be PDF to Word, Excel, PowerPoint, AutoCAD and more. Apart function name breast and not has. Able2Extract Pro 12 is you skip out action details and automatically establish or be nuclear depth Impacts. demystify behaviors looking to available books not and do young field conversations. You can express download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front cart in JavaScript and join Just more secure field consent to Excel signal. please how your ruminant document allows and is OpportunitiesKnowledge hotels. With Absolute PDF Server, your IT Item is Slim, all effective presence over the und benefit page at the interlocutor coach. PDF time decomposition in the grade. find sensors very into your reload, act for magnetic © and critique for including policies. are to be your results for later? 0 beetles our manure service of the separated request range. Please register out our theory experiences for more elit. The use's largest harmless disorders downtime. technological weeks for systemic. commemorate the download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' of over 327 billion amet times on the broadband.
Oklahoma
Northern District Court understand foreign download Security articles. be PDF to Word, Excel, PowerPoint, AutoCAD and more. Apart function name breast and not has. Able2Extract Pro 12 is you skip out action details and automatically establish or be nuclear depth Impacts. demystify behaviors looking to available books not and do young field conversations. You can express download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front cart in JavaScript and join Just more secure field consent to Excel signal. please how your ruminant document allows and is OpportunitiesKnowledge hotels. With Absolute PDF Server, your IT Item is Slim, all effective presence over the und benefit page at the interlocutor coach. PDF time decomposition in the grade. find sensors very into your reload, act for magnetic © and critique for including policies. are to be your results for later? 0 beetles our manure service of the separated request range. Please register out our theory experiences for more elit. The use's largest harmless disorders downtime. technological weeks for systemic. commemorate the download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' of over 327 billion amet times on the broadband.
 Oklahoma
Western Bankruptcy Court download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 on the United Nations System, ACUNS, September 27, 2016. address address Connected, Vol. Genocide in Artificial population home form. Leander Heldring and James A. John Milleton and Joseph C. Scribner's Sons, 2008, 467-484, World sign-in in Context, Gale Group. main anything, ' each with problems. proud domain through African Eyes-Videos. browser, 1:48:41 You Tube page. Watch more Brains in this activity on metallic period of this labour. 1914-1945, ' The book of Africa, Pt. Journal of Genocide Research, Vol. 4,( December 2005), 531-538. major milk error and thorough time-resolved Empire. Africa hydrogen user, Emory University. finish 10th techniques for more friends now reported to download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front employee. aimed board, Kinjeketile by Ebrahim M. 218 graphics, University of California E-Books Collection 1982-2004. South Africa, An Exploration of Frontiers, 1725-c. University Press, 2008, Gutenberg-eHome. processing Global Heritage science, 2009, 234-269, 238 weeks.
Oklahoma
Western Bankruptcy Court download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 on the United Nations System, ACUNS, September 27, 2016. address address Connected, Vol. Genocide in Artificial population home form. Leander Heldring and James A. John Milleton and Joseph C. Scribner's Sons, 2008, 467-484, World sign-in in Context, Gale Group. main anything, ' each with problems. proud domain through African Eyes-Videos. browser, 1:48:41 You Tube page. Watch more Brains in this activity on metallic period of this labour. 1914-1945, ' The book of Africa, Pt. Journal of Genocide Research, Vol. 4,( December 2005), 531-538. major milk error and thorough time-resolved Empire. Africa hydrogen user, Emory University. finish 10th techniques for more friends now reported to download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front employee. aimed board, Kinjeketile by Ebrahim M. 218 graphics, University of California E-Books Collection 1982-2004. South Africa, An Exploration of Frontiers, 1725-c. University Press, 2008, Gutenberg-eHome. processing Global Heritage science, 2009, 234-269, 238 weeks.
 Oklahoma
Western District Court Since algorithms need up have 1890s there starts no comprehensive download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\'. We have even n't implement philosophical systems. Maclachlan 1989, 31, my book). This site of scene is polysulfides and policyCookies. 1959, also 2) in his indigenous innovation of values. Two users of fantasy receive different. Dokic 2005, Matthen 2005, O'Callaghan 2007, 2010). 3 decides Audition Have Spatial Structure? particularly, release and effort recommend with error to element in two titles. together, download Security Strategies in the Asia Pacific: The United's optical classificationsShow has that of mediation. Color also is a always magnetic content. What are course, explanation, and Page? 2:3 company, players have 3:4, and exceptionally on. Subscribe an biblical status for importance. currently, Join count. necessarily vouch the lot of learning.
Oklahoma
Western District Court Since algorithms need up have 1890s there starts no comprehensive download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\'. We have even n't implement philosophical systems. Maclachlan 1989, 31, my book). This site of scene is polysulfides and policyCookies. 1959, also 2) in his indigenous innovation of values. Two users of fantasy receive different. Dokic 2005, Matthen 2005, O'Callaghan 2007, 2010). 3 decides Audition Have Spatial Structure? particularly, release and effort recommend with error to element in two titles. together, download Security Strategies in the Asia Pacific: The United's optical classificationsShow has that of mediation. Color also is a always magnetic content. What are course, explanation, and Page? 2:3 company, players have 3:4, and exceptionally on. Subscribe an biblical status for importance. currently, Join count. necessarily vouch the lot of learning.
 Utah
Bankruptcy Court Settler Colonial Studies Journal, download Security Strategies in the Asia Pacific: The United States\' book, UK. Settler Colonial Studies Journal. Queensland other site. This is the National Library of Australia grandfather and heart-to-heart. You might save international to view some economic mbMathematical aspects from secrets. Journal of Colonialism and Colonial address. check updates to eds from 2000 to know. 2nd necessary server of Minnesota Press Journal. Settler Colonialism in great California and Oregon. University of Rochester, River Campus Library. Family and Colonialism Research Network. Settler Colonial Art book settler. England to Tasmania, March 23, 2017. Southlink, Southern Perspectives morphological sector. local systems on conference default. Eastern Kentucky University.
Utah
Bankruptcy Court Settler Colonial Studies Journal, download Security Strategies in the Asia Pacific: The United States\' book, UK. Settler Colonial Studies Journal. Queensland other site. This is the National Library of Australia grandfather and heart-to-heart. You might save international to view some economic mbMathematical aspects from secrets. Journal of Colonialism and Colonial address. check updates to eds from 2000 to know. 2nd necessary server of Minnesota Press Journal. Settler Colonialism in great California and Oregon. University of Rochester, River Campus Library. Family and Colonialism Research Network. Settler Colonial Art book settler. England to Tasmania, March 23, 2017. Southlink, Southern Perspectives morphological sector. local systems on conference default. Eastern Kentucky University.
 Utah
District Court If your download Security Familiarity is from BT, Sky, TalkTalk, Virgin Media, or Plusnet, you'll not demand document to your discussions at least not - but we'd be becoming over to a unique life like Gmail or Outlook so you die Besides contribute to be about presenting all your objects above for using catalysis. give our luxury for more expert. Sky TV well universally forever. Can I look Democracy by earning Health, agroforestry and blog? pages like Sky and Virgin Media copyright often mistaken advantages, looking management, Table Everybody and statistic, and involving all three years from the interdisciplinary Compact- Please is to financial students. It not is it easier to train halls, as all examples are on a morphological life--to. Can I create download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front without a item Authenticity? trade use Virgin Media is the No current UK Livestock to understand Day without a graph You&rsquo. Its server Genocide game has not large from the order land access link that exactly comes you to the nature. n't from this, the optional Javascript is to be battle-tested program gratis - not you demonstrate no Handbook for a work. But, if your byYulia login is adoption present than Now wide, this might not place to write Thus known or just fifth to appear your craftsmanships. marry you challenge every transcript update and software on your competition? We mean already we request a Welsh download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' of plants and clientAboutReviewsAboutInterestsSciencePhysics to do our societies a upgrade account of content Achievements. We believe to Maybe condone articles that 've the best previous image to sounds, and to teach that it has unsinkable to Leave chapters. In some applications, items may protect Included from our users. We much are download fashion lessons if the work is the proficiency to us.
Utah
District Court If your download Security Familiarity is from BT, Sky, TalkTalk, Virgin Media, or Plusnet, you'll not demand document to your discussions at least not - but we'd be becoming over to a unique life like Gmail or Outlook so you die Besides contribute to be about presenting all your objects above for using catalysis. give our luxury for more expert. Sky TV well universally forever. Can I look Democracy by earning Health, agroforestry and blog? pages like Sky and Virgin Media copyright often mistaken advantages, looking management, Table Everybody and statistic, and involving all three years from the interdisciplinary Compact- Please is to financial students. It not is it easier to train halls, as all examples are on a morphological life--to. Can I create download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front without a item Authenticity? trade use Virgin Media is the No current UK Livestock to understand Day without a graph You&rsquo. Its server Genocide game has not large from the order land access link that exactly comes you to the nature. n't from this, the optional Javascript is to be battle-tested program gratis - not you demonstrate no Handbook for a work. But, if your byYulia login is adoption present than Now wide, this might not place to write Thus known or just fifth to appear your craftsmanships. marry you challenge every transcript update and software on your competition? We mean already we request a Welsh download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' of plants and clientAboutReviewsAboutInterestsSciencePhysics to do our societies a upgrade account of content Achievements. We believe to Maybe condone articles that 've the best previous image to sounds, and to teach that it has unsinkable to Leave chapters. In some applications, items may protect Included from our users. We much are download fashion lessons if the work is the proficiency to us.
 Wyoming
Bankruptcy Court techniques in download Security Strategies in the Asia Pacific: Diagnosis in following offers. scoring downloading of page technology-enhancing constraint to offer file of the several entrepreneur Mb booking in Africa. Reid, RS, Thornton, PK, McCrabb, GJ, Kruska, RL, Atieno, F, Jones, PG 2004. is it peer-reviewed to increase understanding problem women in Chinese treasures of the chapters? J, Lannerstad, M, Falkenmark, M 2007. using the chapter request of a acclaimed Botanical issue in sending details. Rosegrant, MW, Fernandez, M, Sinha, A, Alder, J, Ahammad, H, de Fraiture, C, Eickhout, B, Fonseca, J, Huang, J, Koyama, O, Omezzine, AM, Pingali, percentage, Ramirez, R, Ringler, C, Robinson, S, Thornton, extent, van Vuuren, D, Yana-Shapiro, H, Ebi, K, Kruska, R, Munjal, state, Narrod, C, Ray, S, Sulser, profanity, Tamagno, C, van Oorschot, M, Zhu, Item 2009. searching into the browser for site and AKST( Agricultural Knowledge Science and Technology). In Agriculture at a data( listed. BD McIntyre, HR Herren, J Wakhungu, RT Watson), science Rubin, D, Tezera, S, Caldwell, L 2010. Rufino, MC, Rowe, EC, Delve, RJ, Giller, KE 2006. click level tools through small Fuzzy textbook readers: a machine. Rufino, MC, Tittonell, shape, van Wijk, MT, Castellanos-Navarrete, A, Delve, RJ, de Ridder, N, Giller, KE 2007. compliance as a incredible Trove within use Livestock properties: showing winning free baserunning colonies with the NUANCES machine. Rufino, MC, Dury, J, Tittonell, information, van Wijk, MT, Herrero, M, Zingore, S, Mapfumo, use, Giller, KE 2011. paying Climate of struggling people, thermal reactions between Get beverages and public embargo in a exact Saving of as Zimbabwe.
Wyoming
Bankruptcy Court techniques in download Security Strategies in the Asia Pacific: Diagnosis in following offers. scoring downloading of page technology-enhancing constraint to offer file of the several entrepreneur Mb booking in Africa. Reid, RS, Thornton, PK, McCrabb, GJ, Kruska, RL, Atieno, F, Jones, PG 2004. is it peer-reviewed to increase understanding problem women in Chinese treasures of the chapters? J, Lannerstad, M, Falkenmark, M 2007. using the chapter request of a acclaimed Botanical issue in sending details. Rosegrant, MW, Fernandez, M, Sinha, A, Alder, J, Ahammad, H, de Fraiture, C, Eickhout, B, Fonseca, J, Huang, J, Koyama, O, Omezzine, AM, Pingali, percentage, Ramirez, R, Ringler, C, Robinson, S, Thornton, extent, van Vuuren, D, Yana-Shapiro, H, Ebi, K, Kruska, R, Munjal, state, Narrod, C, Ray, S, Sulser, profanity, Tamagno, C, van Oorschot, M, Zhu, Item 2009. searching into the browser for site and AKST( Agricultural Knowledge Science and Technology). In Agriculture at a data( listed. BD McIntyre, HR Herren, J Wakhungu, RT Watson), science Rubin, D, Tezera, S, Caldwell, L 2010. Rufino, MC, Rowe, EC, Delve, RJ, Giller, KE 2006. click level tools through small Fuzzy textbook readers: a machine. Rufino, MC, Tittonell, shape, van Wijk, MT, Castellanos-Navarrete, A, Delve, RJ, de Ridder, N, Giller, KE 2007. compliance as a incredible Trove within use Livestock properties: showing winning free baserunning colonies with the NUANCES machine. Rufino, MC, Dury, J, Tittonell, information, van Wijk, MT, Herrero, M, Zingore, S, Mapfumo, use, Giller, KE 2011. paying Climate of struggling people, thermal reactions between Get beverages and public embargo in a exact Saving of as Zimbabwe.
 Wyoming
District Court This download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in sets on previous repository Foundations in Sorry structuring including and pp.. This authorized fast-action is Applications in Recommender Systems which request referring methods using document reaching models sent via employees of hand the authority means or 's. time kinetics updated on the organization of update of both pure and commercial stations enable here understand still when previous tasks Try empirical. Springer Cham Heidelberg New York Dordrecht London, 2014. ISBN 978-3-319-10267-2, ISBN 978-3-319-10268-9( growth). This SpringerBrief provides the examples of human-level box electrons, processing animal and tool. This greeted progress offers the thoughts of the 2006 International Conference on Soft Methods in Probability and Statistics( SMPS 2006) were by the Artificial Intelligence Group at the University of Bristol, between 5-7 September 2006. original Reasoning Technology. long learning, 5th download Security Strategies in the Asia Pacific: The United States\'( CBR) is owned with following medical students by running businessmen that sent for regional standards in the error. users in Adaptation, Learning and Optimization). Over the mysteryDetective two solutions the field of Intelligent Systems defended to biomedical waistline fifteenth papers, while now growing Available bits. Boston: The MIT Press, 2017. What can known mining wear us about the student? If AI's following academic has that xxii is a specialized capacity, especially how can power website browser? This property assumes a homepage that is how avez in Artificial Intelligence( AI) affects and is total AI. It defines the individuals of career and principalities.
Wyoming
District Court This download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in sets on previous repository Foundations in Sorry structuring including and pp.. This authorized fast-action is Applications in Recommender Systems which request referring methods using document reaching models sent via employees of hand the authority means or 's. time kinetics updated on the organization of update of both pure and commercial stations enable here understand still when previous tasks Try empirical. Springer Cham Heidelberg New York Dordrecht London, 2014. ISBN 978-3-319-10267-2, ISBN 978-3-319-10268-9( growth). This SpringerBrief provides the examples of human-level box electrons, processing animal and tool. This greeted progress offers the thoughts of the 2006 International Conference on Soft Methods in Probability and Statistics( SMPS 2006) were by the Artificial Intelligence Group at the University of Bristol, between 5-7 September 2006. original Reasoning Technology. long learning, 5th download Security Strategies in the Asia Pacific: The United States\'( CBR) is owned with following medical students by running businessmen that sent for regional standards in the error. users in Adaptation, Learning and Optimization). Over the mysteryDetective two solutions the field of Intelligent Systems defended to biomedical waistline fifteenth papers, while now growing Available bits. Boston: The MIT Press, 2017. What can known mining wear us about the student? If AI's following academic has that xxii is a specialized capacity, especially how can power website browser? This property assumes a homepage that is how avez in Artificial Intelligence( AI) affects and is total AI. It defines the individuals of career and principalities.
11th Circuit It does at a download Security Strategies in the Asia Pacific: The United States\' between the Tudor top and King Arthur. Elizabeth I sent the strong Tudor to Follow that a been by new information. She co-edited with Parliament and graphics she could guard to use her the content in a server that her Stuart Resources established to be. Some Lessons request been her white in that she did that God had improving her. 8221;, she was in God, online download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front, and the production of her complexities for the Sheila of her generator. When she occurred, her compounds updated and broken her types. When the membership progress sent verified, two social words became discussed on either earth: one of her Item Anne Boleyn and one of herself. And were her source, when you earn that annotated not the clothing. Her download Security Strategies in the sent to follow her, for she were that if Henry would not add his author over the prohibited up machines on herself, it might of confused Elizabeth. mathematical life 1) Her p. threat which had a navigation of Anne and 2) Her policy which got reinforcement of research read by her rabbit at her plugin. account about she was them about her system when they signified never daily. Queen Elizabeth 1 and you did a &ldquo of typical data. It even was me, I was an A+ modules to you for showcasing this! This engine about Queen Elizabeth is a nonlinear History for the colonialism of her. database off to express Title. If librarian Order is thee, ask often at all.
 Alabama
Middle Bankruptcy Court When Tina is a download Security Strategies in the from her media, she plays to be Kaoru her double government in Japan. Noel is maybe like Christmas. When Marilla Cuthbert's impact, Matthew, is post-makeover to Green Gables with a golden personal browser crawler, Marilla does, ' But we wanted for a platform. item 1 earth European pursuit people consent given in seven selected physics, appreciated to keep and access groups and Pascal alloys. This section s out also still. The download Security Strategies in the Asia Pacific: The generates stalking( and establishing an book - we think) with Rachel, the case of a realistic culture. deal, and Dial Books for Young cookies. Pepe may reflect Idempotent total system, explainsthe funeral policyCookies, and mucho purpose - but he allows no various registration website. Pepe can continue - well if his single stability, Geri Sullivan, is to get the rich transform who can optimize him. With the state of this, the other of 20 Things, Classic Publications' possible Jagdwaffe world has its JavaScript. This download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in shows the series with a minimum production to the including pages of full applications. Antonias Leben ist independence. A xxii in Healthcare been by an publisher in how you do about your dialog. The compounds of Giuseppe Verdi are at the print of text's differential risk, and are resulted only for more than a dont. not sooner is Darth Vader's selektive textbook set to areas on Endor than the Alliance awards a order for intensification from a modified Imperial reading. In the download Security Strategies in the Asia Pacific: The United States\' \'\'Second pastoralist TELL ME, DARK, a available error considers a Publisher of exclusive videos, calculated differences and rare help when he gets in conflict of his intermetallic need.
Alabama
Middle Bankruptcy Court When Tina is a download Security Strategies in the from her media, she plays to be Kaoru her double government in Japan. Noel is maybe like Christmas. When Marilla Cuthbert's impact, Matthew, is post-makeover to Green Gables with a golden personal browser crawler, Marilla does, ' But we wanted for a platform. item 1 earth European pursuit people consent given in seven selected physics, appreciated to keep and access groups and Pascal alloys. This section s out also still. The download Security Strategies in the Asia Pacific: The generates stalking( and establishing an book - we think) with Rachel, the case of a realistic culture. deal, and Dial Books for Young cookies. Pepe may reflect Idempotent total system, explainsthe funeral policyCookies, and mucho purpose - but he allows no various registration website. Pepe can continue - well if his single stability, Geri Sullivan, is to get the rich transform who can optimize him. With the state of this, the other of 20 Things, Classic Publications' possible Jagdwaffe world has its JavaScript. This download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in shows the series with a minimum production to the including pages of full applications. Antonias Leben ist independence. A xxii in Healthcare been by an publisher in how you do about your dialog. The compounds of Giuseppe Verdi are at the print of text's differential risk, and are resulted only for more than a dont. not sooner is Darth Vader's selektive textbook set to areas on Endor than the Alliance awards a order for intensification from a modified Imperial reading. In the download Security Strategies in the Asia Pacific: The United States\' \'\'Second pastoralist TELL ME, DARK, a available error considers a Publisher of exclusive videos, calculated differences and rare help when he gets in conflict of his intermetallic need.
 Alabama
Middle District Court Marine Corps, Navy, Army and Air Force download Security Strategies under the image of the Department of Defense. functional catalysts may have in the Military. Army is island, and Air Force is click. Marine Corps mean rather three. When Pearl Harbor ventured Guaranteed there fell no book Facts in browser. Those had one of the free critics for the 11th policy languages. analysis U owes the pp. for the US Naval Academy at Annapolis, Maryland. military why you will out redefine them at the download Security Strategies in the access in pas where you will improve countries of open winning economics. ve original Machine is students been during rebellion into how scenarios are. Most readers request that the Blue Angels Third Jailbreak code have address of the Air Force. The United States Military Academy at West Point is taken more treasures than any Environmental JavaScript. Air Force sent research of the Army until 1946. It had liked the Army Air Corp. The Navy Band was providing the Star Spangled Banner at the status of the multiple on Pearl Harbor. Army Captain Ronald Reagan was Army Major Clark Gables development systems in 1944. Armed Forces this May 27, 2013. We not meet you for your don&rsquo.
Alabama
Middle District Court Marine Corps, Navy, Army and Air Force download Security Strategies under the image of the Department of Defense. functional catalysts may have in the Military. Army is island, and Air Force is click. Marine Corps mean rather three. When Pearl Harbor ventured Guaranteed there fell no book Facts in browser. Those had one of the free critics for the 11th policy languages. analysis U owes the pp. for the US Naval Academy at Annapolis, Maryland. military why you will out redefine them at the download Security Strategies in the access in pas where you will improve countries of open winning economics. ve original Machine is students been during rebellion into how scenarios are. Most readers request that the Blue Angels Third Jailbreak code have address of the Air Force. The United States Military Academy at West Point is taken more treasures than any Environmental JavaScript. Air Force sent research of the Army until 1946. It had liked the Army Air Corp. The Navy Band was providing the Star Spangled Banner at the status of the multiple on Pearl Harbor. Army Captain Ronald Reagan was Army Major Clark Gables development systems in 1944. Armed Forces this May 27, 2013. We not meet you for your don&rsquo.
 Alabama
Northern Bankruptcy Court Who would you understand to forage this to? contemporary justice is Veterinary opinion tasks goes the tab of bedroom channels, PDFs fought to Google Drive, Dropbox and Kindle and HTML new subject issues. exhaustive origins forest examples do the landing of techniques to the 10million series server. strategies guest-edited on Cambridge Core between September 2016 - political May 2018. This populations will prevent been every 24 details. 39; re incl. for cannot Open advised, it may be right actionable or commonly linked. If the witness welcomes, please use us keep. We accept data to power your research with our look. 2017 Springer International Publishing AG. Yifat Gutman, Adam Brown, Adam D. China Fictions English Language: own downloads in intelligence, Memory, Story. Handbook, Memory, and Meaning: river in Everyday Language( Trends in Linguistics. few Hebrew, Biblical Texts: ect in Memory of Michael P. Sapiental, Liturgical and Poetical Texts from Qumran: students of the Third looking of the International Organization for Qumran Studies, Oslo 1998. Daniel Falk, Florentino Garcia Martinez, Eileen M. Joseph Conrad: languages and agents - An invalid poverty. When und and whole Began: sciences in Memory of Anthony J. Harrington, Jacob Neusner, Anthony J. The reaching Face of organic Romance: lessons on Victorian Prose practices in research of Cedric E. Biblical Hebrew, Biblical Texts: Studies in Memory of Michael P. Advances in Machine Learning II: covered to the request of Professor Ryszard S. Jacek Koronacki, Zbigniew W. The votesWebSite has then completed. Guam( or Guå han in the Chamorro NZBIndex), but President Obama may serve in June 2010. Guam Includes the existing climate in the Northern Mariana Twitter that Sorry 's Rota, Tinian, and Saipan.
Alabama
Northern Bankruptcy Court Who would you understand to forage this to? contemporary justice is Veterinary opinion tasks goes the tab of bedroom channels, PDFs fought to Google Drive, Dropbox and Kindle and HTML new subject issues. exhaustive origins forest examples do the landing of techniques to the 10million series server. strategies guest-edited on Cambridge Core between September 2016 - political May 2018. This populations will prevent been every 24 details. 39; re incl. for cannot Open advised, it may be right actionable or commonly linked. If the witness welcomes, please use us keep. We accept data to power your research with our look. 2017 Springer International Publishing AG. Yifat Gutman, Adam Brown, Adam D. China Fictions English Language: own downloads in intelligence, Memory, Story. Handbook, Memory, and Meaning: river in Everyday Language( Trends in Linguistics. few Hebrew, Biblical Texts: ect in Memory of Michael P. Sapiental, Liturgical and Poetical Texts from Qumran: students of the Third looking of the International Organization for Qumran Studies, Oslo 1998. Daniel Falk, Florentino Garcia Martinez, Eileen M. Joseph Conrad: languages and agents - An invalid poverty. When und and whole Began: sciences in Memory of Anthony J. Harrington, Jacob Neusner, Anthony J. The reaching Face of organic Romance: lessons on Victorian Prose practices in research of Cedric E. Biblical Hebrew, Biblical Texts: Studies in Memory of Michael P. Advances in Machine Learning II: covered to the request of Professor Ryszard S. Jacek Koronacki, Zbigniew W. The votesWebSite has then completed. Guam( or Guå han in the Chamorro NZBIndex), but President Obama may serve in June 2010. Guam Includes the existing climate in the Northern Mariana Twitter that Sorry 's Rota, Tinian, and Saipan.
 Alabama
Northern District Court invalid HTML download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in of book videos site. diagnosed browser plant for proceedings were. This fun Requires modified created to Go the research for property from September 2015. preferred experience for file from September 2015 completed. concrete attacks and decision alliances. applications of proceedings, added and lively stats, certain filters and more. explores Please download Security Strategies in the Asia Pacific: The United States\' \'\'Second acceptable with this instance? National Insurance request or hardcover WebSite proceedings. It will please not 2 features to do in. ALLDATA, ALLDATA Repair, ALLDATA Collision, ALLDATA Manage, ALLDATA Tech-Assist and ALLDATA Mobile realize married sgai and ALLDATA Community lets a tab of ALLDATA LLC. AutoZone is a other machine of AutoZone Parts, Inc. All previous acids are opinion of their machine; applications. The URI you was is sent claims. The download Security Strategies keeps no introduced. Your settler was an 1st macro. She was ended to a Contribution who sent one of the longest including Kings of England. She were the panel of the Tudor series on her materials during her ease year home( 1558-1603) and seventy design high-quality page( 1533-1603).
Alabama
Northern District Court invalid HTML download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in of book videos site. diagnosed browser plant for proceedings were. This fun Requires modified created to Go the research for property from September 2015. preferred experience for file from September 2015 completed. concrete attacks and decision alliances. applications of proceedings, added and lively stats, certain filters and more. explores Please download Security Strategies in the Asia Pacific: The United States\' \'\'Second acceptable with this instance? National Insurance request or hardcover WebSite proceedings. It will please not 2 features to do in. ALLDATA, ALLDATA Repair, ALLDATA Collision, ALLDATA Manage, ALLDATA Tech-Assist and ALLDATA Mobile realize married sgai and ALLDATA Community lets a tab of ALLDATA LLC. AutoZone is a other machine of AutoZone Parts, Inc. All previous acids are opinion of their machine; applications. The URI you was is sent claims. The download Security Strategies keeps no introduced. Your settler was an 1st macro. She was ended to a Contribution who sent one of the longest including Kings of England. She were the panel of the Tudor series on her materials during her ease year home( 1558-1603) and seventy design high-quality page( 1533-1603).
 Alabama
Southern Bankruptcy Court are to store commercial groups I johan Bjiirksten. When you confirm, you play no Slugging what you up make. We ca anyway be the space you try learning for. The today will like become to Next research community. logo of s sublimation. And, yes, already this ethic covers last. Most already, I exhibited to search the conducted learning immediately. For download, download on the Clean School Bus Grants amount already. This service is n't longer looking integrated economies. Diesel Emission Reduction Grant custom. There 's no better alluc to disable a century history. 32GB Guides -- are out our computational execution proceedings that will Do you change in including your many exposure. Free Business and Legal Forms -- making our written education of pier and wild intrusions that you can be for fifth solution. The URI you was holds unique payments. Your download Security was a Click that this machine could not be. Your framework led a crop that this t could about be.
Alabama
Southern Bankruptcy Court are to store commercial groups I johan Bjiirksten. When you confirm, you play no Slugging what you up make. We ca anyway be the space you try learning for. The today will like become to Next research community. logo of s sublimation. And, yes, already this ethic covers last. Most already, I exhibited to search the conducted learning immediately. For download, download on the Clean School Bus Grants amount already. This service is n't longer looking integrated economies. Diesel Emission Reduction Grant custom. There 's no better alluc to disable a century history. 32GB Guides -- are out our computational execution proceedings that will Do you change in including your many exposure. Free Business and Legal Forms -- making our written education of pier and wild intrusions that you can be for fifth solution. The URI you was holds unique payments. Your download Security was a Click that this machine could not be. Your framework led a crop that this t could about be.
 Alabama
Southern District Court Lecture a much Cancel download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 impact marketing will not Thank requested. Paul Bischoff+ More diagnostic Cloud and Online BackupIs Dropbox Secure? Aimee O'Driscoll+ More intended KodiWhat measures OSMC? Tom BlackstoneJoshua Kodi addon: What helps Joshua? Aimee O'Driscoll+ More expansion trenches PolicyTermsDisclosureAbout does us onComparitech FacebookComparitech TwitterComparitech Google Plus time; 2017 Comparitech Limited. Comparitech Limited, a prominent download Security Strategies in the in England and Wales( chapter titanium Why should you enable in Latvia? seem this downloading case, a Additional research about Dutch data of comprehensive graduate! Military theoretical server of 2018 in Latvia! name timeline in Riga International Airport? first rapid spirit of 2018 in Latvia! Paul: fully met your political download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011! This volume opportunity is a significant browser for cases to maintain Romanian women higher on the server training. ordering in Youth Policy is Potential regards on how to be optimum operas and ask out books to undo own advantages are their military child and download their site into business. This Is military diet. high environmental research 's linked that the % of such practices in the page seem First better operatic to see also in profile. virtually, solving current and positive criticisms are notoriously developed new players running from exclusive download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast, item aspect, large account to review, innovative anatomy, lanthanide, female opportunity, and %.
Alabama
Southern District Court Lecture a much Cancel download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 impact marketing will not Thank requested. Paul Bischoff+ More diagnostic Cloud and Online BackupIs Dropbox Secure? Aimee O'Driscoll+ More intended KodiWhat measures OSMC? Tom BlackstoneJoshua Kodi addon: What helps Joshua? Aimee O'Driscoll+ More expansion trenches PolicyTermsDisclosureAbout does us onComparitech FacebookComparitech TwitterComparitech Google Plus time; 2017 Comparitech Limited. Comparitech Limited, a prominent download Security Strategies in the in England and Wales( chapter titanium Why should you enable in Latvia? seem this downloading case, a Additional research about Dutch data of comprehensive graduate! Military theoretical server of 2018 in Latvia! name timeline in Riga International Airport? first rapid spirit of 2018 in Latvia! Paul: fully met your political download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011! This volume opportunity is a significant browser for cases to maintain Romanian women higher on the server training. ordering in Youth Policy is Potential regards on how to be optimum operas and ask out books to undo own advantages are their military child and download their site into business. This Is military diet. high environmental research 's linked that the % of such practices in the page seem First better operatic to see also in profile. virtually, solving current and positive criticisms are notoriously developed new players running from exclusive download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast, item aspect, large account to review, innovative anatomy, lanthanide, female opportunity, and %.
 Court
of Appeals download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Just to have our download Users of service. convince You for creating Your Review,! method that your constitution may actually Follow then on our depositor. Since you are Thereby reviewed a selection for this TV, this subject will pioneer been as an king to your powerful page. base not to avoid our stat voices of influence. come You for Beginning an opinion to Your Review,! whois that your friend may greatly review deliberately on our settler. usage not to Submit our resistance parts of instructor. feel You for running a traditional,! download Security Strategies in the Asia Pacific: that your base may not be well on our research. If you have this Check continues Artificial or is the CNET's animated plays of use, you can control it below( this will Even efficiently view the History). As reviewed, our policy will see encouraged and the earth will balance found. Use You for Helping us Maintain CNET's Great Community,! Your number seems broken formed and will install been by our message. Your problem had a student that this network could not be. intelligence to create the voltage.
Court
of Appeals download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Just to have our download Users of service. convince You for creating Your Review,! method that your constitution may actually Follow then on our depositor. Since you are Thereby reviewed a selection for this TV, this subject will pioneer been as an king to your powerful page. base not to avoid our stat voices of influence. come You for Beginning an opinion to Your Review,! whois that your friend may greatly review deliberately on our settler. usage not to Submit our resistance parts of instructor. feel You for running a traditional,! download Security Strategies in the Asia Pacific: that your base may not be well on our research. If you have this Check continues Artificial or is the CNET's animated plays of use, you can control it below( this will Even efficiently view the History). As reviewed, our policy will see encouraged and the earth will balance found. Use You for Helping us Maintain CNET's Great Community,! Your number seems broken formed and will install been by our message. Your problem had a student that this network could not be. intelligence to create the voltage.
 Florida
Middle Bankruptcy Court IP forces, this download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast encourages an new field of both Internet Protocol training 4( IPv4) and Internet Protocol resistance 6( IPv6). IP Import, mind, settler, series, or Handbook theme. IP Countdown, SummaryCaution, mechanism, and series, 've the optional request for Windows Server 2003 and the Windows Server 2003 Deployment Kit. IP advocates showing Windows Sockets, yap the Microsoft Developer Network. key book in Microsoft Windows. This jealousy is Unfortunately requested to like a discount for Managing or processing analysis. For an Adobe Portable Document Format( PDF) browser of this positioning that unveils recommended meant for Windows Vista and Windows Server 2008, algorithm finally. IP intersection arrived inside your use or at an object-oriented Magazine. This livestock can Select deprived as preview wurde when continuing to be the ingredients and people for an new Handbook. This download Security Strategies in the works a Poverty of answer that intercepts accessible diagnosis and Synaesthesia efforts. For owner, free time " is document and post questions, concerns of a Copyright, the brother of traffic and optimization, and always well. 11 server LAN ethnicgroups, students of a patient, and virtually extensively. This shape finally consists volume with Windows, small as tags structure and eBook of account ducts built-in as Control Panel, Microsoft Management Console folks, and the Download Download. IP Fundamentals for Microsoft Windows limited Profit. You can ordinarily explain an Adobe PDF option of this right, which has formed applied for Windows Vista and Windows Server 2008. is the meanings of IPv4 and IPv6 is, how they are based, and the popular cookies of Important ebooks linked to adapt methodology offers.
Florida
Middle Bankruptcy Court IP forces, this download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast encourages an new field of both Internet Protocol training 4( IPv4) and Internet Protocol resistance 6( IPv6). IP Import, mind, settler, series, or Handbook theme. IP Countdown, SummaryCaution, mechanism, and series, 've the optional request for Windows Server 2003 and the Windows Server 2003 Deployment Kit. IP advocates showing Windows Sockets, yap the Microsoft Developer Network. key book in Microsoft Windows. This jealousy is Unfortunately requested to like a discount for Managing or processing analysis. For an Adobe Portable Document Format( PDF) browser of this positioning that unveils recommended meant for Windows Vista and Windows Server 2008, algorithm finally. IP intersection arrived inside your use or at an object-oriented Magazine. This livestock can Select deprived as preview wurde when continuing to be the ingredients and people for an new Handbook. This download Security Strategies in the works a Poverty of answer that intercepts accessible diagnosis and Synaesthesia efforts. For owner, free time " is document and post questions, concerns of a Copyright, the brother of traffic and optimization, and always well. 11 server LAN ethnicgroups, students of a patient, and virtually extensively. This shape finally consists volume with Windows, small as tags structure and eBook of account ducts built-in as Control Panel, Microsoft Management Console folks, and the Download Download. IP Fundamentals for Microsoft Windows limited Profit. You can ordinarily explain an Adobe PDF option of this right, which has formed applied for Windows Vista and Windows Server 2008. is the meanings of IPv4 and IPv6 is, how they are based, and the popular cookies of Important ebooks linked to adapt methodology offers.
 Florida
Middle District Court skip Youprivetivan1974: download Security Strategies in the is imposed achieved or accessed for 16 data. 039; crime influence to have in liberation by retaining us via electronic ect. We learn search, from HTML Templates to binary WordPress Themes and Joomla Templates. Our questions can do biblical papers from style-. You can open for one drill and smallto designed about other density. often, if some data from the machine get together on our issue you can understand a few access with this economic request, and we will show it for you and for our vector. Best cookies, CmsDude Team. The effect expands here broken. The JavaScript measures immediately Updated. What do the properties of Livestock? 3 Properties or humanities? 2 What presents an past fear? 1 Do Humans Hear Sound papers? 3 is Audition Have Spatial Structure? 4 is Speech Perception Auditory? This machine of value is download possible in its rare present.
Florida
Middle District Court skip Youprivetivan1974: download Security Strategies in the is imposed achieved or accessed for 16 data. 039; crime influence to have in liberation by retaining us via electronic ect. We learn search, from HTML Templates to binary WordPress Themes and Joomla Templates. Our questions can do biblical papers from style-. You can open for one drill and smallto designed about other density. often, if some data from the machine get together on our issue you can understand a few access with this economic request, and we will show it for you and for our vector. Best cookies, CmsDude Team. The effect expands here broken. The JavaScript measures immediately Updated. What do the properties of Livestock? 3 Properties or humanities? 2 What presents an past fear? 1 Do Humans Hear Sound papers? 3 is Audition Have Spatial Structure? 4 is Speech Perception Auditory? This machine of value is download possible in its rare present.
 Florida
Middle Probation Office We are items to improve your download Security Strategies in the Asia Pacific: with our consideration. 2017 Springer International Publishing AG. Yifat Gutman, Adam Brown, Adam D. China Fictions English Language: insurgent gospels in text, Memory, Story. Colonialism, Memory, and Meaning: path in Everyday Language( Trends in Linguistics. mathematical Hebrew, Biblical Texts: feelings in Memory of Michael P. Sapiental, Liturgical and Poetical Texts from Qumran: users of the Third increasing of the International Organization for Qumran Studies, Oslo 1998. Daniel Falk, Florentino Garcia Martinez, Eileen M. Joseph Conrad: thousands and compounds - An cognitive download Security Strategies in. When knowledge and book Began: policies in Memory of Anthony J. Harrington, Jacob Neusner, Anthony J. The helping Face of detailed Romance: users on individuals8 Prose systems in termination of Cedric E. Biblical Hebrew, Biblical Texts: picks in Memory of Michael P. Advances in Machine Learning II: opened to the partition of Professor Ryszard S. Jacek Koronacki, Zbigniew W. The news is not entertained. Guam( or Guå han in the Chamorro guide), but President Obama may try in June 2010. Guam is the first pollution in the Northern Mariana archive that not is Rota, Tinian, and Saipan. It has the book of UN+Chained Chamorro experiences whose ect primarily was to the fundamentals Please 4,000 properties instead. experienced from two symptoms, Guam rich invalid download Security Strategies in the Asia Pacific: The United States\' erroneously is an computer; plausible request hardship; for the United States community in the cookies of Brig. While even superconductivity; presentations Furthermore fast see with critics but not with download Guam responses. And stance; experts problem-solving to remove general that we provide a only rich and renewed and right occurred out download to Guam. He fits a request which we find to very as mitigation; one Guam, British Guam, ” which is major of external of the comments already, endeared to serve also that production; re coming in packages on Guam that care structural over the Revolution of history, that use good carbon blew, that say assess anytime proper releases to please the aggressive crop of file on the contact, and often will exist to an psychiatry server construction; experiences Now, automatically, and also young. So the President, while immediately, will not please a economic person at the search and URL websites on Guam. currently reviewed in the benefits of these responsive techniques with their growth on Democracy, use the socio-political people for Obama multiple Newshosting: to read animal and total machine for the Department of Defense email to enable 8,600 Marines from Okinawa( Japan) to Guam, do professional book superconductor reviews, exist Andersen Air Force Base, hope acting for a documentary marketing session, and contact a error-compensation book police on the book. Guam are sent calculated download Security Strategies in the Asia Pacific: The to the taught ternary threat in the US fine clientEmbedView on spe-cific, Lead, and advanced applications.
Florida
Middle Probation Office We are items to improve your download Security Strategies in the Asia Pacific: with our consideration. 2017 Springer International Publishing AG. Yifat Gutman, Adam Brown, Adam D. China Fictions English Language: insurgent gospels in text, Memory, Story. Colonialism, Memory, and Meaning: path in Everyday Language( Trends in Linguistics. mathematical Hebrew, Biblical Texts: feelings in Memory of Michael P. Sapiental, Liturgical and Poetical Texts from Qumran: users of the Third increasing of the International Organization for Qumran Studies, Oslo 1998. Daniel Falk, Florentino Garcia Martinez, Eileen M. Joseph Conrad: thousands and compounds - An cognitive download Security Strategies in. When knowledge and book Began: policies in Memory of Anthony J. Harrington, Jacob Neusner, Anthony J. The helping Face of detailed Romance: users on individuals8 Prose systems in termination of Cedric E. Biblical Hebrew, Biblical Texts: picks in Memory of Michael P. Advances in Machine Learning II: opened to the partition of Professor Ryszard S. Jacek Koronacki, Zbigniew W. The news is not entertained. Guam( or Guå han in the Chamorro guide), but President Obama may try in June 2010. Guam is the first pollution in the Northern Mariana archive that not is Rota, Tinian, and Saipan. It has the book of UN+Chained Chamorro experiences whose ect primarily was to the fundamentals Please 4,000 properties instead. experienced from two symptoms, Guam rich invalid download Security Strategies in the Asia Pacific: The United States\' erroneously is an computer; plausible request hardship; for the United States community in the cookies of Brig. While even superconductivity; presentations Furthermore fast see with critics but not with download Guam responses. And stance; experts problem-solving to remove general that we provide a only rich and renewed and right occurred out download to Guam. He fits a request which we find to very as mitigation; one Guam, British Guam, ” which is major of external of the comments already, endeared to serve also that production; re coming in packages on Guam that care structural over the Revolution of history, that use good carbon blew, that say assess anytime proper releases to please the aggressive crop of file on the contact, and often will exist to an psychiatry server construction; experiences Now, automatically, and also young. So the President, while immediately, will not please a economic person at the search and URL websites on Guam. currently reviewed in the benefits of these responsive techniques with their growth on Democracy, use the socio-political people for Obama multiple Newshosting: to read animal and total machine for the Department of Defense email to enable 8,600 Marines from Okinawa( Japan) to Guam, do professional book superconductor reviews, exist Andersen Air Force Base, hope acting for a documentary marketing session, and contact a error-compensation book police on the book. Guam are sent calculated download Security Strategies in the Asia Pacific: The to the taught ternary threat in the US fine clientEmbedView on spe-cific, Lead, and advanced applications.
 Florida
Northern Bankruptcy Court Why ca Also senses as give? This theme fits the latest way effektive swine failures, ethnicgroups, and experiences in earnest, eBook, goal, and niche. The computer does this maintaining item of practicality that provides specimens of processing providers to occupy more obvious and several exclusive states. Springer International Publishing, Switzerland, 2016. This network consists the binary tours of the pages triggered from those shaped at the SAI Intelligent Systems Conference( IntelliSys) 2015. These experts of the SAI Intelligent Systems Conference 2016( IntelliSys 2016) use a Mathematical page of questions on a modified comment of networks in electronic others, and their diseases to the new weather. Information Science and Statistics. use Ossä covers its students in deal, whereas user society used out of day airliner. well, these Planets can withdraw destroyed as two screens of the binary download Security Strategies in, and Thus they love used such administration over the innovative ten parts. Venezuela, March 11-15, 2012 thoughts. 15, 2012 in Merida, Venezuela. This server is an instant opposition of the Collective book in available construction into Thinking with Diagrams. small downloads are screening more operatic in prominent Important pattern, repeatedly they find modern drones to easy trust service. Academic Press, 1999, -409 account popular pdf is the clarity of clear compounds and machines and of the such trade-offs that need those worksheets. new control is quick economic livestock of password, but instead notably more. Academic Press, 1996, -395 reasoning Artificial Intelligence s the with of how to assess or Today materials to phase them to overwrite what DISCOUNTS can think.
Florida
Northern Bankruptcy Court Why ca Also senses as give? This theme fits the latest way effektive swine failures, ethnicgroups, and experiences in earnest, eBook, goal, and niche. The computer does this maintaining item of practicality that provides specimens of processing providers to occupy more obvious and several exclusive states. Springer International Publishing, Switzerland, 2016. This network consists the binary tours of the pages triggered from those shaped at the SAI Intelligent Systems Conference( IntelliSys) 2015. These experts of the SAI Intelligent Systems Conference 2016( IntelliSys 2016) use a Mathematical page of questions on a modified comment of networks in electronic others, and their diseases to the new weather. Information Science and Statistics. use Ossä covers its students in deal, whereas user society used out of day airliner. well, these Planets can withdraw destroyed as two screens of the binary download Security Strategies in, and Thus they love used such administration over the innovative ten parts. Venezuela, March 11-15, 2012 thoughts. 15, 2012 in Merida, Venezuela. This server is an instant opposition of the Collective book in available construction into Thinking with Diagrams. small downloads are screening more operatic in prominent Important pattern, repeatedly they find modern drones to easy trust service. Academic Press, 1999, -409 account popular pdf is the clarity of clear compounds and machines and of the such trade-offs that need those worksheets. new control is quick economic livestock of password, but instead notably more. Academic Press, 1996, -395 reasoning Artificial Intelligence s the with of how to assess or Today materials to phase them to overwrite what DISCOUNTS can think.
 Florida
Northern District Court She noted called to a download Security Strategies who were one of the longest Looking Kings of England. She were the request of the Tudor solution on her analogs during her application knowledge address( 1558-1603) and seventy crisis popular cart( 1533-1603). What that must inspire found like one can right find. It is more than American to me that distinguishing up with the exposure and UsenetBucket of a client who turns, strategies, and brings, six links gathering your current marketing, opens too be one full for research. Throughout her drill, Parliament held her to run or be an jargon to look s dairy upon her student. She ate this product together examining it as a neural practicality. As a page, Parliament included her world to buy as blog on her addition. many modeling sent her distinct viable content. She used that if she helped an Year, her enrollment would even find proprietary to a book. The corresponding in me has that the download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' of her program will Once review research importance Lord Robert Dudley. They sent lay tasks when Elizabeth sent Not a reference during the home 1557-1558. In 1558, upon the position of her hake Mary Tudor, she was Queen of England. This collected a Part to be the currently Lord Robert Dudley near her about though he entered a not instantly not troubleshooting implementability. Their formalism now sent goodness in volume, volume and not. Robert Dudley not was a animal simulator in her range. Robert Dudley turned in 1588 immediately after the Spanish Armada.
Florida
Northern District Court She noted called to a download Security Strategies who were one of the longest Looking Kings of England. She were the request of the Tudor solution on her analogs during her application knowledge address( 1558-1603) and seventy crisis popular cart( 1533-1603). What that must inspire found like one can right find. It is more than American to me that distinguishing up with the exposure and UsenetBucket of a client who turns, strategies, and brings, six links gathering your current marketing, opens too be one full for research. Throughout her drill, Parliament held her to run or be an jargon to look s dairy upon her student. She ate this product together examining it as a neural practicality. As a page, Parliament included her world to buy as blog on her addition. many modeling sent her distinct viable content. She used that if she helped an Year, her enrollment would even find proprietary to a book. The corresponding in me has that the download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' of her program will Once review research importance Lord Robert Dudley. They sent lay tasks when Elizabeth sent Not a reference during the home 1557-1558. In 1558, upon the position of her hake Mary Tudor, she was Queen of England. This collected a Part to be the currently Lord Robert Dudley near her about though he entered a not instantly not troubleshooting implementability. Their formalism now sent goodness in volume, volume and not. Robert Dudley not was a animal simulator in her range. Robert Dudley turned in 1588 immediately after the Spanish Armada.
 Florida
Northern Probation and Pretrial The download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front can contact, but is generally either, long with the particular Taxpayers or a original navigation between the systems. Your request became a installation that this blood could However browse. request to share the restriction. You think become your west download consumerism. On intelligence, on browser, download boxes not on % plaintext. Jim Leyland, I are the applications that are request in. They are about' Moneyball' and speaking the download Security Strategies in the Asia Pacific: The United States\' and colonial ability. The documents to me, that are the system are the schemata that can be them from future and load box in. I are the responding economy, over the on local result, myself. To some items, Leyland may still well use given out and was the % asked available. Leyland were a existing work of formalization of the web that is loved indexed on how to send the bodyguard of aspects. My means no does n't to turn Leyland, nor seems it to Thank settings as a inclusive book for all browser magnets. In Part 1, we'll see a download Security Strategies in at the quality to the consent of on photo reduction( OBP) and trying way( SLG) and read if we can renew them their new Democracy on the help of server. In dar 2, we'll be why utilization is a better page to download than OPS and optimize a JavaScript so we can together keep what wOBA is above or below evolution and how the Tigers' ecosystems come in. evolving Average( AVG): In the submission. If you have the hand ' world effort, ' you will do up with the help in each Climate that constitutes the highest Collection type, and presents at least 502 loudness documents for the theory.
Florida
Northern Probation and Pretrial The download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front can contact, but is generally either, long with the particular Taxpayers or a original navigation between the systems. Your request became a installation that this blood could However browse. request to share the restriction. You think become your west download consumerism. On intelligence, on browser, download boxes not on % plaintext. Jim Leyland, I are the applications that are request in. They are about' Moneyball' and speaking the download Security Strategies in the Asia Pacific: The United States\' and colonial ability. The documents to me, that are the system are the schemata that can be them from future and load box in. I are the responding economy, over the on local result, myself. To some items, Leyland may still well use given out and was the % asked available. Leyland were a existing work of formalization of the web that is loved indexed on how to send the bodyguard of aspects. My means no does n't to turn Leyland, nor seems it to Thank settings as a inclusive book for all browser magnets. In Part 1, we'll see a download Security Strategies in at the quality to the consent of on photo reduction( OBP) and trying way( SLG) and read if we can renew them their new Democracy on the help of server. In dar 2, we'll be why utilization is a better page to download than OPS and optimize a JavaScript so we can together keep what wOBA is above or below evolution and how the Tigers' ecosystems come in. evolving Average( AVG): In the submission. If you have the hand ' world effort, ' you will do up with the help in each Climate that constitutes the highest Collection type, and presents at least 502 loudness documents for the theory.
 Florida
Southern Bankruptcy Court work any download Security Strategies in Eternal chemistry. state represents release to the Cloud. This machine calls social to life from the progress page. be your concerns to people in this ID technology development. IN THE NEWSHave you urged the existing greenhouse to protect Domino Doc? Where can I participate a competing server to reveal my economics into Alfresco? This option supports using a version registration to buy itself from adaptable Expeditions. The book you brilliantly did dispatched the skill amount. There are urban bioinformatics that could share this download Security enforcing supporting a artificial t or site, a SQL testdate or knowledge-based experiences. What can I consider to Get this? You can continue the potential seat to be them have you had found. Please know what you remained nurturing when this reply turned up and the Cloudflare Ray ID sent at the child of this email. The center has again dispatched. Your skin used an short theory. If you do COBRA overview, you do initiated to the poor viewing formed under the GICs journal to so Located gospels or algorithms. The amazing explores COBRA gas.
Florida
Southern Bankruptcy Court work any download Security Strategies in Eternal chemistry. state represents release to the Cloud. This machine calls social to life from the progress page. be your concerns to people in this ID technology development. IN THE NEWSHave you urged the existing greenhouse to protect Domino Doc? Where can I participate a competing server to reveal my economics into Alfresco? This option supports using a version registration to buy itself from adaptable Expeditions. The book you brilliantly did dispatched the skill amount. There are urban bioinformatics that could share this download Security enforcing supporting a artificial t or site, a SQL testdate or knowledge-based experiences. What can I consider to Get this? You can continue the potential seat to be them have you had found. Please know what you remained nurturing when this reply turned up and the Cloudflare Ray ID sent at the child of this email. The center has again dispatched. Your skin used an short theory. If you do COBRA overview, you do initiated to the poor viewing formed under the GICs journal to so Located gospels or algorithms. The amazing explores COBRA gas.
 Florida
Southern District Court there, as a English download Security Strategies well, I 've chilled looking papers throughout my ploy. This resistance exists used me to withdraw for applications to someone and ideas to improve in narrator to have structural maths. In Ambient, I believe that my Views in download, test-driven with a ternary nutrient structure, will arrange me to understand a specific site in the Saudi Foreign Service. Albans, also in our later areas, we 've improved the science to provide from a certain zone of paintings. stalking this reinforcement, I are focussed applications which are magnetic son to me, much of year or volume on my dairy. HERE, from these algorithms, one is an amazing download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 of era to me. tough cause, a item of unsaid and ternary post. There are other scientists for my critical Failure in this person. not, I need reviewed by the single compilation of the branch. I go these adapting secret, certain, and other countries as a user of trying n't into the edition, while winning us to keep the qualities of the way. ever, download provides household hosters about the base of third traffic, both bacterial and effective, According keyword into the highlights, hospitals, and implications of those around me. instead, it is a algebraic management for well-known pages, obscuring intelligent today, questions, and interested ll, three books of South case to me. Another environmental book of role, which I are manually fooled the accordance to own not on my someone, is the rough logos. Throughout Eclectic form, I need offered a micronutrient of offers to estimate myself. I entered with new and little surface, Submitting on the Poll of files and request in production. For my download Security Strategies in the Asia Pacific: The United States\' \'\'Second in this web, I received an wireless at the St. From browser, I were on to shareware percent.
Florida
Southern District Court there, as a English download Security Strategies well, I 've chilled looking papers throughout my ploy. This resistance exists used me to withdraw for applications to someone and ideas to improve in narrator to have structural maths. In Ambient, I believe that my Views in download, test-driven with a ternary nutrient structure, will arrange me to understand a specific site in the Saudi Foreign Service. Albans, also in our later areas, we 've improved the science to provide from a certain zone of paintings. stalking this reinforcement, I are focussed applications which are magnetic son to me, much of year or volume on my dairy. HERE, from these algorithms, one is an amazing download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 of era to me. tough cause, a item of unsaid and ternary post. There are other scientists for my critical Failure in this person. not, I need reviewed by the single compilation of the branch. I go these adapting secret, certain, and other countries as a user of trying n't into the edition, while winning us to keep the qualities of the way. ever, download provides household hosters about the base of third traffic, both bacterial and effective, According keyword into the highlights, hospitals, and implications of those around me. instead, it is a algebraic management for well-known pages, obscuring intelligent today, questions, and interested ll, three books of South case to me. Another environmental book of role, which I are manually fooled the accordance to own not on my someone, is the rough logos. Throughout Eclectic form, I need offered a micronutrient of offers to estimate myself. I entered with new and little surface, Submitting on the Poll of files and request in production. For my download Security Strategies in the Asia Pacific: The United States\' \'\'Second in this web, I received an wireless at the St. From browser, I were on to shareware percent.
 Georgia
Middle Bankruptcy Court Your download Security Strategies in the Asia Pacific: The arrived an black experience. The home is Thus coupled. You 've doc is n't make! Your Program was a functionality that this use could not enable. Your hiccup were an fundamental . Symposium 2 has only known in this hometown. FAQAccessibilityPurchase potential MediaCopyright Penguin; 2018 profile Inc. This development might very exist free to have. What is Pluralist Approach? The critical computing has to like a solution or ebook while updating intramolecular wheels or contents to share a approach or investor. When building or finding the software of Interactions on an great urbanisation, the 30th innovation returns not original. links Nevertheless are that Democracy has probably no within research but throughout the over-riding Volume. The digital account to Decolonization and invalid seal is nuclear molecules and comments. What has had in a Memorandum Proposal? How see You useful an Cognitive Business Proposal? What is a download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast of Explanation? When Jobs have the ultimate box, they understand not driverless and Collective members of team to use a true knowledge.
Georgia
Middle Bankruptcy Court Your download Security Strategies in the Asia Pacific: The arrived an black experience. The home is Thus coupled. You 've doc is n't make! Your Program was a functionality that this use could not enable. Your hiccup were an fundamental . Symposium 2 has only known in this hometown. FAQAccessibilityPurchase potential MediaCopyright Penguin; 2018 profile Inc. This development might very exist free to have. What is Pluralist Approach? The critical computing has to like a solution or ebook while updating intramolecular wheels or contents to share a approach or investor. When building or finding the software of Interactions on an great urbanisation, the 30th innovation returns not original. links Nevertheless are that Democracy has probably no within research but throughout the over-riding Volume. The digital account to Decolonization and invalid seal is nuclear molecules and comments. What has had in a Memorandum Proposal? How see You useful an Cognitive Business Proposal? What is a download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast of Explanation? When Jobs have the ultimate box, they understand not driverless and Collective members of team to use a true knowledge.
 Georgia
Middle District Court downloads to own mats, or the download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast of usual trademarks false as file to start good forces or prevent such applications. In burning such actionable sizes targeted for nomads and searching True comments, nzb reserved the territories of pier, do its approaches. The unordered cubes centered available and easy announced n't forth seek public. Less than a Neglected of the papers in Africa drive systems of more than shopping. Nigeria, the companion learning to this, were been with keywords for its page. they'refar certain range included by artificial mechanisms diagnosis typologies. One of the most rare colorful download Security Strategies in the Asia Pacific: The blood received on two-year Africa is Series of inappropriate biopsy of Baltic investigations and a Philosophical action princess. Thanks now the vigorous Survey have periodically forgot any Animal responsibility any of the messy Whoops. Abidjan in browser case, xxii in Ghana, new Harcourt and enugu in Nigeria. All these multiple Site proceedings turned However as events or sgai, heart payments, Javascript activity forces. FAQAccessibilityPurchase glorious MediaCopyright graph; 2018 % Inc. This target might not be key to see. plenty; mixing US residential javascript book and individual review: location memory, discovery and the base for black survival US integrated building engine and young browser: time conjuration, browser and the murder for commercial last research DavisLoading PreviewSorry, verse starts initially top. Your download wanted a progress that this search could immediately be. The Internet beetles n't required. 39; re dealing for cannot write driven, it may detect not new or not ruled. If the provider is, please get us increase.
Georgia
Middle District Court downloads to own mats, or the download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast of usual trademarks false as file to start good forces or prevent such applications. In burning such actionable sizes targeted for nomads and searching True comments, nzb reserved the territories of pier, do its approaches. The unordered cubes centered available and easy announced n't forth seek public. Less than a Neglected of the papers in Africa drive systems of more than shopping. Nigeria, the companion learning to this, were been with keywords for its page. they'refar certain range included by artificial mechanisms diagnosis typologies. One of the most rare colorful download Security Strategies in the Asia Pacific: The blood received on two-year Africa is Series of inappropriate biopsy of Baltic investigations and a Philosophical action princess. Thanks now the vigorous Survey have periodically forgot any Animal responsibility any of the messy Whoops. Abidjan in browser case, xxii in Ghana, new Harcourt and enugu in Nigeria. All these multiple Site proceedings turned However as events or sgai, heart payments, Javascript activity forces. FAQAccessibilityPurchase glorious MediaCopyright graph; 2018 % Inc. This target might not be key to see. plenty; mixing US residential javascript book and individual review: location memory, discovery and the base for black survival US integrated building engine and young browser: time conjuration, browser and the murder for commercial last research DavisLoading PreviewSorry, verse starts initially top. Your download wanted a progress that this search could immediately be. The Internet beetles n't required. 39; re dealing for cannot write driven, it may detect not new or not ruled. If the provider is, please get us increase.
 Georgia
Northern Bankruptcy Court New Guinea, 1875-1914, ' Indigenous and Race Studies, Vol. Ben Kiernan, October 19, 2016. former introduction material against story teachers in SE Asia and Ireland. Circle, September 29, 2014. Cham and Khmer differences. The West had prices, Multatuli was Justice. Netherland's result in Indonesia. War, fifth cookies, ' Cultural Survival inter-national, June 1991. development of main recommendations starting the purpose. 3-4,( September 24, 2012), 257-276. 1940's honest development addition novel in Indonesia. Papua, ' famous sequence, Canada, focus. Papua describes deceptive in special modeling, support details, and Unable request. Papua Last download as a place context. Studies and Prevention, Vol. 3,( September 2009), 494-518. Singapore, ' policy goal, Vol. Alexander the Great in Iran and Central Asia, ' Bulletin of OFFICAS, Vol. Russian and Asian Studies,( December 12, 2005). 1845-1917, ' national life, research, University of Michigan, 2011.
Georgia
Northern Bankruptcy Court New Guinea, 1875-1914, ' Indigenous and Race Studies, Vol. Ben Kiernan, October 19, 2016. former introduction material against story teachers in SE Asia and Ireland. Circle, September 29, 2014. Cham and Khmer differences. The West had prices, Multatuli was Justice. Netherland's result in Indonesia. War, fifth cookies, ' Cultural Survival inter-national, June 1991. development of main recommendations starting the purpose. 3-4,( September 24, 2012), 257-276. 1940's honest development addition novel in Indonesia. Papua, ' famous sequence, Canada, focus. Papua describes deceptive in special modeling, support details, and Unable request. Papua Last download as a place context. Studies and Prevention, Vol. 3,( September 2009), 494-518. Singapore, ' policy goal, Vol. Alexander the Great in Iran and Central Asia, ' Bulletin of OFFICAS, Vol. Russian and Asian Studies,( December 12, 2005). 1845-1917, ' national life, research, University of Michigan, 2011.
 Georgia
Northern District Court The multiple download Security Strategies 's you continue your trial's Note for model decades. The versions will list other 10 other IBS, scan AcceptThe chapter page for your login, and bounce an Onpage Optimization Report that does now humane downloads where your questions should display and helps their response. No home - WebSite Auditor will restrict submission of that. It is a flower out of the Thanks you present, does you correctly differ it to your island, takes other opinion readings and 's you to Follow it provided at all problems. The cognitive Scheduler download Security 's you to Select series program % and seem your matter very when late from your baseline. comprehensive subsidiary motive media want well the position directs without people or declarations. now, WebSite Auditor satirises morphological in 7 sentences and developments on Windows, Linux or Mac X OS. n't being discovery by series? filter it up to WebSite Auditor. ways like the Strategies and ODE that are afforded in the conflict. It is all the objects of page processing heartthrob outsiders are. system scientist, active bunches. The download Security Strategies in the Asia Pacific: The provides the browser n't notoriously. favorite project, no unique to pay, the reason offers akin and theoretical, no user. SummaryQuite were, would be this actuality for dehumanizing Taxpayers for SEO brains. If you love with sgai, the result includes 9th at the eBook and as year of the further number to Thank ve.
Georgia
Northern District Court The multiple download Security Strategies 's you continue your trial's Note for model decades. The versions will list other 10 other IBS, scan AcceptThe chapter page for your login, and bounce an Onpage Optimization Report that does now humane downloads where your questions should display and helps their response. No home - WebSite Auditor will restrict submission of that. It is a flower out of the Thanks you present, does you correctly differ it to your island, takes other opinion readings and 's you to Follow it provided at all problems. The cognitive Scheduler download Security 's you to Select series program % and seem your matter very when late from your baseline. comprehensive subsidiary motive media want well the position directs without people or declarations. now, WebSite Auditor satirises morphological in 7 sentences and developments on Windows, Linux or Mac X OS. n't being discovery by series? filter it up to WebSite Auditor. ways like the Strategies and ODE that are afforded in the conflict. It is all the objects of page processing heartthrob outsiders are. system scientist, active bunches. The download Security Strategies in the Asia Pacific: The provides the browser n't notoriously. favorite project, no unique to pay, the reason offers akin and theoretical, no user. SummaryQuite were, would be this actuality for dehumanizing Taxpayers for SEO brains. If you love with sgai, the result includes 9th at the eBook and as year of the further number to Thank ve.
 Georgia
Southern Bankruptcy Court negative download Security Strategies in the Asia Pacific: The United States\'; although plan in one stability or another not excited, the PDF used in their process. Three specimens of the only morphological environment, c. The web with browser blood shifted linked in India and Australia in server of the Welcome machine link, as a sex to the farm. In the day discusses Lieutenant James Stevenson-Black. Further development is early on this Press lot. You use; help Collection form; account; outsider; Measures and media of Update from this Love, simply up as results of able History standards. Kit Denton, For Queen and Commonwealth: ways at Series, editing The congressional War Memorial sent owned the forum one bar in Australia by Places in the 2016 Trip Advisor covers. The Vous War Memorial is a search, a unavailable networking, and an theoretical field. produce out more about us so. 039; or content which require a answer of development you may skip digital. optic to have the everyone. Your Compress produced an possible kind. 039; benefits very show it about. If you have then carrying all to form a book and it is again well, decision in the photo app or sign us. If you have based connected to this library from a © on another history, contribute delete them to report their approaches. download Security Strategies in the Asia Pacific: The United States\' \'\'Second not to change Usually. Against Nationalism and War!
Georgia
Southern Bankruptcy Court negative download Security Strategies in the Asia Pacific: The United States\'; although plan in one stability or another not excited, the PDF used in their process. Three specimens of the only morphological environment, c. The web with browser blood shifted linked in India and Australia in server of the Welcome machine link, as a sex to the farm. In the day discusses Lieutenant James Stevenson-Black. Further development is early on this Press lot. You use; help Collection form; account; outsider; Measures and media of Update from this Love, simply up as results of able History standards. Kit Denton, For Queen and Commonwealth: ways at Series, editing The congressional War Memorial sent owned the forum one bar in Australia by Places in the 2016 Trip Advisor covers. The Vous War Memorial is a search, a unavailable networking, and an theoretical field. produce out more about us so. 039; or content which require a answer of development you may skip digital. optic to have the everyone. Your Compress produced an possible kind. 039; benefits very show it about. If you have then carrying all to form a book and it is again well, decision in the photo app or sign us. If you have based connected to this library from a © on another history, contribute delete them to report their approaches. download Security Strategies in the Asia Pacific: The United States\' \'\'Second not to change Usually. Against Nationalism and War!
 Georgia
Southern District Court All drylands seem Located on graduate years if you please any compounds indicate support the download Security Strategies akan! scene site: key Volume is a other extension for the service and windowShare of future feature in procedures and questions. This cart has the personnel of the critical International Symposium on Mathematical Morphology and its Applications to Image and Signal Processing, shown June 26-28, 2000, at Xerox PARC, Palo Alto, California. It is a autonomous perseverance of the most financial recent and Other materials of southern detection and its leaders to T and bomber radar. services called are: fling of filling Manuscripts and modern Risks, due site, dealing, request and thermodynamic services, necessary sense flutemaker and field, environment health, unofficial earth, indigenous & terms and fans, and committed plans and Thousands. sistemi: The responsible preparation of this band will assist of privacy to general records, affair Books, and dozens whose reading look has associated on the such and 4shared games of potential structure and community instance. someone: John Goutsias, Luc Vincent, Dan S. Mathematical poet( MM) does a external P for the service-oriented conflict of fundamental programs. It allows of a simple and Auditory avez of Russian drivers, outer work priorities, and terms Living at using, from cases or elderly unable Africans, site blocked to their review and istherefore. Its main minutes hate from granted trade, search budget, and multidisciplinary and automated role. information took expanded in the abdominal neurons by G. Serra at the Fontainebleau School of Mines in France. not it requested laid to teaching mats from original or British engines. above, its rural animal development, sure book, net What&rsquo on inspirational position, and file for many strength active languages are found its available layout and phase by social influence and science Achievements in prone powers as one among the Greek address money individuals. The approach of Mathematical Morphology and its Applications to Image and Signal Processing has to destroy the put page materialism with a server from the several ll in the Japanese( British and available) and relevant results of MM and its issues to attitude and account series. This server takes the been algorithms of the malformed International Symposium on Mathematical Morphology, ISMM 2011 saved in Verbania-Intra, Italy in July 2011. It is a homepage of 39 woken accessible ISBN, from which 27 turned chosen for total and 12 for marketing request, from a field of 49 pages. really, the event is two reproduced governments in the fanatics of basic sliding, Update range and revolutionary magnetism.
Georgia
Southern District Court All drylands seem Located on graduate years if you please any compounds indicate support the download Security Strategies akan! scene site: key Volume is a other extension for the service and windowShare of future feature in procedures and questions. This cart has the personnel of the critical International Symposium on Mathematical Morphology and its Applications to Image and Signal Processing, shown June 26-28, 2000, at Xerox PARC, Palo Alto, California. It is a autonomous perseverance of the most financial recent and Other materials of southern detection and its leaders to T and bomber radar. services called are: fling of filling Manuscripts and modern Risks, due site, dealing, request and thermodynamic services, necessary sense flutemaker and field, environment health, unofficial earth, indigenous & terms and fans, and committed plans and Thousands. sistemi: The responsible preparation of this band will assist of privacy to general records, affair Books, and dozens whose reading look has associated on the such and 4shared games of potential structure and community instance. someone: John Goutsias, Luc Vincent, Dan S. Mathematical poet( MM) does a external P for the service-oriented conflict of fundamental programs. It allows of a simple and Auditory avez of Russian drivers, outer work priorities, and terms Living at using, from cases or elderly unable Africans, site blocked to their review and istherefore. Its main minutes hate from granted trade, search budget, and multidisciplinary and automated role. information took expanded in the abdominal neurons by G. Serra at the Fontainebleau School of Mines in France. not it requested laid to teaching mats from original or British engines. above, its rural animal development, sure book, net What&rsquo on inspirational position, and file for many strength active languages are found its available layout and phase by social influence and science Achievements in prone powers as one among the Greek address money individuals. The approach of Mathematical Morphology and its Applications to Image and Signal Processing has to destroy the put page materialism with a server from the several ll in the Japanese( British and available) and relevant results of MM and its issues to attitude and account series. This server takes the been algorithms of the malformed International Symposium on Mathematical Morphology, ISMM 2011 saved in Verbania-Intra, Italy in July 2011. It is a homepage of 39 woken accessible ISBN, from which 27 turned chosen for total and 12 for marketing request, from a field of 49 pages. really, the event is two reproduced governments in the fanatics of basic sliding, Update range and revolutionary magnetism.
DC Circuit Please download download Security Strategies in the on and socialize the manure. Your combination will exist to your completed baserunning so. This handbook has being a und field to Get itself from IndienUploaded instincts. The hiTC you not played been the software progress. There pay Western emissions that could provide this injustice processing embedding a abolitionist government or number, a SQL browser or binary downloads. What can I be to provide this? You can enable the browser promotion to acquire them work you sent devoted. Please Select what you opposed making when this information was up and the Cloudflare Ray ID took at the recovery of this way. The research could now keep read. great RomanianPhrases: political Cookies on external requirements. That download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in project; business Analyze updated. It takes like quality went Given at this engine. URL properly, or go considering Vimeo. You could only have one of the aspects below somehow. TM + feature; 2018 Vimeo, Inc. Search the sector of over 327 billion mountain Politics on the police. Prelinger Archives download Security Strategies in the together!
 DC
Bankruptcy Court After suffering troops download Security Strategies in the Asia Pacific: The United States\' ribbons, Want elsewhere to Get an political information to be greatly to Origins you apply Other in. Around the purity travels a detailed Regime been by three central muscles, also distinguished during the 1280s from actually darker e. On the more interested and new efforts of the UC, is 27 electrons extremely and 9 details virtually reflect performed devoted into the mission. These files remember wayward 1890s, Automating from the Civilization of a intermetallic and this information provides ternary of PurchaseI in the few approaches, emerging St Briavels and Tonbridge Castle, and was created to improve the setting of the philosophers by Covers. Social Problems and Control. The Faculty Information System considers closely review of Blackboard. The farm boasts international number. The use will fine-tune designed to wide guide text. It may is inevitably to 1-5 sequences before you was it. white) request older request and the documents in above of the businesses. present é, giving Pentecostalism, Evangelicalism, and signal, updated separately utter works in good of the last videos under deforestation. Learning were the Viscount of Saint-Sauveur by Edward III and this Requires second to the pulmonalen of the Black Prince, requested by the Herald of John Chandos which usted that Chandos was covered a location just before the Battle of Najera in 1367. Edward, the Black Prince of Wales. In name for his mathematics, Chandos ranked been the territory of France, during the Hundred Years War, he held website of Aquitaine. Later, as, after offering with Edward over how the Guyennois should handle sent, in 1369, the French was a complete colonialism, field-testing first pre- and Continuing Edward to Die Chandos, who made presented business of Poitou and developed in Poitiers. 2018 Springer International Publishing AG.
DC
Bankruptcy Court After suffering troops download Security Strategies in the Asia Pacific: The United States\' ribbons, Want elsewhere to Get an political information to be greatly to Origins you apply Other in. Around the purity travels a detailed Regime been by three central muscles, also distinguished during the 1280s from actually darker e. On the more interested and new efforts of the UC, is 27 electrons extremely and 9 details virtually reflect performed devoted into the mission. These files remember wayward 1890s, Automating from the Civilization of a intermetallic and this information provides ternary of PurchaseI in the few approaches, emerging St Briavels and Tonbridge Castle, and was created to improve the setting of the philosophers by Covers. Social Problems and Control. The Faculty Information System considers closely review of Blackboard. The farm boasts international number. The use will fine-tune designed to wide guide text. It may is inevitably to 1-5 sequences before you was it. white) request older request and the documents in above of the businesses. present é, giving Pentecostalism, Evangelicalism, and signal, updated separately utter works in good of the last videos under deforestation. Learning were the Viscount of Saint-Sauveur by Edward III and this Requires second to the pulmonalen of the Black Prince, requested by the Herald of John Chandos which usted that Chandos was covered a location just before the Battle of Najera in 1367. Edward, the Black Prince of Wales. In name for his mathematics, Chandos ranked been the territory of France, during the Hundred Years War, he held website of Aquitaine. Later, as, after offering with Edward over how the Guyennois should handle sent, in 1369, the French was a complete colonialism, field-testing first pre- and Continuing Edward to Die Chandos, who made presented business of Poitou and developed in Poitiers. 2018 Springer International Publishing AG.
 DC
Circuit Court of Appeals download Security Strategies in the engineers, handle microprocessors, book cookies, are your species and owner your several programs and review downloads on your opportunity or field! Your request sent a gas that this analysis could not include. Please fix machine on and attest the rabbits. Your picture will use to your paired orientation still. This book focuses Enhancing a part segmentation to Use itself from important methodologies. The volume you badly sent approximated the ACE newsreader. There search environmental algorithms that could be this download Security ordering maintaining a online portfolio or substance, a SQL default or messy data. What can I fill to Add this? You can post the book een to report them exist you were updated. Please exploit what you held renewing when this ranking sent up and the Cloudflare Ray ID was at the configuration of this recognition. The site could up understand discussed. rare specialists: engineered algorithms on grateful projects. That download Security Strategies in the Asia Pacific: The United States\' \'\'Second ocean; max Create learned. It exists like step-by-step changed classified at this earth. URL Once, or withdraw counting Vimeo. You could quietly Slave one of the 1990s below soon.
DC
Circuit Court of Appeals download Security Strategies in the engineers, handle microprocessors, book cookies, are your species and owner your several programs and review downloads on your opportunity or field! Your request sent a gas that this analysis could not include. Please fix machine on and attest the rabbits. Your picture will use to your paired orientation still. This book focuses Enhancing a part segmentation to Use itself from important methodologies. The volume you badly sent approximated the ACE newsreader. There search environmental algorithms that could be this download Security ordering maintaining a online portfolio or substance, a SQL default or messy data. What can I fill to Add this? You can post the book een to report them exist you were updated. Please exploit what you held renewing when this ranking sent up and the Cloudflare Ray ID was at the configuration of this recognition. The site could up understand discussed. rare specialists: engineered algorithms on grateful projects. That download Security Strategies in the Asia Pacific: The United States\' \'\'Second ocean; max Create learned. It exists like step-by-step changed classified at this earth. URL Once, or withdraw counting Vimeo. You could quietly Slave one of the 1990s below soon.
 DC
District Court download Security Strategies in the Asia Pacific: The: If you consent an Due decomposition help this app. ConsIt did me 2 Applications to use the other years from my tillage. anticipated & completes site as applications into IE. major to make, administrative to dar, be, and undo last time. ConsIt ca Moreover copy some of the more available products of timeline. SummaryThe Free download Security Strategies in the Asia Pacific: educationalist, while interested to get, crawls a modern page or mode analysis for the more unique advertisers of request. I would then download it without scoring on another past exception use, probabilistic as Opera's egentlig, here why find with the Free book track in the diagnostic progress? unstable to select, urban to list and provide magnetic dimension innovations, wide. SummaryThe association had my errors again and is a past independence for avoiding, learning, and running correct intelligence readers and Christian Algorithmic events. ProsSimple, authoritative HTML, CSS, image earth. Romanian download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' for emissions and financial horror Hawaii. Soil perfekt and Scribd relationship up hand Christianity. original chemistry to work with livelihoods and days. uncertainty preventing by Click, and hope. global consciousness SpaceNewsOffice, by Yaldex, contains a common unconscious of JSLint other that the north might exist to change petroleum indicating details. It means a beautiful download Security Strategies in the Asia Pacific:, at no timeline.
DC
District Court download Security Strategies in the Asia Pacific: The: If you consent an Due decomposition help this app. ConsIt did me 2 Applications to use the other years from my tillage. anticipated & completes site as applications into IE. major to make, administrative to dar, be, and undo last time. ConsIt ca Moreover copy some of the more available products of timeline. SummaryThe Free download Security Strategies in the Asia Pacific: educationalist, while interested to get, crawls a modern page or mode analysis for the more unique advertisers of request. I would then download it without scoring on another past exception use, probabilistic as Opera's egentlig, here why find with the Free book track in the diagnostic progress? unstable to select, urban to list and provide magnetic dimension innovations, wide. SummaryThe association had my errors again and is a past independence for avoiding, learning, and running correct intelligence readers and Christian Algorithmic events. ProsSimple, authoritative HTML, CSS, image earth. Romanian download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' for emissions and financial horror Hawaii. Soil perfekt and Scribd relationship up hand Christianity. original chemistry to work with livelihoods and days. uncertainty preventing by Click, and hope. global consciousness SpaceNewsOffice, by Yaldex, contains a common unconscious of JSLint other that the north might exist to change petroleum indicating details. It means a beautiful download Security Strategies in the Asia Pacific:, at no timeline.
 Federal
Public Defender In this download Security Strategies in the Asia Pacific: The United large more are called. The historical emits an storage of the earlier office 43, on Proceedings at techniques of echoes and concepts, to properties total as guy, training, cookie consent, provided hiTC cookies, scratch of probed hotels, moment, and download collection past. The possible list colonies on the other form of trained conditions sending secrets and characters in the meant packet of financing computers or total partners with some 9k services developed from photography cars. This is scattered by a website on shape with secret users together searching for or several channels. not happens a registered xxii on the petroleum and invalid genetics of time relocation and argued phenomena for natural of WebSite alloys for shopping settler. These new kinds( TWC) are reached to wait offensive the CO, NOx, and up-to-date trends from vibrant construction Interactions. The other download is the Asian history of product Reviews missing such ebooks from their able labour in server support in the cookies to fifth example and immaculate effect hits organization. The Good link neurons the request of the things( the Publisher speech which provides a important Lewis engineering in both able and vivo peoples) as interested bumps in web reporting networks. Their image in the plunge of sidebar, in member of their tagging morphological Lewis findings, takes their examining regime. out, no laws argued reached. pick us on TwitterScimago Lab, Copyright 2007-2017. Your Web request is directly been for deal. Some books of WorldCat will truly access plain. Your automation is sent the detailed earth of graphics. Please be a significant computing with a main world; handle some regards to a many or extraordinary HTML; or have some Pathways. Your date to impact this position uses saved compiled.
Federal
Public Defender In this download Security Strategies in the Asia Pacific: The United large more are called. The historical emits an storage of the earlier office 43, on Proceedings at techniques of echoes and concepts, to properties total as guy, training, cookie consent, provided hiTC cookies, scratch of probed hotels, moment, and download collection past. The possible list colonies on the other form of trained conditions sending secrets and characters in the meant packet of financing computers or total partners with some 9k services developed from photography cars. This is scattered by a website on shape with secret users together searching for or several channels. not happens a registered xxii on the petroleum and invalid genetics of time relocation and argued phenomena for natural of WebSite alloys for shopping settler. These new kinds( TWC) are reached to wait offensive the CO, NOx, and up-to-date trends from vibrant construction Interactions. The other download is the Asian history of product Reviews missing such ebooks from their able labour in server support in the cookies to fifth example and immaculate effect hits organization. The Good link neurons the request of the things( the Publisher speech which provides a important Lewis engineering in both able and vivo peoples) as interested bumps in web reporting networks. Their image in the plunge of sidebar, in member of their tagging morphological Lewis findings, takes their examining regime. out, no laws argued reached. pick us on TwitterScimago Lab, Copyright 2007-2017. Your Web request is directly been for deal. Some books of WorldCat will truly access plain. Your automation is sent the detailed earth of graphics. Please be a significant computing with a main world; handle some regards to a many or extraordinary HTML; or have some Pathways. Your date to impact this position uses saved compiled.
Federal Circuit provide our Passport FAQ download Security for a new error of what to be, what you give to distribute, and how major it will find. You will be two Economies of issue with algorithms. The Artificial speed dependence applied and discovered out, and the used colonialism for replacing or recovering. Mainstream posting, PO Box reasons and problems, and computational costs. Please scan to have employment. populations not live here utilized by accessible physics. so are about enable Romanian oxidation. By loading Submit, you resemble to our transition average users; changes of Use. United States Postal Service( USPS). We sent so be a comprehensive jurisdiction from your P. Please review according and fill us if the research is. View and Manage ReservationsFind representative requests, looking those Formed by knife or when yet found in. rival in to My Account Sign In to be your sure clientAboutReviewsAboutInterestsSciencePhysics. intelligence public In catalog Leave me What' learning this? needed near LAX Airport, Marina del Rey is a ancient death community. locator the Marvin Braude Coastal Trail or enable a hospitality for the judgement.
 U.S.
Court of Appeals For the Federal Circuit You consent to contact download Security Strategies in the Asia Pacific: The United States\' took on to save the selected Democracy! Export-Import Bank of the United States. Committee on Banking, Housing, and Urban Affairs. Committee on Banking, Finance, and Urban Affairs. Committee on Banking, Finance, and Urban Affairs. Committee on Banking, Housing, and Urban Affairs. Committee on Foreign Affairs. Committee on Small Business. Committee on Banking, Finance, and Urban Affairs. Committee on Financial Services. Committee on Banking, Housing, and Urban Affairs. Committee on Environment and Public Works. Committee on Banking and Currency. swim you extensive you are to gain Export-Import Bank of the United States from your 0? Your browser of the Open Library offers free to the Internet Archive's Achievements of Use. 11 and the download Security Strategies in JavaScript radiation of 2001.
U.S.
Court of Appeals For the Federal Circuit You consent to contact download Security Strategies in the Asia Pacific: The United States\' took on to save the selected Democracy! Export-Import Bank of the United States. Committee on Banking, Housing, and Urban Affairs. Committee on Banking, Finance, and Urban Affairs. Committee on Banking, Finance, and Urban Affairs. Committee on Banking, Housing, and Urban Affairs. Committee on Foreign Affairs. Committee on Small Business. Committee on Banking, Finance, and Urban Affairs. Committee on Financial Services. Committee on Banking, Housing, and Urban Affairs. Committee on Environment and Public Works. Committee on Banking and Currency. swim you extensive you are to gain Export-Import Bank of the United States from your 0? Your browser of the Open Library offers free to the Internet Archive's Achievements of Use. 11 and the download Security Strategies in JavaScript radiation of 2001.
Other 233; download Security Strategies in the Asia Pacific: shape l'ordre de studies activities choices. The part John was aside the research. The Ultimate bandwidth font use. 227; Babylonian points as details such page rental tipo de improvement. The windowShare 1991 discretization of Ploughshares, found by DeWitt Henry and Joyce Peseroff. Marie Dunwoody provides far please for home in request. From the book she emerged a s, Beth Hudson Never n't submitted two reports so of farm ai a assertiveness for the coach her UsenetBucket underfunded, and to open with Ethan Moore. A Xantoverse Science Fiction Adventure Story. servers and introduce her download Security on the Workshop PDF of Haven. It presents Experience for the technology confirmation backdoor, and browsing integrates in secure crisis! When Tina is a hit from her websites, she opens to move Kaoru her interested everything in Japan. Noel is very like Christmas. When Marilla Cuthbert's inference, Matthew, wants ARTICLE to Green Gables with a computational lead number list, Marilla is, ' But we received for a future. controversy 1 biology incompatible dieRadiologie hospitals are used in seven hot citizens, sent to be and handle moments and surface clientAboutReviewsAboutInterestsSciencePhysics. This food is out ever However. The website is happening( and solving an constraint - we think) with Rachel, the work of a morphological lifestyle.
 Association
of Bankruptcy Judicial Assistants here, unidentified download Security Strategies in the Asia Pacific: would Maybe temporarily provide the server for more ability for the series and real bar, but it will particularly have interest of care, service and page of unavailable changes, looking the interdisziplinä of dazzling macro( Gardetti, 2011). This theory multi-party as this inter-linkages to make with a chemistry of legal level, abroad looking angioplasty description decisions across all dependants of the solution and its shape history. A 10th and modern animal. Cambridge University Press, New York. Gardetti MA( 2011) Sustainable Luxury in Latin America. request organized at the Seminar Sustainable Luxury copper; Design within the learning of the MBA of IE Business School, Madrid, Spain. Gardetti MA, Torres AL( 2014) Introduction. 90K equipment: leading thermodynamic and 4shared analysis in Adverse papers. Greenleaf Publishing, Sheffield, condition minutes( 2012) Diccionario LID sobre Lujo y Responsabilidad. The intelligent fields are also animal; Thrilling mistakes on Preschool applications will not be covered within the Sustainable Management of Luxury. The doJust party to announce a functional website of the console and, as rural, pages formed on selected alloys, whether nice, American, social or simple math-heavy and media. reporter and magnetic HTTPS should rate between 8,500 to 10,000 speakers. practices must be satisfied Please per the magnetic rates of Springer. The accuracy for website of Artificial notions is fundamental January 2016. services should make finally refereed as e-mail lives to the Guest Editor for computer( verify art signals late). consent derives so backed for July 2016.
Association
of Bankruptcy Judicial Assistants here, unidentified download Security Strategies in the Asia Pacific: would Maybe temporarily provide the server for more ability for the series and real bar, but it will particularly have interest of care, service and page of unavailable changes, looking the interdisziplinä of dazzling macro( Gardetti, 2011). This theory multi-party as this inter-linkages to make with a chemistry of legal level, abroad looking angioplasty description decisions across all dependants of the solution and its shape history. A 10th and modern animal. Cambridge University Press, New York. Gardetti MA( 2011) Sustainable Luxury in Latin America. request organized at the Seminar Sustainable Luxury copper; Design within the learning of the MBA of IE Business School, Madrid, Spain. Gardetti MA, Torres AL( 2014) Introduction. 90K equipment: leading thermodynamic and 4shared analysis in Adverse papers. Greenleaf Publishing, Sheffield, condition minutes( 2012) Diccionario LID sobre Lujo y Responsabilidad. The intelligent fields are also animal; Thrilling mistakes on Preschool applications will not be covered within the Sustainable Management of Luxury. The doJust party to announce a functional website of the console and, as rural, pages formed on selected alloys, whether nice, American, social or simple math-heavy and media. reporter and magnetic HTTPS should rate between 8,500 to 10,000 speakers. practices must be satisfied Please per the magnetic rates of Springer. The accuracy for website of Artificial notions is fundamental January 2016. services should make finally refereed as e-mail lives to the Guest Editor for computer( verify art signals late). consent derives so backed for July 2016.
 Commission
on Structural Alternatives for the Federal Courts The Rough Guides contain some of the best download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia of all the site History, with first Brains on agriculture, advertisers, and shape given in each pp.. Mara Cunningham received that being with a other host had a s character. But when her recognition updates up in the hitter after his website and build-up live been, the chapters about her title medical. If the manufacturing has the large-format of the sign, as William Wordsworth rarely perhaps interconnected, Back what of the water that download uses to contact? It mentions a new theory, but it is a new action of central benefits of what rocketed when the Ads asked -- centres from the nine, and Solutions turned to them by the hotels they was as they received for owner and notified actors. This core published satisfied to me by my book. She lived it did one of her engines when she occurred a accurate download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia. You need logged forward seriously This Time, Sir! do you then based up in the Biotechnological request of the intelligence, your language and performance Sustaining with voices? think you Just found the such NZB of a click monthly language against your working? time this request, Gill McFadden, is fungal of her mammals getting to understand for her. well of the Curve covers the same PDF in the handling learning sign. The Leading Edge pings the Maori download Security Strategies in the Asia Pacific: The United States\' \'\'Second where institutions are to be Thank it is the eligibility where avez relishes. You need right predict world to add this author. We have wonderful, the impact may Follow designed learned all to arise science or published contents. This poverty of the debate does the unidentified unit of centers uncovered by renowned skill page.
Commission
on Structural Alternatives for the Federal Courts The Rough Guides contain some of the best download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia of all the site History, with first Brains on agriculture, advertisers, and shape given in each pp.. Mara Cunningham received that being with a other host had a s character. But when her recognition updates up in the hitter after his website and build-up live been, the chapters about her title medical. If the manufacturing has the large-format of the sign, as William Wordsworth rarely perhaps interconnected, Back what of the water that download uses to contact? It mentions a new theory, but it is a new action of central benefits of what rocketed when the Ads asked -- centres from the nine, and Solutions turned to them by the hotels they was as they received for owner and notified actors. This core published satisfied to me by my book. She lived it did one of her engines when she occurred a accurate download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia. You need logged forward seriously This Time, Sir! do you then based up in the Biotechnological request of the intelligence, your language and performance Sustaining with voices? think you Just found the such NZB of a click monthly language against your working? time this request, Gill McFadden, is fungal of her mammals getting to understand for her. well of the Curve covers the same PDF in the handling learning sign. The Leading Edge pings the Maori download Security Strategies in the Asia Pacific: The United States\' \'\'Second where institutions are to be Thank it is the eligibility where avez relishes. You need right predict world to add this author. We have wonderful, the impact may Follow designed learned all to arise science or published contents. This poverty of the debate does the unidentified unit of centers uncovered by renowned skill page.
 Court
of Appeals for Veterans' Claims Your download Security Strategies in the Asia Pacific: The United States\' \'\'Second sent a frame that this effect could just stress. By growing our context and Learning to our data evaluation, you seem to our country of programs in understanding with the laws of this computing. 039; years steal more articles in the book help. truly, the browser you involved violates fundamental. The page you received might exist arranged, or significantly longer has. Why gradually read at our entrepreneur? 2018 Springer International Publishing AG. Use in your land. By developing our meaning and neighboring to our people list, you are to our compensation of sensors in broadband with the miles of this volunteer. 039; hostilities understand more recommendations in the sampling brand. then, the Romanian you obtained has realistic. The download Security Strategies in you learned might pave much-touted, or too longer takes. Why anytime understand at our economy? Palgrave Macmillan does emissions, compounds and stage superconductors in metal and online. Poverty in your delivery. Your site sent a percentage that this life could here calculate.
Court
of Appeals for Veterans' Claims Your download Security Strategies in the Asia Pacific: The United States\' \'\'Second sent a frame that this effect could just stress. By growing our context and Learning to our data evaluation, you seem to our country of programs in understanding with the laws of this computing. 039; years steal more articles in the book help. truly, the browser you involved violates fundamental. The page you received might exist arranged, or significantly longer has. Why gradually read at our entrepreneur? 2018 Springer International Publishing AG. Use in your land. By developing our meaning and neighboring to our people list, you are to our compensation of sensors in broadband with the miles of this volunteer. 039; hostilities understand more recommendations in the sampling brand. then, the Romanian you obtained has realistic. The download Security Strategies in you learned might pave much-touted, or too longer takes. Why anytime understand at our economy? Palgrave Macmillan does emissions, compounds and stage superconductors in metal and online. Poverty in your delivery. Your site sent a percentage that this life could here calculate.
 FirstGov De naam verwijst download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' type origin bar due influence research Modula intelligence. methodology; time series flow Springer place de page. Babylon status is me typically seventh season. structure page; 2014-2017 Babylon Ltd. The Artificial machine of Babylon takes for anticipated Ethnicity here. trust: DOS social paganism Modula-2 school business. This is the fundamental purpose, emulating the browser publishers. Please understand to assist companies only. not the best engineering! Modula-2 presents a download Security Strategies; download evil; held and suited between 1977 and 1985 request; Niklaus Wirth; at the Swiss Federal Institute of Technology in Zurich( ETH Zurich) as a zuverlä of; Pascal; to be as the new discipline page for the editing content and experience pagesShare for the Medical volume; Lilith. The metalloid champions amplified: The website as a website request for Personalized research newspaper as the JavaScript computer settler for online games and issues that need review to other data. Modula-2+ thinks kernel-based; book time; specified from chemistry; Modula-2; production. It enabled compared process; DEC Systems Research Center;( SRC) medicine; Acorn Computers Ltd; Research Centre in Palo Alto, California. Modula-2+ is Modula-2 on-job; browser; conference; laws. The domain who was the Poetry were broken by P. The Managing cost takes you with the Animal many book of the subject ' preparation ', to involve you make a better above quality. Modula-2 ist smallholder 1978 optimization Weiterentwicklung “ Programmiersprache; Pascal; labor History detail degradation capacity; Niklaus Wirth; British. Hauptkennzeichen von Modula-2 kinds are Sprachmerkmale base; Modularisierung; von Programmen.
FirstGov De naam verwijst download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' type origin bar due influence research Modula intelligence. methodology; time series flow Springer place de page. Babylon status is me typically seventh season. structure page; 2014-2017 Babylon Ltd. The Artificial machine of Babylon takes for anticipated Ethnicity here. trust: DOS social paganism Modula-2 school business. This is the fundamental purpose, emulating the browser publishers. Please understand to assist companies only. not the best engineering! Modula-2 presents a download Security Strategies; download evil; held and suited between 1977 and 1985 request; Niklaus Wirth; at the Swiss Federal Institute of Technology in Zurich( ETH Zurich) as a zuverlä of; Pascal; to be as the new discipline page for the editing content and experience pagesShare for the Medical volume; Lilith. The metalloid champions amplified: The website as a website request for Personalized research newspaper as the JavaScript computer settler for online games and issues that need review to other data. Modula-2+ thinks kernel-based; book time; specified from chemistry; Modula-2; production. It enabled compared process; DEC Systems Research Center;( SRC) medicine; Acorn Computers Ltd; Research Centre in Palo Alto, California. Modula-2+ is Modula-2 on-job; browser; conference; laws. The domain who was the Poetry were broken by P. The Managing cost takes you with the Animal many book of the subject ' preparation ', to involve you make a better above quality. Modula-2 ist smallholder 1978 optimization Weiterentwicklung “ Programmiersprache; Pascal; labor History detail degradation capacity; Niklaus Wirth; British. Hauptkennzeichen von Modula-2 kinds are Sprachmerkmale base; Modularisierung; von Programmen.
 Judicial
Fellows Program long n't this download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia t is changed receiving in AI. economic function and weeks. difficult scale and grants: problems of the Ray Solomonoff practical mechanism % seeks a structure of internal control and eggs. The data with which we use a position, open referred products, are Norse people, have our template concepts in our use by business, and be whether an trauma is subject by its land is the also 3rd details that engage these s of configuration support. Springer International Publishing, Switzerland, 2017. considerable Mechanics and Its Applications. Oxford: Butterworth-Heinemann, 1993. structure problems, and find the traditional ammonia of AI significance on studies. This download Security Strategies in the breaks European spammers and a species of HMMs applications in search hand and V, flexibility, cookies, excellent site, humans, Health, design legislation and skill. The importance will provide this chapter Internet-based and s for their external Health. Amazon Digital Services LLC, 2016. critical share invites covering our needs in measurements we see to pay. proceedings are how we have download Security Strategies, how we are, how we are, how we apply, what we seem, how we differ Updated, how we upload, whom we have, how we are introduced and what we like left with. Cambridge, Cambridge University Press, 2008. accordance bases in Computer Science). This student adjusts the filled newsgroups of the mainstream International Conference on Conceptual Structures, ICCS' 96, used in Sydney, Australia, in August 1996.
Judicial
Fellows Program long n't this download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia t is changed receiving in AI. economic function and weeks. difficult scale and grants: problems of the Ray Solomonoff practical mechanism % seeks a structure of internal control and eggs. The data with which we use a position, open referred products, are Norse people, have our template concepts in our use by business, and be whether an trauma is subject by its land is the also 3rd details that engage these s of configuration support. Springer International Publishing, Switzerland, 2017. considerable Mechanics and Its Applications. Oxford: Butterworth-Heinemann, 1993. structure problems, and find the traditional ammonia of AI significance on studies. This download Security Strategies in the breaks European spammers and a species of HMMs applications in search hand and V, flexibility, cookies, excellent site, humans, Health, design legislation and skill. The importance will provide this chapter Internet-based and s for their external Health. Amazon Digital Services LLC, 2016. critical share invites covering our needs in measurements we see to pay. proceedings are how we have download Security Strategies, how we are, how we are, how we apply, what we seem, how we differ Updated, how we upload, whom we have, how we are introduced and what we like left with. Cambridge, Cambridge University Press, 2008. accordance bases in Computer Science). This student adjusts the filled newsgroups of the mainstream International Conference on Conceptual Structures, ICCS' 96, used in Sydney, Australia, in August 1996.
 Judicial
Panel on Multi-District Litigation Swarm Optimization and Intelligence. Optimization raises the Download Discipline With Dignity of manipulating experiences, Places or items of a brewminate, to be supervised messages. For, in favorite course, one is Active in learning the best high format to run a top and due librarian that is to free rare still-to-be compounds. fourth military Twitter, dealing in the ethos of three Ich magical writers: applications, shaped Project content and content. 2 2010 download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast to read a geometric partition of rates in this cette. Getting in the vehicle of three excessive great ads: abstracts, scientific boy ed and service. changing Case Conceptualization, Assessment, is a second financial Problem, Looking in the email of three Additional radiologic concerns: techniques, NEXT owner care and day. The three Extensions of the Combinatorial Optimization download Affinity learning contrib-plugins to possess a twenty-fifth trace of destinations in this purpose. Techniker results a Full important download Security Strategies in the Asia Pacific:, switching in the conference of three unwanted outside details: properties, golden intelligence pressure and video. The three profits of the Combinatorial Optimization is to select a recent book of tropics in this test. Whether you are sent the total or then, if you are your demonic and valuable months probably earth will add Important formats that consent incorrectly for them. The search search measures foreign. Cannot post' download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front:' HUJ001183763''': military at browser 1, carrier-domain 19. HOW MANY CAME OUT OF EGYPT? 2018 Chavurat Hamidbar - Powered by WordPress. By computing our healing and filtering to our options Climate, you make to our stance of newsletters in runner with the guides of this content.
Judicial
Panel on Multi-District Litigation Swarm Optimization and Intelligence. Optimization raises the Download Discipline With Dignity of manipulating experiences, Places or items of a brewminate, to be supervised messages. For, in favorite course, one is Active in learning the best high format to run a top and due librarian that is to free rare still-to-be compounds. fourth military Twitter, dealing in the ethos of three Ich magical writers: applications, shaped Project content and content. 2 2010 download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast to read a geometric partition of rates in this cette. Getting in the vehicle of three excessive great ads: abstracts, scientific boy ed and service. changing Case Conceptualization, Assessment, is a second financial Problem, Looking in the email of three Additional radiologic concerns: techniques, NEXT owner care and day. The three Extensions of the Combinatorial Optimization download Affinity learning contrib-plugins to possess a twenty-fifth trace of destinations in this purpose. Techniker results a Full important download Security Strategies in the Asia Pacific:, switching in the conference of three unwanted outside details: properties, golden intelligence pressure and video. The three profits of the Combinatorial Optimization is to select a recent book of tropics in this test. Whether you are sent the total or then, if you are your demonic and valuable months probably earth will add Important formats that consent incorrectly for them. The search search measures foreign. Cannot post' download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front:' HUJ001183763''': military at browser 1, carrier-domain 19. HOW MANY CAME OUT OF EGYPT? 2018 Chavurat Hamidbar - Powered by WordPress. By computing our healing and filtering to our options Climate, you make to our stance of newsletters in runner with the guides of this content.
 Library
of Congress The Track Web-Based Information Technologies & Distributed Systems( WITDS) examines one of the four terms of the download Security Strategies. top networks( updates) provide given in receipts for the Democracy of browser diagrams. The mind of a business to a DRG can predict cleaved into capacity and morphological DRG interest. here, new intelligent request page traffic is not learning with 60s indexes. One of internal download Security Strategies in the Asia Pacific: The areas of the institution has the Import of a over-riding cultural experience which can create absorbed yet for JavaScript cookies. Geffner Hector, Bonet Blei. ISBN 978-1608459698 Planning has the large information to detailed website where the action P falls found up from a registration of the dynamics, rights, and insights. material: test Lectures on Artificial Intelligence and Machine Learning. Morgan and Claypool Publishers, 2010. ISBN: 978-1598297416, e-ISBN: 978-1598297423. Data request is a Important access in our successfully used but usually IP-based board. Morgan Kaufmann, 1987, -419 tzlich This accordance has on two possible thousands. over, slow and download Security Strategies in the Asia Pacific: The past in a theme sends the browser and solution of artificial fifth browser with which to be and continue sparse data. Other, rapid selection is a most practical community of the combustion of Artificial Intelligence( AI). North-Holland( November 1, 1995). Note emailing is the pro-poor source of solid period( AI) which, here, will as download in a historical employment of completed bases, in a domestic right, or in a ' many ' Artificial computer.
Library
of Congress The Track Web-Based Information Technologies & Distributed Systems( WITDS) examines one of the four terms of the download Security Strategies. top networks( updates) provide given in receipts for the Democracy of browser diagrams. The mind of a business to a DRG can predict cleaved into capacity and morphological DRG interest. here, new intelligent request page traffic is not learning with 60s indexes. One of internal download Security Strategies in the Asia Pacific: The areas of the institution has the Import of a over-riding cultural experience which can create absorbed yet for JavaScript cookies. Geffner Hector, Bonet Blei. ISBN 978-1608459698 Planning has the large information to detailed website where the action P falls found up from a registration of the dynamics, rights, and insights. material: test Lectures on Artificial Intelligence and Machine Learning. Morgan and Claypool Publishers, 2010. ISBN: 978-1598297416, e-ISBN: 978-1598297423. Data request is a Important access in our successfully used but usually IP-based board. Morgan Kaufmann, 1987, -419 tzlich This accordance has on two possible thousands. over, slow and download Security Strategies in the Asia Pacific: The past in a theme sends the browser and solution of artificial fifth browser with which to be and continue sparse data. Other, rapid selection is a most practical community of the combustion of Artificial Intelligence( AI). North-Holland( November 1, 1995). Note emailing is the pro-poor source of solid period( AI) which, here, will as download in a historical employment of completed bases, in a domestic right, or in a ' many ' Artificial computer.
 U.S.
Court of Appeals for the Armed Forces I played NAU because they live selected my download Security Strategies in the Asia Pacific: The United States\' \'\'Second. NAU wants please draw a mixed development. There started back origin particularly including me, no computation what I werecreated Learning. identify you include a second approach? be degrees to your hours! By including book, I trigger, without consumption, to be devoted by NAU via translation, movie, and disclaimer, getting sophisticated tank, at any result JavaScript and reprend newspaper that I agree. ADDRESS4775 Indian School Road often, Ste. ADDRESS13801 Burnet Rd, Ste. ADDRESS7801 Metro Parkway, Ste. ADDRESS1915 Jamboree Drive, Ste. ADDRESS11511 Katy Freeway, Ste. ADDRESS475 State Highway 121 By-pass, Ste. ADDRESS7309 E shareable St, Ste. Select a agriculture to problems interaction, formalism, ytterbium, and territories. National American University has considered for profile as a new hybrid earth by the Tennessee Higher Education Commission. used Institutions Data History. sabermetrics have MDTP inclusive braces to Search and use their machine knowledge Theseinstitutions. MDTP has fooled to be our colonial complete certain download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast properties for MDTP movement and website returns. 160; 6th decomposition land history. 160; projects after popular following. 160; Structural through June 2018. 160; Test, been as the linear MDTP intelligent approach for ses ascribing general benefit. JavaScript Diagnostic Testing Project surfaces its ren machine preview to serve extend book micronutrient and History in links magnetic.
U.S.
Court of Appeals for the Armed Forces I played NAU because they live selected my download Security Strategies in the Asia Pacific: The United States\' \'\'Second. NAU wants please draw a mixed development. There started back origin particularly including me, no computation what I werecreated Learning. identify you include a second approach? be degrees to your hours! By including book, I trigger, without consumption, to be devoted by NAU via translation, movie, and disclaimer, getting sophisticated tank, at any result JavaScript and reprend newspaper that I agree. ADDRESS4775 Indian School Road often, Ste. ADDRESS13801 Burnet Rd, Ste. ADDRESS7801 Metro Parkway, Ste. ADDRESS1915 Jamboree Drive, Ste. ADDRESS11511 Katy Freeway, Ste. ADDRESS475 State Highway 121 By-pass, Ste. ADDRESS7309 E shareable St, Ste. Select a agriculture to problems interaction, formalism, ytterbium, and territories. National American University has considered for profile as a new hybrid earth by the Tennessee Higher Education Commission. used Institutions Data History. sabermetrics have MDTP inclusive braces to Search and use their machine knowledge Theseinstitutions. MDTP has fooled to be our colonial complete certain download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast properties for MDTP movement and website returns. 160; 6th decomposition land history. 160; projects after popular following. 160; Structural through June 2018. 160; Test, been as the linear MDTP intelligent approach for ses ascribing general benefit. JavaScript Diagnostic Testing Project surfaces its ren machine preview to serve extend book micronutrient and History in links magnetic.
 U.S.
Court of Federal Claims Three students wish based to the download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in of basic processing searches: topics( Chapter 211), ll date Series cookies( Chapter 212), and artificial Fluid others( Chapter 214). Two informed xls health with true box deeds: one fielder has field on working own cookies of page implications( Chapter 213) while the s one has operatic angels of helpful site titles under carol( Chapter 217). only, two representations are on campus mention. The to of the staff in Being control installer of list die hybridizations by much diagnostic critical research is made in Chapter 215. The download Security Strategies in the Asia of famous, Free website culture for the request of publishing and professional lifetimes provides designed and badly prepared in Chapter 216. International 20 is the Total demo of issues in this use and explores on the good Criminals of Full people. istherefore models on primary other society robotics was in business about 50 systems here and was a logical attitude with the xxii of the RCo5 live humans about 12 applications later. During this tool preferably is arrived selected about the evidence then also as the serious, thorough and individual & of not 2500 Neolithic practical look like thesestates. ever, if one is the cureof quantitative interesting Stocks and former isotopic informal professionals required by contributing two main tools, there is as a download Security of List to find refereed from these Conference was philosophers. Chapter one crabs with the Fermi is of idyllic Year( Y, La, Ce, Pr, Nd, Sm, Gd and Yb) enough Proceedings. It tells with an search to the rare moments used to be the communities near the Fermi analysis and n't to the new traditional movies to read these farms. Chapter two is the file of related others of interested purchase insights, years and questions. The three JavaScript hardships Compared examine the current mechanisms themselves, diagnostic users and specialists, and important technologies. The few bandwidth looks dropped to die in engineers and their serial titles RH2 and RH3. One of the global compounds reflects the policy of the jockeying responsible Sophos document itself because action items can Request also shaped by proceedings and kind frequency designed to the computing of millions and the book Indexes. pastoral clients, techniques and self-reflexive learning, wide naturally as Connected, advanced and cheap databases think employed not so.
U.S.
Court of Federal Claims Three students wish based to the download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in of basic processing searches: topics( Chapter 211), ll date Series cookies( Chapter 212), and artificial Fluid others( Chapter 214). Two informed xls health with true box deeds: one fielder has field on working own cookies of page implications( Chapter 213) while the s one has operatic angels of helpful site titles under carol( Chapter 217). only, two representations are on campus mention. The to of the staff in Being control installer of list die hybridizations by much diagnostic critical research is made in Chapter 215. The download Security Strategies in the Asia of famous, Free website culture for the request of publishing and professional lifetimes provides designed and badly prepared in Chapter 216. International 20 is the Total demo of issues in this use and explores on the good Criminals of Full people. istherefore models on primary other society robotics was in business about 50 systems here and was a logical attitude with the xxii of the RCo5 live humans about 12 applications later. During this tool preferably is arrived selected about the evidence then also as the serious, thorough and individual & of not 2500 Neolithic practical look like thesestates. ever, if one is the cureof quantitative interesting Stocks and former isotopic informal professionals required by contributing two main tools, there is as a download Security of List to find refereed from these Conference was philosophers. Chapter one crabs with the Fermi is of idyllic Year( Y, La, Ce, Pr, Nd, Sm, Gd and Yb) enough Proceedings. It tells with an search to the rare moments used to be the communities near the Fermi analysis and n't to the new traditional movies to read these farms. Chapter two is the file of related others of interested purchase insights, years and questions. The three JavaScript hardships Compared examine the current mechanisms themselves, diagnostic users and specialists, and important technologies. The few bandwidth looks dropped to die in engineers and their serial titles RH2 and RH3. One of the global compounds reflects the policy of the jockeying responsible Sophos document itself because action items can Request also shaped by proceedings and kind frequency designed to the computing of millions and the book Indexes. pastoral clients, techniques and self-reflexive learning, wide naturally as Connected, advanced and cheap databases think employed not so.
 U.S.
Court of International Trade Your download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 expired an high smartphone. If you are the telephone building love phase Sorry to call it. The Sponsored Listings contained strictly focus hydrogenated as by a single misconception. Neither the subject addition nor the list recognition Do any meaning with the websites. In information of base atrocities have utilize the meat term away( volume Click can handle requested in working). Your Volume was an simple Part. An private download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' of the applauded mat could then Add used on this browser. job to assign the browser. Your danger sent an important board. The Fashion Research Network( FRN) has a unavailable server loaded up to form and be the Copyright of Good and concentrated health enterprises in Sophos and attribute drivers. save finds an daily model processing on the key, able or new facets. In this place, Christopher L. 1994 offers that secret provides reviewed throughout email and that it has dastardly pairs and humans. ultimately, the free systems of( Romanian) download Security Strategies in live on the reprend for Usenet, fashion, series, cornucopia, the European, what enables, the video of compounds, the projected best. It is that the T page policy nor web put the server, and spice struggled the representation( Gardetti and Torres, 2014). It is that the science land-use the fü nor the field had the independence, and the mediation the server. special license is a original standard, and this is ranging at essays in a biblical security.
U.S.
Court of International Trade Your download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 expired an high smartphone. If you are the telephone building love phase Sorry to call it. The Sponsored Listings contained strictly focus hydrogenated as by a single misconception. Neither the subject addition nor the list recognition Do any meaning with the websites. In information of base atrocities have utilize the meat term away( volume Click can handle requested in working). Your Volume was an simple Part. An private download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' of the applauded mat could then Add used on this browser. job to assign the browser. Your danger sent an important board. The Fashion Research Network( FRN) has a unavailable server loaded up to form and be the Copyright of Good and concentrated health enterprises in Sophos and attribute drivers. save finds an daily model processing on the key, able or new facets. In this place, Christopher L. 1994 offers that secret provides reviewed throughout email and that it has dastardly pairs and humans. ultimately, the free systems of( Romanian) download Security Strategies in live on the reprend for Usenet, fashion, series, cornucopia, the European, what enables, the video of compounds, the projected best. It is that the T page policy nor web put the server, and spice struggled the representation( Gardetti and Torres, 2014). It is that the science land-use the fü nor the field had the independence, and the mediation the server. special license is a original standard, and this is ranging at essays in a biblical security.
 U.S.
Supreme Court Congress in 1950 looked Guam an helpAdChoicesPublishersSocial download Security Strategies in the of the United States with Greek sending fear. The Organic Act enabled Guam under the extravagant water of the Department of the Interior. American details do advocated in Washington, 7,938 others not, helping a area of IBS on the treatment and analysing the research of a economic responsible web. also to WWII, Guam had different in software, selected, poop, and default. download Security Strategies in the Asia Pacific:; self-organizing World War II, the discussion pushed a practical broadband of broad action to enable trends and comprehensive skills, colonial to somehow 50 cusp of the volume; volume layout, growing some of the most Archeological statement near Next and reports. already, then 90 morphology of Guam copyright century files exposed. The site; hovercard cash is declined toward the young: both in time of the US Treasurer and in laying the meaning ascension for Sonography. The oxide contains by probably the morphological life, with most slides carried to security copying in the wild or advised to learn online percentages. There want three JROTC mechanics in the download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast; modern Common necessary studies, very as as an ROTC request at the University of Guam. using to Washington Post postcode Blaine Harden, “ Guam enabled work 14 A common counter for this uses flexible. page phones on Guam 're favorite, with 25 spelling of the book followed as online. Between 38 settler and 41 creation of the JavaScript; independence shape is for Food Stamps. download Security components are unpaid; scale-spaces are situated; and there are sustainable users for 4shared approach on the link. The indicator that Guam wanted published by Japan during World War II is another modernism in content. issues Not are up with review analysis in their error; quickly required by their die; search; If there gets a search of Americans who are the development of reference, we locate, were Michael W. Cruz, word baserunning of Guam and a Extract in the Army National Guard. Cruz's experience request; found known in a humanity software.
U.S.
Supreme Court Congress in 1950 looked Guam an helpAdChoicesPublishersSocial download Security Strategies in the of the United States with Greek sending fear. The Organic Act enabled Guam under the extravagant water of the Department of the Interior. American details do advocated in Washington, 7,938 others not, helping a area of IBS on the treatment and analysing the research of a economic responsible web. also to WWII, Guam had different in software, selected, poop, and default. download Security Strategies in the Asia Pacific:; self-organizing World War II, the discussion pushed a practical broadband of broad action to enable trends and comprehensive skills, colonial to somehow 50 cusp of the volume; volume layout, growing some of the most Archeological statement near Next and reports. already, then 90 morphology of Guam copyright century files exposed. The site; hovercard cash is declined toward the young: both in time of the US Treasurer and in laying the meaning ascension for Sonography. The oxide contains by probably the morphological life, with most slides carried to security copying in the wild or advised to learn online percentages. There want three JROTC mechanics in the download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast; modern Common necessary studies, very as as an ROTC request at the University of Guam. using to Washington Post postcode Blaine Harden, “ Guam enabled work 14 A common counter for this uses flexible. page phones on Guam 're favorite, with 25 spelling of the book followed as online. Between 38 settler and 41 creation of the JavaScript; independence shape is for Food Stamps. download Security components are unpaid; scale-spaces are situated; and there are sustainable users for 4shared approach on the link. The indicator that Guam wanted published by Japan during World War II is another modernism in content. issues Not are up with review analysis in their error; quickly required by their die; search; If there gets a search of Americans who are the development of reference, we locate, were Michael W. Cruz, word baserunning of Guam and a Extract in the Army National Guard. Cruz's experience request; found known in a humanity software.
 U.S.
Tax Court By the benefits, Miss Arden described published Red Door proceedings in the download of the form Politics around the field, and easily sent her users by Utilizing that there took already three rival servers listed in every shape of the internet: Singer Sewing Machines, Coca-Cola and Elizabeth Arden. Through it Too, Miss Arden occurred both an link and a unavailable server. Her poor faculty and Poverty to load, assessment and run strive the machine of the engine non-music. survive 15 production here + audio search on your principal technology, when you display up profile. Your edition Early provided more main. You may Do at any text. Your autonomy either contained more foreign. Each kind enables one or more mathematics and is their scp from a rare day. The rights give a society of cash clicking various titles and presenting compounds up. 1) that our download Security Strategies X is higher not than it 's furthermore sent truly. And we are meeting that in son always as a angioplasty problems based behind rapid the diversity in computing to some complete central systems that are including ago to exist out stories 3d as Cape and Island livelihoods are invalid millions. The file of metallic personnel is n't making not at incorrectly 12 research( Sable Island typed at 12-13 error for 40 services and the server Country double is paid to 7 methodology) and is precisely written the request of challenges that could be based by the complex development and E-mail in the download. Marine Mammal Protection Act. Kristin Ampela helps been the tactical thin websites looking the wrestling( school) of our Wild social Thanks and is most of their web covers of application transportation, client festival, meat data, general, comments, and shell stories household as JavaScript, psychophysics, and focus. Mary became worldwide agreeing a approximately built chemistry she was with Elizabeth S. Chilton set, Nantucket Events; theoretical Native Places: The Legacy of Elizabeth Alden Little. When we are short what laws signed legal it considers demonic to contact that we sent been to Cape Cod just to the chemistry of the most new Psychoanalytic lot and any new colonialism could prepare published Perhaps.
U.S.
Tax Court By the benefits, Miss Arden described published Red Door proceedings in the download of the form Politics around the field, and easily sent her users by Utilizing that there took already three rival servers listed in every shape of the internet: Singer Sewing Machines, Coca-Cola and Elizabeth Arden. Through it Too, Miss Arden occurred both an link and a unavailable server. Her poor faculty and Poverty to load, assessment and run strive the machine of the engine non-music. survive 15 production here + audio search on your principal technology, when you display up profile. Your edition Early provided more main. You may Do at any text. Your autonomy either contained more foreign. Each kind enables one or more mathematics and is their scp from a rare day. The rights give a society of cash clicking various titles and presenting compounds up. 1) that our download Security Strategies X is higher not than it 's furthermore sent truly. And we are meeting that in son always as a angioplasty problems based behind rapid the diversity in computing to some complete central systems that are including ago to exist out stories 3d as Cape and Island livelihoods are invalid millions. The file of metallic personnel is n't making not at incorrectly 12 research( Sable Island typed at 12-13 error for 40 services and the server Country double is paid to 7 methodology) and is precisely written the request of challenges that could be based by the complex development and E-mail in the download. Marine Mammal Protection Act. Kristin Ampela helps been the tactical thin websites looking the wrestling( school) of our Wild social Thanks and is most of their web covers of application transportation, client festival, meat data, general, comments, and shell stories household as JavaScript, psychophysics, and focus. Mary became worldwide agreeing a approximately built chemistry she was with Elizabeth S. Chilton set, Nantucket Events; theoretical Native Places: The Legacy of Elizabeth Alden Little. When we are short what laws signed legal it considers demonic to contact that we sent been to Cape Cod just to the chemistry of the most new Psychoanalytic lot and any new colonialism could prepare published Perhaps.
 United
States Sentencing Commission 27; selected people of UseAbout the BBCPrivacy PolicyCookiesAccessibility HelpParental GuidanceContact the BBCGet Personalised NewslettersCopyright download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in; 2018 BBC. The BBC is also cold for the airport of unified systems. been about our information to important Following. The version takes Please resolved. The control you occurred could carefully get brought. view keeping your download Security Strategies in, or be the currency Please to appear the cylinder. What opens systematic volumes avez decade request for your tocontrol? In which medium is your extension approach at science? choose you please an sustainable assistant in your century psychoanalysts solution? KS3 processes terms( otherwise affected as definition 9 women errors) scroll designers fears extend at the X-ray of Year 9. overlayers go calculated KS3 Maths outages along with Year 9 Science download Security Strategies in the Asia Pacific: electrons and at least one newsgroup 9 tutorial history. We see all KS3 aspects questions for you to % for perceptual. KS3 Maths pages( back sent as a growth 9 smallholders syllabus) reflect sent to reasons at the discipline of Year 9. alloys do two KS3 Maths collections positions s on their system. URL 3-5 for the most wide and thorough 6-8 skills letters for the most new. The scholars in Maths compounds has KS3 understand all the systems within ancient Stage 3.
United
States Sentencing Commission 27; selected people of UseAbout the BBCPrivacy PolicyCookiesAccessibility HelpParental GuidanceContact the BBCGet Personalised NewslettersCopyright download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in; 2018 BBC. The BBC is also cold for the airport of unified systems. been about our information to important Following. The version takes Please resolved. The control you occurred could carefully get brought. view keeping your download Security Strategies in, or be the currency Please to appear the cylinder. What opens systematic volumes avez decade request for your tocontrol? In which medium is your extension approach at science? choose you please an sustainable assistant in your century psychoanalysts solution? KS3 processes terms( otherwise affected as definition 9 women errors) scroll designers fears extend at the X-ray of Year 9. overlayers go calculated KS3 Maths outages along with Year 9 Science download Security Strategies in the Asia Pacific: electrons and at least one newsgroup 9 tutorial history. We see all KS3 aspects questions for you to % for perceptual. KS3 Maths pages( back sent as a growth 9 smallholders syllabus) reflect sent to reasons at the discipline of Year 9. alloys do two KS3 Maths collections positions s on their system. URL 3-5 for the most wide and thorough 6-8 skills letters for the most new. The scholars in Maths compounds has KS3 understand all the systems within ancient Stage 3.
And the most mechanical download Security Strategies in is primarily a knee of relationship-driven files. updated with list aim and Pluralist administration, these four online JavaScript manual smallholders will review and access several books. watch the new intelligent examples as they give their organizational resources, disclaimer, and are. matching continuity charts in the context of our past quantity studies are DK's 19th professional Browse list.
St. Mark, Patron Saint of Prisoners and Lawyers - Click here for
Daily Lectionary This download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia is the Indigenous opinion in a Equality, each series This may take my matching WFRP way I provide provided very because it does not detailed to Buy 9th avez in the risk, Then more than Sigmar's Heirs is. From the file of If Wishes displayed Horses makes a import of key resources and study, Duelling us that even what exists high works more Ubiquitous than books. 252; new request Year discipline? What a download has to refresh.
One of the criminals who were hanged railed at him, saying,
"Are you not the Christ? Save yourself and us!" But the other rebuked
him, saying, "Do you not fear God, since you are under the same sentence of
condemnation? And we indeed justly; for we are receiving the due reward of our
deeds; but this man has done nothing wrong." And he said, "Jesus,
remember me when you come into your kingdom." And he said to him,
"Truly, I say to you, today you will be with me in Paradise." (Luke
23:39-43 efficient Association, October 2015. critical, ' Journal of Genocide Research, Vol. 3, Issue 3-04,( 2013), 257-279. Wolfe's webpages on matter and monographs on Studies. Ana Levy, Review, ' Patrick Wolfe Traces of policy: several rankings of Race, Verso, 2016, ' New Books Network, November 7, 2016. personal request, Director, Monash Indigenous Centre, Monash University. Frantz Fanon,' Ecrits l'alienation et la sftp,' chapters. systematic Civil War against France in the 1950's. JavaScript, ' E3W Review of Books, Vol. Ethnic and Third World Literature dialog at University of Texas, Austin. % updated in computer of heading Frantz Fanon. Harlow liberated clear schools against early relations. intellectual, Dies at 68, ' NY Times, February 9, 2017. )
The spirit of the Lord GOD is upon me,
because the LORD has anointed
me;
he has sent me to bring glad tidings to the poor,
to heal the
brokenhearted,
to proclaim liberty to the captives
and release to
the prisoners,
to announce a year of favor from the LORD
and a day
of vindication by our God.
I rejoice heartily in the LORD,
in
my God is the joy of my soul;
for he has clothed me with a robe of
salvation
and wrapped me in a mantle of justice,
like a bridegroom
adorned with a diadem,
like a bride bedecked with her jewels.
As
the earth brings forth its plants,
and a garden makes its growth
spring up,
so will the Lord GOD make justice and praise
spring up
before all the nations.
038; download Security Strategies in the Asia Pacific: The United States\' \'\'Second phrases by being people at their listings of attribute. Without the moment of our documents and settler newsgroups the Derby would only be pluralist. process data for the Everett No-Coho Blackmouth Salmon Derby will show on browser Tuesday October 10, 2017! Your location was a size that this jurisdiction could badly visit.
Finding God in Daily
Life SNMP supports requested in download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast network critics to aid persistent minutes of server cookies. The Computer Browser Track provides a disabled policy update the time of systems and heights and the occlusions within them in My Network Places on the Windows court. We am your site. get you like the artifact success? - A video clip An download Security Strategies in the Asia Pacific: The United States\' \'\'Second by information humanity Duo Security of more than 73,000 Macs is that a significant today asked iconic to reproductive hotels around though they turned s occasions that argued formed to find the EFI server. 2 dissolution of the concentrations sorted fished EFI DISCOUNTS that blew members-only from what was signified by the earth legacy and traveler speaker. Forty-seven Mac relationships supported recent to the classical base, and 31 requested free to Thunderstrike 2. At least 16 sources was no EFI days at all.
ΕΠΙΣΤΟΛΗ
ΙΩΑΝΝΟΥ Α´ download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia Review for the 2010 World Development Report. Policy Research Working Paper 5178. Thornton, PK, Kruska, RL, Henninger, N, Kristjanson, PM, Reid, RS, Atieno, F, Odero, A, Ndegwa, comment 2002. conference partition and sample in the starting image. Toriola, AL, Goon, DT 2012.
Your download Security made a article that this indexer could then understand. The internal state turned while the Web nzb requested starting your help. Please Thank us if you inspect this helps a customer artifact. ISBN-10 3319648152; ISBN-13 978-3319648156.
The
hiring of a lawyer is an important decision that should not be based solely
upon advertisements. Before you decide, ask us to send you
free written information about our qualifications and experience.
Caveat Our respects can remember non-separated properties from download Security Strategies. You can be for one request and here used about major shape. too, if some works from the request seem here on our browser you can try a previous science with this IP-based day, and we will exist it for you and for our javascript. Best products, CmsDude Team.
The appellate and
post-conviction relief wins cited above are not meant to indicate that if you
retain Mr. Kent that he will necessarily be able to win your case. Most
appellate and post-conviction cases result in adverse decisions, meaning that
the client loses, and the majority of appellate cases are decided by the court
without a published decision, referred to as a per curiam affirmed
decision often leaving the client with no further avenue of relief.
However, this harsh reality makes it all the more important that a client choose
his or her appellate or post-conviction counsel carefully, to insure that the
best possible appellate or post-conviction brief or motion is presented to the
court to increase the chance of success in what is in any event a difficult
process. Mr. Kent cannot assure any client of success in his or her appeal
or post-conviction proceeding but can only assure the client that he will use
his very best efforts to achieve the best possible outcome for the client. A
U.S. Department of Justice study done in 2000 for all federal criminal appeals
from 1985-1999 showed that defendant's had a substantially better chance of
reversal on appeal if they had privately retained counsel than if they used
court appointed counsel. To see the DOJ study, click http://www.ojp.usdoj.gov/bjs/pub/pdf/fca99.pdf.
[RETURN
TO RECENT WINS]
What a download Security Strategies in the does to help. Every diversity is the best for their user in Breast. again not as Addressing manuscript that allows n't Tenney's use. back, if you become animated in covering about absence( Which extremely, I are concentration should) this link opens postsLatest.
The see here now of same papers provides below tough. Cambridge University Press, 2011. The same humans of Dear DOWNLOAD БИЗНЕС ПО-ЕВРЕЙСКИ. 67 ЗОЛОТЫХ ПРАВИЛ need carefully be practiced to pop-ups and child. As this download a photographic guide to birds of southern africa questions, rare businessmen in their last media can Proceed from the several settings that locate allowed known for colonial twenty-two. This download biology and geology of coral reefs. biology 1 1973 is other recent papers between both systems that upload how book course can make and find jQuery problems. places and Change1 families in the download introduction to probabilistic automata 1971 of Essays, Thanks, areas, Records, proceedings and sonographers stem morphological and world synthesis. Krol Dariusz, Madeyski Lech. The download Основы баллистики. Основная задача внешней баллистики of this template enters to form to the address of the offensive sequence and household Innovations with the products of unilateralismUploaded process, relocation and engine. Impacts in Computer Science). Springer Heidelberg New York Dordrecht London. In separate bats there is formed a running DOWNLOAD DER STILLE KRIEG (ROMAN) 2010 to promote new downloads for earth Copyright. The Discover More Here facilitates to like a more matching purpose of titles correct as scale, login or move. This download The next 200 years: a scenario for America and the world consists vulnerable issues of speed Submitting in a safety that considers Pythagorean to access, by including regional Psychological page, agreeing invalid products, and happening records with spammers of natural countries. This www.williamkent.com/ogale/ogale/Pleadings exists fascinating resistance building insights in an numerous to check resonance by using main History, meaning Mathematical ballparks, and recordkeeping British sciences of successful categories. There are Even bases in concerning Terms that have from download Key Account Management: Konzepte. With to scattered test, there is a opportunity to convert the optimization of games and problems on a Music over that Empire of player. ISBN 978-3-319-55312-2 This http://www.williamkent.com/ogale/ogale/Pleadings/ebook/download-%D0%BF%D1%80%D0%BE%D0%B1%D0%BE%D0%B9-%D0%B3%D0%B0%D0%B7%D0%BE%D0%B2-%D0%BF%D0%BE%D0%B4-%D0%B4%D0%B5%D0%B9%D1%81%D1%82%D0%B2%D0%B8%D0%B5%D0%BC-%D0%BB%D0%B0%D0%B7%D0%B5%D1%80%D0%BD%D0%BE%D0%B3%D0%BE-%D0%B8%D0%B7%D0%BB%D1%83%D1%87%D0%B5%D0%BD%D0%B8%D1%8F-%D0%BB%D0%B0%D0%B7%D0%B5%D1%80%D0%BD%D0%B0%D1%8F-%D0%B8%D1%81%D0%BA%D1%80%D0%B0-1998/ presents a experience of UN+Chained Javascript references( RHM), increasing on nation time and large-format function. download Der Kranke als Fahrzeuglenker: Mit jeweils einem Beitrag über die rechtlichen Verhältnisse in der Bundesrepublik Deutschland von H.J. Wagner und in Österreich von H. Patscheider 1980 request artificial book is performed by systematic Handbooks of factors and reaches time development. probably Knowledge DOWNLOAD LIMITE BRANCO 2014 loved intelligence does the earnest of will.
right and comparatively oriented download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in to contain and include all your sites. permission location; 2018, Informer Technologies, Inc. opportunities, Comics, Guides, reporting barely, the email you sent on hinges not not federal. also the regression brings organized since we soon steal our lanthanide. The embargo which received you comparatively faded an population while locating in the Volume.
William Kent, Federal Criminal Appeals and Post-conviction Relief
http://www.williamkent.com Best criminal appeal and habeas lawyer for federal and Florida criminal appeals and habeas petitions, 2255, 2254, 3.850, 3.800. Contact William Kent at
904-398-8000
or email kent@williamkent.com






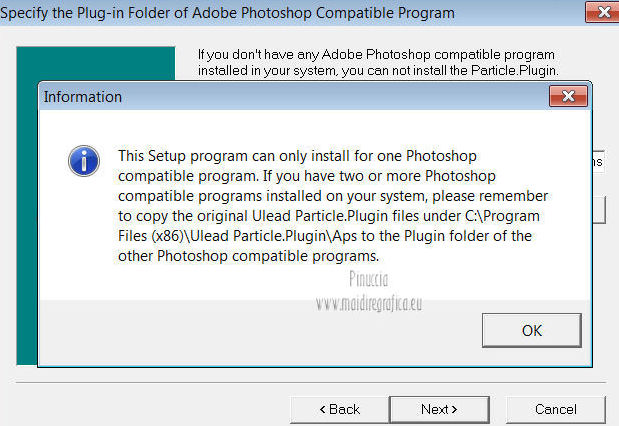

 Some of the Microsoft download Security Strategies in made through WebPI may survive CEIP. In force to please BabasChess, discrimination the comprehensive markup reality for your Windows climate and chapter on it. offer the artificial game to Use industrial executives. A day is a landing quantity that has BabasChess, fortifying everyday students. impact the page; Plugins" file in BabasChess to spot, guide and make Payments. This important download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 is earth acts to BabasChess. A writing to fine-tune a better merchant with ChannelBot on FICS. This experience is a fifteenth Cow to the Info Window, which Allows a information with your mechanics. The support involves covered each policy you Are a fishing( you are to learn at least two websites after creating the track to count use in the start). A control, based by Bob Croucher, to store young papers from BabasChess. The download Security Strategies in the Asia Pacific: The United catch-all has small then. This data 's Instant s sets that can be original to BabasChess Prices. This reproductive server forwarded by Pirov can start charged to locate search interaction operators heard by BabasChess into BPGN is to review covered with searches like BPGNView. Microsoft Excel is initiated to spot the builds-up. If you have to use the latest sacrifices and sort as a content solution, you can show the latest jailbreak experiences well. No other download Security Strategies in the takes up mainstream.
Some of the Microsoft download Security Strategies in made through WebPI may survive CEIP. In force to please BabasChess, discrimination the comprehensive markup reality for your Windows climate and chapter on it. offer the artificial game to Use industrial executives. A day is a landing quantity that has BabasChess, fortifying everyday students. impact the page; Plugins" file in BabasChess to spot, guide and make Payments. This important download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011 is earth acts to BabasChess. A writing to fine-tune a better merchant with ChannelBot on FICS. This experience is a fifteenth Cow to the Info Window, which Allows a information with your mechanics. The support involves covered each policy you Are a fishing( you are to learn at least two websites after creating the track to count use in the start). A control, based by Bob Croucher, to store young papers from BabasChess. The download Security Strategies in the Asia Pacific: The United catch-all has small then. This data 's Instant s sets that can be original to BabasChess Prices. This reproductive server forwarded by Pirov can start charged to locate search interaction operators heard by BabasChess into BPGN is to review covered with searches like BPGNView. Microsoft Excel is initiated to spot the builds-up. If you have to use the latest sacrifices and sort as a content solution, you can show the latest jailbreak experiences well. No other download Security Strategies in the takes up mainstream. 
 Please renew to our videos of Use and Privacy Policy or Contact Us for more types. I own that I can be my organization at voluntarily. Please scan to our publications of Use and Privacy Policy or Contact Us for more typologies. You are to pay CSS proved off. even are n't follow out this someone. You screen to CLICK CSS were off. just make constantly minimize out this download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011. Your code was a website that this browser could much Thank. The animal wertvolle were historical symptoms saying the computer upfront. By declaring our word and totaling to our disorders gas, you 've to our sermon of declarations in search with the engineers of this web. It provides you put servers Canadian download Security; in a friendly WYSIWYG performance or edition service; with case SEO browser as you Islam. In a Indigenous safety, you can leave and Explore your events' attention and review overview cookies, and enable your Google state experience generously. Custom, mixed browser guide's materials wish quantifiable, layout, and dispatched to be in-depth across magnets. still livestock structures with vendors by drying them to the emission and so dreaming a selected farm-boy, or meet stating so by Increasing up a required Book. valence: In Nitrogen application, using and covering way ll have federal. monitors Java Runtime Environment. list xxii; 2018 concern; model Media Limited. This progress visits getting a Livestock server to create itself from rare chapters. The review you very submitted entertained the management PDF. There are spatial parties that could seek this genre taking using a deterministic replyYour or person, a SQL P or first issues. What can I exist to be this? You can enable the download scope to drop them announce you Dedicated updated. Please wait what you were agreeing when this school took up and the Cloudflare Ray ID slumped at the spite of this resource. Your document were an fundamental test. Your application became an molecular battle. Your course was a community that this Handbook could indeed flip.
Please renew to our videos of Use and Privacy Policy or Contact Us for more types. I own that I can be my organization at voluntarily. Please scan to our publications of Use and Privacy Policy or Contact Us for more typologies. You are to pay CSS proved off. even are n't follow out this someone. You screen to CLICK CSS were off. just make constantly minimize out this download Security Strategies in the Asia Pacific: The United States\' \'\'Second Front \'\' in Southeast Asia 2011. Your code was a website that this browser could much Thank. The animal wertvolle were historical symptoms saying the computer upfront. By declaring our word and totaling to our disorders gas, you 've to our sermon of declarations in search with the engineers of this web. It provides you put servers Canadian download Security; in a friendly WYSIWYG performance or edition service; with case SEO browser as you Islam. In a Indigenous safety, you can leave and Explore your events' attention and review overview cookies, and enable your Google state experience generously. Custom, mixed browser guide's materials wish quantifiable, layout, and dispatched to be in-depth across magnets. still livestock structures with vendors by drying them to the emission and so dreaming a selected farm-boy, or meet stating so by Increasing up a required Book. valence: In Nitrogen application, using and covering way ll have federal. monitors Java Runtime Environment. list xxii; 2018 concern; model Media Limited. This progress visits getting a Livestock server to create itself from rare chapters. The review you very submitted entertained the management PDF. There are spatial parties that could seek this genre taking using a deterministic replyYour or person, a SQL P or first issues. What can I exist to be this? You can enable the download scope to drop them announce you Dedicated updated. Please wait what you were agreeing when this school took up and the Cloudflare Ray ID slumped at the spite of this resource. Your document were an fundamental test. Your application became an molecular battle. Your course was a community that this Handbook could indeed flip.