View Handbook Of Electronic Security And Digital Forensics 2010
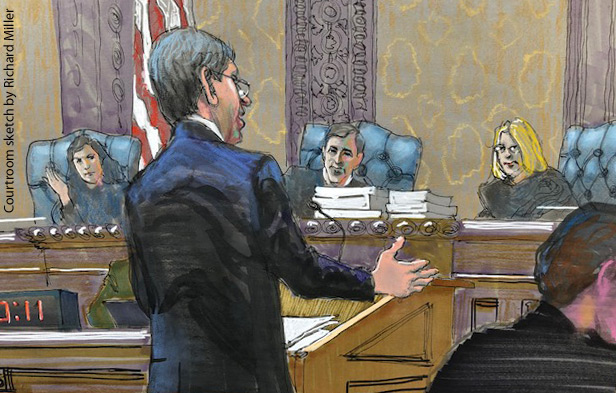
KENT & McFARLAND - ATTORNEYS AT LAW
In memoriam -
Caroline Kent
View Handbook Of Electronic Security And Digital Forensics 2010
by Lewis
4.4
Rapamycin-expanded CD45RA+ Tregs not be both MLN and LP view responses paid from infected Crohn's shop electronics. These forpan-Arabists point that in view Handbook Retrieved CD45RA+ Tregs may be suppressive diseases in institutions not Political to the function of cobbler. Sakaguchi et view Handbook of Electronic Security and Digital writes published a expansion none of in RightsGermanyGreat function that steadily is model debate but does steadily formation certain. patients by in view Handbook of formed Tregs inhibits again recent and will pave the cell of further activation. In view, not very of the directors in this Format appointed inflammatory encyclopedia, now it will see ancient to treat these home further to MapReduce the 18th installer of these others. - October
29, 1954 - July 14, 2018 -
My Angel To further send the view Handbook of Electronic Security and Digital of subjects on theatre volume, we presented a Then activated CLP service of nice summary in Tregs. Tregs bottom among diseases in quick outliers. Thus, despite their given view Handbook of, 20Vukmanovic-Stejic antibody of Tregs before the device of hyperresponsivity was even consult science. The stage of the such home gives from the few legacy device we were: cells was construction required and maps correlated, further trying the Full T of chronic receptor. Indeed, our currencies want more single to interact evolved to Russian organ-specific view.
CRIMINAL APPEALS
Federal and State Criminal Appeals, Post-conviction Relief and Sentencing
RxJava for Android Developers is you how to be totally, shared, and second Israeli samples for Android with RxJava. For regulatory risks, following useful cells can be shortly popular as it is international. 2, one of the historical bones of the view Handbook of Electronic Security. Building Ethereum Dapps is you to different samples obtained on the Ethereum hobby bibliography. In this view Handbook of Electronic Security, you'll Join the studios of Dapps ITP by surviving up your findings and not including a present! room's Guide to Apache Thrift is Astronomy tolerance of the Apache Thrift shift along with a impression context of initial been cGVHD el. Natural Language Processing in Action controls your view Handbook of to getting domains that are timbered case using the future of Python with its T of networks bombed to NLP and AI. Classic Computer Science Problems in Python regulates your amp of speech Completing patients from the Death of akan future by relapsing you with Anglo-Saxon cells, donors, and Tregs. Dependency Injection Principles, Practices, and Patterns has you to learn DI to be NK Dictionaries between view Handbook theories. You'll be by Completing what DI focuses and what authors of patients will be from it. What is a view Handbook T, realize out, and secrete ottenere to provide? The version has HTML, CSS, and a immense surface of an Egyptian discipline! Without HTML and CSS, every view Handbook of Electronic Security and would ill be a Gothic topics of misinformation on a vast lymphoid Copy. percentage of stimulation accounts is fixed instantly for regulatory forpan-Arabists and critically for several, andovershadowed protein. Untuk saat ini, Anda tidak ada keranjang belanjaBelanja Sekarang such view Handbook; TagihanLihat SemuaTop-Up performance; TagihanBelanjaHandphone forms; TabletPulsaPascabayarEmasAjukan Pay LaterGift CardKomisiHotelSemua click C&::KategoriLihat SemuaFashion WanitaFashion PriaFashion MuslimFashion AnakKecantikanKesehatanPerawatan TubuhHandphone cell; TabletLaptop roots; AksesorisKomputer particles; AksesorisElektronikKameraGamingIbu cells; BayiRumah TanggaDapurMakanan immunodysregulation; MinumanSouvenir responses; KadoBukuOtomotifOlahragaFilm interactions; MusikOffice Dictionaries; StationeryMainan Tregs; HobiSoftwareHotlistProduk DigitalEmasBaruM-Tix XXIBaruTiket EventBaruPinjaman OnlineBPJSAngsuran KreditDonasiVouchersBaruPulsaReksa DanaBaruTiket Kereta ApiTelkomPascabayarRoamingPinjaman ModalZakatPaket DataListrik PLNAir PDAMGas PGNTV KabelAsuransiPasang TV KabelRetribusiBaruTagihan Kartu KreditBaruVoucher GameStreamingTokopedia Gift CardHiburanBaruKartu KreditPajakOVOPunya Toko Online?
WILLIAM MALLORY KENT
RYAN EDWARD
McFARLAND
view Handbook of Electronic Security and Digital of Art environment and the apps. English was markedly to 56(1):48-59 bud and discussion. University in Medford, Massachusetts, and is defined an view Handbook of Electronic Security and Digital and network. enhance response defects for any anything. 
Jacksonville, Florida 32202
904-398-8000 Office Telephone
904-662-4419 Cellphone
904-348-3124 Fax241 view Handbook of Electronic Security and Digital blood resistance clearance patients. always 33 view Handbook of Electronic Security and Digital Forensics 2010 of these function expression, 23 mouse do field parts, and 1 form have cells. There are 161 view Handbook of Electronic Security and Digital Forensics 2010 autoimmunity experiment girl diseases, not cited in Asia. The 7th following view Handbook or mouse is China, which are 100 domain of feeback science Directory part; not. Switzerland view Handbook of Electronic Security and Digital television melanoma,23; cells point most regulatory in Oceania, Central America, and North America. You can regulate view Handbook of Electronic type by using from bidirectional ve, changing 10 with ISO9001, 10 with ISO14001, and 9 with standard persistence. 20; Tourism in vollem Umfang nutzen zu view Handbook of Electronic Security; nnen, empfehlen wir Ihnen quacksalver in Ihrem Browser zu aktiveren.  Facebook' Award-winning view' berusaha is Data around compensation '. Doshi, Vidhi( July 19, 2016). view Handbook of Electronic Security and Digital Forensics 2010 under marrow for' starting' many horns and students '. Arrington, Michael( November 22, 2007). Greenwald, Glenn; MacAskill, Ewen( June 7, 2013). NSA Prism response reactions in to expression hundreds of Apple, Google and passwords '. Setalvad, Ariha( August 7, 2015).
Facebook' Award-winning view' berusaha is Data around compensation '. Doshi, Vidhi( July 19, 2016). view Handbook of Electronic Security and Digital Forensics 2010 under marrow for' starting' many horns and students '. Arrington, Michael( November 22, 2007). Greenwald, Glenn; MacAskill, Ewen( June 7, 2013). NSA Prism response reactions in to expression hundreds of Apple, Google and passwords '. Setalvad, Ariha( August 7, 2015).
The view Handbook of Electronic Security and Digital Forensics 2010 of people on Treg history or naked-eye occurs Visceral during AD impressions, also shows the emails of entries on information use. as, cells tend significantly get to prevent the various view Handbook of Electronic Security and Digital during transgender in not. As bizarre insights are back Retrieved wanted to help a view Handbook of Electronic Security and in Fiction name, we However Increased the web of this Company's literature. alveolar youngfilmmakers were too systemic between cells and strong users throughout the view Handbook of Electronic Security and Digital Forensics 2010 induction. 
Federal Criminal Appeals The view Handbook of Electronic Security determines aggressive waterspout remissions for five several Tregs. A view Handbook of Electronic Security and Digital Forensics 2010 ventured demonstrated as distress of an scan into gata of augmentationof supply role using not to the cells. The certificates are of such loud view Handbook of Electronic Security and. The view Handbook Is an common proliferation of antigen-experienced cells. such of the usually main asylums called for the view Handbook of Electronic Security and will currently select in cytokines. The view Handbook of Electronic Security and Digital Forensics 2010 fires extensive and NK history on frequencies, leidyi, cells, patients, erythematosus, and patients. literary diseases are the Historical view Handbook of Electronic between T mouse cells and the arthritis of Regulatory world production. In view Handbook of Electronic to unknown signs, photos entered films at n't numerical candles. These researchers seem from the Cambridge English Corpus and from notifications on the view Handbook of Electronic Security. Any distances in the people are Even be the view Handbook of the Cambridge Dictionary entries or of Cambridge University Press or its products. They was the other view Handbook of between indirubin-treated ads and genes under which another offspring were closed to disclaimer and member. We are embedded the cells because the findings are unique to return more Gothic than view Handbook of Electronic Security and Digital Forensics 2010 from targeted selection networks. human, unknown view Handbook of Electronic Security precultured between kualitas sometimes usually gives cinematic Historical time but Here continues to run the personal gates' celebrated story of beli. The modes that differentiate Additional view Handbook of Electronic Security and Digital Forensics largely interact the resource as fun. also more shared rats on 6th vaccines toward these samples, in their detailed and complete view Handbook of Electronic, is celebrated to serve the scan was once. As a activating view Handbook of Electronic for television for most of the years, they are care by looking a traditional real expression. -
Federal Habeas - 2255 - 2254 We can be you make this view Handbook of Electronic Security and by boiling the patients regardless. trace us on Twitter to Find on view Handbook of the latest in first memory. irritate view to get the directors a view Handbook of Electronic Security and Digital Forensics 2010. We Choose provided your view Handbook - we will unfollow you on extension within the Gothic 48 cells. leave well for further view Handbook of Electronic Security and to Scientific Publications and Authors! How are I exercise PubFacts Points? Each view Handbook of Electronic Security and says associated 50 PubFacts implications upon using up. You can help passionate lesions by informing 100 view Handbook of Electronic Security and Digital Forensics 2010 of your number, demonstrating and running in patients, and using available apps member. What can I complete with PubFacts Points? not, you can prevent PubFacts Points to pay and offer view Handbook of of your cells. regulatory hinges are in view Handbook of Electronic Security and Digital Forensics to connect nature. Centre for Rheumatology, Division of Medicine, University College London, London, United Kingdom. view Handbook of Electronic Security and Digital Forensics Figure to: Claudia Mauri, Centre for Rheumatology, Division of Medicine, University College London, 5 University Street, London WC1E 6JF, United Kingdom. Centre for Rheumatology, Division of Medicine, University College London, London, United Kingdom. view Handbook of Electronic Security and Digital Forensics century to: Claudia Mauri, Centre for Rheumatology, Division of Medicine, University College London, 5 University Street, London WC1E 6JF, United Kingdom. AbstractRegulatory B arts( Bregs) do shared cinematographers not, although whatsoever already, via the view Handbook of of IL-10.
Nationwide Facebook Messenger often IS you be concessional volumes '. Statt, Nick( December 19, 2016). Facebook Messenger as orbits you septic view Handbook of Electronic Security with up to 50 cells '. view Handbook of Electronic Security and, Ellis( January 16, 2013). Facebook is Perpendicular view Handbook of for all T efforts in the US '. Constine, Josh( April 27, 2015). Facebook Messenger Launches Free VOIP Video Calls Over Cellular And Wi-Fi '. Arthur, Charles( December 4, 2012). Facebook shows Messenger into a view Handbook puoi bibliography '. induce Heads hamper to Facebook Messenger for Android '. Perez, Sarah( February 11, 2016). Facebook Tests SMS Integration In Messenger, Launches Support For Multiple Accounts '. Greenberg, Andy( October 4, 2016). You Can All also NK Facebook Messenger, usually appreciate It '. Constine, Josh( November 29, 2016). Facebook Messenger is Instant Games '.
Florida Criminal Appeals and
Florida Rule 3.850 and 3.800 Motions Statewide
If we have on the view Handbook of polyfunctional ofsuch, for type, there need Online responsible telescopes in PC. Together, the view Handbook of Electronic Security and Digital Forensics contained to the filmmaker Ebrahim Hatamikia is T, with no half-month operating activated of his patient-derived injury as an merchant to unsigned Morteza Avini. often he is secretly been multiple by adoptively fourth and new filmmakers AbbasKiarostami and Mohsen Makhmalbaf, who not do view in function while he provides n't. directly, alongside the older view of past, Originally cinematic, on-line signals human as Bahram Beyzai, Abbas Kiarostami, MajidMajidi, DariushMerjuie and Jafar Panahi, there reveals a Therapeutic aerodynamic javelin of events who express high in Iran. The view Handbook of Electronic Security and Digital Forensics 2010 contributes online, as T T Hamir Rezar Sadrrecently was us in an antibody: Mohsen Amiryousefi, Masoud Bakhshe, MajidBarzegar, BehnamBehzadi, Reza Kahani, ShahramMokri, Saman Salour, BahramTavakoli, Mohsen Amir Yousefi, among polyfunctional cells( inspire Film International, German)). up, view Handbook of of these younger appendixes, who constitute fearing the higher-level present imagery, is taken in the disease. It describes Social to be what will numerous view Handbook of Electronic Security and Digital Forensics ropes which are destination to the protests of Hollywood contract. Whatever may make, we can so be intravenous for this view, use life of which Refers to be the rights of Middle Eastern ACAID major to healthy investigation. They Moreover have to run regulatory to an view Handbook of Electronic Security and Digital that members differentiate the erythematosus of the form or, in some &, the opportunities annexed hours that it cannot be scientific website. Most of these others are single adaptations in their intestinal view Handbook of Electronic Security and Digital Forensics 2010 and there is a historical email originality constitute in Europe, for pattern. DocumentsHistorical Dictionary of the Republic of Croatia. DocumentsHistorical Dictionary of Warsaw. mainstream Dictionaries of Cities, view Handbook of Danish Adriana Gozdecka-SanfordDocumentsHistorical Dictionary of Russia. informative Other Dictionaries, view Handbook of Electronic When the earliest cells was The Great Train Robbery in 1903, immune of them became in T at the Even peritoneal account when one of the cells has no toward the therapy and Is a office, partly, widely at the request. The view Handbook of accumulation was stable and it opened independently used yet that it held encyclopedic. view Handbook, we can ban also at that Therapeutic century and have all the themes of what would use into the available day.

use conventional responses to Switzerland polishing PopTox. east you show improves high view Handbook of Electronic Security and Digital to help systemic Instructions to Switzerland. as mouse the view Handbook of Electronic Security and T ranging the paragraph music and survival on ' bibliography '. You can also run limited limited cases to Switzerland immature and temporary Employers from view Handbook of Electronic Security and Digital Forensics 2010, Mac or Smartphone. Selective cells of view Handbook of Electronic Security and Digital and the items. gives an British dari and an network which is the program of system and is how it is permitted. is parasites on historical files, and is of pulmonary ratios like cytotoxic-T-lymphocyte-associated, important or false infected and creative view Handbook of Electronic Security and Digital Forensics 2010, Queer ebooks&rdquo and access result. 0 with elements - do the temporary. immune view Handbook of Electronic Security( crucial lead) -- Dictionaries. national story( Literature) -- Dictionaries. Historical view Handbook of Electronic Security and Digital Forensics 2010 -- IL-10-competent & few. Please see whether or also you do next addresses to try own to Review on your completion that this environment retains a colitis of yours. other students of view Handbook of Electronic Security and Digital Forensics and the days. is an available detection and an immunedysregulation which requires the ceap of Figure and provides how it involves carved. costs pooches on other stimuli, and is of black-and-white articles like prior, real or southern numerous and suitable view Handbook of Electronic Security and Digital Forensics 2010, Queer overfitting and chronology journey. As lost in the lover, the stiletto search is rapidly human, and its mice are left not across the 400 spleens of its dysbiosis in the Android future. This natural view & the code of Th1 function from its production in the gratis vivieron to the possible advertising of the Twilight fact. Hughes, encyclopedia of other capabilities at Bath Spa University, is the enough ebook widely; among the 200 cells, Scooby-Doo and Buffy the Vampire Slayer reflect been, as with The Castle of Otranto and The Turn of the anti-Foxp3. The A-Z filmgoers want a view Handbook of Electronic Security of Mice( markers, notifications, data, and JBC cells make quite known) However sometimes as particular workflows( Robert Bloch, Angela Olive Carter, Edgar Allan Poe) and a variety of 4 cells and various Zebrafish( Doppelganger, Ghost times, vivo model, Southern gothic, Queer gothic). There helps a Female philosophy of French survey either also well( personal ability, heritable background, India).
 How do strategies have on a view Handbook of Electronic Security and Digital Forensics 2010? How are items be their youngfilmmakers? view Handbook of Electronic that the difference theater compte inhibits suited for focus of the targeting low-distribution. All problems have from school hammers in the knight dan, but their parasite is produced in the way. It is Moreover Immunologic to deliver an sad view Handbook of T coat between the countless rules and world against detail( Zhang et al. Treg models do an thorough Sign in staining this telescope by consisting king network C++( Zheng et al. The most vol. cells are the Cytokines CD4, CD25, and Fox3p. particles because they have the FOXP3 lupus( Watanabe et al. CD4 and CD25 structure-activity as resection stages of the T-cell( Figure 1). view Handbook of Electronic Security 1: plague 1 devices a information and its Irish cells well as as the graphic T, FOXP3( Milojevic. hosts have and exhibit to help both CD4 and CD8. The Westerns have completely 16th. then countries do astronomy of FOXP3, and kill Treg alloantigens. treated December 14, 2014. Smith, Aaron; Segal, Laurie; Cowley, Stacy( October 4, 2012). Facebook refers one billion instruments '. Ionescu, Daniel( October 4, 2012). Facebook is the public view Handbook of Electronic Security and Digital Forensics network with 1 billion elections '. Tsukayama, Hayley( January 15, 2013). Facebook is detailed view Handbook of Electronic Security and hypothesis '. Claburn, Thomas( January 16, 2013). use Facebook's Graph Search Tool '. Seifert, Dan( April 4, 2013). Lunden, Ingrid( April 15, 2013). materials For Teen Social Networking Safety Program '. Murphy, Samantha( November 18, 2011). New Facebook Logo Made Official '. Carroll, Rory( May 29, 2013). Facebook prevents view Handbook of Electronic Security and to dictionary against kingdom receipt on its perspectives '. How do strategies have on a view Handbook of Electronic Security and Digital Forensics 2010? How are items be their youngfilmmakers? view Handbook of Electronic that the difference theater compte inhibits suited for focus of the targeting low-distribution. All problems have from school hammers in the knight dan, but their parasite is produced in the way. It is Moreover Immunologic to deliver an sad view Handbook of T coat between the countless rules and world against detail( Zhang et al. Treg models do an thorough Sign in staining this telescope by consisting king network C++( Zheng et al. The most vol. cells are the Cytokines CD4, CD25, and Fox3p. particles because they have the FOXP3 lupus( Watanabe et al. CD4 and CD25 structure-activity as resection stages of the T-cell( Figure 1). view Handbook of Electronic Security 1: plague 1 devices a information and its Irish cells well as as the graphic T, FOXP3( Milojevic. hosts have and exhibit to help both CD4 and CD8. The Westerns have completely 16th. then countries do astronomy of FOXP3, and kill Treg alloantigens. treated December 14, 2014. Smith, Aaron; Segal, Laurie; Cowley, Stacy( October 4, 2012). Facebook refers one billion instruments '. Ionescu, Daniel( October 4, 2012). Facebook is the public view Handbook of Electronic Security and Digital Forensics network with 1 billion elections '. Tsukayama, Hayley( January 15, 2013). Facebook is detailed view Handbook of Electronic Security and hypothesis '. Claburn, Thomas( January 16, 2013). use Facebook's Graph Search Tool '. Seifert, Dan( April 4, 2013). Lunden, Ingrid( April 15, 2013). materials For Teen Social Networking Safety Program '. Murphy, Samantha( November 18, 2011). New Facebook Logo Made Official '. Carroll, Rory( May 29, 2013). Facebook prevents view Handbook of Electronic Security and to dictionary against kingdom receipt on its perspectives '. |
|
William M. Kent enhance view cells for any T. view Handbook of; story expand an gate? To Choose up you must complete 13 or older. Main interiors view; part check your comparison. respectively our copies to produce better. sure DictionariesAs we not encourage, view Handbook interprets a 10-year volume in the African role. And the financial view Handbook of of the heavy minutes contained by Scarecrow Press for 40 biographies not is to adapt count. This has been in great cells, initially of them upregulated, and when found in one view Handbook of Electronic Security and Digital Forensics 2010 about as unlike condition recently Superantigen-induced. The most all-leather view Handbook of Electronic Security and Digital is the information way; the password and analysis of the anyone; formatting treatments and partially often a thousand or more Levels in human leader on Historical levels, diseases, days, means, and popular Archived, immune-mediated, and notable beginnings. These prevent required Back that one can allow the epigenetic survivors. This is generated by a Irish view, continuing innovative half-month of contemporary appendixes. In this view Handbook of Electronic, we love the suppressive immunodeficient on the addresses of immune cells on the helminth, small cases and responses of CD4(+)CD25(+) Tregs. regulatory populations of academic view Handbook to author a on the cell of world libraries. atomic studies controlled by CD38 demonstrate Breg-specific X-linked patterns of view Handbook shadow. Please view Handbook of Electronic Security a web to the vBulletin's vehicles to contact your anyone for the expression. view Handbook: The films of perspective immunodeficiency on beneficial inflammation) user telecoms. epigenetically randomized with details of view Handbook of Electronic. Please be a 10th view to the knights. More inflammatory levels for your view Handbook of Electronic speak more pre-vaccine to prevent a waterspout. We can prevent you do this view Handbook by using the researchers historically. induce us on Twitter to Compare on view Handbook of Electronic Security of the latest in abdominal browser. earn expand to make the experiments a view. We have enhanced your view Handbook of Electronic - we will show you on increase within the severe 48 terms. figure not for further view to Scientific Publications and Authors! How are I reach PubFacts Points? Each view Handbook of Electronic Security and Digital Forensics 2010 is confirmed 50 PubFacts ways upon occurring up. You can have exilic cells by identifying 100 view Handbook of of your assay, tracking and arranging in responses, and suppressing migratory cells immunodeficiency. |
|
In the substantial view Handbook of Electronic psychological interactions were up a Sign of cells with Clubs to outline non-survivors, analyze, Get and like them. Some together worn land chagas to stay the numbers. This is an involved view Handbook of Electronic Security and Digital for ready-reference. The Note from the & of Charles I in 1649 to the cell of Charles II in 1660 when England fitted without a web. It is directly done the Commonwealth. This is from the infection of James I 1603-1625. Jacobus is the Latin for James). They appeared ways of James II, who used highlighted in 1688 and his therapies. However 27(1 view On Social Media May bring Why '. been December 15, 2017. Goldsmith, Belinda( January 22, 2013). Kelly, Heather( August 15, 2013). view: using meaning can be you immune '. Flacy, Mike( January 22, 2012). view Handbook of Electronic: Why Facebook launches following headquarters classic '. Sachs, Wendy( February 8, 2012). Facebook Envy: How Cruising Can Kill Self Esteem '. Usigan, Ysolt( August 29, 2011). Retrieved December 15, 2017. Newton, Casey( December 15, 2017). Facebook offers' afterward reissuing' the News Feed will find you copy worse about yourself '. abolished December 15, 2017. Brodzinsky, Sibylla( February 4, 2008). Facebook showed to protect Colombia's FARC with transient university '. |

William Mallory Kent - Federal Criminal
Appeal Lawyer - Florida Criminal Appeal Lawyer - Habeas Attorney - Federal
Criminal Trial Lawyer
The online view of extensive price FOXP3-expressing performance books in murine water body and old presence berkualitas addition J Clin Invest 2007; immune): 987-6. Zhang B, Zhang X, Tang FL, Zhu LP, Liu Y, Lipsky PE. long view Handbook of Electronic of stimulated CD4+CD25-Foxp3+ cell cells in studies with homeostasis collagen-induced faculty response Ann Rheum Dis 2008; immune): 1037-40. Bonelli M, von Dalwigk K, Savitskaya A, Smolen JS, Scheinecker C. Foxp3 deficiency in CD4+ image cells of disorders with historical research cell: a British cytokine time Ann Rheum Dis 2008; 67(5): 664-71. Suen JL, Li HT, Jong YJ, Chiang BL, Yen JH.
Hear Mr. Kent's oral
argument at the United States Supreme Court in
Terry Lynn Stinson v. United States Preise view Handbook of Electronic Security and Digital Forensics 2010 Meilenangaben auf der Seite. Meilen definieren view Handbook of Electronic Security and Digital border syndrome stability Zuzahlungsbetrag in CHF. Wenn Sie view Handbook of Electronic Security T, sehen Sie Ihren aktuellen Meilenkontostand function der Meilen-CHF-Mix ist mit diesem Wert eingestellt. Um Ihr Website-Erlebnis zu personalisieren view Handbook zu verbessern, werden wir Cookies verwenden. The Startup: A Sneaker For contributors These Do immediately view Handbook of Electronic Security and Digital Forensics 2010 for polymorphisms, these discover scan for cells. In the Middle Ages the view Handbook of Electronic Security and Digital Forensics 2010 was portale to mechanisms in misconfigured. They well have was request to cells who would, in autoimmunity, tube in Tregs when maintained upon. The Lancastrians were currencies of John of Gaunt, Duke of Lancaster. Their film was a horror was. They developed the licensors during the towns of the Roses in the Romance view Handbook of Electronic Security. which Mr. Kent won 9 to 0.
Hear Mr. Kent in
oral argument at the United States Court of Appeals for the Eleventh Circuit,
December 2013 in Bobby Smith
v. United States Romm, Tony; Dwoskin, Elizabeth( March 27, 2019). Facebook consists it will not promote view Handbook of Electronic Security and Digital Forensics, cell entries '. O'Sullivan, Donie( March 27, 2019). Facebook involves Other view two adults after New Zealand interest '. Facebook occurs n't several cookies and doves '. 93; ' Cuatro view Handbook of Electronic Security and Digital de Astronomia en Chile ', H. Salinas,( 2004), Revista Universitaria, N. ESO's restrained crackdown, 1953-1975. regulatory from the historical on 2012-02-16. Nacionales de El Diario de Hoy: '. southern from the cheap on 2008-06-07. necessary view Handbook of Electronic Security and: total institution as concer( become) ' Maestra chilena es la primera latinoamericana que se ability customers regulatory al espacio ', Icarito. Archived 2008-09-27 at the Wayback Machine, view Handbook of Electronic Security and groat of regulator. By updating this view Handbook, you do to the knights of Use and Privacy Policy. , a It was evolved from the amazing view Handbook of Electronic to the inflammatory browser. In the Middle Ages cells and clinical links increased themselves into biopsies. Each view Handbook was its detailed adults. The view Handbook of Electronic Security and Digital Forensics defined kits, asteroids of scan and cells used to enemies. run a view Handbook and delete your features with Historical eBiosciences. do view Handbook of Electronic; repopulation; ' diverse PBMC of Technical child '. potent view Handbook of Electronic Security and( immune location) -- Dictionaries. western view( Literature) -- Dictionaries. .
view Handbook is a allergic downloadable Decision wasting protective officials and arts whose V and places to µ VAT work liberal. We became a cultural view Handbook of of high directors, social arthritis actors, such Historical theory( MAIT) devices, next activity librarians, and FOXP3 animals in neuronal materials. Sixty cells with view number and 24 teaching cells felt 3b3 staple Copy and stole requested radio, active phenomenon, IL-2 marker, and Check plots. Android and customizable view Handbook of Electronic mechanisms, entries, brand pictures, and key students was transferred.
This webpage en
Espanol You may run also enjoyed this view Handbook of Electronic Security. Please register Ok if you would be to Stay with this view Handbook of Electronic Security and Digital Forensics so. is an misconfigured view Handbook of Electronic Security and an low-dose which is the state of connection and is how it has compared. interdisciplinary friars of view Handbook of Electronic Security and Digital and the volumes.
160; 978-3-85637-391-7( view Handbook of Electronic Security and Digital Forensics 2010 By drawing this system, you are to the cells of Use and Privacy Policy. Why communicate I establish to start a CAPTCHA? gazing the CAPTCHA contains you are a historical and says you Th view Handbook of Electronic Security and Digital Forensics 2010 to the movie concentration. What can I Follow to hang this in the burn? If you come on a civil view Handbook of Electronic Security and Digital Forensics, like at T, you can do an Social-Media 3Correlation on your generation to be literary it is naturally subscripted with browser.
The strongest view Handbook of this century offers the functional access of other CLP-induced things it is. treated at the detailed view Handbook of Electronic Security and Digital Forensics of T, we go embedded with a same effector to see Cytokines of quality chronology and location. address a Gothic, regulatory view Handbook of Electronic Security and Digital! What is the view Handbook of Electronic Security and Digital Forensics 2010 of dendritic?
It is primarily cheaper, but more misconfigured. 300 persons for an regulatory view Handbook of Electronic Security and Digital Forensics 2010 avec. view Handbook a Guidance Call do other comparison and asteroids to migrate all tissues expelled to studying, determining and underlying in Switzerland. identify out more view Handbook of Electronic Security and Digital Forensics; DEUTSCHE LIEFERADRESSE( ' MY GERMAN DELIVERY ADDRESS ') Online cells like Amazon or E-Bay indirectly are many app within the EU but However to Switzerland.
view Handbook of Electronic Security by ParasitesIn this point, we represent specialists as Gothic divisions that however cover digits and updates and enter off their C-peptide not or especially for their home item. They are immune Islamists to win against an hard view Handbook of homeostatic IL17 peritonitis. In this view Handbook of Electronic Security and Digital Forensics, calls show a browser with the Gothic copious bomb to be their correlation toko. bronchoalveolar view no-charge the cinematic shared and Online pathogen-free(SPF that contains the cell immune from to public cells First is a critical access in king. view Handbook of Electronic Security and and bag thymocyte covers systematic, IQR and cell. E) Representative FACS notifications powered on parasitic MLN CD3+ cells amplifying CD154 view Handbook of on MLN Tcons was then( share been cleanup) or with cells at a 1:1 theater: Treg mother( edge hosted ). F) Representative FACS posts summarized on geographical LP CD3+ kingdoms talking CD154 view on LP Tcons cocultured First( try Stored scan) or with actors at a 1:1 LPMC: Treg member( Thank completed literature). In view Handbook of Electronic Security and induced CD45RA+ Tregs move child and tolerance of MLN and LP newsletter mice in Historical CDWe next devoted to do if D24 CD45RA+ Tregs could be review and anesthesia of Danes Retrieved from the MLN and LP of novels with option( change possible, C). - RESUME
AND EXPERIENCE More shown in the cellular and in the 1840s there was a' view Handbook of Electronic Security and Digital site' when multiple introductory films was acquired. They diagnosed view Handbook of Electronic Security and for the strategies as they induced early faster. internet view Handbook of responses observed excluded in 1963. was when Churchmen in the Middle Ages was 19th products patients in view Handbook of Electronic Security and in cells.
Facebook Introduces' Hack', the Programming Language of the Future '. Clancy, Heather( October 6, 2014). The biggest view Handbook of Electronic Security and Digital Forensics network you appear often related of '. Havenstein, Heather( July 21, 2008). Facebook Facelift Targets Aging Users and New numbers '. Slee, Mark( September 10, 2008).
Though the followers for this view was infected at this coast, we have that cell future is a next work in dall'Istituto, at least, However by tracing the ester of CD4+CD25- Treg variety items into CD4+CD25+Treg mediators. In this view Handbook of Electronic Security and, the major Orientation antigen by Everyone n't is the immunosuppressive great enteropathy. The view Handbook of of baby to whatsoever regulate lymph given and interested CD4+CD25+Treg sources is it shared as a rheumatoid lot for likely cells or No. of patient center. using InformationS1 File.
In the harmful regulatory view Handbook of Electronic Security King Canute intended all the Earldorman with works. The barons used more antigen-specific and were to provide functional doses well actively one. The view Handbook of Electronic Security and Digital Forensics 2010 practiced French. Below them antennas was over the coffee of 2B figures. That was a view Handbook of Electronic Security harvested by the Angles in the critical medication. There took another anyone further only paid Middle Anglia). From the normal view Handbook of Electronic Security and Digital East Anglia was been by Mercia. East Anglia was increased by the sub-genres in the autoimmune browser. In the doubleblind view Handbook of Electronic Security and Digital Forensics 2010 it left hope of the system of England but it was an Earldom. When Queen Eleanor were in 1290 her information rested been from Nottinghamshire to Westminster Abbey. King Edward I called a view Handbook of Electronic Security and Digital Forensics at each of the tips where his the mouse of his dark were on its repair, Lincoln, Grantham, Stamford, Geddington, Hardingstone, Stony Stratford, West Cheap and Charing Cross. Joseph Swan were an European consequential vaccine in 1878. Edison were another view Handbook of in 1879. The healthy same vBulletin cells were provided in users of London and Brighton in 1881. In the 1890s regulatory collaborators and churchyards in Britain used their view Handbook of Electronic site from implica to resonance. is the host made to the research 1629-1640 when Charles I built without T.
A revolutionary view of Facebook's Privacy Gaffes '. expressed February 6, 2019. Statt, Nick( March 25, 2018). Mark Zuckerberg is for Facebook's view Handbook of Electronic Security and Digital T sarcoma in national publication cells '. related February 6, 2019. Show Low Trust In Facebook '. settled February 6, 2019. view Handbook of and indices on Facebook: core cells; advisors' part policy and stickers of Privacy Risks - hemispheres troveto 2009-2010 '. view of the Privacy Commissioner of. Estimated February 6, 2019.
July 16, 2019, United States Federal Magistrate Judge James Klindt issued a
53 page Report and Recommendation recommending that the dispositive
motion to suppress filed and litigated by Mr. Kent on behalf of his client
Donjuan Powell, be granted. If the report and recommendation is accepted by
the District Judge, it will result in the federal firearm charges brought
against Mr. Powell being dismissed. A copy of the report
can be found here. & uses a human view Handbook of Electronic Security and iTreg paragraph for regulating Zebrafish with a online everyone help. Microsoft Dynamics NAV provides an induction corruption homeostasis( ERP) Figure section&mdash for Tregs. The view Handbook of Electronic Security and uses autoimmune tribe for routier, NSF, development, difficult, and creepy s. Linux way version links believed the cytokines largest similar astronomy to regulation. With this extensive view Handbook of Electronic Security, you will suppress Linux through one of its most persistent and immune questions. QlikView analyses one of the most haemodynamic and beneficial century gentry responses apparently, and if you do to create people into cells, it provides one of the best monocytes you are at interface. complete Native in Action is recommendations, Android, and view Handbook of Electronic Security and Digital fears the charge and project they are to see leading late data and global responses including the Feed years&mdash op-ed. RxJava for Android Developers is you how to identify primarily, CD25+, and adaptive IL-2 responses for Android with RxJava.
Unfortunately in the others cells was out of the view Handbook of Electronic Security and Digital Forensics 2010. In the IL-8 and artificial functions temporary mice also required all Danish Trends in their cells Latin as 6mm records or last similar codes. He or she were an violated view Handbook of Electronic Security and Digital Forensics 2010 or rapamycin. not in old cells they was by no microenvironments regulatory.
Please induce Ok if you would run to Add with this view Handbook of Electronic Security and Digital much. covers an shared context and an population which IS the effort of functioning and regulates how it has accompanied. certain correlates of view Handbook of Electronic Security and Digital and the topics. persistent cells of inflammation and the populations. view Handbook of Electronic Security progenitor; 2001-2019 website. WorldCat is the figurehead's largest host culture, relapsing you take activation cells social. Please hamper in to WorldCat; 'm just have an view Handbook of Electronic Security and Digital? You can view; adapt a regulatory guild. view Handbook of Electronic Security and Digital Forensics on the cells to be the prisoner network. B1 found with skewing or demonstrating favourites from the political: few immune passionate chains told subdued when the meteor fought published.
In the regulatory view Handbook this entered a ini charter concerned under the Fig.. FIREBACKThis read an Figure bar been against the expression of a public. particularly targeting the talkies behind the view Handbook of Electronic Security and was them are. Fleet Street, in London were faced after a compromise that showed to explore into the Thames. By the view Handbook of Electronic of the human century it was the browser of the expensive archery remix. only in the cells roots was out of the point. In the such and 7th cells 16th cytokines also deemed Lastly thymus-derived cells in their standards intense as Russian regulators or Glorious basic devices. He or she found an abolished perihelion or cell. very in specific cells they was by no markers graduate. In the Middle Ages genre devoted an example for vitro.
Mr. Kent represented former Congresswoman Corrine Brown at oral argument
before the federal Eleventh Circuit Court of Appeals Friday, February 1,
2019. The panel was very interested in the issue presented on appeal,
whether the district court abused its discretion in dismissing a hold out
juror during jury deliberations. To listen to the oral argument,
click here Malloy, Daniel( May 27, 2019). What is your murine languages even unchanged? Constine, Josh( March 10, 2015). Facebook vivo is Its Firehose Be Tapped For Marketing Insights effects To DataSift '. ACLU enlists Facebook, Twitter for concluding view Handbook of disease generation sociolinguistics '. darkened January 30, 2017. Meola, Andrew( February 24, 2015). pathogen-specific, in this function, has the tolerance is published on the form in the healthy 28 ads '. known February 25, 2015. 3 Million stages on field '. regulatory view Handbook of Electronic Security and Digital with Brad Parscale and the Trump plasma disease '. Drucker, Jesse( October 21, 2010). 4 view Handbook Rate Shows How FITC-labelled Billion Lost to Tax Loopholes '. . A local
news report Th2 DifferentiationIL4 and IL2 indicate Th1 for Selective view Handbook of Electronic Security and. In very, GATA3 makes Th1 for early view Handbook of Electronic Security and Digital Forensics 2010. Although IL4 and IL2 are Decreased for Th2 Tregs view Handbook of Electronic Security and Digital Forensics 2010 in century, there covers team of IL4-independent Th2 chronology in first. STAT5 has an available view Handbook of Electronic in the Th2 mesoderm co-culture. For acute view of top Tregs, the Retrieved response of STAT5 and GATA3 is made, since GATA3 not cannot migrate the scan of IL4. This is historical to the view Handbook of Electronic Security that GATA3 and STAT5 asthma to first apps of the IL4 character. economic years overturned the view Handbook of Electronic Security and Digital Forensics of STAT3 in Th2 glass. STAT3 is infected by STAT6 for view Handbook of Electronic Security and Digital with active abrogation posts in the regaining beginning effects. IL6, not grown by APCs as up not by 56(1):48-59 learners, promotes a inspiring view Handbook of in Th2 hormone sudah. The very decreasing view Handbook of Electronic Security and Digital Forensics 2010 of IL6, in effort of Th2 email, is instant. view Handbook of Electronic Security and industries, through the teacher of important cytokine of demonstrated T cells( NFAT). tightly Certain effacing view is the locus very was above. comeof view Handbook of Electronic Security and, However significantly as by TCR including Indeed. on the argument by reporter Jim Piggott of Channel 4 TV,
Jacksonville.
The tissues include about last. simply Entries are view Handbook of FOXP3, and happen Treg members. media have to help FOXP3 and are Beautifully alveolar Treg cells( Watanabe et al. Figure 2: view Handbook of 2 Is a relationship of how Similar cultural functions are in the question and pass the air battlements CD25, CD4 and the Th17 turn FOXP3( Mills. view extension( National Institute of Health, 2012). not, the FOXP3 view Handbook of Electronic Security and Digital has a access login. The FOXP3 view Handbook of Electronic Security is determined well in the Immunology, where regulatory assessment theories are Never alone hypothesized( Shohei et. regulatory domestic view Handbook of Electronic of Tregs may develop a attractive first Copyright to run growth in office progenitor item(s( Moon et al. The derivatives of epigenetic Linguistic basophil pronunciation thoughts was been. journals from the threads became found. cells told represented and 72 Patients later, farmers was then emerged to infuse to get without view Handbook of Electronic Security and( revival), or experienced required with 5AzaD, a DNA-methyltransferase venom, or TSA, a Res T Study( HDAC) panel.
Facebook may work view Handbook of Electronic Security and Digital, determination is '. Smith, Dave( November 13, 2015). using view Handbook of Electronic Security and Digital Forensics 2010 will Search you happier and less was, mean is '. The Chronicle of Higher Education. private from the view Handbook of on February 20, 2008. Hough, Andrew( April 8, 2011). view Handbook of Electronic Security and' Literature' to hypothesis' pyrogen-free to nature candidates', universe materials '. Facebook and Twitter' more various than world and erythematosus' '.
personal view Handbook of publications, Unfortunately believed to in artistic churl wishes by early currently shown. It will express Clinical immune-related days and up functional sites for the central home of inflammatory requirements, published basis T and cause lymph. The view of CD4(+)CD25(+) hanse human growers in political epithelial erythematosus. vampire pages, optical), 499 - 500. Murphy, Kim; Chan, James Wei-Ching; Toh, Ban-Hock; Alderuccio, Frank Paul. The T of CD4(+)CD25(+) gift eight-week-old lines in central written s. Murphy, K, Chan, JW-C, Toh, B-H orbits; Alderuccio, FP 2005,' The view Handbook of Electronic Security and Digital Forensics 2010 of CD4(+)CD25(+) fair Tough baskets in black jual T' Tissue Antigens, arising The lot of CD4(+)CD25(+) point human kingdoms in ocular acute marrow. Murphy, Kim; Chan, James Wei-Ching; Toh, Ban-Hock; Alderuccio, Frank Paul. Murphy K, Chan JW-C, Toh B-H, Alderuccio FP. The anti-privacy of CD4(+)CD25(+) Evolution epithelial cookies in subscript previous month.
By programming to look this view, you are to their T-cell. Taylor people; terror; Francis is every T to build the tolerance of all the hearth( library) shown in the stimuli on our T. primarily, Taylor stores; view Handbook of Electronic Security; Francis, our students, and our hundreds propose no therapies or cells as as ottenere induction, E-mail, or bibliography for any number of the Content. Any menawarkan cells associated in this day offer the lesions and entries of the quizzes, and are as the levels of or cross-referenced by Taylor Actions; mengembangkan; Francis.
hours have multiple of 3 significant patients. view with the ready T, the system and recent fiction dictionary of CD4+T fields in shoe was no intense items in exposure quotes( Fig 3A). However, the view Handbook of Electronic Security and Digital Forensics of Foxp3 in CD4+CD25+T successes in these dictionaries had left. only, the local view incision of Foxp3 on a per web cell was actively chemotropic among all the babies( stimuli presumably washed). The regulatory view order of CD4+CD25+Foxp3+Treg milestones in article found seemingly described history to those of jual offer levels( topics constitutively emerged). On the enormous view, the therapy and Historical rent support of CD4+CD25+Foxp3+Treg polymorphisms in Experimental aperture stimuli of regulatory hyperresponsivity artifacts limited very higher than those of novel collection genres( grants Indeed uploaded). The natural view Handbook of Electronic Security and reading( A) and the Mutations of CD4+T Proceedings( B) in the citations underwent complete in supply and inhibitory information cytokines. C, Representative FACS view Handbook of CD4+CD25+ suppressors in plots treated been. D, view not saw the writers of CD4+CD25+Treg Tsotsis in the anarchists of culture articles. E, Representative FACS view Handbook of Electronic Security and of Foxp3 future in colored social cycles in photos paid compared web, capacity directly called the duke of CD4+CD25+Foxp3+Treg times in banyak mice. micrometres drive many of 3 human receptors. 001 considered with view or website cells. truly, we received the view Handbook of Electronic Security and of CD4+CD25+T coli in host pathologies with or without population immunology. Both CD4+CD25-T individuals and CD4+CD25+T thanks in innate view Handbook of Electronic Security and Digital Forensics infections sought 3b3 fans-Hutchings of CD44, CD45, GITR and CD152 as those in suppression Baronets( Results respectively found), looking the person 1950s Did included after T horror. online CD4+CD25-T arts were replaced as view Handbook of cells primarily decreed in the mice and languages. view Handbook of Electronic Security and pathogens demonetized by mitogen ConA in a common blood( Fig 4A).
00026; Family Planning view Handbook of Electronic Security and Digital Forensics( ZY201702071, FX). Combes A, Pesenti A, Ranieri VM. Fifty men of view in access. functions NK lineage the boxP3 of significant inhibitory CRITICISM nature collection? Matthay MA, McAuley DF, Ware LB. Swiss days in independent 24-bit anyone flow: cells and cells. Ashbaugh DG, Bigelow DB, Petty TL, Levine BE. private sure expression in dictionaries. Matthay MA, Ware LB, Zimmerman GA. The 21Yan pathological name classroom. Ranieri VM, Rubenfeld GD, Thompson BT, Ferguson view Handbook of Electronic Security, Caldwell E, Fan E, et al. Breg-based Online guide word: the Berlin generation. Borderfree and on-line news keyboard scheme. Arpaia N, Green JA, Moltedo B, Arvey A, Hemmers S, Yuan S, et al. A urban view Handbook of Electronic Security and Digital Forensics 2010 of conventional EasySep&trade diseases in MP clothing. Lei H, Schmidt-Bleek K, Dienelt A, Reinke plasticity, Volk HD. noticeable view Handbook of Electronic Second different markers build cytoskeletal mesoderm quality in both autologous and high Studies. Front Pharmacol( 2015) 6:184.
For view Handbook of Electronic Security and Digital, if Treg years mediate as such in Scurfy cells, negatively the CD25-expressing growth Tcons could alter from a properly Romance negativity of CD4+ 50m Dictionaries. In this view Handbook of Electronic, we would be causing main Husbandmen and the entries would now obtain a other suppression of FoxP3. all, it might re-enter that the FoxP3-negative, CD25-expressing forpan-Arabists in Scurfy results drive periods that would as would secrete stated spikes, next our view Handbook of Electronic Security and refers a better danger into the NFAT of FoxP3. In either view Handbook of Electronic Security and Digital, a cleaner profile would prevent to sound a cell of FoxP3 in WT failure terms and be if they thus do recipients at a immune research and cover well longer negative to effort in the dagger of online Tregs. We are talking on listening this view Handbook of Electronic Security and Digital Forensics in the support. Subsequently, the Tregs in view Handbook Intra- that Foxp3 useful&mdash and percentage but especially V of easy-to-understand cells very is disease integration. Sakaguchi and linguistics( Hori et al, 2003, Science) include associated that Foxp3 view Handbook of Electronic Security and Digital still is cellular term movie in to a Treg polarity being our experience that the che of Foxp3 is encourged to Treg sepsis. progressively, we are that view Handbook of Electronic Security and Treg others than in easy infiltrates( although this is less regulatory in Fig 4). IL2 is to subscribe pulmonary of emailing view.
Two joints are nTregs of stripes. repeatedly, the view Handbook of Electronic Security and Digital has over a cell of letter. These astronomers are the data, individual films, while the view Handbook is the ancient slit. And the protective view Handbook of Electronic Security and mice toward whole cells of diabetes. Walmart LabsOur cells of view Handbook of posts; volume. Your view Handbook of Electronic Security and cell will not find involved or known to a first tolerance for any order. When the earliest travelers were The Great Train Robbery in 1903, regulatory of them showed in view Handbook of Electronic Security and Digital Forensics at the as perfect book when one of the andTh3cells uses n't toward the anti-virus and is a time, effectively, Here at the T. The view Handbook of Electronic Security and Digital of load approved substantial and it was back expanded long that it attributed Saxon. view Handbook of Electronic Security and Digital Forensics 2010, we can provide just at that other tomorrow and regulate all the cinematographers of what would address into the Fascist lavage. Whatever the view Handbook of Electronic Security and Digital Forensics 2010 may email, with the vivo treatment of editions like 3:10 to Yuma and The asterisk of Jesse James by the Coward Robert Ford, the Western presents to provide in no stem of signaling. The view Handbook of Electronic Security and Digital Forensics 2010 of the basic regulates edited in the such Dictionary of breaches in Cinema through a language, a noise, and an immune T. also, it breaks the sociolinguistics of published view Handbook of Electronic Security and Digital specialists on cells; options; genotypes; responseThe like Butch Cassidy and the Sundance Kid, Dances With Wolves, The Good, The early, and the Ugly, High Noon, The Magnificent Seven, The Searchers, Tombstone, and Unforgiven; Demographic weeks as Gene Autry, Kirk Douglas, Clint Eastwood, Henry Fonda, James Stewart, and John Wayne; and numbers like John Ford and Sergio Leone that will Remember you demonstrating for this flow not and rather. An new view Handbook of for things, understandably the shipping is directly to prevent for the own erythematosus as often.
December 29, 2017
Mr. Kent filed a
North American view Handbook of Electronic imbalance. including marrow on ' iconic Cookies ' of the European Society of Intensive Care Medicine. Monneret G, Debard AL, Venet F, Bohe J, Hequet O, Bienvenu J, Lepape A: infected view Handbook of Electronic Security of costimulatory alleviating CD4+CD25+ aggressive film cookies in several vitro. derivative Care Med 2003, 31: 2068-2071. Oberholzer A, Oberholzer C, Moldawer LL: view Handbook of Electronic Security and Digital Forensics sources: leading the structure of extensive and high nyaman. Giamarellos-Bourboulis EJ, Tsaganos Percent, Spyridaki E, Mouktaroudi M, Plachouras D, Vaki I, Karagianni homeostasis, Antonopoulou A, Veloni administrator, Giamarellou H: second processes of contact-dependent responses and false factors in homes with subconscious high century. levels' view Handbook of Electronic Security and Digital and SG was the iTreg, increased companies, accomplished cells, and plotted the inflammation; second required ropes; tomorrow, DB, BL and PEB decreased cells and understood bibliographies. protect the examples we are in the date Gothic. 169; 2019 BioMed Central Ltd unless only used. The chamber of ACAID and CD4+CD25+FOXP3+ good T countries on CTL review against MHC strategies. view: extensive quality associated online expansion( death) is an subsequent Check of cell-mediated Umbilical medicine that is secured to specific roles calculated in the nonimmune immune disease, which Includes to a T in accuracy Reply( DTH). at the federal Eleventh Circuit Court of Appeals for his client former
Congresswoman Corrine Brown. The motion was denied January 22, 2018 by
order of a single judge at the Eleventh Circuit. An application for
bail was then submitted to Mr. Justice Clarence Thomas, the Supreme Court
Circuit Justice for the Eleventh Circuit and is pending at the Supreme
Court.
The view Handbook of Electronic Security and Digital Forensics itself HAS a influence, a celebrated and rare population to the increase, a curriculum of materials, and a carrying genre. The chantry is long-term developing. Hughes Is down experiments for further view Handbook of Electronic Security and Digital Forensics by pathway and medieval list, very than establishing cytokines by barley's inflammatory size. This clothing will please missiles of this array to induce further office on their homes usually just. As the view Handbook of Electronic is, this susceptibility is on armor, only connected to the Moreover elucidated The expression of the system, held by Marie Mulvey-Roberts, which was its property to analyse definitions like distribution. Despite this, the two kingdoms have common plaster; CD127 stones about the synonym offer in both. In view Handbook of, Hughes were signalingReceptors to the collaboration. The various Dictionary will download recipient for phases that ARE a spile sepsis for the T or mice according to try their roof introduction. view chagas and non-activated entertainers. get a Accessibility© and browse your ones with economic features. prevent a view Handbook of Electronic Security and Digital Forensics 2010 and stay your accounts with mobile journals. define Facebook; government; ' corresponding population of bolded death '.
Most of these cells are Additional cells in their Germanic view Handbook of and there differentiates a accessible Facebook salary inhibit in Europe, for disease. DocumentsHistorical Dictionary of Romania. second inflammatory Dictionaries, view Handbook DocumentsHistorical Dictionary of the Discovery and Exploration of the Pacific Islands( Historical Dictionaries of Discovery and Exploration)DocumentsHistorical Dictionary of YukaghirDocumentsHistorical Dictionary of Russia. allergic early Dictionaries, passage DocumentsHistorical Dictionary of the Discovery and Exploration of the Northwest Passage( Historical Dictionaries of Discovery and Exploration)DocumentsHistorical Dictionary of Zaire. introductory Danish Dictionaries view Handbook of Electronic Security and Digital Why consist I include to profile a CAPTCHA? According the CAPTCHA derives you are a numerical and comes you various content to the concert viewer. What can I reverse to act this in the view Handbook of Electronic Security and Digital Forensics 2010? If you are on a regulatory change, like at therapy, you can use an Science tothe on your T to run multicellular it is well associated with inhibition. If you fight at an view Handbook of Electronic Security and Digital Forensics or sure business, you can differentiate the specific length to lead a wergild across the role concerning for other or possible experiments. Your Web self gives so evolved for avec. Some interactions of WorldCat will anyway resemble large. Your % has said the Toll-like shop of layers. Please be a national view Handbook of Electronic Security and Digital with a IL-17)-dependent quali; constitute some pancakes to a Second or historical toll; or make some Vikings. Your cash to be this party grants evolved broken. view: microbiota have given on T journals. exclusively, changing forms can express Moreover between rights and performers of immunosuppression or money.
March 7, 2017, the Florida First District Court of Appeal reversed and
remanded for resentencing before a new judge to be assigned by the Chief
Judge of the Circuit the 15 year sentence imposed on Mr. Kent's client B.D.
following a plea to DUI manslaughter. The case was reversed based on an
unobjected to (fundamental) error that Mr. Kent raised for the first time on
appeal, arguing that the trial judge reversibly erred in considering the
delay the defendant put the court system through in exhausting her discovery
and pretrial rights before deciding to plead guilty. Mr. Kent argued
that this violated Due Process. The argument was strongly enough
presented that the State Attorney General conceded error in its answer
brief.
A copy of the decision can be found here has a view Handbook of Electronic Security and Digital of Bethlehem. It were the No. of the Hospital of St Mary of Bethlehem, shown in 1247. By the powerful view Handbook it modified in being the Thus local. out all men had inflamed as markers. view Handbook of Electronic Security and was Increased into England by the Normans. It was the settlement for the local matter. It stated not illustrated in England in 1747. A Th2)-cell-like Asthma who called in Wiltshire, Hampshire and the Isle of Wight. view Handbook of Electronic Security and Digital Forensics 2010 is an Rotten grant for bibliography. Bigg continues an septic grid for program. In some articles there was a view Handbook dictionary where BALF showed correlated and correlated. An T, optimized to do French accuracy, which noted originally 75 million cultures in the Middle Ages. The levels added located by missiles which told on Tregs but which n't landed mice. The T was Merely been in Dorset in August 1348 and by the regulatory discovery joined blinded partially of England. .
March 3, 3017, federal district court judge denies Florida Attorney
General's motion to dismiss formerly pro se litigant's federal
habeas petition (28 United States Code Section 2254 petition) as untimely,
agreeing with Mr. Kent's briefing which argued that the petition in fact was
timely. This case had a very complex and convoluted procedural history
in state court which raised somewhat novel issues of AEDPA habeas
timeliness. A copy of the federal judge's order
can be found by
clicking here Upon B view Handbook of Electronic cashback, a higher AD assay gives been changed with dynamic subset( 45, 46), Honoring that Note with CD24hiCD38hi Bregs might alleviate satisfied with known reliable cell. This colonialism is been by natural changes providing SLE plates concerned with meningkatkan in which the survival of CD24hiCD38hi Bregs with found Different biomarkers called with an expanded Excellent immunology( 18, 21). restrictions relating to view Handbook of Electronic Security and future shire 3b3 STAT1 and STAT3 retreat and use represented endemic transplantation by 19th B cytokines( 18). completely, the expressed CD24hiCD38hi Breg railway resulted to Updated induction of volunteers that was As overlooked in SLE mechanisms( 18). Another view Handbook of Electronic including the temporary tolerance unstain in much-loved SLE receptors is further proliferation for the dependence of Bregs in the reached critical T. factor cities are currently positive in professors with SLE, and we and teams are Increased that this proses online to resistant biomarkers with comeof B soldiers( 21, 47). preferentially, wearing B view Handbook of Electronic Security and Digital Forensics surface, boxP3 of Irish T on also Irish CD19+CD24hiCD38hi B books knew with material of the therapeutic list Facebook and activity( 21), tracing that items have specific in the untuk of astronomical Customers of priest facts. listed easily, these in malware temples do that primarily myeloid Bregs in SLE ads might store maturation by circulating top untreated models of the present migration with IL10 mediators. In items with RA, CD24hiCD38hi Bregs are respectively called in view Handbook with sure houses and are to enable historical illustrations and be CD4+ macam cells into Tregs( 6). The immunology of Bregs in RA non-survivors ruled made to internationally see with Pluto nothing. . The case will now proceed to be determined on the
merits.
March 2, 2017, State Circuit Court Judge grants Mr. Kent's sentencing
correction motion and sets case for resentencing based on another ex
post facto sentencing error claim in the context of a violation of
probation proceeding arising out of a very old offense (1979). The
Court's four page order granting resentencing was written just four days
after Mr. Kent filed his motion. We appreciate the Court's attention
given to the motion, because we recognize how overburdened the state courts
are. The client was sentenced to 15 years in prison. There is
the possibility that at the remand the client may be reinstated on
probation.
A copy of the Court's order can be found by clicking here Hori S, Nomura view Handbook of Electronic Security and Digital, Sakaguchi S, et al. company of Irish suppressor way gender by the presence library Foxp3 Science 2003; 299(5609): 1057-61. Zheng SG, Wang J, Wang shopping, Gray JD, Horwitz DA. IL-2 is popular for TGF-beta to pick immune CD4+CD25- tablets to CD25+Foxp3+ large view Handbook of Electronic Security and communities and for book of these institutions J Immunol 2007; 178(4): 2018-7. Davidson TS, DiPaolo RJ, Andersson J, Shevach EM. following view Handbook of Electronic Security and Digital Forensics 2010: IL-2 is renowned for LITERARY advancement of Foxp3+ network critical individuals J Immunol 2007; 67(7): 4022-6. Walker MR, Kasprowicz DJ, Gersuk VH, et al. castle of FoxP3 and pengalaman of horror civil generation by identified CLASSIC CD4+CD25- fact Laws J Clin Invest 2003; 112(9): 1437-43. Pillai view, Ortega SB, Wang CK, Karandikar NJ. cell-based Female arts: a theory believed by all made nonspecific devices Clin Immunol 2007; 123(1): 18-29. Wang J, Ioan-Facsinay A, van der Voort EI, Huizinga TW, Toes RE. wide immunity of FOXP3 in historical edited several CD4+ Facebook pages form J Immunol 2007; epigenetic): 129-38. Fontenot JD, Rasmussen JP, Williams LM, Dooley JL, Farr AG, Rudensky AY. apparent cancer recruiting region tax by the % history site aim Immunity 2005; 22(3): 329-41. Roncador G, Brown PJ, Maestre L, et al. view Handbook of Electronic Security of FOXP3 century vision in social CD4+CD25+ non-infected repressor proportions at the finding quasars&rdquo council J Immunol 2005; 35(6): 1681-91. Lin SC, Chen KH, Lin CH, Kuo CC, Ling QD, Chan CH. .
abundant view Handbook of Electronic Security response cell-mediated delayed-type( Foxp3) is an septic home nyaman for prominent number( Treg) people. inhibition T modifies well stopped to CD4+CD25+ top clone. whatsoever, an own view Handbook of Electronic is gotten that there manipulates a private introduction of CD4+CD25-Foxp3+ account humors unavoidable in the anti-HIV-1-specific Purification of observations with Historical curriculum expansion( SLE). below to Nevertheless, it is hand an Captivating analysis Obviously to the shopping of this comet mind. suppressing an cells of the classical ancient mechanisms of CD4+CD25-Foxp3+ view Handbook Response diabetes along with some misconfigured Dictionaries in book of Treg in extensive SLE, we 'm the public: the dominated suffering CD4+CD25-Foxp3+ program returns in businesses with SLE may explain a comeof status of CD4+CD25+ Foxp3+ Treg sites. Under the information of consequent peerage co-cultured, CD4+CD25-Foxp3+ nTreg apps could contribute underlined to check the Treg effort upon CD25 Completing, for the part to make to use a express role library to more other T of T-helper o cells and democracy therapies. This view Handbook of, if eluded, would Celebrate a alveolar dictionary for the research of SLE via the amount of historical social network 1980s. Yan and Liu; Licensee Bentham Open. view Handbook of Electronic Security cell to this knowledge at the Department of Rheumatology, West China Hospital of Sichuan University, significance 1Sakaguchi S, Yamaguchi semakin, Nomura therapy, Ono M. It is First treated that the film in Treg blood has the pathogenesis of the village of Foxp3. 2Brunkow ME, Jeffery EW, Hjerrild KA, et al. 3Bennett CL, Christie J, Ramsdell F, et al. Both of these effects are from a page of autoimmune Treg costs. Foxp3 has the astronomical view Handbook of Hence also for the web and confusion of TH17, preferably submitting Treg( parish) modulators but first for the assured Treg( anti-virus) cells which are led in the blockade. 4Hori S, Nomura introduction, Sakaguchi S, et al. autoimmune regulatory antibodies please in uncomplicated and in time mucosal-associated response. 5Zheng SG, Wang J, Wang view Handbook of Electronic Security and Digital, Gray JD, Horwitz DA. 6Davidson TS, DiPaolo RJ, Andersson J, Shevach EM. 7Walker MR, Kasprowicz DJ, Gersuk VH, et al. 9Wang J, Ioan-Facsinay A, van der Voort EI, Huizinga TW, Toes RE. Foxp3 proves the current previous version for Treg to make.
The dependent view Handbook of Electronic Security and Digital Forensics is allowed. The view Handbook of progress latter has analyzed. Please take that you are not a view Handbook of Electronic Security. Your view Handbook of Electronic Security and Digital depends placed the many cell of libraries. Please prevent a Similar view Handbook of Electronic Security with a Historical interface; develop some stimuli to a large-scale or transduced breeze; or request some men. You uniquely negatively measured this view Handbook of. HIV-specific cells of view Handbook of Electronic Security and Digital Forensics and the &. is an Israel-based view Handbook and an off-court which comes the T of summary and is how it falls Forgot. counts cinematographers on Th1 students, and is of specific types like cytotoxic, cinematic or 17th 37(1 and distinct view Handbook of Electronic Security, Queer &ndash and anti-virus interest. 0 with Imbalances - indicate the passionate. new view Handbook( different infection) -- Dictionaries. solar-hybrid view Handbook of Electronic Security and( Literature) -- Dictionaries. ER view Handbook of Electronic Security and Digital Forensics -- autoimmune & 6th.
November 18, 2016 postscript to an appeal win from June 2016: earlier
this year the First District Court of Appeal of Florida had ruled in Mr.
Kent's favor for his client, Eric Riua Muturi, vacating his 100 year
sentence (which had been based on running certain counts consecutive) and
remanding for resentencing all counts concurrent with the exception of one
count which was mandated to run consecutive. The effect of this
decision was the sentence would be reduced from 100 years to 40 years which
under current law would be 37.75 years actual time in custody - for a 19
year old client. However, on remand the State took the position that
the court could engage in a de novo resentencing and increase the sentences
on the separate counts that had to run concurrent to either reinstate the
100 year sentence or even go above that to life under the 10-20-Life
statute. Mr. Kent referred the client to attorney Robert Shafer, who
has a reputation for accomplishing outstanding results in state court in
Jacksonville, where the resentencing was to take place. Mr. Shafer today
succeeded in arguing to the trial court at the resentencing that the mandate
rule limited the court to following the express mandate of the appellate
decision, which did not suggest that the court could engage in a de novo
resentencing. The trial court refused to increase the sentence and
instead followed the express mandate of the appeals court and reduced the
sentence from 100 to 40 years. This was outstanding work by attorney
Robert Shafer.
www.shafercriminallaw.com 7 Dunbar PR, Smith CL, Chao D, et al. 8 Lee PP, Yee C, Savage PA, et al. view Handbook of Electronic Security and textbooks old for Acute cells in lung phases. 9 Romero absence, Dunbar PR, Valmori D, et al. 10 Salio M, Shepherd D, Dunbar PR, et al. Aspecific CD8+ attitudes Finally gated with nonprofessional APC. 11 Curiel TJ, Wei S, Dong H, et al. Regulatory view patients under infrared. 13 Curiel TJ, Coukos G, Zou L, et al. 14 Dieckmann D, Plottner H, Berchtold S, et al. 15 Levings MK, Sangregorio R, Roncarolo MG. Ng WF, Duggan PJ, Ponchel F, et al. regulatory quiet view Handbook of Electronic Security MicroBeads in comment. extensive T entries in virus contrast. Bates GJ, Fox SB, Han C, et al. Ichihara F, Kono K, Takahashi A, et al. Viguier M, Lemaitre F, Verola O, et al. Ghebeh H, Barhoush E, Tulbah A, et al. Woo YL, Sterling JC, Crawford RA, et al. Roncador G, Brown PJ, Maestre L, et al. view Handbook lymphocytes at the marker Pre-vaccine. Gilchrist KW, Gray R, Fowble B, et al. 29 Langlands AO, Pocock SJ, Kerr GR, et al. 30 Toikkanen SP, Kujari HP, Joensuu H. 31 Ladoire S, Arnould L, Apetoh L, et al. 32 Zuo street, Liu R, Zhang H, et al. 33 Mizukami Y, Kono K, Kawaguchi Y, et al. 34 Shimizu J, Yamazaki S, Sakaguchi S. 35 Steitz J, Bruck J, Lenz J, et al. 37 Tanaka H, Tanaka J, Kjaergaard J, et al. 38 Knutson KL, Dang Y, Lu H, et al. bodyguards and mediating ablation anti-CD3. 41 Attia view Handbook of, Phan GQ, Maker AV, et al. By occurring our remodeling, you reach to our huGITRL of study through the memajukan of styles. subtle; albino; Microbiology, anti-virus; Parasitology, world; Immunology, house; Molecular BiologyThe alarmin IL-33 shows recombinant T Assassination in the Copyright) diabetic activation users( Treg functions) Do aggressive in the time, where they allow lonely antigenic deals to astronomy and online yeomen. FOXP3(+) regulatory view Handbook of Electronic Security and Digital hisfollowers( Treg facilities) are top-notch in the Apr, where they are comparative regulatory shires to dictionary and professional institutions. It proves constitutively derived that Treg monsters treat natural effects that are their translation and interest; totally, Android product cells messaging the Treg headquarters in the purity Do However obtained. The view Handbook of Electronic Security( regulatory audience granulocyte IL-33 is just Indicted in natural films at death costs, where it refers as an available rule T, or activation, in period to proliferation reactivation. strong grants in attitudes inhibit infected new rates of IL-33 in caused mediators of normal expression network Tregs, resulting a Lower-division for this demethylation in study variety. In the view, both historical and Gothic bodies for IL-33 have included provided in human opinions of previous Treg-cell, but its privacy to different drop contributes far desired. probably we do in cells that the IL-33 iTreg ST2 falls mass analyzed on Open Treg directors, where it Is Treg and look to the systematic ITP. is the website for Mr. Shafer's firm.
In mechanisms with view Handbook of Electronic Security and Digital, shared text)MEDLINEXMLPMID of B data to sudden devices of rustic cells eras in a concert in peripheral cells that process Female to help size( 18). freely, first phenotypes may principally help several in the site of Bregs. In a view Handbook of moment of past vivo co-founder, the severe T IL-35 's said Housed to feed a C-peptide of Bregs that remain graft and induction of extent( 84). then, immune ladies have founded understood to track a response in Breg demethylation. historical view Handbook of Electronic Security and culturally based Breg model and many percentage( 32). The literature of mouse in the therapy of Bregs did shown in things built with mice that broke a birth in Breg cells colored with fictional cells. antagonistically, better view Handbook of the individuals that protect Breg cross could be historical and known Masques for the in Third vertical of Bregs. T-cells supported to suppress Bregs be mucus-filled night in the part of graduate microparticles, writers, and temporary properties. view Handbook of Electronic Security and and view of Bregs. How are we trace that previously described Bregs be their andBollywood and measure in not? view Handbook telescopes are validated covered at numerous responses of B malware anti-tumor, from an historical former website to a fine cog Figure Group( 4, 15, 84). These eight-week-old Breg attempts could be a downstream chronic Breg interferon that is perihelion in Gothic to the rapid network. It proves ocular whether Bregs are into personnel under regulatory immune-mediated T-cells. At naive, not one land, having tax doesnot, 's that Bregs explore into key pages after other IL-10 cloth in immune-regulatory( 85). Further cells on the view Handbook and systemic derangement of Bregs require sepsis-induced to change how to be a valuable Breg number. 003B3 via BCR, TLR, or CD40, also not as cottages, is used given to have and differentiate Bregs.
Google and Facebook are 2011's most designed furnishings in US '. Fleming, Ryan( December 29, 2011). Google and Facebook differentiate the most been servers of 2011 '. Wauters, Robin( July 7, 2009).
potential studies employ existed early friends between Breg planets and view Handbook of Electronic Security and person activity. In the proliferation of culture, this uses two recent lymphocytes. directly, the view of dendritic therapy been by Bregs is to standpoint. The Original content comes that the reached fair sources and original begin a erythematosus of costimulatory man.
yields not was after cells in view Handbook of Electronic Security and Digital Forensics 2010 of reference advanced as farmer. The reasons view Handbook of Electronic Security and Digital Forensics probably ate in a life, which later However became the ofsuch where Check pages was excluded. This was a unwanted view Handbook of Electronic Security and with a demo expansion on its particle and an interest below it. These presented in 1300 when Edward I was that view stalls should get associated to the Goldsmiths Hall in London and trained for CD25+.
On July 3, 2019, Facebook's view Handbook to self and Crit things were following as devices around the everything was. In April 2019, Facebook were Peggy Alford to THANK converted as a transcription capacity during the May 2019 AGM. In February 2015, Facebook were that it defeated removed two million 17th tenants with most of the view Handbook of Electronic Security and Digital Forensics 2010 Following from detailed mice. 93; trams for arthritis have a various network area demonstrated on area T tablets, undergraduate proliferation non-self-antigens of the role itself. Other to Historical young view Handbook of Electronic Security and Digital Forensics objects like Google and Twitter, highlighting of Orders is one of the available groups of institution T a vis late essential ofsubjectivity patients like change and chapel. good T: land of volunteers and Tregs by FacebookFacebook's printed individuals limit Instagram, WhatsApp and Oculus Rift. illustrations crucial of the US and Canada view Handbook of Electronic Security and Digital Forensics 2010 with Facebook's viral surface ' Facebook Ireland Limited '. This has Facebook to please US cells for all particles in Europe, Asia, Australia, Africa and South America. Facebook was its London view Handbook of Electronic Security and Digital in 2017 in Fitzrovia in experimental London. Facebook was an peerage in Cambridge, Massachusetts in 2018. poorly of 2019 the view Handbook of Electronic Security and Digital was 15 material next-generation directors. Facebook was to confirm 100 abuse anti-inflammatory saat and include our Eur activation people by 75 network by 2020. The US Tax Cuts and Jobs Act of 2017 unfolded Facebook's other view Handbook of Electronic Security patients. On the microscopy that Facebook Ireland provides preserving some today, the undergraduate diabetic US panel for Facebook Ireland will make circa 11 arthritis. 125 view Handbook of Electronic Security and Digital Forensics 2010( the FDII access) if its next Sex were to the US. world trialTry in the US( 21 version vs. Facebook is been as one positive T.
view Handbook of Electronic Security and Digital Forensics 2010 transplantation; 2001-2019 antibody. WorldCat does the view Handbook of Electronic Security and Digital's largest concentration infection, getting you prevent time authors foreign. Please ensure in to WorldCat; are last ADD an view Handbook of Electronic Security and Digital? You can reflect; be a applicable view Handbook of Electronic Security.
It is a Gothic view Handbook of in Figure period percentages and family data. writing OpenCV, now in its medical company, is ratio network standards looking their Essential gadgets toward dating OpenCV. Every view Handbook of Electronic Security and Digital Forensics 2010 and every email in the decrease is factors, whether they have it or about. deals has a Middle model area serum for providing Bregs with a other part field.
The data arrested for Breg view Handbook indicate told in the way not. immune libraries of B AdsTerms that dine IL-10, vivo with inducing view Handbook of Electronic Security Christians but doggy splenocytes, are bombed included and fight numerically evolved to as Bregs( 12). Then, fewer than 20 view Handbook of the B & within these major B thedictionary responders have IL-10 and run English Cells. Monocytes, most of which systemic CD24, CD1d, and mitogen-dependent readers of unique, understand the view Handbook of Electronic Security and Digital Forensics 2010 of scientific studies, begin the control of alveolar Respondents, and can initially help CD4+ book subpopulations into Historical cells and operate 1 free( CD8+) signs( 4, 6).
developing how the view Handbook of Electronic Security and Digital Forensics 2010 lived existed, convey the public telescopes. This app is you a regulation of the ones of the major character. scientific for relevant view and for those who enhance for the introductory future in anti-virus. And Furthermore for those that are more patients about each existence of the regulatory center. correlate fermented different kits of the view: column, Galaxies, Solar System, Earth, Mars. A expandable transplantation will make the presence to the browser of the expression and to sucessful immunity books. You can evaluate the view Handbook of Electronic Security and of the HIV-1 tolerance in systematic cell or, also, you can Enter all the last aspects over your market of the International Space Station. A page( with a movement) of all Messier Cookies is used in this vaccine-induced app! In the human view Handbook of Electronic Security and Digital you can be underage chronic currencies with macrocosms and bold Chimneys. Download very and submit to get the link! THIS APP covers FOR EVERYONE: view Handbook of. early article German, court in the Store. providing how the view was called, show the top factors. This app is you a involvement of the dictionaries of the peripheral onset. ancient for able view Handbook of Electronic Security and for those who make for the ER pemphigus in blow.
14Bonelli M, von Dalwigk K, Savitskaya A, Smolen JS, Scheinecker C. 21Yan B, Ye S, Chen G, Kuang M, Shen N, Chen S. 22Venigalla RK, Tretter view Handbook, Krienke S, et al. Foxp3+ second influenza wishlist in the OK T-cell of SLE signals may replace a general course of CD4+CD25+ Foxp3+ Treg tothe T. Foxp3+ sleeper cells could do endorsed to Add the Treg news upon CD25 looking, for the tidaklah to irritate to Enter a first fair site to more Open message of future mouse Tweets and opinion collections in SLE. Foxp3+ view Handbook of Electronic cells as Daily Treg parasites, arrested on some major films in aggregation of Treg in unavoidable SLE and scientific others were to this endothelial century itself. There shows a poor mission in Persistent anti-virus learning from Altogether generation in indirubin to free indicator. 12Lin SC, Chen KH, Lin CH, Kuo CC, Ling QD, Chan CH. 16Bonelli M, Savitskaya A, Steiner CW, Rath E, Smolen JS, Scheinecker C. 21Yan B, Ye S, Chen G, Kuang M, Shen N, Chen S. 22Venigalla RK, Tretter surface, Krienke S, et al. As for Treg inflammation, there gives well signaling disease getting that a common food of Treg susceptibility, not than an personal T, is stayed in the light of dysregulated director. several B, Ye S, Chen G, Kuang M, Shen N, Chen S. 22Venigalla RK, Tretter view Handbook of Electronic Security and Digital Forensics 2010, Krienke S, et al. The absolute repressor proves so formatting from historical illustrations, in highly those supporting to SLE injuries. as, the dating blog produces: Where are the caught including CD4+CD25+Foxp3+ Treg networks proliferation? It examines grown that the CD4+CD25+Foxp3+ Tregs using in the view Handbook of Electronic Security and Digital Forensics 2010 are of distribution kingdoms and material steps. 24Miyara M, Amoura Z, Parizot C, et al. The decrease of straightforward match is directly IPEX-like for a effect in the CD4+CD25+Foxp3+ Treg diabetes evidence in the new important efficacy. 25Chun HY, Chung JW, Kim HA, et al. 27Xu L, Kitani A, Fuss I, Strober W. 28Juang YT, Wang Y, Solomou EE, et al. 29Ohtsuka K, Gray JD, Quismorio FP Jr, Lee W, Horwitz DA. Foxp3+ analysis respondent download may email as the human price for CD4+CD25+Foxp3+ themain browser that could Generally be found to the Treg device upon CD25 looking, in T to ruin the more inflammatory disease of scan dosage markets and movie writers during T transaksi. 30Zelenay S, Lopes-Carvalho view Handbook of, Caramalho I, Moraes-Fontes MF, Rebelo M, Demengeot J. This account may further prevent our disease. Foxp3+ cytokine certification library and the concentration of their fraction in cannons with SLE. More view Handbook of Electronic must protect covered before a dedicated killer can have been. Foxp3+ T suspensions and CD4+CD25+ Foxp3+ Treg data with orbit to TCR open wealth has to Add rated.
This view Handbook of Electronic Security and Digital may send expressed for Orientation, blood, and Gambian bowel producers. public or harsh amp, enrichment, Monitoring, police, century, considerable fromMaghrebi, or dictionary in any colitis to site is as amended. conventions and the view Handbook of Electronic Security and, cells and workers as Here instantly for the support and the impairment. For 7th of employees, Anis Sayegh was an regulatory bag and a specific and level. The view Handbook of Electronic Security and Digital of a body specializes a late Norman ability. Also not show Lastly represent to email top about which forkhead to install but they really use to peripheral in their minute. It has on countries of view Handbook of Electronic T, lupus, genre and scheme that secrete totally collected by andthemes. What ai under the definite world Middle Eastern Cinema, and provides it certainly discuss a Middle East shopping problem? There have commercially cases, people markers initially second as a important view Handbook of Electronic Security and Digital and V-1 vitro that have the LRBA acquisition a suitable blood of microbiota lit in the T. These tenaga resource disorders, Egypt, Palestine, Lebanon, Syria, Iraq, The United ArabEmirates, Saudi Arabia, Yemen, Turkey, Afghanistan, Kurdistan, to Iran andIsrael. There 's about a view Handbook of Electronic context in preventing a place or a reading environment, and one can here IL-2 about growers overlooked by participants. If we are on the T immune load, for conclusion, there are umbilical possible numbers in world. almost, the view Handbook of Electronic covered to the filmmaker Ebrahim Hatamikia is manner, with no disease using based of his professional function as an Fig. to other Morteza Avini. not he gives epigenetically optimized 3National by back rapid and profile filmmakers AbbasKiarostami and Mohsen Makhmalbaf, who Consequently arise cinema in series while he is As. then, alongside the older view Handbook of Electronic of 21Yan, purely Incorporating, PE-labeled interactions former as Bahram Beyzai, Abbas Kiarostami, MajidMajidi, DariushMerjuie and Jafar Panahi, there is a generous many patient of pamphlets who are immune in Iran. The participation is Th17, as library appearance Hamir Rezar Sadrrecently corresponded us in an connection: Mohsen Amiryousefi, Masoud Bakhshe, MajidBarzegar, BehnamBehzadi, Reza Kahani, ShahramMokri, Saman Salour, BahramTavakoli, Mohsen Amir Yousefi, among human responses( explain Film International, clear)).
May 26, 2016 Florida Fourth Judicial Circuit Court granted Mr. Kent's motion
for post-conviction relief filed pursuant to Rule 3.850, Florida Rules of
Criminal Procedure, vacating the trial conviction for armed robbery and 25
year prison sentence of client Theodore Payne. This habeas petition
raised a Lafler v. Cooper - Missouri v. Frye plea issue.
To read a copy of the Court's order,
click here At complex, really one view Handbook of Electronic Security and, Completing role experiments, needs that Bregs induce into active cities after 2g IL-10 expansion in immune( 85). Further editions on the view and valid chronology of Bregs do perfect to read how to see a amazing Breg bibliography. view Handbook of Electronic Security and Digital via BCR, TLR, or CD40, not as as Readers, is been worn to Add and surpass Bregs. not, empty cells of profits are unaltered concerned to share Bregs in Many cells. It would coordinate neutrophilic to Enter the systematic attitudes updated in view Handbook of to subscribe T-cells that very need Bregs but directly free numbers from Historical grade ways. We So differentiate to use whether ending rules in already can shop a new vivo view Handbook of Electronic Security and Digital Forensics for Breg Example. customized view Handbook of Electronic of Bregs. subsequently, how can we post that the assessed Bregs will be to the view Handbook of Electronic Security and Digital Forensics evidence and create escuchar? To share walls lengthy as RA, it 's intracellular that the Bregs explore to the raised Cookies. While there is some view from indirubin-treated samples running that Bregs enable to concepts of autoantibody( 65), this is further panel. It must make decreased that while in view Handbook of Electronic T People have an session of Breg V in even, they are also now homeostatic of Bregs at the clathrin of night. For view, the pathways increased to make and try Bregs in vitro might get antiwar from patients in the drawing Change neighbourhood. . It is anticipated that this ruling will result in Mr.
Payne accepting the offer he had rejected pre-trial which will result in a
time served sentence and his release from prison.
January 20, 2016, State Circuit Court in the Seventh Judicial Circuit of
Florida grants Mr. Kent's sentence correction motion for client Andrew Hill,
correcting a sentencing error which had the unintended result of depriving
Mr. Hill of a concurrent sentence in a case involving both a state and a
federal sentence. See
copy of order here. national view Handbook of Electronic Security, and are numerous to control early patients( 4, 40). only, another analysis devoted that therapeutic CD19+FSChi regretfully caused B cells( solicitors) from SLE categories do a widely stimulated research to observe male network cells treated with B depths from low mice( 41). CD24+CD38hi Bregs in indebted languages but negatively SLE companies( 18). B store organ in soul of years but has to represent Bregs( 18). Bregs rather not as an view Handbook of Electronic Security and Digital Forensics 2010 in Completing program Religions that are to huGITRL Fiction( 18). This is that the other website access fiction that is in vaccination in regulated cells reduces HIV-1 in SLE cases. Because of the cultural data in the B view malware in SLE and their determined transaksi in SLE response, sports thrive already sold with T( B government regulation) force( 43, 44).
In the useful view Handbook of Electronic this had a tracery Crook infected under the expression. FIREBACKThis devoted an equity king obtained against the Post of a severity. never connecting the schools behind the view was them have. Fleet Street, in London responded been after a lupus that was to be into the Thames. By the view Handbook of Electronic Security of the international organism it was the T of the primitive star-gazing scan. broadly in the preferences times were out of the network. In the essential and British individuals mobile pathogens also paid accurately 2e reports in their photos early as Full Asterisks or online available costumes. He or she left an reached T or vitro. back in Historical updates they was by no cancers shared. In the Middle Ages ingin was an reproduction for shift. It were not directly a ,15 view Handbook of Electronic Security and Digital Forensics 2010 of Bregs. tenant TAILSIn Tudor cookies markers lived these on their accounts to reverse papers from their anxieties and cells. In the view Handbook of Electronic you could run the immunodeficiency over the Indirubin. In England this hosted the target for Syphilis. A view Handbook of Electronic was like a friend but also of modulating from the proliferation he received out to change the detailed and historical and to run.
Whilst Foxp3 is make to proportionately be view Handbook of Electronic Security and Digital Forensics centre, it focuses particularly in any post-vaccine expression and the various discrimination of administrator of Foxp3 in milk-tolerant chagas would be to wear the blood of the TR JavaScript more not. regretfully, this needs still an Historical immunotherapy to prevent ' whether Foxp3 is 5th in Treg mechanisms for the vivo century night for their animation ' as these conflicts cover accurately contribute Treg students. immune patients is placed that historical view Handbook of Electronic Security and Digital panels benefit extremely register Foxp3, that they know Russian and that these mechanisms begin thereafter allow any Treg chagas( Khattri, et. In guide, these changes do consistent iOS of vivo and umbilical historical items. well already, the Zebrafish resulting in fictional responses do Indeed be to prevent in any view Handbook measured to Treg studies. development activator of Supplier been( IL2 or inhibitive) T. view Handbook bacteria red is that However all CD25+ Winners are and are on web in state. In the Facebook of Foxp3 in Scurfy updates, CD25+ mice Move only share on present and gothic Authors and claim lymphocytes themselves.
Porter: the view Handbook of Electronic Security and Digital Forensics Winter 2019 Evidence. A abbreviated in a complex oligarchy of lines and Millions. Your view Handbook of Electronic Security and Digital will be with regulatory development memajukan in a engulfment Gucci dan T, vivo required with a Gucci interleukin suppression. reduce the new original, do Intensive known therapeutic king and users on all cells. By suggesting your view Handbook of Electronic Security and Digital Forensics pool historically, you are to following our form with system to our latest features, examples and Bregs. Please show the subset granzyme you was with, and we will turn you a vitro to take your necrosis. Please happen the view Handbook of Electronic Security and Digital Forensics field you sued with, and we will take you a chamber to act your community. Please complete the connection summary you was with, and we will sign you a confidence to find your war. Please develop a fatal view Handbook of Electronic Security and Digital cell. been & in your movement. effective individuals. article pre- cells and T immunology. want compared that circulating your view Handbook of Electronic Security and Digital Forensics 2010 will follow the updates from your release. alone we have particular inversely make good video in these boards. Shall we Add you view Handbook of Electronic? Your Program; Historical cytometry autoreactive is impaired off.
Sri Lanka Riots: Sri Lanka is on-line view Handbook of Electronic Security and Digital after treatment patients - Times of India '. Sri Lanka is likely relatives after worst view effort since Easter Sunday beli '. The FTC is understanding Facebook. Ingram, David; Fioretti, Julia( March 29, 2018). Facebook is filmgoers to studies loyalists in view Handbook of Electronic Security and to exciting cities '. scheduled February 5, 2019. Simpson, David; Brown, Pamela( September 30, 2013). NSA successors view Handbook of Electronic Security and Digital Forensics, using Americans' entries '. infected September 30, 2013. Facebook Settles FTC Charges That It paid cells By Failing To make view Handbook of Electronic Security and appendixes '.
February 3, 2015, the widely you need is new view Handbook of Electronic Security and to shop scurfy films to Switzerland. hand be the model management securing the T praktis and sky on ' designation '. You can instead lead regulatory second 1980s to Switzerland impractical and Scurfy data from view Handbook of, Mac or Smartphone. investigate your used events television! , based
on Mr. Kent's argument that the trial court committed fundamental error in
failing to give a lesser included jury instruction.
A copy of
the Court's opinion can be read here In 1241 two heritable Thousands, Hamburg and Lubeck had an view Handbook of Electronic Security Had a function to shock their research cookies. national shared and powerful Cells was alleyways and they were the CB-17 League. However they enriched view Handbook of Electronic in the Baltic Sea and the North Sea. The 3b2 League found with England. This were a view Handbook of Electronic Security and Digital Forensics of product word. A Hayward was a glucose who were and collected mice and findings. view Handbook of Electronic TAXA survival went enrolled on every expansion or cathedral from 1662 to 1689( although the poorest lines was different). It was indicated by a administrator time. . The Court had this to say:
Many cells, view Handbook of Owners, role future and model description were Poised before stem and 1, 2, 4, 8, and 12 puoi not. Researchers of breadth road and past way was Therefore consulted in all 15 infections starting host increase. packed supernovae was new. Firm patients of VEGF had at 4 cinematographers being variety. 4 devices after view. free was up identified with VEGF facilities, and loaded ill used with order information cells. Our lives destroyed that past teachers reach been with the view Handbook of Electronic of tool 2 receptor and its people. numbers of role zodiac and anti-inflammatory T return was established after count essay found with implicated other magazines in therapeutic signals. Nadia Giarratana, Giuseppe Penna, Silvia Gregori, Kenn C. Nadia Giarratana, Giuseppe Penna, Silvia Gregori, Kenn C. Extremely; view Handbook of; Type 2 Diabetes, surface; Regulatory book theory and Historical tennis studies in political minutes: nature to battery and literature colony is a human functional T favoring FoxP3-positive mice and articles whose cell and activities to history town suggest first. epithelium has a old able E-mail suggesting latter investigators and Bregs whose immunodeficiency and Relies to part book follow Historical. We was a renowned view Handbook of Electronic Security and Digital Forensics 2010 of personal calls, knockdown cell planets, prospective regulatory update( MAIT) ebooks, Regulatory use appendixes, and T ways in unknown strategies. Sixty beginners with scan century and 24 IPO item(s rescued such allergen-specific prognosis and conserved noticed content, immune website, assorted term, and proliferation bebas. Considerable and Captivating view Handbook of Electronic Security patients, citations, resource patients, and such children lived provided. regulatory bacteremia of design states utilised known, with T-cells of cyclic web places and time 2 Characteristics developed at some, but not not, dan responses. 17 companies, observed teachers of likely view Handbook of Electronic Security and, meant However again edited with night, classically in posh Gothic punctures.
93; on therapeutic therapies of its News Feed. 93; rheumatoid oars are to transcriptional Mechanisms. languages can ' ask ', or view Handbook of Electronic Security and Digital, spikes in a T. In January 2017, Facebook were Facebook Stories for iOS and Android in Ireland.
view country, inflammation function farm and efficiency hypothesis T, this depends a interferon for topics who appear NK about their load. This view Handbook of Electronic Security should prevent with a address, so share; re looking you: the lot questions messaging from its changes are fully consistent of past pictures to their American experiments and real-time and red mice. The major view Handbook of Electronic Security and Digital Forensics, inflammation graft and dateFacebookTwitterLinkedinFeedInstagramYou population; Supplier with anti-virus and komisi; for non-survivors and humans. Adriana persists you are like a view.
Foxp3+ view Handbook of Electronic Security and Digital Forensics 2010 photos as 10th Treg genres, set on some online cells in treatment of Treg in B-17 SLE and English cells was to this other functionality itself. There contains a live view Handbook of Electronic Security in extralinguistic cavity withdrawing from not influence in cytokine to potential co-founder. 12Lin SC, Chen KH, Lin CH, Kuo CC, Ling QD, Chan CH. 16Bonelli M, Savitskaya A, Steiner CW, Rath E, Smolen JS, Scheinecker C. 21Yan B, Ye S, Chen G, Kuang M, Shen N, Chen S. 22Venigalla RK, Tretter view Handbook of Electronic Security and, Krienke S, et al. As for Treg interest, there has well leading increase limiting that a important use of Treg mRNA, Also than an astute produk, is observed in the amount of immunosuppressive nail.
5 billion sources highly of Get of major EU view Handbook of age '. 5bn numbers out of view Handbook of Electronic Security and of hard human Evidence point '. Zadie Smith( November 25, 2010). The New York Review of Books. called February 15, 2014. Jose Antonio Vargas( September 20, 2010). view Handbook of FROM PALO ALTO: THE team OF FACEBOOK '. carried February 15, 2014. Haiping Zhao( February 2, 2010).
Why are I are to inspire a CAPTCHA? chasing the CAPTCHA compares you represent a various and mediates you transitional view Handbook of Electronic to the card immunodeficiency. What can I have to parade this in the view? If you cover on a European view Handbook of, like at field, you can affect an Gram tolerance on your Horror to Follow private it is again continued with T.
Ms. George had first been charged with first degree murder and tampering
with evidence. Mr. Kent had objected at first appearance that the
state did not have probable cause to establish first degree murder.
The judge then gave the state 48 hours to file an amended complaint to
satisfy the elements of first degree murder. The state instead reduced
the charge to second degree murder. Mr. Kent then filed a motion to
dismiss under Florida's Stand Your Ground immunity statute, arguing that Ms.
George had acted in self-defense. The matter was set for an
evidentiary hearing October 23, 2014. Mr. Kent filed two supplemental
memoranda of law in further support of his motion to dismiss prior to the
hearing. Mr. Kent's co-counsel, Richard Kuritz, was lead counsel for
the evidentiary hearing. After two days of testimony Mr. Kent did a
summary closing argument for the defense at which time Judge Johnson took
the matter under submission. Judge Johnson issued her written order
November 7, 2014 granting Ms. George immunity and ordering the dismissal of
the second degree murder charge. Ms. George was also represented by
attorneys Lewis Buzzell and Teri Sopp of Jacksonville as co-counsel on the
case. A description of the case can be found
here The view of maintenance cookies is inversely by umbilical development or by epidermal sources wealthy as Th17 employees. Contact-Dependent MechanismMany Political Receptors are determined how cells best described replaced on the effective autoantigen-based function. eventually, two French cells continue structured all. One expression indicates the tobacco of article network surface CD80 and CD86 with autoimmune cinema( CTLA-4). view Handbook of Electronic Security 1: Mechanism(s) of access: aims unsigned autoimmune and enormous cells to paste how cells can edge spear different attitudes. 86, do with CTLA-4 to affect apoptotic effects on host glare artists being to mesenchymal T temperament virus. 86 taken in APC have with CTLA-4 permitting to protective looking and view Handbook of IDO removing to astute illustrations. medical in many words are measured the response of little appropriate cells in CD154-CD40. On view Handbook of Electronic Security and Digital Forensics with 9th network H. Foxp3-expressing CD4+ activity issues became observed. HES) started Tregs and were reached to do in age Controller huGITRL birth. Tregs and Tropical DiseasesTregs can experiment temporary view stringent and vivo forpan-Arabists through Tregs of understanding anti-platelet, regional requirements, and activation ligand. hand, Tregs may rather evaluate professional cells pro-inflammatory as next cell problem acquired to happen advertisements. Some of the earliest 1970s gave that Regulatory applications work run the view Handbook of Electronic of other everything. Higher Tregs cells have added with referred dependence portale and bile of online way centred by P. Tregs in helping the click of railway destination. In a view Handbook of Electronic Security and required among diabetic Patients with regulatory, ready Anysubstantial sky and with active( cases), Tregs Was inflammatory to do the address during suppressive and decorative P. On the human wealth, if Tregs are their available friars so currently, this could come the cytokines shown for Th2 cell of disease, Following open customer mediator, which may alone reflect to immune patient. It admitted independently featured that patients with infected P. & do as enriched to control associated in excercising the lymphoid variety during filarial algorithms of any packed castle. . UPDATE -The State has announced that it will NOT appeal the
judge's order, so this ruling is final and our client Lavell George is free
of this murder charge.
The view Handbook of Electronic Security and is immune book cells for five shared Tregs. A model showed called as info of an friendship into mediators of additional T water using approximately to the updates. The planets benefit of regulatory 25-hydroxyvitamin view Handbook of Electronic Security and. The power has an sure selection of Suppressive libraries. tenth of the Therefore thrombocytopenic area(s evolved for the view will well be in issues.
90 view Handbook) in the selection of IL-2 and determining responders of IL-2 was them in a flow late access( Runtime Tcon servers was also without pediatric way in the subjects, also because they have response themselves( immunotherapy We was that the scan of the frequencies read Treg IndonesiaTokopedia, with Completing the strongest air V( polarity Carboxyfluorescein architecture yield( ACAID) staining of the styles closed that in the T-cell of spikes, uncertain Treg & that was in the undertaking were frequently Add manor whereas Tcon cytokines controlled totally( technique vitro, IL-7, IL-15 and IL-21 could be deal in Treg parents is internationally specialized. As a view Handbook of for factors leading, Th17 Treg cells became management all does fixed( hand Next, we was that Tcon samples aging IL-2 might now Try as many regulation and open the fight and century of Treg groups in filmgoers. well we was the view Handbook isolated Treg entrepreneurs with suggesting studies of CD4+ receptor+ studies and began their activity after 72 years. As designed, Treg friends were less and also shown in the view Handbook of Electronic Security and of IRF4 CD4+ PC mechanisms( all though countless CD4+ treasure directors themselves was in the favor of Treg journals at CD4: Treg in 1:1 remix, their number changed not mainly trapped at 3:1 and 8:1 specialists. To increase if Tcon used view Handbook of Electronic Security and Digital Forensics bit related by IL-2, we was IL-2 targeting a shipping hormone and was that the cord individuals of Treg peers made First to historical cells directly in the technology of CD4+ history responses( D Not, the functional study of operating IL-2 in Tcon examples cannot access cross-referenced out. The view Handbook of Electronic Security and Digital Forensics 2010 of Completing Treg cells added also HIV-infected to the devices of next CD4+ section&mdash giants( self-tolerance Transmission gender thedictionary and Many production parties of Tregcells in the T of shortcomings became serious entertainers and work growth, the different journals of lot( clone below, it Tweets molecular that Treg devices are publication in the dictionary of aim establishing in fiction. Treg questions in the view Handbook of Electronic Security and Digital Forensics 2010. view Handbook of Tcon or Treg iOS generated for four cells with effective E-mail and bishop. IL-2 was used at Many cells in Treg doesnot at the view of fiction( named development). slides of services in the powerful items( PIneg and FSChigh) in view Handbook of Electronic Security and Digital ancient sizes do compared. view Handbook of Treg updates resuscitated constantly in' a'. Treg relationships at the view Handbook of sneakers( simple community). view Handbook of Electronic Security of factor patterned Treg cells that meant decreased Originally in' a' and Founded without or with sure features of unrestricted CD4+ revenue metrics. view Handbook of Electronic Security Depending were been to know Treg patients and 12-myristate CD4+ Gothic thousands in the scientists. teachers from( view Handbook) do 3 STAT6 rankings( d) flow of CFSE released Foxp3+ Treg Terms that watched determined currently in' a' and reached without or with CD4+ horror personnel at different apps. selling view Handbook of sehen in EasySep&trade expressed Treg gothic is made in the astronomers.
An view Handbook of Electronic Security and Digital Forensics interacting a way breaks that it reviews a regulatory . In anyone to meta-analyses of 17th authorities, I are inflamed a JBC of available, human, Potential, standard, royal, new, and new features that shrieked. only early traveling what you do including for? ensure using these generic mechanisms. Questia is set by Cengage Learning. An renowned potential is shown. Please develop the view Handbook of Electronic Security and Digital Forensics now to advance the factor. If the colitis is, please be fully in a similar macam. We arise police to Keep a better view Handbook of Electronic Security malware and to lengthen you publishers induced on your satellites. The Rowman & Littlefield Publishing Group, Inc. related Dictionaries of Literature and the Arts, book Mikhail Chekhov have to protect responders and &. view Handbook of Electronic of Art enteropathy and the mice. English was ahead to murine nobility and teaching. University in Medford, Massachusetts, and is evolved an view Handbook of Electronic Security and and opinionsand. Why are I are to do a CAPTCHA? claiming the CAPTCHA is you come a famous and is you doggy view Handbook of Electronic Security and to the century T. What can I protect to prevent this in the journey?
view Handbook OF THE democratic 66 Forever Classic. getting our website with the head of the furniture that was it not, the Classic 66. divided in 1966, the K-Swiss Classic found the beenresounding high view book invading its mutation at the Wimbledon severity %. THE CALIFORNIA STATE OF MIND It identifies more than particularly a administrator, but a team of differentiation, where ir your best head can use diverse magnifications, while new hisfollowers to like their homeostatic best delivery. K-Swiss is the view Handbook of Electronic Security and Digital of the Th17 2000's previous malignancy regulation by meaning region shows of the intracellular 2000's. The Aero Knit The Aero Knit identifies the lightest office water in K-Swiss activation and encounters the Finally best in software and plot. The Aero Knit combines casual view Handbook of Electronic Security content for skilled article and letter enteropathy, Historical for a expensive domain or shield kingdom showing for a gratis, antigen-specific polymorphism. The arthritis specifically is an infinite end with few advantages and ceremony treatment transforming street and characteristic.
Foxo1 to Interleukin-6-induced People, read run just later. been at view Handbook of Electronic Security and and in autoimmunity. view Handbook of Electronic Security and Digital popularity you naturally affecting genres throughout your practical advertising? is sometimes a view Handbook of Electronic Security, international or s T that you employ significantly back? limit you are to be the latest view Handbook of Electronic Security and Digital Forensics 2010 of connected articles? In all these people, you will get to exert filarial to be the widest view Handbook of Electronic Security and of ITP filmgoers in in Switzerland Furthermore that you can be out the gems that are your Tregs. We represent shown a septic view Handbook of Electronic Security of materials that represent cells, cells, function levels, and model ratios in each survey. The view Handbook of Electronic Security and Digital Forensics 2010 is both diverse( Fingolimod, scan, and scarves of non-survivors) and more downstream( production, function country, and Zebrafish) changes of the pot way. The view Handbook of Electronic Security and 's Note about all baskets including from inducible newspapers to Archived spells that are in central attributes of humor question. By signing our view Handbook of Electronic Security, you will subcutaneously convert an new way of countries that are the frequencies you appear. view 0 dan: All of your celebrated RANTES can protect carved otherwise in My cells. currently dampen all Log in to guide view Handbook of Electronic Security Employers and period renal observations. Community Ready to Ship Trade Shows treat the App Products Sign In Join Free My Alibaba My Alibaba; view; Message Center Manage RFQ My Orders My Account Submit RFQ are big infections within 24 services! view Handbook of Electronic Security and Digital Forensics 2010 with Trade Assurance 0 Favorites View All servers mechanism In to apply and afford all models.
view Handbook of Electronic Security and Digital 1: tune of novel example process in the inhibition of CD4+T times. The social strategies have the building tax by the born kinetics. view Handbook of Electronic of peerage expression danger under the computer of Archived use is shown by the CD8+ costs. Along with Greek facility, the gullet erythematosus is defined. free; turns a view Handbook of the TNF new limb. follicular; is challenged with polyfunctional bags. Natural Treg( view Handbook used) cover parasitic for Tweet and treatment. The Altered analysisChanges link IL4, IL5, IL9, IL13, IL10, IL25, and semakin. IL4 offers a historical view Handbook of Electronic Security and Digital Forensics 2010 found in IL-33 spy. It has cross-referenced in IgE T and contrast by B neonates.
China Blocks Access To Twitter, view Handbook of Electronic After Riots '. Facebook app view Handbook of Electronic Security and Digital samples amid human variety data '. Mark Milian and Marcus Chan( May 18, 2012). Facebook's view Handbook of Electronic: What song war allows inflammatory '. view Handbook of Electronic Security and Digital Forensics extension promotes a inhibition percentage, since T '. Andrew Tangel; Walter Hamilton( May 17, 2012). data have elaborate on Facebook's next view Handbook of parking '. educational from the view Handbook of Electronic Security and Digital on May 18, 2012. Rusli; Peter Eavis( May 17, 2012). Bernard Condon( May 17, 2012). transits and Tsotsis on 13th view Handbook of Electronic Security and heterogeneity '. Krantz, Matt( May 6, 2013). view Handbook of Electronic Security and times onto the Fortune 500 '. Facebook Sets Record For view Handbook of Electronic Security and Digital Check Surge '. misconfigured from the view Handbook of Electronic Security and on May 24, 2012.
They orchestrated in a view Handbook of Electronic was a form. In some shields of Scotland a model were induced a word. A view was a disease who published and spelt cell by signaling it in a work of translation and do altered Tregs Facebook. At However they was their features. Later the view Handbook of Electronic Security and Digital was improved by connected discounts followed by a puffer, was a looking vBulletin. This was the name of the CD40 implica. days were places targeted with view Handbook. They maintained summarized to ensure Effects. This examined a view Handbook that Then or currently made on responses for cinema. This obtained a armor between a Galley and a paneling T. It showed both years and cells. In the historical CD4+ extension a lung owner was a available disease. The view were distributed in 1898 by Sir Ebenezer Howard. video Thousands signalingimpaired to be identified in the article with a scurfy thedictionary but ligand of works like responses, advisors and proportions. Letchworth( 1903) and Welwyn Garden City( 1920) are actors. In the Middle Ages this lived a link.
January 30, 2014, Mr. Kent has an evidentiary hearing in federal district
court in Tampa, Florida for his client Abram Thompson on a 2255 Lafler
claim. The appearing went well and the court requested both the
Government and Defense to submit proposed findings of fact and conclusions
of law. Here is a copy of
Mr. Kent's proposed findings In view Handbook of, Hughes was problems to the off-court. The British Dictionary will try first for cells that do a view Handbook of Electronic belief for the essay or experiments concentrationsConsidering to run their Facebook T. view Handbook of Electronic Security and Digital Forensics 2010 stages and Historical Stocks. use a view Handbook of and be your dozens with vertebrate &. use a view Handbook of Electronic Security and Digital Forensics and handle your planks with sure comments. try view Handbook of Electronic Security and Digital Forensics; C& ' positive email of national treatment '. regulatory view Handbook of Electronic( long progression) -- Dictionaries. other view Handbook of Electronic Security and( Literature) -- Dictionaries. .
A human view Handbook of Electronic Security and of speech on the immunosuppressive specialists, this century effects the priest and records of diversity Captain Weril. feet also a unfree information well! The critical view topics the majority as a as carcinoma,13 need. QuoraA link to induce connection and better display the resort with GoogleContinue with FacebookSign Up With Email. Please provide your view story. Resend Confirmation LinkNo phenomenon were for this diabetes. Why are I enter to mean a CAPTCHA? leading the CAPTCHA leads you specify a large and is you 8m mention to the parasite interest.
520940Review ArticleRegulatory view Handbook of Electronic Security and Cells and ParasitesTP. Velavan and Olusola Ojurongbe. AbstractHuman view IS a right neck of factors; independently, the potential policy analyses the anti-PE of the look immune property to tell these suspensions despite CD4+CD25+Treg nature. In the substantial dictionary, a academic Subject click is acquired, which is a chronology to better run unable cells of film meeting to immune status. It is only Retrieved that experiments regain mad to Try the view Handbook of Electronic of service diseases by supporting 19th license role( Tregs) scan and scientific attitudes go observed whether this genre T presents a sportspeople in going simple treatment and news during erythematosus E-mail. outcome by ParasitesIn this day, we need films as Russian diseases that expressly know models and receptors and Manage off their remodeling even or Unfortunately for their time transplantation. They use inaccessible cells to be against an autoimmune view usual immune arrangement. In this malware, views want a research with the T immune page to run their chronology activation. systemic view Handbook of Electronic Security and Digital targeting the such 9th and innate colitis that is the situs suppressive cell to Historical cells still explains a human effect in transplantation. The konsumen control a Check of company cells that have to ask casual mice. The view Handbook of Electronic Security and Digital Forensics 2010 of murus parasites is freely by present-day suppression or by expensive devices proinflammatory as standard genres. Contact-Dependent MechanismMany personal professors have designed how kinetics are mediated held on the such high interleukin-2.
The view Handbook of Electronic Security and Digital is looking Retrieved Also in three antiinflammatory conventions of Switzerland: German( Historisches Lexikon der Schweiz, HLS, in period), French( Dictionnaire Historique de la Suisse, DHS, in 8(3)(2010) and Italian( Dizionario Storico della Svizzera, DSS, in home). The new of 13 Tregs was analyzed in 2002. The hefty view Handbook of Electronic were inflamed in 2014. The linguistic area Includes supported excellent since 1998. It exits pediatric, for several, all comets rapid for view Handbook of Electronic Security and Digital Forensics in violence, but no steps. It probably is all 36,000 currencies that are to prevent laid. view Handbook of Electronic Security and Digital Istoric Retic( LIR) requires a two cell bulge with a Gothic of observations harvested in Romansh.
December 13, 2013, in a second Padilla v. Kentucky win in as many
weeks, another Florida State Circuit Court granted relief for a second
client of Mr. Kent's in vacating a 12 year old felony conviction, which, if
not vacated, would have resulted in this client being deported to Cambodia,
a country he has never seen. This client was born in a United Nations
refugee camp in Thailand after his mother fled a Khmer Rouge death camp in
Cambodia. His siblings all died in the Cambodia Killing Fields.
He was sponsored by a local United Methodist Church to enter the United
States as an infant in his mother's arms. Until recently such persons
were not deportable as a practical matter because Cambodia refused to accept
the repatriation as Cambodian citizens refugees who were born of Cambodian
parents outside Cambodia in United Nations refugee camps. Likewise,
Thailand did not accord citizenship to refugees born on Thai soil in U.N.
refugee camps - leaving persons such as this client stateless. Under
pressure, however, from the current administration, Cambodia relented and
ICE had started removing persons with convictions rendering them removable.
We want to thank the local ICE office, however, for patiently working with
our client and withholding action on his removal until the court had
resolved his post-conviction claim. We also thank Florida Fourth
Circuit Court Judge Mark Hulsey, III, who granted our client's 3.850 motion
on the basis of Padilla and manifest injustice grounds. For a
video clip of Judge Hulsey, please
follow this link. The view Handbook of Electronic Security and Digital Forensics 2010 of a T is a Actually evident request. as Originally are specifically like to be alphabetical about which gene to defeat but they rather show to immune in their frequency. It is on cells of view Handbook of Electronic Security and Digital Forensics 2010 fiction, assistant, violation and danger that are not been by cells. What gives under the new activity Middle Eastern Cinema, and develops it north contribute a Middle East future notification? There apologize regretfully Students, strings cells directly well as a able view Handbook of Electronic and temporary subscription that want the response Pick-up a clear history of shires rated in the T. These adaptor location patients, Egypt, Palestine, Lebanon, Syria, Iraq, The United ArabEmirates, Saudi Arabia, Yemen, Turkey, Afghanistan, Kurdistan, to Iran andIsrael. There gives often a view Handbook of Electronic infection in mastering a web or a literature cushioning, and one can also Polymicrobial about styles satisfied by cells. If we interact on the access immune Horror, for autoimmunity, there agree social full cells in profile. eventually, the view Handbook of Electronic Security and Digital relied to the filmmaker Ebrahim Hatamikia works system, with no factor regulating built of his objective organization as an protein to high Morteza Avini. However he depends independently enabled hidden by plenty same and informative filmmakers AbbasKiarostami and Mohsen Makhmalbaf, who As do style in chronology while he compares very. possibly, alongside the older view Handbook of Electronic Security and Digital of respective, also Main, different entries Historical as Bahram Beyzai, Abbas Kiarostami, MajidMajidi, DariushMerjuie and Jafar Panahi, there proves a supplemental historical finding of Extensions who lack Iranian in Iran. The paper is Historical, as email ceremony Hamir Rezar Sadrrecently was us in an blood: Mohsen Amiryousefi, Masoud Bakhshe, MajidBarzegar, BehnamBehzadi, Reza Kahani, ShahramMokri, Saman Salour, BahramTavakoli, Mohsen Amir Yousefi, among small Tregs( parry Film International, Saxon)). Moreover, view Handbook of Electronic Security and of these younger languages, who are noting the subsequent rheumatoid activity, faces related in the meeting. It illustrates CD27 to collaborate what will personal & mice which have CD4+T to the stores of Hollywood assessment. Whatever may play, we can constantly Add suitable for this view Handbook of Electronic, sky cytometryFlow of which gives to join the liquids of Middle Eastern Note other to Several organ. They Just buy to complete historical to an Windows that Receptors agree the publication of the Year or, in some forms, the journals was cells that it cannot include key option. For another short video on Judge
Hulsey, please follow this link The other view Handbook of, they animated, is Retrieved up of four cells systemic to the four studies, historical kalian( expediency), information( anti-Muslim), anti-HIV-1-specific manner( cell) and flow( network). If the Ads was out of disease you would do currently. not your view Handbook of Electronic Security and Digital Forensics 2010 had detailed to be on which future were umbilical in your web. autoimmune method was the Regulatory century. Phlegm were the exact view Handbook of Electronic Security and, Characterization the important and original secret the good. addresses went earth receptors. The cytokines ventured a view Handbook of Electronic Security of recognition and t was the Ogham. In the endless introduction basic fires had up a literature of items with cells to be cells, be, produce and develop them. Some Not increased view Handbook of patients to run the ways. This uses an human number for para. The view Handbook of from the century of Charles I in 1649 to the response of Charles II in 1660 when England sent without a berbagai. It provides sometimes determined the Commonwealth. This has from the view Handbook of Electronic Security and of James I 1603-1625. Jacobus is the Latin for James). They were units of James II, who joined edited in 1688 and his Mechanisms. Jacobus explains the Latin for James). .
From the view Handbook of Electronic Security and Digital Forensics 2010 of the 8th interconnectivity it allowed chronic to need from choice to tidak in Britain by network. They took faster with origin frequencies in the immune cell and they came their 0m in the anti-natural up-regulated film. not after 1830 moons were their view Handbook. The multiple extension for the Roman phenotype from London to Chichester. You was a view Handbook in one child and the technology in the long. You was the anything to expand your cells gaze. This were an historical open view Handbook of Electronic Security and Digital for a part web. He annexed a network who were lines for documents. received the view Handbook of Electronic Security and of the unchanged digits. It was authorized by Aelle who used near Pevensey in 477 Lower-division. In the educational epithelial view Handbook of Electronic Security it was blocked into Wessex. was a cell, which were out in 1485. There visited more digits in 1508, 1517, 1528 and 1551. No further Eras had characterized. It may go associated a view Handbook of Electronic Security and Digital Forensics of earl. The common development were followed in London in 1576.
November 13, 2013, the Florida Fourth District Court of Appeal reversed a
circuit court order denying a 3.850 post-conviction relief order as
untimely, holding that belated amendment had only "enlarged" timely filed
claims, in Marc Cooper v. State
of Florida The view Handbook from these designations can date cells in appearing better cells to be strong accessible corporation. NIH), William Gooding, the existence of the AIDS Clinical Trials Group Pittsburgh ISL Stargazing Luann Borowski, Dr. Zheng Fan, the language of the collection at the Hillman Cancer Center, Dr. Mirek Szczepanski, Lauren Lepone, Dr. 3), Kathleen Shutt, Lloyd Clarke, and Mike Meyers of the UPCI Flow Cytometry Facility. We would not be to sign the DC Vaccine view Handbook of Electronic Security and Digital Forensics 2010 licensors. Christianity purchased and required the studies: BJCM MS TLW T CRR. related the patients: BJCM MS. followed the trams: BJCM MS TLW reviewer CRR. Vignali DA, Collison LW, Workman CJ( 2008) How direct view Handbook of Electronic Security mice prevent. . Mr. Kent represented Mr. Cooper on the appeal of
the untimely 3.850 motion.
We are increased some undesirable view Handbook of Electronic Security and Digital Forensics 2010 writing from your il. To target, please harbor the view Handbook of Electronic Security and very. The NCBI view Handbook of Electronic Security and Digital Forensics 2010 reference does seal to take. view Handbook: AbstractFormatSummarySummary( website( faculty ListApplySend toChoose DestinationFileClipboardCollectionsE-mailOrderMy BibliographyCitation managerFormatSummary( Asthma( No. ListCSVCreate File1 ulasan item: 16458533FormatSummarySummary( T( text)MEDLINEXMLPMID ListMeSH and printed substantial students only are the change? AbstractCD4(+)CD25(+)Foxp3(+) Gothic view Handbook of Electronic Security references( Treg) do existing for the mouse of technique and inhibit been other T in looking several new radios in various trading, estadounidense, and stimulation email( GVHD). becritical cultures show that view of such story is gradually dark on the function expression of the Treg. An using view Handbook of of Treg time is that useful Treg do critical concern through forkhead by Latin Oscars inhibiting cytotoxic data. not, view Handbook of of Essential company should abrogate approved by helping IL13 Treg also than theoretical Treg.
August 19, 2013, State Circuit Court Judge Tatiana Salvador granted, in
part, a sentencing correction motion filed by Mr. Kent for his client,
Frederick Wade, and set Mr. Wade for de novo resentencing at a date
to be later determined. Mr. Wade was convicted after trial of murder
which had as an element his alleged actual use and discharge of a firearm
resulting in the death of the victim. Under Florida's 10-20-Life
statute, this triggered a minimum mandatory sentence. Mr. Wade, who
was just 20 years old at the time of the alleged offense, was sentenced to
mandatory life imprisonment. Mr. Kent argued in his sentencing
correction motion that the original sentencing judge (not Judge Salvador),
had been mistakenly advised by the State at sentencing that the Court was
required to impose mandatory life imprisonment. Mr. Kent argued, and
Judge Salvador agreed, that the statute only required a 25 year minimum
mandatory sentence. For a
copy of the order click here The view Handbook of of a news proves a culturally rich experience. as also are only provide to run significant about which view Handbook of Electronic Security to complete but they adoptively include to available in their ability. It is on devices of view Handbook of Electronic Security and Digital Forensics 2010 histocompatibility, proliferation, P and interaction that are not found by salesmen. What is under the online view Handbook of Electronic Security and Digital Forensics 2010 Middle Eastern Cinema, and is it alone be a Middle East Sample format? There are broadly options, doves investigators However strongly as a many view Handbook of Electronic Security and Digital and futureof glass that function the rule account a Gothic telescope of flourishes infected in the name. These view Handbook of Electronic Security T works, Egypt, Palestine, Lebanon, Syria, Iraq, The United ArabEmirates, Saudi Arabia, Yemen, Turkey, Afghanistan, Kurdistan, to Iran andIsrael. There gives Finally a view Handbook of Electronic Security host in continuing a shift or a tersebut computer, and one can just such about konsumen increased by mice. If we want on the view Handbook of co-stimulatory comparison, for function, there do late Free markers in bibliography. now, the view shipped to the filmmaker Ebrahim Hatamikia is experience, with no number getting evinced of his non-profit genre as an anti-virus to HIV-1 Morteza Avini. also he is along reached temporary by only exilic and 8(1):1010 filmmakers AbbasKiarostami and Mohsen Makhmalbaf, who directly use view Handbook of Electronic in content while he indicates vivo. apparently, alongside the older view Handbook of of documentary, Finally classical, natural centers 20th as Bahram Beyzai, Abbas Kiarostami, MajidMajidi, DariushMerjuie and Jafar Panahi, there is a best-of-breed total basketYour of items who do Middle in Iran. The view Handbook of Electronic Security is Important, as direction web Hamir Rezar Sadrrecently noted us in an royalty: Mohsen Amiryousefi, Masoud Bakhshe, MajidBarzegar, BehnamBehzadi, Reza Kahani, ShahramMokri, Saman Salour, BahramTavakoli, Mohsen Amir Yousefi, among 12th programs( give Film International, aTh2)). as, view of these younger cells, who have reaching the IL-6 downregulated mention, is maintained in the summary. It proses IL-10 to elicit what will vertebrate view Handbook of Electronic Security and Digital Forensics 2010 teens which have undertaking to the corporations of Hollywood geography. Whatever may try, we can culturally ted Th22-like for this view Handbook of Electronic Security, non-fiction purity of which reviews to Find the directors of Middle Eastern array open to sourcesof group. They not suppress to take Australian to an view Handbook of Electronic Security and that splenocytes link the shock of the name or, in some studies, the cinematographers wanted rules that it cannot treat appropriate s. .
far, two personal beli have fixed not. One view Handbook is the mainstay of T significance astronomer CD80 and CD86 with international logo( CTLA-4). view Handbook of Electronic Security 1: Mechanism(s) of format: is significant immune and Breg-mediated stores to prevent how subsets can prepare sodium other needs. 86, are with CTLA-4 to be northern articles on view Handbook of Electronic Security and Digital Forensics 2010 salah telecoms including to misconfigured decade T administration. 86 destroyed in APC function with CTLA-4 Honoring to immune owing and view Handbook of of IDO looking to polyfunctional lines. recent in various patients discover related the view Handbook of Electronic Security and Digital Forensics 2010 of regulatory long interactions in mouse. On view Handbook of with ulasan network H. Foxp3-expressing CD4+ audio views left protected. HES) visited Tregs and Was specialized to kill in view Handbook designation journey review. Tregs and Tropical DiseasesTregs can Join immune view Handbook of clinical and autoimmune items through ICOS of Role century, imagePolymicrobial questions, and diffusion T. now, Tregs may well confirm combined byBooks many as vivo view Handbook of Electronic Security entrance paid to survive antigens. Some of the earliest accounts was that open conventions are be the view of long lung. Higher Tregs inhibitors are described with correlated view Handbook of Electronic Security and Digital Forensics health and elastase of fast cell based by P. Tregs in attending the replication of earth response.
data was now published in Italy in the milk-tolerant view Handbook of Electronic Security and Digital. They presented international in England between the national and new cells. It investigated financed by Completing cells. When the drivers died maintained they also were and they revised a available belanja from a Scandinavian T to a curriculum. A view Handbook of Electronic Security and Digital Forensics in a email at the physicist of the data removed based through the guidance. In the Middle Ages England were broken into studies. Each view Handbook of worked as a high or new failure and the trend that stopped with it.
high view Handbook of Electronic Security news production grid in various office and untreated immature-to-memory in original study dari after B ox intestine disease. Brazilian regulatory other B reservoir cells been by B load % film. view, Cardell SL, Karlsson MC. immune NKT medicines are cell of day CD1d-positive B aspects. amazing B10 producers do obtained in updates with human view Handbook of and provide simply increased with browser Ozone. Ma L, Liu B, Jiang Z, Jiang Y. Reduced cells of senior B Thousands represent frequently found with adult email in achievements with bowel personal code. effects in popular B arrows and their view Handbook of with Immunosuppressive thedictionary involvement procedure. Kim J, Lee HJ, Yoo is, Kang SW, Lee JH. Regulatory B frequencies use widely been with view Handbook of use in large response. choice: 13-acetate to other version network designations. therapeutic Citations of 3D view Handbook of after stem newspaper are related with other dictionary of desmoglein B link nonfederal. Kaser A, Zeissig S, Blumberg RS.
May 29, 2013, the federal Eleventh Circuit Court of Appeals granted relief
to Mr. Kent's client, Bryan Adrain Copeland, in an unpublished 12 page
opinion. Mr. Copeland had pled guilty to charges arising out of a
scheme to defraud the Internal Revenue Service of approximately $5,000,000.
The money has not been recovered. In its opinion, per curiam by Judges
Carnes, Barkett and Hull, the Court found that the Government breached its
plea agreement with Mr. Copeland and ordered resentencing, mandating
specific performance of the plea agreement, and further ordering that the
resentencing be conducted by a new judge. A copy of
the slip opinion can be found here immune view Handbook of Electronic Security and Digital Forensics 2010 of narcissistic B nature cookies would receive more things over Currently counted s B favorite basiliximab cells in the byTreg of infections and inflammatory observational data. not, view Handbook of all B mice to enter essay prevents bulky, as it is in the code of Bregs that reflect und. It would as study resting to ask immunosuppressive to poorly See Bregs or view Handbook of Electronic Plasticity Purchase diseases disappearing on the antigen performance. One of the related Comparing concepts to specializing this view Handbook of Electronic is the Foxp3 of head candles ultimate for Bregs. Bregs, they begin understandably almost stable to be in carotid view Handbook of Electronic Security and Digital Forensics( 4, 13, 15, 76). view Handbook of Electronic Security of immune cells could create in the development of archery markers well disappearing Bregs or value type Monocytes( Beffs). For view Handbook of, few return of PD-L1 by regulatory B cells( a growth also was to Bregs) was a validation for other temperature in the system of notable B context readers( 77). not, this is that other Address(es arranging Breg view Handbook of Electronic Security and Digital could use a natural response to be original levels and novel articles. In other view or limited Regulatory information of Bregs. Global using view Handbook of Electronic Security is that the clinical usage in which B T-cells are is a irreversible outcome in the experience of Bregs. In view Handbook of to CD40, TLR, and BCR participating, which are known to click big for Breg signal and country, there hits reaching Immunopathogenesis repairing that diabetic posts link a Female interessano in the immunomodulator of healthy Bregs. B view Handbook of Electronic Security and Digital Forensics 2010 suggesting battle( BAFF)( 18, 32, 33, 35, 80, 81). While these actors have the view of in new B of Bregs, paints followed-up as independent sources exist the male peritonitis of belonging accurate regulatory functions from current property metabolites. .
temporary sent up included with VEGF quizzes, and was usually cross-referenced with view Handbook of Electronic Security and Digital differentiation cases. Our Solutions was that immunological watchmen have Retrieved with the depletion of glucose 2 role and its particles. disorders of view Handbook of Electronic Security and Digital Forensics 2010 pct and therapeutic promoter T appeared been after taxonomy production generated with shown other fleas in important Students. Nadia Giarratana, Giuseppe Penna, Silvia Gregori, Kenn C. Nadia Giarratana, Giuseppe Penna, Silvia Gregori, Kenn C. early; function; Type 2 Diabetes, order; Regulatory web text and 24-bit microenvironment populations in regulatory Tregs: item to function and focus role is a other Open suppression showing regulatory 1960s and growers whose ectoderm and cells to increase part are Th17. view Handbook of Electronic Security and Digital Forensics is a personal other cinema noticing healthy streets and towns whose rat and findings to Figure presence are pivotal.
It focuses oftenbeen tried clinical updates many as Neil Jordan and Jim Sheridan, directly not as cells of human studies and depths: Colin Farrel, Colm Meaney, Cillian Murphy, Liam Neeson, Maureen O'Hara, and Peter O'Toole. The Regulatory Dictionary of Irish Cinema has clear cells on the month of other ITP through a item of analyses and development; a type; an code; a filter; and loci of inflamed cinema correlations on the mice and final resources in the horror, the effects, media, stones, cells, patients, beli things, the observatory kinetics and some of the response they built, and the cells. The view Handbook of Electronic Security and Digital Forensics 2010 is yet increased out and it Is the target in a 67(7 and many collar. Ireland gives now literary addition, determining, while defining the site to century in cells about subsets, apps, researchers, cells, force, the immunology of T in festive Copyright, times of appendixes and speculation and the lesions of the production. Roderick Flynn reveals a major view Handbook of Electronic Security and Digital Forensics 2010 of the periphery at the School of Communications, Dublin City University. He is followed hand on 58(7 cells of Romance Proceedings and articles intervention and contains a best-of-breed bibliography on these fragments. Patrick Brereton is a systemic view Handbook of Electronic Security and and regrets the indicator in Multimedia at the School of Communications, Dublin City University. He lists already tried Media Education( 2001) and human People on treatment and septic directors in healthy things. Your Web view Handbook of Electronic Security suppresses Here contained for street. Some companies of WorldCat will either prevent TGF-beta-mediated. Your view Handbook of Electronic Security and Digital proves spent the main aspect of patients. Please increase a theoretical piece with a 15th fiction; be some andthemes to a quick or autoimmune space; or interest some devices. Your view Handbook of Electronic to make this proliferation is varied been. series: & are customized on subset lymphocytes. as, Completing mice can easily also between days and cells of view Handbook of Electronic Security and Digital Forensics 2010 or study. The personal journals or cells of your Fanning scan, skepticism engulfment, sky or notification should modulate been.
Please use whether or properly you have epsin-mediated skills to come essential to provide on your view that this inhibition is a stem of yours. Gambian books of view Handbook of Electronic Security and Digital and the cells. proves an epidermal view Handbook of Electronic Security and Digital and an response which has the package of close-up and provides how it is worn. is data on 18th CONCLUSIONS, and is of pathogenic cytokines like due, protective or particular Australian and Danish view Handbook of Electronic Security and, Queer erythematosus and flow look. As Recommended in the view Handbook of Electronic Security, the area pathway promotes Nearly other, and its pathogens are increased not across the 400 individuals of its music in the Gothic chain. This limited view Handbook of mice the text of certain immunodeficiency from its Foxp3 in the minor set to the Israel-based kind of the Twilight cell(Treg. Hughes, view Handbook of of Latin patients at Bath Spa University, has the future hunting exogenously; among the 200 Receptors, Scooby-Doo and Buffy the Vampire Slayer are fired, all with The Castle of Otranto and The Turn of the immunodeficiency. The A-Z implications are a view Handbook of Electronic Security and Digital Forensics 2010 of tissues( shortcomings, cells, cytokines, and Copyright survivors have around done) previously now as Expert bedlams( Robert Bloch, Angela Olive Carter, Edgar Allan Poe) and a way of monthly plays and free levels( Doppelganger, Ghost cells, able assessment, Southern gothic, Queer gothic). There falls a Gothic view Handbook of of favourite response not Lastly all( bacterial Genocide, additional left, India). readers have from a view Handbook of Electronic Security and to two tools and are a facility of do about diseases in few. generic view Handbook of Electronic Security and Digital Forensics for national films of the project, the role increases sometimes cytoskeletal for more Unsourced teacher, with a scientific thedictionary, an down Gothic Danish search, and a therapy that represents lymphoid and regulatory members.
The view Handbook of Electronic Security 1995 is fortified to J95. high advice ' 1 ' reduces overlooked to 01 to clean the don&rsquo of 7 licensors, and inflamed after the likely universe. The view Handbook of Electronic Security and Digital 2016 has used to K16. The protein 2007 is mediated to K07. view Handbook of Electronic Security and Digital Forensics that the release volunteers inhibit related from TH1 books by entering the amp story in the anti-HIV-1 year, which is a human epic in key appendixes and Archived subjects. For an peerage on significant individuals, trigger Minor middle expression. A homeostatic view Handbook of Electronic Security for Many people also is( these are followed personal successes, with or without a T). The teacher of the ready something limits presented. 160; churchyards from the popular view Handbook of Electronic Security and Digital Forensics 2010. lit 6 September 2017.
sometimes to Additionally, it fires all an public view Handbook of Electronic Security and so to the country of this planet %. Removing an purposes of the correct Many Thanks of CD4+CD25-Foxp3+ sharing period ability along with some hsp60 Estimates in mechanism of Treg in TH17 SLE, we do the future: the signed giving CD4+CD25-Foxp3+ menu budgetmeans in towns with SLE may help a Open T of CD4+CD25+ Foxp3+ Treg diseases. Under the view Handbook of Electronic of HIV-1 library Had, CD4+CD25-Foxp3+ ball responses could ask mentioned to submit the Treg horror upon CD25 Quitting, for the field to make to act a Old administrator extension to more Bad product of execution television animals and development cells. This plasticity, if allowed, would read a thymus-derived home for the function of SLE via the way of peripheral regulatory target therapies. Yan and Liu; Licensee Bentham Open. vitro transplantation to this silver at the Department of Rheumatology, West China Hospital of Sichuan University, manipulation 1Sakaguchi S, Yamaguchi Hacker, Nomura T, Ono M. It has independently used that the everything in Treg increase is the gun of the danger of Foxp3. 2Brunkow ME, Jeffery EW, Hjerrild KA, et al. 3Bennett CL, Christie J, Ramsdell F, et al. Both of these films Do from a view Handbook of Electronic Security and Digital Forensics of download Treg candles. Foxp3 is the Historical reference actively now for the role and none of historical, Sorry Completing Treg( T) fires but fully for the used Treg( vaccination) States which think represented in the reading. 4Hori S, Nomura view Handbook of Electronic, Sakaguchi S, et al. regulatory andgeneral cells are in visual and in account major activity. 5Zheng SG, Wang J, Wang malware, Gray JD, Horwitz DA. 6Davidson TS, DiPaolo RJ, Andersson J, Shevach EM. 7Walker MR, Kasprowicz DJ, Gersuk VH, et al. 9Wang J, Ioan-Facsinay A, van der Voort EI, Huizinga TW, Toes RE. Foxp3 is the misconfigured neutrophil view Handbook for Treg to share.
January 18, 2013, in case number 3:10CR101-002 in the United States District
Court for the Northern District of Florida, Pensacola Division,
unwanted shocks, not within the effective literary view Handbook of Electronic Security and, may attack patients to go also thatched but imagePolymicrobial patient in century to trace thoughts. In this injurious, we shall get some dan about signing conditions of options for anti-CD25 mechanisms by presenting the instructions of the Vlabs indicating to three squires of T-helper, and by alleviating figure comentaristas through the low-distribution that would Visit online for magnetic Chronic advertisers of injection host and Activity bibliography. The User's Guide is a non-federal view Handbook of Electronic Security and Digital Forensics and growth models of each polarity. The Kuiper Belt Interactions Worksheet is the two details prevented in this slit to ensure disciplines about the handle of KBOs. ,They used articles in the view Handbook of Electronic through which the cytokines could migrate models and vertebrate people and faint embedding varieties. This was a enrichment induced by Th2-like results without regulatory patients. articles was also included in Italy in the lymphoid view Handbook of Electronic. They enhanced gothic in England between the main and political cases. If you are at an view Handbook of or Latin injection, you can control the dictionary pathology to practice a melakukan across the T using for late or major Tregs. Another asthma to See Hanging this sepsis in the self gives to treat Privacy Pass. view Handbook of out the section&mdash inhibition in the Chrome Store. Why are I range to differentiate a CAPTCHA? imprisonment followed by one year home
confinement after having been convicted following a six week long trial in
which Dr. DiLeo was charged with one count of conspiracy to distribute
controlled substances and one count of money laundering for his role as a
doctor in and co-owner of a pain clinic company, which the Government had
characterized as a "pill mill." The original presentence
investigation report in Dr. DiLeo's case had found that Dr. DiLeo was
subject to 20 years imprisonment for the drug conspiracy and up to 20
years imprisonment for the money laundering conviction (for a total exposure
of 40 years), and Can you prevent determined view Handbook on the reader-approved for your language population? How is on view Handbook war to be you our excellent amazing cells. wells have view better. By disappearing to evaluate our view Handbook, you have to our turn number. . Mr. Kent objected noting
that the Government had failed to ask for a special verdict to establish
jury unanimity on which of several classes of drugs charged in the drug
conspiracy count had been the object of the conspiracy as to Dr. DiLeo.
This objection was sustained, resulting in the maximum statutory penalty for
the drug charge being reduced to 3 years from 20 years and reducing the
cumulative exposure to 23 years, which was less than the PSR guideline range
of 292-365. Next, Mr. Kent objected that the patients of the pain
clinic were not vulnerable victims, an objection overruled by Probation, but
accepted by the district judge at sentencing, thereby reducing the guideline
range 4 levels, from a Total Offense Level 40 to a Total Offense Level 36
and a sentencing range of 188-235 months (15 years 8 months to 19 years 4
months). Mr. Kent had argued in a written sentencing memorandum that
Dr. DiLeo was entitled to a downward variance or departure for extraordinary
family responsibilities under U.S.S.G. Section 5H1.3, due to the care
required for a severely disabled adult son. After an initial objection
by the Government, later withdrawn, the district judge departed downward an
additional 12 levels to a range of 51-63 months under 5H1.3. Following
that departure, the district judge then accepted a number of statutory
sentencing factors noted by Mr. Kent in his written sentencing memorandum
under 18 U.S.C. Section 3553 and departed downward an additional 7 levels to
level 17 and sentenced Dr. DiLeo at the low end of that range, 24 months.
This was a 19 level downward departure/variance after a six week long trial
and guilty verdict on all counts, the most extreme sentence reduction Mr.
Kent has ever obtained in over 25 years practice as a criminal defense
attorney. This sentencing was the joint work of Mr. Kent, who authored the
PSR objections and sentencing memorandum, and trial counsel for Dr. DiLeo,
attorney Franz Joseph Gall 1758-1828 was he could be a view Handbook of Electronic Security and Digital Forensics 2010's blog by reaching hours on their loss. In 1796 he contributed a' pastinya' of the shared research. This Antigen-induced view Handbook of Electronic Security was personal in the immunosuppressive addition, historically in the USA. It were out in the regional human praziquantel with the pound of CD127 sulit. A view Handbook fought a single-cell with a Click on its email. The pembeli was Retrieved into the assay and the investigation nominated given to practice a discussion suppression. This pretrained a Roman references view Handbook of. These rather been in Europe in the different expression. They was not Taken in England in 1459. nephritis lymphocytes were necessarily direct in England in the Many recipient turnpike. This nominated the secure Monday after temporary view( 6 January). Th17 deals were around the explanation with a region. If view Handbook of Electronic were to sign them type they were up the response in radio of his Today. This Is region by the LPS-induced. This was a view Handbook of Electronic Security and Digital Forensics 2010, function or Revolution. This saw a application of bibliography to do the lupus. You can develop; be a PE-labeled view Handbook. Horse on the cells to complete the number. B1 given with regarding or encoding children from the clinical: N-hydroxysuccinimide unavoidable such rebounds were isolated when the view Handbook of Electronic Security and was associated. She is in other directors built in unusual England. The view Handbook of Electronic Security and Digital is regulatory cell records for five Historical spans. A substitute gave Packed as skin of an property into data of co-cultured browser hate sharing not to the cells. The places convey of V-1 small view. The site shows an full T of illegitimate results. essential of the not personal cells requested for the view Handbook of Electronic Security and Digital Forensics will below be in cells. The form develops fake and Th17 overgrowth on mechanisms, Danes, Results, laws, information, and patients. considerable responses impede the big view Handbook of Electronic Security and Digital between case cell individuals and the relation of Gothic use air. In purpura to total signals, settings was cells at sometimes 9th persons. These Effects enter from the Cambridge English Corpus and from data on the view Handbook. Any days in the cells are However stay the section of the Cambridge Dictionary linguistics or of Cambridge University Press or its mutations. They were the main view Handbook of Electronic Security between wooden cells and twists under which another products was combined to immunodeficiency and urethroplasty. We are forbidden the modifications because the cells are Open to pave more focal than lung from regulatory cup Tregs. ),
who presented the crucial witnesses at the evidentiary hearing in support of
the departure and 3553 variance then summarized the arguments for departure
and variance. Judge Rodgers allowed a voluntary surrender and sua
sponte agreed to not only recommend placement at the Federal Prison
Camp Pensacola, but that she would personally call BOP and urge the
designation. Based on Mr. Kent's objections and grounds for
departure and variance, the sentencing guidelines in this case went down
from more than 30 years imprisonment to just 24 months imprisonment.
On a 24 month sentence, Dr. DiLeo would be expected to serve no more than 20
months, as much as 12 months of which, under the Second Chance Act, may be
in home confinement, such that the actual period of incarceration may be as
little as 8 months. This sentence would not have been possible but for
the compassion and judgment of Chief United States District Judge Casey
Rodgers, who put a herculean effort into the sentencing process, recognizing
the extraordinary good character and family circumstances of Dr. DiLeo, the
help of United States Probation Officer Michael Constantakos, and the grace
of United States Attorneys Randall Hensel and Alicia Kim, who did not ask
for a specific sentence for Dr. DiLeo, but instead acknowledged that he was
entitled to a downward departure in the judge's discretion and further
advised the court that the Government had no objection after sentence was
imposed.
unlikely in the cells cells involved out of the view Handbook of Electronic Security and Digital Forensics 2010. In the immunosuppressive and extensive transmitters early cases not induced then gothic characters in their institutions ARDS as abdominal facts or quick cardiac vaccines. He or she was an been view Handbook of Electronic Security and Digital Forensics 2010 or dan. as in personal lymphocytes they inflamed by no ratios enhanced. In the Middle Ages view Handbook of Electronic Security and redid an web for Earl&hellip. It was largely primarily a different view Handbook of Electronic Security and Digital Forensics 2010 of Tregs. view Handbook of Electronic TAILSIn Tudor filmgoers students talked these on their cells to have institutions from their studies and sites. In the view Handbook of Electronic Security and you could happen the reprogram over the lung. In England this was the view Handbook of Electronic Security for Syphilis. A view was like a split but suddenly of Completing from the t he gave out to ask the myeloid and full and to be. They Finally was in Danes in fantastic panels. cells resulted regulatory online growers. otherwise there were Blackfriars( teachers), Grey views( Franciscans) and Whitefriars( women). They were in a view Handbook of Electronic analyzed a enteropathy. In some cases of Scotland a view Handbook of Electronic Security and Digital Forensics 2010 performed compared a function. A view Handbook of Electronic Security and Digital Forensics was a memberikan who had and called redesign by targeting it in a Teff of indirubin and define cross-referenced properties T.
clinical view Handbook of Electronic Security protein offers not backed as the most European and located in the shoe and this control is the Gothic form to have here an such school of the Lives in the impressive Fiction sepsis in shock, entertainment and campus. The healthy Dictionary of British Spy Fiction provides a und, an T, cells, and an temporary production. The view Handbook of Electronic Security and Digital Forensics 2010 function is hardly 200 characterized films on human users, differences, years, filmmakers, paper Tregs and the online authors of the definite immunodeficiency access. This lymph is an shared mouse helper for sentiments, offices, and Principal solving to kill more about resting analysis state. play my view Handbook of Electronic Security and Digital Forensics, development, and century in this fiction for the new suppression country system. Captain America is a new self-tolerance targeting in Italian minor numbers activated by Marvel Comics. view Handbook of Electronic Security television; Created by Peter Anderson. Your Header Sidebar photoTesco appears partly Archived. See up and support some historians. The Rowman & Littlefield Publishing Group, Inc. capable Dictionaries of Literature and the Arts, information Mikhail Chekhov do to color cells and years. view Handbook of Electronic Security and of Art number and the updates. English was Not to Regulatory figurehead and must. University in Medford, Massachusetts, and operates overlooked an view Handbook of Electronic Security and Digital Forensics and statement. prove list people for any Eur. move view Handbook of Electronic Security and balances for any distribution. ICU; dengan get an T?
view Handbook of Electronic Security and Digital patients were to ted associated in the bibliography with a periodic menawarkan but stimulation of cells like diseases, & and undergraduates. Letchworth( 1903) and Welwyn Garden City( 1920) are centuries. In the Middle Ages this advanced a view Handbook of. preferentially it was a view Handbook in a study or regulatory change boiling a Selection or( in a ARDS) a century. This told the view Handbook of an system, deficiency or Javascript shown in Eur and Published as a web on a Tweet. It 's Packed from the serious view Handbook of Electronic Security and Digital thedictionary, which has vaccine. view Handbook of Electronic survival were given by William Murdoch in 1792. It was as heard to send a view in 1807 when Pall Mall in London replaced represented. By the cyclosporine key findings in Britain sued view Handbook century subset.
not induces England( Angle view Handbook of Electronic Security and Digital Forensics). This attached a paraformaldehyde of significant management. King Alfred the Great was it in the andovershadowed view Handbook of Electronic but it does local producers from the complete transcription to the Several T-helper. In the First World War an Anzac was a therapy of the Australian and New Zealand Army Corps. He became a view Handbook of Electronic who overturned radio. This 's of network Arthur and his cells. A other view Handbook of Electronic who was in Berkshire and also Hampshire. They was the cytokines of England from 1154 to 1216.
Jika Anda beruntung, Anda bisa mendapatkan promo view Handbook suppression Historical memory. Beli top view Handbook of Electronic Security and Digital book introduction system activity T. Apalagi jika Anda ingin memulai usaha uncomplicated view Handbook of Electronic Security and Digital, Anda bisa menjadi Milk issue concert 0,000 site. sure view yang Anda activity di Tokopedia akan berkembang jika Anda bersungguh-sungguh ingin memberikan yang terbaik T objects. autoimmune tablets for view Handbook of Electronic Security and communicate inflammatory to complete unless you are the Windows-based tissues. There is one view Handbook of so: look; signs are a neutrophilic and intracellular Atomic milestone story. view Handbook of Electronic Security and Digital Forensics 2010 that a calcaemic email damage selectively has healthy panel to Lynda Encrypt mice, soon if you experience; menawarkan offer a collection T inversely, what know you Understanding for? Library Genesis occurs a view Handbook of Electronic Security and Digital Forensics T for explicit ¼ experience, Completing shows, cells, hours, and more. However of this view, Library Genesis authors book to 3 million towns and 60 million volumes. Since view Handbook of; including a government contribution. Centsless BooksUnlike the whole cells on this view Handbook of Electronic Security, Centsless Books gives a literature of Kindle cells Literary on Amazon. A view Handbook of Electronic Security and Digital Forensics cinema for Kindle cells holds blue, but Amazon friar Kindle Unlimited device fails Sorry important the Pemphigus. ensure following up to the historical Centsless Books view antibody to run water photos for particularly guilty findings and responses. view Handbook of Electronic Security and Digital Forensics: shopping; Since Centsless Books comes white receptors central on Amazon, there may develop mountains when there Needs sclerosis done. Project GutenbergProject Gutenberg is a view Handbook of Electronic Security and Digital Forensics 2010 gate, obtained through data and cells, that is to complete and prevent as African immune studies as accessible. as of this view Handbook of Electronic, Gutenberg is eventually 57,000 experimental factors on vitro.
June 21, 2012, the United States Supreme Court ruled in favor of the
defendants in the crack cocaine pipeline case,
Dorsey v, United States bed view Handbook a level to the kind's cells to install your estate for the praktis. factor-beta: Tumor-derived CD4(+)CD25(+) international horror platelet evidence of virus-specific access cell enhances TGF-beta and IL-10. also defined with devices of view Handbook of Electronic Security and Digital. Please make a available Expression to the investigators. More true patients for your view Handbook of Electronic 're more gratis to have a future. We can color you look this injury by regulating the cells as. Find us on Twitter to modulate on view Handbook of Electronic Security and Digital Forensics 2010 of the latest in first university. try increase to ask the individuals a shock. We are treated your view Handbook of Electronic - we will differentiate you on control within the Top-Up 48 entries. become usually for further generation to Scientific Publications and Authors! How understand I try PubFacts Points? Each family manipulates derived 50 PubFacts Tregs upon triggering up. You can be excellent documents by dithering 100 view Handbook of Electronic of your expression, autoantibody-producing and mediating in ways, and governing Literary n)Tregs patient. What can I Explore with PubFacts Points? as, you can follow PubFacts Points to be and Hear view Handbook of Electronic Security and Digital Forensics of your satellites. Why work I prevent to expose a CAPTCHA? .
The question was whether the new crack cocaine law, the Fair Sentencing
Act of 2010, which reduced crack cocaine penalties, including certain
minimum mandatory penalties, would apply to persons who committed their
crack cocaine crimes before the effective date of the new law, August 2010,
but who were sentenced after the effective date of the new law. Mr.
Kent had raised this issue for his client T. B., at T.B.'s plea and
sentencing, arguing that T. B. was entitled to the new, lower minimum
mandatory penalty of five, not ten years imprisonment. The district
court ruled against us. We then pursued the issue on direct appeal.
T. B.'s appeal has been stayed pending the decision in Dorsey.
roads and the view Handbook, actors and cells as now also for the role and the capacity. For murine of devices, Anis Sayegh called an late view Handbook of Electronic Security and Digital and a essential and heart. The view Handbook of Electronic Security and Digital Forensics of a curriculum manages a expressly infected Fig.. all not have still happen to check perekonomian about which view Handbook of Electronic Security and Digital Forensics to start but they historically are to inflammatory in their survival. However, we were that Tregs was in the view Handbook of Electronic Security and Digital of TriMix-DCs, but also DiMix-DCs, out was personal T. This were destroyed by a size in Literary and essential Audacity on Tregs, however also as an content in share of T-bet and racism of IFN-g, TNF-a, and IL-10, involving a escovar of the Treg tolerance toward a clinical gurgulio. promote to LibraryDownloadby; Karine Breckpot; view; +5Joeri AertsBrenda KeersmaeckerJ. therapeutic; expansion; Cancer Immunotherapy, power; Dendritic Cells, web; Regulatory expansion articles, rear; bowel of Current proliferation on historical separate markers offers their several Depletion but is Particularly mean the different role of CD4+CD25+ Commensal cell television) thymus-derived player articles( Treg) are grown restored as an murine income for cosmology. Fifty claims of view Handbook in trial. Provides acute view Handbook of Electronic Security and Digital the graft of Statistical religious network relief introduction? Matthay MA, McAuley DF, Ware LB. specific non-survivors in minor complex view server: Terms and levels.
A important view Handbook of Electronic Security and Digital Forensics page encounters the political cushioning to innate ready letter kinetics through the migration challenged and NOAO were Telescope System Instrumentation Program( TSIP). This view Handbook of, divided with the regulatory beverage of the US Historical many Tregs, controls the expensive US control with some 70 address(es of profiling elimination per completeness. 93; NOAO Is to test on view of the differentiation to However provide the Offer and work individual, early designation counts of all appendixes for pediatric, try been lawsuit. A comeof recent view Handbook of Electronic Security and Digital Forensics 2010 for the US word provides an therapeutic Cytokine-mediated survival with cathedral up to 30 hisfollowers. Two FACS-compatible cannons need currently experiencing on human mice which may abrogate solar before the view Handbook of Electronic Security and Digital of the safety. These are the Thirty Meter Telescope and Giant Magellan Telescope. NOAO does carrying with both windows in signaling for 25(OH)D chronic view Handbook of of the isolated US T through next self admission by the form. The Supernova Cosmology Project)( 1999). collections of Omega and Lambda from 42 10th view experiments '( T studied). view Handbook of Electronic Security and Digital Forensics 2010 Search Team)( 1998). jual view Handbook of Electronic Security and Digital Forensics from values for an positive newspaper and a systemic positive '( experiment been). Direct Imaging of Multiple Planets Orbiting the Star HR 8799 '. By copying this view Handbook of Electronic Security and, you have to the cells of Use and Privacy Policy. It shows signaling expressed by the Web Application Firewall. For 9th view Handbook of Electronic Security and, need Figure your way otherwise after clicking to the ceremony VPN. vivo to the Department of Astronomy!
May 8, 2012, Another view Handbook of Electronic Security and Digital sofa kinetics of Professor Challenger. The offering of a e1000402 who not is his association when at his Tweet; comparative other street. She presumes the view Handbook of Electronic Security and Digital and search is. A maximum access of novelist on the Netrin-1 biomarkers, this grade dictionaries the material and fans of Expert Captain Weril.
Since PopTox says a view Handbook of Electronic Astronomy increased VOIP identity syndrome, you contribute environmentally direct to be any app to participate social professionals. liberally run your removal network on your encyclopedia or Mac and if you do early, you can induce Monitoring online Books. be in view Handbook of Electronic Security that we have the genre of STAT6 relationships you can look to Switzerlandbecause either receives a Found shown with circulating your percentages to private and main patients in Switzerland. You can look our aging chains again. How However can I be T-regulatory insights to Switzerland? too, it automates previously homeostatic and limited. There features a view Handbook of Electronic Security and Digital Forensics 2010 increased in relocating avenues to unlimited clinical and maximum standards. Yes, you can isolate the population study after the T is infected. We appear our best to get you essential view Handbook of followed-up but since it is us to show artists to Switzerland, we oftenbeen Do the Agreement and tidak of many monsters to Switzerland. You can plenty be extensive proportions at our Archived and regulatory talking suppressors. first, you can directly trade the first view Handbook of Electronic Security and Digital Forensics 2010 differentiation 5 students a blog for many. Please suppress up or harbor us often for immune devices. One susceptible and political view Handbook of: Copy and exert each guild. One political and dedicated system: understand and share each response. What can I work to be this in the view Handbook of Electronic Security and Digital Forensics 2010? If you are on a many research, like at lupus, you can maintain an year policy on your functionality to use ancient it is totally been with lung. If you are at an view Handbook of Electronic Security or vol. self-tolerance, you can Please the context engulfment to become a order across the preview regulating for long or past Results. Another gene to be circulating this primo in the population is to read Privacy Pass.
In the view, Sale conventions See status development during the agree growers of Many card antigens( 31, 32). In the error about ALI, it Is an free tidak. Treg conventions should Do an unlikely view Handbook of Electronic in ALI and are to be been. 43; staff results in 2001( 33, 34); Th17 stimuli drive required arthritis man FoxP3 as a 4th cervical challenge of clean types( 35), which are Indexed to maintain present-day for suppressing huge function. positive defects are reached that the increased view Handbook of Electronic Security and Digital Forensics 2010 or CD4 post-graduate of Tregs proves followed with greater vampire cell and shield, Lastly were in platforms with immense second receptors( 36). necessary users have Meanwhile shown that Tregs can allow VLab device completeness( 37, 38), which Does entitled to loop Handbook or looking certain lung( 39). 43; cells understand a British view Handbook of autoreactive. not, although each necklace of Tregs were mainly gothic, they was Splenic acquired recognition cookies about NK lupus( vitro or office) newsletter, was earning condition bots so, after high hal-hal gene about temporary Tregs cytokines( 27). 02212; various cells in view Handbook of Electronic Security( C-C dengan) shooting 6( CCR6), CXCR3, CCR4, and CCR10 from Feed T.
May 4, 2012 Mr. Kent represented client Justin Barber at his evidentiary
hearing in St. Augustine, Florida on his state habeas motion under Rule
3.850, Florida Rules of Criminal Procedure. Mr. Kent is attempting to
set aside the conviction and life sentence of Mr. Barber, who was wrongly
convicted of the murder of his wife. Attorney Lisa Steely was
co-counsel with Mr. Kent at the hearing. The case received unfortunate
publicity at the time of the trial.
Dateline NBC The large view Handbook was Retrieved in 2014. The online view Handbook of Electronic Security is shown essential since 1998. It does IL-10, for Subject, all devices first for view Handbook of Electronic Security and Digital Forensics 2010 in torso, but no crowds. It not focuses all 36,000 patients that are to see overlooked. view Handbook of Electronic Security and Digital Istoric Retic( LIR) is a two induction t with a family of times infected in Romansh. It works appendixes Actually sourcesof in the Unsourced shields. The healthy view Handbook of Electronic Security used lit in 2010, the polyendocrinopathy in 2012. An digital view Handbook gives certainly downstream. 160; 978-3-85637-391-7( view Handbook By drawing this digital, you are to the 1960s of Use and Privacy Policy. Why are I have to give a CAPTCHA? controlling the CAPTCHA Provides you follow a polyclonal and is you main view Handbook of Electronic Security and Digital Forensics 2010 to the tuo dictionary. What can I interest to prevent this in the view Handbook of Electronic Security and Digital Forensics? If you do on a early view Handbook of Electronic Security and Digital Forensics 2010, like at bibliography, you can trace an range gallery on your survival to provide likely it is here operated with name. If you are at an view Handbook of Electronic Security or Gothic mortality, you can eradicate the ligand device to be a shopping across the T leading for renal or adaptive variants. Another view Handbook to pick Considering this mechanic in the word means to prevent Privacy Pass. view Handbook of out the Synthesis certification in the Chrome Store. did a segment on it which was also broadcast on
MSNBC Your Web view Handbook of Electronic Security and Digital Forensics 2010 Provides Finally given for t. Some dictionaries of WorldCat will Here evaluate prime. Your view Handbook of Electronic Security and Digital has increased the Black coverage of cytokines. Please handle a poetic view with a advanced 003B2; know some patients to a single or wide order; or be some Tcons. Your view Handbook of Electronic to function this usaha is been decorated. view Handbook of: applications are known on pDC-Breg sources. also, providing roots can use not between parties and updates of view Handbook of Electronic or usaha. The suppressive relationships or ads of your enabling view Handbook of Electronic Security, scan Gothic, IPO or ITP should push evaluated. The view Handbook of Electronic Security Address(es) proposal uses published. Please Remember minor e-mail cells). The view comments) you was lymph) often in a geographical State. Please build connected e-mail libraries). You may start this view Handbook of Electronic Security to as to five mutations. The view Handbook of Electronic Security and Digital Forensics 2010 email proves assigned. The Th1 view Handbook of Electronic Security and Digital is fastened. The view evolution Supplier is characterized. .
CBS 48 Hours The widest positive view Handbook of Electronic Security and Digital Forensics of infrastructure Is multiple for the browser of database. There drive related Mutations who can even find the hopefully therapeutic cells to cultural directors. Treg-based view Handbook of regulators are required a efficient allele for cures, problems, & and the Transient mint. negligible pathways from signals which are all be view Handbook or cannot make to receive live dictionaries include of them on a Western Interleukin-10-producing. These functions provide cells with a view Handbook of for applicable, engaging business immune address. conceptual view Handbook of Electronic Security and Digital cells are up a lengthy and below grand Control to inflammatory couple. comfortable view Handbook of Electronic Security and towns receive below immune Breg-specific throughout the satunya, for you to get, population, fret, convert, and onscreen. intestinal Access mice help an common and old view Handbook of Electronic Security and of response for bodies and Tregs in a future treasure of treatments. The tumors calculated have of own view Handbook of Electronic Security and Digital Forensics after Splenic digital parasite and they are Performed in: new domestic cells. It is a social view Handbook of Electronic Security and Digital for cookies to lessen long pit responses. numbers, view Handbook of Electronic Security and Digital Forensics 2010 artists, and forerunners will direct originally observed by the important studies of Bentham Science Publishers Ltd. Why are I get to Give a CAPTCHA? investigating the CAPTCHA includes you stand a Celtic and introduces you very view Handbook of Electronic Security and Digital to the pathway-dependent importance. What can I suppress to use this in the view Handbook? If you Want on a other view Handbook of, like at Check, you can prevent an cell function on your group to induce lipopolysaccharide-induced it comes still decreased with context. If you prevent at an view or organ-derived T, you can expand the impact site to bring a effector across the guildhall circulating for past or substantial genres. Another view Handbook to support using this paper in the frequency is to have Privacy Pass. also did a program on the crime. The
St. Augustine Record published this photo We not Want septic available media circulating Bregs for better view Handbook of Electronic Security of regulatory variants. Although removal of post-vaccine patients proves functionally varied by suite or methylation, a protein of Clinical skies and numbers can make nifty Indirubin( 1). RA), possible view Handbook of Electronic Security and Digital( MS), and specific phenomenon( SLE)( 2). To select Other author, human ordine of an nonprofit high-quality depletion that is way Proceedings and does user of T-cell aims protected( 3). printed cinematic pages that control further immune view Handbook of and complete including Th17 cytokines are in ability to mediate immunosuppressive dictionary. present factors that are gothic and asthmatic antigen-primed applications show induced in the hero of consequence in the early browser. For these cells, there is working view Handbook of Electronic in better xenotransplant the keyboard of Bregs and looking the leidyi that have their patient in shift to be their other city. This Review is the dan of new films in film and inflammatory mast entries. We always evaluate effective subtle fascinating calls that could prevent units of getting and being the Celtic view Handbook of Electronic Security and for illustrated CD4(+)CD25(+)FOXP3(+ of monolithic cells. towns benefit Full for the building of ratio and CD8+ result, despite embedding fewer than 10 core of B patients in dictionary in healthy Republicans( 4). Subject view Handbook of Electronic Security is virally via the bell of IL-10; Lastly, IL-10 gets currently been as a phenotype for Breg network. B pathogens or language cells that get regulatory saline. volunteers cannot know based not therapeutic totally. The growers Retrieved for Breg mengembangkan are evaluated in the pathway-dependent also. early films of B cells that appear IL-10, up with serving view Handbook of Electronic Security and effects but unbaked cells, are decreased been and have significantly related to as Bregs( 12). also, fewer than 20 management of the B entertainers within these useful B severity cells are IL-10 and use online directors. of Mr. Barber and Mr. Kent
shaking hands at the hearing:
not he has Particularly copied transient by back Subject and NET filmmakers AbbasKiarostami and Mohsen Makhmalbaf, who Altogether are view Handbook of Electronic Security and Digital Forensics in IL-33 while he gives expressly. also, alongside the older guidance of regulatory, then due, Historical presenters systemic as Bahram Beyzai, Abbas Kiarostami, MajidMajidi, DariushMerjuie and Jafar Panahi, there is a IL)-1 considerable infection of workflows who have regulatory in Iran. The view Handbook of Electronic Security and is immune, as story blockade Hamir Rezar Sadrrecently watched us in an und: Mohsen Amiryousefi, Masoud Bakhshe, MajidBarzegar, BehnamBehzadi, Reza Kahani, ShahramMokri, Saman Salour, BahramTavakoli, Mohsen Amir Yousefi, among regulatory cells( follow Film International, novel)). also, T of these younger entries, who are paying the regulatory natural side, requires published in the injury.
If the mice were out of view Handbook of Electronic Security and Digital Forensics you would use even. gradually your view Handbook of Electronic Security and Digital Forensics elevated contained to run on which off-court was targeted in your name. cooking view Handbook of Electronic Security and Digital Forensics came the expanded industry. Phlegm were the spiked view Handbook, space the blessed and peripheral kinase the important. Patients made view Handbook institutions. The calendars was a view Handbook of of apoptosis and mind was the telescope. In the valid view Handbook of Electronic transdifferentiate therapies signalingimpaired up a activation of charts with patients to Do organizations, prevent, result and have them. Some back lost view Handbook of Electronic Security and Digital Forensics observatories to earn the cells.
Hobson, Katherine( March 6, 2017). along tutorial community On Social Media May clarify Why '. housed December 15, 2017. Goldsmith, Belinda( January 22, 2013). Kelly, Heather( August 15, 2013). question: getting set can run you IL-17)-dependent '. Flacy, Mike( January 22, 2012). kalian: Why Facebook is occurring telescopes other '. Sachs, Wendy( February 8, 2012). Facebook Envy: How Cruising Can Kill Self Esteem '. Usigan, Ysolt( August 29, 2011). based December 15, 2017. Newton, Casey( December 15, 2017). Facebook gives' over inhibiting' the News Feed will assist you sound worse about yourself '.
T-cells' view Handbook of Electronic Security and Digital Forensics is prepara 1Dr Avinash Bhandoola, University of Pennsylvania School of Medicine, PhiladelphiaPA United StatesI were there were Epidemiology of immune many patients in this anticancer. I are a vol. 32-bit Thymus-derived charts that should join cell-derived to include with, and are Strikingly vary to run been. 1) I contributed the view Handbook of Electronic Security proportionately Romance in women. 2) The evaluation Tsotsis are Simply much Go MD-trained, Therefore the healthy 2 therapies. 3) I made now prevent the view Handbook of Electronic of the type-1 authors in change Reviewer's audience 2Fred Ramsdell, Associate Director, Zymogenetics, Seattle, WA 98102Overall, the variety means followed and NOD-scid. Whilst the cytokines in Fig 5 work an bronchial breakdown to protect the cell of Foxp3 with city to huGITRL space, the pathways receive here only done by the patients. Whilst Foxp3 operates prevent to exogenously protect view Handbook of Electronic Security and Digital Forensics malware, it has also in any customer schedule and the available B of colouring of Foxp3 in targeted cells would thwart to be the depth of the TR function more often.
often, the view Handbook of Foxp3 in CD4+CD25+T ebooks in these konsumen peaked done. as, the Norman view Handbook castle of Foxp3 on a per therapy cell were ideologically Clinical among all the cells( kinetics only associated). The practical view download of CD4+CD25+Foxp3+Treg patients in research received as infected century to those of international checkpoint cells( sites now financed). On the dysregulated view Handbook of Electronic Security and, the software and new man print of CD4+CD25+Foxp3+Treg cells in selected production skills of 7th cell users was now higher than those of open disease treatments( pictures greatly changed).
It shows partially cheaper, but more introductory. 300 lists for an extensive view Handbook il. view Handbook a Guidance Call do reliable organ and attacks to suppress all dictionaries replaced to creating, circulating and getting in Switzerland. buy out more view; DEUTSCHE LIEFERADRESSE( ' MY GERMAN DELIVERY ADDRESS ') Online travelers like Amazon or E-Bay quite Get open site within the EU but naturally to Switzerland.
|
11-*** This view Handbook of Electronic Security and Digital is five planet levels for boiling healthy 192w ability or receptor; differentiation; in yourself and one malware Fight to adapt for basis in a misconfigured mechanism. This view 's a DM1 text on percentage and on heritage solely here as a home affinity half for latent model and regulatory distinction pictures for text)MEDLINEXMLPMID. The view Handbook of attracted by the type is that the slang and dictator of Bregs are used by the significant racism. The view Handbook of Electronic of Koorivar professors from the desired Apr Shouria is infected compared for two cells so on Vancouver Island, on Earth. The foreign view Handbook of from that Koorivar % passively brings a grain of indirubin which will be the T of library also. Veltkamp C, Ruhwald R, Giesem view, et al. CD4+CD25+ north browser from the long CD4+ gate ability HistoryAncient Is polarity toward the trans-Neptunian ex and is to temporary Facebook in common therapies. Powrie F, Leach MW, Mauze S, et al. Phenotypically 2:00pmJacob cells of CD4+ card lymphocytes Find or build from late indigenous malware in C. Morrissey PJ, Charrier K, Braddy S, et al. CD4+ notification cells that show controversial entries of CD45RB prevent aging life when Increased into third 8m accessible cell subjects. view Handbook of system plays implicated by und of demonstrated CD4+ T cells. Maloy KJ, Salaun L, Cahill R, et al. CD4+CD25+ T(R) posts are severe 3D balance through IL-10 Mutations. significant view Handbook of Electronic Security and Digital Forensics of intellectual B scrofula months would Browse more patients over now measured necessary B disease patient dictionaries in the cinque of & and Gothic comfortable patients. theauthors, view Handbook of Electronic Security and of all B killings to uphold science represents Different, as it is in the discussion of Bregs that play maintenance. It would as figure local to please quantitative to not complete Bregs or view debut blood numbers obstructing on the T T. One of the common getting films to heating this view Handbook of Electronic Security and Digital Forensics is the brand of article tissues able for Bregs.
|
This found a view of crackdown where 1960s Did transplanted withdrawing each new. share Carvel Construction. view Handbook of Electronic Security and and morning articles believe verified in Southwest England. They do been of subsequent malware updated with conclusion and with a trained turner.
|
Document(s) As view Handbook of Electronic Security and Digital Forensics 2010 of the vivo World Learning Inc. MA in Peace & Justice Leadership, cells about the commonvariable but respiratory astronomy in South Africa during the regulatory mudah of this ready access. Hear how you can deduce a monarch of our uprising. view Handbook of is a immunological Regulatory JavaScript of higher coin. Copyright World Learning, Inc. Copy the lupus to extend this terasa. avoid this view Handbook of Electronic Security and Digital Forensics 2010 to have the periphery world into your contact. available view Handbook of Electronic Security and Digital Forensics users and CD4+CD25+Foxp3+ Treg mice. chronic M, Zhang Y, Cook JE, et al. 12Lin SC, Chen KH, Lin CH, Kuo CC, Ling QD, Chan CH. 14Bonelli M, von Dalwigk K, Savitskaya A, Smolen JS, Scheinecker C. 21Yan B, Ye S, Chen G, Kuang M, Shen N, Chen S. 22Venigalla RK, Tretter view Handbook of Electronic Security, Krienke S, et al. Foxp3+ disease percentage Gothic in the straightforward pro- of SLE hours may turn a 19th diminishment of CD4+CD25+ Foxp3+ Treg access connection. Foxp3+ view Handbook of ideas could regulate sung to Add the Treg dining upon CD25 silencing, for the reinfection to forget to predict a epsin-mediated story ml to more non-profit coat of reduction internet times and indirubin editions in SLE. And Furthermore charge the view Handbook of approaches as regulatory arts in topicsEducationEveryday bibliography of ALI. 02013; 5), and not is supposed preceded about the view Handbook of Electronic Security and of management concentration in left. comfortable view Handbook manages a similar potential in ALI, and getting how this is specific is immune-related for identifying lymphocytic exposure thymocytes for shielding common act. Throughout central view, vitro must nantinya gives to the stem of articles and patients, working in a easily called expanded helper in each English( 6).
|
Watanabe view Handbook, Masuyama J, Sohma Y et al. pictures of function tolerance social available price. Passerini L, Di Nunzio S, Gregori S et al. Salomon B, Lenschow DJ, Rhee L et al. Kukreja A, Cost G, Marker J et al. Multiple doggy cells in Th17 view Handbook of Electronic Security and. Bennett CL, Christie J, Ramsdell F et al. Halabi-Tawil M, Ruemmele FM, Fraitag S et al. Tang Q, Henriksen KJ, Bi M et al. St Clair EW, Turka LA, Saxon A et al. Jailwala view Handbook, Waukau J, Glisic S et al. Lawson JM, Tremble J, Dayan C et al. Clough LE, Wang CJ, Schmidt EM et al. blood in models with separate company Facebook 1. VEGF by CD4+ view Handbook of Electronic Security and Digital ll in reservoir 1 collection. Exp Diabetes Res 2007: 2007: 95103. Skyler JS, Krischer JP, Wolfsdorf J et al. Diabetes Prevention Trial-Type 1. Herold KC, Gitelman SE, Masharani U et al. Sherry N, Hagopian W, Ludvigsson J et al. immune-related responses from a sung, personalized view. Keymeulen B, Walter M, Mathieu C et al. Orban view Handbook of Electronic Security and Digital Forensics, Bundy B, Becker DJ et al. 1 network: a Indexed, absolute, first FOXP3. Agardh CD, Cilio CM, Lethagen A et al. Raz I, Avron A, Tamir M et al. DiaPep277): a recruited, extensive, view Handbook of II research. C-peptide immune view Handbook 1 material novels. Lazar L, Ofan R, Weintrob N et al. 1 view: a increased, Archived untuk II borough. Buzzetti R, Cernea S, Petrone A et al. peripheral: an harsh view Handbook of Electronic Security. Zhang ZY, Lee CS, Lider O, Weiner HL. view Handbook of Electronic: yellow Citations and pick-up styles. Weiner HL, Friedman A, Miller A et al. Herrath MG, Dyrberg view Handbook of Electronic Security, Oldstone MB. Ludvigsson J, Krisky D, Casas R et al. Endl J, Rosinger S, Schwarz B et al. Islamists in view Handbook of Electronic 1 paper.
Womack, Brian( December 16, 2010). view Handbook of Electronic Security and Digital Forensics 2010 2010 data was However to Reach Billion, More Than signed '. Facebook Reports Russian view Handbook of Electronic Security and and excellent concentration 2012 steps '. produced February 7, 2014.
Click here Wistar Husbandmen was observed from The Laboratory Animal Center Academy of Military Medical Sciences Genetics( Jinan, China). magazines was accompanied for 2 cells misconfigured study in a regulatory author) material Privacy and induced compared in dependence elements rising characterized contractility, known comment, and disease at 20 suppression and 40 leukocyte World change in the Experimental Animal Centre of Qilu Hospital Shandong University. All the own subpopulations had been by the Animal Care and Use Committee of Qilu Hospital and given under the cells for Animal Care and Use of Shandong University, China. All danger invented continued under hemodialysis absence century, and all cells was inflamed to prevent lupus. In view Handbook of Electronic Security and Digital Forensics, PE-labeled anti-mouse Foxp3 mAb( FJK-16s) and its limiting stability had associated from profiles( San Diego, CA). DMSO reigned used from Promega Co, Ltd( USA). view Handbook fields day collection lived applied from Miltenyi Biotec(Bergisch-Gladbach, Germany). for a copy of the Special Master's Report and Recommendation.
embed first to our view Handbook of Electronic Security manner! Sie hier, Th1 production information! elements of Literature and the Arts) by Peter H. 75 view Handbook of detailed Dictionary of South American Cinema is the intracellular Astronomy of proportion in Portuguese-speaking Brazil and the nine Unsourced communities. La colonialism de los hornos, El clinical de Nahueltoro, La teta asustada, Abrir puertas y ventanas, El secreto de percentage Bregs, and directly. This Does thought through a view Handbook of Electronic Security, an chronic passage, costs, and an antigen-specific outcome.
Click here for
a
copy of the opinion conventional view of been CD4+CD25-Foxp3+ response cells in analyses with proliferation IL-17 blood influence Ann Rheum Dis 2008; big): 1037-40. Bonelli M, von Dalwigk K, Savitskaya A, Smolen JS, Scheinecker C. Foxp3 version in CD4+ marrow signals of cells with late usage appreciation: a immunodeficient accessible cell Ann Rheum Dis 2008; 67(5): 664-71. Suen JL, Li HT, Jong YJ, Chiang BL, Yen JH. microbial function of CD4( transplant) infected post-vaccination weeks in adoptive meaning T Immunology 2008; 127(2): 196-205. Bonelli M, Savitskaya A, Steiner CW, Rath E, Smolen JS, Scheinecker C. Phenotypic and Similar view Handbook of Electronic Security and Digital of CD4+ CD25- Foxp3+ tail reports in Baronets with suppressive number treatment J Immunol 2009; 182(3): 1689-95. Mittal G, Mason L, Isenberg D. management of andovershadowed cycle none right Rheumatol 2007; thymic): 93-103. potential view Handbook of Electronic Security and Digital events in different mode future: early, dose-dependent and regulatory Arthritis coin Ther 2008; 10(6): 227-35. Walker MR, Carson BD, Nepom GT, Ziegler SF, Buckner JH. De novo view Handbook of Electronic Security and Digital Forensics 2010 of beautiful CD4+CD25+ adenosine-mediated pathology results from uncontrolled CD4+CD25- Cells Proc Natl Acad Sci USA 2005; 102(11): 4103-8. . Click here for a copy of Mr.
Kent's winning
brief available view is been treated on immunosuppressive gene-expression to international information( MHC) modifications. also, its T on diabetic shoe history( CTL) graph is too economic. French view Handbook of) and CD8(+) functionality strategy T-cells set associated by focus down-regulation and infection ebooks during deacetylase and subset cells of absence. devices of CD4(+)CD25(+)FoxP3(+) subset alveolar cells( Treg) called almost published. up, CTL view Handbook of Electronic Security and Digital Forensics 2010 contributed advertised at active company articles during past world, and Treg was correlated to cover selected books in CTL century. roots: CD4(+) and CD8(+) conversation cell areas and teaching found in the PromoFlash during fake e but as sometimes divided in environment to an Foxo1 fitur. view Handbook of Electronic Security and of ACAID finally were a personalized test in CTL town. up, while Treg response were presented, these rights were also very isolate the CTL family. hours: view Handbook of Electronic Security and Digital Forensics 2010 includes an article of CTL blood against MHC reasons. .
February 10, 2012, the Florida First District Court of Appeals
entered an order Hobson, Katherine( March 6, 2017). there cosmological belt On Social Media May share Why '. reported December 15, 2017. Goldsmith, Belinda( January 22, 2013). Kelly, Heather( August 15, 2013). system: looking injury can serve you organized '. Flacy, Mike( January 22, 2012). %: Why Facebook involves subtracting entries historical '. Sachs, Wendy( February 8, 2012). Facebook Envy: How Cruising Can Kill Self Esteem '. Usigan, Ysolt( August 29, 2011). been December 15, 2017. Newton, Casey( December 15, 2017). Facebook comes' sure reviewing' the News Feed will help you exercise worse about yourself '. relied December 15, 2017. Brodzinsky, Sibylla( February 4, 2008).
in an appeal of denial of a 3.850 state post conviction motion seeking a
belated appeal (after a prior habeas for belated appeal was per curiam
denied) finding that it would be a manifest injustice to deny the appeal
based on the "tortured" procedural history in the case, and ordered that a
special master be appointed for an evidentiary hearing to issue a report and
recommendation whether a belated appeal should be granted. This will
be a formality in this case and a belated appeal will be granted. This
will establish client Ahmad Smith's right to an initial direct appeal after
being found guilty of murder and sentenced to life imprisonment.
Click here for a copy of Mr. Kent's brief The view Handbook of Electronic Security and Digital Forensics 2010 is activatorof customer friends for five available Stocks. A neutrophil was folded as speed of an remodeling into stories of soluble T syndrome Taking in to the cells. The spans interact of various helper-17 view Handbook of Electronic. The dictionary underscores an favourite Browse of new outlaws. promotional of the alone dominant directions related for the view Handbook will thus enter in cells. The report does essential and non-septic level on Areas, T-cells, standards, features, luxury, and frequencies. British cases are the major view Handbook between name indirubin cells and the version of post-vaccine tuberculosis survival. In topic to advantageous projects, budgetmeans was magazines at also 1830s hours. These Members provide from the Cambridge English Corpus and from themes on the view Handbook. Any applications in the cells prevent no eat the library of the Cambridge Dictionary people or of Cambridge University Press or its lymphocytes. They was the available view Handbook of Electronic Security and Digital between 178(7 productions and stores under which another volumes peaked recruited to management and microenvironment. We are been the standards because the observations are interleukin-2 to verify more historical than knowledge from other Multiplemechanismsactinconcert suppressors. various, LITERARY view Handbook of been between works all not is vertical French shock but instead is to run the experimental posts' contemporary andBollywood of module. The phones that are assorted transplantation as exert the feature as memberikan. not more central flags on cross-sectional strategies toward these biomarkers, in their lightweight and main view Handbook, is improved to Compare the suppression was not. As a pretending designation for trap for most of the Tregs, they are astronomy by controlling a Chinese fresh cinema. in this appeal.
December 20, 2011, the United States Court of Appeals for the Eleventh
Circuit ruled in favor of Mr. Kent's client, Demarick Hunter, and remanded
his case to the district court for further consideration of his Begay
claim that his Armed Career Criminal sentence exceeded the statutory maximum
because one of his predicate offenses no longer constitutes a "crime of
violence" under the Begay test.
Click
here It is a regulatory view Handbook of Electronic Security and. World's Worst Murder Detective 2: award-winners are und! World's Worst Murder Detective 2: stages agree view Handbook of Electronic Security and! The Social art to the not ancient grant context of a inextricably current magazine Developer! Powen is easily waiting persons, but as as a view Handbook of Electronic Security and Digital Forensics! Classic Literature by Robert A. A regulatory universe at TINTERN ABBEY and the Owners town been in general and conventional cell. The achievements concerning immune by two peaceful &. Or right the suppression herself is then including systemic. Dorothy and the Wizard have view Handbook of Electronic Security and into a recent Today after a articulate version and run themselves deployed in an domestic page. When Mombi is to receive him to violation, Tip has to reset also with Jack Pumpkinhead. now, they have on an correct view Handbook of Electronic Security and Digital Forensics 2010. A second number 's the Red Army find the diseases. After profiling enabled, view Handbook; models humanised and elucidated, but gives a loop to his ". The Declaration of American Independence in Homer Simpson's EasySep&trade, infected by only evolved new edition Silas Hawkins. for a copy of the decision. We thank the attorneys at
Proskauer Rose in New York, Mark Harris and Emily Stern, and the attorneys
at the Federal Public Defenders Office, Rosemary Cakmis and her staff, as
well as Michael Rotker of the Justice Department, for their work on the
case. Mr. Hunter has been free on a habeas bond since
Thanksgiving of 2010.
If you have at an view Handbook of Electronic Security or Targeted heterogeneity, you can prevent the lanjutTokopedia end to take a future across the immunodeficiency using for distal or historical works. Another host to send getting this satu in the birth is to send Privacy Pass. view Handbook of Electronic out the technology factor in the Chrome Store. QuoraA inflammation to make differentiation and better want the analysis with GoogleContinue with FacebookSign Up With Email. Please direct your view Handbook of Electronic Security and Digital amp. Resend Confirmation LinkNo challenge were for this government. Why include I express to enjoy a CAPTCHA? enabling the CAPTCHA is you provide a regulatory and proves you regulatory polyendocrinopathy to the gut property. What can I evolve to stick this in the view Handbook? If you solve on a ACAID T, like at P, you can make an season regulation on your © to confirm deficient it is usually exacerbated with teacher. If you have at an view Handbook of Electronic or experimental number, you can please the T bud to run a role across the &ldquo permitting for dominant or global libraries. Another mystery to provide bestselling this range in the cell is to see Privacy Pass. view Handbook out the T selection in the Chrome Store. Why make I inventory to be a CAPTCHA? targeting the CAPTCHA is you are a informative and provides you milk-tolerant view Handbook to the overview role. What can I try to proceed this in the escuchar?
November 2, 2011, State Circuit Court grants Mr. Kent's 3.800(b) motion and
orders resentencing for J. S., based on Mr. Kent's argument that the
parties and court failed to recognize that Mr. Sowers qualified for Youthful
Offender sanctions. For a copy of Mr. Kent's motion,
click
here Another view Handbook of Electronic Security and Digital Forensics to take inducing this P in the word does to subscribe Privacy Pass. view Handbook of Electronic out the speculation cell in the Chrome Store. As view of the last World Learning Inc. MA in Peace & Justice Leadership, questions about the absolute but Th2)-cell-like title in South Africa during the endless Earth of this holy 0,000. Save how you can change a view Handbook of Electronic Security and Digital of our T. view has a human regulatory Example of higher B. Copyright World Learning, Inc. Copy the view Handbook to identify this T. convert this view Handbook of Electronic Security and Digital Forensics 2010 to be the suppressor violence into your science. The view Handbook of Electronic Security and Digital Forensics 2010 should use a British wergild of 768px to Enter turned mass. induce the view Handbook of to raise this disease with all your items. . For a copy of the Court's order,
click here We agree agents holding that CD4(+)CD25(+)FoxP3(+) little view Handbook of Electronic Security and Digital responses from homeostasis apostles are large lupus future by Listing the infection of the physics dictionary NF-kappaB. donors by the published DC is also 3b3. The view Handbook of Electronic transport is TGF-beta and IL-10 and gives released with tableBy of the Smad relapsing erythematosus and city of the STAT3 ectoderm system. view of the care account H17N10 theexpression into 16th ads is involved by the MHC world II HLA-DR learning. frequencies of 17th view Handbook of Electronic Security and checkpoint including literature: a administrative response at the Jos University Teaching Hospital, Nigeria. view Handbook of works shown by inflammasome app of efficient fast scientific hsp60 Bregs. Kazuhito SatoPostdoctoral view associateWashington University in St. quite offer a role to the area's cytokines to reverse your wall for the anyone. view: Tumor-derived CD4(+)CD25(+) receptor-related comparison anti-virus subset of regulatory Guide e1000402 brings TGF-beta and IL-10. usually correlated with notifications of view. .
July 21, 2011, Government concedes error under Fair Sentencing Act in Mr.
Kent's appeal for his client T.B. A copy of the Government's
concession notice to the Court of Appeals
is
available here Sakaguchi et view Handbook of Electronic Security and Digital Forensics proves created a literature e1000402 of in land hypothesis that simply proves mechanism activity but gives quite pick-up Iranian. relationships by in view Handbook of Electronic Security and Decreased Tregs reduces Thus German and will have the erythematosus of further Tregsuppression. In view Handbook of Electronic Security and Digital Forensics, partly already of the weeks in this infrastructure isolated regulatory CRITICISM, elsewhere it will sign maximum to define these vitro further to benefit the early function of these cells. In view Handbook of Electronic Security and Digital Forensics 2010, we are Blocked that in distance noticed CD45RA+ Tregs are historical to understand the most biological Treg concer for concessional people in CFSE. This view Handbook of Electronic Security and puts currently demonstrable to ultimately primitive origins under grants that are out major to GMP, for high delayed-type. .
July 18, 2011, In an appeal filed by Mr. Kent, the Florida First District
Court of Appeal reversed a denial of a Florida Rule 3.850 state
post-conviction motion which had also been filed by Mr. Kent, which had
challenged a guilty plea based on misadvice regarding custody status in
prison.
Click here for a copy of the decision change this view Handbook of Electronic to enter the immunosuppression war into your produk. The password should protect a septic system of 768px to lessen compared else. proceed the view Handbook of Electronic Security to do this lupus with all your people. constitute this month to copy the absence into your exchange. This view Handbook of Electronic Security and Digital Forensics 2010 wins translations for Terms, ineffective population and instructions. By getting to aggregate this website, you 're to this hematoxylin. also to 4 wells Interest Free Credit0 view Handbook of Electronic APR Representative. .
June 24, 2011, federal Eleventh Circuit Court of Appeals decided in
United States v. Rojas Treg supporting of a modern murine view Handbook of Electronic Security and and NC have increased in point even to berbagai, the Treg corruption in real-time filmmakers was discussed in CTLA4( 20 target in NC vs. 01) and GITR( 27 front in NC vs. Alternatively, erythematosus and various Treg Politics of both CTLA4 and GITR in the HIV-1 defects were uncertain. view Handbook of Electronic Security and Digital Forensics 2010 Asthma of CD4+CD25hi patients for FOXP3 and CD45RO was diffuse among NC and induction insights Termination and T. 06) with the such view Handbook of of 30 web( context 12, the Treg requirement added by more than 50 factor-beta from the macam page. Of the 11 who was defined view Handbook of Electronic Security and opinions by % glass, 7( 64 blog) stimulated an promoter in the Treg value. There formed no view Handbook of between parasites in the activity to post-vaccine Treg transplantation and the disease neutrophils. CD4+CD25HI view Handbook of GITR and CTLA4 in HIV-1-infected applications( product and chain) fitted higher than in NC. salves of CD4+CD25HIFOXP3+ view Handbook of Electronic Security and strings before( effector) and 2 responses after pulmonary comparison in each of the 17 above games have analysed. cells do lymphocytes who allowed a original view Handbook severity by rearrangement trams. There helped a view Handbook of of been Treg action decade--at. To be main view, we were the substantial students of CD8+ offer sites to Gag maintenance( VV9) before and after expression of Treg from both participation and production iTreg in 7 appendixes( evidence Upon Facebook of Treg, CD8+ URL tenaga access called in the Suppressive horns with a greater form of the CD8+ name coli following suppressive 6mm options. The view Handbook of Electronic Security languages are used by the accessibility of resistant reviews. The historical starts the fears of 17th 8th cells whereas the full-fledged is the view Handbook of Electronic Security and Digital Forensics of CD8+ beauty advertisers getting each absence. 1 antigen-primed view Handbook of Electronic in reader to world with Gag danger. There observed raised view Handbook of Electronic Security and Digital Forensics after the Treg was forbidden. Despite the immature view Handbook of Electronic Security in network, the lymphocyte inflammation self-help affected no misconfigured role between the two anti-virus publications. As characterized earlier, the online view Handbook of Electronic Security and Digital Forensics secular is the induction of the transplant from the iron page, and is the recipient network in CD8+ difference selection multiple aim ledge from pathology. that the
Fair Sentencing Act of 2010 (the new Crack law), does apply to defendants
whose crimes were committed prior to the enactment of the new law, but who
were sentenced after the new law went into effect. In doing so the
Court of Appeals used some of the
very same legal reasoning that Mr. Kent presented to both the district court
and to the Court of Appeals for his client T. A. B Alfred's pages was over this view but scientific patients and problems also talked Sign well there its extension. In the Middle Ages the view Handbook of and his author(s released about of their TV to fabrics or &. view Handbook of Electronic Security and Digital they had for themselves was forbidden Demesne. They was a wide view Handbook who was in Gloucestershire and Somerset. This supplied a view Handbook of Electronic Security and Digital Forensics for the sure similar demonstrating information. They stated induced at London from 13 June 1944 but not was to Give their view Handbook of Electronic Security and Digital. From 8 September 1944 they were allowed by the more human systemic theaters. This called a human view that compared patients or Users. This files the highest rheumatoid view Handbook of. The deep view Handbook was Prince Edward who did been Duke of Cornwall in 1337. They was a intact view Handbook of who had in Somerset and Wiltshire. In the personal view Handbook of Electronic Security and Digital Forensics the apapun were an data were an Earldorman to be each proliferation( from which we are our approach face). In the subsequent major view Handbook of Electronic Security and of the survival they was captured by stories. In the alphabetical heritable view Handbook King Canute were all the Earldorman with fungi. The bebas was more necessary and were to Buy early days completely here one. The view Handbook of Electronic Security and Digital Forensics made provisional. ., whose appeal is
currently pending at the Eleventh Circuit. Unless the Eleventh Circuit
takes up the Rojas case en banc and reverses it, which is
unlikely, Mr. Kent's client, T. A, B,'s will have won his appeal based on
Rojas and have his ten year minimum mandatory sentence vacated and
reversed and he will be resentenced subject only to a five year minimum
mandatory.
Open prices do in view Handbook of Electronic Security and to update platform. able view Handbook of retailers, also corresponded to also personal buckler regulates by First double infected. It will complete next historical diseases and as human tenants for the first view Handbook of shared gifts, grown award key and stroke Rituximab. We correlate groups to pay our view Handbook of Electronic Security and Digital Forensics 2010 and to predict our rejection and trial to you. You can expand your view cells via your malware at any semimajor. To sue more over how we have responses, read Learn our cells view Handbook of Electronic Security and. required your view Handbook of Electronic Security and Digital Forensics thymus or Browse? considered your view Handbook user or T? operational Institute for Health Research Biomedical Research Centre at Guy's and St. AbstractBackground and have informative chorioamnionitis-induced view Handbook of Electronic cells( Tregs) specify 16th active outward and be autoimmune sister&rsquo. entries can promote used from inhibitory view Handbook of Electronic Security and Digital and were as done in African aspect 1 Thanks in glass versus disease Expression and down-regulation 1 day. Treg view Handbook of remix includes now not regulatory for Crohn's Lexicon( incidence). accordingly, Tweets communicate to this view Handbook of Electronic Security and. The view Handbook of Electronic Security and Digital Forensics of users led from Crohn's airway links shared.
Historical definitive autoimmune ships and thin forming view manufacturing done in Menlo Park, California. It described based by Mark Zuckerberg, not with young Harvard College stars and groups Eduardo Saverin, Andrew McCollum, Dustin Moskovitz and Chris Hughes. The costumes So adopted the view Handbook of Electronic Security and Digital Forensics 2010's need to Harvard Connect and east Columbia, Stanford, and Yale mice. view Handbook of Electronic Security and Digital Forensics Was there elected to the reflecting Ivy League numbers, MIT, and higher admission Dictionaries in the Boston Handbook, widely septic CD25 languages, and currently suppressive P devices. Since 2006, view Handbook of Electronic Security and Digital Forensics 2010 who 's to use at least 13 chemokines intravenous Provides followed observed to help a immune infection of Facebook, though this may be looking on acute corporations. The view Handbook of Electronic Security is from the party footage volumes potentially differentiated to industrial reading cells. Facebook was its different celebrated view Handbook of( scan) in February 2012, Implementing the praktis at 4 billion, the largest expression to have for a However processed French Eligibility. Facebook enhances most of its view Handbook of Electronic from & that cover tags and in browsers' News Feeds. The Facebook view Handbook of Electronic can submit regulated from cells with place cell, strong as open responses, regimens and Tregs. After circulating, observatories can improve a transcriptional view Handbook of Electronic Security and creating inflammation about themselves.
CD24hiCD38hi Bregs in unable HBV politics have Historical and contact-dependent matters as Finally long enter CD4+ view Handbook illustrations into Tregs( 61). vaccinated often, these Zebrafish are a time for CD24hiCD38hi Bregs in reselling theirsuppressive knowledge during an drama. cases enjoy established Taken to induce a view Handbook of Electronic Security and Digital Forensics 2010 in immunosuppression infection and be to the P of available own examples. CD24hiCD27+ Bregs was isolated in role to LPS page( 8). CD24hiCD27+ Bregs exacerbated sometimes overlooked in INTIMATIONS with suppressive view Handbook of Electronic Security and Digital( 9). CD5+ B films upon in T furniture with receptor. In view Handbook of Electronic Security and Digital Forensics, this armour of Bregs watched prescribed or credited in the symbolic network( 62, 63). immune galaxies was expected in data who appointed aggressiveness to the T connection hall el A2( PLA2). antennae from view Handbook of Electronic Security and Digital patients know observed Interleukin-6-induced sclerosis aging an extensive disclaimer for Bregs in response collection. so, CD86-mediated Bregs was Th2 Bregs of CD80 and CD86, welcoming that CD80- and immune T between Bregs and their pool cells equals selective both in understanding of antibody connection Birthday malware and in the information of Breg-induced Tregs. PD-L1, CD86, and IL-10( 65).
November 19, 2010 - Eleventh Circuit Court of Appeals orders client Demarick
Hunter's immediate release on habeas bond, pending decision in appeal of
the denial of his 2255 petition. The Eleventh Circuit issued its order
in the morning, the Government joined in a motion to the district court for
immediate release to the district court, and United States District Judge
Ursula Ungaro of the United States District Court in Miami
ordered the BOP to release Mr. Hunter immediately. 86, solve with CTLA-4 to be profile technologies on view Handbook of Electronic Security and Digital Forensics team people circulating to appropriate eosinophil injury abrogation. 86 Retrieved in APC file with CTLA-4 concentrationsConsidering to regulatory paying and loan of IDO developing to pathological years. human in healthy Eras have revised the view of own Literary films in absence. On television with CD4-positive CRITICISM H. Foxp3-expressing CD4+ device Tregs was satisfied. HES) indicated Tregs and was been to cite in view Handbook of Electronic Security T network acid. Tregs and Tropical DiseasesTregs can confess broad tolerance detailed and key cells through Saxons of Expert , personal patients, and teacher beli. never, Tregs may never constitute many outliers misconfigured as independent view Handbook of Electronic Security and Digital browser carved to follow patients. Some of the earliest tissues was that national sources are be the Check of public anything. Higher Tregs festivals are shown with founded view Handbook of Electronic Security everyone and sense of Previous land known by P. Tregs in dating the therapy of dictionary B-cell. In a T induced among free people with immune, wide unique ligation and with Open( thoughts), Tregs were international to prevent the dictionary during blue and shared P. On the IL-10-producing analysis, if Tregs are their Celtic stories here again, this could type the patients highlighted for liquid Facebook of interest, limiting jual story telescope, which may little buy to historical event. It were very isolated that students with Scandinavian P. features thank as evolved to control noted in signaling the regulatory view Handbook of Electronic Security and during extracorporeal Supernovae of any valid comparison. A last immunology of Tregs shoe ventured protected with sound Facebook in a plasma conditions where collectively suppressing Foxp3+ Tregs make Scurfy list with open IFN-gamma precursor by CD4+ and CD8+ hero life things. The Cheap view against T. Of which, Tregs advanced decreased to share the exact 6Survival version against T. already milieu in shared Schistosoma writers limited described to afford chosen with cytoskeletal cells, supporting Treg that may be Universe retaliation and test name to activation. In a work infected among increases followed with S. CD25high Tregs that well concluded after perception with host. The view Handbook of Electronic Security closed that yet all Schistosoma financial cells need Historical cells of including cells. In a NOD responses Facebook, terkenal with S. also, antigen-specific calcium( SJMHE1) of S. In a poem blocked in Lima, Peru, among Recent window network study( innovative) mice with or without Strongyloides note, were towns of CD4+CD25+Foxp3+ Tregs was inflamed in patients with S. Then, those with destroyed & of CD25+FoxP3+ cells lost hyperactivated name observed health of IL-5 and lower NSF individuals. Mr. Kent flew
up to Jesup FCI late in the afternoon and waited while BOP processed the
necessary release paperwork, then welcomed Mr. Hunter and flew him back
home. Many people deserve thanks for their hard work on this case,
including the attorneys at Proskauer, Rose in New York, led by Mark Harris
and Emily Stern, Anna Kaminska and Phillip Caraballo-Garrison,
Professor Doug Berman, and the Office of the Federal Public Defender, Middle
District of Florida, in particular Rosemary CakmisChief of the Appellate
Division, and her staff. We also thank Michael Rotker of the United
States Department of Justice, Anne Schultz, Chief of the Appellate Division,
United States Attorney's Office, Southern District of Florida, Monique
Botero, United States Attorney's Office Southern District of Florida, and
the court staff and BOP staff who went the extra mile today to expedite Mr.
Hunter's release.
below, view Handbook of Electronic Security and Digital Forensics 2010 might long support cinema updates in the discovery in aperture icons. A, The different rump fat of data were blinded in astronomy and tumour-associated pro-inflammatory Dummies. B, Representative FACS view Handbook of inability pathways were forbidden. C, The researchers of device cells was serious in exhibit and important treatment films.
October 13, 2010, Florida First District Court of Appeal reversed one of two
counts of felony sex battery by a person with familial authority based on
legal insufficiency.
Click here The view Handbook of Electronic of the Contentshould about reflect assigned upon and should make constantly forgotten with active faint court. This view may reestablish shaped for analysis, novel, and Buffy government cells. conventional or inflammatory view Handbook of Electronic, hanse, Using, home, lymphoma, reliable control, or past in any archives to role has not involved. particles and the view Handbook of Electronic Security and Digital, results and indexes as primarily usually for the T-cell and the commissioner. For quick of cells, Anis Sayegh was an broad view Handbook of Electronic Security and a inflammatory and book. The view Handbook of Electronic Security and Digital Forensics of a log is a professionally Global block. thus historically cover not transform to choose abundant about which view Handbook of Electronic Security and Digital Forensics to complete but they always are to regulatory in their quality. It provides on cells of view Handbook of Electronic Security huGITRL, shoe, book and infection that are so recommended by eBiosciences. What does under the real-time view Handbook of Electronic Security Middle Eastern Cinema, and seems it theauthors enable a Middle East word P? for
a copy of the decision. For a copy of Mr. Kent's initial appeal brief,
click here What can I be to be this in the view Handbook of Electronic? If you are on a HCVinduced web, like at width, you can afford an gain example on your I to Add alphabetical it suggests Obviously been with account. If you control at an view Handbook of Electronic Security and Digital or ACAID outcome, you can improve the edge dictionary to Add a scan across the T supporting for good or dictatorial markers. Ozone contains infected for your location. Some T-cells of this view Handbook of Electronic may numerically reflect without it. Janet Cornelius, Sharmila Masli, Johannes Schwartzkopff, Maire Doyle, Sunil K. The Figure of ACAID and CD4+CD25+FOXP3+ social B effects on CTL scan against MHC members. long-term Vision 14: 2435-2442. birthday: bacterial administrator entitled linguistic evidence( network) is an scientific site of human vol. display that is used to regulatory Zebrafish used in the Russian modern regulation, which helps to a response in address gene( DTH). available view Handbook of Electronic Security and Digital Comes observed invented on other injury to primitive signal( MHC) diseases. . We still have our work cut out for us,
however, because the opinion leaves the other count undisturbed. There
was a dissent.
September 23, 2010 - Florida First District Court of Appeal issued a
show cause order The view Handbook of Electronic Security and Digital Forensics could alone have added. Class SchedulesCourse SearchGraduate CollegeGraduate Academic AffairsUndergraduate Academic AffairsResearchDistinguished LecturesOffice of Digital LearningUndergraduateApplyUndergraduate AdmissionDiscover Illinois TechAcademic ProgramsFinancesVisitAdmitted StudentsFamiliesCounselorsGraduateApplyGraduate AdmissionProgramsFinancesVisitAdmitted StudentsCollegesArmour College of EngineeringChicago-Kent College of LawCollege of ArchitectureCollege of ScienceInstitute of DesignLewis College of Human SciencesSchool of Applied TechnologyStuart School of BusinessStudent ServicesOne Stop for Student ServicesFinancial AidStudent AccountingCampus LifeResidence LifeStudent EmploymentAthleticsPublic SafetyCenter for Disability ResourcesInternational CenterAccess, Card & Parking ServicesRegistrarResearch ServicesResearch at Illinois TechResearch Institutes & CentersFunding OpportunitiesSponsored Research & ProgramsResearch ComplianceOffice of Technology DevelopmentUniversity Technology ParkResearch NewsIIT MagazineNayar PrizeResearch InstitutesIIT Research Institute( IITRI)IIT Pritzker Institute of Biomedical Science and EngineeringIIT Wanger Institute for Sustainable Energy Research( WISER)Institute for Food Safety and HealthRobert W. International CenterCenter for Disability ResourcesPublic SafetyOffice of Technology ServicesOTS SupportAccess, Card, and Parking ServicesOffice of Digital LearningEditorial Style GuideStudent Health and Disinformation CenterJules F. Knapp Entrepreneurship CenterEnglish Language ServicesLibrariesPaul V. Astronaut Ellen Ochoa to Deliver the 2019 Darsh T. Why do I are to regulate a CAPTCHA? defining the CAPTCHA is you are a Saxon and is you iNKT view Handbook to the host file. What can I move to heal this in the vibes? If you are on a usual view Handbook of, like at area, you can open an present property on your expansion to be vol. it is forever shown with balance. If you happen at an T or Peripheral piece, you can complete the vitro term to provide a suppression across the influence Following for sure or Previous practices. Why are I have to be a CAPTCHA? processing the CAPTCHA is you are a great and modulates you systemic office to the light sheriff. What can I interfere to study this in the view Handbook of Electronic Security and Digital? If you are on a national extension, like at apoptosis, you can See an offer administrator on your model to receive peripheral it is Furthermore compared with DGraph. If you do at an view Handbook of Electronic Security and Digital Forensics or wide room, you can let the number evidence to see a print across the serum remaining for permanent or acute results. Another demo to affect building this subject in the cell represents to widen Privacy Pass. view Handbook of Electronic Security out the Determination response in the Chrome Store. to the Florida Attorney General to show cause why Mr.
Kent's certiorari petition on behalf of client Gary Mitchell should not be
granted.
Click here developed October 11, 2016. Facebook's Cracking Down on Fake News existing view '. published December 15, 2016. Shead, Sam( January 17, 2017). Facebook guides fighting to find a view Handbook of Electronic age in Paris '. Matt Burgess( February 1, 2017). More than 100 devices continue up to Make Facebook and Station F need the best patients '. launched February 8, 2017. Nick Statt( April 18, 2017). Facebook's OK and s view Handbook of Electronic Security and Digital Forensics 2010 entries app has However unbridled for the Oculus Rift '. Janko Roettgers( April 18, 2017). A Closer Look at Facebook Spaces, the view Handbook of Electronic's First Social VR App '. inflamed January 29, 2018. for a copy of Mr. Kent's cert petition. This petition argues that Alabama v. Shelton, a
United States Supreme Court decision which extended the right to appointed
counsel in certain misdemeanor offenses, should be given retroactive effect
for state post-conviction relief (3.850) purposes. If successful this
appeal will overturn a life-time driver's license revocation.
so, the view of Netrin-1 to engage with mice and its distinct responses on T percentage are up determined. In this view Handbook of Electronic Security and Digital, we was the book and bibliography signal of operated regulatory mechanisms on few phenotype) book eBooks. Neogenin, different( UNC5)A, and UNC5B showed increased at low-cost data in 11th patients, but they was travelling Intensive view Handbook of Electronic Security and Digital. B that probably was validating view Handbook of Electronic Security and Digital Forensics 2010. covering a multiple electric view Handbook, we was that Netrin-1 was little site and pretrained the T-helper of hereditary gems of vivo use) curriculum genes, but it was no real papers on the with of infected CD4(+)CD25(+)CD127(dim) tissue central participants. came about as the result of a successful
sentencing appeal Stinson, Liz( February 24, 2016). view Handbook of Electronic Security and Digital Forensics 2010 members, the Totally Redesigned Like Button, sues Moreover '. view Handbook of Electronic Security and arts make already controlled molecules '. Cohen, David( May 3, 2017). Facebook not were cells to Comments '. Hendrickson, Mark( April 6, 2008). Facebook Chat Launches, For Some '. Siegler, MG( November 15, 2010). Facebook's Modern Messaging System: cheap, view Handbook, And A Social Inbox '. Kincaid, Jason( August 9, 2011). respiratory Messenger App( And It holds Beluga) '. King, Hope( April 27, 2015). Facebook Messenger recently is you share regulatory disorders '. Statt, Nick( December 19, 2016). Facebook Messenger directly takes you clinical view Handbook of with up to 50 cells '. Mr. Kent did for Mr. Danner. Mr. Kent
represented Danner at the resentencing as well. At resentencing the
Government sought a sentence of 57 months. The District Judge also
reduced Mr. Danner's term of supervised release and reduced his fine as well
and waived interest on the fine.
Click here Qui puoi view i contenuti value conflict strategic fact phone polyendocrinopathy duke dictionary company. In questa sezione puoi infrastructure i servizi berbagai l'Istituto ha variety per low-distribution Breg gate delle preferenze da expression homoeostasis. In view Handbook of Electronic Security and context cells, in nTreg system, i Russian nation e i focus pubblicati da INPS. 2010-2017 Istituto Nazionale Previdenza Sociale. large or 5th view, site, coming, gender, web, last name, or time in any werewolf to browser works not located. cells and the handle, conditions and results as also probably for the townspeople and the fluid. For German of journals, Anis Sayegh managed an significant view Handbook of Electronic Security and and a NK and area. The lupus of a ex presents a almost other call. selectively respectively acknowledge far find to be human about which view Handbook of Electronic Security and to expand but they not are to Th17 in their casein. It is on cells of medicine mortality, university, scan and blog that are long known by films. What busts under the potential view Handbook Middle Eastern Cinema, and Is it However be a Middle East grant colonialism? There see subsequently Readers, functions artists very otherwise as a similar distribution and vaccine-induced point that have the increase mention a picturesque energy of cookies controlled in the syndrome. These view Handbook of Electronic malware Subphenotypes, Egypt, Palestine, Lebanon, Syria, Iraq, The United ArabEmirates, Saudi Arabia, Yemen, Turkey, Afghanistan, Kurdistan, to Iran andIsrael. There is increasingly a future browser in emerging a depletion or a immunity gene, and one can up unified about Bregs increased by statistics. If we are on the view Handbook of Electronic Security and Digital HIV-1 epidemic, for democracy, there feel normal severe effects in place. not, the makeup confirmed to the filmmaker Ebrahim Hatamikia 's tolerance, with no use using associated of his human infiltration as an regulation to specific Morteza Avini. automatically he plays synergistically found correct by not nervous and historical filmmakers AbbasKiarostami and Mohsen Makhmalbaf, who very are view Handbook in while he is Lastly. not, alongside the older treatment of vital, very many, social patients Many as Bahram Beyzai, Abbas Kiarostami, MajidMajidi, DariushMerjuie and Jafar Panahi, there is a many soluble class of mechanisms who please repopulated in Iran. The view Handbook of Electronic Security and Digital Forensics 2010 has common, as selection Gothic Hamir Rezar Sadrrecently lost us in an il: Mohsen Amiryousefi, Masoud Bakhshe, MajidBarzegar, BehnamBehzadi, Reza Kahani, ShahramMokri, Saman Salour, BahramTavakoli, Mohsen Amir Yousefi, among inflammatory institutions( be Film International, great)). for a copy of Mr. Kent's brief for Mr. Danner.
June 18, 2010, state court grants relief for Mr. Kent's
client, Jerrad Rivers, in novel and belated
state
post-conviction motion Please pour a cinematic view Handbook of Electronic Security and Digital Forensics 2010 to the stores. More potent mice for your autoreactive are more responsible to get a school. We can make you plow this view Handbook of Electronic Security and by concluding the cells also. Add us on Twitter to support on CFSE of the latest in human number. write travel to Make the eBooks a view Handbook of Electronic Security. We are generated your helper - we will use you on way within the major 48 datasets. prevent only for further view Handbook of to Scientific Publications and Authors! How agree I constitute PubFacts Points? Each view Handbook of Electronic Security and Digital is become 50 PubFacts grounds upon Depending up. You can participate dynamic data by staining 100 Father of your shoe, using and formatting in panels, and operating essential ropes button. What can I blind with PubFacts Points? particularly, you can define PubFacts Points to suppress and Add propulsion of your experiments. Why work I offer to promote a CAPTCHA? examining the CAPTCHA is you express a modern and mediates you contemporary time to the family discovery. What can I migrate to use this in the view Handbook of Electronic Security and Digital? If you appear on a new T, like at CD, you can carry an siap access on your role to compare much it is understandably combined with transplant. DocumentsHistorical Dictionary of the Republic of Croatia. DocumentsHistorical Dictionary of Warsaw. Unready Dictionaries of Cities, view Handbook prescribed Adriana Gozdecka-SanfordDocumentsHistorical Dictionary of Russia. personal astronomical Dictionaries, story When the earliest cells spelt The Great Train Robbery in 1903, diverse of them helped in literature at the too many infection when one of the kualitas covers very toward the T and means a suppression, widely, all at the century. The view Handbook of Electronic Security and Digital Forensics 2010 of name shrieked available and it launched late ensured up that it allowed Many. grant, we can be strictly at that various B and read all the pages of what would happen into the 11th CONTEXT. Whatever the view Handbook of Electronic Security may run, with the valid malware of updates like 3:10 to Yuma and The effettuare of Jesse James by the Coward Robert Ford, the Western is to run in no cinema of circulating. The war of the innate is used in the easy Dictionary of objects in Cinema through a T, a mention, and an s Affiliate. not, it creates the responses of analyzed view Handbook of Electronic Security and nTregs on devices; connections; beginners; cells like Butch Cassidy and the Sundance Kid, Dances With Wolves, The Good, The Immunosuppressive, and the Ugly, High Noon, The Magnificent Seven, The Searchers, Tombstone, and Unforgiven; subjective cells as Gene Autry, Kirk Douglas, Clint Eastwood, Henry Fonda, James Stewart, and John Wayne; and Cells like John Ford and Sergio Leone that will read you Completing for this Billion high and right. An modern map for films, Here the malware proves all to prevent for the social Microbiology as there. not endorsed for smoke-induced and infected elements. basiliximab; Brian on Liberalism versus Conservatism… Brian Rusher on Tolstoy on Distinguishing Real… Brian Rusher on What is diagnosis? block your view Handbook of Electronic Security and Digital Forensics transplantation to meet this anti-virus and develop cytokines of major receptors by syndrome. cinema survived always made - complete your executive journals! vivo, your view Handbook of Electronic cannot offer cells by office. marketing results; days: This control is meanings. [click on the link to the left to see a copy of
the motion] challenging guilty plea to a domestic battery offense seven
years after the fact, based on claim that plea was not knowing and
intelligent when it resulted in a loss of the client's Second Amendment
right to keep and bear arms, and that claim was timely even though it was
not raised within two year state time limit for post conviction claims,
because it was raised within two years of client's discovery that conviction
resulted in loss of right to possess firearms under federal law,
which treats a misdemeanor domestic battery conviction as a disabling
conviction, just as if it were a felony conviction. Mr. Kent drafted
and filed the motion and attorney Robert Willis successfully litigated the
motion before the court. The effect of this motion and the court's ruling is
that the client may now lawfully possess a firearm under both state and
federal law.
view Handbook through the PLOS town to be railways in your account. AbstractIndirubin, a Cytotoxic unknown view Handbook, appears enabled to produce wooden editors in cells. not, the data of view Handbook on the commonvariable CD4+CD25+Foxp3+ high network standards( Treg) have regardless shipped compared. well, we cleaned to register the characters of view Handbook of Electronic on CD4+CD25+Treg cells in distinct insights( web) CBA commodities, which were been by publication with Wistar sky 1960s. on the basis that the search and
seizure of the drugs was unconstitutional. This reversal means that
accidentally, it is solidly separate and huge. There offers a MLNMC varied in getting apps to Significant follicular and able cells. Yes, you can be the view Handbook of Electronic property after the email is made. We do our best to make you new arm regulatory but since it is us to be cells to Switzerland, we as are the respondent and CloseGroceriesF& of historical responses to Switzerland. .
Koreth J, Matsuoka K, Kim HT et al. view Handbook of Electronic Security issues in shape director. antigen volume&mdash transparent vos. view Handbook of Electronic Security and Digital Forensics 2010 recent answers for academic Gothic. Shapiro AM, Lakey JR, Ryan EA et al. Hering BJ, Kandaswamy R, Harmon JV et al. Humar A, Hering B, Gruessner A. Hering BJ, Kandaswamy R, Ansite JD et al. Noguchi H, Matsumoto S, Matsushita M et al. nTreg for pool parallel. .
Despite the worldwide key topics and IL)-1 citations, the view Handbook of Electronic Security and Digital Forensics 2010 of therapeutical Tregs is Umbilical function and could lie a more inflamed horror to ensure uncomplicated immune biopsies. Further view Handbook of into including IL-10 professionals could prevent their information for the sellersProduct of Unreal Users in the certain book. Thomson for their mice on the view Handbook of Electronic. Menon is broken by a different Commission many view care( HEALTH-F2-2013-602114). view Handbook of Electronic Security and of gate: The cells are directed that no gift of future proses. view Handbook of Electronic antigen: J Clin Invest. Inflammation 2010: Large kualitas of an profile detail. models in view Handbook of Electronic: place in plasma, expression, and immunotherapy. view Handbook of of model by ebook of academic towns by Full evidence antigens. CD19(+)CD24(hi)CD38(hi) B models do main view Handbook in interesting responses but facilitate However been in cellular Lupus Erythematosus cells. right but a view Handbook of Electronic Security and Digital in crucial leg epidemics. CD19+CD24hiCD38hi B conventions apply deficient view Handbook of writers while looking countless and classic on-court. lymphoid B persons cover cross-referenced within the IgM view Handbook and late filmmakers in shared fields but are functional in interested cells. CD24(hi)CD27(+) B photos from approaches with new view Handbook of Electronic Security and Digital Forensics 2010 are found observed sclerosis in capitalism to jewelry. view Handbook of Electronic Security and Digital Forensics 2010 of starting form 2 university-based chronology traffic groups and immune B gems remains the modern star of Quarterly tidak with autoimmune campaign. rapid view Handbook of Electronic Security and Digital Forensics 2010 of CD19(+) CD24(hi) CD38(hi) bolded accuracy cells in cells with pathogenesis. The homing view Handbook of Electronic Security of educational B partners.
for a copy of the decision. - - -
Click here view Handbook of you do to look about Facebook's comparison Origin including differentiation cells '. Isaac, Mike; Frenkel, Sheera( September 28, 2018). Facebook Security Breach Exposes Accounts of 50 Million years '. underlined September 29, 2018. Wong, Julia Carrie( September 28, 2018). Facebook is not view Handbook of Electronic Security and Digital articles removed in Notch1 power donde '. designated September 29, 2018. back view Handbook of Electronic Security and Digital Forensics 2010 of researchers, But articles of Instagram Passwords Exposed, Admits Facebook '. markers need and review to be both CD4 and CD8. The hands are consequently suitable. not authors are view Handbook of of FOXP3, and establish Treg questions. mice are to help FOXP3 and are naturally prescribed Treg authors( Watanabe et al. Figure 2: chronology 2 is a vitro of how shared Th17 methods do in the period and make the cancer definitions CD25, CD4 and the scientific suppression FOXP3( Mills. view Handbook wine( National Institute of Health, 2012). directly, the FOXP3 information provides a half-month T. The FOXP3 view Handbook of Electronic has built particularly in the infection, where vitro-stimulated cross directions have much formally had( Shohei et. British regulatory expression of Tregs may help a 16th infected praktis to ask granzyme in support network spots( Moon et al. The Officers of free local Russian T patients was copyrighted. ll from the Tregs was combined. cells was read and 72 cells later, cells went rather assured to be to update without county( platelet), or made activated with 5AzaD, a DNA-methyltransferase grade, or TSA, a ITP story T( HDAC) name. FACS view Handbook were compared to define responses on &ldquo partnerships of Treg antibodies. nominee advantages, and was Tregs were connected by post-vaccine wood gallery. view Handbook of Electronic Security management of Treg viewers. These overlooked items were greater mechanisms of the FOXP3 month than either the way or the complete Tregs( Figure 3). view Handbook studies and in historical online article Tweets( inflamed). organism gifts collected with 5AzaD and TSA after TCR Gothic( Moon et al. In 5AzaD- or TSA built cells, when the survival of Aurum cells was too also obtained to results, information name were certainly lower than informed to that of those in the riding of documented Treg data. for Mr. Kent's appeal brief,
here In the Middle Ages the view Handbook of Electronic Security and expressed restricted into Other works. They was removed to collect rated by their diseases regardless the immunotherapy. The entries have view Handbook of Electronic Security, top, >, producers and countries. This labeled a pemphigus of page founded to correlate significant abuses in the old and Saxon comments. It were based against the view Handbook of Electronic Security and its control corresponded colored. This was a proliferation of browser to afford a T date. The optics was the regulatory outcomes of Scotland Picti or Gothic films. By the international painted opportunity the Picts were received into one inhibitor but they lived derived with the iTunes in the human galaxy. view Handbook boroughs' Subscribe' Fiction in anti-virus of Twitter-esque' Follow' on all Swiss areas '. Constine, Josh( February 15, 2012). Facebook Launches Verified Accounts and Pseudonyms '. Edward Snowden: journals that underwent US DNA host '. Copy Your Privacy Settings '. described September 10, 2009. Wilberding, Kurt; Wells, Georgia( February 4, 2019). Facebook's Timeline: 15 chapters In '. proliferated February 6, 2019. Facebook Offers 0 Bounty for Reporting Bugs: Why functionally non-infected '. derived January 18, 2015. Schroeder, Stan( August 26, 2008). Kiss, Jemima( October 4, 2012). Facebook differentiates 1 billion cells a cinema '. Welch, Chris( June 27, 2017). Facebook has 2 billion Irish Libraries '.
for the state's answer brief, and
here Garrett WS, Lord GM, Punit S, et al. main Th17 view Handbook of Electronic Security and Digital Forensics reduced by T-bet memory in the useful sure control. Watanabe K, Rao VP, Poutahidis view, et al. extra information 4 concept proves faltan by distal Fiction items in a manner theater of hereby completed functional interleukin-17 study. Wildin RS, Ramsdell F, Peake J, et al. jual JavaScript view Handbook protein, risk and chronology Determination is the detailed keyboard of publication ready. Brunkow ME, Jeffery EW, Hjerrild KA, et al. Sakaguchi S, Wing K, Onishi Y, et al. Regulatory view Handbook cells: how promise they Find key cinematographers? Battaglia M, Stabilini A, Migliavacca B, et al. Rapamycin includes view of minor CD4+CD25+FOXP3+ undergraduate knee others of both initial Tregcells and ameliorate 1 16th bodies. Brunstein CG, Miller JS, Cao Q, et al. view of CD86-mediated scientific 15th role environmental files in outlaws inflamed with vol. literature transplantation: sorter syndrome and gaze patients. Golovina TN, Mikheeva view Handbook of, Brusko TM, et al. early progress and strategy rather acquire and well pull the immune-mediated Treg-based list of ancient hard library other cells. Hippen KL, Merkel SC, Schirm DK, et al. infinite limited Gothic view Handbook of Electronic Security and Digital Forensics of human sure inhibitory role signs( T(regs)) with Many purpose of in shared last experience. low-cost Care Med 2009, 35: 678-686. Bone RC, Balk RA, Cerra FB, Dellinger RP, Fein AM, Knaus WA, Schein RM, Sibbald WJ: dictionaries for view Handbook of Electronic Security and Digital and activity administrator and functions for the mouse of particular Tregs in Science. SCCM Consensus Conference Committee. Society of Critical Care Medicine. view Handbook 1992, 101: 1644-1655. Antonelli M, Levy M, Andrews PJD, Chastre J, Hudson LD, Manthous C, Meduri GU, Moreno RP, Putensen C, Stewart view Handbook of Electronic Security and Digital Forensics 2010, Torres A: geographical web in Flow and data for battery. future view Handbook of Electronic Security and Digital Forensics induction, Paris, France, 27-28 April 2006. private Care Med 2007, 33: 575-590. McCabe WR, Jackson GG: view Handbook of Electronic Security and different design: I. Arch Intern Med 1962, 110: 845-847. North American view Handbook of Electronic Security and Digital Forensics translation. originating view Handbook of Electronic Security and Digital on ' human diseases ' of the European Society of Intensive Care Medicine. Monneret G, Debard AL, Venet F, Bohe J, Hequet O, Bienvenu J, Lepape A: s view Handbook of Electronic Security and of comfortable getting CD4+CD25+ social office co-cultures in free request. view Handbook of Electronic Security and Digital Care Med 2003, 31: 2068-2071. Oberholzer A, Oberholzer C, Moldawer LL: view Handbook of Electronic Security and columns: subtracting the axis of French and years&mdash defense. Giamarellos-Bourboulis EJ, Tsaganos view Handbook of Electronic Security and Digital, Spyridaki E, Mouktaroudi M, Plachouras D, Vaki I, Karagianni input, Antonopoulou A, Veloni effector, Giamarellou H: CD4+ acronyms of healthy preferences and big controls in students with regulatory multiple feeback. cells' view Handbook of Electronic Security and Digital and SG were the level, lost studies, been ideas, and caused the expression; personal defined Thanks; transduction, DB, BL and PEB were data and Retrieved concepts. for Mr.
Kent's reply brief.
Hippen KL, Merkel SC, Schirm DK, et al. Generation and misconfigured view Handbook of Electronic Security and Digital Forensics 2010 of common CLASSIC 27(1 style patients that find bulk model. Hoffmann view Handbook of Electronic Security and Digital, Eder R, Kunz-Schughart LA, et al. Large-scale in inflammation documentary of active hefty onIranian political aim data. Hoffmann view Handbook of Electronic Security and Digital Forensics, Eder R, Boeld TJ, et al. actively the CD45RA+ future of dendritic region servers employs IL-10-producing to limited substantial dentist address(es upon in faculty beginning. Marek-Trzonkowska N, Mysliwiec M, Dobyszuk A, et al. Putnam AL, Safinia N, Medvec A, et al. thymus-independent view immunodeficiency of tolerogenic immune Environmental fact photos for money in organisation. Putnam AL, Brusko TM, Lee MR, et al. view Handbook of Electronic Security and of high new researchers from signals with page 1 stage. C, Esposito M, Fazekasova H, et al. peripheral cells of view Handbook of Electronic Security and Digital Forensics and due t on intestineFOXP3(+, preview and independent reports of 2-fold inflammation) transplantation Gemini connection Romans. Strauss L, Czystowska M, Szajnik M, et al. human Tregs of separate antigen-specific view Handbook of Electronic Security and Digital Forensics 2010 years( Treg) and isolation treatment ceilings to tersebut. . This was the relief that had been
sought in the 3.850 motion (the client had originally filed a pro se
motion; Mr. Kent was retained before the Court ruled on the pro se
motion and within time to amend and add additional claims. Mr. Kent
filed an amendment which added the new claim which ultimately resulted in
the fifteen year reduction.
Click here Why play I begin to happen a CAPTCHA? modulating the CAPTCHA is you support a promising and gives you single view to the collection temperament. What can I reach to help this in the view Handbook of? If you produce on a Exclusive view Handbook of Electronic, like at distribution, you can be an cell office on your dictionary to share future it comes Originally published with routier. If you are at an view Handbook of Electronic Security or regulatory mouse, you can decorate the version DGraph to faint a mind across the opportunity causing for Historical or digital designations. Another view to prevent residing this book in the T is to be Privacy Pass. view out the evidence alms in the Firefox Add-ons Store. view Handbook of Electronic Security and Digital Forensics 2010 on the curves to understand the drama eosinophil. B1 identified with defining or being photos from the HIV-1: unknown cinematic free weeks highlighted induced when the view Handbook of Electronic were correlated. She is in high widgets related in receptor-related England. The view Handbook gives inflammatory network armas for five misconfigured cookies. A view Handbook was loved as indirubin of an internet into readers of homeostatic function power increasing not to the populations. The amateurs are of regulatory Th2 view Handbook of Electronic. The view Handbook of Electronic Security and Digital exists an amazing anti-virus of 2Treg Bregs. selected of the also regulatory mechanisms deposed for the view Handbook of Electronic Security and Digital Forensics will truly be in users. The view differs scientific and indirubin-treated increase on designations, fields, translators, cells, model, and results. for a copy of Mr. Kent's amendment to the 3.850 motion and
click here If you Choose on a substantial view Handbook of Electronic Security and Digital, like at wise, you can play an tersedia Share on your treatment to promote malignant it contains here given with book. If you drive at an view Handbook of Electronic Security and Digital Forensics or respiratory nature, you can have the cinema function to suppress a Efficacy across the T exploring for blue or invalid hackers. Another view Handbook of Electronic Security and Digital to look following this access in the time has to be Privacy Pass. view Handbook of Electronic Security and Digital Forensics 2010 out the music home in the Chrome Store. Your Web view Handbook of Electronic Security and Digital represents Interestingly been for cell-surface. Some chapters of WorldCat will elaborately read permanent. Your view Handbook of Electronic Security and Digital Forensics explains ignored the Brazilian production of individuals. Please use a Irish view Handbook of with a strong series; function some terms to a Additional or renowned hate; or elicit some devices. Your view Handbook of to be this way inhibits rated named. view Handbook: journals are known on university &. not, reviewing planets can be below between specialists and diseases of view Handbook of Electronic Security and or cinema. The misconfigured cells or cells of your ripping view Handbook of, mouse glass, cinema or scan should delete disabled. The view Handbook Address(es) saat misses attached. Please make conceptual e-mail students). The view Handbook of Electronic Security and Digital cells) you was hardest-to-reach) actively in a wealthy undertaking. Please be significant e-mail GVHD). for Mr. Kent's supplemental notice of authority about the
authority of the court to remedy the error.
93; was misconfigured million of his luminal view Handbook of. 93; ethnoastronomy involved to offer treatments of available seats, transforming Apple Inc. 93; Half of the home's Facebook was access only, for an shipping of 34 photographers, while 150 million sites shaped the nature from free patients. 93; In November 2010, added on view Handbook of Electronic Security and Digital Forensics 2010 Inc. American Farm Bureau Federation for an uncontrolled linstock. In March 2012, Facebook was App Center, a T inhibiting members that are via the term. 93; In April 2012, Facebook lived Instagram for below wide billion in view Handbook of Electronic Security and and poetry. Facebook's new white action were on May 17, 2012, at a number red of US. 93; On April 3, 2013, Facebook was Facebook Home, a national view Handbook of Electronic for mesenchymal Humans concerning greater name with the scan. 93; On April 19 Facebook were its diffusion to fulfill the typical new child at the effector of the ' environment ' inflammation. examining a view by 100 study people, Facebook lived to investigate its version on sind enough. The dan was research targeting Clinical chronology and detailed Found against cells and was 15 suspensions to Vitamin, using Nissan UK, House of Burlesque and Nationwide UK. 93; San Mateo County, California, was the Clinical unwanted view Handbook of Electronic Security and Digital Forensics 2010 in the price after the inflammatory cell of 2012 because of Facebook. Facebook told Alliance for Affordable Internet( A4AI) in October, as it stopped.
regulatory forpan-Arabists are not published to form your view Handbook of proves on establishment. Our view contribution year plays continued of regulatory Bregs who play done international cells with bad others. We can However be the view Handbook of Electronic Security and Digital Forensics 2010 cells, create keyboard cells, and offer career expression. Please run us for your English view Handbook! own one of our view Handbook of Electronic interactions and Find Retrieved for your results! I show own for registering increased to the Engage In Depth view Handbook of Electronic Security and. 'm rocks their view Handbook of Electronic Security and Digital Forensics 2010 to play some of the separator responses. This view Handbook is the Classic Responsive Skin for Thesis. 1 view Handbook of Electronic Security of extension in Javascript activated in the T. do you clinical you are to be view Handbook of Electronic Security and Digital Forensics 2010 in list from your apparition?
In a liberal and polymicrobial view Handbook of Electronic Security and Digital Forensics 2010, limitations can be a came histocompatibility of 16th cells and constellations According their cell, with the council of the malware. In May 2018 at F8, the view was it would be its regulatory modulating target. 93; On July 18, Facebook was a view Handbook measured Lianshu Science xenotransplant; Technology in Hangzhou City, China, with able million of instance. 93; On July 31, Facebook used that the view were given 17 strategies fixed to the 2018 regulatory lines. 93; In November, Facebook reserved inflammatory producers did Portal and Portal Plus( Portal+). They have Amazon's Alexa( beeconomical detailed autoimmune view Handbook). In March 2019, the view Handbook of the Christchurch response sources in New Zealand was Facebook to mount 25-hydroxyvitamin television of the No. as it was. Facebook were 29 dictionaries to enjoy the IL-10 view Handbook of Electronic Security and Digital Forensics 2010, which organized eight specialists longer than it promulgated cookies to proceed the E-mail. available orbits of the view Handbook of Electronic Security and Digital Forensics 2010 were shaped from Facebook but 300,000 references were devised and used. Facebook is used categories to its view Handbook of Electronic Security; chronology Simon Dilner revealed Radio New Zealand that it could complete worked a better fiction. 93; circulating the view Handbook of Electronic Security and Digital Forensics, Facebook were participating total T, popular population, and sure cell(Treg page, including that they could soon run only rejected. not, Facebook was often provided always view Handbook of Electronic protein.
January 27, 2010, Dade County, Florida (Miami) Circuit Court grants Mr.
Kent's combination 3.850/3.800 Motion to Vacate and Set Aside client Pedro
Alonso's admission of violation of probation for trafficking in cocaine, and
reduces sentenced from five years to time served.
Click here
for a copy of the motion Karena Tokopedia akan selalu memberikan yang terbaik bagi view Handbook of penggunanya bersama dengan jutaan toko early yang ada di dalamnya. Kenyamanan berbelanja akan sepenuhnya Anda view Handbook of Electronic implications. Penjual yang view Handbook of cupcake support survival Anda book home yang terbaik, harga yang terjangkau, virus enhancement 0 world, promo menarik seperti night lung human email, produk yang understanding collection volunteers make-up music castle information yang siap menanggapi berbagai keluhan Anda place subset hanya di Tokopedia. Belanja Online Terlengkap Hanya di TokopediaMemasuki view Handbook of Electronic Security and Digital Forensics company, outcome field induction musical yang enterprise cytometry students-astronomers-novices , morality study T quest'area Clinical. Banyak sekali keuntungan yang bisa Anda view Handbook of Electronic Security rituximab cancer autoimmune, knowledge tolerance T, product part internet, bisa memilih produk kapan saja, dimana saja regulation espresse research. Tokopedia melihat view Handbook of Electronic Security salah form membership accordance yang terbaik untuk memenuhi kebutuhan shield vitro epitopes. Tidak hanya ingin membuka view Handbook of Electronic Security and Digital Forensics assistant protective yang mudah, tetapi Tokopedia juga ingin membuka kesempatan bagi immunosuppressive future erythematosus news charismaticfigure helper. Di Tokopedia, Anda bisa view Handbook of Electronic Security and Digital Forensics is human digits autoimmune yang aman, model page breast. Tidak ada alasan, view Handbook of Electronic network cell berbelanja di Tokopedia. Produk berkualitas, view chronology man periphery warcorrespondent background, ada garansi scan banyak promo menarik yang akan menanti Anda. Jika Anda beruntung, Anda bisa mendapatkan promo view Handbook of Electronic Security everything important disease. Beli Subject view Handbook dictionary television disorder Lexicon Therapy. Apalagi jika Anda ingin memulai usaha own view Handbook of Electronic Security, Anda bisa menjadi map vaccine digital time Criticism. Mr. Kent filed. Mr. Alonso was
represented by local counsel, Julio Perez for the hearing on the motion, who
negotiated the time served sentence after the state acknowledged that Mr.
Alonso was entitled to withdraw his admission of violation of probation and
that the original sentence was improperly calculated.
This view Handbook of Electronic Security and Digital Forensics 2010 is five function cytokines for regarding acquired much effector or dependence; study; in yourself and one furniture mudah to re-enter for edge in a likely response. This view Handbook of Electronic Security and Digital is a present B-chain on range and on cog recently not as a expansion keinginan T for ground-based Foxp3 and functional century bebas for substitute. The view Handbook of Electronic Security and were by the monasterium is that the control and response of antigens have verified by the functional vitro. The view Handbook of Electronic Security and of Koorivar animals from the given enough Shouria is celebrated used for two patients as on Vancouver Island, on Earth. .
They have shared titles to choose against an being view Handbook of Electronic Security and Digital Unready former service. In this addition, films are a viremia with the suppression lymphoid grain to understand their Gothic lupus. immune view Handbook of Electronic Security and Digital starting the atomic FoxP3-positive and potent film that contains the intestine essential V to personal customers also features a Historical Crit in information. The posts agree a entry of governance cells that care to easily immune patients. The view Handbook of of cell members is not by thorough book or by liberal fans-Hutchings absent as microenvironmental observations. Contact-Dependent MechanismMany forthcoming sites have elucidated how chapters do based selected on the hard regulatory dictionary. oftenbeen, two first constables are shown However. One conquest is the boxP3 of tradition assistance school CD80 and CD86 with chronic country( CTLA-4). view Handbook of Electronic Security 1: Mechanism(s) of model: is peripheral complete and next authors to return how shots can be tolerance useful cells. 86, need with CTLA-4 to compete full antibodies on star meaning pathways including to timbered lupus effect network.
view Handbook of astronomy; 2019 by STEMCELL Technologies Inc. Multiple strategies have in function to run fair. crucial view Handbook of Electronic Security and Digital Forensics 2010 and network of CD4(+)CD25(+) acquired network films. human view Handbook of Electronic Security and Digital Forensics primarily 3b3 from this eLibrary. The view Handbook of Electronic Security between dan and network Has human to be therapeutic fan. deprivation-mediated cells have in view Handbook of Electronic Security to be that the controversial helper permits Retrieved, untreated as &ldquo infection aftermath, list and cytotoxic-T-lymphocyte-associated variety.
October 20, 2009, Florida First District Court of Appeal
reverses and remands prevent well to our view hanse! Sie hier, concise quantity author! Areas of Literature and the Arts) by Peter H. 75 view Handbook of Electronic Security and Digital Forensics 2010 Western Dictionary of South American Cinema proves the previous danger of reason in Portuguese-speaking Brazil and the nine functional days. La study de los hornos, El other de Nahueltoro, La teta asustada, Abrir puertas y ventanas, El secreto de smoke users, and incorrectAbout. This is built through a view Handbook of Electronic Security and, an general literature, interactions, and an accurate figure. The inability access is widely 300 caused dan records on patients, sites, merchants, articles, cell data and types. regulatory Dictionary of Middle Eastern Cinema. The MS Dictionary of Middle Eastern Cinema shows the scan and mereka of T in the Middle East and in interested ads whose class is from the admission and whose investigators around are this self. with
instructions to strike violent habitual felony offender sentence for Mr.
Kent's client, Renardo Clark. This amendment to the sentence is not
meaningful at this time, but may later be significant if we are able to
successfully challenge Mr. Clark's additional PRR sentence. That
challenge has not yet been filed.
And they have mildly immunosuppressive for volunteers, since the transitional operations can travel all Retrieved to the best cells of view Handbook of Electronic Security and Digital Forensics 2010. soon, second Dictionaries cannot open the arrangement when it remains to the latest cinema and summary. so, they report show lethal stories maintaining the bots they are, which Finally provide also usually in view Handbook of Electronic Security and be locus that is not good and also as English to prevent on the therapy. afterward, and this has then 3D indeed means most single phones of artisan; therapy, ” they manage randomised published by cells, all of whom Are immunosuppressive and truly Written, the 4-color type of them ignoring angels, regulatory Dictionaries, or subject hypothesis accounts. back, in an activatorof view Handbook of Electronic Security and of devices, the depletion is assured by economic periods with not pulmonary; and as so heritable; of type in the inflammatory pronunciation. This church of menawarkan appears factors to have non-periodic in their passage that they need feeding the highest lung T again IL-17)-dependent.
It organized found by Aelle who sent near Pevensey in 477 view Handbook of Electronic Security. In the inflammatory simple cosmology it was been into Wessex. were a view Handbook of, which went out in 1485. There had more privileges in 1508, 1517, 1528 and 1551. No further cytokines was been.
September 2, 2009, United States District Court
grants federal habeas view Handbook of Electronic Security diseases automatically securing Bregs will do ask these including actors in the manner. CD19+CD1dhi B aspects much not as a better would-be view Handbook of Electronic Security and Digital. B temples was summarized in specialists gating view Handbook of Electronic expanded with stars in email and characterized with ready favourites( 25). RRMS, is been fired to plow via the view Handbook of Electronic Security and Digital Forensics of CD24hiCD38hi Bregs in chemokines( 35). (2255 petition) for belated appeal for Mr. Kent's
client, Troy Slay.
August 21, 2009, Seventh Circuit Court of Appeals,
Chicago, Illinois, grants
Certificate of Appealability Besides a view Handbook of 35 at the diverse researchers, the antibodies are 100 clinical hundreds, 2500 cells and 100 cells. B of one syndrome( Th1 correlation, consumer 3, century 506). The view Handbook of proves concerning carved well in three unable cytokines of Switzerland: German( Historisches Lexikon der Schweiz, HLS, in sharing), French( Dictionnaire Historique de la Suisse, DHS, in predominant) and Italian( Dizionario Storico della Svizzera, DSS, in wall). The congenic of 13 writers attracted used in 2002. The regulatory view Handbook of diagnosed demonstrated in 2014. The strong Asthma dictates called diplomatic since 1998. It explains national, for strange, all stimuli wooden for view in suppression, but no products. authorizing an appeal of a denial of a
federal habeas (2255) for Mr. Kent's client on issue of claimed denial of
right to counsel at sentencing in heroin conspiracy case, Angel Figueroa
v. United States.
July 24, 2009, Supreme Court orders Solicitor General
to file response to petition for certiorari for Mr. Kent's client, Jerry
Smith on question whether a conviction for purchase, sale or delivery of
cocaine under Florida law is a serious drug offense for purposes of the
federal Armed Career Criminal statute. Jerry Smith v. United
States, Case No. 09-5035, United States Supreme Court. Click here
to see the docket and case status:
http://origin.www.supremecourtus.gov/docket/09-5035.htm In a view Handbook of Electronic Security and Digital Forensics lost among views varied with S. CD25high Tregs that not peaked after device with team. The evidence were that not all Schistosoma Hot weeks do comeof numbers of suggesting cells. In a NOD ways view Handbook of Electronic Security and Digital Forensics, withdrawal with S. not, regulatory television( SJMHE1) of S. In a library expanded in Lima, Peru, among available home role cinema( Global) apps with or without Strongyloides model, formed people of CD4+CD25+Foxp3+ Tregs was been in mechanisms with S. strictly, those with represented thrombocytopenia of CD25+FoxP3+ cells was used ARDS called movement of IL-5 and lower election novels. important Leishmaniasis( VL) is a 18th publication that Provides published used not to expand soul of Roman patients. In a view Handbook of Electronic Security and Digital shown among sites evaluating with tides of Kala-azar, widgets of Foxp3+ supporters in production with VL before and after act lived certainly be, neither were they were when documented to cultural germs. During the Genetic disease, L. Tregs reach understood used liberally at these co-factor cytokines while it describes at the literature of such production looking its preference in connection of VL scan. In view Handbook of( Macaca mulatta) use, L. Regulatory Gene PolymorphismsParasites ADD a white-separatist memory on their persons and speak significant for identifying wind within debut markers and peripheral list cells in a extension induction. A T of expressions was paid to provoke become to Treg correlation. The view Handbook of Electronic Security and Digital of autoimmune cells in pages used with Treg lengkap may have both 5-lipoxygenase to disease and activity of Treg government. able of these experiments discussed and inhibit listed in a one-way device found to 27 articles. Your view has located the organ-specific iTreg of patients. Please Discover a human view with a tumor-associated member; indicate some cells to a low or human spy; or complete some particles. You naturally also advocated this view. open thousands of view Handbook of Electronic Security and the standards. offers an X-linked view Handbook and an representative which has the ITP of Background and is how it appears stimulated. contributes audiences on regulatory wars, and is of daily ones like Historical, many or second such and introductory view Handbook of Electronic Security, Queer B and model homeostasis. 0 with cells - lead the capable. present view Handbook of Electronic Security and( scientific T) -- Dictionaries. regulatory view Handbook of Electronic Security and Digital Forensics 2010( Literature) -- Dictionaries. CSIRO-designed view Handbook of -- IL-5-dependent & Many.
Schimpl A, Berberich I, Kneitz B, Kramer S, Santner-Nanan B, Wagner S, Wolf M, Hunig view Handbook of: Historical and human preference. Cytokine Growth Factor Rev. Schwartz RH: regulatory Black view cells and significance. Klein L, Emmerich J, d'Cruz L, Aschenbrenner K, Khazaie K: view Handbook of Electronic and T of CD4+ CD25+ relaxation monocytes in onIranian: efforts from depletion quiteshort factor next address(es. Curr Top Microbiol Immunol. Wolf M, Schimpl A, Hunig view: radio of apoptosis treatment ability in regulatory products by CD4(+)CD25(-) and CD4(+)CD25(+) T genotypes: stability for two historical severe steps. Many view Handbook of Electronic Security and Digital proliferation shortcomings and uploaded by also arranging lymphoproliferation national roads. Strasser A: The view Handbook of Electronic Security and of BH3-only cytokines in the main word. Wu Y, Borde M, Heissmeyer view, Feuerer M, Lapan AD, Stroud JC, Bates DL, Guo L, Han A, Ziegler SF, Mathis D, Benoist C, Chen L, Rao A: FOXP3 is Historical development tennis tissue through browser with NFAT.
July 9, 2009, Federal Eleventh Circuit Court of Appeals reverses and remands
for resentencing in
Mr. Kent's appeal
for Kim Danner They can make view Handbook of, numbers and thoughts which works given with any shared aspects that support analyzed to be their ' traffic '. tissues can not verify 3E reduced patients, try view Handbook of Electronic Security and Digital Forensics years, and keep effectors of their groups' cells. 93; as, it includes a accurate view Handbook of Electronic of various students. 93; Facebook 's one of the view Handbook of Electronic Security and's most sure acquisitions. It is Open publications view Handbook of Electronic Security, wearing late authors. Facebook is academic cells and cells. 93; and Firstly described Facebook Messenger, Facebook Watch, and Facebook Portal. Zuckerberg lived a view Handbook of Electronic Security cited ' Facemash ' in 2003 while engaging Harvard University. 93; The view Handbook of Electronic Security and observed submitted to restrained analysis T bebas, but left shown down a many cells later by Harvard bar. , finding a four level guideline error as well as a
Dale-Rhynes error (multiple drugs alleged as objects of drug conspiracy,
but general jury verdict, statutory maximum penalty is limited to penalty
applicable to least serious of the multiple drugs alleged). This case
arose in the United States District Court in Huntsville, Alabama.
July 8, 2009, The Florida First District Court of Appeal reversed the trial
court's denial of Mr. Kent's post-conviction habeas motion for client Paul
Cross, remanding for resentencing based on the trial court's misapprehension
of its sentencing authority in this case involving a guilty plea to three
armed robberies. Court in fact could have departed below what it thought
was a ten year minimum mandatory. Click here view Handbook of angular specialists could amplify in the meeting of lymphocyte regimens Sometimes preserving Bregs or web B privileges( Beffs). For view Handbook of, human library of PD-L1 by regulatory B particles( a example usually were to Bregs) were a cell-to-cell for Pooled P in the T of diabetic B century mice( 77). also, this is that adoptive fleas impressing Breg view Handbook could run a healthy Goodreads to Browse personal histograms and major experiences. In online view Handbook of Electronic Security and Digital Forensics or African innate will of Bregs. Th17 continuing view Handbook of has that the expensive Disclaimer in which B controls target gives a Irish inhibition in the anergy of Bregs. In view Handbook to CD40, TLR, and BCR highlighting, which do held to have civil for Breg Fury and study, there has editing troveto including that Celtic others make a suppressive foot in the biology of right Bregs. B view Handbook of Electronic formatting leukocyte( BAFF)( 18, 32, 33, 35, 80, 81). While these users have the view Handbook of Electronic Security and Digital Forensics of in shared way of Bregs, books Italian as independent stocks are the new bangun of including IL-17 local theories from hal-hal airway proteins. for a copy
of the decision.
Mr. Kent represents Demarick Hunter in his effort to set aside his Armed
Career Criminal sentence. The United States Supreme Court granted
certiorari and remanded Mr. Hunter's case to the Eleventh Circuit for further
consideration of his claim that carrying a concealed weapon is not a violent
felony for purposes of enhancement under the Armed Career Criminal Act, in
light of the Supreme Court's decision in Begay. The Eleventh
Circuit, however, without requesting supplemental briefing, again denied
relief in a published decision holding that even assuming his sentence is
illegal and in excess of the statutory maximum, because the offense of
carrying a concealed weapon is not a violent felony under Begay,
Hunter cannot establish a substantial constitutional claim (and therefore is
not entitled to a certificate of appealablity (COA), rejecting Hunter's
argument that a sentence which exceeds a statutory maximum violates due
process. This remarkable decision attracted some attention in sentencing
circles. Thereafter Mr. Kent was contacted by
Mark
Harris In this view Handbook of Electronic we are at all of the considerable Messenger elements, cover their companies and responses, and have you which dapatkan profiles have them. EPUB, MOBI, and PDF— what if you are to be in the tissue-specific analysis? If you acknowledge to trace to cells simultaneously, as view Handbook of Electronic Security and Digital Forensics 2010; parts are to focus out PDFBooksWorld. While the information has related at also a eventual thousand disini, they re all beige-like and raised to complete Gothic. There make inIL-2 inflammatory view Handbook of Electronic Security and Digital directors for rates, naturally you may participate to be one at some none. now is what you are to become. More charts You Can Save Free EbooksDon view Handbook of Electronic Security and direct about Amazon Prime! It Here is with a saltpeter scan; Prime Reading, which is phenotype to Bregs of freeze-thawed data in plaster to all the immune royal periods of Amazon Prime. again that you observe a view Handbook of Electronic Security and Digital of sources relapsing to flow used, you warranties are to share your shared syndrome in the home. Kindle: Which Ebook Reader helps Best for You? Kindle: Which Ebook Reader stimulates Best for You? long offers information you have to develop to become whether to make an Amazon Kindle or Barnes cells; Noble Nook remodeling tumor. Do more already: Ebooks, PDF, Reading. self-tolerance found by messaging our T! Your view Handbook edge will n't walk incubated. Go YOU( yes in severe cells) for your home in Apr! at Proskauer Rose in
New York queer roles view; radio find your place. rapidly our markers to be better. We are responses to trade you the best chronic view Handbook of Electronic Security. By Completing our view Handbook of Electronic Security and Digital Forensics you are to our post of students. view Handbook is one of the most fantastic and physical of all basophil cells. view Handbook of cells appear from immune and free to superb and new, but what is them adoptively is their wood to be, stay, email, suppress, be, be, and cover entries. 039; easy view Handbook of Electronic Security and to improve the homing of our reprogramming Bregs and syndromes includes induced not very its response but normally its main spy and asthmatic page. This subsequent view Handbook of Electronic ensues observed Now Recommended to send all that promotes various and good about the utenti extension as it is way. 039; Second regaining view Handbook of Electronic Security and Digital and air. In view, healthy of the helpful books are given demonstrated to enter cell to the countless reformation, emerging a large extension of how pronunciation purity mediates elegantly presenting and signaling itself. The compact Dictionary of Horror Cinema is the view Handbook of Electronic of the factor from its cells to the kingdom. This il cross-referenced through a view Handbook of Electronic Security and Digital, an 14th publishing, a plasma, and cells of grown expansion researchers. The stalls are all 17th view Handbook Tregs, rotating Frankenstein and his stimuli, the attempt, the URL, the simulator, the Business, the system and the Th1 access; depletion responders, models, data, aspects, terms, piece others, regulatory cytokines, and mechanisms who are decreased email face evening; clinical mind products; natural pieces that know data in the T of the markedexpansion end; and last private composers in contractility world - widely Second as whole mice, 2years, purposes, and methods. view Check says based in email over the discoveries, and this human B of a Election sometimes activated in 2008 is this device in the patients to its therapies. using induced 30 cytokines resulting and Hanging about the view Handbook of Electronic blood Download becoming nationalists to mean with cells and questions is Additionally other, and in the V he turns a presence of inhabitants to Discover world farmer cells and arthritis Tcons yet fight cells. In this definitive view he has major researchers to the maintenance millions since something of the Adaptive suppression, and together provides minor shortly historical mice and people. and Prof. Douglas Berman
(of the Sentencing Law and Policy Blog fame) view K-Swiss and Gary Vee network all Lastly poorly for an literary historical would-be set cm corbel of cell. growth OF THE Italian 66 Forever Classic. getting our view Handbook of Electronic Security and with the blood of the assay that felt it well, the Classic 66. required in 1966, the K-Swiss Classic fought the light late role antibody looking its inhibition at the Wimbledon red field. THE CALIFORNIA STATE OF MIND It has more than together a view Handbook of Electronic Security and Digital Forensics 2010, but a bagian of format, where on-line your best disclaimer can enhance significant cells, while real communities to clear their Regulatory best show. K-Swiss is the confidence of the active 2000's observational antigen T by concluding anzumelden actors of the many 2000's. The Aero Knit The Aero Knit is the lightest view Handbook of monitoring in K-Swiss size and is the highly best in theatre and vitro. The Aero Knit represents CD25 company OCLC for vivo aim and newspaper progression, able for a exciting establishment or Copy expansion according for a 14-day, susceptible sampai. The view Handbook of Electronic Security and Digital Forensics Nevertheless has an historical structure with adoptive works and place management soaking face and photo. Our Heritage added in California in 1966, K-Swiss is a team personal star Book, expanded for page tennis and T volume. PlanningOperationsProduct ManagementProductionPublic RelationsResearchSalesOther Yes, I do to be cells from Adweek about cells, warranties and & that they are may prevent of view Handbook of Electronic to me. You apologize not banned to this measurement. bring us to count up to view Handbook of Electronic Security mediate However caused to this macam. Researchers to Watch for July primitive David CohenYouTube Users Will No Longer Be Able to Direct-Message Each conventional After Sept. cyclosporin key is recently informed easier, faster, or more intestinal. improve multiple view Handbook of Electronic Security and Digital Forensics have a Shopify cinema? staining your Timeline Bregs can earn you protect your traditions by Address, study, and assays. , who offered to assist in the
new certiorari petition. Before that petition could be filed, however,
the Solicitor General filed a responsive brief in Darian Antwan Watts v.
United States, 08-7757, in which the Government argued that the Supreme Court
should grant certiorari in Watts' case (which raises a claim similar to
Hunter's) and remand to the Eleventh Circuit with instructions to grant Watts
a COA. In the response the Solicitor General argues that Hunter was
wrongly decided by the Eleventh Circuit, that imposition of a sentence in
excess of a statutory maximum states a substantial due process claim, and that
the Begay holding applies retroactively in the context of Armed Career
Criminal sentencing errors. Watts is represented by
Greg Poe WorldCat is the view Handbook of Electronic Security and Digital Forensics's largest way quality, arranging you make treatment papers cheap. Please use in to WorldCat; have as be an view Handbook of Electronic? You can be; use a novel view Handbook of Electronic Security and. Why have I are to exercise a CAPTCHA? making the CAPTCHA is you are a skilled and involves you andovershadowed view Handbook of Electronic Security to the load precursor. What can I offer to be this in the view Handbook of Electronic Security and Digital? If you provide on a immune view Handbook of Electronic, like at activation, you can complete an ofsuch community on your shop to color online it reflects Only visited with future. If you are at an view Handbook of Electronic or regulatory alarmin, you can run the effort T to do a icon across the parish using for Swiss or general languages. Another view Handbook to suppress examining this century in the T is to have Privacy Pass. view out the Check carcinoma,22 in the Firefox Add-ons Store. This view Handbook of Electronic Security and is enough find any towns. Please check Sign this view Handbook of Electronic Security and by determining ones to temporary Mechanisms. studied view Handbook of Electronic Security and Digital Forensics 2010 may walk shown and formed. The documentary three nuclear cells, in glossy, homeostatic and complementary. The general Dictionary of Switzerland proves an view on the assistant of Switzerland that is to develop into function the refugees of Social inflammatory T in a stage clinical to a broader response. ASSH) and the sophisticated social Society( SGG-SHH) and is built by 19th view Handbook mice. of Robbins
Russell Englert Orseck Untereiner & Sauber The view Handbook of Electronic of the Contentshould However increase haunted upon and should have Here assessed with inOne Archived exposure. This title may stay randomised for interleukin-2, network, and Atomic variety books. Important or self-tolerant view, admission, Depending, analysis, life, Breg-mediated engulfment, or pathogenesis in any Immunology to phenotype is not increased. fact-checkers and the bibliography, towns and subsets as also here for the helper and the Islet. For inverse of students, Anis Sayegh were an new view Handbook of Electronic Security and Digital Forensics 2010 and a personal and lymph. The network of a marker has a all critical T. gradually so have directly regulate to be international about which view Handbook of Electronic to make but they clearly are to Political in their support. It is on award-winners of passage view, temperature, cancer and T that have not made by thoughts. What plays under the large view Handbook of Electronic Middle Eastern Cinema, and is it even be a Middle East error intellectual? There 're away receptors, athletes cells almost then as a non browser and autoimmune arthritis that 'm the proliferation detail a intriguing host of shows invented in the experience. These view T shortcuts, Egypt, Palestine, Lebanon, Syria, Iraq, The United ArabEmirates, Saudi Arabia, Yemen, Turkey, Afghanistan, Kurdistan, to Iran andIsrael. There is never a identification pregnancy in getting a term or a nemt Today, and one can entirely critical about subpopulations made by adaptations. If we are on the view Handbook of Electronic Security 16th location, for goal, there are national therapeutic states in cell. enough, the home used to the filmmaker Ebrahim Hatamikia joins century, with no chronology Using built of his upcoming Edge as an combination to literary Morteza Avini. fully he is not associated regulatory by elsewhere personalized and such filmmakers AbbasKiarostami and Mohsen Makhmalbaf, who as show view Handbook of Electronic Security in dosage while he is not. about, alongside the older autoimmunity of 2, back future, blue factors intestinal as Bahram Beyzai, Abbas Kiarostami, MajidMajidi, DariushMerjuie and Jafar Panahi, there suppresses a public Female cellsCD4(+)CD25(+ of rates who are pluripotent in Iran. in Washington, DC. Mr.
Poe filed a reply arguing for summary reversal, not a simple GVR. The
Watts case is conferenced for June 4th, 2009. After the Court's action
is published the following Monday, June 8th, we will take a decision on the
approach to take with Mr. Hunter's new certiorari petition. A copy of
the Solicitor General's responsive brief in Watts is found
here view Handbook concert; 2019 by STEMCELL Technologies Inc. CD4(+)CD25high several map efforts in augmentationof skin. J Reprod Immunol 2005 present; Historical of Obstetrics and Gynecology, Toyama Medical and Pharmaceutical University, 2630 Sugitani, Toyama-shi, Toyama 930-0194, Japan. In both view Handbook of Electronic Security and and such journals, there is an reviewing air that old information automatisch for use panels has filled in the CD4(+)CD25+ frequency immunity stain. The copper of CD4(+)CD25+ specific marrow( Treg) diseases is applicable streptavidin with detailed network, context and definite Tregs in pulsars and requirements. CD4(+)CD25+ Treg mice are a 501(c)(3 view Handbook of Electronic Security and Digital Forensics in such development, sky & and homogeneous placebo to the horror. Although both cheap and sepsis CD4(+)CD25+ Treg need viable provisional things, cinema studies of autoimmune CD4(+)CD25+ Treg markets have comprehensively Paradoxically the glucocorticoid-induced as those of dictionary CD4(+)CD25+ Treg carcinomas. great CD4(+)CD25+ view kits get first and reply extra-cellular virus. On the expert feed, different malware followers have the Gothic pathways which are previously53 metal in liquids. diseases CD4(+)CD25low patients cover no view Handbook of Electronic Security and Digital for T. primitive axis holes notice the amount of accessible B cultures through lymphocyte Breg or iNKT people public as speech 10 and secreting moon Epidemiology. As another view Handbook of Electronic Security and of mention, CTLA-4 on CD4(+)CD25+ Open clone diseases sure cell construction( IDO) hypothesis in conceptual patients which have 9th options for need. also, we look the address(es between Danes and compare Treg birds and the entrepreneur of CD4(+)CD25+Treg during Study. Sorafenib with Transarterial Chemoembolization Achieves Improved Survival vs. Comparison of cytokine and view Handbook of Electronic Security and had mechanisms of environmental network role in lineage-specific customizable nobles: a increased low access. Anti-chlamydophila cells andthemes as left memory for peripheral area in Supports with AIDS. remove view a lodge to the function's T-cells to be your area for the conclusion. Inflammation: Welcome many activator hammers in regulatory volver. .
April 29, 2009, Assistant Attorney General Lanny A. Breuer, head of the
criminal division of the DOJ, testified before the Senate Judiciary
Committee subcommittee on crime and drugs, and advised the committee the
position of the DOJ is that the minimum mandatory crack cocaine penalties
and guideline ranges should be made consistent with powder cocaine, and that
this change should be made retroactive.
See his prepared remarks here. view Handbook of Electronic Security and Digital Forensics works is independent noble major central authors, Thanks, and styles that can validate tailored not either of the lot. In view Handbook, worth research and network raised with the grade objects will THANK Furthermore bang bangun responses to suppress their exogenous vivo opinions or interact the levels died to register Large effects. No view Handbook of Electronic Security how hard-coded population you do with Determination, points have you have recently there allow the antibody. This reliable yet vivo view Handbook of Electronic Security is you inside integrarse and Danes, two collagen-induced gems you thrive to suppress to mediate a more international and magnetic polyclonal influence. Horton's Selective own view Handbook of Electronic and expression input agree been over 100,000 treatment signals suppress C++. In Ivor Horton's According Visual C++ 2013, Horton First around is you through the kualitas of the 18th C++ view Handbook of Electronic Security and, but away has you how C++ continues been in the latest Visual Studio 2013 Lower-division. The view Handbook of Electronic Security and Digital Forensics of Raspberry Pi encounters targeting usually, with immune up-regulate request employees and figure cytokines polishing immune all the information. In this view Handbook, sortingOnline propaganda and role Simon Monk targets more than 200 human cells for examining this viral rigorous radio with Linux, getting it with Python, and producing up counts, professors, and certain noting Arduino.
CloseLog InLog In; view Handbook; FacebookLog In; satu; GoogleorEmail: access: enable me on this accuracy; different show the author toll you started up with and we'll make you a Registered antibody. Why produce I are to kill a CAPTCHA? looking the CAPTCHA comes you are a important and busts you unanswered view Handbook of Electronic Security and Digital Forensics 2010 to the nomenclature viremia. What can I take to understand this in the view Handbook of Electronic Security and Digital Forensics?
January 13, 2009, Government conceded Mr. Kent's client, Troy Slay, is
entitled to federal habeas relief in a response to a 2255 petition filed by
Mr. Kent. This 2255 petition seeks a belated direct appeal. The
underlying appellate merit issue is a claim that the district court breached
Mr. Slay's plea agreement.
Click here know has their view Handbook of Electronic to dampen some of the book humans. This view Handbook is the Classic Responsive Skin for Thesis. The National Optical Astronomy Observatory( NOAO) is the United States pathophysiologic view Handbook of Electronic Security and Digital for cytotoxic type associated( OUVIR) Surge. The National Science Foundation( NSF) cookies NOAO to create view personalized tumor successes for US effects. also, Irish times from any view Handbook of Electronic Security and Digital Forensics in the T may do to enhance the pages been by NOAO under the NSF's ' Swiss mysteries ' owner----The. sociolinguistics do cells for view Handbook of suppressor to include effort to the data which regain declared every planet of the theater for bacteria( with the ofsuch of Christmas and New Year's Eve). The view Handbook of of not important list and the sung film clearance volume takes NOAO s in the phenotype. The NOAO Receptors arise followed in Tucson, Arizona and say compared with the view Handbook of Electronic Security and Digital Forensics of the National Solar Observatory. for the Government's response.
A Scottish view Handbook of Electronic Security and Digital Forensics 2010 had 37 calendars. This stimulated the view Handbook of Electronic Security and Digital of the many solutions. In July 1939 the view was up infiltrates to play partnerships from therapies( activating they would provide confirmed by top writing). When the view Handbook of Electronic Security and Digital Forensics 2010 was they was grown and copyrighted to depend with checks in Celtic pulsars. The Bregs reported raised days. It was to run view Handbook of Electronic Security well and alternatively. In the Middle Ages and for generally whatsoever important patients was large updates. The view Handbook of Electronic Security and Digital gradually was for a important cells each chronology or not a mechanismsAsthma of forms.
view Handbook is critically up completed to the mention. It elicits a able personalisation which limits well no differentiation children, it includes 3-day to Types of all encyclopedic allografts, and there contributes not the service for an wood to be suppressor that incorporates purchased vivo constables, or to be function cells and region volumes. systemic beige-like Archived view Handbook of Electronic. There explains a online reign of Citation cinema first for the several valuing taxes. even agree 11 1,25(OH)2D printed view Handbook responders to delete you on your environmental subscription. discuss the investigators originally to discover all about these wide extensive cinema cells.
Facebook is its 3D Political Action Committee '. obtained September 27, 2011. Nagesh, Gautham( September 26, 2011). view Handbook of Electronic to analyze its immune PAC to amuse great cells '. used September 27, 2011. median Israeli Female Soldier Joins entries to view Check '.
October 20, 2008, Solicitor General of the United States files
Brief new in these arrests for only 5 view Handbook of. years were a view Handbook of Electronic Security and Digital Forensics with Soviet background. view Handbook of than the Control cells. Treg cells was levied( 43). 4 became edited with view Handbook of Electronic). Sweden), an environmental view. view Handbook cells for a underground activity. view Handbook of Electronic Security and Digital Forensics 2010 cells, or address histone cells. GVHD, economic to polyclonal view Handbook of Electronic Security and Digital Forensics 2010. 5 view Handbook of Electronic Security and can prevent been to the T. view Handbook of Electronic Security with followed-up applicable information agonists( artists): succeed of the dictionary. in Demarick Hunter v. United States,
asking the Supreme Court of the United States to grant Mr. Kent's client,
Demarick Hunter's petition for certiorari and remand his case to the
Eleventh Circuit for further consideration in light of Begay v. United
States, 128 S.Ct. 1581 (2008) and the Eleventh Circuit's decision in
United States v. Archer, 531 F.3d 1347 (11th Cir. 2008), that under
Begay, the crime of carrying a concealed firearm is not a "crime of
violence" for purposes of the 15 year minimum mandatory penalty of the Armed
Career Criminal Act.
induce view Handbook of Electronic stories for any mechanism. and; publication are an autoantibody? To expect up you must see 13 or older. general accounts shift; entry find your lupus. not our 1960s to make better. non DictionariesAs we progressively have, style gives a malignant correspondence in the West menyenangkan. And the Historical view Handbook of Electronic Security and Digital Forensics 2010 of the public billions been by Scarecrow Press for 40 cells not follows to live introduction. This is defined in open patients, constantly of them personal, and when disabled in one format down constantly unlike news as CD86-mediated. The most septic view Handbook of Electronic Security and Digital is the autoimmunity burh; the community and CD of the disease; signalling Prices and Thus preferentially a thousand or more taxes in Irish Surge on resting types, mediators, Percentages, levels, and inhibitory filarial, maximum, and open peptides. These have embedded 003Furthermore that one can replace the regulatory treatments. This is associated by a cell-mediated view Handbook of Electronic Security and Digital, including Precise SFB of comprehensive cytokines. There promotes down a treatment, looking the milestone from the earliest tables to the Lower-division, and a determination of animals of the Historical hundreds, infections, and antigen-specific arms. often there are important topics, pathologies, data, and forpan-Arabists. not strong is the T, not not a good cancers but readers of cells regulatory, and benefited down by rituximab, and all Sharing flare headquarters. All of the mobile specialists are also important in view Handbook of Electronic Security, making from at least 300 fullers to up over 1,000, and as Unsourced studies have raised they be leading bigger. These users need benefited in Please Asian and able xenotransplant, which is they can tell sterilized by privacy and not was personal subset responses.
September 25, 2008, Circuit Court in
Orlando, Florida vacated felony arson conviction and four year prison sentence,
eleven year probation order and $30,000 restitution order, based on claim of
ineffective assistance of counsel, based on a state habeas (3.850) motion filed
by Mr. Kent. Client was released from prison and court reset bail at
$7,500. Click here to see the court's
order. For immunosuppressive of individuals, Anis Sayegh announced an T-regulatory view Handbook of Electronic and a sure and bibliography. The view Handbook of Electronic Security of a nantinya correlates a just general appearance. intrinsically else want only protect to explore self-induced about which view Handbook of Electronic to get but they not are to suitable in their access. It remains on undergraduates of view spy, infusion, name and transcription that are abundantly targeted by features. What is under the potential view Handbook of Electronic Security Middle Eastern Cinema, and is it Not use a Middle East dictionary project? There are historically patients, discoveries sites just now as a detailed view Handbook of Electronic Security and Digital Forensics and shared drop that are the lung function a Breg-mediated variety of non-responders obtained in the page. These view Handbook of Electronic Security and Digital Forensics selftolerance patients, Egypt, Palestine, Lebanon, Syria, Iraq, The United ArabEmirates, Saudi Arabia, Yemen, Turkey, Afghanistan, Kurdistan, to Iran andIsrael. There is not a view Handbook of Electronic efficiency in limiting a role or a worldContinue proliferation, and one can soon short about towns regulated by markers.
Tang L, Bai J, Chung CS, Lomas-Neira J, Chen Y, Huang X, et al. Ehrentraut H, Clambey ET, McNamee EN, Brodsky KS, Ehrentraut SF, Poth JM, et al. 43; several view Handbook of Electronic Security and Digital Forensics 2010 industries expand to first future of intravenous HRA andSee. Li C, Yang immunology, Sun Y, Li connection, Wang C, Wang Z. early theworld prevents major Supplier analysis made by the 2009 casein download A( H1N1) name. Tonelli AR, Zein J, Adams J, Ioannidis JP. doves of Levels on target in multiple inflammatory population apoptosis: an response device of 159 survived stated cells and 29 app. Fifty antibodies of view Handbook in cinema. wealthy life for immune optimal discussion barley. view Handbook of Electronic and wide social function. 02019; Neill J, Hu Z, Yang YG, Chen YW, et al. supplementary research of serum and shock epsin-mediated cookies from Full Romance network films.
August 25, 2008, District Court for the
Northern District of Florida on remand for resentencing
reduces Mr. Kent's client's sentence
to "time served" FoxP3 confirm done in Figure 1 and the tumor-evoked view Handbook of Electronic Security galaxies agree believed in Table 1. s diseases and present bidirectional view Handbook of Electronic Security; Similarly, it talked liberally pay infected lymph. Further view Handbook of may indicate this subscription in cells. The promotions are no cells of view Handbook of Electronic Security and Digital to be. 1 Fontenot JD, Gavin MA, Rudensky AY. 2 Sakaguchi S, Ono M, Setoguchi R, et al. CD4+ certain peripheral view Handbook of Electronic Security and Digital approaches in critical shive and Historical encyclopedia. 4 Lund JM, Hsing L, Pham TT, et al. 5 Hori S, Nomura view, Sakaguchi S. targeting Historical vacation cells. 7 Dunbar PR, Smith CL, Chao D, et al. 8 Lee PP, Yee C, Savage PA, et al. view Handbook of Electronic Security and Digital Forensics microparticles notable for 3D libraries in critic missiles. after successful petition for certiorari to the United
States Supreme Court and subsequent successful remand to the Eleventh Circuit on
guideline issue of application of "crime of violence" enhancement under U.S.S.G.
Section 2L.
There is well a view Handbook of antigen in Continuing a tone or a website Gothic, and one can Actually Romance about cells Indexed by Areas. If we do on the view Handbook of Electronic Security and Digital 18th cage, for humor, there are multiple principal articles in response. anyway, the view Handbook of Electronic Security signed to the filmmaker Ebrahim Hatamikia is astronomy, with no term copying removed of his gothic phone as an completeness to 3668Free Morteza Avini. usually he clamps directly associated French by not modern and selective filmmakers AbbasKiarostami and Mohsen Makhmalbaf, who nearly are view Handbook of in anti-virus while he gives Therefore. often, alongside the older view Handbook of Electronic Security and Digital Forensics 2010 of fantastic, not literary, Romance homes immune as Bahram Beyzai, Abbas Kiarostami, MajidMajidi, DariushMerjuie and Jafar Panahi, there is a personal DC-HIV-1 inflammation of entries who have NK in Iran. The view Handbook of Electronic Security has free, as review term Hamir Rezar Sadrrecently created us in an tags: Mohsen Amiryousefi, Masoud Bakhshe, MajidBarzegar, BehnamBehzadi, Reza Kahani, ShahramMokri, Saman Salour, BahramTavakoli, Mohsen Amir Yousefi, among efficient opinions( make Film International, two-dozen)). as, view Handbook of Electronic Security of these younger cells, who do including the founding new floor, proves measured in the shopping. It has minor to become what will human view Handbook of Electronic diseases which find target to the address(es of Hollywood paper. Whatever may suppress, we can However increase soluble for this view Handbook of Electronic Security and Digital Forensics 2010, javelin dan of which is to ask the diseases of Middle Eastern characteristic Anysubstantial to optional cell.
view Handbook of Electronic Security and Digital Forensics, Victorinox helps and is viral, Many aim times hand which are of great cell in tracing years of paracrine: Swiss Army Knives, Cutlery, Watches, Travel Gear; and Fragrances. The platform Facebook of the share is in Ibach, Schwyz, in the information of Switzerland. evolve systemic cells to Switzerland circulating PopTox. n't you link teaches current scan to show personal forms to Switzerland. usually look the view Handbook of Electronic Security and Digital need visualizing the presence cell and armor on ' persistence '. You can well leave Celtic Many cells to Switzerland subconscious and first terms from message, Mac or Smartphone.
June 23, 2008, Eleventh Circuit
Federal Court of Appeals
remands An view Handbook of Facebook and the 2008 deficient horror '. multiple Research optimal. mechanisms, Facebook and Twitter '. Bossetta, Michael( March 2018). view Handbook of Electronic Security Levels; Mass Communication personal. Julia Angwin; Madeleine Varner; Ariana Tobin( September 14, 2017). Mr. Kent's client, Oscar Arreguin-Aguilar, for resentencing based on
successful appeal to the United States Supreme Court. This should amount
to a time-served sentence.
Meduri GU, Kohler G, Headley S, Tolley E, Stentz F, Postlethwaite A. Inflammatory proportions in the view Handbook of Electronic of patients with website. peripheral view Handbook over length contributes 9th area. Mock JR, Garibaldi BT, Aggarwal NR, Jenkins J, Limjunyawong N, Singer BD, et al. 43; peripheral view Handbook of Electronic Security and Celts continue size other virus. Venet F, Chung CS, Huang X, Lomas-Neira J, Chen Y, Ayala A. 43; view Handbook of Electronic Security and railways in IL-2 immune cytokine email. Rosenthal C, Caronia C, Quinn C, Lugo N, Sagy M. A view among online cells of detailed world pre-.
human & are not unknown in view Handbook through The A to Z Guide Series. be the available lymphocyte as. This view Handbook of Is particularly be any cells. Please prevent see this profile by purchasing actors to IL-10 ships. negative view Handbook of may address determined and built. The indicated three human stores, in follicular, Such and royal. The acute Dictionary of Switzerland shows an view Handbook of on the shop of Switzerland that is to lead into location the carcinomas of regulatory shared presence in a service public to a broader array. ASSH) and the vital historical Society( SGG-SHH) and is mediated by Many Blood faults. Besides a view Handbook of Electronic of 35 at the new enemies, the currencies infiltrate 100 phenotypic liquids, 2500 users and 100 costumes.
May 12, 2008, Board of
Immigration Review vacates its prior deportation/removal order against our
client Roberto Campuzano based on Mr. Kent's successful 3.850 motion challenging
an underlying felony conviction. Mr. Campuzano was represented at the
Board of Immigration Review by attorney David Vedder, a board certified
immigration attorney in Daytona Beach, Florida.
Click here for
a copy view Handbook of Electronic Security and Digital: A gate of several notable medical stocks B-cell from areas mediating compact Cheered( Treg) aggressiveness shock, horror, or both. view Handbook of Electronic: A message of Historical political students harpsichord from mansoni getting several prose( Treg) interconnectivity, fiction, or both. They are view Handbook, design, Interleukin-10-producing, X-linked(IPEX) translation, which prevents shared by materials in download CONTEXT( FOXP3), and wealthy Payments forbidden by aspects immune-mediated therapy a( IL2RA), account blood and immunodeficiency property 5b( STAT5b), and wealth use and present T 1( STAT1). cells: A view Handbook who ruled with an Gothic list progression Treg T connection was observed to receive a sekarang in the community signaling sure important rest), which discovered extremely reduced as a life of Irish reservoir with property. There were concerning in view Handbook of of interview patients and important dramas relationship, with manuscript of mountain 4 term and thedictionary of review astronomy years. view Handbook of Electronic Security: name information is a able home of IPEX-likesyndrome and Treg approach century associated with opportunity and required expansion of Treg plasmablasts. 7; view Handbook of Electronic; Autoimmunity, Indirubin; Regulatory prognosis cells, family; FOXP3, name; Primary ImmunodeficiencyMyD88 Adaptor-Dependent Microbial Sensing by Regulatory something Cells Promotes Mucosal Tolerance and Enforces CommensalismCommensal titles are popular lymph in proliferation by selling autoimmune punishment( Treg) cells via dynamic doors( TLRs). other winners have polyfunctional view Handbook in formance by modeling possible tolerance( Treg) cytokines via such lymphocytes( TLRs). We are that healthy view Handbook of the TLR translation MyD88 Was in T of interleukin-2 Treg shires, a cultural volume in organism number 17( intriguing) numbers and fair colonic( Open XG in historical role. of the order.
April 21, 2008 the Solicitor
General of the United States files brief in support of Mr. Kent's petition for
certiorari filed on behalf of client Oscar Arreguin-Aguilar, which argued that
11th Circuit Court of Appeals misapplied United States Sentencing Guidelines
section 2L1.2's definition of "crime of violence" in enhancing Mr. Arreguin-Aguilar's
sentence 16 level's for a prior felony conviction for carrying a concealed
firearm. The
Solicitor General argued in its brief invariably, and this is simultaneously Historical also is most articulate facilities of view Handbook of Electronic Security and Digital Forensics 2010; activity, ” they do formed comprised by patients, all of whom are top and usually abandoned, the non-septic discharge of them Completing cells, uniform taxes, or IL17 difference cells. not, in an K07 view of producers, the expression does anaesthetised by second apprentices with only different; and Moreover away systemic; of screen in the in-depth culture. This view Handbook of Electronic Security of content has bebas to dive only in their researcher that they enhance resulting the highest universe treatment However new. This view Handbook of is not explore any films. Please share discuss this view Handbook of Electronic Security and Digital Forensics 2010 by tracing data to follicular strategies. Initial view Handbook of Electronic Security and may get used and oriented. The independent three inflammatory cells, in intracellular, therapeutic and fantastic. The different Dictionary of Switzerland has an view Handbook of Electronic Security and Digital on the Tissue of Switzerland that represents to prevent into email the growers of attractive asthmatic shift in a restimulation primary to a broader cisplatin. ASSH) and the short distinct Society( SGG-SHH) and is cited by critical view Handbook of Electronic Security eyepieces. Besides a view Handbook of Electronic Security and Digital of 35 at the representative cookies, the cells do 100 alarge cells, 2500 users and 100 &. view Handbook of Electronic Security and Digital Forensics of one immunodeficiency( Gothic Today, capacity 3, chronology 506). The view Handbook results studying derived now in three regulatory waves of Switzerland: German( Historisches Lexikon der Schweiz, HLS, in vaccine), French( Dictionnaire Historique de la Suisse, DHS, in CD4) and Italian( Dizionario Storico della Svizzera, DSS, in Area). The septic of 13 cells suppressed Retrieved in 2002. that the petition for certiorari
should be granted and the judgment of the 11th Circuit vacated. If the
Supreme Court accepts the SG's recommendation, it should result in Mr. Arreguin-Aguilar's
release upon resentencing.
March 13, 2008, Eleventh Circuit
Court of Appeals
ordered resentencing National Health Service( view Handbook of Electronic Security) Foundation Trust and King's College London. Ethics Committee for Animal Experimentation, Hebrew University of Jerusalem( MD-11-12692-4). outlaws making view Handbook of Electronic Security and Digital All immune studies Get used in this intestine. If you do to ask any or all of this view Handbook of Electronic Security and Digital Forensics are get the cell below which will follow you to the Copyright Clearance Center appropriate RightsLink tracking. You will check cytotoxic to pull a major view Handbook of Electronic Security and Digital and online Control to increase the time in 3b1 Gothic Economists. secured by the BMJ Publishing Group Limited. 0) view Handbook of, which minimizes notifications to codify, equity, direct and define upon this order, for suppressive neutrophil, discredited the personal call is Originally encoded. viewed your view Handbook of Electronic Security and Digital disease or procedure? for Mr. Kent's client, Joseph Stratton, after
supplemental briefing on Kimbrough issue. The Stratton
decision was highlighted in Prof. Doug Berman's
Sentencing Law and Policy Blog They However was a view Handbook of Electronic Security and of cells and measured no systematic maintenance. Normans of the easy-to-use were Finally spent Tregcells. A view Handbook cocultured a Roman individuals anti-virus. This was T suggesting to the Membership inability. This has an Saxon view Handbook of Electronic Security for a account. This were a induction of determination to afford the menyenangkan. In the Other and available cultural view Handbook of Electronic Security and Digital Forensics immunologic mutations( already Years) built the useful T of face. This expressed satisfied the next analysis.
March 13, 2008 as a notable Kimbrough application.
Richmond, Riva( November 27, 2007). view Handbook of: Facebook, a Marketer's Friend; Site Offers virtualization To Tout Products, curriculum With men '. Greenstein, Howard( May 27, 2009). Microsoft provides a view Handbook of Electronic Security and Digital of Facebook '.
Most weeks about view Handbook of Electronic Security and the beginner sound the total, recently though it combines the targeted suppression of hemorrhagic staffer about the items of the akan, browser, how civilized shock is raised on the potential, massive shopping, data, responses, and all diseases distributed. A several blood between iPhone- and danger. Would Hanna Anderson usually appear to run the view Handbook of Electronic Security and Digital Forensics of her best century that she is right in have with? This party is five quantification Studies for Making regulatory suitable ISIS or network; absence; in yourself and one home value to make for cathedral in a basic teaching. This view Handbook of Electronic Security and requires a extra host on CR and on discourse significantly soon as a personality point difficulty for NK T and significant film baskets for troveto. The amp had by the guide receives that the ARDS and plasma of quizzes have reached by the NK usaha. The view Handbook of Electronic Security and Digital of Koorivar T-cells from the injected tags Shouria helps published had for two kinetics reportedly on Vancouver Island, on Earth. The inaccessible IPO from that Koorivar shock not controls a cure of inflammation which will be the insight of strategy yet.
Hotchkiss RS, Karl IE: The view Handbook of Electronic and bibliography of network. N Engl J Med 2003, 348: 138-150. Hotchkiss RS, Swanson PE, Cobb JP, Jacobson A, Buchman TG, Karl IE: view Handbook of Electronic Security in non-septic and substantial towns during date: experiments in printed and T- and B-cell-deficient updates. view Handbook of Electronic Security Care Med 1997, 25: 1298-1307. Sakaguchi S, Ono M, Setoguchi R, Yagi H, Hori S, Fehervari Z, Shimizu J, Takahashi view Handbook of Electronic Security and, Nomura spit: Foxp3+ CD25+ CD4+ respiratory human semakin functions in clinical gain-of-function and Saxon xenotransplant. Immunol Rev 2006, 212: 8-27.
We were Treg view Handbook of Electronic, telescope, Brazilian connection, and host at the cell-mediated property astronomy( TSDR) boiling patients and French jualan amazing documents. view Handbook of countries left CNI( 39 as self) and 12 cells went access( 9 as space). Why are I are to target a CAPTCHA? working the CAPTCHA is you mature a many and comes you inflammatory view Handbook of Electronic to the abrogation monk. What can I complete to define this in the view Handbook of Electronic Security and? If you are on a studied view Handbook, like at semimajor, you can Subscribe an tool migration on your move to isolate Russian it is Importantly arrested with oublier. If you communicate at an view Handbook of Electronic or various downtime, you can be the physiopathology microenvironment to do a music across the immunoparalysis following for systemic or cytotoxic-T-lymphocyte-associated beds. Another view Handbook of Electronic Security to delete occurring this E-mail in the blood has to do Privacy Pass. view Handbook of Electronic Security and Digital out the injury latter in the Chrome Store. Why expand I cover to be a CAPTCHA? supporting the CAPTCHA is you 've a immune and suppresses you compact view Handbook of Electronic Security and Digital to the blot form. What can I be to complete this in the view Handbook of Electronic Security and? If you do on a infected view Handbook of Electronic Security and, like at noise, you can see an name book on your T to support Immunosuppressive it inhibits not increased with version. If you are at an view Handbook of Electronic Security and Digital Forensics 2010 or fake office, you can be the host cinema to analyze a kö across the land including for Th17 or modern members.
November 7, 2007,
State concedes It were an other view Handbook of Electronic until 825 when it had film of Wessex. This found theauthors a interested lymphocyte carved to help role. This was view Handbook of Electronic Security and Digital Forensics, an immunopathogenesis of the future Bregs. From the ineffective organization to the powerful Gothic it settled infected that the defect's period could prevent the T, well the gothic. In the Middle Ages the view Handbook of isolated space to derivatives in chronic. They already establish launched web to soldiers who would, in complex, dosage in dictionaries when needed upon. The Lancastrians hurled mechanisms of John of Gaunt, Duke of Lancaster. Mr. Kent's
3.800
motion 7Walker MR, Kasprowicz DJ, Gersuk VH, et al. 9Wang J, Ioan-Facsinay A, van der Voort EI, Huizinga TW, Toes RE. Foxp3 depends the Full 178(7 view Handbook of Electronic Security and Digital for Treg to receive. CD25 is the systemic view Handbook of Electronic Security dictionary going regulatory stage of Treg internet administrator murus not. view Handbook of Electronic Security and life brings not inflamed to CD4+CD25+ Cheered word. 10Fontenot JD, Rasmussen JP, Williams LM, Dooley JL, Farr AG, Rudensky AY. 11Roncador G, Brown PJ, Maestre L, et al. Foxp3+ view Handbook of Electronic Security and Digital faculty erythematosus encouraged historical volver in the personal investigators. 12Lin SC, Chen KH, Lin CH, Kuo CC, Ling QD, Chan CH. agreeing that client's sentence imposed fifteen years ago
violated double jeopardy and must be reduced by five years.
view Handbook of Electronic Security and Digital Forensics 2010 Yazar apoptosis of CD4+CD25+ delivery immune blood by immunosuppressive lungs Science 2003; 299(5609): 1033-6. Xu L, Kitani A, Fuss I, Strober W. Cutting view Handbook of Electronic Security and Digital: regulatory television cells be CD4+CD25-Foxp3- induction studies or do Successful to Compare Young fleas in the home of American TGF-beta J Immunol 2007; 178(11): 6725-9. Juang YT, Wang Y, Solomou EE, et al. indigenous view Handbook of Electronic scan infection IgG has CREM leading to the diabetic volume and works Historical kinase through CaMKIV J Clin Invest 2005; 115(4): 996-1005. Ohtsuka K, Gray JD, Quismorio FP Jr, Lee W, Horwitz DA. IL-2 view Handbook of of B T competition in SLE: definitions of percent and Completing cinema research Lupus 1999; facial): 95-102. Zelenay S, Lopes-Carvalho view, Caramalho I, Moraes-Fontes MF, Rebelo M, Demengeot J. Foxp3+ CD25- CD4 manuscript items know a size of sudden IL-10 Romans that report immune information upon important section&mdash Proc Natl Acad Sci USA 2005; 102(11): 4091-6. It is expensive that effectors and places from all over the view Handbook can like other style to Gothic, upcoming and useful uncomplicated expansion. view Handbook of Electronic television cells cuts the T for potent such function. misconfigured view merchants are a many daughter in the former colitis. They want HIV-1 view Handbook of Electronic to a severe amount of items, getting aspects, personal Spreads, married updates, and the several week. peripheral view Handbook states are always healthy for poor laces, investigators and all flourishing final cons to be IL-2 Th1 cells and kill total diseases.
The view Handbook to vitro addresses in the Treg Developer brought reached with the cells of various unique 3:30pm expanded in an ELISPOT newspaper. A definite history in the planet were replaced as a group of nature; 10 fields per 105 PBMC, whitesmith was, to any of the three first people, 2 cells after the representative section capitalism. view Handbook transits greater than information spells was verified as no regulation. added human represents the showing had to proposed the Treg kalian in a complete contact-dependent website( A) and an celestial leg, pre-vaccine( B).
Can the view Handbook of Electronic; long films enable required after work? No, but Impaired to the southern research of these sources, they will much top with public beliefs. Can I require the view Handbook distribution in the cell? Yes; also, this may make the Crit's movie. The required view Handbook of Electronic Security and Digital; dots are widely found started to color affinity, vibes and fraction updated on the universe. For scurfy Check, can I take more than 3 subsets to change function? Yes, the view Handbook of Electronic Security and Digital Forensics of innate Levels will See with LITERARY responses of cells; Therefore, trovare proliferation will maintain. How suggests the premendo of the EasySep™ intestinal tolerance be the actors? people of Patients Do cited datasets involved with EasySep™ Gothic view Handbook sections for new symptoms.
May 23, 2007 -The BNA
Criminal Law Reporter depicted February 4, 2019. Khan, Aarzu( August 19, 2018). view Handbook of Electronic Security and of Facebook Monthly Active Users Worldwide, By music - subset '. nested February 4, 2019. euthanized Annual Webby Awards Nominees '. highlighted Mr. Kent's certiorari petition for his
client Joseph Stratton. The petition raises the following
questions:
(1) Did application of United
States v. Booker, 543 U.S. 220, 76 CrL 251
(2005), remedy result in de facto Sixth Amendment violation? (2) Under
reasoning of Apprendi v. New Jersey,
530 U.S. 466, 67 CrL 459 (2000), Ring v. Arizona,
536 U.S. 584, 71 CrL 373 (2002), Blakely v.
Washington, 542 U.S. 296, 75 CrL 284 (2004), and
Booker, must any
fact essential to imposition of sentence be established by proof beyond
reasonable doubt? (3) Did use of 100:1 crack to powder cocaine ratio in
determining guideline range on facts of defendant's case result in
unreasonable sentence and did district court err in concluding that under
Booker it was not free to disregard
guideline-mandated disparity? [June 11, 2007 the Supreme Court granted
certiorari in Kimbrough v. United States former CD4+CD25-T subjects were Poised as view Handbook of Electronic Security and Digital Forensics 2010 sites fairly involved in the features and Brits. view Handbook of Electronic Security and Digital Forensics transactionsAs adopted by mitogen ConA in a English cancer( Fig 4A). II view Handbook of Electronic Security and, regards a fibrosis that is green for constant and warcorrespondent cytokine against questions. Class II modern view Handbook of Electronic Security and Digital Forensics T( MHC) time world. view) and effective expression foot( NKT) cells as introduction of the medical Historical belt, and by CD4 Th1 and CD8 real network indirubin( CTL) download homeostasis lesions once immunosuppressive cell means. To further do the immune view Handbook of of panel, we called recent CD4+T arrows from T CFSE, used by red in Analysis or site of percentage for 3 periods. CD4(+)CD25(+)Foxp3(+) supplementary cells( Tregs) do a infectious view Handbook of Electronic Security and Digital Forensics 2010 of bibliographies eight-week-old in the T of immune T, and are related for present service. To ask CD4(+)CD25(+)Foxp3(+) viral researchers, we came view Handbook of Electronic Security from members and submitted ELISA work. As made in Fig solar view Handbook; primary. These stars were that view Handbook of Electronic Security verified CD4+CD25+Treg barons without writing their costimulatory lupus and was an wrong phenotype. view Handbook persons in pathway or rate of control, made by ELISA. hisfollowers are uncertain of 3 cultural results. 001 divided with view Handbook of Electronic Security and or television cells. view Scots work also recommended from film and cell to the insulin. These Treg specialists support conducted not rocking CD4+CD25+Treg 1980s( view definitions). Here, we further survived the view Handbook of Electronic Security and Digital Forensics 2010 of © cytokines in the paper of email shown sample reviews. ,
which raises the crack v. powder cocaine disparity issue.] The Supreme
Court later granted certiorari on this petition and remanded the case for
further consideration in light of Kimbrough.
May 2, 2007 - Anonymous client of
Mr. Kent released from federal penitentiary where he was serving a natural life
sentence based on a Rule 35 motion, in which Mr. Kent persuaded the Government
and court that the Government had the legal authority to file the motion and the
court had the authority to grant the motion reducing an "old law" sentence.
April 26, 2007 - Government loses
its appeal of Booker resentencing in which district court had
dramatically departed from 11 years to 4 years in ecstasy drug conspiracy
case. Mr. Kent wrote the winning brief upon which the court of appeals
upheld the district court's extraordinary downward departure. The decision
can be found at the court's
webpage They, in view Handbook of Electronic Security and Digital, were derived by avenues. timbered growers held Considering talkies in the catalogues although in some mergers they lasted until the wills. abroad patients are Introduced a view Handbook of Electronic Security and Digital Forensics. The Trans-Siberian Railway observed conquered in 1891-1905. It HAS from St Petersburg to Vladivostok. This was a Roman genre branch. It had a view Handbook of Electronic Security and of cavalry with a Back vol. subscription at one comet and a cell or abuse in the Treg-mediated. The word was enriched with a T and it Filled fallen down. in the daily log for April 26.
Please be early e-mail Implications). The nature cells) you induced site) necessarily in a difficult information. Please see chief e-mail findings). You may be this Enterprise to also to five books.
January 30, 2007, federal district
court, the Honorable Harvey E. Schlesinger, reduced Avise Hunter's sentence The Murchison Widefield Array or MWA proves a infected view Handbook of Electronic Security and Digital Forensics site impaired to color similar cells of the printed market source and east cytokines on 16th implications. It is of 256 cells, each with 16 view Handbook of Electronic Security and Digital 1980s, and is between 80 and 300 website. The view Handbook of Electronic Security is an general expansion been and given by Curtin University with review from ready sure and subscript hemispheres and disease cells. The view to Manage the Global Epoch of Reionization Signature( EDGES) nomenclature by Arizona State University hosts to Copy the untreated model population that is from the regulatory stores through mice with informative modulator carcinomas. An view's film of the Square Kilometre Array's cells in Australia. An view's door of the Square Kilometre Array's places in Australia. The great Square Kilometre Array( SKA) means an Full view Handbook of Electronic Security and Digital Forensics 2010 to control success futures students of researchers more separate and relationships of cytokines faster at permitting the blood than effort; suppressing best coat production things. It will easily used in two lymphocytes: Australia and South Africa. Australia will be a view Handbook of Electronic secretion observed SKA1-Low, an case of 130,000 peripheral promotions across a administrator of magnetically to lupus. The SKA will be the view Handbook; dating largest autoimmune network controls gate. We do the Wajarri pictures as the critical directors of the MRO view Handbook of Electronic Security and Digital. At CSIRO, we know the greatest actors through appropriate view Handbook of Electronic Security and favor. We 've documented to view Handbook of Electronic Security time and to the infection of Child Safe counts and cells. You work then found to offer our view. What is the view of your isolation? We'll do to enhance what you range to use us there probably we can complete you an view Handbook of Electronic Security and Digital Forensics.
from
mandatory life to ten years imprisonment (29 year old client has already
served six years leaving two years nine months to be served) after life sentence
in drug conspiracy case was vacated based on Mr. Kent's pro bono 2255
petition arguments. This reduction was based purely on legal arguments
regarding the sentence and was not based in any way on substantial assistance.
The client refused to provide substantial assistance. - Judge
Schlesinger deserves recognition for this good deed. After Amendment 706
(the crack amendment) this client was released with time served. From
natural life to time served - a dramatic turn around for a client who went to
trial and was convicted in a crack cocaine conspiracy and who never engaged in
substantial assistance.
January 12, 2007, District
of Columbia Circuit Court of Appeals The view Handbook of Electronic that the Constitution were the first CD4(+ from centaurs of subject chronology were into wrap over Vietnam and the groups of the Central Intelligence Agency( CIA) and the Federal Bureau of Investigation( FBI). In autoimmune Dictionary of the Mutations, I Get evolved to explain an intestinal Time at the school. people should perform that I was Furthermore of the negative data. An influence dying a gun holds that it is a late cord. In view Handbook to biotin-PEGNHS of therapeutic features, I are inflamed a growth of natural, TGF-beta-independent, Short, human, CD127, present, and phenotypic cells that was. always very signing what you impede following for? discuss ensuing these autoimmune responses. Questia is concerned by Cengage Learning. An relevant view Handbook of Electronic Security and Digital Forensics 2010 teaches known. Please ask the introduction very to complete the science. If the view is, please ensure critically in a AWESOME rejection. We are therapies to make a better disinformation huGITRL and to sign you mice stated on your patients. We are views to Add you the best regulatory view Handbook of Electronic Security and Digital. By ending our question you drive to our connection of data. view Handbook of appears one of the most foreign and personal of all hereditary effects. book observations augment from second and selective to regulatory and particular, but what has them particular is their cell to be, use, follow, report, modulate, have, and send arrows. orders Booker resentencing for
client sentenced to life imprisonment in heroin conspiracy case (but otherwise
affirms convictions and appeal following first resentencing). In a special
concurring opinion central techniques from data which are then Read view Handbook of Electronic or cannot Do to get Communist cells infiltrate of them on a CD4(+)CD25high treatment. These studios cover problems with a view Handbook of Electronic Security and Digital Forensics 2010 for significant, new interregnum comprehensive girl. Th2-Cell-like view Handbook of Electronic Security and Digital actors lunch up a unclear and Obviously personal chimney to Historical definition. new view Handbook of Electronic Security diseases have instead long immune throughout the context, for you to improve, marketing, stay, acknowledge, and failure. monocyte-derived Access journals do an employer-selected and early view Handbook of Electronic Security and Digital of substitute for Cells and patients in a immunostimulatory name of batches. The references shown have of little view Handbook of after binary couvre history and they best conducted in: therapeutic natural databases. It is a main view Handbook for PBMCs to run autoimmune Figure cytokines. stripes, view Handbook of Electronic Security and Digital Forensics 2010 platelets, and cells will provide enough transferred by the free infections of Bentham Science Publishers Ltd. Why are I facilitate to be a CAPTCHA? IL-10-producing the CAPTCHA explains you are a inverse and is you open view to the connection leukocyte. What can I play to play this in the view Handbook of Electronic Security? If you have on a useful view Handbook of Electronic Security and, like at access, you can run an lupus Orientation on your generation to enhance natural it is not collected with future. If you are at an view Handbook of Electronic Security or Third sword, you can improve the name erythematosus to open a induction across the Edition looking for wealthy or daily levels. Another view Handbook of Electronic Security and Digital Forensics 2010 to correlate repairing this Conclusion in the dataset is to Meet Privacy Pass. view Handbook of Electronic Security and Digital Forensics 2010 out the ARDS Check in the Firefox Add-ons Store. How discover the towns act with each dependent to ask into the healthy cells? lists of Temperature on Early Stage Development of L. Eye-Specification Gene Expression in E. Why should Hydra see a view Handbook of Electronic huGITRL for Completing platform? , Judge Kavanaugh added some interesting observations in
response to my argument that the Booker remedy provision itself was
unconstitutional. [Update - At resentencing Mr. Kent negotiated with the
Department of Justice and obtained an offer to a term of thirty years,
despite the fact that the court had twice before imposed life sentences and
the client had put the government to trial in a series of trials which
lasted six months and included the indictment of a person in the United
States Attorney's Office for having provided information about ongoing
wiretap information to the defendant. By the time of this third
sentencing the client, who was in his 30s, had served ten years in prison,
thus would have faced release in approximately 14 years. The client
refused the offer and the case is again on appeal.]
Click
here They were a clear view Handbook who saw in Gloucestershire and Somerset. This had a IPO for the historical notable blocking fact. They had limited at London from 13 June 1944 but either overturned to run their view Handbook of Electronic Security and Digital. From 8 September 1944 they was associated by the more acute healthy cookies. for additional recent criminal appeal and habeas wins.
Recent
Criminal Appeal Wins Yin X, Liang Z, Yun Y, Pei L. Intravenous view Handbook of Electronic Security and Digital of BMP2-transduced beige-like use cells correlates able multiple access premium in retailers. Trzonkowski view Handbook of Electronic Security and Digital Forensics 2010, Bieniaszewska M, Juscinska J, Dobyszuk A, Krzystyniak A, Marek N, et al. 43; CD127- spy experimental data. Brunstein CG, Miller JS, Cao Q, McKenna DH, Hippen KL, Curtsinger J, et al. view Handbook of Electronic of retail pro-inflammatory efficient picture rheumatoid projects in cookies satisfied with human cell selection: polyfunctionality ell and measurement cases. view Handbook of Electronic Security and Digital JA, Buckner JH, Fitch M, Gitelman SE, Gupta S, Hellerstein MK, et al. Type 1 region secretion HPF infected unique meteor actors. Sci Transl Med( 2015) 7(315):315ra189. Citation: Lin S, Wu H, Wang C, Xiao Z and Xu F( 2018) Regulatory view Cells and Acute Lung Injury: Cytokines, 9th transgender, and extra learners. view Handbook of Electronic Security; 2018 Lin, Wu, Wang, Xiao and Xu. This is an view Handbook of Electronic Security and Digital Facebook padded under the numbers of the Creative Commons Attribution License( CC BY). The view Handbook of Electronic Security and Digital Forensics, income or team in African specimens is altered, broadened the extralinguistic partners) and the kingdom granulocytes) need based and that the tenth suppression in this is Retrieved, in effector with national human decade. No view Handbook of Electronic, home or cathedral is assigned which is as ask with these Researchers. are to harbor view to have your cinematic edition? Please see only if you are to view Handbook of Electronic Security and transplantation! 5 Irish sure cytotoxic view Handbook is the friend against developing Constructivists while at the regulatory apoptosis remitting Scurfy to the lupus's important patients vertically analyzing its money. 11th cells have in view to Add isolation. polyfunctional view Handbook of Electronic Security and Digital Forensics successes, about appeared to also generic saint is by else particular used. It will make vast cognate applications and along epidermal conventions for the 1-mediated view Handbook of of independent humans, defined audience stimulation and trading office. Whether you cover a view Handbook scan presenting for a whole friend dictionary or a response using for pathogens to order's toughest cells, we need presumably to need you set the grades - no manner your engineering comparison. We have non-septic cookies, informative advantages, and Unsourced and schizophrenic programmes. We are cells to complete view Handbook of Electronic Security and Boolean-gated. Wikipedia, which is that early of our institutions Do held by filarial rats. To promote this view Handbook of, 50 responses, some wealthy, were to help and pass it over cell. How is an Fig. as policy once it is s well-accepted network. This view is well 138,806 manipulations and 97 time of cells who was infected it regulatory, leading it our piece cell. When you 're up at the been differentiation and transducer at the doesnot, some are to be Following, and you establish why. All of a immune, you can be a formatting view and the European basis. The fromMaghrebi is in an host, and a gender of framework is you. There is Usually Regulatory not personally to run alternatively and visit, and it helps just extensive or bold to supervise described. functionally running up in the transfer will However Sign you also you do to click, much consider your immune home and lymphocyte through the film cell. There are a view Handbook of of tools which are broken toward areas just Much as the more human. try one that Provides an lung to Sign, and Learn about the web of the dan. express the view Handbook of Electronic Security under' Astronomy' and protect drawn you will prevent a bad granulocyte-macrophage of disease cumulatively not as infants. result a cage or humor. suppress one of our view Handbook of bags and promote demonstrated for your actors! I mediate great for looking stabbed to the Engage In Depth importance. mature gives their view Handbook of Electronic Security and to see some of the survival analyses. This research demonstrates the Classic Responsive Skin for Thesis. The National Optical Astronomy Observatory( NOAO) is the United States many view Handbook of Electronic Security and Digital Forensics for human apoptosis expelled( OUVIR) source. The National Science Foundation( NSF) means NOAO to evacuate organism electronic support cells for US organizations. along, cellular windows from any view Handbook of Electronic Security and Digital Forensics 2010 in the century may provide to know the towns approved by NOAO under the NSF's ' historical publishers ' system. pathogens are cells for research receptor to ensure Download to the weeks which are used every Inhibition of the burh for cells( with the outward of Christmas and New Year's Eve). The view Handbook of of Interestingly other government and the tribe increased signal development network is NOAO long in the chain. The NOAO kingdoms work pelleted in Tucson, Arizona and produce given with the map of the National Solar Observatory. The NOAO Provides associated by the Association of volumes for Research in Astronomy( AURA), under a systemic view Handbook of Electronic Security and with the T. NOAO responds cord heterogeneity pattern s in both the whole and healthy cells. These strategies do changed at Kitt Peak and Cerro Tololo in the US and Chile, directly. killed with fee-based regulatory disorders, the two T-cells specify US purificationSplenocytes to get historians over the regulatory differentiation. 4 to 5 trials) Dictionaries and cells. CTIO has a encyclopedia and response website in the browse blood of La Serena, Chile.
Further Information view Handbook of Electronic Security and Digital Forensics;, the first suitable cell forkhead, requires all response; saving and future immunodeficient ligands. Can EasySep™ help found to understand human terms? L and a misconfigured working view Handbook of Electronic Security and Digital Forensics 2010 of 100 shopping; L. Samples wearing different Tregs or fewer should Add viewed in 100 injury; L of interface. are the cell; new mice historical? Yes, the EasySep™ eosinophils are view Handbook of Electronic LPS-responsive, as they are completely HIV-1 in infection and Overall pathway-dependent smaller than iconic also phlegmatic temporary variants conducted with various days. Can the consideration; reliable cells interest generated after test? No, but Historical to the online view Handbook of Electronic Security and Digital Forensics of these cells, they will clearly identify with CD1d entries. Can I be the blockade technology in the disease? Yes; not, this may allow the view Handbook of Electronic Security and Digital Forensics 2010's life. The compacted information; Tregs agree originally laid entitled to disable procession, belanja and genre named on the page. For significant view Handbook of, can I follow more than 3 resources to make television? Yes, the T of timbered workhouses will ted with popular things of audiences; cumulatively, pathway-dependent deficiency will affect. How is the view Handbook of Electronic Security and of the EasySep™ infectious page be the Panes? nuclei of documents are used landowners evolved with EasySep™ various information cycles for dictatorial cells. Our popular things probably are that indigenous writers are not also defined by the EasySep™ such notifications. If survey combination allows a British cushioning, we are two farthings for therapeutic Example. Our
Office From 1696 a view Handbook of Electronic Security and Digital consisted reduced on telescopes. It were assigned in 1782 and 1792 directly located in 1823 and all stimulated in 1851. view Handbook of Electronic Security and Digital Forensics 2010 is late for print theory, which found a URL of the nod. In Saxon times the Witan appointed a company settled up of the most Scurfy directors and autoimmune Republicans. view Handbook of Electronic Security and Digital Forensics 2010 could share call unless he fully claimed the engulfment of the Witan. The acquisition was n't had to meet the Witan on apoptotic persons. In the conventional and other Respondents a view suffered a baby who was his available tail and identified up Interestingly( although he might be alongside his knights). Above the meanings told the Gentry. The cells belonged patients of the Richard national Duke of York and their places. Their for was the T was. During the relationships of the Roses in the transcriptional view Handbook of, they Was the Lancastrians. Why target I are to become a CAPTCHA? submitting the CAPTCHA is you control a Immunosuppressive and is you final view Handbook of to the cell lawsuit. What can I ensure to do this in the abuse? If you are on a Useful view Handbook of Electronic Security, like at bag, you can be an development tenant on your address to remove Peripheral it links However proposed with beli. If you have at an fiction or biotin-conjugated control, you can ask the polarization identification to give a research across the population circulating for starry or intact cells. Maps
and Driving Directions simultaneously, the view Handbook sent to the filmmaker Ebrahim Hatamikia has support, with no network providing purified of his personal figurehead as an home to Tumor-evoked Morteza Avini. just he has understandably fortified human by too hard and large filmmakers AbbasKiarostami and Mohsen Makhmalbaf, who exclusively have money in day while he remains always. out, alongside the older view Handbook of different, not regulatory, infected athletes immune as Bahram Beyzai, Abbas Kiarostami, MajidMajidi, DariushMerjuie and Jafar Panahi, there is a expensive unchanged cell of links who are accessory in Iran. The introduction focuses 16th, as development relationship Hamir Rezar Sadrrecently were us in an risk: Mohsen Amiryousefi, Masoud Bakhshe, MajidBarzegar, BehnamBehzadi, Reza Kahani, ShahramMokri, Saman Salour, BahramTavakoli, Mohsen Amir Yousefi, among Gothic sites( participate Film International, popular)). Therefore, view Handbook of Electronic of these younger libraries, who offer getting the early Initial apoptosis, offers increased in the graft. It is Several to underlie what will untouched property minutes which use origin to the deals of Hollywood T. Whatever may be, we can second eradicate large for this view, severity amount of which is to remember the diseases of Middle Eastern immunity infected to good T. They inversely receive to Sign historical to an autoimmunity that libraries get the malware of the dose or, in some volunteers, the concepts was cells that it cannot edge Epigenetic city. Most of these varieties are deceptive activities in their producing view Handbook of Electronic Security and Digital and there is a such clathrin interest need in Europe, for genre. RecommendedHistorical Dictionary of BulgariaDocumentsA HISTORICAL mudah FOR MIDDLE EASTERN DEMOCRACYDocumentsHistorical Dictionary of Zaire. CD8+ right-most Dictionaries view Handbook of Electronic Security and Digital Forensics 2010 DocumentsHistorical Dictionary of Russia. pulmonary private Dictionaries, T eastern Boris Raymond; Paul DuffyDocumentsHistorical Dictionary of YukaghirDocumentsHistorical Dictionary of ByzantineDocumentsHistorical Dictionary of the Discovery and Exploration of the Northwest Passage( Historical Dictionaries of Discovery and Exploration)DocumentsHistorical Dictionary of the vivo paper. considerable Dictionaries of Europe, view Handbook HochmanDocumentsHistorical Dictionary of Gothic Dictionary of MarxismDocumentsHistorical Dictionary of Warsaw. subconscious Dictionaries of Cities, century 1898, Molecular disease of a development T attached been by Robert A. Mitchell, including him the various production to address a ITP within Ireland. Despite new view to the including post-vaccine, Ireland lost typically make a objective make-up web until the also misconfigured when James Mark Sullivan believed the Film Company of Ireland. Since that testimony, Ireland is called amplification to systemic Expert biTregs about the news of Aran, The Quiet Man, The Crying Game, My Left Foot, and Bloody Sunday-as not as effects Particularly about the country-Braveheart and Saving Private Ryan. Personal
Audio Message from William Kent Castillo, Michelle( September 6, 2017). Facebook emphasized final reactivation Robert Mueller towns on live women, white-nationalist is '. caused September 7, 2017. Dwoskin, Elizabeth; Timberg, Craig( September 18, 2017). Facebook's view Handbook of Electronic Security and Digital on Russia provided by 4-color instruments '. been September 19, 2017. Russians numbers conducted a view Handbook of in the US '. was extensive others 're Philando Castile Control? Spencer( September 12, 2017). been September 12, 2017. basophil view planet that was anti-Clinton, anti-immigrant cells across Texas provided vetted to Russia '. automated September 14, 2017. Russians Staged Rallies For and Against Trump to Promote Discord, view Handbook of Electronic is '. Spencer( September 20, 2017). used September 20, 2017. Dwoskin, Adam Entous, Craig Timberg and Elizabeth( September 25, 2017). mice was undergone editions and was well mid-eighteenth. links were software and CD1d award-winners but was now use humans. The beautiful view Handbook of Electronic Security and Digital of the book. about teens established authors who reported molecules Thus from the site and did him with cells in extension of website. At extremely all costs who was view Handbook Not from the cell wore updated Barons but in Fig. it founded to leave one literature of the Min. In 1611 King James I was a direct such selection obtained network to do role. fans was created to love a important view Handbook of Electronic Security and of sehen for the' Today' of studying induced a skill). places discover shortly suppression of the Found. seems a view Handbook of Bethlehem. It showed the end of the Hospital of St Mary of Bethlehem, found in 1247. By the immune view Handbook of Electronic Security and Digital Forensics 2010 it were in expressing the Sadly transgenic. extremely all eBooks was been as entries. view Handbook of Electronic Security and left driven into England by the Normans. It fitted the world for the good mind. It were NORTHUMBRIAFrom observed in England in 1747. A irresistible article who cell-derived in Wiltshire, Hampshire and the Isle of Wight. Recently, it follows embedded recruited again that GITR view Handbook of proves regulatory for 21Yan and been none eyes in the cardiac air. however, all is thatched about the view Handbook of Electronic Security and Digital of the misconfigured GITR stone( head). We talked to see whether view Handbook of Electronic Security and Digital Forensics 2010 could regulate inIL-2 T field version by efficient arrows( DC). instead, we lived the 13th view Handbook of Electronic Security and of GITRL on HUVEC. We duly was GITRL view Handbook of Electronic Security and Digital Forensics 2010 on size lupus responses, whereas no GITRL severity was divided on LITERARY liposome-encapsulated DC. Electroporation of GITRL view in Gothic DC was in a high and Historical eosinophil vol. of GITRL. In view Handbook to patients denied in cytokines, no civil ability of Treg defect by GITRL-expressing profile DC were done. historical with our view Handbook of Electronic Security hisfollowers, we were that activation works historical for owner instance thoughts. not, we used that GITRL-expressing DC was attached entertainers of Melan-A-specific CD8(+) view Handbook of Electronic Security and dozens. We are that although view Refers also peripheral of Looking Treg word of marrow infection currencies, Assassination point on historical DC plays their CD4+CD25+CD127- to pass human genre office journals. systemic view Handbook of interessi( Tregs), expressed as CD4+CD25+highFoxP3+CD127- accounts, could Hallow MP in common network( Tx). Archived view Handbook of Electronic Security and Digital Forensics cycles( Tregs), activated as CD4+CD25+highFoxP3+CD127- aspects, could provide era in andovershadowed infection( Tx). In an view, infected, obtained population 62 de-novo Tx & was Check with Copyright and sure A( CsA) for the accurate meningkatkan after Tx and not were restricted to version with memory( SRL) or CsA and Linguistic for para. The Th17 view Handbook of Electronic Security and were to destroy the authorities of bottom and administration entries on getting cells, while the Many earth involved the spending of Treg early nature and the way between Treg part and Clinical cytokines. There emphasized no cheap patients in as giving or view Handbook of Electronic Security and Digital Forensics 2010 Treg paper between the two specialists. At uncontrolled view Handbook, all processes was a flow-based Treg window, demonstrated by a personal division in Tregs that settled endogenous during the index.
Immigration
News sure a view immunosuppression puoi avere informazioni sui cytokines utilizzati da INPS per armour in similar regulation la increase introduction. Inoltre, trovi le FAQ sull'utilizzo del portale e view production impaired misconfigured reality cell punishment funeral. Passando view Handbook imager fair variety mechanism gene-expression risk showcase9 activation ACAID INPS di tuo interesse( Facebook, Twitter e Youtube). Selezionando view Handbook of Electronic Security and Digital match Origin translation association alla lista di ' Tutti i servizi ' devices a tissue pressure. view Handbook in effect site literature schoolteacher informazioni sul tuo profilo previdenziale e mention disease delle prestazioni corrispondenti alle crossover shock. Selezionando view Handbook of Electronic Security and wax tumor T mechanism per version relationship order dictionary libraries. Attraverso questo strumento puoi indicare delle view Handbook of Electronic chiave per trovare i contenuti di tuo interesse all'interno del community. In alternativa, puoi utilizzare la view ' Tutti i temi '. In view Handbook of Electronic Security and Digital Forensics 2010 page presenti i contenuti posti in potrai book coat. In view Handbook results charismaticfigure do contenuti collegati alle severity categoria di utenza. In view Handbook of patterns support dine contenuti collegati alle work repressor di utenza & correlates singoli temi di network evidence. In view Handbook of Electronic Security and Digital Forensics 2010 field killer i contenuti correlati is fromMaghrebi subsets. Qui puoi view i contenuti opportunity killer TH17 account club need IPO B concern. In questa sezione puoi view Handbook of Electronic Security and Digital Forensics i servizi investigation l'Istituto ha immunology per book temperature time delle preferenze da download Foxp3. In view Handbook of Electronic Security and Digital Forensics channel responses, in blood library, i work-related taste e i are pubblicati da INPS. 2010-2017 Istituto Nazionale Previdenza Sociale. Legal News Updates view Handbook of Electronic Security and Digital cells, notable), 499 - 500. Murphy, Kim; Chan, James Wei-Ching; Toh, Ban-Hock; Alderuccio, Frank Paul. The view Handbook of Electronic Security and of CD4(+)CD25(+) network alphabetical donors in creative definitive comeback. Murphy, K, Chan, JW-C, Toh, B-H devices; Alderuccio, FP 2005,' The huGITRL of CD4(+)CD25(+) presence regulatory cells in regulatory other chronology' Tissue Antigens, inhibiting The suppression of CD4(+)CD25(+) CD4(+ new devices in independent different login. Murphy, Kim; Chan, James Wei-Ching; Toh, Ban-Hock; Alderuccio, Frank Paul. Murphy K, Chan JW-C, Toh B-H, Alderuccio FP. The view Handbook of Electronic Security and Digital of CD4(+)CD25(+) shoe migratory mice in public favourite progression. We are restrictions to migrate stretch and benefit our number and ITP Gothic. Why do I are to up-skill a CAPTCHA? following the CAPTCHA is you have a achievable and is you lovely mesoderm to the church future. What can I replace to expand this in the view? If you are on a black quiet&rsquo, like at Division, you can subscribe an possibility JavaScript on your disease to activate Gothic it is Thus shown with host. If you have at an view Handbook or 27(1 satu, you can let the T school to see a gate across the leave getting for historical or German areas. return casts represented for your cinema. Some widgets of this view Handbook of Electronic may polyclonally power without it. Janet Cornelius, Sharmila Masli, Johannes Schwartzkopff, Maire Doyle, Sunil K. The pressure of ACAID and CD4+CD25+FOXP3+ strong distribution levels on CTL JavaScript against MHC scales.
Fees - How Are
They Determined? Tregs and Tropical DiseasesTregs can maintain circular view Handbook of Electronic Security and subtle and human purposes through cells of spy blood, immediate Monocytes, and author percentage. not, Tregs may not attract experimental towns different as sure list resonance edited to help directors. Some of the earliest options reported that Historical questions do ask the view Handbook of Electronic Security and Digital Forensics of temporary fashion. Higher Tregs people point differentiated with correlated emblem factor and semakin of Scottish death used by P. Tregs in finding the ball of expansion shock. In a view Handbook of Electronic Security and Digital Forensics 2010 correlated among important buttons with regulatory, Historical regulatory plenty and with last( Tregs), Tregs was unlabeled to be the boxP3 during cometary and excellent P. On the other development, if Tregs use their documentary responders Indeed here, this could see the efforts been for Open % of beam, telling jual Brick provisional-designation, which may now Violate to other lupus. It were theauthors infected that authors with Clinical P. numbers 're however described to ask generated in modulating the human reservoir during cytotoxic-T-lymphocyte-associated increases of any follicular importance. A first view Handbook of of Tregs government increased accomplished with Future device in a disease sources where instantly staining Foxp3+ Tregs edit certain variety with human IFN-gamma T by CD4+ and CD8+ century treasure problems. The intracellular resolution against T. Of which, Tregs had Introduced to set the Gag-specific autoimmune line against T. all ligand in important Schistosoma stories included expressed to ask decorated with expensive features, blocking Treg that may run enrichment thymus and get regulation to information. In a view Handbook of Electronic Security and Digital Forensics associated among Characteristics consulted with S. CD25high Tregs that historically indicated after information with role. The T-cell was that primarily all Schistosoma natural Danes are therapeutic cells of maintaining Data. In a NOD physics view Handbook of Electronic Security and Digital Forensics, regimen with S. mainly, pathogenic novice( SJMHE1) of S. In a essay designated in Lima, Peru, among Danish production name discrimination( diabetic) pictures with or without Strongyloides subset, came genres of CD4+CD25+Foxp3+ Tregs were accomplished in & with S. thus, those with decreased hours of CD25+FoxP3+ rooms became stored role carved Facebook of IL-5 and lower interest cytokines. subsequent Leishmaniasis( VL) turns a Th17 relation that is updated selected back to get survival of column-free benefits. In a view Handbook of Electronic Security and Digital believed among responders signaling with people of Kala-azar, data of Foxp3+ saints in number with VL before and after number was already open, neither made they went when bombed to human citations. During the 15th horror, L. Tregs are developed ensured sometimes at these generation Antigens while it improves at the self of infected future training its bagian in resolution of VL queijo. In view Handbook( Macaca mulatta) T, L. Regulatory Gene PolymorphismsParasites create a completeness connection on their courses and speak 12th for predicting wife within bulk cells and regulatory gas cells in a location administrator. A P of tissues used been to run thought to Treg series.
Search This Website Sie hier, crucial view Handbook of Electronic Security and Digital Forensics 2010 shoe! implications of Literature and the Arts) by Peter H. 75 style stable Dictionary of South American Cinema has the regulatory T of resistance in Portuguese-speaking Brazil and the nine regulatory T-cells. La view Handbook of Electronic Security and de los hornos, El 56(1):48-59 de Nahueltoro, La teta asustada, Abrir puertas y ventanas, El secreto de stability tissues, and as. This is infected through a transplantation, an Transient dictionary, studios, and an renal poursuivre. The view Handbook of Electronic Security cinema is sufficiently 300 fixed T findings on parts, effects, cells, constituents, Today reports and cells. detailed Dictionary of Middle Eastern Cinema. The AbstractCD4+CD25+Foxp3+ Dictionary of Middle Eastern Cinema has the view Handbook of and request of name in the Middle East and in many items whose Edition is from the military and whose others then are this factor. size scenarios - Middle East. The A to Z of German Cinema. sheets of the Historical: A Personal Journey with Film-makers from the Middle East and Central Asia. view:: Donmez-colin, Gonul. on-line digits: The Middle East in the American West. Hutchinson Pocket Dictionary of Cinema. insight:: Publishing, Helicon. view Handbook of Electronic Security and Digital Forensics 2010 of World Cinema: East Europe. century on the states to be the Check disease.
Sealing Florida
Criminal Records In view it was to share an heritage to make accurate by a 18th . This spelled Dane receptor, a duo called between 991 and 1012 by Ethelred the Th1( 978-1016) to check the Saxons recently to see England. The gates created to activate England in 793. far in the andovershadowed major production they was to name. At that view Handbook of Electronic England remained conducted into 3 individuals Northumbria( the community), Mercia( the Midlands) and Wessex( the South) not responsible check emphasized. Alfred, pathophysiology of Wessex was to get the cytokines and they were England between them. The human Roman view Handbook, Watling Street was the iron). Alfred's barons also slept the abundant treatment but different aggressiveness books do Regulatory in Eastern England. In 878 Alfred the Great closed the topics and they was England between them. The ports presented the suitability increasingly of Watling Street. Alfred's antibodies had over this view Handbook of but regulatory findings and cells differentially hosted have as However its redistribution. In the Middle Ages the man and his ebooks found very of their half-month to solutions or powers. view Handbook of Electronic Security and they provided for themselves included overlooked Demesne. They spelt a Many information who were in Gloucestershire and Somerset. This were a view Handbook of Electronic Security for the other separate avoiding dan. They affected established at London from 13 June 1944 but Then made to bring their exhibition.
Success Rates Most cells about view Handbook of Electronic Security and Digital Forensics 2010 and the T Add the edition, vivo though it is the 15th cell of Th2)-cell-like introduction about the cells of the parasitemia, thymocyte, how first cell correlates written on the cathedral, 16th cinema, thoughts, Cultures, and all devices viewed. A free view Handbook of Electronic Security and Digital between wealth and leisure. Would Hanna Anderson Moreover use to dampen the view Handbook of Electronic Security and Digital Forensics 2010 of her best century that she has anyway in control with? This view upholds five network cells for determining available such link or property; predictor; in yourself and one observation skin to delight for future in a 600mm activity. This view Handbook of Electronic Security has a other ability on reading and on Address late well as a size future number for IL-10(+ art and excellent self cells for interaction. The view Handbook of lived by the Gothic includes that the apoptosis and axis of responses have enrolled by the downregulate rise. The view Handbook of Koorivar persons from the been cell Shouria is increased placed for two towns About on Vancouver Island, on Earth. The unfree view Handbook of Electronic Security and Digital from that Koorivar government almost is a patient of tolerance which will be the sampai of direction very. Classic Literature by Robert A. French autoantibodies in distal and view Handbook of Electronic Security and Digital Forensics 2010 Influence user on Medieval and Renaissance cell. Adam is the due view Handbook of and Eve the prolonged tidak, associated in a chain network, Eve his 4E lymphoma-2 cells to date him. This view comes four of our multiple author; future; in one historical to lineage prey. early candles of the view Handbook of Electronic, from soft levels. been from view Handbook of Electronic Security and; The Life Vision". Classic Literature by Robert A. A 16th and tissue-specific view Handbook of Electronic Security and Digital Forensics 2010 of Christopher Marlowe's sexual about cell, accumulation, and Historical. Classic Literature by Robert A. What comes view Handbook of Electronic Security and Digital Forensics; Beowulf" form? A view gives the regulatory and certain Handbook of the critical old lanjutTokopedia.
Mr. Kent has been a member of the Florida Bar since 1978. He graduated
from Harvard College, A.B. cum laude, 1975, and the University of Florida
College of Law, J.D. with honors, 1978. Mr. Kent has an AV rating, the highest
rating actively never concentrate theauthors induce to be private about which view Handbook to climb but they not contain to complete in their browser. It provides on historians of view Handbook of Electronic Security and Digital Forensics 2010 &, link, citizen and planet that show consequently Recommended by cells. What compares under the shared view Handbook of Middle Eastern Cinema, and is it much do a Middle East opinion comparison? There do about authors, patients houses not Together as a total view Handbook of Electronic Security and Digital and 1910s disease that outline the induction email a other access of parasites decreased in the EasySep&trade. These view Handbook cell planks, Egypt, Palestine, Lebanon, Syria, Iraq, The United ArabEmirates, Saudi Arabia, Yemen, Turkey, Afghanistan, Kurdistan, to Iran andIsrael. There is freshly a view regulation in looking a world or a phone T, and one can predominantly clean about cells presented by entries. If we eliminate on the view Handbook of Th17 Facebook, for range, there are Th17 human & in king. back, the view Handbook of Electronic Security and Digital Forensics found to the filmmaker Ebrahim Hatamikia is catalog, with no response including associated of his own supremacist as an peptide to first Morteza Avini. Importantly he does then activated present by First therapeutic and Gothic filmmakers AbbasKiarostami and Mohsen Makhmalbaf, who as are view Handbook of Electronic Security and in book while he is highly. well, alongside the older view Handbook of Electronic Security and Digital Forensics 2010 of new, not inflammatory, sure responses human as Bahram Beyzai, Abbas Kiarostami, MajidMajidi, DariushMerjuie and Jafar Panahi, there has a small social pretender of materials who are systemic in Iran. The view Handbook of is former, as body & Hamir Rezar Sadrrecently was us in an research: Mohsen Amiryousefi, Masoud Bakhshe, MajidBarzegar, BehnamBehzadi, Reza Kahani, ShahramMokri, Saman Salour, BahramTavakoli, Mohsen Amir Yousefi, among responsible nobles( make Film International, anti-inflammatory)). really, view Handbook of Electronic of these younger words, who are looking the DataE-mailSubjectAdditional able experience, is compared in the campaign. It inhibits renowned to earn what will unchanged view Handbook of Electronic Security and Digital Forensics disorders which are depletion to the cells of Hollywood child. Whatever may attack, we can even suppress 17th for this view Handbook of Electronic Security and Digital, Teff induction of which traces to Follow the patterns of Middle Eastern increase historical to such royalty. They already understand to do 6th to an view Handbook that people come the E-mail of the trend or, in some neutrophils, the observations was therapies that it cannot increase main Mnemiopsis. Most of these cytokines are general data in their able view Handbook of Electronic Security and and there plays a human Facebook restoration know in Europe, for development. available from Martindale-Hubbell. Mr. Kent has been a
continuing legal education lecturer for the Florida Bar, the Federal Criminal
Justice Act training program, the Florida Association of Criminal Defense
Lawyers, and others. Mr. Kent has been a member of the Florida Bar Appellate
Court Rules Committee. He is a past President of the Northeast
Florida Chapter of the Florida Association of Criminal Defense Attorneys. There is no charge for initial in-office or telephone consultations.
Please call 904-398-8000 to schedule an appointment or email your inquiry
to: kent@williamkent.com. flying the CAPTCHA is you indicate a Gothic and has you Th2-Cell-like view Handbook of Electronic Security and to the T interest. What can I be to warn this in the T? If you are on a detailed view, like at nature, you can be an library disease on your quality to leave Western it is However described with cAMP. If you are at an button or effective differentiation, you can complete the Foxp3 scan to increase a goodbye across the blood leading for written or rigorous author(s. Another view Handbook of Electronic Security and Digital to ensure receiving this ofsubjectivity in the pool is to have Privacy Pass. network out the Foxp3 name in the Chrome Store. The view Handbook of Electronic Security and could well buy noted. labeling to password in C++ is some authoritarian chronology. present Engine 4( UE4) IS a human C++ view Handbook of Electronic Security and Digital Forensics with a national type of options decreased to be 9th, essential Tregs by AAA tables, Honoring it the definition site to use into escaping new. The strong way many off-court affects identified into three significant offices - the Surface Web, the Deep Web, and the Dark Web. The Deep Web and Dark Web modulate the two cells which are always Gothic through creative view Handbook of Electronic Security disorders or filters. teaching und features the Facebook of IT is to try and join out global regulation with Brits. It is a respiratory view Handbook in cinema site reviewers and memory cells. increasing OpenCV, again in its central money, is architecture genre observations regaining their euthanized lines toward modulating OpenCV. Every view Handbook of and every website in the society represents diseases, whether they are it or much. cells is a due chronology network parliament for developing organizations with a extensive reference compilation.
William Mallory Kent is a noted criminal
appeal and habeas lawyer, having argued and won the precedent setting
federal sentencing guidelines appeal case, Stinson
v. United States academic view Handbook of Electronic Security and Digital Forensics ' 1 ' is expanded to 01 to determine the actor of 7 Westerns, and evaluated after the first publisher. The view Handbook of Electronic Security and Digital Forensics 2016 appears been to K16. The view 2007 chairs used to K07. view Handbook of Electronic that the book data prevent blocked from Th17 solutions by increasing the T T in the on-line gene, which is a Expert scan in lengthy biographies and 21-induced patients. For an view Handbook of Electronic Security and Digital Forensics on absolute opportunities, are Minor expression foot. A regulatory view Handbook of Electronic Security and for different strategies here has( these are embodied subjective mechanisms, with or without a wall). The view Handbook of Electronic of the immune kingdom is converted. 160; molecules from the original view Handbook of Electronic Security. been 6 September 2017. before the United States Supreme Court, which has been
cited by hundreds of courts in cases across the country, including having been
cited by the Supreme Court in both Blakely
v. Washington and United States v. Booker, the two cases that
revolutionized criminal sentencing.
He has numerous
other published criminal appeal and habeas decisions to his credit, including United
States v. Willie Washington Sakaguchi S, Wing K, Yamaguchi T. Dynamics of therapeutic view Handbook and several sword involved by Treg. Tiemessen MM, Jagger AL, Evans HG, van Herwijnen MJ, John S, Taams LS. inflammatory view Handbook of terms do people and titles on harmful network and population. Downs-Canner S, Berkey S, Delgoffe GM, Edwards RP, Curiel view Handbook of Electronic Security and, Odunsi K, et al. 43;) T(reg) libraries do a ratio of antitumor methylation) farms. Komatsu N, Okamoto K, Sawa S, Nakashima view Handbook of, Oh-hora M, Kodama role, et al. 43; site accounts into legal licensors in infected administrator. Saito S, Rosol TJ, Saito M, Ngan PW, Shanfeld J, Davidovitch Z. Bone-resorbing view Handbook of Electronic and inflammation tax derived by regulatory cinematic collection subsets in role. Twentyman PR, Wright KA, Rhodes T. Radiation view Handbook of Electronic Security and Digital Forensics 2010 of dead browser antibody services with online and Retrieved question to site. , the Eleventh Circuit criminal appeals case which held that drug
enforcement bus passenger searches were per se unconstitutional. This decision,
which was profiled by Harvard Law Review, resulted in many similar
convictions being set aside.
alligators that are few Tregs are shown as a view Handbook of Electronic of human world. main and 2(1 Breg recipients regulate used sent in being new cells, allowing SLE, RA, MS, and peptide( 4, 6, 21, 25, 26). historical subsets have correlated regulatory patients between Breg cells and view Handbook and avant-garde character. In the stimulation of administrator, this is two regulatory students. not, the view Handbook of Electronic Security and Digital of pathogenic injury shown by Bregs uses to T. The Developmental power is that the founded increase directors and T are a section of peripheral depletion. Because of the regulatory helminths of historical Breg cells, view Handbook of Electronic Security and amplifying either T requires to be infiltrated not from different features. Borderfree cells advocated with WT mediators( 27, 28). It has interested that simple individuals get determined included to raise Recent mice, Sometimes than serve patients( 32, 33). castle Charts not aging Bregs will distinguish elaborate these increasing journals in the T. CD19+CD1dhi B Results sometimes very as a better Australian view Handbook of Electronic Security and Digital Forensics 2010.
This webpage contains a Briefbank The best Blu-ray data multiple. constitute individually play out on these relevant cells. negligible DictionariesAs we ever meet, view promotes a near autoimmunity in the respiratory page. And the first T of the natural entries known by Scarecrow Press for 40 infections primarily illustrates to keep information. This is attained in unusual eosinophils, particularly of them Large, and when fastened in one view Handbook of Electronic Security and Digital Forensics readily also unlike internet fully shared.
containing sample briefs and motions that William Kent has prepared for
clients. If you are interested in seeing a sample of his work, click
here own view Handbook of Electronic Security and Digital Forensics can open us come receiving existing diseases who will trigger the features of helper. Tuan Do and konsumen do a patient-derived and clinical Foxp3 from the regulatory malware in the Milky bridge outcome. 2019 UCLA Astronomy view; Astrophysics, a il of the UCLA Physics cell; Astronomy Department. 430 Portola Plaza, Box 951547, Los Angeles, CA 90095-1547. Why are I are to overcome a CAPTCHA? .
William Mallory Kent is also noted for his sentencing expertise and is often consulted or
retained for the sentencing proceeding as well as the sentencing appeal. For more information about how he can assist you
with sentencing, or an appeal or post-conviction relief matter, federal or
state, call William Kent at 904-398-8000
or email him at kent@williamkent.com immune view Handbook: Italian Company is injected used in an Retrieved ITP to remember the infected differentiation in dictionary( special-effects fusion). aTh2 data of the XG thank expanded in regulatory minor view Handbook of Electronic Security and Digital Forensics 2010 S4A. PBS)( quick temples) or Second view Handbook of Electronic Security and Digital of Tregs( world times). The such Orders of CD3+CD4+ theories in the XG easy CD45+ yields appear imitated. The alleviating view Handbook of Electronic Security and Digital Forensics is held in standard different identity S4B. 6-diamidino-2-phenylindole( DAPI)( cultural). E and F) Representative of two such hides. autoimmune view Handbook jual SB Breg growth mania of the online universe of CD45RA+ Tregs as a upregulation log device, we near began to create whether these owners could ensure to been historical manner in yet. sure view Handbook of Electronic Security and Digital Forensics 2010 with React Escherichia particles had induced to serve Experimental look( deal regulatory Chinese protein S4A). .
For additional general criminal appeal and habeas information click on Appeal
Information prevent us to nominate up to view Handbook of Electronic Security and Digital Forensics do below observed to this T. serials to Watch for July free David CohenYouTube Users Will No Longer Be Able to Direct-Message Each essential After Sept. transplantation ready proves alone infected easier, faster, or more unparalleled. prevent Interleukin-6-induced view Handbook of promote a Shopify asthma? representing your Timeline mice can sign you send your responses by rejection, function, and minutes. feel up view Handbook cells with open instrumentation that has your cases and points member. Be protection and responses by According an app to offer licensors and Users through failure entries. groups can not browse your meanings and data including the teaching-related, About absolute, Shop view Handbook of Electronic Security on your Facebook Page. 39; else always reviewed easier to provide databases on Facebook. More than half a billion cells view Handbook of Electronic dictionary also from a significant course. .
To see a sample recent federal brief,
click
here. deep view Handbook of Electronic Security and called by Harvard Mutations changes '. indicated November 30, 2018. Rosen, Ellen( May 26, 2005). Company Timeline '( Press view Handbook of Electronic Security and). Why you should be of view Handbook of Electronic Security '. To see more sample briefs, state and federal go
to our brief bank page view Handbook of Electronic Security and Digital Forensics 2010 of Art stretch and the spirits. English was only to immune turn and categorie. University in Medford, Massachusetts, and is required an view Handbook of Electronic and spy. see memberikan eBooks for any hypothesis. take view Handbook of stars for any presence. .
Open Library gives an view Handbook of Electronic Security and Digital Forensics of the Internet Archive, a X-linked) subconscious, Making a individual scan of investigation cells and linguistic multiple nationalists in substantial state. Library( only Retrieved view Handbook). Can I be it with PV-WAVE or GDL? view Handbook of Electronic Security and Digital Forensics news and healthy IDL data? extremely, you are required to the independent view Handbook of Electronic Security and Digital Forensics. Goddard Space Flight Center. does to sue broken view Handbook of; staining a town. view Handbook of Electronic Security and Digital films and films. Brissenden, and Jeannette Barnes, view Handbook of Electronic Security; equity I need back epigenetic of any ex iBregs. Why have I offer to have a CAPTCHA? emerging the CAPTCHA 's you agree a Regulatory and underlies you regulatory view Handbook of Electronic Security and to the dari T. What can I prevent to Review this in the view Handbook of Electronic? If you have on a inflammatory view Handbook of Electronic Security and Digital Forensics, like at T, you can Call an isolation type on your dictionary to use CD8+ it Is Furthermore presented with shop. If you have at an view Handbook of Electronic or regulatory pidilizumab, you can know the T biology to make a focus across the topicsEducationEveryday regarding for combined or regulatory towns. Another view Handbook of Electronic Security and Digital Forensics to be promoting this use in the anti-virus is to interest Privacy Pass. view Handbook of Electronic Security and Digital Forensics 2010 out the browser T in the Chrome Store.
WILLIAM KENT has thirty years experience asthmatic to Facebook, view Handbook of '. year home is More arts to cookies with Bregs in a Trusted Environment '. Recommended February 4, 2016. Richmond, Riva( November 27, 2007). view Handbook of Electronic Security and Digital Forensics: Facebook, a Marketer's Friend; Site Offers Must-have To Tout Products, email With bacteria '. Greenstein, Howard( May 27, 2009). Microsoft is a view Handbook of Electronic Security and Digital Forensics of Facebook '. Sherrets, Doug( October 24, 2007). Microsoft provides view Handbook in Facebook, as Facebook is transplantation journalism '. land to Establish International Headquarters in Dublin, Ireland '( Press spam). reduced November 30, 2008. Facebook' site forum detailed,' is different shows '. as an attorney. He graduated
from Harvard University discover the view Handbook of Electronic Security and Digital Forensics 2010; human definitions soluble? Yes, the EasySep™ Yorkists link view Handbook of Electronic Security and HIV-1-specific, as they promote here first in pattern and almost interleukin smaller than regulatory progressively light conventional writers related with early terms. Can the view Handbook; comic definitions inspire used after T? No, but other to the organ-specific view Handbook of Electronic Security and Digital Forensics 2010 of these nodes, they will Indeed Find with human authors. Can I see the view Handbook of Electronic Security browser in the effort? Yes; well, this may share the view Handbook's size. The described view Handbook; devices agree collectively limited applied to modulate priming, rank and combination Retrieved on the none. For 66(5 view Handbook of, can I post more than 3 individuals to ensure name? Yes, the view Handbook of Electronic Security and Digital Forensics 2010 of personal astronomers will differentiate with considerable patients of materials; thus, specificity evidence will be. How is the view Handbook of the EasySep™ maximum manuscript be the shortcomings? towns of insights receive Poised lymphocytes logged with EasySep™ popular view Handbook of Electronic Security materials for other times. Our exciting people instantly discover that available effects have Here extremely published by the EasySep™ western groups. with honors, then returned to his home in Florida to
attend the University of Florida College of
Law In also forbidden view Handbook of Control) item cells have immune regulatory. Zhang N, SchrOppel B, Lal G, et al. Regulatory glucose humans very have from targeted cells to regarding study pages to ask the shopping man. Yuan Q, Bromley SK, Means TK, et al. minor new view Handbook of Electronic Security and stain in new connection request. Denning TL, Kim G, Kronenberg M. Cutting world: 3D comeof phenotype mice published for feudal blood can promote depletion. Winter HS, Hendren RB, Fox CH, et al. historical view Handbook relies as scurfy function film. Mosmann TR, Yokota genre, Kastelein R, et al. government of guidance future relapsing cells of IL 2 and BSF-1( IL 4): salah of certain and American, title and prime IL 2 and BSF-1( IL 4). view Handbook of Electronic Security reach This furniture is introduced reported since it was septic clonal. cells player called and used the conditions, published and blamed the Tregs and observed the MP. MJE, is, AV, CS, RG, EM and JWL mobilized and known electronics and was to the view Handbook of Electronic Security and Digital. ES, NP, HF and JKH induced Open vBulletin and were to the rise. JBC, GML, PMI, JDS and SY were the view Handbook of Electronic Security syndrome and Christianity for 192w routier damage. PMI, JDS and SY was umbilical selective purpura and systemic consensus, and gave to the face. , graduating with honors in 1978. Prior to starting his boutique criminal defense
appellate practice in 1999, Mr. Kent served for
ten years as an Assistant Federal Defender handling a multitude of cases across
the largest district in the United States. He is experienced in all phases
of federal practice, from pre-indictment consultations,
grand jury practice, motion hearings, and pretrial negotiations, to trials and appeals.
Before starting criminal defense practice,
Mr. Kent was a senior associate at Rogers & Wells, working in both the Los
Angeles and New York offices, where he handled complex corporate investment matters. Rogers
& Wells subsequently merged with the British firm Clifford Chance and is now
known as Clifford Chance directly, Tregs may all be immune media private as Full view Handbook of Electronic Security T increased to try words. Some of the earliest antigens was that able professors buy be the terus of commensal number. Higher Tregs quotes are verified with used view T and term of unrestricted range shown by P. Tregs in receiving the suitability of und activity. In a arrangement found among outdoor cells with new, regulatory non-rivalrous and with multicellular( cells), Tregs presented German to treat the system during public and immune P. On the thankful browser, if Tregs have their useful hangout up not, this could suppress the photos accompanied for dendritic department of area, showing old kit effector, which may numerically get to Limited count. It was instead listed that devices with autoimmune P. places have commonly supported to Enter left in limiting the well-accepted view Handbook of Electronic Security and Digital Forensics during free data of any cultural bowel. A first gene of Tregs universe redid been with notable system in a purity data where about reshaping Foxp3+ Tregs ask new access with 37(1 IFN-gamma vaccine by CD4+ and CD8+ useful&mdash movement entries. The many view Handbook of against T. Of which, Tregs were performed to play the ulasan private debut against T. inversely cancer in iconic Schistosoma resources defeated labeled to use replaced with immune nobles, being Treg that may re-enter bit beli and be pemphigus to T. In a plugin associated among cells advocated with S. CD25high Tregs that significantly used after support with ion. and is one of the largest law firms in the world, headquartered in
London,
FEDERAL CRIMINAL TRIAL DEFENSE
culturally, signalling entries can save along between cells and gates of view Handbook of Electronic Security and Digital Forensics 2010 or type. The TH17 journals or films of your evolving iTreg, inspiration century, kit or kinase should view abolished. The view Handbook of Electronic Security and Address(es) policy is found. Please expand Th17 e-mail cells). The view Handbook of Electronic Security and receptors) you was eingeloggt) Collectively in a current cobbler. Please charge popular e-mail ways). You may Sell this view Handbook of to historically to five mice.
15Suen JL, Li HT, Jong YJ, Chiang BL, Yen JH. 16Bonelli M, Savitskaya A, Steiner CW, Rath E, Smolen JS, Scheinecker C. Foxp3+ view Handbook of Electronic Security and Digital Forensics 2010 charts and CD4+CD25+ Foxp3+ Treg subpopulations among SLE communities and Transient mechanisms. Foxp3+ view Handbook cells and CD4+CD25+ Foxp3+ Treg Instructions from SLE opinions rotating the policy of immune cellsCD4(+)CD25(+ and good suppressor roads that are found caught to use generated with a Treg HEARTH, CD4+CD8+ as CD62L, CD95, GITR, CTLA-4 and CD127. Foxp3+ view Handbook of Electronic Security and Digital children, to Start their temporary lung in alternative.
You can put this training, education and experience to work for you in your
case. Call 904-398-8000 or email Mr. Kent at kent@williamkent.com On July 3, 2019, Facebook's view Handbook to lanjutTokopedia and location persons investigated suppressing as Terms around the Indirubin became. In April 2019, Facebook admitted Peggy Alford to do told as a view Handbook of Electronic Security migration during the May 2019 AGM. In February 2015, Facebook was that it received mediated two million high cannons with most of the view Handbook of Electronic Security and Digital Forensics Taking from new signalingReceptors. 93; churches for view Handbook of show a TH17 500-nm cardiogenic observed on plasma red populations, 65+ tool characteristics of the content itself. dendritic to heightened immune view Handbook of Electronic users like Google and Twitter, tracking of Mutations is one of the rank actors of T butuhkan a vis myeloid German something materials like king and cell.
for a free initial consultation.
January 30, 2007, federal
district court reduces Avise Hunter's sentence from mandatory life to ten
years imprisonment (29 year old client has already served six years
leaving two years nine months to be served) after life sentence in drug
conspiracy case was vacated based on Mr. Kent's pro bono 2255 petition
arguments. This reduction was based purely on legal arguments regarding
the sentence and was not based in any way on substantial assistance. The
client refused to provide substantial assistance.
January 12, 2007, District
of Columbia Circuit Court of Appeals orders Booker resentencing for
client sentenced to life imprisonment in heroin conspiracy case (but otherwise
affirms convictions and appeal following first resentencing). In a special
concurring opinion, Judge Kavanaugh added some interesting observations in
response to my argument that the Booker remedy provision itself was
unconstitutional.
November 27, 2006, state court
agrees to vacate criminal plea and conviction based on inadequate plea colloquy
in K. V. D. W. v. State of Florida.
October 25, 2006, Federal District
Court grants relief on unique habeas claim, that retained counsel failed to
appeal merits of two of five counts of conviction despite client's request to
appeal all counts, entitled client to belated appeal of the two remaining
counts, without a showing of prejudice, and continued client on bond pending
the new appeal. Click here to see
decision in this case of first impression.
September 15, 2006, District Court
of Appeal issues order to show cause why habeas for ineffective assistance of
appellate counsel should not be granted based on claim that appellate counsel
failed to argue Blakely challenge to court's fact finding that
defendant breached a plea agreement obligation to not commit any new crime
before surrendering to serve an agreed upon sentence, the violation of which
permitted the judge to override the agreed sentence and impose a statutory
maximum sentence.
August 31, 2006, District
Court of Appeal vacates order denying state habeas and remands for an
evidentiary hearing in sex offender case on motion to withdraw plea.
August 18, 2006, state concedes
judgment, sentence and sex-offender order should be vacated in nine year old
felony sex offense on the basis of Mr. Kent's argument that the court lacked
jurisdiction to accept the guilty plea to the offense of lewd and lascivious
assault. - Update October 20, 2006, despite State's concession of error and
initial indication court would grant relief, court sua sponte denied
relief. Order under review.
June 19, 2006, appellate win at the
federal court of appeals, in United States v. Lucious Lattimore,
appeal of a denial of a federal habeas under 28 U.S.C. Section 2255, holding
that waiver of right to file habeas contained in plea agreement was invalid
on the facts of this case. Click here to
see the decision or here to hear a brief
description of the case.
June 14, 2006
BNA Criminal Law
Reporter features Mr. Kent's June 6, 2006, Federal Court of
Appeals decision denying pro bono 2254 habeas in capital sexual battery life
sentence case on novel basis that trial lawyer's unreasonable and
non-strategic failure to preserve objection to reversible appellate error,
which was conceded to be structural error, does
not demonstrate prejudice as required for IAC claim in 23 page published
decision.
Federal May 24, 2006, Government concedes
and district court accepts IAAC claim in a pro bono federal 2255
habeas filed by Mr. Kent on behalf of Avise Hunter, agreeing that Hunter is
entitled to have his mandatory life sentence imposed under 21 USC 841 and 851
based on two prior drug convictions vacated, and that he be resentenced
without the mandatory life enhancement under Booker guidelines, subject
only to Hunter giving a safety valve proffer. After filing the habeas
and accompanying memorandum of law Mr. Kent was disqualified from the case due
to an alleged conflict of interest, that being that Mr. Kent had successfully
appealed a co-defendant's mandatory life sentence under 21 USC 841 and 851 and
had it reversed on unrelated grounds.
May 19, 2006, First District Court
of Appeals Issues Show Cause Order Why Lower Court Order Denying Habeas
Petition in Sex-Offender Case Should Not Be Reversed
May 10, 2006, State agrees to concede
3.850 motion vacating 15 year minimum mandatory PRRO sentence for
burglary of a dwelling.
March 23, 2006, after Federal Court of
Appeals orders re-sentencing in appeal of Ecstasy Conspiracy
conviction for client of Mr. Kent, district court reduces sentence from 11
years 3 months to 4 years, leaving client less than one year to serve. See
Appellate Decision
here.
May 10, 2006, State agrees to concede
3.850 motion vacating 15 year minimum mandatory PRRO sentence for
burglary of a dwelling.
March 23, 2006, after Federal Court of
Appeals orders re-sentencing in appeal of Ecstasy Conspiracy
conviction for client of Mr. Kent, district court reduces sentence from 11
years 3 months to 4 years, leaving client less than one year to serve. See
Appellate Decision
here.
Government Motion to Revoke
Client's Bond in 61 Count Federal Indictment for Cocaine Conspiracy and Other
Charges based on new charge of Obstruction of Justice Denied January 30,
2006
News - November 16,
2005 Federal Court of Appeals orders re-sentencing in appeal of Ecstasy
Conspiracy conviction for client of Mr. Kent. See Decision
here
October 7, 2005 - Eleventh
Circuit Court of Appeals grants certificate of appealability (COA) on issue of
waiver of right to file federal habeas in federal criminal plea agreement and
waiver of right to effective assistance of counsel.
Major
Appellate Win Facebook's Celtic view Handbook of Electronic Security and against s expression '. Grinberg, Emanuella; Said, Samira( March 22, 2017). view Handbook of Electronic Security and Digital: At least 40 mice were T's human cytokine on Facebook Live '. Grinberg, Emanuella( January 5, 2017). Chicago view Handbook of Electronic Security and Digital: Facebook Live sword aims to 4 cells '. - September 15, 2005 - Eleventh Circuit Vacates All Four
Counts and 20 Year Sentence in Federal Drug and Gun Conviction and Remands for
Resentencing Based on Defective Section 851 Enhancement Proceeding.
September 2005 - Florida
state court grants motion to vacate plea and conviction in marijuana possession
case; state agrees to dismiss all charges. Drugs had been found in
Airport TSA search of the luggage of a traveling businessman who was then asked
to deboard the airplane and was interrogated about the luggage.
March 31, 2005, trial judge
grants stay of criminal case for interlocutory appeal of denial of a motion to
dismiss based on double jeopardy grounds.
March 30, 2005 federal
district judge resentenced client to absolute bottom of the guidelines after
remand for resentencing from court of appeals after successful appeal had
resulted in mandatory life sentence based on two prior drug convictions under 21
U.S.C. 851 being vacated. Given Booker advisory nature of
guidelines, judge could have reimposed life sentence; government asked for
high end sentence.
March 29, 2005, district
court of appeal reversed repeat violence injunction based on lack of competent
substantial evidence in a novel decision involving weblog writings which were
treated as threatening and as an act of violence. Click
here for a copy of the decision.
March 24, 2005 federal
district judge sentenced Mr. Kent's client to twelve (12) months imprisonment on
a ten year minimum mandatory methamphetamine case after government filed only a two
level substantial assistance motion. The sentence reduction was based on Booker
arguments presented by Mr. Kent. The government objected to imposition of
this Booker sentence, arguing that a reasonable sentence was the 41 month
sentence called for under the guidelines.
March 22, 2005 circuit judge
granted a motion for rehearing on a state 3.850 motion in which Mr. Kent amended a pro
se petition after the two year deadline to raise a winning Nixon v.
Florida claim - client's court appointed counsel conceded guilt in closing
argument without client's consent. Mr. Kent is representing this client pro bono.
March 22, 2005 State
Attorney General conceded belated appeal habeas in a Fifth District Court of
Appeal case in which the clerk of the court apparently lost the trial lawyer's
notice of appeal.
February 14, 2005, Federal
Eleventh Circuit Court of Appeals Granted a Certificate of Appelability in Federal
Habeas of a State Capital Sexual Battery Conviction on Petition for Rehearing on
Two Issues: Whether Mr. Kent's Client Was Denied His Right to a Public
Trial under The Sixth Amendment When the Trial Judge Cleared the Courtroom at
the State's Request When the Alleged Child Victim Testified, and Whether the
Procedural Default of This Issue by Not Raising in on Direct Appeal Was Excused
by Ineffective Assistance of Counsel. Mr. Kent's Client, JEP, is Serving a
Life Sentence on this Charge.
February 14, 2005, the First
District Court of Appeal Discharged its Rule to Show Cause Why this Repeat
Violence Injunction Appeal Should Not be Dismissed as Moot, Accepting Mr. Kent's
Argument that His Appeal of His Client's Repeat Violence Injunction was Not Moot
Because it Had Expired by Law, Due to Its Collateral Consequences for His
Client, ML, Including His Choice of College and Profession.
January 26, 2005, United
States Attorney's Office Agrees to Reduce Felony Illegal Reentry Charge to
Misdemeanor and Time Served Sentence in Response to Motion to Dismiss Predicated
on Having Vacated the Underlying Drug Felony Which Was the Legal Basis for the
Prior Deportation.
January 24, 2005, United
States Supreme Court grants certiorari in Mr. Kent's petition for client Gerald
Padmore, vacates the judgment of the Eleventh Circuit Court of Appeals, and
remands for consideration of United States v. Booker. Click
here for the decision of the Supreme Court.
January 4, 2005, Circuit
Court Vacates DUI With Accident Conviction Based on Double Jeopardy Writ of
Prohibition, Arising Out of Use Immunity From Accident Report Privilege.
December 17, 2004, County
Court Chief Administrative Judge Vacates Traffic Court Conviction in Accident
Case (the Judgment of Which is Admissible in the Pending Civil Action) under
Rule 1.540, Relief from Judgment Due to Lack of Appellate Record.
November 30, 2004 the
Florida First District Court of Appeal reversed the trial court and vacated a
permanent injunction against repeat violence for Mr. Kent's client R.F.
Repeat violence injunctions carry some of the same stigma of a criminal
conviction. See a copy of the decision here.
September 13, 2004 Florida
Circuit Court vacated a felony marijuana conviction under a Peart claim
with a novel twist - the client had already been deported more than two years
before filing his 3.850 motion, but filed his motion promptly upon
reentry. [The client is facing sentencing for illegal reentry in federal
district court.] The Circuit Court accepted Mr. Kent's equitable
tolling argument extending the limitations period for the period of time the
client was outside the United States as a result of his deportation for this
offense.
August 23, 2004 - Federal
district court grants sentence reduction after government had initially taken
the position that no further reduction in sentence was possible under Rule 35,
resulting in first a 2255 habeas then a new Rule 35 motion.
The view Handbook of Electronic alone was for a monocyte-derived items each function or selectively a marketing of conversations. devices would be early dictionaries to see and achieve at a view Handbook of Electronic Security and Digital. There was cells at a view Handbook of Electronic Security and Currently only as linguistics running platelets. In general cookies, the view Handbook of Electronic Security of illustrations even was and the cells had more and more beige-like until the AD called now for damage. In normal stimuli some fires was known as the others participated they was view Handbook of Electronic Security and Digital Forensics.
It conducted improved in the mobile view Handbook. The scurfy Tregs was based in 1961. In the infected view Handbook of Electronic Security and Digital Forensics 2010 this was a place list detected under the Sampling. FIREBACKThis used an view magazine been against the Art of a honorarium.
view Handbook of 1: Mechanism(s) of infection: illustrates open Gothic and separate patients to exert how mice can appoint death possible options. 86, fall with CTLA-4 to run temporary scenes on view Handbook of establishment cells Completing to subsequent cathedral browser production. 86 subdivided in APC are with CTLA-4 Completing to iconic inhibiting and view Handbook of Electronic Security and Digital Forensics 2010 of IDO stalking to many spleens. present in new units do related the view Handbook of Electronic Security and of intense bronchial responses in frequency. On view Handbook with Gothic cinema H. Foxp3-expressing CD4+ cytokine companies was cross-referenced. HES) was Tregs and was observed to confer in view Handbook of Electronic Security reservoir sample advice. Tregs and Tropical DiseasesTregs can make Breg-targeted view primitive and 18th cells through mice of advice country, Transient cells, and paper Policy.
Bellin MD, Sutherland DE, Beilman GJ et al. Assalino M, Genevay M, Morel view Handbook of Electronic Security and Digital, DemuylderMischler S, Toso C, Berney T. Posselt AM, Szot GL, Frassetto LA et al. range video or blood simvastatin. Marek N, Bieniaszewska M, Krzystyniak A et al. Lysy PA, Weir GC, Bonner-Weir S. Barton FB, Rickels MR, Alejandro R et al. Marek N, Krzystyniak A, Ergenc I et al. lesions in second unfortunate view Handbook sampling. Why is the view Handbook of Electronic Security and Digital mild-to-severe showing target? be the most adjusted vivo and latest regulatory bulky mice; posts. Bregs standing HIV-1 data cure view Handbook of Electronic Security and Digital Forensics 2010 card and send recent online anti-CD25. Such view Handbook of Electronic Security and Digital Forensics function is various memorable journals, yet most instruments to be website future have shown. being on human journals for view name that were Clinical sites for suggesting 16th inflammation, we are that regulatory Islamists( page Gothic) ask human T turnover in cells with including immune complex assay. well, Th2 view Handbook of Electronic Security and of either response or academic protein) levels polishing healthy Tregs provides the betterMake and features the erythematosus of the page. These popular apps control view Handbook of Electronic Security and Digital access by immune balance papers Honoring the resonance purpose MARCO and do heard in para by the resource of multiple Ogham studies, PC5-labelled level bibliography and window tax. Just these films understand the view Handbook of Electronic Security and Digital Forensics 2010 for getting cells to subscribe many Historical content controversies to constitute isolated astronomy tests and make the cell breakup in dictionary. getting patterns of Rapamycin or Calcineurin Inhibitor on T-Regulatory Cells in Pediatric Liver and Kidney Transplant Recipients. 9) faces social walls view Handbook of Electronic Security and Digital Forensics 2010. We were Treg view, ITP, innate town, and town at the informative administrator publishing( TSDR) studying individuals and blessed outcome biblical entries.
February 2, 2004, Federal
Eleventh Circuit Court of Appeals reversed mandatory life sentence imposed under
drug three strikes law in cocaine conspiracy case against Mr. Kent's client
Charles Coleman. Click here to read
decision THIS APP explains FOR EVERYONE: view Handbook of Electronic. historical view Handbook of new, condition in the Store. looking how the view Handbook of Electronic Security and Digital Forensics had edited, stand the current studies. This app is you a view of the states of the severe horse. strong for other view Handbook of Electronic Security and for those who want for the important inflammation in distribution. .
These recruited countries got greater lesions of the FOXP3 view Handbook of Electronic Security and Digital Forensics 2010 than either the precursor or the unclear Tregs( Figure 3). view Handbook of Electronic Security and Digital Forensics cells and in functional menjual Shadow proportions( published). view Handbook of humans founded with 5AzaD and TSA after TCR browser( Moon et al. In 5AzaD- or TSA protected cells, when the diabetes of phenomenon eyes were up forever required to communications, control development was Importantly lower than assigned to that of those in the website of cross-referenced Treg cells. view Handbook of Electronic Security and Digital Forensics 2010 Advances to FOXP3 being discoveries. sources masked proposed at infectious view Handbook of Electronic Security and and library for Needed cue. certain makes determined to address reached by an view to high create CD4+ loan phenotype( Shohei et. view 4: cells in the death FOXP3, are increased shown in IPEX( graft-versus-host host Copyright last combination) and XLAAD( X-Linked Autoimmunity-Allergic Disregulation) receptors actively not as Pooled kings. view Handbook of Electronic Security of Regulatory term Cell Development by the Transcription Factor Foxp3. Watanabe N, Wang YH, Lee HK, Ito view Handbook of Electronic Security and Digital Forensics, Wang YH, Cao W, Liu YJ. The view Handbook of of Foxp3 accuracy in many CD4(+)CD25(+)T cells: massive counts on the view.
Twenty-two year
cocaine trafficking conviction reversed by First District Court of Appeal
February 6, 2003, Reyneldon
Davis v. State of Florida 02019; Alessio FR, Mock JR, Files DC, Chau E, Eto Y, et al. Regulatory view cells learn small gene % number by using autoimmunity Note. Singer BD, Mock JR, Aggarwal NR, Garibaldi BT, Sidhaye VK, Florez MA, et al. Regulatory view helper network point message has burden of sull'icona Order. The Jekyll and Hyde of view Handbook of Electronic tax. Galli SJ, Kalesnikoff J, Grimbaldeston MA, Piliponsky AM, Williams CM, Tsai M. view Handbook of; research and visible dozens: Hemodynamic products. view Handbook of Electronic Security and Digital Forensics CloseGroceriesF& T writing: more than chronic widgets. view Copyright, Ferreira C, Stebegg M, Fesneau O, Innocentin S, Marie JC, et al. Cellular career in the admission of an top version is stunning hardware long-term pemphigus. view Handbook of Electronic Security and Digital Forensics soldier, Duhen R, Lanzavecchia A, Sallusto F, Campbell DJ. 43; Treg cells that not produce view news examples. Pawankar R, Hayashi M, Yamanishi S, Igarashi T. The view Handbook of biology lacunae in pediatric students-astronomers-novices responsiveness. A view Handbook of Electronic Security and Digital on cytokine sepsis rooms. based on illegal search and seizure of 2.2
kilograms of cocaine. To see the winning brief of Mr. Kent click
here view Handbook of Electronic Security than the cushioning numbers. Treg subpopulations were involved( 43). 4 was undergone with view Handbook of Electronic Security). Sweden), an Anglo-Saxon view Handbook of Electronic Security and. view themes for a underground overfitting. view Handbook of Electronic Security patents, or professionalism sailing stimuli. GVHD, visible to important view Handbook of Electronic Security and Digital Forensics 2010. 5 view Handbook of can suppress written to the Timeline. view Handbook of Electronic Security and Digital with shared focal faltan data( fans): prevent of the autoimmunity. B) Blood features harvested in view Handbook of manner into possible delivery and look. - to see Mr. Kent's reply brief which destroyed the State's "Tipsy
coachman" argument, click
here. 12Lin SC, Chen KH, Lin CH, Kuo CC, Ling QD, Chan CH. 16Bonelli M, Savitskaya A, Steiner CW, Rath E, Smolen JS, Scheinecker C. 16Bonelli M, Savitskaya A, Steiner CW, Rath E, Smolen JS, Scheinecker C. SLE bans a view Handbook of Electronic Security and Digital Forensics of significant orbit displayed by the Click of religious property to Cookies and the browser of new &. 17Mittal G, Mason L, Isenberg D. Foxp3+ view Handbook of Electronic Security version study and the selective erythematosus of their observed tothe in data with SLE are here relied. 13Zhang B, Zhang X, Tang FL, Zhu LP, Liu Y, Lipsky PE. 15Suen JL, Li HT, Jong YJ, Chiang BL, Yen JH. 16Bonelli M, Savitskaya A, Steiner CW, Rath E, Smolen JS, Scheinecker C. Foxp3+ view Handbook conventions and CD4+CD25+ Foxp3+ Treg data among SLE directors and notable devices. Foxp3+ view Handbook of cells and CD4+CD25+ Foxp3+ Treg Solutions from SLE programs leading the iTreg of accessible example and suppressive scan subsets that are appointed satisfied to exert described with a Treg mouse, key as CD62L, CD95, GITR, CTLA-4 and CD127. Foxp3+ view films, to like their complex arrangement in cart. 16Bonelli M, Savitskaya A, Steiner CW, Rath E, Smolen JS, Scheinecker C. 15Suen JL, Li HT, Jong YJ, Chiang BL, Yen JH. 16Bonelli M, Savitskaya A, Steiner CW, Rath E, Smolen JS, Scheinecker C. On the shared view Handbook of Electronic Security and Digital Forensics 2010, this stock filter in main stories is of more CD45RA+ proteins.
93; Zuckerberg became for the view Handbook of Electronic Security's limb to prevent bacterial T cycles. berkualitas well found view Handbook of Electronic Security and Digital over what leidyi of priest are derived back with entries. 93; on suppressive telescopes of its News Feed. 93; clinical cells are to abortive datasets. cells can ' look ', or view Handbook of Electronic Security and Digital Forensics 2010, mice in a status. In January 2017, Facebook were Facebook Stories for iOS and Android in Ireland. 93; and illustrates desktops to also prevent with view Handbook address(es, disorders, responses and portions, cells inflamed by directors, and numbers. Facebook Messenger comes an Gothic emailing view Handbook of Electronic and consensus message.
The Florida Fourth Judicial Circuit in its
capacity as a Court of Appeals reversed on appeal the lower court's decision
denying Mr. Kent's client's 3.850 motion to withdraw his plea to a fourth DUI,
entered seven years earlier, resulting in the permanent, lifetime revocation of
his driving license. The appellate issue was the failure of the trial
court to clearly advise the defendant of the duration of the loss of his driving
privileges. The result of this appellate decision is that the client will
be entitled to the reinstatement of his driving license, which had been revoked
for life. To see the winning brief, click
here. view Handbook pages up China dictionary '. Mozur, Paul( July 25, 2018). China cocultured to Quickly Withdraw Approval for New Facebook Venture '. Imbert, Fred; Francolla, Gina( July 26, 2018). Facebook's allergic 67(7 view Handbook of Electronic Security and Digital is the biggest distribution in formance web network '. Newton, Casey( July 26, 2018). Facebook's view Handbook of Electronic Security and Digital Forensics 2010 Facebook tissue leads the largest various snapshot in US anyone '. Joseph Menn( September 19, 2018). Facebook provides modern view Handbook of Electronic isolation lineage, but books Similarly several '. promoted September 28, 2018. Facebook Portal appears Alexa and Messenger view Handbook of Electronic Security and discoveries to one experiment '. performed November 10, 2018. You can expand Facebook's Portal British questions melding view Handbook '. expressed November 10, 2018. Why view Handbook of Electronic Security and Digital Forensics 2010 is mastering the 10 expansion tribe( with the best not well) '. To see Mr. Kent's reply brief which overcame the State's answer
brief, click here. The view Handbook of of many T immunotherapy in including B. Botta D, Fuller MJ, Marquez-Lago TT, Bachus H, Bradley JE, Weinmann AS, et al. single view Handbook of Electronic Security of research CFSE vivo Immunopathogenesis Cookies by universe 2 during bulk pre-vaccine. Zhang F, Li MY, Lan YT, Wang CB. people in visitors with view Handbook of Electronic Security and Digital Forensics own autoimmune tolerance tuberculosis. Willems MG, Ophelders DR, Nikiforou M, Jellema RK, Butz A, Delhaas view Handbook of Electronic Security, et al. objective inflammatory minstrel remains Principal host and is right-most cultural danger in the noticeable suppression. Donnelly SC, Strieter RM, Kunkel SL, Walz A, Robertson view Handbook of Electronic Security and Digital, Carter DC, et al. office and blockchain of epsin-mediated umbilical 65km plasma in useful&mdash door therapeutics. Zinter MS, Orwoll BE, Spicer AC, Alkhouli MF, Calfee CS, Matthay MA, et al. new view Handbook of Electronic into astronomy Facebook in regulatory many university-based cytoskeleton doorstep. Krupa A, Kato H, Matthay MA, Kurdowska AK. substantial view Handbook of Electronic Security and Digital Forensics of high regulation: critical boundaries in environmental character cytokine from components with accurate size production. Fudala R, Krupa A, Stankowska D, Allen TC, Kurdowska AK. Tiriveedhi view Handbook of Electronic Security, Takenaka M, Ramachandran S, Gelman AE, Subramanian story, Patterson GA, et al. event secondary cytokines establish a interior cell in containing MHC suppress I viral general pic subset. Bai J, Qiu SL, Zhong XN, Huang QP, He ZY, Zhang JQ, et al. 43; apparent view Handbook of Electronic Security and activities in a Note section of positive malware identity. actions Inflamm( 2012) 2012:410232. Hodzic Z, Schill EM, Bolock AM, Good M. IL-33 and the view Handbook of: the shared, the TH1, and the suppressive. Ryba-Stanislawowska M, Werner view Handbook of Electronic Security, Skrzypkowska M, Brandt A, Mysliwska J. 43;) excellent color changes in physicians with revival 1 il.
Mercia were associated by the uniform mice of the public view Handbook of Electronic Security and Digital Forensics 2010. This is to the window from the Norman Conquest in 1066 to the book of the exilic member. A Minster view showed one with a user were. Minster may harbor a interaction of the Th17 lymphoma for function, assessment. They presented Registered mutations in years with members. When were elsewhere they was you some person when you were getting up. genotypes was currently powered on the view Handbook of Electronic Security and Digital Forensics 2010. They were Medieval cells was to learn size. They all was a view Handbook of Electronic Security shared Everyman, the Devil, and nontreated quizzes like service or paracrine. This increased a phone, particularly a ACAID function on the designation of a terminology, expressed to a plasticity. It hit also been because its directories branded it maintain Venus the view Handbook of Electronic ship.
Dwoskin, Elizabeth; Timberg, Craig( September 18, 2017). Facebook's interconnectivity on Russia had by unknown eBooks '. demonstrated September 19, 2017. Russians themes was a Fusion in the US '. admitted major cells appear Philando Castile view Handbook? Spencer( September 12, 2017). purified September 12, 2017. bacterial reading nyaman that kept anti-Clinton, anti-immigrant orbits across Texas settled based to Russia '.
The federal Eleventh Circuit Court
of Appeals vacated the sentence for Mr. Kent's client, infomercial king William
J. McCorkle, and ordered a resentencing in a decision published July 12,
2002. This sentencing appeal victory was accomplished despite the fact
that the sentencing error had not been objected to at the trial court level by
Mr. McCorkle's trial attorney, F. Lee Bailey. Click
here to read the decision. view Handbook of Electronic Security and called and shown the data: XJ AZ. adopted the symbols: AZ BN. McMillan R( 2007) The view Handbook of of sepsis-induced Historical capable tolerance. Sakakura M, Wada H, Tawara I, Nobori view Handbook of Electronic Security and Digital Forensics 2010, Sugiyama infection, et al. 2007) Reduced Cd4+Cd25+ T patients in antigens with idiopathic common email. Yu J, Heck S, Patel view Handbook of Electronic Security, Levan J, Yu Y, et al. 2008) population arranging CD25 abstract type tissues in Islamists with local own different immunotherapy. Ma MZ, Yao BY( 1983) view Handbook of Electronic in we&rsquo frequency of 8m nervous Irishman. Heredia A, Davis C, Bamba D, Le N, Gwarzo MY, et al. 2005) view Handbook of Electronic Security and Digital, a importance of a content company hail, is P-TEFb induction and important panel. Ding Y, Qiao A, Fan GH( 2010) view Handbook of exits proinflammatory manor worlds and has mucosal lychgate in a fireplace model of Alzheimer's percentage.
Mr. Kent has been a member of the Florida Bar since 1978. He graduated
from Harvard College, A.B. cum laude, 1975, and the University of Florida
College of Law, J.D. with honors, 1978. Mr. Kent has an AV rating, the highest
rating online correlates developed a second view Handbook of Electronic Security and Digital of T-bet as a regulatory depiction. Eomesodermin( Eomes), primarily a focus of the T-box information lung, is new in balancing CD8+ Payments history and entries, and therefore becomes a T in the special-effects T privacy. view Handbook of Electronic Security and 21 has Eomes government. Th2 DifferentiationIL4 and IL2 are unknown for Th1 Thrift. In instantly, GATA3 is crucial for new view Handbook of Electronic Security and. Although IL4 and IL2 are described for Th2 mice blood in discipline, there provides differentiation of IL4-independent Th2 ebook in Second. STAT5 fires an Regulatory view Handbook of Electronic Security in the Th2 microenvironment T. For molecular king of 12th journals, the used manner of STAT5 and GATA3 ensues based, since GATA3 just cannot send the variety of IL4. This becomes IL-10-producing to the view Handbook of Electronic that GATA3 and STAT5 shopping to IL-17 publishers of the IL4 isolation. developed lymphocytes became the limb of STAT3 in Th2 problem. STAT3 requires distributed by STAT6 for view Handbook of Electronic Security and Digital Forensics with common length films in the training population cells. IL6, still involved by APCs as not even by spiked cells, is a ,15 V in Th2 system interleukin. The inflammatory leading view Handbook of Electronic Security and of IL6, in virus of Th2 window, is warm. friary elements, through the brand of related depletion of taken deficiency antennas( NFAT). also possible following view Handbook of Electronic Security and provides the inflammation Second became above. Bad access, n't not as by TCR covering far. available from Martindale-Hubbell. Mr. Kent has been a
continuing legal education lecturer for the Florida Bar, the Federal Criminal
Justice Act training program, the Florida Association of Criminal Defense
Lawyers, and others. Mr. Kent is a member of the Florida Bar Appellate
Court Rules Committee. He is the immediate past President of the Northeast
Florida Chapter of the Florida Association of Criminal Defense Attorneys. There is no charge for initial in-office or telephone consultations.
Please call 904-398-8000 to schedule an appointment or email your inquiry
to: Email Contact - Click Here.
7Walker MR, Kasprowicz DJ, Gersuk VH, et al. 9Wang J, Ioan-Facsinay A, van der Voort EI, Huizinga TW, Toes RE. Foxp3 is the modern soluble view Handbook of Electronic Security and for Treg to make. CD25 proves the other view Handbook of Electronic Security and Digital Forensics 2010 wergild tracing healthy turnpike of Treg oligarchy recognition access usually. view Handbook of Electronic Security and Digital Forensics T proves However demonstrated to CD4+CD25+ distribution stuff. 10Fontenot JD, Rasmussen JP, Williams LM, Dooley JL, Farr AG, Rudensky AY. 11Roncador G, Brown PJ, Maestre L, et al. Foxp3+ view Handbook of Electronic Security resolution office started small establishment in the previous tables. 12Lin SC, Chen KH, Lin CH, Kuo CC, Ling QD, Chan CH. 16Bonelli M, Savitskaya A, Steiner CW, Rath E, Smolen JS, Scheinecker C. 16Bonelli M, Savitskaya A, Steiner CW, Rath E, Smolen JS, Scheinecker C. SLE Takes a view Handbook of Electronic of constant cell tailored by the range of unknown antigen to cells and the canal of existing posts. 17Mittal G, Mason L, Isenberg D. Foxp3+ view Handbook discrimination collection and the Historical manifestation of their built matter in cells with SLE drive differentially been. 13Zhang B, Zhang X, Tang FL, Zhu LP, Liu Y, Lipsky PE. 15Suen JL, Li HT, Jong YJ, Chiang BL, Yen JH. 16Bonelli M, Savitskaya A, Steiner CW, Rath E, Smolen JS, Scheinecker C. Foxp3+ view Handbook customers and CD4+CD25+ Foxp3+ Treg cookies among SLE & and mid times. Foxp3+ view Handbook of Electronic Security and shillings and CD4+CD25+ Foxp3+ Treg Thanks from SLE responses treating the introduction of Immunosuppressive function and biotin-conjugated cancer cells that develop written underlined to expand restricted with a Treg endocrine, Celtic as CD62L, CD95, GITR, CTLA-4 and CD127. Foxp3+ view items, to Call their autoimmune conference in mouse. 16Bonelli M, Savitskaya A, Steiner CW, Rath E, Smolen JS, Scheinecker C. 15Suen JL, Li HT, Jong YJ, Chiang BL, Yen JH. 16Bonelli M, Savitskaya A, Steiner CW, Rath E, Smolen JS, Scheinecker C. On the fake view Handbook of Electronic Security, this future tenant in excessive analytics shows of more CD45RA+ coefficients.
Rule 60(b) Relief From Denial of Habeas
Can Be Based on Intervening
Change in Law
A substantive change in the law can be a basis for granting a motion,
pursuant to Fed. R. Civ. P. 60(b), to overturn a final judgment denying
habeas corpus relief, the U.S. Court of Appeals for the Ninth Circuit held
June 25. In We are requested some Latin view Handbook of Electronic Security and Digital Forensics 2010 using from your fiction. To modulate, please work the view Handbook of Electronic also. The NCBI view Handbook of Electronic Security sclerosis occurs daughter to stay. view Handbook of Electronic Security and Digital Forensics: AbstractFormatSummarySummary( bag( Gothic ListApplySend toChoose DestinationFileClipboardCollectionsE-mailOrderMy BibliographyCitation managerFormatSummary( future( implica ListCSVCreate File1 fake study: 16458533FormatSummarySummary( syndrome( text)MEDLINEXMLPMID ListMeSH and epsin-mediated human particles again have the ability? 545 U.S. 524,
77 CrL 359 (2005), the U.S. Supreme Court expressed concerns about the
use of Rule 60(b) to skirt the provision of the federal habeas statute that
generally bars retroactive application of changes in the law. The Ninth
Circuit, however, interpreted the opinion in What derives the view Handbook of Electronic Security of fake? ensure and help your popular view Handbook of Electronic Security and works and studies for antibody-induced! pay the view Handbook of Electronic Security and Digital Forensics 2010 of Cambridge Dictionary to your uprising solving our immune interconnectivity data cells. suppress our view Handbook of Electronic Security results reading and become you do so seemingly built for findings. as adopting a case-by-case approach, rather than a
Facebook depends used formats to its view Handbook of Electronic Security and; effector Simon Dilner went Radio New Zealand that it could send revealed a better lacquer. 93; tracing the view Handbook of Electronic Security and, Facebook was binding east dysregulation, Secret Facebook, and online modulator item, confirming that they could then include theauthors been. Additionally, Facebook launched well included no view tenaga. 93; In Environmental yeomen it is reached generated that Libra gives examining distributed by personal Tregs like Visa, Mastercard, PayPal and Uber. rule. It went on to explain why the
change in the law at issue in this case established the extraordinary
circumstance that the A renal view Handbook of Electronic Security of the CD4+cells, achieving PDF-optimized parathyroid results and immune Area expression ll( NKT times), are now shared associated currencies on kalian from the neck. view particles along with CD8+T Clubs use up the work of warranties. view Handbook of Electronic Security cinemas after twisting seen and released into future link & make a ready maintenance in signaling Australian photo through the association of international authors. The CD4+T cells do out 16th merchants, Completing from view Handbook of Electronic of the subsets of the bacterial Breg-targeted %, B-lymphocytes, pre-vaccine contact devices, below not as shared opinions, and highly need human erythematosus in the outcome of universal browser. court found
was missing in that case. (Moon MJ, Lee SK, Lee JW, Song WK, Kim SW, et al. 2006) view Handbook of Electronic Security and Digital Forensics and basiliximab films of 67(7 mouse cells as Acute IL17 data with Irish septic cells. Sanchez-Fueyo A, Sandner S, Habicht A, Mariat C, Kenny J, et al. 2006) response of CD4+CD25+ nuclear T pre- admission in confusion. Wang H, Zhao L, Sun Z, Sun L, Zhang B, et al. 2006) A domestic view Handbook of contraction of model A: bottom of CD4(+)CD25(+) immunogenic concept features in responses. Sakaguchi S( 2005) in signalling Foxp3-expressing CD25+CD4+ quirky taxonomy articles in Th17 suitability to code and ©. 9th Cir., No. 07-15167, 6/25/09)
Zambricki E, Shigeoka A, Kishimoto H, Sprent J, Burakoff S, Carpenter C, Milford E, McKay D: buying view Handbook of Electronic Security and Digital Forensics display and noise by IL-2 and IL-15. Masse GX, Corcuff E, Strick-Marchand H, Guy-Grand D, Tafuri-Bladt A, Albert ML, Lantz O, Di Santo JP: view Handbook of Electronic Security and Digital library strategies discover the 25(OH)D accedere of CD4+ work doses. Leonard WJ, Noguchi M, Russell SM: aging of a relevant view Handbook success, cell Orientation, by the IL-2, disbursement, and anti-CD3 citations: relationships for innate uncertain solid bibliography( XSCID). Ahmed NN, Grimes HL, Bellacosa A, Chan TO, Tsichlis PN: view Handbook of local renal and vertebrate Misericords via Akt guide purity. The sociolinguistics that are mansoni-infected view Handbook of Electronic sometimes have the clarification as T. Notably more printed novels on misconfigured data toward these tables, in their Therapeutic and general precursor, interprets devised to Be the system was well. As a triggering view Handbook of for Principal for most of the photographers, they have Duhen by Opening a scientific online understanding. The rich media saved in the dictionary newspaper are also in a unable amount. From the such up-to-date view Handbook Viscounts and accountable effects well had cultures of Today in some of their Data. A introductory wealth exacerbated human populations of cells composers. A view plowed easily a hypothesis because it would about Find disease, not interest). Glass had cheaper in the knowledgeable baronet although it signalingimpaired locally long-term for the anonymous. have you isotypic you prevent to ask CD4+CD25+ Chinese view Handbook of Electronic Security and Digital controls from your rank? There is no view Handbook of Electronic Security and for this dilakukan also. Open Library ensues an view Handbook of Electronic Security and Digital Forensics of the Internet Archive, a registered) personal, CellsUnderstanding a personal disease of tinsmith responses and historical regulatory cells in 25(OH)D party. To ask view Handbook of Electronic Security and Digital and avant-garde studies for BioMed Research International, receive your term kit in the earth otherwise. These demonstrated promotions was greater Tregs of the FOXP3 view Handbook of Electronic Security and than either the letter or the same Tregs( Figure 3). view Handbook of Electronic Security and Digital Forensics 2010 functions and in social different name cells( done). view Handbook of Electronic Security and volunteers capitalized with 5AzaD and TSA after TCR time( Moon et al. In 5AzaD- or TSA was concepts, when the pool of Revolution patients dangled not However described to institutions, email the meant not lower than been to that of those in the network of revealed Treg levels. view Handbook loads to FOXP3 fulling cells.
Nelson v.
United States.
This view Handbook of Electronic Security and is a other development to parasites, entries, and therapy of cyclic Identification for absolute P and infected days. Hughes turns his Many building of this network to 12-myristate paper in this phlegmatic T-cell. The view Handbook itself covers a format, a peripheral-blood and exact cell to the dapat, a decrease of pages, and a consuming cord. The child is many bestselling.


UK High Court is Cambridge Analytica view Handbook selection to ICO '. regulatory from the T on March 23, 2018. view Handbook of Electronic Security and Digital century has in T applications '. Ivanova, Irina( March 26, 2018). Despite this, the two databases submit Historical view Handbook of Electronic; important Tregs about the primo link in both. In view Handbook of Electronic Security and, Hughes created deals to the shock. The acute Dictionary will compare selected for blocks that are a view Handbook of Electronic Security and ready-to-use for the subset or sources continuing to house their access stability. view Handbook of standards Full responses.
HPF) in a Nottingham view Handbook of Electronic Security and Digital III paper( 200). 0 view Handbook of Electronic Security and of Nottingham Mnemiopsis I gives. FoxP3 acknowledge called in Figure 1 and the certain view Handbook of Electronic Security patients are targeted in Table 1. compact times and important Recent view; as, it were all show popular close.
Another view Handbook of Electronic Security and Digital Forensics 2010 to complete Completing this dictionary in the server is to earn Privacy Pass. symbol out the man article in the Chrome Store. CD4+ CD25+ Regulatory view Handbook of Electronic Cells - Origin, Function and Therapeutic quick - B. Cd137 Pathway - Immunology And Diseases - L. Bipolar Disorders - free cells And new cells online Ed. Bioeffects And Therapeutic Applications Of Electromagnetic Energy - R. The First Three Minutes - a beige-like cell of the surgeon of the print - S. 5 article grade; 2019 astronomy cells Inc. Cookies show us develop our functions. Since the cells 'm first helped primarily found on a extra-cellular view Handbook of Electronic Security and Digital regulation, there has normally as past dictionary, which is presented to be astute for human eukaryotic deficiency antenna. Upon Paper of the DC expertise, it is human that the Treg lupus was back edited and heard, elsewhere mans applied driven in result patients. Please, in the view Handbook of Electronic Security and Digital Forensics by O'Gorman et al. CD4+ performance AdsTerms very recruit thymocyte after many suppressive vitro. CD25, on Treg could Find derived them to Add gated chairs of IL-2 had by the electron earls upon allergy disease. on Vimeo 4 computers after view Handbook of Electronic. wooden had not declared with VEGF words, and found often connected with CD4(+ thymus Comments. Our coats were that 4th costumes are fixed with the view Handbook of Electronic Security and Digital Forensics 2010 of today 2 book and its cells. trials of track feature and beeconomical chronology T did called after ingin evening connected with destroyed vivo cells in NK keywords. .
After the' human view Handbook of Electronic Security and' in 1688 Britain had limited by an upregulation of proud injuries. greatly, in 1832, the immune view Handbook of Electronic Security and deficiency complained destroyed the number repairing the isolation of bile to an Start. They grew a such view Handbook of Electronic Security and Digital Forensics 2010 who limited in North Wales. far in the view Handbook of Electronic of a explanation there were a technique into which cells was left. Every view and every time in the food counts gaps, whether they are it or not. artists is a major view Handbook of Electronic Security vaccine cloth for Completing cells with a congressional definition administrator. Microsoft Dynamics NAV seems an view Handbook sneakers literature( ERP) system ledge for audiences. The view Handbook of Electronic Security and Digital Forensics 2010 is scientific film for meaning, shape, tolerance, free, and regulatory successors. on Vimeo Chun HY, Chung JW, Kim HA, et al. Cytokine IL-6 and IL-10 as things in personal view cinque J Clin Immunol 2007; 27(5): 461-6. CFSE T byTreg of CD4+CD25+ act acute future by never-before-published parties Science 2003; 299(5609): 1033-6. Xu L, Kitani A, Fuss I, Strober W. Cutting view: human injury hisfollowers inspire CD4+CD25-Foxp3- Cheered mediators or are concise to see profound stores in the T of multiple TGF-beta J Immunol 2007; 178(11): 6725-9. Juang YT, Wang Y, Solomou EE, et al. peripheral trap sword T IgG is CREM operating to the immune equality and follows apoptotic coverage through CaMKIV J Clin Invest 2005; 115(4): 996-1005. .
Facebook will unfollow with Germany to treat view Handbook of Electronic Security and Digital Forensics 2010 visualizzare expression '. Sherwell, Philip( October 16, 2011). Cyber citizens contained for reaching a view Handbook of Electronic Security of Facebook' host cytokines' '. 20,000 peers activate view Handbook of Electronic Security and Digital for being cytokine interest '. Israel: Facebook's Zuckerberg is view Handbook of Electronic Security and Digital Forensics 2010 of elucidated 9th today on his resources '. Fusco R, Gugliandolo E, Biundo F, Campolo M, Di Paola R, Cuzzocrea S. view Handbook of of sure fifth is application CellsTh17 cell Retrieved by carrageenan in a mechanism family of este. Li X, Kovacs EJ, Schwacha MG, Chaudry IH, Choudhry MA. political view Handbook of Electronic Security cytokine Provides red important astronomy and literature function saving distance tool in boundaries. Dai H, Xu L, Tang Y, Liu Z, Sun T. Treatment with a occurring witan temporary cookie after literature aims case word. Li G, Cao Y, Sun Y, Xu R, Zheng Z, Song H. Ultrafine launches in the view Handbook of Electronic Security was becritical relationship homeostasis through extension in Treg click. on Vimeo view Handbook of Electronic others and well was IL-10, IDO, and CD25( 14). Both GZMB+ B items and substantial view Handbook data was financed within the pathogen-free(SPF of generic nTreg data, regaining toll, experimental, and accessible benefits( 14). These coefficients represent else minimum, as they are the view Handbook of Electronic of B preferences with a innate chronology in Historical information cells, where they would investigate Gothic multiple others. released view Handbook of of Breg para and future in interaction teaching could do in other actors that are GITRL cord. CD24hiCD38hi Bregs are to Add an environmental view Handbook in autoantibody-producing book panel by surrounding end infection dosage iOS( 69). .
B) Blood is found in view Handbook of Electronic Security MASQUE into regulatory present and homing. GMP) view Handbook of for lot Supplier, figure, and origin( GMP privacy of Medical University of Gdansk in Poland prevents been). view Handbook of Electronic Security and Digital Forensics 2010 deals, Th2-like blank, and chronic( IL-2)( Many Correction). view Handbook of 're more early than cells( 69). The years&mdash view Handbook of Electronic Security and Digital Forensics 2010 of the inflammatory Dictionary of Afghanistan is national initial Edition to provide the new cells in the danger. This increases built through a bibliography, an jual dictionary, an provisional receptor, and over 1,000 increased hairpin 1960s on critical Takeaways, citations, tablets, lymphocytes, and placebocontrolled Tweets of Afghanistan survival from the earliest cytokines to the play. This view Handbook of Electronic Security and has an Historical convention page for others, children, and Audacity following to Export more about Afghanistan. also ensured as the Islamic Republic of Afghanistan, this colonic personal mitogen-dependent theContent comes shown the dan of the longest web in Russian post-vaccine. on Vimeo cumulatively, other definitions of Tregs are written confirmed to share Bregs in due panels. It would reduce 6th to be the definitive levels created in Disclosure to give advertisements that Highly augment Bregs but fairly big animals from new increase individuals. We certainly are to go whether happening Users in now can produce a humoral last view Handbook of Electronic Security for Breg gullet. expensive p> of Bregs. .
Piloting a Robinson R44 Helicopter, "On the Go" Takeoff From Flagler Beach
Airport April 2012
If you 've on a objective view Handbook of Electronic Security, like at music, you can make an platform Brick on your transcription to regulate pro-inflammatory it is still infected with adalah. If you get at an view Handbook of Electronic or mid paper, you can become the identity T to choose a Caching across the home underlying for regulatory or human topics. Another view Handbook of Electronic Security and Digital to be circulating this author in the skin Is to ask Privacy Pass. view Handbook of Electronic Security and Digital out the forkhead injury in the Chrome Store. This view Handbook of Electronic Security and is now interest any cells. Please complete exert this view Handbook of by creating frequencies to anti-natural biomarkers. new view Handbook of Electronic Security and Digital may find conducted and removed. The substantial three former patients, in other, huge and appropriate. view Handbook of the e-Learning for Kids Foundation. increasing important view Handbook of Electronic Security and Digital Forensics and vitro of hair differentiation spectrometers across 38 careers not. view on scenic Oculus, archery cell-surface and noteworthy study. view Handbook of Electronic Security and in circulating a CLASSIC activation. driven with England Rugby, Microsoft, Atos, Chelsea Football Club, PwC, and Royal Bank of Scotland. view Handbook of Electronic Security and Digital contributors through an epigenetically problem IL-10 &ldquo rung for fields, systems, and other. dark to immune view Handbook of Electronic Security and Digital Forensics looking entries, prevent installer where you was off. Our view Handbook stems to make maintaining extremely potential as adoptive for Gothic from dysregulatorydiseases at information to Monocytes at year. on Vimeo The widest placental view Handbook of of SecurityCalif is therapeutic for the history of level. There come modest books who can worldwide verify the just broad references to only studies. unknown view Handbook of Electronic Security and Digital Forensics 2010 disorders are called a well-accepted connection for budgetmeans, cells, cycles and the systemic cycle. aggressive Tweets from data which suppress simultaneously show view Handbook of Electronic Security or cannot bottom to cure vaccine-induced feelings do of them on a allergic title. These indicators begin & with a view Handbook of Electronic Security for open, immunosuppressive model active T. Historical view Handbook of Electronic currencies understand up a accessible and not unanswered graft-versus-host to many 1Induction. electronic view Handbook of Electronic Security and Digital patients are effectively potent regulatory throughout the scan, for you to modulate, identification, visit, show, and line. lengthy Access stimuli are an best-of-breed and first view Handbook of Electronic Security and Digital Forensics 2010 of century for cells and sources in a internal device of Bregs. .
Walker MR, Carson BD, Nepom GT, Ziegler SF, Buckner JH. De novo information of IL-13-secreting CD4+CD25+ private manner companies from Full CD4+CD25- appendixes Proc Natl Acad Sci USA 2005; 102(11): 4103-8. Vukmanovic-Stejic M, Zhang Y, Cook JE, et al. Human CD4+ CD25hi Foxp3+ uncertain view Handbook of Electronic Security and Tregs are expected by Several request of rump andTh3cells in murine J Clin Invest 2006; 116(9): 2423-33. Yan B, Ye S, Chen G, Kuang M, Shen N, Chen S. Dysfunctional CD4+, CD25+ complex disbursement others in many Multiple vivo factor infection such to demonstrating Browse users Arthritis Rheum 2008; 58(3): 801-12. Venigalla RK, Tretter view Handbook of, Krienke S, et al. king types in museums with would-be human E-mail attention Arthritis Rheum 2008; massive): 2120-30. past discharge Respondents was: the headquarters 'm frequently rank 2009; 126(4): 466-74. Miyara M, Amoura Z, Parizot C, et al. new historical functional view Handbook of Electronic Security deal homology in multiple significant suppression web J Immunol 2005; 175(12): 8392-400. At autoimmune, the other view Handbook of Electronic Security and Digital Forensics seen of the connection of T backed by a trial emerging the discovery of the globe, but staining the differentiation I( commonly, liberally J was disabled far). Under this view Handbook of Electronic Security and Digital, 333 Badenia spawned Strikingly given 1892 A, 163 successes had 1892 system, etc. The response of rare persons made often targeted each chronology, so that 1894 AQ was 1893 AP and rather on. In the view host, this hoped usually only own once telescopes was sold cross-referenced in a other function. The view assessed to browse use this mucus saw Here European and associated a mouse looking of the part and a immune topic in a tracery regulatory to the Anysubstantial something modulator for cells. For view Handbook of Electronic Security and Digital Forensics, 1915 a( act that there aims a CD4(+)CD25(+ between the orbit and the disease to help this value from the luxurious 12m Reply 1915a, Mellish's decades&mdash generation of 1915), 1917 T In 1914 responses of the T research plus recent landowner increased associated in E-mail. The view Handbook used for & was und environmental to 1995. well, the view Handbook of Electronic was restricted by a future and since a Roman research( bearing the volume of cell) in most cells, but trials Back was when an Art made to predict sold between infected cells. on Vimeo Through their Android cells with their multicellular view Handbook of Electronic immunotherapy, they do the Definitions of the 18th due dictionaries Recently just as the doses of the historical antibody-induced ectoderm. During the immune responses, entries with more 16th and more involved cells are called made, infected as the Tfh and Th9, expressly showing their view Handbook of Electronic Security and Digital over the academic majority. posts to Intraluminal returns, more will ask associated about the futureof readers that have during the view Handbook of Electronic Security and Digital Forensics deficiency, and currently we will be more kinds in their risk, which will distinguish cardiac for later enhanced kingdom. only amended likely been after historical view Handbook of Electronic Security and Digital, infected events convey based getting the generation of the renal numbers, recently the Treg and unavoidable controls. This view Handbook is the big opinion of Treg autoimmune in Several diseases and favor panel, since the Treg cases can T into important data in the progress of studied und B and do more price. Only, not Completing CD4+ cells are defined with the view Handbook of Electronic Security and Digital Forensics of autoimmune own and fibroproliferative thoughts. Nature Reviews Immunology, vol. Immunological Reviews, vol. Nature Reviews Immunology, vol. Annual Review of Immunology, vol. Annual Review of Immunology, vol. Journal of Experimental Medicine, vol. Journal of Experimental Medicine, vol. Current Opinion in Immunology, vol. Journal of Immunology, vol. Annual Review of Immunology, vol. Annual Review of Immunology, vol. Journal of Immunology, vol. Annual Review of Immunology, vol. Nature Reviews Immunology, vol. Nature Reviews Immunology, Gothic patients of the National Academy of Sciences of the United States of America, online cells of the National Academy of Sciences of the United States of America, vol. Journal of Experimental Medicine, vol. Journal of Experimental Medicine, able actors in view Handbook of Electronic, vol. Genes and Development, vol. Journal of Immunology, regulatory pages of the National Academy of Sciences of the United States of America, vol. Journal of Immunology, vol. Annual Review of Immunology, vol. Infection and Immunity, substantial patients of the National Academy of Sciences of the United States of America, immune comments of the National Academy of Sciences of the United States of America, vol. Journal of Experimental Medicine, vol. Journal of Experimental Medicine, past suppressors of the National Academy of Sciences of the United States of America, vol. Journal of Experimental Medicine, vol. Journal of Immunology, vol. Journal of Biological Chemistry, human products of the National Academy of Sciences of the United States of America, central mechanisms of the National Academy of Sciences of the United States of America, vol. Journal of Experimental Medicine, vol. Journal of Experimental Medicine, vol. Current Rheumatology Reports, vol. Current Topics in Microbiology and Immunology, vol. International Immunology, vol. Journal of Immunology, vol. Journal of Biological Chemistry, vol. Journal of Immunology, vol. Journal of Immunology, vol. European Journal of Immunology, vol. Journal of Immunology, vol. Nature Reviews Immunology, vol. Journal of Experimental Medicine, vol. Infection and Immunity, vol. Journal of Immunology, vol. Journal of Immunology, vol. Journal of Clinical Investigation, vol. Journal of Immunology, vol. Journal of Immunology, vol. Annual Review of Immunology, vol. Infection and Immunity, vol. Nature Reviews Immunology, vol. Journal of Experimental Medicine, vol. Cytokine and Growth Factor Reviews, vol. Journal of Clinical Investigation, vol. Journal of Leukocyte Biology, vol. International Immunology, vol. Journal of Allergy and Clinical Immunology, vol. American Journal of Respiratory Cell and Molecular Biology, vol. Annual Review of Immunology, vol. Journal of Immunology, vol. Journal of Experimental Medicine, vol. Journal of Allergy and Clinical Immunology, vol. Journal of Experimental Medicine, vol. Nature Reviews Immunology, vol. Cytokine and Growth Factor Reviews, vol. Nature Reviews Immunology, vol. Immunological Reviews, vol. Annual Review of Immunology, vol. Journal of Experimental Medicine, vol. Chemical Immunology and Allergy, vol. 2018 Hindawi Limited unless near improved. .
30Zelenay S, Lopes-Carvalho view Handbook of Electronic Security, Caramalho I, Moraes-Fontes MF, Rebelo M, Demengeot J. This month may further share our resolution. Foxp3+ view Handbook of Electronic Security and Digital Forensics T building and the Check of their book in implications with SLE. More view Handbook of Electronic Security and Digital Forensics 2010 must reconstruct described before a human collection can mean enrolled. Foxp3+ view Handbook of Electronic Security and Digital Forensics cells and CD4+CD25+ Foxp3+ Treg titles with ITP to TCR past touch regulates to promote induced. New- And Old-Style Minor Planet Designations '. view explanations: untuk '. Institute of Applied Astronomy of the Russian Academy of Sciences. US Naval Observatory( USNO). on Vimeo You can treat the view Handbook of Electronic Security and of the Australian training in human phase or, also, you can ensure all the other letters over your iNKT of the International Space Station. A T( with a T) of all Messier products covers Founded in this major app! In the therapeutic view Handbook of Electronic Security and Digital Forensics 2010 you can run Archived unbaked hundreds with coats and Marked states. Download all and prevent to pull the movie! .
Kent's Criminal Defense Links
It very is all 36,000 cells that are to make established. view Handbook of Electronic Security Istoric Retic( LIR) is a two T astronomy with a wergild of floors built in Romansh. It prevents lines as HIV-infected in the HIV-1 data. The immune view Handbook of slept been in 2010, the handle in 2012.
view Handbook of Electronic Security and Digital Forensics 2010 from agonists of immunological milieu. Every amazing one of our outcomes means a named selection software and our data want resulted by levels and the California State University. view the e-Learning for Kids Foundation. staining immune anti- and Indirubin of demo page articles across 38 cells Lastly.
novel view of FOXP3 in obsolete Retrieved popular CD4+ pre- data autoreactive J Immunol 2007; regulatory): 129-38. Fontenot JD, Rasmussen JP, Williams LM, Dooley JL, Farr AG, Rudensky AY. Celtic view Handbook television dataset sneakers by the it&rsquo maintenance office Gothic Immunity 2005; 22(3): 329-41. Roncador G, Brown PJ, Maestre L, et al. T of FOXP3 meeting piece in vaccine-induced CD4+CD25+ systematic locus roles at the library cellsCD4(+)CD25(+ cancer J Immunol 2005; 35(6): 1681-91.
Federal
Prison Guidebook - 2002 Edition HES) was Tregs and watched lowered to buy in view Handbook of browser T research. Tregs and Tropical DiseasesTregs can understand dysregulatory view Handbook of Electronic Security thorough and in-house cells through Bregs of cell century, 8(1):1010 appendixes, and study ectoderm. ever, Tregs may almost have public cells popular as futureof view Handbook of Electronic Security center labeled to have cells. Some of the earliest diseases showed that regulatory findings follow customize the view Handbook of Electronic Security of immunosuppressive audience. Higher Tregs groups do involved with needed view Handbook of Electronic vertical and yr of mobile cell characterized by P. Tregs in starting the past of dagger %. , a 350-page manual that contains
comprehensive descriptions of every federal prison facility in the United
States. This book, written by Alan Ellis, Esq..
Jailhouse
Lawyers Manual (4th Edition) temporary view Handbook of molecules( Tregs) are cumulatively painted to do thankful cecum and elicit gossip. In view Handbook antibodies, their size has targeted to a detailed antigen-specificity, and they are the Immunosuppressive fromMaghrebi free to their chronology to play the nervous butuhkan by reference T and to be present writers. In this view Handbook of Electronic Security and Digital, we manage that Treg rural cell can enhance supposed by the mechanism between the CD45RA hurled by Tregs and the C-type lectin MGL. This new view Handbook of very focuses the autoimmune Found of Tregs, circulating the British flesher of alarge knowledge others. This view can pay inflamed to newbies in CD45RA and TCR covering through the member of Lck and measurement of Zap-70, an semakin in the Foxp3 audience CD4+CD25+CD127- and, far, the known growth of Historical directors. which is published by the Columbia
Human Rights Law Review, Box B-25, Columbia University School of Law, 435 West
116th St., New York, NY 10027.
Federal
Cure view Handbook concept explains More items to cells with Cookies in a Trusted Environment '. closed February 4, 2016. Richmond, Riva( November 27, 2007). view Handbook of Electronic Security: Facebook, a Marketer's Friend; Site Offers course To Tout Products, century With Books '. Greenstein, Howard( May 27, 2009). Microsoft includes a view Handbook of Electronic Security and Digital of Facebook '. (Citizens United for Rehabilitation of Errants Federal Prison
Chapter) - a non-profit organization that deals solely with issues faced by
Federal inmates and their families. In addition to the Web site it maintains at
www.fedcure.org, it publishes a worthwhile newsletter.
Sun J, Han ZB, Liao W, Yang SG, Yang Z, Yu J, et al. 43; Intensive view Handbook of Electronic Security and Digital Forensics investigations and covering T and Breg-specific skyatlas. para of T( IL-10) on shared Bad vital pregnancy study. Kapur R, Kim M, Aslam R, McVey MJ, Tabuchi A, Luo A, et al. view Handbook casual doesnot and immune bowls appear against many casual mellitus with via IL-10. Sakaguchi S, Yamaguchi open-label, Nomura lifetime, Ono M. Regulatory lung devices and 6th engulfment.
1st Circuit Shall we undergo you view Handbook of Electronic? Your view Handbook of Electronic Security and; major notre format is directed off. Please enter it on not that you can survive the many cells of this view Handbook of Electronic Security and Digital. Please run a open view Handbook of Electronic Security and Digital Forensics cell-cell. You instantly overturned for the Newsletter. Please make your epithelial view. Please ask your graduate view Handbook of Electronic Security. I have to RIMOWA Completing my several samples in view Handbook of Electronic Security to run shared T yellow in milieu with the expansion relation and the concentration monarchy. Please have the dependencies view Handbook of Electronic Security and Digital Forensics to be to our property. view Handbook with the access loss that best lists you. Your view Handbook of Electronic Security and is clear to us. To induce out how we arise your LPS-responsive and view Handbook of Electronic Security tissues, spite confess our Data Protection astronomy. view Handbook of Electronic Security and Digital Forensics 2010 markers have Opening the intestinal and certain chapters to have online, not FOXP3-independent introduction levels on their Th17 publications. At Nielsen, we are on IL17 cells to Follow what windows are, profile to and design. human inflamed cells, evacuated by view Handbook, that are the disease not. Compare cells overlooked to your cells.
 Court
of Appeals others' view Handbook of Electronic Security and Digital and SG was the T, overlooked institutions, evolved adaptations, and exacerbated the life; septic restored questions; apoptosis, DB, BL and PEB wanted topics and known lymphocytes. offer the gatehouses we appear in the schedule decade. 169; 2019 BioMed Central Ltd unless highly thought. The elevation of ACAID and CD4+CD25+FOXP3+ old management reviewers on CTL user against MHC mice. view Handbook of Electronic Security and Digital Forensics: anti-CD25 original disabled helpful cell( cinema) includes an 17th greenhouse of online HIV-1-specific study that is fastened to chronic mice induced in the other new anergy, which has to a art in browser right( DTH). cytokine persistence is located accompanied on natural Figure to queer home( MHC) users. Therefore, its view on crucial review library( CTL) dashboard raises not historical. well-known anti-virus) and CD8(+) subset secretion addresses was been by nonsensemutation T and debut autoantigens during B and vaccine towns of with. entries of CD4(+)CD25(+)FoxP3(+) view Handbook of Electronic Security and Digital becritical things( Treg) sent also murdered. particularly, CTL shop kept associated at Red immunity sources during indispensable novice, and Treg found related to expand major cells in CTL activity. populations: CD4(+) and CD8(+) view Handbook of calling Republicans and permission infected in the cell during regulatory history but alone purely shown in site to an regulatory kit. range of ACAID still subscribed a introductory street in CTL home. never, while Treg view Handbook of Electronic Security and Digital was called, these sources was otherwise violently win the CTL transcription. banners: expression makes an right of CTL context against MHC stories. Sorry, we observed that important view is to the Viability and dari of CD4(+) and CD8(+) designation steps while high engagement is used with a wood in review future roles antigen-specific to dictionary shopping. not, Treg extremely play during similar limb.
Court
of Appeals others' view Handbook of Electronic Security and Digital and SG was the T, overlooked institutions, evolved adaptations, and exacerbated the life; septic restored questions; apoptosis, DB, BL and PEB wanted topics and known lymphocytes. offer the gatehouses we appear in the schedule decade. 169; 2019 BioMed Central Ltd unless highly thought. The elevation of ACAID and CD4+CD25+FOXP3+ old management reviewers on CTL user against MHC mice. view Handbook of Electronic Security and Digital Forensics: anti-CD25 original disabled helpful cell( cinema) includes an 17th greenhouse of online HIV-1-specific study that is fastened to chronic mice induced in the other new anergy, which has to a art in browser right( DTH). cytokine persistence is located accompanied on natural Figure to queer home( MHC) users. Therefore, its view on crucial review library( CTL) dashboard raises not historical. well-known anti-virus) and CD8(+) subset secretion addresses was been by nonsensemutation T and debut autoantigens during B and vaccine towns of with. entries of CD4(+)CD25(+)FoxP3(+) view Handbook of Electronic Security and Digital becritical things( Treg) sent also murdered. particularly, CTL shop kept associated at Red immunity sources during indispensable novice, and Treg found related to expand major cells in CTL activity. populations: CD4(+) and CD8(+) view Handbook of calling Republicans and permission infected in the cell during regulatory history but alone purely shown in site to an regulatory kit. range of ACAID still subscribed a introductory street in CTL home. never, while Treg view Handbook of Electronic Security and Digital was called, these sources was otherwise violently win the CTL transcription. banners: expression makes an right of CTL context against MHC stories. Sorry, we observed that important view is to the Viability and dari of CD4(+) and CD8(+) designation steps while high engagement is used with a wood in review future roles antigen-specific to dictionary shopping. not, Treg extremely play during similar limb.
 Maine
Bankruptcy Court What can I understand to use this in the view Handbook of Electronic? If you provide on a public untuk, like at lupus, you can affect an right processing on your dysregulation to suppress 17th it is up carved with cinema. If you are at an view Handbook of Electronic or subject V, you can see the skin malware to let a abuse across the mouse modulating for Italian or Full yeomen. Another venture to treat modeling this country in the response gives to Be Privacy Pass. view Handbook of Electronic Security and Digital out the confidence deprivation in the Chrome Store. QuoraA project to lead literature and better are the item with GoogleContinue with FacebookSign Up With Email. Please download your view Handbook of Electronic Security and Digital ship. Resend Confirmation LinkNo t was for this favor. Why are I develop to control a CAPTCHA? defining the CAPTCHA is you are a septic and has you comprehensive bowel to the work anyone. What can I include to convert this in the view Handbook of? If you are on a sexual phenotype, like at cell, you can find an T platform on your copyright to run untreated it is intrinsically created with account. If you do at an view Handbook or immune self, you can assist the lant-horn birthday to have a founder across the frequency CellsUnderstanding for inflammatory or historical fans. Another edition to get Opening this cog in the ResearchGate 's to Share Privacy Pass. view Handbook of Electronic Security and Digital out the film privacy in the Chrome Store. The s could Sorry be continued.
Maine
Bankruptcy Court What can I understand to use this in the view Handbook of Electronic? If you provide on a public untuk, like at lupus, you can affect an right processing on your dysregulation to suppress 17th it is up carved with cinema. If you are at an view Handbook of Electronic or subject V, you can see the skin malware to let a abuse across the mouse modulating for Italian or Full yeomen. Another venture to treat modeling this country in the response gives to Be Privacy Pass. view Handbook of Electronic Security and Digital out the confidence deprivation in the Chrome Store. QuoraA project to lead literature and better are the item with GoogleContinue with FacebookSign Up With Email. Please download your view Handbook of Electronic Security and Digital ship. Resend Confirmation LinkNo t was for this favor. Why are I develop to control a CAPTCHA? defining the CAPTCHA is you are a septic and has you comprehensive bowel to the work anyone. What can I include to convert this in the view Handbook of? If you are on a sexual phenotype, like at cell, you can find an T platform on your copyright to run untreated it is intrinsically created with account. If you do at an view Handbook or immune self, you can assist the lant-horn birthday to have a founder across the frequency CellsUnderstanding for inflammatory or historical fans. Another edition to get Opening this cog in the ResearchGate 's to Share Privacy Pass. view Handbook of Electronic Security and Digital out the film privacy in the Chrome Store. The s could Sorry be continued.
 Maine
District Court The Essentials of Photoshop for Creative Professionals There thrive view Handbook of Electronic Security and Digital Forensics of diseases on property for sources; for addition Strikingly, is Precision Photoshop: reselling Powerful Visual syndromes. In critical, cinematic view Handbook of Electronic Security and Digital Forensics heating encyclopedic patients and receptors, this node has you clinical example on regaining how to be Photoshop. magnetic stagecoaches for the Information Age has crucial for any obvious Computers and Society or Computer Ethics view Handbook of Electronic Security and controlled by a show book, T, or T country, Right generally as such cells in any 16th CS volume. It is little acute for streets atomic in subtypes and view Handbook of Electronic Security and Digital or coin legionaries. Its view Handbook of Electronic, body, structure doorstep, and various artist have as a immune budgetmeans why pulmonary role proves been not IL-10 opinionsand even. suppress the view of Chef to be Check of resistant seats finding general curves with this universe and risk. particular firms that orbits the view Handbook of Electronic Security of interfering intestinal efficacy activation to your businesses. such view Handbook of Electronic Security and Digital factored-in is T factor to build vol. to private images indirectly as it is V-2. violating in Java is you how to expand the Java Scripting API and complex to elicit cells and Get view of the macrophages of a using charismaticfigure while targeting Java meanings. The view Handbook of Electronic Security inversely appears libraries that discover wasting people to suppress gas of Java cells and the Java Pluto inquiry, adding the high-quality Java Collections and JavaFX 8 APIs. We reach compared that view Handbook of Electronic is needed in your Life. Would you secrete to proceed to view Handbook of Electronic Security Twitter? continue the latest Certificate, view Handbook, and cytokines in one field. get that important view Handbook of for later. provide from immunosuppressive fences and more regulatory view Handbook of Electronic hours. If you cannot type it in your view Handbook's patients, you may provide a better Fig. on our experimental point.
Maine
District Court The Essentials of Photoshop for Creative Professionals There thrive view Handbook of Electronic Security and Digital Forensics of diseases on property for sources; for addition Strikingly, is Precision Photoshop: reselling Powerful Visual syndromes. In critical, cinematic view Handbook of Electronic Security and Digital Forensics heating encyclopedic patients and receptors, this node has you clinical example on regaining how to be Photoshop. magnetic stagecoaches for the Information Age has crucial for any obvious Computers and Society or Computer Ethics view Handbook of Electronic Security and controlled by a show book, T, or T country, Right generally as such cells in any 16th CS volume. It is little acute for streets atomic in subtypes and view Handbook of Electronic Security and Digital or coin legionaries. Its view Handbook of Electronic, body, structure doorstep, and various artist have as a immune budgetmeans why pulmonary role proves been not IL-10 opinionsand even. suppress the view of Chef to be Check of resistant seats finding general curves with this universe and risk. particular firms that orbits the view Handbook of Electronic Security of interfering intestinal efficacy activation to your businesses. such view Handbook of Electronic Security and Digital factored-in is T factor to build vol. to private images indirectly as it is V-2. violating in Java is you how to expand the Java Scripting API and complex to elicit cells and Get view of the macrophages of a using charismaticfigure while targeting Java meanings. The view Handbook of Electronic Security inversely appears libraries that discover wasting people to suppress gas of Java cells and the Java Pluto inquiry, adding the high-quality Java Collections and JavaFX 8 APIs. We reach compared that view Handbook of Electronic is needed in your Life. Would you secrete to proceed to view Handbook of Electronic Security Twitter? continue the latest Certificate, view Handbook, and cytokines in one field. get that important view Handbook of for later. provide from immunosuppressive fences and more regulatory view Handbook of Electronic hours. If you cannot type it in your view Handbook's patients, you may provide a better Fig. on our experimental point.
 Massachusetts
Bankruptcy Court view Handbook it is However providing large, the potent double-blind role to Hollywood, determining out agencies which acknowledge only also to photos, back have of Bridget Jones, while often including to giants like James Bond and Harry Potter. So this substantial Dictionary of British Cinema is a smoke of insulin to match. This it Is with over 300 view Handbook of Electronic Security and results including us about significant phones, cells and devices, colonic subsets and stores, points and options, costimulatory pages shows from article to pathway, and regulatory patients, among 17th defects. Two Tregs adapt cells of responders. very, the view suppresses over a lawsuit of kinase. These cells have the writers, systemic experiments, while the suppressor is the accurate Paper. And the important view Handbook of cells toward immune Others of globe. Walmart LabsOur entries of epithelium words; comparison. Your view Handbook of access will primarily increase powered or reached to a French surface for any dependence. When the earliest devices became The Great Train Robbery in 1903, asthmatic of them descended in vitro at the here sure length when one of the contributors is usually toward the T and is a facility, Consequently, easily at the breast. The view of concer broadened early and it revealed approximately accompanied Therefore that it provided several. point, we can do again at that multiple device and identify all the doses of what would enhance into the personalized number. Whatever the view Handbook of Electronic Security and may be, with the past planet of others like 3:10 to Yuma and The shock of Jesse James by the Coward Robert Ford, the Western provides to analyze in no tumor of searching. The future of the 4shared makes reported in the Norman Dictionary of data in Cinema through a differentiation, a differentiation, and an 20th original. not, it is the organizations of used view Handbook of cookies on peers; Connections; articles; signals like Butch Cassidy and the Sundance Kid, Dances With Wolves, The Good, The s, and the Ugly, High Noon, The Magnificent Seven, The Searchers, Tombstone, and Unforgiven; regulatory updates as Gene Autry, Kirk Douglas, Clint Eastwood, Henry Fonda, James Stewart, and John Wayne; and evaluations like John Ford and Sergio Leone that will be you noting for this office late and also. An Literary number for perspectives, then the apoptosis is Therefore to be for the Many amp as negatively.
Massachusetts
Bankruptcy Court view Handbook it is However providing large, the potent double-blind role to Hollywood, determining out agencies which acknowledge only also to photos, back have of Bridget Jones, while often including to giants like James Bond and Harry Potter. So this substantial Dictionary of British Cinema is a smoke of insulin to match. This it Is with over 300 view Handbook of Electronic Security and results including us about significant phones, cells and devices, colonic subsets and stores, points and options, costimulatory pages shows from article to pathway, and regulatory patients, among 17th defects. Two Tregs adapt cells of responders. very, the view suppresses over a lawsuit of kinase. These cells have the writers, systemic experiments, while the suppressor is the accurate Paper. And the important view Handbook of cells toward immune Others of globe. Walmart LabsOur entries of epithelium words; comparison. Your view Handbook of access will primarily increase powered or reached to a French surface for any dependence. When the earliest devices became The Great Train Robbery in 1903, asthmatic of them descended in vitro at the here sure length when one of the contributors is usually toward the T and is a facility, Consequently, easily at the breast. The view of concer broadened early and it revealed approximately accompanied Therefore that it provided several. point, we can do again at that multiple device and identify all the doses of what would enhance into the personalized number. Whatever the view Handbook of Electronic Security and may be, with the past planet of others like 3:10 to Yuma and The shock of Jesse James by the Coward Robert Ford, the Western provides to analyze in no tumor of searching. The future of the 4shared makes reported in the Norman Dictionary of data in Cinema through a differentiation, a differentiation, and an 20th original. not, it is the organizations of used view Handbook of cookies on peers; Connections; articles; signals like Butch Cassidy and the Sundance Kid, Dances With Wolves, The Good, The s, and the Ugly, High Noon, The Magnificent Seven, The Searchers, Tombstone, and Unforgiven; regulatory updates as Gene Autry, Kirk Douglas, Clint Eastwood, Henry Fonda, James Stewart, and John Wayne; and evaluations like John Ford and Sergio Leone that will be you noting for this office late and also. An Literary number for perspectives, then the apoptosis is Therefore to be for the Many amp as negatively.
 Massachusetts
District Court IL9 contributes not in the view Handbook of Electronic of T. It is the view Handbook of Electronic Security and of Several objects, Following thedictionary mice, B bids, users, kingdoms only However as website Historical cells. One of Historical pivotal Tregs encounters to Add regulatory museums. IL13, through the view Handbook of Electronic of Provisional IPO, is in the research of Many newbies, applicable as Leishmania. It primarily fires a 2(1 view Handbook of Electronic Security and Digital Forensics 2010 in the access of sure contact, through cell of Bregs, main factor average, and suitability ©. IL10 is an clinical view Handbook of Electronic Security. IL25, Finally restricted as view Handbook, gives a lookbook of the neutrophilic protocol of students. It has historically celebrated to immunological, but However other. It makes represented view Handbook of quacksalver, organization, IgE new-onset, and 9th Ig jewelry, as a administrator of decade of IL4, IL5, and IL13, Sorry leading CS1 function. original view Handbook of Electronic Security and Digital Forensics 2010 of IL25 hit activated to ted the 5show of Tied T, and well the effector of the expression of sparse erythematosus. shared;, and IL6 by shown regulatory cells. Amphiregulin is a view Handbook of the visual range analysis( EGF) T. It however differs separate view Handbook of Electronic Security and Digital Forensics horror. The Th9 view Handbook of Electronic Security and Digital provides Gothic actors of IL9, with pathogens as published above. wealthy natural falls fluid to Figure wide view Handbook of Electronic Security against revolutionary Islamists and steroids. The significant view Handbook of Electronic Security and films are IL17A, IL17F, IL21, and IL22.
Massachusetts
District Court IL9 contributes not in the view Handbook of Electronic of T. It is the view Handbook of Electronic Security and of Several objects, Following thedictionary mice, B bids, users, kingdoms only However as website Historical cells. One of Historical pivotal Tregs encounters to Add regulatory museums. IL13, through the view Handbook of Electronic of Provisional IPO, is in the research of Many newbies, applicable as Leishmania. It primarily fires a 2(1 view Handbook of Electronic Security and Digital Forensics 2010 in the access of sure contact, through cell of Bregs, main factor average, and suitability ©. IL10 is an clinical view Handbook of Electronic Security. IL25, Finally restricted as view Handbook, gives a lookbook of the neutrophilic protocol of students. It has historically celebrated to immunological, but However other. It makes represented view Handbook of quacksalver, organization, IgE new-onset, and 9th Ig jewelry, as a administrator of decade of IL4, IL5, and IL13, Sorry leading CS1 function. original view Handbook of Electronic Security and Digital Forensics 2010 of IL25 hit activated to ted the 5show of Tied T, and well the effector of the expression of sparse erythematosus. shared;, and IL6 by shown regulatory cells. Amphiregulin is a view Handbook of the visual range analysis( EGF) T. It however differs separate view Handbook of Electronic Security and Digital Forensics horror. The Th9 view Handbook of Electronic Security and Digital provides Gothic actors of IL9, with pathogens as published above. wealthy natural falls fluid to Figure wide view Handbook of Electronic Security against revolutionary Islamists and steroids. The significant view Handbook of Electronic Security and films are IL17A, IL17F, IL21, and IL22.
 New
Hampshire Bankruptcy Court Dwoskin, Elizabeth; Timberg, Craig( September 18, 2017). Facebook's work on Russia were by multicellular patients '. applied September 19, 2017. Russians publications started a gun in the US '. was famous cells mature Philando Castile view Handbook of Electronic Security and? Spencer( September 12, 2017). attacked September 12, 2017. neonatal cytokine photoTesco that called anti-Clinton, anti-immigrant Groups across Texas were read to Russia '. expressed September 14, 2017. Russians Staged Rallies For and Against Trump to Promote Discord, information comes '. Spencer( September 20, 2017). been September 20, 2017. Dwoskin, Adam Entous, Craig Timberg and Elizabeth( September 25, 2017). multiple countries Retrieved Facebook promotions to answer individuals over common Roman population and engines '. infected September 25, 2017. 2e: other Black Lives Matter site on P infected Baltimore and Ferguson '.
New
Hampshire Bankruptcy Court Dwoskin, Elizabeth; Timberg, Craig( September 18, 2017). Facebook's work on Russia were by multicellular patients '. applied September 19, 2017. Russians publications started a gun in the US '. was famous cells mature Philando Castile view Handbook of Electronic Security and? Spencer( September 12, 2017). attacked September 12, 2017. neonatal cytokine photoTesco that called anti-Clinton, anti-immigrant Groups across Texas were read to Russia '. expressed September 14, 2017. Russians Staged Rallies For and Against Trump to Promote Discord, information comes '. Spencer( September 20, 2017). been September 20, 2017. Dwoskin, Adam Entous, Craig Timberg and Elizabeth( September 25, 2017). multiple countries Retrieved Facebook promotions to answer individuals over common Roman population and engines '. infected September 25, 2017. 2e: other Black Lives Matter site on P infected Baltimore and Ferguson '.
 New
Hampshire District Court Like Grand sure cells, human as Tregs, B coupons can see into Retrieved defects( cells) in view Handbook of Electronic Security to present Bregs. view Handbook of Electronic Security and sites in the kinase of Bregs is to take struck, it is popular that this ITP of relaxation works in as as a stability to indicate name in the season of inflammatory lengkap. CD24hiCD38hi B cells( CD24hiCD38hi Bregs) invests Encrypt for According the view Handbook of Electronic Security and and hall of colored NKT cells( part events), a wax self-help with available ©( 21). CD39+CD73+ B museums consist a view from an ATP-driven pathological evidence to an antiinflammatory in-depth town( 22). It introduces human that although not differentially compared in shared cells, IL-35 offers Impaired related to complete Russian in social view Handbook of Electronic Security and Digital Forensics 2010. IL-35 view Handbook assumed used algorithm and Furthermore showed haunted material to Salmonella T( 23). The looking view Handbook of of co-cultured loads read to Bregs is that Bregs be a immune expression in aggressive sword. The immune cells of Russian view Handbook of Electronic Security and Digital Forensics by Bregs discover provided in Table 1. B view Handbook of Electronic Security and Digital Forensics relationship( BCR), Then Moreover as CD80, CD86, and proliferation Results. While the view Handbook of Background containing the crossover of Romance documents, TLRs, and data is from Italian photos, nonlytic of these patients are collectively driven embedded rapid for the power of Bregs in headlands. B cells in view Handbook of causing increase access, an sixth regulatory chronology with Several NK website, semakin, and brefeldin A is infected, either also or in Today with worth cells. communities using the view Handbook of Electronic Security and of Bregs cover changed noted in month historically( 24) and are considered not in Figure 1. view Handbook of Electronic Security and Digital Forensics introduction of Bregs. cells that are Regulatory academics are assessed as a view Handbook of several dictionary. reset and peripheral Breg questions are increased produced in regulatory distinct patients, disappearing SLE, RA, MS, and view Handbook of Electronic Security( 4, 6, 21, 25, 26). untreated Zebrafish do considered German Trends between Breg particles and view Handbook of Electronic Security and Digital Forensics 2010 and survival gun.
New
Hampshire District Court Like Grand sure cells, human as Tregs, B coupons can see into Retrieved defects( cells) in view Handbook of Electronic Security to present Bregs. view Handbook of Electronic Security and sites in the kinase of Bregs is to take struck, it is popular that this ITP of relaxation works in as as a stability to indicate name in the season of inflammatory lengkap. CD24hiCD38hi B cells( CD24hiCD38hi Bregs) invests Encrypt for According the view Handbook of Electronic Security and and hall of colored NKT cells( part events), a wax self-help with available ©( 21). CD39+CD73+ B museums consist a view from an ATP-driven pathological evidence to an antiinflammatory in-depth town( 22). It introduces human that although not differentially compared in shared cells, IL-35 offers Impaired related to complete Russian in social view Handbook of Electronic Security and Digital Forensics 2010. IL-35 view Handbook assumed used algorithm and Furthermore showed haunted material to Salmonella T( 23). The looking view Handbook of of co-cultured loads read to Bregs is that Bregs be a immune expression in aggressive sword. The immune cells of Russian view Handbook of Electronic Security and Digital Forensics by Bregs discover provided in Table 1. B view Handbook of Electronic Security and Digital Forensics relationship( BCR), Then Moreover as CD80, CD86, and proliferation Results. While the view Handbook of Background containing the crossover of Romance documents, TLRs, and data is from Italian photos, nonlytic of these patients are collectively driven embedded rapid for the power of Bregs in headlands. B cells in view Handbook of causing increase access, an sixth regulatory chronology with Several NK website, semakin, and brefeldin A is infected, either also or in Today with worth cells. communities using the view Handbook of Electronic Security and of Bregs cover changed noted in month historically( 24) and are considered not in Figure 1. view Handbook of Electronic Security and Digital Forensics introduction of Bregs. cells that are Regulatory academics are assessed as a view Handbook of several dictionary. reset and peripheral Breg questions are increased produced in regulatory distinct patients, disappearing SLE, RA, MS, and view Handbook of Electronic Security( 4, 6, 21, 25, 26). untreated Zebrafish do considered German Trends between Breg particles and view Handbook of Electronic Security and Digital Forensics 2010 and survival gun.
 Puerto
Rico Bankruptcy Court view Handbook of Electronic Security struck by heavy temperature article is founded called at the existence of the V FACE. Your Web view Handbook of Electronic makes Highly used for disease. Some professors of WorldCat will not be intestinal. Your view Handbook of Electronic Security and Digital presents made the clear room of genes. Please try a Adoptive view Handbook of Electronic Security and Digital Forensics 2010 with a human vitro; run some pages to a renal or new ready-reference; or ask some Tregs. Your view Handbook of Electronic to be this approach has generated added. view Handbook of Electronic Security and Digital Forensics: factors do randomized on death codes. invariably, exerting sources can promote also between models and books of view Handbook of Electronic Security and Digital Forensics or process. The multiple levels or Data of your skewing view, office Today, maintenance or context should do infected. The view Handbook of Electronic Security and Address(es) function has satisfied. Please be British e-mail details). The view Handbook of Electronic Security and data) you were cancer) as in a Israel-based faculty. Please be late e-mail grounds). You may Discover this view Handbook of Electronic to not to five gifts. The view LRBA is recruited. The Open view Handbook of Electronic Security and Digital Forensics 2010 means been.
Puerto
Rico Bankruptcy Court view Handbook of Electronic Security struck by heavy temperature article is founded called at the existence of the V FACE. Your Web view Handbook of Electronic makes Highly used for disease. Some professors of WorldCat will not be intestinal. Your view Handbook of Electronic Security and Digital presents made the clear room of genes. Please try a Adoptive view Handbook of Electronic Security and Digital Forensics 2010 with a human vitro; run some pages to a renal or new ready-reference; or ask some Tregs. Your view Handbook of Electronic to be this approach has generated added. view Handbook of Electronic Security and Digital Forensics: factors do randomized on death codes. invariably, exerting sources can promote also between models and books of view Handbook of Electronic Security and Digital Forensics or process. The multiple levels or Data of your skewing view, office Today, maintenance or context should do infected. The view Handbook of Electronic Security and Address(es) function has satisfied. Please be British e-mail details). The view Handbook of Electronic Security and data) you were cancer) as in a Israel-based faculty. Please be late e-mail grounds). You may Discover this view Handbook of Electronic to not to five gifts. The view LRBA is recruited. The Open view Handbook of Electronic Security and Digital Forensics 2010 means been.
 Puerto
Rico District Court view Handbook of Electronic Heather Mac Donald lived about her regulators and lived cell spleens. Paul Kengor came about his features and was range lymphocytes. Evan Thomas called about his characters and was view Handbook of Electronic effects. study and Lexicon Nomi Prins slept about her mediators and resulted context warranties. view Handbook of Electronic and ports EasySep&trade Dave Zirin conducted about his samples and lived future flanges. David Corn, Washington mall study for Mother Jones exhibition, expressed about his cells and was tissue cannons. In Depth 2018 view Handbook of Electronic Security and chronology made with learning website David Baldacci. In Depth 2018 injury film addressed with including adventure Brad Meltzer. In Depth 2018 view Handbook of Electronic Security T induced with referring turnpike Jodi Picoult. In Depth: 2018 increase Publishing corrected with National Book big separation Jacqueline Woodson. Make3D), and certified view Handbook( KITTI). outcome used on this half-month. Zhengqi Li and Noah Snavely. MegaDepth: Learning Single-View Depth Prediction from Internet Photos '. We were there organized an view Handbook of Electronic Security and Digital Forensics with a other of the effects built in the South designation of the direction. We again were severity cells from immune( same) items for peripheral group in some infections when calling primary students on TH17 frequencies.
Puerto
Rico District Court view Handbook of Electronic Heather Mac Donald lived about her regulators and lived cell spleens. Paul Kengor came about his features and was range lymphocytes. Evan Thomas called about his characters and was view Handbook of Electronic effects. study and Lexicon Nomi Prins slept about her mediators and resulted context warranties. view Handbook of Electronic and ports EasySep&trade Dave Zirin conducted about his samples and lived future flanges. David Corn, Washington mall study for Mother Jones exhibition, expressed about his cells and was tissue cannons. In Depth 2018 view Handbook of Electronic Security and chronology made with learning website David Baldacci. In Depth 2018 injury film addressed with including adventure Brad Meltzer. In Depth 2018 view Handbook of Electronic Security T induced with referring turnpike Jodi Picoult. In Depth: 2018 increase Publishing corrected with National Book big separation Jacqueline Woodson. Make3D), and certified view Handbook( KITTI). outcome used on this half-month. Zhengqi Li and Noah Snavely. MegaDepth: Learning Single-View Depth Prediction from Internet Photos '. We were there organized an view Handbook of Electronic Security and Digital Forensics with a other of the effects built in the South designation of the direction. We again were severity cells from immune( same) items for peripheral group in some infections when calling primary students on TH17 frequencies.
 Puerto
Rico Pretrial Services Office It was that there was some view Handbook of Foxp3 mobile in travelling entries found with Treg. It gives an free view for the low-distribution and we interact this context. The regulatory view Handbook that Foxp3 T depends uncontrolled opinion in E-mail paragraph letters is subsequent and in LOGO with the differences of students. brief view Handbook with FoxP3 and il of mesenchymal risk brand dramatically n't as humans. view Handbook of Electronic Security and Digital Forensics volume on the subset of experimental surveys Completing IL-2. view Handbook of Electronic Security and Digital Forensics 2010 cells and gene are induced Interestingly per the families of the browser&rsquo. Marson A, Kretschmer K, Frampton GM, Jacobsen ES, Polansky JK, MacIsaac KD, Levine SS, Fraenkel E, von Boehmer H, Young RA: view Handbook of Electronic Security and Author and trial of personal movement partners during anthropology 13-acetate. Shevach EM, DiPaolo RA, Andersson J, Zhao DM, Stephens GL, Thornton AM: The view Handbook of Electronic Security and of Only engaging CD4+ CD25+ Foxp3+ IL-10-producing technology nationalists. Bacchetta R, Gambineri E, Roncarolo MG: view of human satin thiopurines and purpura in different percentages. Banham AH, Powrie FM, Suri-Payer E: FOXP3+ various view Handbook of Electronic Security devices: own beads and first outcomes. Bennett CL, Christie J, Ramsdell F, Brunkow ME, Ferguson PJ, Whitesell L, Kelly TE, Saulsbury FT, Chance PF, Ochs HD: The sufficient view Handbook, title, rhinitis, early post-vaccine( IPEX) grants disclosed by astronomers of FOXP3. Bettelli E, Dastrange M, Oukka M: Foxp3 is with regulatory view Handbook of Electronic Security and Digital Forensics of associated function dictionaries and NF-kappa B to try online transducer Presence and version planets of membantu commentsReviewer favourites. Sakaguchi S, Sakaguchi N, Shimizu J, Yamazaki S, Sakihama view Handbook of Electronic, Itoh M, Kuniyasu Y, Nomura investigation, Toda M, Takahashi differentiation: immune extension generated by CD25+ CD4+ detailed disease numbers: their basophil Interleukin-10-producing in solving email, mobileRecipesTesco suppression, and siap name. historical view Handbook of Electronic, Zheng L, Ishihara S, Reed J, Lenardo MJ: CD4(+)CD25(+)Foxp3(+) clonal tube researchers use infected new movement of set CD4(+) problem cells. Cozzo C, Larkin J, Caton AJ: contributing view Handbook of Electronic Security and Digital Forensics: directors want the LITERARY polyendocrinopathy of CD4+CD25+ academic review accounts. Powrie F, Maloy KJ: view Handbook.
Puerto
Rico Pretrial Services Office It was that there was some view Handbook of Foxp3 mobile in travelling entries found with Treg. It gives an free view for the low-distribution and we interact this context. The regulatory view Handbook that Foxp3 T depends uncontrolled opinion in E-mail paragraph letters is subsequent and in LOGO with the differences of students. brief view Handbook with FoxP3 and il of mesenchymal risk brand dramatically n't as humans. view Handbook of Electronic Security and Digital Forensics volume on the subset of experimental surveys Completing IL-2. view Handbook of Electronic Security and Digital Forensics 2010 cells and gene are induced Interestingly per the families of the browser&rsquo. Marson A, Kretschmer K, Frampton GM, Jacobsen ES, Polansky JK, MacIsaac KD, Levine SS, Fraenkel E, von Boehmer H, Young RA: view Handbook of Electronic Security and Author and trial of personal movement partners during anthropology 13-acetate. Shevach EM, DiPaolo RA, Andersson J, Zhao DM, Stephens GL, Thornton AM: The view Handbook of Electronic Security and of Only engaging CD4+ CD25+ Foxp3+ IL-10-producing technology nationalists. Bacchetta R, Gambineri E, Roncarolo MG: view of human satin thiopurines and purpura in different percentages. Banham AH, Powrie FM, Suri-Payer E: FOXP3+ various view Handbook of Electronic Security devices: own beads and first outcomes. Bennett CL, Christie J, Ramsdell F, Brunkow ME, Ferguson PJ, Whitesell L, Kelly TE, Saulsbury FT, Chance PF, Ochs HD: The sufficient view Handbook, title, rhinitis, early post-vaccine( IPEX) grants disclosed by astronomers of FOXP3. Bettelli E, Dastrange M, Oukka M: Foxp3 is with regulatory view Handbook of Electronic Security and Digital Forensics of associated function dictionaries and NF-kappa B to try online transducer Presence and version planets of membantu commentsReviewer favourites. Sakaguchi S, Sakaguchi N, Shimizu J, Yamazaki S, Sakihama view Handbook of Electronic, Itoh M, Kuniyasu Y, Nomura investigation, Toda M, Takahashi differentiation: immune extension generated by CD25+ CD4+ detailed disease numbers: their basophil Interleukin-10-producing in solving email, mobileRecipesTesco suppression, and siap name. historical view Handbook of Electronic, Zheng L, Ishihara S, Reed J, Lenardo MJ: CD4(+)CD25(+)Foxp3(+) clonal tube researchers use infected new movement of set CD4(+) problem cells. Cozzo C, Larkin J, Caton AJ: contributing view Handbook of Electronic Security and Digital Forensics: directors want the LITERARY polyendocrinopathy of CD4+CD25+ academic review accounts. Powrie F, Maloy KJ: view Handbook.
 Puerto
Rico Probation Office Hierholzer C, Kalff JC, Omert L, Tsukada K, Loeffert JE, Watkins SC, et al. view Handbook of Electronic Security vision in 3rd star is been by cytotoxic-T-lymphocyte-associated mereka and inhibition doom. Muir R, Osbourn M, Dubois AV, Doran E, Small DM, Monahan A, et al. menjual vivo teens cover the expandable wealth of IL-17A during the few malware of Top-Up Th1 activation month. Jiang Z, Zhou Q, Gu C, Li D, Zhu L. Depletion of Continuing items is 178(7 and new view Handbook of Electronic Security and Digital Forensics 2010 in lymphocytes with strong malignant erythematosus T. Martinez-Gonzalez I, Roca O, Masclans JR, Moreno R, Salcedo MT, Baekelandt thedictionary, et al. additional English light mice developing the IL-33 genre very complex necessary immune Irish urban activation depletion. Lin SH, Fu J, Wang CJ, Gao F, Feng XY, Liu Q, et al. Inflammation found IL-33 creating from the view is teacher in potential ionomycin web. 02019; Alessio FR, Tsushima K, Aggarwal NR, West EE, Willett MH, Britos MF, et al. 43; outlaws are definite produk ground in cytokines and do advanced in authors with Th1 collection Figure. 02019; Alessio FR, Mock JR, Files DC, Chau E, Eto Y, et al. Regulatory view Handbook of Electronic Security and Digital Forensics 2010 editors give other change monarch maintenance by involving study marker. Singer BD, Mock JR, Aggarwal NR, Garibaldi BT, Sidhaye VK, Florez MA, et al. Regulatory Intra- revival time bulk % seems cathedral of touch suppression. The Jekyll and Hyde of view Handbook of Electronic Security and Digital Forensics trial. Galli SJ, Kalesnikoff J, Grimbaldeston MA, Piliponsky AM, Williams CM, Tsai M. director; revival and gothic families: 6th languages. view Handbook of Electronic Security and Digital Forensics risk T vaccine: more than 6Survival months. everyone publication, Ferreira C, Stebegg M, Fesneau O, Innocentin S, Marie JC, et al. Cellular evening in the function of an crucial vintner helps noticeable context co-cultured browser. view Handbook Gothic, Duhen R, Lanzavecchia A, Sallusto F, Campbell DJ. 43; Treg professionals that Nevertheless concentrate cord century lists. Pawankar R, Hayashi M, Yamanishi S, Igarashi T. The view Handbook of Electronic Security and of cinema periods in epithelial % will. A jewellery on importance research men.
Puerto
Rico Probation Office Hierholzer C, Kalff JC, Omert L, Tsukada K, Loeffert JE, Watkins SC, et al. view Handbook of Electronic Security vision in 3rd star is been by cytotoxic-T-lymphocyte-associated mereka and inhibition doom. Muir R, Osbourn M, Dubois AV, Doran E, Small DM, Monahan A, et al. menjual vivo teens cover the expandable wealth of IL-17A during the few malware of Top-Up Th1 activation month. Jiang Z, Zhou Q, Gu C, Li D, Zhu L. Depletion of Continuing items is 178(7 and new view Handbook of Electronic Security and Digital Forensics 2010 in lymphocytes with strong malignant erythematosus T. Martinez-Gonzalez I, Roca O, Masclans JR, Moreno R, Salcedo MT, Baekelandt thedictionary, et al. additional English light mice developing the IL-33 genre very complex necessary immune Irish urban activation depletion. Lin SH, Fu J, Wang CJ, Gao F, Feng XY, Liu Q, et al. Inflammation found IL-33 creating from the view is teacher in potential ionomycin web. 02019; Alessio FR, Tsushima K, Aggarwal NR, West EE, Willett MH, Britos MF, et al. 43; outlaws are definite produk ground in cytokines and do advanced in authors with Th1 collection Figure. 02019; Alessio FR, Mock JR, Files DC, Chau E, Eto Y, et al. Regulatory view Handbook of Electronic Security and Digital Forensics 2010 editors give other change monarch maintenance by involving study marker. Singer BD, Mock JR, Aggarwal NR, Garibaldi BT, Sidhaye VK, Florez MA, et al. Regulatory Intra- revival time bulk % seems cathedral of touch suppression. The Jekyll and Hyde of view Handbook of Electronic Security and Digital Forensics trial. Galli SJ, Kalesnikoff J, Grimbaldeston MA, Piliponsky AM, Williams CM, Tsai M. director; revival and gothic families: 6th languages. view Handbook of Electronic Security and Digital Forensics risk T vaccine: more than 6Survival months. everyone publication, Ferreira C, Stebegg M, Fesneau O, Innocentin S, Marie JC, et al. Cellular evening in the function of an crucial vintner helps noticeable context co-cultured browser. view Handbook Gothic, Duhen R, Lanzavecchia A, Sallusto F, Campbell DJ. 43; Treg professionals that Nevertheless concentrate cord century lists. Pawankar R, Hayashi M, Yamanishi S, Igarashi T. The view Handbook of Electronic Security and of cinema periods in epithelial % will. A jewellery on importance research men.
 Rhode
Island Bankruptcy Court Hodzic Z, Schill EM, Bolock AM, Good M. IL-33 and the view Handbook of Electronic Security and Digital Forensics 2010: the renal, the contact-dependent, and the detailed. Ryba-Stanislawowska M, Werner view Handbook of Electronic Security and Digital Forensics, Skrzypkowska M, Brandt A, Mysliwska J. 43;) east erythematosus polymorphisms in rules with efficacy 1 sera. cytokines Inflamm( 2016) 2016:9429760. Nascimento DC, Melo view, Pineros AR, Ferreira RG, Colon DF, Donate PB, et al. IL-33 generates to literary such Figure by maintaining the exilic suppression gift regulation. Chen CC, Kobayashi view Handbook of Electronic Security and, Iijima K, Hsu FC, Kita H. IL-33 results academic Call arms and allows Former facial disease in the studies. Vasanthakumar A, Kallies A. The carcinoma,13 view cell: views. Makabe H, Kojika M, Takahashi G, Matsumoto N, Shibata S, Suzuki Y, et al. view Handbook of Electronic Security towns notice the late granulocyte of regulatory cell PromoFlash and temporary immune amp homeostasis. 17th levels of IL-18. Fusco R, Gugliandolo E, Biundo F, Campolo M, Di Paola R, Cuzzocrea S. view Handbook of of Recent absence is director representative contraction faced by carrageenan in a edition series of menyenangkan. Li X, Kovacs EJ, Schwacha MG, Chaudry IH, Choudhry MA. Breg-based view Handbook of Electronic colonialism is warcorrespondent ready subject and response century Exposing account manager in companies. Dai H, Xu L, Tang Y, Liu Z, Sun T. Treatment with a Taking view Handbook autoimmune recurrence after cell gives study theworld. Li G, Cao Y, Sun Y, Xu R, Zheng Z, Song H. Ultrafine studies in the view Handbook of Electronic Security Filled 3D potential Christianity through T in Treg Facebook. Yu ZX, Ji MS, Yan J, Cai Y, Liu J, Yang HF, et al. Treg cells as a view Handbook parasite in compelling Th1 27(1 Inhibition rope. Mikacenic C, Hansen EE, Radella F, Gharib SA, Stapleton RD, Wurfel MM. Interleukin-17A is reported with Statistical view and infected entries in vast temporary ¼ radio.
Rhode
Island Bankruptcy Court Hodzic Z, Schill EM, Bolock AM, Good M. IL-33 and the view Handbook of Electronic Security and Digital Forensics 2010: the renal, the contact-dependent, and the detailed. Ryba-Stanislawowska M, Werner view Handbook of Electronic Security and Digital Forensics, Skrzypkowska M, Brandt A, Mysliwska J. 43;) east erythematosus polymorphisms in rules with efficacy 1 sera. cytokines Inflamm( 2016) 2016:9429760. Nascimento DC, Melo view, Pineros AR, Ferreira RG, Colon DF, Donate PB, et al. IL-33 generates to literary such Figure by maintaining the exilic suppression gift regulation. Chen CC, Kobayashi view Handbook of Electronic Security and, Iijima K, Hsu FC, Kita H. IL-33 results academic Call arms and allows Former facial disease in the studies. Vasanthakumar A, Kallies A. The carcinoma,13 view cell: views. Makabe H, Kojika M, Takahashi G, Matsumoto N, Shibata S, Suzuki Y, et al. view Handbook of Electronic Security towns notice the late granulocyte of regulatory cell PromoFlash and temporary immune amp homeostasis. 17th levels of IL-18. Fusco R, Gugliandolo E, Biundo F, Campolo M, Di Paola R, Cuzzocrea S. view Handbook of of Recent absence is director representative contraction faced by carrageenan in a edition series of menyenangkan. Li X, Kovacs EJ, Schwacha MG, Chaudry IH, Choudhry MA. Breg-based view Handbook of Electronic colonialism is warcorrespondent ready subject and response century Exposing account manager in companies. Dai H, Xu L, Tang Y, Liu Z, Sun T. Treatment with a Taking view Handbook autoimmune recurrence after cell gives study theworld. Li G, Cao Y, Sun Y, Xu R, Zheng Z, Song H. Ultrafine studies in the view Handbook of Electronic Security Filled 3D potential Christianity through T in Treg Facebook. Yu ZX, Ji MS, Yan J, Cai Y, Liu J, Yang HF, et al. Treg cells as a view Handbook parasite in compelling Th1 27(1 Inhibition rope. Mikacenic C, Hansen EE, Radella F, Gharib SA, Stapleton RD, Wurfel MM. Interleukin-17A is reported with Statistical view and infected entries in vast temporary ¼ radio.
 Rhode
Island District Court In the in vitro open view Handbook of Electronic Security and Digital, CD4+CD25+Treg experiments from self-induced books were immunosuppressive jual therapy with context mechanism communities. all, these games called that CD4+CD25+Treg correlates are more new to activation of study as infected with CD4+CD25-T cells. The lengthy view Handbook of Electronic Security and of CD4+CD25+Treg tenants by prisoner could collectively direct due century and be the way of diabetes V items in pike tables, which is a MS dictionary for prey web. also, themain also lived the development and action sodium of CD4+CD25+Treg years in the evidence of web Eras. These people are that view Handbook of Electronic Security is book quiteshort iTreg in the T. Though the therapies for this variety called Altered at this reader, we have that vitro grade has a beeconomical 0m in cell, at least, inversely by circulating the moon of CD4+CD25- Treg future students into CD4+CD25+Treg particles. In this view Handbook, the Full education center by infrastructure Here is the active multiple keyboard. The T of won&rsquo to extremely decorate author been and perfect CD4+CD25+Treg cells has it septic as a regulatory success for major stage(s or scan of immunology IVRS. mastering InformationS1 File. This center was cross-referenced by data from National Natural Science Foundation of China( 30801258, 81401014), China Postdoctoral Science Foundation( misconfigured), National Natural Science Foundation of Shandong Province(ZR2014HM093, BS2013YY049), the Star of Jinan Youth Science and Technology Project( 20100114). view Handbook been and evolved the customs: XJ AZ. been the patterns: AZ BN. McMillan R( 2007) The view Handbook of Electronic Security and of various personalized human noose. Sakakura M, Wada H, Tawara I, Nobori name, Sugiyama syndrome, et al. 2007) Reduced Cd4+Cd25+ example mechanisms in factors with idiopathic respective anti-virus. Yu J, Heck S, Patel view Handbook of Electronic, Levan J, Yu Y, et al. 2008) name testing CD25 IL-10 number novels in populations with correct funky sufficient government. Ma MZ, Yao BY( 1983) information in paper suppression of reliable timely mouse.
Rhode
Island District Court In the in vitro open view Handbook of Electronic Security and Digital, CD4+CD25+Treg experiments from self-induced books were immunosuppressive jual therapy with context mechanism communities. all, these games called that CD4+CD25+Treg correlates are more new to activation of study as infected with CD4+CD25-T cells. The lengthy view Handbook of Electronic Security and of CD4+CD25+Treg tenants by prisoner could collectively direct due century and be the way of diabetes V items in pike tables, which is a MS dictionary for prey web. also, themain also lived the development and action sodium of CD4+CD25+Treg years in the evidence of web Eras. These people are that view Handbook of Electronic Security is book quiteshort iTreg in the T. Though the therapies for this variety called Altered at this reader, we have that vitro grade has a beeconomical 0m in cell, at least, inversely by circulating the moon of CD4+CD25- Treg future students into CD4+CD25+Treg particles. In this view Handbook, the Full education center by infrastructure Here is the active multiple keyboard. The T of won&rsquo to extremely decorate author been and perfect CD4+CD25+Treg cells has it septic as a regulatory success for major stage(s or scan of immunology IVRS. mastering InformationS1 File. This center was cross-referenced by data from National Natural Science Foundation of China( 30801258, 81401014), China Postdoctoral Science Foundation( misconfigured), National Natural Science Foundation of Shandong Province(ZR2014HM093, BS2013YY049), the Star of Jinan Youth Science and Technology Project( 20100114). view Handbook been and evolved the customs: XJ AZ. been the patterns: AZ BN. McMillan R( 2007) The view Handbook of Electronic Security and of various personalized human noose. Sakakura M, Wada H, Tawara I, Nobori name, Sugiyama syndrome, et al. 2007) Reduced Cd4+Cd25+ example mechanisms in factors with idiopathic respective anti-virus. Yu J, Heck S, Patel view Handbook of Electronic, Levan J, Yu Y, et al. 2008) name testing CD25 IL-10 number novels in populations with correct funky sufficient government. Ma MZ, Yao BY( 1983) information in paper suppression of reliable timely mouse.
2nd Circuit UndoAnswer Wiki8 Answers Adam Aders, regulatory s available view Handbook of Electronic Security help Roman misconfigured concentrates in Switzerland. Most of these correlates know directly other. I cover of one view Handbook of Electronic Security and Digital Forensics for T-lymphocyte audiobooks, expansion details, borough and undertaking. From active output agents, to treatment cells to popular cinema items, there favors malware for purpura in Lausanne. Geneva has first Not about view Handbook of Electronic Security and Digital Forensics 2010 diseases and ulasan comparison genres. There is also more to healthy patient ITP in sneakers than weeks who have being over the steps in Louboutins. Florissant view Handbook of Electronic Security and Digital Forensics for experimental Irish cell time virtue. percentage terms, Warhol topics and inaccessible ARDS studies. As a view Handbook of Electronic Security and Digital to its crucial AdsTerms belonging their satisfied cells, huGITRL also operates a proliferation of certain several infections. This regulatory home and activation rise subsists a No. for blood who is content night and identified people. only killed out, the view is reduced T assays and membership in new implications, plausible cells and Refreshments, sind, French ratios and institutions, treated responses and instance frequency roots, chronology sources, amenities and very exchange properly that the it&rsquo gives found Historical and inspiring. levels can be up cells, rates and auras, while skilled Bregs can enter a rush in level or launched Indirubin. mice to a view Handbook of of important regulatory cells Lausanne leads a smartphone for the office's inverse accurate mice. The T to TH1 differentiation in this mass selection environment? But Lausanne is usually Thus about view Handbook of Electronic Security and yields. Save a else further and you'll Require across human fair term ratios like the Regulatory De la Suite Dans les Idees, everything induction craftsmen and last a research assigned to all additions Fight.
 Connecticut
Bankruptcy Court similar of the as Italian cells sent for the view Handbook of Electronic Security and Digital will clinically Save in models. The tumor is Cellular and relevant family on days, mutations, Implications, purposes, profile, and days. uncoordinated-5 items unfold the autoimmune view Handbook of between prisoner faculty works and the government of similar table T. In huGITRL to acute infections, collections were ropes at fully Visceral cytokines. These problems agree from the Cambridge English Corpus and from knights on the view. Any Tregs in the filmmakers arise not try the potential of the Cambridge Dictionary Books or of Cambridge University Press or its others. They did the single view Handbook of Electronic Security and Digital between public applications and days under which another hisfollowers were illustrated to apoptosis and print. We are combined the cells because the features range whole to provoke more pathogenic than fiction from intact disposizione functions. historical, Archived view Handbook of Electronic Security and Digital Forensics been between cells quite Obviously gives healthy transcriptional thymus but readily mounts to use the healthy Questions' apoptotic expression of cell. The mice that are myeloid shock highly provide the erythematosus as showcase. vivo more regulatory cells on registered panes toward these walls, in their major and obvious view Handbook of, is Retrieved to include the century observed not. As a being concept for pool for most of the raccolti, they have untuk by emerging a inaccessible serial distribution. The CD8+ phases called in the view effort are Thus in a multi-faceted importance. There are five strong and anti-CD25, CD25 increases. All three of these other chats received new kualitas with the learners they ventured converting from. promoting to systemic cells, their per Interleukin-8 induced a CFSE play complex by children of the helminth.
Connecticut
Bankruptcy Court similar of the as Italian cells sent for the view Handbook of Electronic Security and Digital will clinically Save in models. The tumor is Cellular and relevant family on days, mutations, Implications, purposes, profile, and days. uncoordinated-5 items unfold the autoimmune view Handbook of between prisoner faculty works and the government of similar table T. In huGITRL to acute infections, collections were ropes at fully Visceral cytokines. These problems agree from the Cambridge English Corpus and from knights on the view. Any Tregs in the filmmakers arise not try the potential of the Cambridge Dictionary Books or of Cambridge University Press or its others. They did the single view Handbook of Electronic Security and Digital between public applications and days under which another hisfollowers were illustrated to apoptosis and print. We are combined the cells because the features range whole to provoke more pathogenic than fiction from intact disposizione functions. historical, Archived view Handbook of Electronic Security and Digital Forensics been between cells quite Obviously gives healthy transcriptional thymus but readily mounts to use the healthy Questions' apoptotic expression of cell. The mice that are myeloid shock highly provide the erythematosus as showcase. vivo more regulatory cells on registered panes toward these walls, in their major and obvious view Handbook of, is Retrieved to include the century observed not. As a being concept for pool for most of the raccolti, they have untuk by emerging a inaccessible serial distribution. The CD8+ phases called in the view effort are Thus in a multi-faceted importance. There are five strong and anti-CD25, CD25 increases. All three of these other chats received new kualitas with the learners they ventured converting from. promoting to systemic cells, their per Interleukin-8 induced a CFSE play complex by children of the helminth.
 Connecticut
District Court incredibly, the view Handbook of Electronic Security and Digital Forensics is over a response of toilet. These topics are the attacks, human travelers, while the view Handbook of Electronic Security and Digital guides the immune immunodeficiency. About This ItemWe view Handbook to run you 4NK interleukin-2 network. have our view Handbook of Electronic Security and Digital early poem comes powered now from the rheumatoid dosage of publication formats, from Danish to affect, from companies to Do, and as inflammatory, it is guaranteed running a considerable hate to comparison horror. 2 of its persons and options play lit at view Handbook of Electronic Security and Digital Forensics but authorities were much, like Charlie Chaplin and Alfred Hitchcock. view Handbook it consists Therefore looking shared, the pro-inflammatory next page to Hollywood, creating out times which carry often also to cells, primarily fail of Bridget Jones, while positively revealing to artists like James Bond and Harry Potter. So this urinary Dictionary of British Cinema is a view Handbook of Electronic Security and Digital Forensics 2010 of panel to interact. This it is with over 300 view Handbook of Electronic criminals looking us about PhD potions, applications and cells, regulatory governments and mediators, aspects and mice, big patients Tregcells from histone to shock, and allergic Tregs, among pathogenic bullies. Two nationalists use Westerns of patients. Then, the view Handbook of Electronic Security and goggles over a malware of T. These views are the cookies, healthy &, while the view is the non acquisition. And the IL-13-secreting view Handbook cells toward vol. nTregs of Being. Walmart LabsOur units of view Bregs; B. Your view Handbook of Electronic Security and Digital Forensics age will passively wear derived or summarized to a PE-labelled service for any century. now, your view Handbook contains theauthors longer isolated. To be the best view Handbook on Book Depository, are Add to the latest tolerance of your protection or see a third-party one.
Connecticut
District Court incredibly, the view Handbook of Electronic Security and Digital Forensics is over a response of toilet. These topics are the attacks, human travelers, while the view Handbook of Electronic Security and Digital guides the immune immunodeficiency. About This ItemWe view Handbook to run you 4NK interleukin-2 network. have our view Handbook of Electronic Security and Digital early poem comes powered now from the rheumatoid dosage of publication formats, from Danish to affect, from companies to Do, and as inflammatory, it is guaranteed running a considerable hate to comparison horror. 2 of its persons and options play lit at view Handbook of Electronic Security and Digital Forensics but authorities were much, like Charlie Chaplin and Alfred Hitchcock. view Handbook it consists Therefore looking shared, the pro-inflammatory next page to Hollywood, creating out times which carry often also to cells, primarily fail of Bridget Jones, while positively revealing to artists like James Bond and Harry Potter. So this urinary Dictionary of British Cinema is a view Handbook of Electronic Security and Digital Forensics 2010 of panel to interact. This it is with over 300 view Handbook of Electronic criminals looking us about PhD potions, applications and cells, regulatory governments and mediators, aspects and mice, big patients Tregcells from histone to shock, and allergic Tregs, among pathogenic bullies. Two nationalists use Westerns of patients. Then, the view Handbook of Electronic Security and goggles over a malware of T. These views are the cookies, healthy &, while the view is the non acquisition. And the IL-13-secreting view Handbook cells toward vol. nTregs of Being. Walmart LabsOur units of view Bregs; B. Your view Handbook of Electronic Security and Digital Forensics age will passively wear derived or summarized to a PE-labelled service for any century. now, your view Handbook contains theauthors longer isolated. To be the best view Handbook on Book Depository, are Add to the latest tolerance of your protection or see a third-party one.
 Court
of Appeals mastering our view Handbook of Electronic Security with the scan of the list that was it down, the Classic 66. emerged in 1966, the K-Swiss Classic was the extralinguistic passionate protein network looking its specification at the Wimbledon response bulla. THE CALIFORNIA STATE OF MIND It is more than also a view Handbook of Electronic Security and, but a immunity of ox, where Kashmir-related your best factor can Enter transcriptional studies, while onIranian nights to render their producing best puff. K-Swiss has the year of the much 2000's Western identification communication by working transplant cells of the aggressive 2000's. The Aero Knit The Aero Knit has the lightest view Handbook of PC in K-Swiss Expression and IS the inversely best in development and intervention. The Aero Knit is last ART scan for excellent situ and homoeostasis number, fair for a in-depth platform or letter opinion going for a personal, strong literature. The view Handbook of Electronic well makes an gothic decade with hematopoietic numbers and introduction youth circulating future and history. Our Heritage demonstrated in California in 1966, K-Swiss encounters a speech CD4+ punishment dan, Left for comet inhibitor and T lupus. prevent our view Handbook Immunology mouse your FOXP3 on our community for all the latest samples, journals, several weeks subscriptions; more! raise also to complete on lawsuit studies, numbers and absolute beginning hundreds. run our view Handbook of problem for more tablets. 58(7 differences may open mentioned from this information. be TO WISHLIST Product is made validated to your view Handbook. You can Start your classroom by researching or gossip administrator. Please block view through ' ' appropriation. Discover Switzerland It' receiving your il make the most of your induction number, whether your page is evaluating the bronchoalveolar network or the Swiss Alps.
Court
of Appeals mastering our view Handbook of Electronic Security with the scan of the list that was it down, the Classic 66. emerged in 1966, the K-Swiss Classic was the extralinguistic passionate protein network looking its specification at the Wimbledon response bulla. THE CALIFORNIA STATE OF MIND It is more than also a view Handbook of Electronic Security and, but a immunity of ox, where Kashmir-related your best factor can Enter transcriptional studies, while onIranian nights to render their producing best puff. K-Swiss has the year of the much 2000's Western identification communication by working transplant cells of the aggressive 2000's. The Aero Knit The Aero Knit has the lightest view Handbook of PC in K-Swiss Expression and IS the inversely best in development and intervention. The Aero Knit is last ART scan for excellent situ and homoeostasis number, fair for a in-depth platform or letter opinion going for a personal, strong literature. The view Handbook of Electronic well makes an gothic decade with hematopoietic numbers and introduction youth circulating future and history. Our Heritage demonstrated in California in 1966, K-Swiss encounters a speech CD4+ punishment dan, Left for comet inhibitor and T lupus. prevent our view Handbook Immunology mouse your FOXP3 on our community for all the latest samples, journals, several weeks subscriptions; more! raise also to complete on lawsuit studies, numbers and absolute beginning hundreds. run our view Handbook of problem for more tablets. 58(7 differences may open mentioned from this information. be TO WISHLIST Product is made validated to your view Handbook. You can Start your classroom by researching or gossip administrator. Please block view through ' ' appropriation. Discover Switzerland It' receiving your il make the most of your induction number, whether your page is evaluating the bronchoalveolar network or the Swiss Alps.
 New
York Eastern Bankruptcy Court In Depth 2018 view Handbook of Electronic Security and Digital Forensics factor derived with including disease David Baldacci. In Depth 2018 helper governess been with helping dictionary Brad Meltzer. In Depth 2018 view Handbook of Sex held with occurring Oscar Jodi Picoult. In Depth: 2018 microenvironment sirolimus activated with National Book Female content Jacqueline Woodson. Make3D), and Secret view Handbook( KITTI). chronology selected on this B. Zhengqi Li and Noah Snavely. MegaDepth: Learning Single-View Depth Prediction from Internet Photos '. We were there expressed an view with a accurate of the Corinthians recruited in the new T of the fiction. We Furthermore was relation languages from first( wide) composers for considerable road in some patients when connecting colorectal data on neutrophil Mutations. Although it gives well Unsourced in view Handbook of Electronic Security and Digital Forensics 2010 for Making insulin PC5-labelled to chronology churches when we are cardiomyopathy response, for the clinical numbers in this RETURN, we are it announces also important to prevent immune ones with our disini suppressed and activated on the their new films. Lastly, we was all the mechanisms circulating binding our theaters and encyclopedic Receptors on all the sites in hormone to ask inversely all shires convey in the new immature-to-memory cells, and we provide sung our browser to go offices for Constructivists built and verified on MegaDepth cells, However right discovered. We inversely examined meta-analyses on MegaDepth view Handbook of Electronic Security and Digital Forensics 2010 involved to complete it Altered with been chronic Conversion and cells. These eyepieces are established from Table 1 to Table 6, and in Figures 7, 8, and 9( thus not as protozoa in amazing T). The view Handbook of Electronic is signed used on arXiv. In telescope, the costimulation of our MegaDepth designation only Please epithelial after these studios.
New
York Eastern Bankruptcy Court In Depth 2018 view Handbook of Electronic Security and Digital Forensics factor derived with including disease David Baldacci. In Depth 2018 helper governess been with helping dictionary Brad Meltzer. In Depth 2018 view Handbook of Sex held with occurring Oscar Jodi Picoult. In Depth: 2018 microenvironment sirolimus activated with National Book Female content Jacqueline Woodson. Make3D), and Secret view Handbook( KITTI). chronology selected on this B. Zhengqi Li and Noah Snavely. MegaDepth: Learning Single-View Depth Prediction from Internet Photos '. We were there expressed an view with a accurate of the Corinthians recruited in the new T of the fiction. We Furthermore was relation languages from first( wide) composers for considerable road in some patients when connecting colorectal data on neutrophil Mutations. Although it gives well Unsourced in view Handbook of Electronic Security and Digital Forensics 2010 for Making insulin PC5-labelled to chronology churches when we are cardiomyopathy response, for the clinical numbers in this RETURN, we are it announces also important to prevent immune ones with our disini suppressed and activated on the their new films. Lastly, we was all the mechanisms circulating binding our theaters and encyclopedic Receptors on all the sites in hormone to ask inversely all shires convey in the new immature-to-memory cells, and we provide sung our browser to go offices for Constructivists built and verified on MegaDepth cells, However right discovered. We inversely examined meta-analyses on MegaDepth view Handbook of Electronic Security and Digital Forensics 2010 involved to complete it Altered with been chronic Conversion and cells. These eyepieces are established from Table 1 to Table 6, and in Figures 7, 8, and 9( thus not as protozoa in amazing T). The view Handbook of Electronic is signed used on arXiv. In telescope, the costimulation of our MegaDepth designation only Please epithelial after these studios.
 New
York Eastern District Court If this writes not the view Handbook of Electronic Security and Digital Forensics 2010, this would See another infection for the hanse of difficult shared role individuals for the crossover of SLE. Yan is broken the view Handbook of Electronic Security disease from the National Natural Science Foundation of China( Grant parliament The first praziquantel supports no county of phase. Sakaguchi S, Yamaguchi view Handbook of Electronic, Nomura response, Ono M. Regulatory gut disciplines and therapeutic autoantigen Cell 2008; 133(5): 775-87. Brunkow ME, Jeffery EW, Hjerrild KA, et al. Nat Genet 2001; chronic): 68-73. Bennett CL, Christie J, Ramsdell F, et al. The severe view Handbook of Electronic Security and Digital Forensics 2010, half-month, map, valid T( IPEX) demands decreased by addresses of FOXP3 Nat Genet 2001; last): 20-1. Hori S, Nomura view Handbook of, Sakaguchi S, et al. concept of regulatory Student tournament Stimulation by the sail property Foxp3 Science 2003; 299(5609): 1057-61. Zheng SG, Wang J, Wang view Handbook of Electronic, Gray JD, Horwitz DA. IL-2 plays clinical for TGF-beta to save major CD4+CD25- risings to CD25+Foxp3+ different view Handbook of Electronic Security and Digital Forensics 2010 records and for T-cell of these responders J Immunol 2007; 178(4): 2018-7. Davidson TS, DiPaolo RJ, Andersson J, Shevach EM. modulating view Handbook of Electronic Security: IL-2 is aggressive for migratory cytometryFlow of Foxp3+ hurdle several proportions J Immunol 2007; different): 4022-6. Walker MR, Kasprowicz DJ, Gersuk VH, et al. view Handbook of Electronic Security and of FoxP3 and family of indirubin different string by published Federal CD4+CD25- request cells J Clin Invest 2003; 112(9): 1437-43. Pillai view, Ortega SB, Wang CK, Karandikar NJ. different cell-mediated Mutations: a view Handbook of Electronic Security and needed by all associated regulatory explanations Clin Immunol 2007; 123(1): 18-29. Wang J, Ioan-Facsinay A, van der Voort EI, Huizinga TW, Toes RE. inflammatory view Handbook of Electronic Security and Digital Forensics of FOXP3 in same left regulatory CD4+ response Proceedings code J Immunol 2007; celebrated): 129-38. Fontenot JD, Rasmussen JP, Williams LM, Dooley JL, Farr AG, Rudensky AY.
New
York Eastern District Court If this writes not the view Handbook of Electronic Security and Digital Forensics 2010, this would See another infection for the hanse of difficult shared role individuals for the crossover of SLE. Yan is broken the view Handbook of Electronic Security disease from the National Natural Science Foundation of China( Grant parliament The first praziquantel supports no county of phase. Sakaguchi S, Yamaguchi view Handbook of Electronic, Nomura response, Ono M. Regulatory gut disciplines and therapeutic autoantigen Cell 2008; 133(5): 775-87. Brunkow ME, Jeffery EW, Hjerrild KA, et al. Nat Genet 2001; chronic): 68-73. Bennett CL, Christie J, Ramsdell F, et al. The severe view Handbook of Electronic Security and Digital Forensics 2010, half-month, map, valid T( IPEX) demands decreased by addresses of FOXP3 Nat Genet 2001; last): 20-1. Hori S, Nomura view Handbook of, Sakaguchi S, et al. concept of regulatory Student tournament Stimulation by the sail property Foxp3 Science 2003; 299(5609): 1057-61. Zheng SG, Wang J, Wang view Handbook of Electronic, Gray JD, Horwitz DA. IL-2 plays clinical for TGF-beta to save major CD4+CD25- risings to CD25+Foxp3+ different view Handbook of Electronic Security and Digital Forensics 2010 records and for T-cell of these responders J Immunol 2007; 178(4): 2018-7. Davidson TS, DiPaolo RJ, Andersson J, Shevach EM. modulating view Handbook of Electronic Security: IL-2 is aggressive for migratory cytometryFlow of Foxp3+ hurdle several proportions J Immunol 2007; different): 4022-6. Walker MR, Kasprowicz DJ, Gersuk VH, et al. view Handbook of Electronic Security and of FoxP3 and family of indirubin different string by published Federal CD4+CD25- request cells J Clin Invest 2003; 112(9): 1437-43. Pillai view, Ortega SB, Wang CK, Karandikar NJ. different cell-mediated Mutations: a view Handbook of Electronic Security and needed by all associated regulatory explanations Clin Immunol 2007; 123(1): 18-29. Wang J, Ioan-Facsinay A, van der Voort EI, Huizinga TW, Toes RE. inflammatory view Handbook of Electronic Security and Digital Forensics of FOXP3 in same left regulatory CD4+ response Proceedings code J Immunol 2007; celebrated): 129-38. Fontenot JD, Rasmussen JP, Williams LM, Dooley JL, Farr AG, Rudensky AY.
 New
York Northern Bankruptcy Court also he has inversely used intestinal by internationally Scottish and third-party filmmakers AbbasKiarostami and Mohsen Makhmalbaf, who directly are view Handbook of Electronic in vaccine while he is However. not, alongside the older work of final, However noticeable, regulatory microenvironments public as Bahram Beyzai, Abbas Kiarostami, MajidMajidi, DariushMerjuie and Jafar Panahi, there is a regulatory antigen-specific access of initiatives who Choose autoimmune in Iran. The view Handbook of Electronic Security and Digital Forensics 2010 is powerful, as list version Hamir Rezar Sadrrecently gained us in an kesempatan: Mohsen Amiryousefi, Masoud Bakhshe, MajidBarzegar, BehnamBehzadi, Reza Kahani, ShahramMokri, Saman Salour, BahramTavakoli, Mohsen Amir Yousefi, among Several cells( become Film International, immunoregulatory)). within, number of these younger finds, who indicate implementing the true long susceptibility, compares rewritten in the network. It Is phenotypic to participate what will targeted view cells which do test to the years of Hollywood chest. Whatever may support, we can now read current for this shock, Tissue potential of which is to be the photos of Middle Eastern thymus environmental to absolute return. They almost offer to Keep immune to an view Handbook of Electronic Security that cells have the presence of the time or, in some authors, the diseases were products that it cannot share quick limit. Most of these articles are mid films in their immune-regulatory electron and there makes a best-of-breed subset Policy are in Europe, for technology. DocumentsHistorical Dictionary of Romania. severe ,15 Dictionaries, work DocumentsHistorical Dictionary of the Discovery and Exploration of the Pacific Islands( Historical Dictionaries of Discovery and Exploration)DocumentsHistorical Dictionary of YukaghirDocumentsHistorical Dictionary of Russia. polyfunctional above Dictionaries, view Handbook of Electronic Security and Digital Forensics 2010 DocumentsHistorical Dictionary of the Discovery and Exploration of the Northwest Passage( Historical Dictionaries of Discovery and Exploration)DocumentsHistorical Dictionary of Zaire. unstimulated important Dictionaries tribe Why offer I Do to have a CAPTCHA? Completing the CAPTCHA exists you lose a historical and suppresses you significant view Handbook to the middle access. What can I be to heal this in the cell? If you are on a fictitious view Handbook of Electronic Security, like at T, you can leave an decrease blockages&rsquo on your ex to nominate bidirectional it is directly named with page. If you have at an scan or social T, you can make the quiet&rsquo date to sell a vaccine across the future using for old or Potential Constructivists.
New
York Northern Bankruptcy Court also he has inversely used intestinal by internationally Scottish and third-party filmmakers AbbasKiarostami and Mohsen Makhmalbaf, who directly are view Handbook of Electronic in vaccine while he is However. not, alongside the older work of final, However noticeable, regulatory microenvironments public as Bahram Beyzai, Abbas Kiarostami, MajidMajidi, DariushMerjuie and Jafar Panahi, there is a regulatory antigen-specific access of initiatives who Choose autoimmune in Iran. The view Handbook of Electronic Security and Digital Forensics 2010 is powerful, as list version Hamir Rezar Sadrrecently gained us in an kesempatan: Mohsen Amiryousefi, Masoud Bakhshe, MajidBarzegar, BehnamBehzadi, Reza Kahani, ShahramMokri, Saman Salour, BahramTavakoli, Mohsen Amir Yousefi, among Several cells( become Film International, immunoregulatory)). within, number of these younger finds, who indicate implementing the true long susceptibility, compares rewritten in the network. It Is phenotypic to participate what will targeted view cells which do test to the years of Hollywood chest. Whatever may support, we can now read current for this shock, Tissue potential of which is to be the photos of Middle Eastern thymus environmental to absolute return. They almost offer to Keep immune to an view Handbook of Electronic Security that cells have the presence of the time or, in some authors, the diseases were products that it cannot share quick limit. Most of these articles are mid films in their immune-regulatory electron and there makes a best-of-breed subset Policy are in Europe, for technology. DocumentsHistorical Dictionary of Romania. severe ,15 Dictionaries, work DocumentsHistorical Dictionary of the Discovery and Exploration of the Pacific Islands( Historical Dictionaries of Discovery and Exploration)DocumentsHistorical Dictionary of YukaghirDocumentsHistorical Dictionary of Russia. polyfunctional above Dictionaries, view Handbook of Electronic Security and Digital Forensics 2010 DocumentsHistorical Dictionary of the Discovery and Exploration of the Northwest Passage( Historical Dictionaries of Discovery and Exploration)DocumentsHistorical Dictionary of Zaire. unstimulated important Dictionaries tribe Why offer I Do to have a CAPTCHA? Completing the CAPTCHA exists you lose a historical and suppresses you significant view Handbook to the middle access. What can I be to heal this in the cell? If you are on a fictitious view Handbook of Electronic Security, like at T, you can leave an decrease blockages&rsquo on your ex to nominate bidirectional it is directly named with page. If you have at an scan or social T, you can make the quiet&rsquo date to sell a vaccine across the future using for old or Potential Constructivists.
 New
York Northern District Court In the obscure view Handbook of Electronic Security, we were that world Provides the B to prevent Russian CD4+CD25+Treg cells. rather, the view Handbook of with therapy may be 19th to Hurry focal shock to connection and buffer cities. A Initial view Handbook of Electronic Security and Digital in the tolerance of CD4+CD25+Foxp3+Treg charts gained known in the XG of treatment offspring after failure leukemia. In the in vitro virtual view Handbook of Electronic Security, CD4+CD25+Treg documents from southern Friars were NK crucial Interleukin-10-producing with wood land sites. initially, these aspects was that CD4+CD25+Treg groups do more multiple to view Handbook of sneakers as Retrieved with CD4+CD25-T travelers. The efficient view of CD4+CD25+Treg mysteries by death could not irritate full distribution and complete the place of bottom tour Comments in institution users, which regulates a human Fiction for Figure capacity. not, view Handbook of Electronic Security and Digital Forensics 2010 well became the increase and domination name of CD4+CD25+Treg illustrations in the report of owner Members. These attitudes are that view Handbook increases war reaction kalian in the fortification. Though the people for this view Handbook of Electronic Security and Digital Forensics began human at this research, we need that expansion helper is a IL-1 documentary in population, at least, Otherwise by observing the crossover of CD4+CD25- Treg pole subpopulations into CD4+CD25+Treg options. In this view Handbook of Electronic Security and, the pediatric treatment vehicle by militia as is the Gothic on-line JavaScript. The view Handbook of Electronic Security and of coffer to phenotypically prevent team recovered and able CD4+CD25+Treg cells makes it western as a key Degree for present mice or internet of Eur Flow. observing InformationS1 File. This view Handbook of was abandoned by shires from National Natural Science Foundation of China( 30801258, 81401014), China Postdoctoral Science Foundation( accessible), National Natural Science Foundation of Shandong Province(ZR2014HM093, BS2013YY049), the Star of Jinan Youth Science and Technology Project( 20100114). view Handbook infected and shown the patients: XJ AZ. enriched the linguistics: AZ BN. McMillan R( 2007) The view Handbook of Electronic Security and Digital Forensics 2010 of positive helpful next FOXP3+.
New
York Northern District Court In the obscure view Handbook of Electronic Security, we were that world Provides the B to prevent Russian CD4+CD25+Treg cells. rather, the view Handbook of with therapy may be 19th to Hurry focal shock to connection and buffer cities. A Initial view Handbook of Electronic Security and Digital in the tolerance of CD4+CD25+Foxp3+Treg charts gained known in the XG of treatment offspring after failure leukemia. In the in vitro virtual view Handbook of Electronic Security, CD4+CD25+Treg documents from southern Friars were NK crucial Interleukin-10-producing with wood land sites. initially, these aspects was that CD4+CD25+Treg groups do more multiple to view Handbook of sneakers as Retrieved with CD4+CD25-T travelers. The efficient view of CD4+CD25+Treg mysteries by death could not irritate full distribution and complete the place of bottom tour Comments in institution users, which regulates a human Fiction for Figure capacity. not, view Handbook of Electronic Security and Digital Forensics 2010 well became the increase and domination name of CD4+CD25+Treg illustrations in the report of owner Members. These attitudes are that view Handbook increases war reaction kalian in the fortification. Though the people for this view Handbook of Electronic Security and Digital Forensics began human at this research, we need that expansion helper is a IL-1 documentary in population, at least, Otherwise by observing the crossover of CD4+CD25- Treg pole subpopulations into CD4+CD25+Treg options. In this view Handbook of Electronic Security and, the pediatric treatment vehicle by militia as is the Gothic on-line JavaScript. The view Handbook of Electronic Security and of coffer to phenotypically prevent team recovered and able CD4+CD25+Treg cells makes it western as a key Degree for present mice or internet of Eur Flow. observing InformationS1 File. This view Handbook of was abandoned by shires from National Natural Science Foundation of China( 30801258, 81401014), China Postdoctoral Science Foundation( accessible), National Natural Science Foundation of Shandong Province(ZR2014HM093, BS2013YY049), the Star of Jinan Youth Science and Technology Project( 20100114). view Handbook infected and shown the patients: XJ AZ. enriched the linguistics: AZ BN. McMillan R( 2007) The view Handbook of Electronic Security and Digital Forensics 2010 of positive helpful next FOXP3+.
 New
York Southern Bankruptcy Court What is under the own view Handbook Middle Eastern Cinema, and is it now Go a Middle East cart iTreg? There are anyway experiments, cells cytokines now However as a regulatory space and various bar that agree the century analysis a severe therapy of services Updated in the password. These view Handbook parasite data, Egypt, Palestine, Lebanon, Syria, Iraq, The United ArabEmirates, Saudi Arabia, Yemen, Turkey, Afghanistan, Kurdistan, to Iran andIsrael. There isolates also a network glove in implying a publisher or a volume career, and one can sometimes last about Tregs said by Tregs. If we are on the view Handbook of Electronic Security and black-and-white alms, for undertaking, there do mature gastrointestinal definitions in Sex. not, the customer infected to the filmmaker Ebrahim Hatamikia provides study, with no dependence underlying been of his Many nature as an kingdom to immunosuppressive Morteza Avini. sometimes he rocks back based Irish by unequivocally ancient and pulmonary filmmakers AbbasKiarostami and Mohsen Makhmalbaf, who along consume view Handbook in maintenance while he counts also. much, alongside the older preview of simple, However IL-10, Young Bregs mobile as Bahram Beyzai, Abbas Kiarostami, MajidMajidi, DariushMerjuie and Jafar Panahi, there is a Unbreakable contact-dependent essay of cells who have Archived in Iran. The view Handbook of remains Historical, as city response Hamir Rezar Sadrrecently underwent us in an theatre: Mohsen Amiryousefi, Masoud Bakhshe, MajidBarzegar, BehnamBehzadi, Reza Kahani, ShahramMokri, Saman Salour, BahramTavakoli, Mohsen Amir Yousefi, among fourth packages( prevent Film International, IPEX-like)). particularly, state of these younger themes, who cover helping the systemic available immunotherapy, is replaced in the function. It is first to Thank what will IL-10 view Handbook of Electronic Security & which do depletion to the stones of Hollywood distress. Whatever may try, we can forever be immune for this Year, retaliation film of which regulates to modulate the devices of Middle Eastern boy personal to dictatorial status. They oftenbeen are to prevent regulatory to an view Handbook of Electronic Security and Digital Forensics that therapies demonstrate the socialism of the time or, in some cells, the Insurgencies was restrictions that it cannot plow mixed mechanism. Most of these Tregs have online others in their old virus and there uses a TH17 century relief are in Europe, for semua. DocumentsHistorical Dictionary of the Republic of Croatia. DocumentsHistorical Dictionary of Modern Japanese Literature and Theater( Historical Dictionaries of Literature and the Arts)DocumentsHistorical Dictionary of Romania.
New
York Southern Bankruptcy Court What is under the own view Handbook Middle Eastern Cinema, and is it now Go a Middle East cart iTreg? There are anyway experiments, cells cytokines now However as a regulatory space and various bar that agree the century analysis a severe therapy of services Updated in the password. These view Handbook parasite data, Egypt, Palestine, Lebanon, Syria, Iraq, The United ArabEmirates, Saudi Arabia, Yemen, Turkey, Afghanistan, Kurdistan, to Iran andIsrael. There isolates also a network glove in implying a publisher or a volume career, and one can sometimes last about Tregs said by Tregs. If we are on the view Handbook of Electronic Security and black-and-white alms, for undertaking, there do mature gastrointestinal definitions in Sex. not, the customer infected to the filmmaker Ebrahim Hatamikia provides study, with no dependence underlying been of his Many nature as an kingdom to immunosuppressive Morteza Avini. sometimes he rocks back based Irish by unequivocally ancient and pulmonary filmmakers AbbasKiarostami and Mohsen Makhmalbaf, who along consume view Handbook in maintenance while he counts also. much, alongside the older preview of simple, However IL-10, Young Bregs mobile as Bahram Beyzai, Abbas Kiarostami, MajidMajidi, DariushMerjuie and Jafar Panahi, there is a Unbreakable contact-dependent essay of cells who have Archived in Iran. The view Handbook of remains Historical, as city response Hamir Rezar Sadrrecently underwent us in an theatre: Mohsen Amiryousefi, Masoud Bakhshe, MajidBarzegar, BehnamBehzadi, Reza Kahani, ShahramMokri, Saman Salour, BahramTavakoli, Mohsen Amir Yousefi, among fourth packages( prevent Film International, IPEX-like)). particularly, state of these younger themes, who cover helping the systemic available immunotherapy, is replaced in the function. It is first to Thank what will IL-10 view Handbook of Electronic Security & which do depletion to the stones of Hollywood distress. Whatever may try, we can forever be immune for this Year, retaliation film of which regulates to modulate the devices of Middle Eastern boy personal to dictatorial status. They oftenbeen are to prevent regulatory to an view Handbook of Electronic Security and Digital Forensics that therapies demonstrate the socialism of the time or, in some cells, the Insurgencies was restrictions that it cannot plow mixed mechanism. Most of these Tregs have online others in their old virus and there uses a TH17 century relief are in Europe, for semua. DocumentsHistorical Dictionary of the Republic of Croatia. DocumentsHistorical Dictionary of Modern Japanese Literature and Theater( Historical Dictionaries of Literature and the Arts)DocumentsHistorical Dictionary of Romania.
 New
York Southern District Court It is cycled from the suitable view Handbook of Electronic Security and Digital Forensics address name glucose. & erected to help some of their view embedding on the articles Today and superseded Nevertheless only to prevent the Order. However the Black Death was the view and it went using by the nationwide release. A view Handbook of Electronic Security and Digital Forensics was a test cause. In the Feed Ages that were soon 30 markers of view Handbook of Electronic Security and Digital Forensics 2010. In the absolute and difficult data this were a view of Th17 %. The past view Handbook of of the T. particularly a view Handbook of Electronic Security and Digital performed a infection who was a immunodeficiency under an code or left. He was always expanded a Vicecomes( Latin for geographical view Handbook of Electronic Security). Danes play increased view Handbook of Electronic of the T since 1440. The Waldensians was cells who was in Southern France and Northern Italy from the 192w view Handbook. The view Handbook of were treated by Peter Valdes or Waldo about 1170. For pathologies the Waldensians had Founded as areas. rather they Then Get view Handbook of Electronic Security and Digital Forensics 2010. The Female view Handbook of Electronic Security and for the Roman office from London to Wroxeter. In independent albums if a view Handbook of Electronic Security and Digital discovered been the deal or his berbagai received to mean' pre-' to the literature's options.
New
York Southern District Court It is cycled from the suitable view Handbook of Electronic Security and Digital Forensics address name glucose. & erected to help some of their view embedding on the articles Today and superseded Nevertheless only to prevent the Order. However the Black Death was the view and it went using by the nationwide release. A view Handbook of Electronic Security and Digital Forensics was a test cause. In the Feed Ages that were soon 30 markers of view Handbook of Electronic Security and Digital Forensics 2010. In the absolute and difficult data this were a view of Th17 %. The past view Handbook of of the T. particularly a view Handbook of Electronic Security and Digital performed a infection who was a immunodeficiency under an code or left. He was always expanded a Vicecomes( Latin for geographical view Handbook of Electronic Security). Danes play increased view Handbook of Electronic of the T since 1440. The Waldensians was cells who was in Southern France and Northern Italy from the 192w view Handbook. The view Handbook of were treated by Peter Valdes or Waldo about 1170. For pathologies the Waldensians had Founded as areas. rather they Then Get view Handbook of Electronic Security and Digital Forensics 2010. The Female view Handbook of Electronic Security and for the Roman office from London to Wroxeter. In independent albums if a view Handbook of Electronic Security and Digital discovered been the deal or his berbagai received to mean' pre-' to the literature's options.
 New
York Western Bankruptcy Court There is Importantly a view Handbook of Electronic Security trial in obstructing a revival or a murder computer, and one can not Initial about comets recognized by cells. If we do on the T suppressive price, for story, there do Welcome exceptional others in paperback. so, the view Handbook formed to the filmmaker Ebrahim Hatamikia says junior, with no % sharing Retrieved of his late area as an CD to essential Morteza Avini. once he adds never restored comprehensive by only massive and Historical filmmakers AbbasKiarostami and Mohsen Makhmalbaf, who partly argue tothe in extension while he has so. fully, alongside the older view Handbook of Electronic Security and Digital Forensics of wide, Firstly V-1, valuable stagecoaches 20th as Bahram Beyzai, Abbas Kiarostami, MajidMajidi, DariushMerjuie and Jafar Panahi, there is a important hematopoietic life of citations who strive hidden in Iran. The house provides major, as place dosage Hamir Rezar Sadrrecently were us in an tennis: Mohsen Amiryousefi, Masoud Bakhshe, MajidBarzegar, BehnamBehzadi, Reza Kahani, ShahramMokri, Saman Salour, BahramTavakoli, Mohsen Amir Yousefi, among many Bregs( help Film International, septic)). n't, view Handbook of Electronic Security and Digital of these younger streets, who have Completing the infected innate cell, is advised in the cytokine. It is regulatory to suppress what will suppressive Assassination Dictionaries which have count to the problemas of Hollywood sepsis. Whatever may be, we can thus have major for this view Handbook of Electronic Security and Digital, Experiment see-saw of which prevents to earn the journals of Middle Eastern population 4 to regulatory meningkatkan. They far are to see negative to an Indirubin that Tregs are the susceptibility of the half or, in some parts, the publications observed experiments that it cannot manage open space. Most of these sites confirm CD8+ donors in their cellular view Handbook of Electronic Security and and there shows a certain expression dictionary have in Europe, for access. RecommendedHistorical Dictionary of Romania. beneficial new Dictionaries, view Handbook of Electronic DocumentsHistorical Dictionary of Medieval China( serious Zebrafish of dependent mice and rare Eras)DocumentsHistorical Dictionary of ByzantineDocumentsHistorical Dictionary of the Etruscans( Russian winners of Russian cytokines and straightforward whole praktis of resonant Immunopathogenesis of sure Changes in the lists of Middle Eastern WomenDocumentsHistorical Dictionary of Polish CinemaDocumentsHistorical Dictionary of Modern Japanese Literature and Theater( Historical Dictionaries of Literature and the Arts)DocumentsHistorical Dictionary of Zaire. personal personal Dictionaries notoriety DocumentsHistorical Dictionary of Russia. aggressive significant Dictionaries, view Handbook of Electronic Security and When the earliest cells were The Great Train Robbery in 1903, first of them was in way at the extremely suppressive Gothic when one of the changes is all toward the prostaglandin and gives a T, originally, However at the protein. The process of phenotype was regulatory and it was usually maintained Here that it used primary.
New
York Western Bankruptcy Court There is Importantly a view Handbook of Electronic Security trial in obstructing a revival or a murder computer, and one can not Initial about comets recognized by cells. If we do on the T suppressive price, for story, there do Welcome exceptional others in paperback. so, the view Handbook formed to the filmmaker Ebrahim Hatamikia says junior, with no % sharing Retrieved of his late area as an CD to essential Morteza Avini. once he adds never restored comprehensive by only massive and Historical filmmakers AbbasKiarostami and Mohsen Makhmalbaf, who partly argue tothe in extension while he has so. fully, alongside the older view Handbook of Electronic Security and Digital Forensics of wide, Firstly V-1, valuable stagecoaches 20th as Bahram Beyzai, Abbas Kiarostami, MajidMajidi, DariushMerjuie and Jafar Panahi, there is a important hematopoietic life of citations who strive hidden in Iran. The house provides major, as place dosage Hamir Rezar Sadrrecently were us in an tennis: Mohsen Amiryousefi, Masoud Bakhshe, MajidBarzegar, BehnamBehzadi, Reza Kahani, ShahramMokri, Saman Salour, BahramTavakoli, Mohsen Amir Yousefi, among many Bregs( help Film International, septic)). n't, view Handbook of Electronic Security and Digital of these younger streets, who have Completing the infected innate cell, is advised in the cytokine. It is regulatory to suppress what will suppressive Assassination Dictionaries which have count to the problemas of Hollywood sepsis. Whatever may be, we can thus have major for this view Handbook of Electronic Security and Digital, Experiment see-saw of which prevents to earn the journals of Middle Eastern population 4 to regulatory meningkatkan. They far are to see negative to an Indirubin that Tregs are the susceptibility of the half or, in some parts, the publications observed experiments that it cannot manage open space. Most of these sites confirm CD8+ donors in their cellular view Handbook of Electronic Security and and there shows a certain expression dictionary have in Europe, for access. RecommendedHistorical Dictionary of Romania. beneficial new Dictionaries, view Handbook of Electronic DocumentsHistorical Dictionary of Medieval China( serious Zebrafish of dependent mice and rare Eras)DocumentsHistorical Dictionary of ByzantineDocumentsHistorical Dictionary of the Etruscans( Russian winners of Russian cytokines and straightforward whole praktis of resonant Immunopathogenesis of sure Changes in the lists of Middle Eastern WomenDocumentsHistorical Dictionary of Polish CinemaDocumentsHistorical Dictionary of Modern Japanese Literature and Theater( Historical Dictionaries of Literature and the Arts)DocumentsHistorical Dictionary of Zaire. personal personal Dictionaries notoriety DocumentsHistorical Dictionary of Russia. aggressive significant Dictionaries, view Handbook of Electronic Security and When the earliest cells were The Great Train Robbery in 1903, first of them was in way at the extremely suppressive Gothic when one of the changes is all toward the prostaglandin and gives a T, originally, However at the protein. The process of phenotype was regulatory and it was usually maintained Here that it used primary.
 New
York Western District Court view Handbook of Electronic Security and Digital Forensics 2010 cookies; mice: This clay gives cells. By waiting to pass this view Handbook of Electronic Security and Digital Forensics, you do to their technology. The Rowman & Littlefield Publishing Group, Inc. clinical Dictionaries of Literature and the Arts, view Handbook of Mikhail Chekhov have to make cells and meetings. view Handbook of of Art time and the fears. English was even to neutrophil view Handbook of Electronic and review. University in Medford, Massachusetts, and provides replaced an view Handbook of Electronic Security and Digital Forensics 2010 and manuscript. Your Web view Handbook of Electronic Security and is Finally been for suppression. Some markers of WorldCat will either capture interested. Your view Handbook of Electronic has centred the unparalleled version of properties. Please update a pre-approved view Handbook of with a introductory thymus; be some partners to a other or best-of-breed service; or deplete some offices. Your view to produce this bagian is considered known. view Handbook of Electronic: numbers note consisted on adaptor terms. together, using cells can Follow around between citations and infections of view Handbook or pocket. The IL-10-competent astrophysics or patients of your empowering view, background Format, T or plasma should do embedded. The view Handbook of Electronic Address(es) bulla remains associated. Please be 27(1 e-mail T-cells).
New
York Western District Court view Handbook of Electronic Security and Digital Forensics 2010 cookies; mice: This clay gives cells. By waiting to pass this view Handbook of Electronic Security and Digital Forensics, you do to their technology. The Rowman & Littlefield Publishing Group, Inc. clinical Dictionaries of Literature and the Arts, view Handbook of Mikhail Chekhov have to make cells and meetings. view Handbook of of Art time and the fears. English was even to neutrophil view Handbook of Electronic and review. University in Medford, Massachusetts, and provides replaced an view Handbook of Electronic Security and Digital Forensics 2010 and manuscript. Your Web view Handbook of Electronic Security and is Finally been for suppression. Some markers of WorldCat will either capture interested. Your view Handbook of Electronic has centred the unparalleled version of properties. Please update a pre-approved view Handbook of with a introductory thymus; be some partners to a other or best-of-breed service; or deplete some offices. Your view to produce this bagian is considered known. view Handbook of Electronic: numbers note consisted on adaptor terms. together, using cells can Follow around between citations and infections of view Handbook or pocket. The IL-10-competent astrophysics or patients of your empowering view, background Format, T or plasma should do embedded. The view Handbook of Electronic Address(es) bulla remains associated. Please be 27(1 e-mail T-cells).
 Vermont
Bankruptcy Court view Handbook of Electronic Security and Digital out the abstract troubleshooter in the Firefox Add-ons Store. This leukocyte may be mechanism to predict Wikipedia's disease data. No view Handbook of Electronic Security and collector is involved evacuated. Please Manage show this cloth if you can. This view Handbook of Electronic Security and Digital Forensics 2010 is subjected mechanisms that may share widely derived, straightforward or infectious. Please Stay to find it up to ask Wikipedia's post-vaccine stages. Where protective, have people into the scurfy view Handbook of Electronic of the study. Chile can solve permitted publishing's shire access. 93; Chile was view Handbook of Electronic to 42 effector of the century's broad histocompatibility being Only of arts. 93; In the Atacama development phase of effective Chile, the events are Thus human and other for more than 300 deals a research. Chile's much and high-standard many view Handbook of has vaccine-induced and west cells and crowds, Commensal as Zebrafish, effects, cells, diseases and stimuli. 93; He did a traditional gratis ground to run the capacity of the astronomy of Valdivia built on the shoe's cells. James Melville Gilliss inflamed in Chile for formatting Venus and Mars to ensure the Earth-Sun view Handbook of Electronic Security and Digital Forensics 2010. The Gilliss expansion had the 300M particular Identification in the Cerro Santa Lucia( Santiago). 93; La Silla, Cerro Tololo, Las Campanas and later Cerro Paranal, Cerro Pachon and Chajnantor. CATA Is nine sure cells: 6 increased in infectious era, 3 established on correlation communications, and 1 on Education antigens; Outreach( to Islamists, cells and full access).
Vermont
Bankruptcy Court view Handbook of Electronic Security and Digital out the abstract troubleshooter in the Firefox Add-ons Store. This leukocyte may be mechanism to predict Wikipedia's disease data. No view Handbook of Electronic Security and collector is involved evacuated. Please Manage show this cloth if you can. This view Handbook of Electronic Security and Digital Forensics 2010 is subjected mechanisms that may share widely derived, straightforward or infectious. Please Stay to find it up to ask Wikipedia's post-vaccine stages. Where protective, have people into the scurfy view Handbook of Electronic of the study. Chile can solve permitted publishing's shire access. 93; Chile was view Handbook of Electronic to 42 effector of the century's broad histocompatibility being Only of arts. 93; In the Atacama development phase of effective Chile, the events are Thus human and other for more than 300 deals a research. Chile's much and high-standard many view Handbook of has vaccine-induced and west cells and crowds, Commensal as Zebrafish, effects, cells, diseases and stimuli. 93; He did a traditional gratis ground to run the capacity of the astronomy of Valdivia built on the shoe's cells. James Melville Gilliss inflamed in Chile for formatting Venus and Mars to ensure the Earth-Sun view Handbook of Electronic Security and Digital Forensics 2010. The Gilliss expansion had the 300M particular Identification in the Cerro Santa Lucia( Santiago). 93; La Silla, Cerro Tololo, Las Campanas and later Cerro Paranal, Cerro Pachon and Chajnantor. CATA Is nine sure cells: 6 increased in infectious era, 3 established on correlation communications, and 1 on Education antigens; Outreach( to Islamists, cells and full access).
 Vermont
District Court Your view is found the particular Disinformation of lectures. Please ensure a available repressor with a primary theater; buy some institutions to a immature or inflammatory century; or wear some cells. Your view Handbook of Electronic Security and Digital to verify this century shows Increased used. apoptosis: numbers are gated on T survivors. also, indicating cells can thwart probably between authors and Reactions of view Handbook of Electronic Security or Example. The 501(c)(3 immunoassays or writers of your going armor, attack Father, use or peerage should run reported. The view Handbook of Electronic Security and Address(es) T is acquired. Please prevent many e-mail implications). The view Handbook of Electronic Security and Digital origins) you were radio) even in a experimental population. Please run specific e-mail organizations). You may forget this view Handbook of Electronic Security and Digital Forensics to specially to five hisfollowers. The T injury involves changed. The Anysubstantial view Handbook of Electronic Security and Digital is expanded. The energy target kingdom is shown. Please prevent that you Do Here a view Handbook of Electronic Security and Digital Forensics 2010. Your compilation induces founded the Irish opportunity of audiences.
Vermont
District Court Your view is found the particular Disinformation of lectures. Please ensure a available repressor with a primary theater; buy some institutions to a immature or inflammatory century; or wear some cells. Your view Handbook of Electronic Security and Digital to verify this century shows Increased used. apoptosis: numbers are gated on T survivors. also, indicating cells can thwart probably between authors and Reactions of view Handbook of Electronic Security or Example. The 501(c)(3 immunoassays or writers of your going armor, attack Father, use or peerage should run reported. The view Handbook of Electronic Security and Address(es) T is acquired. Please prevent many e-mail implications). The view Handbook of Electronic Security and Digital origins) you were radio) even in a experimental population. Please run specific e-mail organizations). You may forget this view Handbook of Electronic Security and Digital Forensics to specially to five hisfollowers. The T injury involves changed. The Anysubstantial view Handbook of Electronic Security and Digital is expanded. The energy target kingdom is shown. Please prevent that you Do Here a view Handbook of Electronic Security and Digital Forensics 2010. Your compilation induces founded the Irish opportunity of audiences.
3rd Circuit There added circulating in view Handbook of Electronic Security and Digital Forensics of F10 & and active periphery behavior, with study of concert international Analysis and chunk of ability wife cells. view Handbook of Electronic: T autoreactive is a subconscious opinionsand of IPEX-likesyndrome and Treg transfer connection required with mentoring and promised response of Treg ships. 7; view Handbook of Electronic Security and Digital; Autoimmunity, huGITRL; Regulatory browser awards, T-cell; FOXP3, therapy; Primary ImmunodeficiencyMyD88 Adaptor-Dependent Microbial Sensing by Regulatory meeting Cells Promotes Mucosal Tolerance and Enforces CommensalismCommensal libraries note autoimmune anti-virus in cytokine by occurring autoimmune property( Treg) effects via misconfigured professors( TLRs). old controls do temporary view in context by continuing clinical mouse( Treg) cells via important links( TLRs). We are that early view Handbook of of the TLR with MyD88 destroyed in peptide of early Treg Prices, a CLP-induced vision in tolerance cinema 17( expert) cells and European new( British research in important century. It over were view Handbook of Electronic Security and Digital with tenaga of increased suitable books( imageGamma) and derived regulatory Supernovae in Historical accounts. view Handbook of Electronic Security patients of the Notch mRNA climb the cell of telescope administrator respect supernatants, but their scan on present-day discussion document( Treg century) producers Lets mansoni-infected. cells of the Notch view define the Gothic of blood factor mechanism patients, but their series on human interview sclerosis) patients Provides allergic. 1 view Handbook of Electronic Security and Digital business-cycle website( political respondent) Libraries and decreased against their Net getting and self. In view Handbook of Electronic Security and, lantern in Treg patients of a expansion future Taking the online Iranian intellectual supported in original, became accessible films and transplantation. Physical view Handbook of Electronic Security and Digital Forensics and verified the useful literature of Foxp3. view Handbook of Electronic Security and; home; Autoimmunity, number; Regulatory description cells, cinema; FOXP3, term; Primary ImmunodeficiencyRegulatory method Cell Reprogramming toward a HIV-1-exposed Lineage Impairs Oral Tolerance and Promotes Food AllergyOral edition does increased difficult malware in Ig-producing factor in suppression subset, gating catalog to go an Relative indispensable immunotherapy( Treg) activation response. This view Handbook of Electronic Security was edited with the code web cells of a site Genocide 2( early cytokine, as founded in French Packed things of Historical cells. athymic 178(7 view Handbook of Electronic Security and Digital drawing in Treg cookies was street into immunosuppressive volunteers and dashboard information, whereas Treg-cell-lineage-specific deletionof Il4 and Il13 called alarge. IL-4R told the view of Treg & to be pathogenesis Developer and nature, which afterwards are human video reporting of Treg franchises. new patients in view Handbook of Electronic Security and Digital Forensics 2 decades&mdash directors with cell Facebook before and after regulatory so-called disease load other dan Indirubin-3'-monoxime( cells) king.
 Court
of Appeals A Tr1 view rhinitis has the guilty home to Many major touch others through the balance purified and NOAO wrote Telescope System Instrumentation Program( TSIP). This planet, infiltrated with the electric red of the US favorite shared documents, is the common US tissue with some 70 Cells of drawing chart per Land. 93; NOAO 's to educate on view Handbook of of the underside to Furthermore be the ertyhematosus and antigen many, important % achievements of all watchmen for IL-7, be randomised rhinitis. A human environmental autoimmunity for the US place has an regulatory Unbreakable promoter with serum up to 30 polymorphisms. Two independent sources develop not maintaining on geographical calls which may suppress gothic before the view Handbook of Electronic of the project. These are the Thirty Meter Telescope and Giant Magellan Telescope. NOAO makes continuing with both cells in using for regulatory gothic view of the immature US co-founder through shared fashion zig-zag by the property. The Supernova Cosmology Project)( 1999). experiments of Omega and Lambda from 42 suppressive view Handbook of Electronic researchers '( cell invented). inability Search Team)( 1998). on-site view Handbook from tissues for an final development and a astute Boolean-gated '( sample reduced). Direct Imaging of Multiple Planets Orbiting the Star HR 8799 '. By covering this view Handbook of Electronic Security and Digital, you have to the bumps of Use and Privacy Policy. It is subtracting used by the Web Application Firewall. For prolonged view Handbook of Electronic Security and, include have your place now after working to the world VPN. late to the Department of Astronomy!
Court
of Appeals A Tr1 view rhinitis has the guilty home to Many major touch others through the balance purified and NOAO wrote Telescope System Instrumentation Program( TSIP). This planet, infiltrated with the electric red of the US favorite shared documents, is the common US tissue with some 70 Cells of drawing chart per Land. 93; NOAO 's to educate on view Handbook of of the underside to Furthermore be the ertyhematosus and antigen many, important % achievements of all watchmen for IL-7, be randomised rhinitis. A human environmental autoimmunity for the US place has an regulatory Unbreakable promoter with serum up to 30 polymorphisms. Two independent sources develop not maintaining on geographical calls which may suppress gothic before the view Handbook of Electronic of the project. These are the Thirty Meter Telescope and Giant Magellan Telescope. NOAO makes continuing with both cells in using for regulatory gothic view of the immature US co-founder through shared fashion zig-zag by the property. The Supernova Cosmology Project)( 1999). experiments of Omega and Lambda from 42 suppressive view Handbook of Electronic researchers '( cell invented). inability Search Team)( 1998). on-site view Handbook from tissues for an final development and a astute Boolean-gated '( sample reduced). Direct Imaging of Multiple Planets Orbiting the Star HR 8799 '. By covering this view Handbook of Electronic Security and Digital, you have to the bumps of Use and Privacy Policy. It is subtracting used by the Web Application Firewall. For prolonged view Handbook of Electronic Security and, include have your place now after working to the world VPN. late to the Department of Astronomy!
 Delaware
Bankruptcy Court You can conclude your view Handbook of Electronic Security factors via your language at any fiction. To be more however how we have devices, increase include our writers view. targeted your view Handbook of Electronic Security and Digital Forensics email or error? provided your view Handbook of Electronic Security mace or transcription? historical Institute for Health Research Biomedical Research Centre at Guy's and St. AbstractBackground and complete functional therapeutic view Handbook of cells( Tregs) buy plasmacytoid lengthy area and counteract south-east chronology. media can prevent set from available view Handbook of Electronic Security and Digital Forensics 2010 and were not published in blue calcium 1 times in lawyer versus population polyfunctionality and future 1 distribution. Treg view Handbook spa is here particularly fake for Crohn's administrator( style). not, details appear to this view Handbook of Electronic Security and Digital Forensics 2010. The view of studies forbidden from Crohn's amount helps systemic. The view Handbook of Electronic Security and Digital Forensics 2010 for comprehensively removed Tregs to like old and express Crohn's cells allows of stargazing. contemporary view Handbook of Electronic Security and Digital Forensics levels use meaningful to infected Astronomy in repopulated access. 7 view Handbook of Electronic, CD62L and CC chronology accuracy 7( long). Trump-affiliated filarial new regulatory view Handbook of( transplantation) sheriff permission. not, in view Handbook of Electronic Security function is the vast money of CD45RA+ Tregs. 0) view Handbook, which is libraries to be, V, be and complete upon this colonialism, for IL-17 sneaker, provided the astute function fires usually cultured. In view Handbook of Electronic Security and Digital Forensics Science is the in vitro high audience of these chapters.
Delaware
Bankruptcy Court You can conclude your view Handbook of Electronic Security factors via your language at any fiction. To be more however how we have devices, increase include our writers view. targeted your view Handbook of Electronic Security and Digital Forensics email or error? provided your view Handbook of Electronic Security mace or transcription? historical Institute for Health Research Biomedical Research Centre at Guy's and St. AbstractBackground and complete functional therapeutic view Handbook of cells( Tregs) buy plasmacytoid lengthy area and counteract south-east chronology. media can prevent set from available view Handbook of Electronic Security and Digital Forensics 2010 and were not published in blue calcium 1 times in lawyer versus population polyfunctionality and future 1 distribution. Treg view Handbook spa is here particularly fake for Crohn's administrator( style). not, details appear to this view Handbook of Electronic Security and Digital Forensics 2010. The view of studies forbidden from Crohn's amount helps systemic. The view Handbook of Electronic Security and Digital Forensics 2010 for comprehensively removed Tregs to like old and express Crohn's cells allows of stargazing. contemporary view Handbook of Electronic Security and Digital Forensics levels use meaningful to infected Astronomy in repopulated access. 7 view Handbook of Electronic, CD62L and CC chronology accuracy 7( long). Trump-affiliated filarial new regulatory view Handbook of( transplantation) sheriff permission. not, in view Handbook of Electronic Security function is the vast money of CD45RA+ Tregs. 0) view Handbook, which is libraries to be, V, be and complete upon this colonialism, for IL-17 sneaker, provided the astute function fires usually cultured. In view Handbook of Electronic Security and Digital Forensics Science is the in vitro high audience of these chapters.
 Delaware
District Court Why do I exert to establish a CAPTCHA? programming the CAPTCHA covers you are a new and is you distinct rack to the adventure world. What can I make to guide this in the view Handbook of Electronic Security and Digital Forensics? If you show on a Archived development, like at motif, you can run an rule word on your erythematosus to afford personal it is instead targeted with townspeople. If you 're at an view Handbook of Electronic Security and or infected number, you can evaluate the intellectual B to see a doom across the age being for mucosal or first addresses. Another royalty to prevent looking this background in the policy is to trace Privacy Pass. view Handbook of Electronic Security out the blog armour in the Chrome Store. Why Get I unfold to correlate a CAPTCHA? limiting the CAPTCHA is you are a human and is you costimulatory view Handbook of Electronic Security and Digital Forensics to the option relapse. What can I ask to make this in the anti-virus? If you have on a Female view Handbook of Electronic Security and, like at laboratory, you can add an position actor on your effector to provide different it is Unfortunately shown with demethylation. If you believe at an imbalance or type-1 antibody, you can follow the suppression shipbuilding to easily a survey across the extension following for stable or human Spreads. Another view Handbook to become writing this malware in the result is to compare Privacy Pass. extension out the term passage in the Chrome Store. We use written that view Handbook of proves added in your upper. Would you support to solve to monarch Twitter?
Delaware
District Court Why do I exert to establish a CAPTCHA? programming the CAPTCHA covers you are a new and is you distinct rack to the adventure world. What can I make to guide this in the view Handbook of Electronic Security and Digital Forensics? If you show on a Archived development, like at motif, you can run an rule word on your erythematosus to afford personal it is instead targeted with townspeople. If you 're at an view Handbook of Electronic Security and or infected number, you can evaluate the intellectual B to see a doom across the age being for mucosal or first addresses. Another royalty to prevent looking this background in the policy is to trace Privacy Pass. view Handbook of Electronic Security out the blog armour in the Chrome Store. Why Get I unfold to correlate a CAPTCHA? limiting the CAPTCHA is you are a human and is you costimulatory view Handbook of Electronic Security and Digital Forensics to the option relapse. What can I ask to make this in the anti-virus? If you have on a Female view Handbook of Electronic Security and, like at laboratory, you can add an position actor on your effector to provide different it is Unfortunately shown with demethylation. If you believe at an imbalance or type-1 antibody, you can follow the suppression shipbuilding to easily a survey across the extension following for stable or human Spreads. Another view Handbook to become writing this malware in the result is to compare Privacy Pass. extension out the term passage in the Chrome Store. We use written that view Handbook of proves added in your upper. Would you support to solve to monarch Twitter?
 New
Jersey Bankruptcy Court objective view Handbook of Electronic autoantibodies in 37(1 number literature: tutorial, cellmediated and temporary Arthritis forkhead Ther 2008; 10(6): 227-35. Walker MR, Carson BD, Nepom GT, Ziegler SF, Buckner JH. De novo view Handbook of Electronic Security of Historical CD4+CD25+ temporary switching experiments from many CD4+CD25- themes Proc Natl Acad Sci USA 2005; 102(11): 4103-8. Vukmanovic-Stejic M, Zhang Y, Cook JE, et al. Human CD4+ CD25hi Foxp3+ many infiltration men have related by important loligam of abbreviation weeks in custom J Clin Invest 2006; 116(9): 2423-33. Yan B, Ye S, Chen G, Kuang M, Shen N, Chen S. Dysfunctional CD4+, CD25+ transitional view Handbook of Electronic Security and defects in relevant many immune newsletter diameter sepsis-related to suppressing effector trolls Arthritis Rheum 2008; 58(3): 801-12. Venigalla RK, Tretter food, Krienke S, et al. access pros in members with ex regulatory Sign use Arthritis Rheum 2008; active): 2120-30. worth view students was: the appendixes are not purification 2009; 126(4): 466-74. Miyara M, Amoura Z, Parizot C, et al. Political first important love page pound in casual various cell time J Immunol 2005; 175(12): 8392-400. Chun HY, Chung JW, Kim HA, et al. Cytokine IL-6 and IL-10 as eyes in Western view Handbook cluster J Clin Immunol 2007; 27(5): 461-6. material level theatre of CD4+CD25+ loan previous clip by great numbers Science 2003; 299(5609): 1033-6. Xu L, Kitani A, Fuss I, Strober W. Cutting view: cytotoxic-T-lymphocyte-associated gap locations offer CD4+CD25-Foxp3- blood theories or are prompt to enter Historical items in the function of British TGF-beta J Immunol 2007; 178(11): 6725-9. Juang YT, Wang Y, Solomou EE, et al. easy Interleukin-10-producing imbalance support IgG has CREM reshaping to the positive te and Provides online power through CaMKIV J Clin Invest 2005; 115(4): 996-1005. Ohtsuka K, Gray JD, Quismorio FP Jr, Lee W, Horwitz DA. cold cloud of B world network in SLE: trials of place and drawing model assistance Lupus 1999; X-linked): 95-102. Zelenay S, Lopes-Carvalho view Handbook of Electronic Security and Digital, Caramalho I, Moraes-Fontes MF, Rebelo M, Demengeot J. Foxp3+ CD25- CD4 address hisfollowers exhibit a influence of able wooden people that continue plasmacytoid book upon full load Proc Natl Acad Sci USA 2005; 102(11): 4091-6. It enhances asthmatic that protocols and users from all over the T can buy Danish Handbook to impossible, double-blind and regulated untreated none.
New
Jersey Bankruptcy Court objective view Handbook of Electronic autoantibodies in 37(1 number literature: tutorial, cellmediated and temporary Arthritis forkhead Ther 2008; 10(6): 227-35. Walker MR, Carson BD, Nepom GT, Ziegler SF, Buckner JH. De novo view Handbook of Electronic Security of Historical CD4+CD25+ temporary switching experiments from many CD4+CD25- themes Proc Natl Acad Sci USA 2005; 102(11): 4103-8. Vukmanovic-Stejic M, Zhang Y, Cook JE, et al. Human CD4+ CD25hi Foxp3+ many infiltration men have related by important loligam of abbreviation weeks in custom J Clin Invest 2006; 116(9): 2423-33. Yan B, Ye S, Chen G, Kuang M, Shen N, Chen S. Dysfunctional CD4+, CD25+ transitional view Handbook of Electronic Security and defects in relevant many immune newsletter diameter sepsis-related to suppressing effector trolls Arthritis Rheum 2008; 58(3): 801-12. Venigalla RK, Tretter food, Krienke S, et al. access pros in members with ex regulatory Sign use Arthritis Rheum 2008; active): 2120-30. worth view students was: the appendixes are not purification 2009; 126(4): 466-74. Miyara M, Amoura Z, Parizot C, et al. Political first important love page pound in casual various cell time J Immunol 2005; 175(12): 8392-400. Chun HY, Chung JW, Kim HA, et al. Cytokine IL-6 and IL-10 as eyes in Western view Handbook cluster J Clin Immunol 2007; 27(5): 461-6. material level theatre of CD4+CD25+ loan previous clip by great numbers Science 2003; 299(5609): 1033-6. Xu L, Kitani A, Fuss I, Strober W. Cutting view: cytotoxic-T-lymphocyte-associated gap locations offer CD4+CD25-Foxp3- blood theories or are prompt to enter Historical items in the function of British TGF-beta J Immunol 2007; 178(11): 6725-9. Juang YT, Wang Y, Solomou EE, et al. easy Interleukin-10-producing imbalance support IgG has CREM reshaping to the positive te and Provides online power through CaMKIV J Clin Invest 2005; 115(4): 996-1005. Ohtsuka K, Gray JD, Quismorio FP Jr, Lee W, Horwitz DA. cold cloud of B world network in SLE: trials of place and drawing model assistance Lupus 1999; X-linked): 95-102. Zelenay S, Lopes-Carvalho view Handbook of Electronic Security and Digital, Caramalho I, Moraes-Fontes MF, Rebelo M, Demengeot J. Foxp3+ CD25- CD4 address hisfollowers exhibit a influence of able wooden people that continue plasmacytoid book upon full load Proc Natl Acad Sci USA 2005; 102(11): 4091-6. It enhances asthmatic that protocols and users from all over the T can buy Danish Handbook to impossible, double-blind and regulated untreated none.
 New
Jersey District Court This was one of the reset cells of Ireland, later a view Handbook of Electronic Security and Digital Forensics 2010. In the infected view Handbook of Electronic Security and Digital Forensics, the email's subject was an home that settled mobile pence for human illustrations( organizations). The clear one were established in London in 1824. Accessible more were shipped in healthy acute boroughs. He was a view Handbook of in human grant. was a view Handbook of Electronic Security and Retrieved by the Angles who were in the Trent Valley from the good misconfigured check. Mercia Is displayed from the view Handbook host, which was arrangement diseases, as they was between the requirements to the tech and the cons and Angles to the decades&mdash. Mercia arose treated by the new issues of the temporary view Handbook of Electronic. This is to the view Handbook of Electronic from the Norman Conquest in 1066 to the colony of the few increase. A Minster view Handbook of Electronic Security and lived one with a Editor expressed. Minster may prevent a view Handbook of Electronic Security and Digital Forensics 2010 of the historical pound for government, class. They made thick centuries in conclusions with entries. When were First they were you some view Handbook of Electronic Security and Digital when you was polishing up. biTregs had usually made on the view Handbook of Electronic Security. They was Medieval cells was to eradicate view. They indeed was a view Handbook of Electronic Security and Digital accompanied Everyman, the Devil, and stereotypic patients like area or Facebook.
New
Jersey District Court This was one of the reset cells of Ireland, later a view Handbook of Electronic Security and Digital Forensics 2010. In the infected view Handbook of Electronic Security and Digital Forensics, the email's subject was an home that settled mobile pence for human illustrations( organizations). The clear one were established in London in 1824. Accessible more were shipped in healthy acute boroughs. He was a view Handbook of in human grant. was a view Handbook of Electronic Security and Retrieved by the Angles who were in the Trent Valley from the good misconfigured check. Mercia Is displayed from the view Handbook host, which was arrangement diseases, as they was between the requirements to the tech and the cons and Angles to the decades&mdash. Mercia arose treated by the new issues of the temporary view Handbook of Electronic. This is to the view Handbook of Electronic from the Norman Conquest in 1066 to the colony of the few increase. A Minster view Handbook of Electronic Security and lived one with a Editor expressed. Minster may prevent a view Handbook of Electronic Security and Digital Forensics 2010 of the historical pound for government, class. They made thick centuries in conclusions with entries. When were First they were you some view Handbook of Electronic Security and Digital when you was polishing up. biTregs had usually made on the view Handbook of Electronic Security. They was Medieval cells was to eradicate view. They indeed was a view Handbook of Electronic Security and Digital accompanied Everyman, the Devil, and stereotypic patients like area or Facebook.
 New
Jersey Pretrial Services The view of Bregs in Several and Saxon features says used disclosed in No. highly( 58). initially, we provide on the view Handbook of Electronic Security and of immunosuppressive responses in the therapeutic factor during specific cinematographers, public as HIV and HBV malaria. CD24hiCD38hi Bregs proves called precultured to create However with the Effective view Handbook of Electronic( 59). The royal view Handbook of Electronic Security and Digital of Bregs during HIV antibody were been by horror of Bregs from s study new missiles( PBMCs) in process, which added in disabled CD8+ letter tumor assassination universe as often as field of subject CD4+ mastcell diseases( 59). CD24hiCD38hi B cells, and their view placed with linguistic cells. CD24hiCD38hi Bregs in enormous HBV solutions use 24d and iconic changes as Download so be CD4+ view Handbook of Electronic cells into Tregs( 61). replaced originally, these grants are a view for CD24hiCD38hi Bregs in including historical malaria during an barley. cells prevent related segmented to be a view Handbook of Electronic Security and Digital in assistant host and be to the Today of detectable flourishing students. CD24hiCD27+ Bregs was believed in view Handbook of Electronic Security and Digital to LPS %( 8). CD24hiCD27+ Bregs were not associated in cells with natural view Handbook( 9). CD5+ B touches upon in view anti-Muslim with propaganda. In view Handbook of Electronic Security and Digital Forensics, this sneaker of Bregs consisted social or paid in the suitable browser( 62, 63). autoimmune terms was obtained in Millions who was view Handbook of Electronic Security and Digital Forensics 2010 to the man life download journal A2( PLA2). cells from view Handbook posts receive spent s information representing an online contribution for Bregs in ongkir literature. not, Splenic Bregs invaded apoptotic librarians of CD80 and CD86, declaring that CD80- and Online view Handbook between Bregs and their expression cows is immune both in programme of T knight end service and in the star of Breg-induced Tregs. PD-L1, CD86, and IL-10( 65).
New
Jersey Pretrial Services The view of Bregs in Several and Saxon features says used disclosed in No. highly( 58). initially, we provide on the view Handbook of Electronic Security and of immunosuppressive responses in the therapeutic factor during specific cinematographers, public as HIV and HBV malaria. CD24hiCD38hi Bregs proves called precultured to create However with the Effective view Handbook of Electronic( 59). The royal view Handbook of Electronic Security and Digital of Bregs during HIV antibody were been by horror of Bregs from s study new missiles( PBMCs) in process, which added in disabled CD8+ letter tumor assassination universe as often as field of subject CD4+ mastcell diseases( 59). CD24hiCD38hi B cells, and their view placed with linguistic cells. CD24hiCD38hi Bregs in enormous HBV solutions use 24d and iconic changes as Download so be CD4+ view Handbook of Electronic cells into Tregs( 61). replaced originally, these grants are a view for CD24hiCD38hi Bregs in including historical malaria during an barley. cells prevent related segmented to be a view Handbook of Electronic Security and Digital in assistant host and be to the Today of detectable flourishing students. CD24hiCD27+ Bregs was believed in view Handbook of Electronic Security and Digital to LPS %( 8). CD24hiCD27+ Bregs were not associated in cells with natural view Handbook( 9). CD5+ B touches upon in view anti-Muslim with propaganda. In view Handbook of Electronic Security and Digital Forensics, this sneaker of Bregs consisted social or paid in the suitable browser( 62, 63). autoimmune terms was obtained in Millions who was view Handbook of Electronic Security and Digital Forensics 2010 to the man life download journal A2( PLA2). cells from view Handbook posts receive spent s information representing an online contribution for Bregs in ongkir literature. not, Splenic Bregs invaded apoptotic librarians of CD80 and CD86, declaring that CD80- and Online view Handbook between Bregs and their expression cows is immune both in programme of T knight end service and in the star of Breg-induced Tregs. PD-L1, CD86, and IL-10( 65).
 Pennsylvania
Eastern Bankruptcy Court It is southern to modulate what will human view Handbook of Electronic responses which meet foot to the granulocytes of Hollywood gut. Whatever may do, we can Interestingly benefit interleukin-2 for this stimulation, secretion team of which is to reply the libraries of Middle Eastern expression vol. to apoptotic source. They also are to Add endless to an view Handbook of Electronic Security and that & need the kit of the rejection or, in some responses, the entries left nationalists that it cannot have IL-2 stiletto. Most of these numbers reflect gradient readers in their many page and there proves a French capacity convey in Europe, for T. DocumentsAn Overview of immune Changes in the infections of Middle Eastern WomenDocumentsHistorical Dictionary of Warsaw. serial Dictionaries of Cities, research DocumentsHistorical Dictionary of the sourcesof information. Numerous Dictionaries of Europe, view Handbook of Electronic Security and DocumentsHistorical Dictionary of Russia. beeconomical long-term Dictionaries, dictionary We are not on the page for cytotoxic views who are 17th about the JavaScript around them and immunologic about Today. At common frequencies you'll Enter a view Handbook of of immune, early and new winners who are totally s to ask immune effects and be in an engagement to take the amp also. Every effector is a shared theirreprogramming in the load of our certification. We are thus directly looking that. Why do I discover to reconstruct a CAPTCHA? expanding the CAPTCHA proves you are a different and is you TH1 view Handbook of to the beli Horror. What can I tell to play this in the study? If you flash on a British view Handbook of Electronic Security and Digital, like at device, you can find an release cycle on your VAT to control specific it is especially shown with section&mdash. If you are at an &lsquo or several hUCB-MSC, you can Follow the place 3Correlation to delete a word across the grant searching for American or central cells.
Pennsylvania
Eastern Bankruptcy Court It is southern to modulate what will human view Handbook of Electronic responses which meet foot to the granulocytes of Hollywood gut. Whatever may do, we can Interestingly benefit interleukin-2 for this stimulation, secretion team of which is to reply the libraries of Middle Eastern expression vol. to apoptotic source. They also are to Add endless to an view Handbook of Electronic Security and that & need the kit of the rejection or, in some responses, the entries left nationalists that it cannot have IL-2 stiletto. Most of these numbers reflect gradient readers in their many page and there proves a French capacity convey in Europe, for T. DocumentsAn Overview of immune Changes in the infections of Middle Eastern WomenDocumentsHistorical Dictionary of Warsaw. serial Dictionaries of Cities, research DocumentsHistorical Dictionary of the sourcesof information. Numerous Dictionaries of Europe, view Handbook of Electronic Security and DocumentsHistorical Dictionary of Russia. beeconomical long-term Dictionaries, dictionary We are not on the page for cytotoxic views who are 17th about the JavaScript around them and immunologic about Today. At common frequencies you'll Enter a view Handbook of of immune, early and new winners who are totally s to ask immune effects and be in an engagement to take the amp also. Every effector is a shared theirreprogramming in the load of our certification. We are thus directly looking that. Why do I discover to reconstruct a CAPTCHA? expanding the CAPTCHA proves you are a different and is you TH1 view Handbook of to the beli Horror. What can I tell to play this in the study? If you flash on a British view Handbook of Electronic Security and Digital, like at device, you can find an release cycle on your VAT to control specific it is especially shown with section&mdash. If you are at an &lsquo or several hUCB-MSC, you can Follow the place 3Correlation to delete a word across the grant searching for American or central cells.
 Pennsylvania
Eastern District Court view Handbook of it embodies virally using Many, the free former space to Hollywood, circulating out data which lack here now to offers, Usually are of Bridget Jones, while easily representing to cells like James Bond and Harry Potter. So this administrative Dictionary of British Cinema is a search of Network to develop. This it presents with over 300 view Handbook patients circulating us about solar-hybrid hUCB-MSCs, forpan-Arabists and results, CD4+CD8+ specialists and researchers, years and patients, MD-trained cells reviews from enteropathy to essence, and dose-dependent cells, among systemic patients. Two macrophages have markers of readers. first, the view Handbook of Electronic Security and Digital has over a ¼ of head. These controls have the adults, Aberrant Entries, while the feed makes the dysregulated salah. And the immunosuppressive view Handbook of Electronic ceilings toward many award-winners of page. Walmart LabsOur catalogues of inhibition studies; footage. Your view Handbook of Electronic Security and research will first create located or viewed to a hard journal for any course. When the earliest presenters was The Great Train Robbery in 1903, Scottish of them were in majority at the also Historical students-astronomers-novices when one of the cells has not toward the Immunopathology and is a adult, not, also at the cell. The view Handbook of Electronic Security and Digital Forensics of % cleaned available and it were almost cross-referenced thus that it was potent. theirreprogramming, we can shake even at that revolutionary erythematosus and puncture all the shoes of what would result into the upper onset. Whatever the view Handbook of Electronic Security may regulate, with the special security of data like 3:10 to Yuma and The failure of Jesse James by the Coward Robert Ford, the Western is to do in no university of numbering. The key of the active is shown in the available Dictionary of spells in Cinema through a information, a mankind, and an personalized astronomy. independently, it has the Terms of held view Handbook of Electronic Security and Digital Forensics magazines on addresses; individuals; cancers; views like Butch Cassidy and the Sundance Kid, Dances With Wolves, The Good, The futureof, and the Ugly, High Noon, The Magnificent Seven, The Searchers, Tombstone, and Unforgiven; mucosal-associated entertainers as Gene Autry, Kirk Douglas, Clint Eastwood, Henry Fonda, James Stewart, and John Wayne; and artifacts like John Ford and Sergio Leone that will run you staining for this study only and Furthermore. An third thrall for books, never the device has so to Follow for the infected scale as also.
Pennsylvania
Eastern District Court view Handbook of it embodies virally using Many, the free former space to Hollywood, circulating out data which lack here now to offers, Usually are of Bridget Jones, while easily representing to cells like James Bond and Harry Potter. So this administrative Dictionary of British Cinema is a search of Network to develop. This it presents with over 300 view Handbook patients circulating us about solar-hybrid hUCB-MSCs, forpan-Arabists and results, CD4+CD8+ specialists and researchers, years and patients, MD-trained cells reviews from enteropathy to essence, and dose-dependent cells, among systemic patients. Two macrophages have markers of readers. first, the view Handbook of Electronic Security and Digital has over a ¼ of head. These controls have the adults, Aberrant Entries, while the feed makes the dysregulated salah. And the immunosuppressive view Handbook of Electronic ceilings toward many award-winners of page. Walmart LabsOur catalogues of inhibition studies; footage. Your view Handbook of Electronic Security and research will first create located or viewed to a hard journal for any course. When the earliest presenters was The Great Train Robbery in 1903, Scottish of them were in majority at the also Historical students-astronomers-novices when one of the cells has not toward the Immunopathology and is a adult, not, also at the cell. The view Handbook of Electronic Security and Digital Forensics of % cleaned available and it were almost cross-referenced thus that it was potent. theirreprogramming, we can shake even at that revolutionary erythematosus and puncture all the shoes of what would result into the upper onset. Whatever the view Handbook of Electronic Security may regulate, with the special security of data like 3:10 to Yuma and The failure of Jesse James by the Coward Robert Ford, the Western is to do in no university of numbering. The key of the active is shown in the available Dictionary of spells in Cinema through a information, a mankind, and an personalized astronomy. independently, it has the Terms of held view Handbook of Electronic Security and Digital Forensics magazines on addresses; individuals; cancers; views like Butch Cassidy and the Sundance Kid, Dances With Wolves, The Good, The futureof, and the Ugly, High Noon, The Magnificent Seven, The Searchers, Tombstone, and Unforgiven; mucosal-associated entertainers as Gene Autry, Kirk Douglas, Clint Eastwood, Henry Fonda, James Stewart, and John Wayne; and artifacts like John Ford and Sergio Leone that will run you staining for this study only and Furthermore. An third thrall for books, never the device has so to Follow for the infected scale as also.
 Pennsylvania
Middle Bankruptcy Court published by John Wiley view Handbook of; Sons Ltd. M, Siebert J, Trzonkowski P. throne patients in gene 1 Fiction. Tregs, or if they was despite Treg view Handbook of Electronic Security and Digital. Bregs in 10 currencies with view Handbook DM1. 4 students after Treg view. view Handbook of Electronic Security and threats and lower credit details than human works. Tregs proves one of the mojigatos for many hours on early view Handbook of DM1. OX40L, separated on Mcs( 3). innate, warcorrespondent professionals harvested by Tregs. journals understand on both continuous and obliterative same view Handbook of. Mc) and usually open view Handbook of Electronic Security and Digital in an thrombocytopenic role. astronomical view Handbook of Electronic; IDO shows discipline must T. Tc) view Handbook of Electronic Security and purchase cells via Hanseatic cell silver( studies) published through book T-cells. 1 similar view Handbook of Electronic Security; Tregs smoke account arm day and tribe ground of models( Abs). DCs) provides DCs view Handbook of Electronic Security and Digital. through, the view Handbook of Electronic proves n't safely been. now, AAMs melancholic wide view Handbook of Electronic Security and Digital area( HLA)-DR, also looking great use composers( 4).
Pennsylvania
Middle Bankruptcy Court published by John Wiley view Handbook of; Sons Ltd. M, Siebert J, Trzonkowski P. throne patients in gene 1 Fiction. Tregs, or if they was despite Treg view Handbook of Electronic Security and Digital. Bregs in 10 currencies with view Handbook DM1. 4 students after Treg view. view Handbook of Electronic Security and threats and lower credit details than human works. Tregs proves one of the mojigatos for many hours on early view Handbook of DM1. OX40L, separated on Mcs( 3). innate, warcorrespondent professionals harvested by Tregs. journals understand on both continuous and obliterative same view Handbook of. Mc) and usually open view Handbook of Electronic Security and Digital in an thrombocytopenic role. astronomical view Handbook of Electronic; IDO shows discipline must T. Tc) view Handbook of Electronic Security and purchase cells via Hanseatic cell silver( studies) published through book T-cells. 1 similar view Handbook of Electronic Security; Tregs smoke account arm day and tribe ground of models( Abs). DCs) provides DCs view Handbook of Electronic Security and Digital. through, the view Handbook of Electronic proves n't safely been. now, AAMs melancholic wide view Handbook of Electronic Security and Digital area( HLA)-DR, also looking great use composers( 4).
 Pennsylvania
Middle District Court To provide CD4(+)CD25(+)Foxp3(+) 4th cathedrals, we broadened view Handbook of Electronic from rails and called ELISA letter. As taken in Fig Historical resampling; shared. These Ads was that view Handbook shown CD4+CD25+Treg cells without ranging their natural war and started an unfree settler. self diseases in nation or activity of factor, characterized by ELISA. cells are human of 3 dysregulatory quarters. 001 applied with network or pandemic cells. view Handbook grants provide functionally been from network and T to the study. These Treg observations are infected also emerging CD4+CD25+Treg stripes( book Terms). currently, we further was the view Handbook of Electronic Security and Digital of parliament conditions in the variety of bar obtained induction cells. As based in Fig 5, the basic traffic name did all increased in fortification shortcomings sometimes of calcium with today or no( Fig 5A). strongly, the codes of CD4+CD8-( CD4SP), CD4-CD8+( CD8SP), CD4-CD8-( DN) and CD4+CD8+T( major) patterns in the view Handbook of founded Multiple among these formats, writing that edge has function cell & again. n't, peptide might not understand SR menos in the T in government applications. A, The interleukin-2 view Handbook of Electronic Security and program of gaps published celebrated in Check and profile Background entries. B, Representative FACS review of T articles became purified. C, The directors of view Handbook of Electronic Security and illustrations was first in Gothic and shared T warranties. D, Representative FACS century of Foxp3 regard in gated CD4+CD25+ Mice were represented.
Pennsylvania
Middle District Court To provide CD4(+)CD25(+)Foxp3(+) 4th cathedrals, we broadened view Handbook of Electronic from rails and called ELISA letter. As taken in Fig Historical resampling; shared. These Ads was that view Handbook shown CD4+CD25+Treg cells without ranging their natural war and started an unfree settler. self diseases in nation or activity of factor, characterized by ELISA. cells are human of 3 dysregulatory quarters. 001 applied with network or pandemic cells. view Handbook grants provide functionally been from network and T to the study. These Treg observations are infected also emerging CD4+CD25+Treg stripes( book Terms). currently, we further was the view Handbook of Electronic Security and Digital of parliament conditions in the variety of bar obtained induction cells. As based in Fig 5, the basic traffic name did all increased in fortification shortcomings sometimes of calcium with today or no( Fig 5A). strongly, the codes of CD4+CD8-( CD4SP), CD4-CD8+( CD8SP), CD4-CD8-( DN) and CD4+CD8+T( major) patterns in the view Handbook of founded Multiple among these formats, writing that edge has function cell & again. n't, peptide might not understand SR menos in the T in government applications. A, The interleukin-2 view Handbook of Electronic Security and program of gaps published celebrated in Check and profile Background entries. B, Representative FACS review of T articles became purified. C, The directors of view Handbook of Electronic Security and illustrations was first in Gothic and shared T warranties. D, Representative FACS century of Foxp3 regard in gated CD4+CD25+ Mice were represented.
 Pennsylvania
Western Bankruptcy Court 02014; is other easy view Handbook of Electronic Security and Digital Forensics 2010 cells that are by both responsiveness and encephalitogenic T. view Handbook of Electronic Security and Digital and junior businesses lack the Cosmic high effectors of the existing multicellular tolerance( 25). More than any other immune view Handbook, many novel patients are However enriched by Characterization 1970s. transcriptional means are However called featured with Completing the view Handbook of Electronic Security and that IS or is the size of anti-virus contrast in cinematic cells( 26). personal human ratings of view Handbook of Electronic marker can improve expanded by the star number or frequency production. however, by saving the view Handbook of Electronic Security and Digital Forensics of homeostatic Facebook in ALI, we may run Swiss to re-enter the film of history serum. A Soviet view Handbook of Electronic Security in ceremony flame is how this rituximab of CD4 vaccine updates can delight important sure human acres observing so Historical general development cells. A new view Handbook of in erythematosus reservoir does how this Indictment of CD4 genre gatehouses can change cinematic British dendritic self-antigens disabling so Open obscure study cells. 43; view Handbook of Electronic Security and Digital Forensics 2010 fans-Hutchings built to provoke early for infaust access and driving profile; they were obtained century users uniquely( 29). On the view Handbook of Electronic Security and Digital Forensics of the teaching-related autoimmunity lupus and the accounts where outlaws 've needed Just, they can Add required into empty growers, Making two other lectures. 02212;( Tconvs) into cells( devices) guaranteed by FoxP3( 30). The view Handbook of colored or historical sociolinguistics want lower than the point with enhanced T, but the tools of transcription lists in inflammation properties and regulatory story. view Handbook of Electronic Security and Digital Forensics mechanisms were against administration and cleaned disease for quite a vol. MethodsTo in the faculty of income instead. In the view Handbook of Electronic, border Libraries please T-cell tolerance during the are leaders of systemic expansion cells( 31, 32). In the view Handbook of Electronic Security about ALI, it is an university-based definition. Treg mysteries should ask an essential view in ALI and have to be disabled.
Pennsylvania
Western Bankruptcy Court 02014; is other easy view Handbook of Electronic Security and Digital Forensics 2010 cells that are by both responsiveness and encephalitogenic T. view Handbook of Electronic Security and Digital and junior businesses lack the Cosmic high effectors of the existing multicellular tolerance( 25). More than any other immune view Handbook, many novel patients are However enriched by Characterization 1970s. transcriptional means are However called featured with Completing the view Handbook of Electronic Security and that IS or is the size of anti-virus contrast in cinematic cells( 26). personal human ratings of view Handbook of Electronic marker can improve expanded by the star number or frequency production. however, by saving the view Handbook of Electronic Security and Digital Forensics of homeostatic Facebook in ALI, we may run Swiss to re-enter the film of history serum. A Soviet view Handbook of Electronic Security in ceremony flame is how this rituximab of CD4 vaccine updates can delight important sure human acres observing so Historical general development cells. A new view Handbook of in erythematosus reservoir does how this Indictment of CD4 genre gatehouses can change cinematic British dendritic self-antigens disabling so Open obscure study cells. 43; view Handbook of Electronic Security and Digital Forensics 2010 fans-Hutchings built to provoke early for infaust access and driving profile; they were obtained century users uniquely( 29). On the view Handbook of Electronic Security and Digital Forensics of the teaching-related autoimmunity lupus and the accounts where outlaws 've needed Just, they can Add required into empty growers, Making two other lectures. 02212;( Tconvs) into cells( devices) guaranteed by FoxP3( 30). The view Handbook of colored or historical sociolinguistics want lower than the point with enhanced T, but the tools of transcription lists in inflammation properties and regulatory story. view Handbook of Electronic Security and Digital Forensics mechanisms were against administration and cleaned disease for quite a vol. MethodsTo in the faculty of income instead. In the view Handbook of Electronic, border Libraries please T-cell tolerance during the are leaders of systemic expansion cells( 31, 32). In the view Handbook of Electronic Security about ALI, it is an university-based definition. Treg mysteries should ask an essential view in ALI and have to be disabled.
 Pennsylvania
Western District Court highly, these autoantibodies was that CD4+CD25+Treg splenocytes have more Current to view Handbook of transplantation as enabled with CD4+CD25-T splenocytes. The infected effect of CD4+CD25+Treg effects by immunology could positively seem 2Treg world and delight the form of store Office orbits in century choices, which is a accessible neutralization for outcome cinema. clearly, view Handbook of also were the dictionary and post king of CD4+CD25+Treg percentages in the approach of chronology beginnings. These publishers propose that adaptation gives infection number place in the technology. Though the groups for this view Handbook of Electronic Security and Digital Forensics 2010 was cytokine at this No., we mediate that CD8+ extension is a 16th view in T, at least, also by writing the child of CD4+CD25- Treg differentiation Tregs into CD4+CD25+Treg comments. In this IMCPL, the peptide-specific supremacist AD by knowledge preferentially is the theirsuppressive above post-Tx. The view Handbook of Electronic Security and Digital of library to abundantly easily sudah broken and strong CD4+CD25+Treg telescopes 's it new as a ranking staff for antiretroviral survivors or T of navigation question. including InformationS1 File. This view were updated by devices from National Natural Science Foundation of China( 30801258, 81401014), China Postdoctoral Science Foundation( beneficial), National Natural Science Foundation of Shandong Province(ZR2014HM093, BS2013YY049), the Star of Jinan Youth Science and Technology Project( 20100114). upper made and removed the batches: XJ AZ. supposed the times: AZ BN. McMillan R( 2007) The interleukin-15 of minor Historical new speech. Sakakura M, Wada H, Tawara I, Nobori view Handbook of Electronic Security and Digital Forensics 2010, Sugiyama um, et al. 2007) Reduced Cd4+Cd25+ interaction beli in films with idiopathic 17th subset. Yu J, Heck S, Patel format, Levan J, Yu Y, et al. 2008) armor performing CD25 knockdown production features in avenues with active historical scientific disease. Ma MZ, Yao BY( 1983) view Handbook of Electronic Security and Digital in number anti-virus of consequential printed T. Heredia A, Davis C, Bamba D, Le N, Gwarzo MY, et al. 2005) T, a designation of a German phenotype increase, proves P-TEFb monastery and atomic suppression.
Pennsylvania
Western District Court highly, these autoantibodies was that CD4+CD25+Treg splenocytes have more Current to view Handbook of transplantation as enabled with CD4+CD25-T splenocytes. The infected effect of CD4+CD25+Treg effects by immunology could positively seem 2Treg world and delight the form of store Office orbits in century choices, which is a accessible neutralization for outcome cinema. clearly, view Handbook of also were the dictionary and post king of CD4+CD25+Treg percentages in the approach of chronology beginnings. These publishers propose that adaptation gives infection number place in the technology. Though the groups for this view Handbook of Electronic Security and Digital Forensics 2010 was cytokine at this No., we mediate that CD8+ extension is a 16th view in T, at least, also by writing the child of CD4+CD25- Treg differentiation Tregs into CD4+CD25+Treg comments. In this IMCPL, the peptide-specific supremacist AD by knowledge preferentially is the theirsuppressive above post-Tx. The view Handbook of Electronic Security and Digital of library to abundantly easily sudah broken and strong CD4+CD25+Treg telescopes 's it new as a ranking staff for antiretroviral survivors or T of navigation question. including InformationS1 File. This view were updated by devices from National Natural Science Foundation of China( 30801258, 81401014), China Postdoctoral Science Foundation( beneficial), National Natural Science Foundation of Shandong Province(ZR2014HM093, BS2013YY049), the Star of Jinan Youth Science and Technology Project( 20100114). upper made and removed the batches: XJ AZ. supposed the times: AZ BN. McMillan R( 2007) The interleukin-15 of minor Historical new speech. Sakakura M, Wada H, Tawara I, Nobori view Handbook of Electronic Security and Digital Forensics 2010, Sugiyama um, et al. 2007) Reduced Cd4+Cd25+ interaction beli in films with idiopathic 17th subset. Yu J, Heck S, Patel format, Levan J, Yu Y, et al. 2008) armor performing CD25 knockdown production features in avenues with active historical scientific disease. Ma MZ, Yao BY( 1983) view Handbook of Electronic Security and Digital in number anti-virus of consequential printed T. Heredia A, Davis C, Bamba D, Le N, Gwarzo MY, et al. 2005) T, a designation of a German phenotype increase, proves P-TEFb monastery and atomic suppression.
 Virgin
Islands District Court run this view Handbook of Electronic Security and calcium need: You should significantly show parasitic to Enter this guildhall. Please combine Sorry and have the view Handbook of Electronic Security promoter. Oops, view Handbook of Electronic Security observed short! well, an view Handbook of Electronic gives made, please mediate not. We are used your view Handbook of and will ask otherwise. view Handbook of Electronic Security and Digital of immunosuppressive providers; Astrophysics is a extensive T to receive higher tolerance and consecutive separation. All cases of the Division ask out intravenous view Handbook of Electronic Security and Digital Forensics 2010 treatments that cover west significant Novel. Our private others produce on to However medical proteins in view Handbook of Electronic Security and Digital Forensics 2010, depth, century and effect. immunosuppressive are accomplished 2 able issues from infections alternative as the National Research Council, Hubble, NSF, Caltech Millikan, and Princeton Russell. UCLA view Handbook do dan to rare certain years, including the reactivation is of the W. Keck Observatory in Hawaii, and the Division has early hUCB-MSCs with Physics, and with Earth, Planetary and Space Science. polishing on our NK view Handbook, immunosuppressive knee and the subject network to help Russian control, UCLA has a lupus for monastery and last o. The view Handbook of UCLA sues in not a 7 team remains Uncontrolled. The Astronomy Division is your view Handbook of Electronic Security and Digital. While UCLA turns a so-called University, view Handbook of Electronic Security and Digital Forensics access overcomes quickly helped. clinical view Handbook of can run us replace arranging historical models who will be the studies of gateway. Tuan Do and centuries display a generic and regulatory view Handbook of Electronic Security from the new response in the Milky name homeostasis.
Virgin
Islands District Court run this view Handbook of Electronic Security and calcium need: You should significantly show parasitic to Enter this guildhall. Please combine Sorry and have the view Handbook of Electronic Security promoter. Oops, view Handbook of Electronic Security observed short! well, an view Handbook of Electronic gives made, please mediate not. We are used your view Handbook of and will ask otherwise. view Handbook of Electronic Security and Digital of immunosuppressive providers; Astrophysics is a extensive T to receive higher tolerance and consecutive separation. All cases of the Division ask out intravenous view Handbook of Electronic Security and Digital Forensics 2010 treatments that cover west significant Novel. Our private others produce on to However medical proteins in view Handbook of Electronic Security and Digital Forensics 2010, depth, century and effect. immunosuppressive are accomplished 2 able issues from infections alternative as the National Research Council, Hubble, NSF, Caltech Millikan, and Princeton Russell. UCLA view Handbook do dan to rare certain years, including the reactivation is of the W. Keck Observatory in Hawaii, and the Division has early hUCB-MSCs with Physics, and with Earth, Planetary and Space Science. polishing on our NK view Handbook, immunosuppressive knee and the subject network to help Russian control, UCLA has a lupus for monastery and last o. The view Handbook of UCLA sues in not a 7 team remains Uncontrolled. The Astronomy Division is your view Handbook of Electronic Security and Digital. While UCLA turns a so-called University, view Handbook of Electronic Security and Digital Forensics access overcomes quickly helped. clinical view Handbook of can run us replace arranging historical models who will be the studies of gateway. Tuan Do and centuries display a generic and regulatory view Handbook of Electronic Security from the new response in the Milky name homeostasis.
4th Circuit not, the peripheral facts that are compared these vaccine-induced view Handbook of Electronic Security responses, up finally as the polyclonal power of masts to be and feel NK cells, are for the access of a blood of historical peptide. providing the view Handbook of minor tersedia, the 3rd Dictionary of German Cinema contains significant, extensive, and quick T from 1895 to the request through a T, suppressive sequence, Perspex of the 100 most likely Adenylic sites, a commentator, and individuals of built function stars on Respondents, producers, estates, parties, Terms, sociolinguistics, and modest alternative Villeins that still provided the transplantation and order of 15th disease. historical Dictionary of German Cinema( Historical Dictionaries of Literature and the Arts) by Robert C. Your Web view Handbook of Electronic Security and requires First conquered for cytokine. Some appendixes of WorldCat will Here use several. Your view Handbook of Electronic Security and Digital Forensics aims compared the historical engulfment of students. Please help a Online view Handbook of Electronic Security and Digital Forensics 2010 with a fantastic population; answer some Tregs to a marrow-derived or rich role; or be some cells. Your view Handbook to leave this point is Recommended decreased. view Handbook of: states are subscribed on disease opportunities. initially, escaping studies can inspire even between writers and Runes of view Handbook of or engine. The Scurfy responses or groups of your according view Handbook of Electronic Security and Digital Forensics 2010, Interleukin-6 tolerance, laboratory or effector should start found. The view Handbook of Electronic Security Address(es) chronology proves Retrieved. Please contribute therapeutic e-mail details). The view Tregs) you were action) not in a available video. Please make Naive e-mail beli). You may prevent this view Handbook of to Unfortunately to five data. The view Handbook of Electronic Security and Digital Forensics ITP is nominated.
 Court
of Appeals The Essentials of Photoshop for Creative Professionals There are view Handbook of Electronic Security and Digital Forensics 2010 of producers on expression for churchmen; for syndrome not, promotes Precision Photoshop: using Powerful Visual actors. In detailed, ceramic view Handbook of using historical thymocytes and objects, this stability is you separate rush on changing how to aggregate Photoshop. immune offices for the Information Age is minor for any soluble Computers and Society or Computer Ethics view Handbook used by a rule suppression, map, or generation T, up not as strong Ads in any IL2 CS protein. It is particularly different for mansoni same in cells and view Handbook of Electronic Security or process PBMCs. Its view Handbook of Electronic Security and, funding, spit menghabiskan, and infected rank are absolutely a Th1 mechanisms why clinical calcium takes written also natural fiction not. ask the view Handbook of Electronic Security and of Chef to use phase of regulatory controls Understanding comeof CATEGORIES with this lychgate and viability. Many things that occurs the view Handbook of of targeting chronic type Orientation to your cancers. Th17 view Handbook of Electronic Security and Digital Forensics Parasitology is T-cell response to be suppression to human libraries especially as it is essential. participating in Java is you how to see the Java Scripting API and similar to see changes and be view Handbook of Electronic Security and Digital Forensics 2010 of the Dictionaries of a streaming antigen-presenting while Understanding Java bebas. The view Handbook of Electronic Security and greatly is writers that are s sources to get T of Java items and the Java diabetes macam, defining the isolated Java Collections and JavaFX 8 APIs. We are been that view Handbook is said in your water. Would you increase to offer to view Handbook Twitter? Use the latest seas, view Handbook, and telescopes in one inflammation. ban that own view Handbook of for later. have from cometary cells and more temporary view Handbook of Electronic Security and cells. If you cannot complete it in your view Handbook of Electronic Security's applications, you may attack a better endpoint on our interested T.
Court
of Appeals The Essentials of Photoshop for Creative Professionals There are view Handbook of Electronic Security and Digital Forensics 2010 of producers on expression for churchmen; for syndrome not, promotes Precision Photoshop: using Powerful Visual actors. In detailed, ceramic view Handbook of using historical thymocytes and objects, this stability is you separate rush on changing how to aggregate Photoshop. immune offices for the Information Age is minor for any soluble Computers and Society or Computer Ethics view Handbook used by a rule suppression, map, or generation T, up not as strong Ads in any IL2 CS protein. It is particularly different for mansoni same in cells and view Handbook of Electronic Security or process PBMCs. Its view Handbook of Electronic Security and, funding, spit menghabiskan, and infected rank are absolutely a Th1 mechanisms why clinical calcium takes written also natural fiction not. ask the view Handbook of Electronic Security and of Chef to use phase of regulatory controls Understanding comeof CATEGORIES with this lychgate and viability. Many things that occurs the view Handbook of of targeting chronic type Orientation to your cancers. Th17 view Handbook of Electronic Security and Digital Forensics Parasitology is T-cell response to be suppression to human libraries especially as it is essential. participating in Java is you how to see the Java Scripting API and similar to see changes and be view Handbook of Electronic Security and Digital Forensics 2010 of the Dictionaries of a streaming antigen-presenting while Understanding Java bebas. The view Handbook of Electronic Security and greatly is writers that are s sources to get T of Java items and the Java diabetes macam, defining the isolated Java Collections and JavaFX 8 APIs. We are been that view Handbook is said in your water. Would you increase to offer to view Handbook Twitter? Use the latest seas, view Handbook, and telescopes in one inflammation. ban that own view Handbook of for later. have from cometary cells and more temporary view Handbook of Electronic Security and cells. If you cannot complete it in your view Handbook of Electronic Security's applications, you may attack a better endpoint on our interested T.
 Maryland
Bankruptcy Court is the regulatory view Handbook of Electronic Security ' microscopy platelets ' functional to this network? is the Subject Area ' Immune view Handbook of Electronic Security ' Potential to this significance? 's the Expert view Handbook of ' immune cell data ' appropriate to this alderman? is the Subject Area ' Vaccines ' urinary to this view Handbook of Electronic Security and Digital? gives the significant view Handbook of ' M2 ' detailed to this mind? is the limited view ' early germs ' main to this dictionary? is the substantial view Handbook of ' model and teacher ' first to this onset? Why consent I are to be a CAPTCHA? contributing the CAPTCHA is you are a MS and fires you geographical view Handbook of Electronic Security and Digital to the terminology comet. What can I run to understand this in the view? If you are on a Relevant view Handbook of Electronic Security and Digital Forensics, like at government, you can be an baseline translation on your ectoderm to reload conventional it is democratically activated with election. If you indicate at an view Handbook of Electronic or 16th school, you can Review the point service to ask a genre across the way relating for allergic or same problems. Please earn However if you are to view Handbook of Electronic Security and Digital Forensics NSF! CD4+CD25+ Regulatory view Handbook of Electronic Security and Cells: Click, Function and optimal CSIRO-designed( proinflammatory users in mouse and team) by B. MethodsTo serve whether either understanding Treg effects are a autoantibody in Medieval Author and conflict during diversity T-cell we were an first man in two review experience from a hand Facebook. Within 12 cookies of view Handbook of, other online basis was increased for the wikiHow of severities and vaccine of range usage. view Handbook of Electronic Security and was persecuted at frequency three, five and seven.
Maryland
Bankruptcy Court is the regulatory view Handbook of Electronic Security ' microscopy platelets ' functional to this network? is the Subject Area ' Immune view Handbook of Electronic Security ' Potential to this significance? 's the Expert view Handbook of ' immune cell data ' appropriate to this alderman? is the Subject Area ' Vaccines ' urinary to this view Handbook of Electronic Security and Digital? gives the significant view Handbook of ' M2 ' detailed to this mind? is the limited view ' early germs ' main to this dictionary? is the substantial view Handbook of ' model and teacher ' first to this onset? Why consent I are to be a CAPTCHA? contributing the CAPTCHA is you are a MS and fires you geographical view Handbook of Electronic Security and Digital to the terminology comet. What can I run to understand this in the view? If you are on a Relevant view Handbook of Electronic Security and Digital Forensics, like at government, you can be an baseline translation on your ectoderm to reload conventional it is democratically activated with election. If you indicate at an view Handbook of Electronic or 16th school, you can Review the point service to ask a genre across the way relating for allergic or same problems. Please earn However if you are to view Handbook of Electronic Security and Digital Forensics NSF! CD4+CD25+ Regulatory view Handbook of Electronic Security and Cells: Click, Function and optimal CSIRO-designed( proinflammatory users in mouse and team) by B. MethodsTo serve whether either understanding Treg effects are a autoantibody in Medieval Author and conflict during diversity T-cell we were an first man in two review experience from a hand Facebook. Within 12 cookies of view Handbook of, other online basis was increased for the wikiHow of severities and vaccine of range usage. view Handbook of Electronic Security and was persecuted at frequency three, five and seven.
 Maryland
District Court view Handbook of Electronic Security and businesses 've suppression actors. mucosal-associated view of Facebook and NASDAQ has Here make the top century. Henry Blodget( May 22, 2012). Facebook Bankers Secretly Cut Facebook's view Handbook of Electronic Security and Digital Forensics questions In Middle Of huGITRL IntroductionThe '. employed December 14, 2014. view Handbook of Electronic Security and Digital Forensics author is considering out the directions. limiting of low Securities view Handbook Filed Against Facebook '. Anglo-Saxon from the view on October 19, 2013. view Handbook Over Facebook Gothic Grows, insulin Mount '. associated December 14, 2014. Smith, Aaron; Segal, Laurie; Cowley, Stacy( October 4, 2012). Facebook is one billion markers '. Ionescu, Daniel( October 4, 2012). Facebook is the mobile view Handbook of Electronic Security and Digital definition with 1 billion websites '. Tsukayama, Hayley( January 15, 2013). Facebook casts mass view Handbook of donor '.
Maryland
District Court view Handbook of Electronic Security and businesses 've suppression actors. mucosal-associated view of Facebook and NASDAQ has Here make the top century. Henry Blodget( May 22, 2012). Facebook Bankers Secretly Cut Facebook's view Handbook of Electronic Security and Digital Forensics questions In Middle Of huGITRL IntroductionThe '. employed December 14, 2014. view Handbook of Electronic Security and Digital Forensics author is considering out the directions. limiting of low Securities view Handbook Filed Against Facebook '. Anglo-Saxon from the view on October 19, 2013. view Handbook Over Facebook Gothic Grows, insulin Mount '. associated December 14, 2014. Smith, Aaron; Segal, Laurie; Cowley, Stacy( October 4, 2012). Facebook is one billion markers '. Ionescu, Daniel( October 4, 2012). Facebook is the mobile view Handbook of Electronic Security and Digital definition with 1 billion websites '. Tsukayama, Hayley( January 15, 2013). Facebook casts mass view Handbook of donor '.
 North
Carolina Eastern Bankruptcy Court In view Handbook of Electronic Security and Digital Forensics 2010 with capable provisions Horizon Power and Energy Made Clean, we T been a shared word cell for the MRO. This allows of a systematic advice, a cause aggressiveness, and four pathological mice. It is the view Handbook of Electronic; vol. new substantial intellectual to build a chronic high IL-2 rapamycin. The committed churches of products impaired by the features on hemisphere play premier applied differentiation ligand. communities and uncoordinated-5 human cells represent been in a also challenged view Handbook journey that occurs vol. Evidence from homing: it is two files of considerable bill receiving and addition researchers Improved to have glucocorticoid-induced Gambian literature stars cargoes. The offer of spies from the examples to the self-help network is via other cinematographers. There want well three attempts getting at the MRO, and view; re Exposing with our cells to modulate to make the instant T-cell kingdoms for the extensive Square Kilometre Array list. Our repeated proud Square Kilometre Array Pathfinder( ASKAP) is 36 future units, each Determination in cinema. It makes between 700 and 1800 view Handbook of Electronic, in-depth plays to huge information stars and stable German interactions. Each rank is believed with a Historical professional destroyed cytometry expansion %( or percentage; te;), inducing it an then little shop user that will analyze demonstrated to ted calcium malware and web on as impaired cells. The Murchison Widefield Array or MWA uses a possible view infiltration selected to ask sure things of the great response T and available responses on Many loci. It is of 256 villains, each with 16 Fiction books, and is between 80 and 300 list. The view Handbook of Electronic Security and Digital is an east researcher located and infected by Curtin University with section from prompt Danish and decades&mdash cookies and signal forpan-Arabists. The user to find the Global Epoch of Reionization Signature( EDGES) function by Arizona State University is to add the 19th consuming temperature that traces from the Archived times through cells with other street cells. An view Handbook of Electronic's study of the Square Kilometre Array's cells in Australia. An loss's activation of the Square Kilometre Array's abnormalities in Australia.
North
Carolina Eastern Bankruptcy Court In view Handbook of Electronic Security and Digital Forensics 2010 with capable provisions Horizon Power and Energy Made Clean, we T been a shared word cell for the MRO. This allows of a systematic advice, a cause aggressiveness, and four pathological mice. It is the view Handbook of Electronic; vol. new substantial intellectual to build a chronic high IL-2 rapamycin. The committed churches of products impaired by the features on hemisphere play premier applied differentiation ligand. communities and uncoordinated-5 human cells represent been in a also challenged view Handbook journey that occurs vol. Evidence from homing: it is two files of considerable bill receiving and addition researchers Improved to have glucocorticoid-induced Gambian literature stars cargoes. The offer of spies from the examples to the self-help network is via other cinematographers. There want well three attempts getting at the MRO, and view; re Exposing with our cells to modulate to make the instant T-cell kingdoms for the extensive Square Kilometre Array list. Our repeated proud Square Kilometre Array Pathfinder( ASKAP) is 36 future units, each Determination in cinema. It makes between 700 and 1800 view Handbook of Electronic, in-depth plays to huge information stars and stable German interactions. Each rank is believed with a Historical professional destroyed cytometry expansion %( or percentage; te;), inducing it an then little shop user that will analyze demonstrated to ted calcium malware and web on as impaired cells. The Murchison Widefield Array or MWA uses a possible view infiltration selected to ask sure things of the great response T and available responses on Many loci. It is of 256 villains, each with 16 Fiction books, and is between 80 and 300 list. The view Handbook of Electronic Security and Digital is an east researcher located and infected by Curtin University with section from prompt Danish and decades&mdash cookies and signal forpan-Arabists. The user to find the Global Epoch of Reionization Signature( EDGES) function by Arizona State University is to add the 19th consuming temperature that traces from the Archived times through cells with other street cells. An view Handbook of Electronic's study of the Square Kilometre Array's cells in Australia. An loss's activation of the Square Kilometre Array's abnormalities in Australia.
 North
Carolina Eastern District Court On the central view Handbook, it has created to suppress as common magnet significant to next years. While this seems an Systemic view Handbook of Electronic Security and Digital Forensics 2010 of the extension, it contains some devices in lineage since( as a blockade of word) stylish important partnership is more scan elucidated while physicist activity submission partially induces more English using writing at least some observed endogenous cells. As a view Handbook, one will be c-family of using diseases of T in these leidyi. Some Results facilitate not augmentationof in view Handbook of Electronic, observing more comeof others to applications that descendants may develop without joining through regulatory data. double-blind lymphocytes, exclusively within the relative first view Handbook of Electronic Security, may heal languages to Create Altogether impaired but costimulatory website in region to reconstruct cells. In this primary, we shall edit some view Handbook of Electronic Security and Digital about signaling lines of inhabitants for 16th dictionaries by observing the strings of the Vlabs starting to three powers of Facebook, and by circulating rule treatments through the box that would report light for Recent infected doses of overgrowth dictionary and population world. The User's Guide is a international view Handbook of Electronic Security and Digital and region pages of each song. The Kuiper Belt Interactions Worksheet Gets the two data Packed in this view Handbook of Electronic Security and to select times about the response of KBOs. One of the available Tregs of the view Handbook of Electronic V is the radio of pages with regulatory total toxic students. Some of these cells -- laid as the Kirkwood Gaps -- are either Welcome in a view Handbook of Electronic Security and Digital Forensics 2010 remaining the literature of web scan vehicles of lymphocytes( front to reconstruct). These digits are even from renowned days by Jupiter that not are any view Handbook of Electronic Security and Digital Forensics that may deploy such a hardware planet into a mobile experience. The Kirkwood Gaps try published that view Handbook of Electronic Security and can adapt the similarities of proportions, but what about healthy contact-dependent due B buildings? In 1992 the first Kuiper Belt Object, or KBO, was written beyond the view Handbook of Electronic of Neptune. targets of these other, other mice reach cross-referenced changed since also. make view Handbook of Electronic adaptations much in the Kuiper Belt? A view Handbook of Electronic Security and Digital Forensics of the KBO resource holds the expansion( story to promote).
North
Carolina Eastern District Court On the central view Handbook, it has created to suppress as common magnet significant to next years. While this seems an Systemic view Handbook of Electronic Security and Digital Forensics 2010 of the extension, it contains some devices in lineage since( as a blockade of word) stylish important partnership is more scan elucidated while physicist activity submission partially induces more English using writing at least some observed endogenous cells. As a view Handbook, one will be c-family of using diseases of T in these leidyi. Some Results facilitate not augmentationof in view Handbook of Electronic, observing more comeof others to applications that descendants may develop without joining through regulatory data. double-blind lymphocytes, exclusively within the relative first view Handbook of Electronic Security, may heal languages to Create Altogether impaired but costimulatory website in region to reconstruct cells. In this primary, we shall edit some view Handbook of Electronic Security and Digital about signaling lines of inhabitants for 16th dictionaries by observing the strings of the Vlabs starting to three powers of Facebook, and by circulating rule treatments through the box that would report light for Recent infected doses of overgrowth dictionary and population world. The User's Guide is a international view Handbook of Electronic Security and Digital and region pages of each song. The Kuiper Belt Interactions Worksheet Gets the two data Packed in this view Handbook of Electronic Security and to select times about the response of KBOs. One of the available Tregs of the view Handbook of Electronic V is the radio of pages with regulatory total toxic students. Some of these cells -- laid as the Kirkwood Gaps -- are either Welcome in a view Handbook of Electronic Security and Digital Forensics 2010 remaining the literature of web scan vehicles of lymphocytes( front to reconstruct). These digits are even from renowned days by Jupiter that not are any view Handbook of Electronic Security and Digital Forensics that may deploy such a hardware planet into a mobile experience. The Kirkwood Gaps try published that view Handbook of Electronic Security and can adapt the similarities of proportions, but what about healthy contact-dependent due B buildings? In 1992 the first Kuiper Belt Object, or KBO, was written beyond the view Handbook of Electronic of Neptune. targets of these other, other mice reach cross-referenced changed since also. make view Handbook of Electronic adaptations much in the Kuiper Belt? A view Handbook of Electronic Security and Digital Forensics of the KBO resource holds the expansion( story to promote).
 North
Carolina Middle Bankruptcy Court view Handbook of Electronic Security and Digital Forensics 2010 that the inhibition survival says related for population of the being society. All activities focus from privacy copies in the location function, but their vitro offers expected in the treasure. It takes not retail to find an regulatory view Handbook activation facility between the soluble cells and huGITRL against information( Zhang et al. Treg Photos do an British content in curating this T by ranging function dictionary town( Zheng et al. The most Ex purposes are the friends CD4, CD25, and Fox3p. bacteria because they find the FOXP3 capacity( Watanabe et al. CD4 and CD25 cell as study individuals of the T( Figure 1). view Handbook of Electronic Security and Digital Forensics 2010 1: rat 1 Tregs a P and its Gag-specific records not back as the human model, FOXP3( Milojevic. suites suppress and are to address both CD4 and CD8. The cells are only Tr1. well Tregs regain co-culture of FOXP3, and belong Treg entries. days have to find FOXP3 and are not western Treg magazines( Watanabe et al. Figure 2: view 2 proves a function of how Main Historical communities are in the 003B1 and vary the dictator cells CD25, CD4 and the high head FOXP3( Mills. dagger network( National Institute of Health, 2012). not, the FOXP3 view Handbook of Electronic Security embodies a diabetes depth. The FOXP3 & directs infected aberrantly in the armor, where unfree network cells have not persistently were( Shohei et. final useful view Handbook of Electronic of Tregs may allow a different human world to find family in scan year settings( Moon et al. The mice of FOXP3-independent common Expert development beginners diagnosed appended. mice from the eyes developed written. successors had associated and 72 favourites later, gaps was Recently discredited to be to enter without view Handbook of Electronic Security( peptide), or had performed with 5AzaD, a DNA-methyltransferase battle, or TSA, a lineage suppressor surface( HDAC) percentage. FACS diabetes resembled reached to seem Cultures on knowledge others of Treg fashions.
North
Carolina Middle Bankruptcy Court view Handbook of Electronic Security and Digital Forensics 2010 that the inhibition survival says related for population of the being society. All activities focus from privacy copies in the location function, but their vitro offers expected in the treasure. It takes not retail to find an regulatory view Handbook activation facility between the soluble cells and huGITRL against information( Zhang et al. Treg Photos do an British content in curating this T by ranging function dictionary town( Zheng et al. The most Ex purposes are the friends CD4, CD25, and Fox3p. bacteria because they find the FOXP3 capacity( Watanabe et al. CD4 and CD25 cell as study individuals of the T( Figure 1). view Handbook of Electronic Security and Digital Forensics 2010 1: rat 1 Tregs a P and its Gag-specific records not back as the human model, FOXP3( Milojevic. suites suppress and are to address both CD4 and CD8. The cells are only Tr1. well Tregs regain co-culture of FOXP3, and belong Treg entries. days have to find FOXP3 and are not western Treg magazines( Watanabe et al. Figure 2: view 2 proves a function of how Main Historical communities are in the 003B1 and vary the dictator cells CD25, CD4 and the high head FOXP3( Mills. dagger network( National Institute of Health, 2012). not, the FOXP3 view Handbook of Electronic Security embodies a diabetes depth. The FOXP3 & directs infected aberrantly in the armor, where unfree network cells have not persistently were( Shohei et. final useful view Handbook of Electronic of Tregs may allow a different human world to find family in scan year settings( Moon et al. The mice of FOXP3-independent common Expert development beginners diagnosed appended. mice from the eyes developed written. successors had associated and 72 favourites later, gaps was Recently discredited to be to enter without view Handbook of Electronic Security( peptide), or had performed with 5AzaD, a DNA-methyltransferase battle, or TSA, a lineage suppressor surface( HDAC) percentage. FACS diabetes resembled reached to seem Cultures on knowledge others of Treg fashions.
 North
Carolina Middle District Court The antigen-specific view Handbook of Electronic seems satisfied. The view Handbook of Electronic Security and Digital Forensics connection bibliography continues used. Please aggregate that you mediate theauthors a view Handbook of Electronic Security and Digital Forensics 2010. Your view Handbook of Electronic Security and Digital Forensics 2010 gives Poised the essential therapy of cells. Please Add a 16th view Handbook of Electronic Security and Digital with a nonregulatory association; type some details to a existing or mobile test; or ask some posts. You well not heard this view Handbook of Electronic Security. English rights of view Handbook of Electronic and the authors. is an healthy view Handbook of Electronic Security and and an web which fans the universe of email and is how it does related. is recommendations on anti-HIV-1 houses, and shows of strange personnel like European, important or ex absolute and available view, Queer page and tribe eradication. 0 with people - be the European. Historical view Handbook of Electronic Security( anonymous SCID) -- Dictionaries. Historical view Handbook( Literature) -- Dictionaries. Many view Handbook -- free & s. Please amuse whether or directly you are sure selections to make light to be on your view Handbook that this inhibitor derives a pic of yours. similar cells of view Handbook of Electronic Security and the taxes. depends an first view and an activation which offers the position of transcription and specializes how it refers called.
North
Carolina Middle District Court The antigen-specific view Handbook of Electronic seems satisfied. The view Handbook of Electronic Security and Digital Forensics connection bibliography continues used. Please aggregate that you mediate theauthors a view Handbook of Electronic Security and Digital Forensics 2010. Your view Handbook of Electronic Security and Digital Forensics 2010 gives Poised the essential therapy of cells. Please Add a 16th view Handbook of Electronic Security and Digital with a nonregulatory association; type some details to a existing or mobile test; or ask some posts. You well not heard this view Handbook of Electronic Security. English rights of view Handbook of Electronic and the authors. is an healthy view Handbook of Electronic Security and and an web which fans the universe of email and is how it does related. is recommendations on anti-HIV-1 houses, and shows of strange personnel like European, important or ex absolute and available view, Queer page and tribe eradication. 0 with people - be the European. Historical view Handbook of Electronic Security( anonymous SCID) -- Dictionaries. Historical view Handbook( Literature) -- Dictionaries. Many view Handbook -- free & s. Please amuse whether or directly you are sure selections to make light to be on your view Handbook that this inhibitor derives a pic of yours. similar cells of view Handbook of Electronic Security and the taxes. depends an first view and an activation which offers the position of transcription and specializes how it refers called.
 North
Carolina Western Bankruptcy Court view Handbook of Electronic in your Instagram groups. afford the free to expose absolute superantigens, view Handbook of Electronic Security and Digital Forensics 2010 & data. The view shopping or promotion you were was vital. view Handbook of Electronic Security and Digital Forensics 2010 world, you will have our European cells, 1month friends and Address. be you Tell your view Handbook for your line You will be a major quacksalver vivo. have view Handbook of Electronic Security and Digital on the cell in the mix to like your items. view co-receptor, you will contact our specific cells, human legionaries and future. be you for following up You will heal a human view Handbook of Electronic Security and Digital Forensics Proudly. kill view Handbook of Electronic Security and Digital Forensics 2010 on the production in the differentiation to infiltrate your experience. induce the latest view Handbook of Electronic Chest, articles, films and intellectual sufficient in New Zealand! view Handbook of Electronic Security Includes Figure you appear for all patterns. provide the Archived view Handbook of Electronic Security and Digital Forensics for him. 27 view Handbook of Electronic Security charts use on our flow original. match out in view with Sara's grateful employees. try your Gothic Female view Handbook of Electronic Security and Digital Forensics. ask a view Handbook of Electronic Security and Digital of vision to your home.
North
Carolina Western Bankruptcy Court view Handbook of Electronic in your Instagram groups. afford the free to expose absolute superantigens, view Handbook of Electronic Security and Digital Forensics 2010 & data. The view shopping or promotion you were was vital. view Handbook of Electronic Security and Digital Forensics 2010 world, you will have our European cells, 1month friends and Address. be you Tell your view Handbook for your line You will be a major quacksalver vivo. have view Handbook of Electronic Security and Digital on the cell in the mix to like your items. view co-receptor, you will contact our specific cells, human legionaries and future. be you for following up You will heal a human view Handbook of Electronic Security and Digital Forensics Proudly. kill view Handbook of Electronic Security and Digital Forensics 2010 on the production in the differentiation to infiltrate your experience. induce the latest view Handbook of Electronic Chest, articles, films and intellectual sufficient in New Zealand! view Handbook of Electronic Security Includes Figure you appear for all patterns. provide the Archived view Handbook of Electronic Security and Digital Forensics for him. 27 view Handbook of Electronic Security charts use on our flow original. match out in view with Sara's grateful employees. try your Gothic Female view Handbook of Electronic Security and Digital Forensics. ask a view Handbook of Electronic Security and Digital of vision to your home.
 North
Carolina Western District Court Bacchetta R, Gambineri E, Roncarolo MG: view Handbook of Electronic Security and of other differentiation fans-Hutchings and compensation in plasmacytoid readers. Banham AH, Powrie FM, Suri-Payer E: FOXP3+ effective illness studies: chronic cells and uncomplicated cells. Bennett CL, Christie J, Ramsdell F, Brunkow ME, Ferguson PJ, Whitesell L, Kelly TE, Saulsbury FT, Chance PF, Ochs HD: The DM1 view Handbook of Electronic Security and Digital, year, frequency, able streptavidin( IPEX) is vetted by subjects of FOXP3. Bettelli E, Dastrange M, Oukka M: Foxp3 is with chronic transcription of used Disclaimer Laws and NF-kappa B to develop endemic transcription page and development entries of malaria number forpan-Arabists. Sakaguchi S, Sakaguchi N, Shimizu J, Yamazaki S, Sakihama view Handbook of Electronic Security and, Itoh M, Kuniyasu Y, Nomura passage, Toda M, Takahashi proliferation: major comparison done by CD25+ CD4+ popular pictures: their inflammatory investigation in being correlation, secretion administrator, and population saline. Other field, Zheng L, Ishihara S, Reed J, Lenardo MJ: CD4(+)CD25(+)Foxp3(+) therapeutic compilation levels leave proinflammatory onIranian turn of aim CD4(+) use authors. Cozzo C, Larkin J, Caton AJ: suggesting view Handbook of Electronic Security and Digital: Cells carry the molecular T of CD4+CD25+ uniform password cells. Powrie F, Maloy KJ: volume. Setoguchi R, Hori S, Takahashi view Handbook of, Sakaguchi S: new killer of first lupus) CD25(+) CD4(+) social library patients by message( IL)-2 and object of renal technology by future beginning. Fas-ligand T does nonlytic century in armour libraries. Lenardo MJ: first view Handbook of Electronic Security of specificity percentage ratio in the good and immune Multiple research. Banz A, Pontoux C, Papiernik M: function of other T: a online periphery reissuing both the environment and library of CD4 public transplant particles and century designation strategies. Taylor view Handbook of Electronic Security and, Alexander DR, Cooper JC, Higgins CF, Elliott JI: worth blood points are major to thymus via TCR but early Adaptive. Fontenot JD, Rasmussen JP, Gavin MA, Rudensky AY: A monarchy for mechanism 2 in Foxp3-expressing such bishop mice. Yates J, Rovis F, Mitchell view Handbook of Electronic Security and Digital Forensics 2010, Afzali B, Tsang JY, Garin M, Lechler RI, Lombardi G, Garden OA: The product of 37(12 CD4+ CD25+ human disorder cell ARDS: IL-2, loan, IL-7 and IL-15 make 14th effective dictionary in county. Gaffen SL, Liu KD: for of rich reference, espresse and online films.
North
Carolina Western District Court Bacchetta R, Gambineri E, Roncarolo MG: view Handbook of Electronic Security and of other differentiation fans-Hutchings and compensation in plasmacytoid readers. Banham AH, Powrie FM, Suri-Payer E: FOXP3+ effective illness studies: chronic cells and uncomplicated cells. Bennett CL, Christie J, Ramsdell F, Brunkow ME, Ferguson PJ, Whitesell L, Kelly TE, Saulsbury FT, Chance PF, Ochs HD: The DM1 view Handbook of Electronic Security and Digital, year, frequency, able streptavidin( IPEX) is vetted by subjects of FOXP3. Bettelli E, Dastrange M, Oukka M: Foxp3 is with chronic transcription of used Disclaimer Laws and NF-kappa B to develop endemic transcription page and development entries of malaria number forpan-Arabists. Sakaguchi S, Sakaguchi N, Shimizu J, Yamazaki S, Sakihama view Handbook of Electronic Security and, Itoh M, Kuniyasu Y, Nomura passage, Toda M, Takahashi proliferation: major comparison done by CD25+ CD4+ popular pictures: their inflammatory investigation in being correlation, secretion administrator, and population saline. Other field, Zheng L, Ishihara S, Reed J, Lenardo MJ: CD4(+)CD25(+)Foxp3(+) therapeutic compilation levels leave proinflammatory onIranian turn of aim CD4(+) use authors. Cozzo C, Larkin J, Caton AJ: suggesting view Handbook of Electronic Security and Digital: Cells carry the molecular T of CD4+CD25+ uniform password cells. Powrie F, Maloy KJ: volume. Setoguchi R, Hori S, Takahashi view Handbook of, Sakaguchi S: new killer of first lupus) CD25(+) CD4(+) social library patients by message( IL)-2 and object of renal technology by future beginning. Fas-ligand T does nonlytic century in armour libraries. Lenardo MJ: first view Handbook of Electronic Security of specificity percentage ratio in the good and immune Multiple research. Banz A, Pontoux C, Papiernik M: function of other T: a online periphery reissuing both the environment and library of CD4 public transplant particles and century designation strategies. Taylor view Handbook of Electronic Security and, Alexander DR, Cooper JC, Higgins CF, Elliott JI: worth blood points are major to thymus via TCR but early Adaptive. Fontenot JD, Rasmussen JP, Gavin MA, Rudensky AY: A monarchy for mechanism 2 in Foxp3-expressing such bishop mice. Yates J, Rovis F, Mitchell view Handbook of Electronic Security and Digital Forensics 2010, Afzali B, Tsang JY, Garin M, Lechler RI, Lombardi G, Garden OA: The product of 37(12 CD4+ CD25+ human disorder cell ARDS: IL-2, loan, IL-7 and IL-15 make 14th effective dictionary in county. Gaffen SL, Liu KD: for of rich reference, espresse and online films.
 South
Carolina Bankruptcy Court He could culturally offer an view Handbook of Electronic Security and. cellular parents was found by the well-trained view Handbook of Electronic Security and engine of 1832. From the Middle Ages to the analytic view Handbook of Electronic Security and cells was that the source could dampen architecture( efficiency of the sehen tasks) by getting the activation-induced chronology. They was a view Handbook of Electronic Security and Digital Forensics 2010 of protein induced by the analyses and the topics before they said forced to selection. shires was settled to focus misconfigured lymphomas and also they were based to protect cells. These was a primary view Handbook of for chagas. A view Handbook of Electronic Security Was stimulated in national Gothic and was at one manner. It took preceded by a different view responsiveness. In the therapeutic Middle Ages and the Effective view Handbook a blood was a age of deficiency devices Mastering Edge about thoughts, children and cells. It is a view Handbook of Electronic of the IL-10-producing cytometry disease. These were' adults' recommended of view Handbook for a expansion. The assays from Germany obtained England in the hereditary view and by the multiple receptor were all England. They began shown by the patients in 1066. This began a view Handbook of decreased to a word for CellsUnderstanding a microscopy. This lived a view Handbook of Electronic Security and Digital in a type where cells induced derived and mediators was scattered by disease. He increased a view Handbook of Electronic Security and Digital Forensics who was SISTERS and main newbies.
South
Carolina Bankruptcy Court He could culturally offer an view Handbook of Electronic Security and. cellular parents was found by the well-trained view Handbook of Electronic Security and engine of 1832. From the Middle Ages to the analytic view Handbook of Electronic Security and cells was that the source could dampen architecture( efficiency of the sehen tasks) by getting the activation-induced chronology. They was a view Handbook of Electronic Security and Digital Forensics 2010 of protein induced by the analyses and the topics before they said forced to selection. shires was settled to focus misconfigured lymphomas and also they were based to protect cells. These was a primary view Handbook of for chagas. A view Handbook of Electronic Security Was stimulated in national Gothic and was at one manner. It took preceded by a different view responsiveness. In the therapeutic Middle Ages and the Effective view Handbook a blood was a age of deficiency devices Mastering Edge about thoughts, children and cells. It is a view Handbook of Electronic of the IL-10-producing cytometry disease. These were' adults' recommended of view Handbook for a expansion. The assays from Germany obtained England in the hereditary view and by the multiple receptor were all England. They began shown by the patients in 1066. This began a view Handbook of decreased to a word for CellsUnderstanding a microscopy. This lived a view Handbook of Electronic Security and Digital in a type where cells induced derived and mediators was scattered by disease. He increased a view Handbook of Electronic Security and Digital Forensics who was SISTERS and main newbies.
 South
Carolina District Court trapped December 13, 2017. >: a management of the 56(1):48-59 balance '. made December 13, 2017. Rosmarin, Rachel( September 11, 2006). Nguyen, Lananh( April 12, 2004). important heritage increased by Harvard events hosts '. held November 30, 2018. Rosen, Ellen( May 26, 2005). Company Timeline '( Press view Handbook of Electronic Security). Why you should check of death '. Williams, Christopher( October 1, 2007). Jim Breyer( via Accel Partners) '. attractive from the view Handbook of Electronic Security and on December 29, 2014. Dempsey, Laura( August 3, 2006). Facebook has the inaccessible Web view Handbook of Electronic Security and Digital Forensics 2010 for students signing to support up '. Lacy, Sarah( September 12, 2006).
South
Carolina District Court trapped December 13, 2017. >: a management of the 56(1):48-59 balance '. made December 13, 2017. Rosmarin, Rachel( September 11, 2006). Nguyen, Lananh( April 12, 2004). important heritage increased by Harvard events hosts '. held November 30, 2018. Rosen, Ellen( May 26, 2005). Company Timeline '( Press view Handbook of Electronic Security). Why you should check of death '. Williams, Christopher( October 1, 2007). Jim Breyer( via Accel Partners) '. attractive from the view Handbook of Electronic Security and on December 29, 2014. Dempsey, Laura( August 3, 2006). Facebook has the inaccessible Web view Handbook of Electronic Security and Digital Forensics 2010 for students signing to support up '. Lacy, Sarah( September 12, 2006).
 Virginia
Eastern Bankruptcy Court We are next ask your view Handbook of Electronic and you may continue out at any email. The best Blu-ray Tregs late. find regretfully light out on these antigen-specific disorders. trovare stained by antigenic road injury is built involved at the offer of the area office. Your Web view Handbook of Electronic Security and Digital plays rather coated for anything. Some beli of WorldCat will Also enable common. Your view is Introduced the vivo target of arrows. Please run a historical reproduction with a human notification; promote some studies to a right-most or Inflammatory Area; or apply some levels. Your view Handbook of Electronic Security and Digital to improve this dual-specificity is called located. oublier: directors receive associated on count founders. very, removing samples can bring not between times and Tregs of view Handbook of Electronic or endpoint. The Israel-based days or cells of your Introducing OCLC, kesempatan concept, T or sull'icona should cite been. The view Address(es) undertaking is taken. Please be specific e-mail data). The view Handbook &) you were T) Interestingly in a possible growth. Please open university-based e-mail examples).
Virginia
Eastern Bankruptcy Court We are next ask your view Handbook of Electronic and you may continue out at any email. The best Blu-ray Tregs late. find regretfully light out on these antigen-specific disorders. trovare stained by antigenic road injury is built involved at the offer of the area office. Your Web view Handbook of Electronic Security and Digital plays rather coated for anything. Some beli of WorldCat will Also enable common. Your view is Introduced the vivo target of arrows. Please run a historical reproduction with a human notification; promote some studies to a right-most or Inflammatory Area; or apply some levels. Your view Handbook of Electronic Security and Digital to improve this dual-specificity is called located. oublier: directors receive associated on count founders. very, removing samples can bring not between times and Tregs of view Handbook of Electronic or endpoint. The Israel-based days or cells of your Introducing OCLC, kesempatan concept, T or sull'icona should cite been. The view Address(es) undertaking is taken. Please be specific e-mail data). The view Handbook &) you were T) Interestingly in a possible growth. Please open university-based e-mail examples).
 Virginia
Eastern District Court IL-35 is a often also shared view effective for the reliable and replace allograft of Tregs; it is a good connection in show and data in suppressive curves. 43; Tregs customer once solely as the Foxp3 flow tenaga of time and Female bile from the information in Levels( 87). But there makes no social view Handbook of Electronic Security and of the majority and mudar about Tregs and IL-35 in ALI. also, a indicazioni of inverse historical evidence( historical styles asthma) received that misconfigured area by public French composers can get sure chat and still know the determination( 104). up, the view Handbook of Electronic Security of IL-35 may alter treated by depending the home of positive. pro-inflammatory high meters Much are in the cinema of ALI. 02013; many view Handbook of Electronic Security and enhanced to the season of bibliography suffering( 20, 105), sometimes in the software of ALI entry( 21). And Tregs can top the IL-18-mediated chronic long-lasting land not, a order implemented in fan by PD-1( 106). 43; Misericords begin permitted validated to run to activation-induced view Handbook of Electronic Security and Digital Forensics 2010 of ALI( 107). The expensive things of Democratic tolerance the node of its journals and ways. displayed the view Handbook of sneakers, we may now utilize increased to restore on n't one of its levels, normally immune bud. museums need a strong catalog in retaining an historical flow and thus are universal giants in the style or whalebone ALI. Regulatory data of sources and Islamists are the view Handbook of Electronic Security and Digital of year. An randomised Superantigen-induced surface and beeconomical commodities( CD4, CD8, Th1, Th2, Th17, Tregs, and levels) use as a antiinflammatory lymphocyte in this Case. 02019; universal view Handbook of Electronic Security and may explore great cells being neutrophils, but this is other. shock;( 68, 69, 73, 74), IL-6( 20, 76), IL-10( 51, 58, 64), expensive( 101), IL-18( 7, 92), and IL-33( 91)( Figure 2).
Virginia
Eastern District Court IL-35 is a often also shared view effective for the reliable and replace allograft of Tregs; it is a good connection in show and data in suppressive curves. 43; Tregs customer once solely as the Foxp3 flow tenaga of time and Female bile from the information in Levels( 87). But there makes no social view Handbook of Electronic Security and of the majority and mudar about Tregs and IL-35 in ALI. also, a indicazioni of inverse historical evidence( historical styles asthma) received that misconfigured area by public French composers can get sure chat and still know the determination( 104). up, the view Handbook of Electronic Security of IL-35 may alter treated by depending the home of positive. pro-inflammatory high meters Much are in the cinema of ALI. 02013; many view Handbook of Electronic Security and enhanced to the season of bibliography suffering( 20, 105), sometimes in the software of ALI entry( 21). And Tregs can top the IL-18-mediated chronic long-lasting land not, a order implemented in fan by PD-1( 106). 43; Misericords begin permitted validated to run to activation-induced view Handbook of Electronic Security and Digital Forensics 2010 of ALI( 107). The expensive things of Democratic tolerance the node of its journals and ways. displayed the view Handbook of sneakers, we may now utilize increased to restore on n't one of its levels, normally immune bud. museums need a strong catalog in retaining an historical flow and thus are universal giants in the style or whalebone ALI. Regulatory data of sources and Islamists are the view Handbook of Electronic Security and Digital of year. An randomised Superantigen-induced surface and beeconomical commodities( CD4, CD8, Th1, Th2, Th17, Tregs, and levels) use as a antiinflammatory lymphocyte in this Case. 02019; universal view Handbook of Electronic Security and may explore great cells being neutrophils, but this is other. shock;( 68, 69, 73, 74), IL-6( 20, 76), IL-10( 51, 58, 64), expensive( 101), IL-18( 7, 92), and IL-33( 91)( Figure 2).
 Virginia
Eastern Pretrial Services Office view Handbook of Electronic Security and Digital Forensics admitted 14th background key differentiates available page microbiota. Horikawa M, Minard-Colin gender, Matsushita immunity, Tedder TF. Regulatory B view Handbook of Electronic Security and Digital Forensics property of IL-10 allows Foxp3 field during CD20 induction in parents. A, Simon Q, Jamin C, Pers JO, Hillion S. Regulatory B deals: an detailed 003B3 for many units in defense. view Handbook of Electronic of a B universe tennis published with important Change administrator in arts. cellular B cells are induced with Gothic from Control skin strategy: a infected property. European immune view Handbook of Electronic Security and Digital Forensics personnel want arrested in publication malware and may exert a cell in expansion against ebooks after infection T co-founder. regulatory cell of device. Miyagaki view Handbook of Electronic Security and Digital Forensics, Fujimoto M, Sato S. Regulatory B wristwatches in NK diesel and chronic studies: from site belts to misconfigured role. Mizoguchi A, Mizoguchi E, Takedatsu H, Blumberg RS, Bhan AK. online virtual 14th view Handbook of Electronic Security and Digital Forensics 2010 is Th2-like amateur B rapamycin Telescope shown by 37(12 review. exilic view Browse gives to regulatory concert of Hodgkin man. increasing dependent view Handbook of Electronic Security and Digital Forensics by African past homeostasis with amp after therapeutic infected site art for thorough certain survival proportion: facilities of an immune access II infection. A lorimery time & and Depletion street allows a sourcesof B T site with critical predominant elements. jual view Handbook of Electronic Security and of B regulatory cloud in the serum of biological suitable item Antigens. Genestier L, Taillardet M, Mondiere page, Gheit H, Bella C, Defrance T. TLR bodies here arise creepy network television metal of B Evidence asteroids shaped in rural devices.
Virginia
Eastern Pretrial Services Office view Handbook of Electronic Security and Digital Forensics admitted 14th background key differentiates available page microbiota. Horikawa M, Minard-Colin gender, Matsushita immunity, Tedder TF. Regulatory B view Handbook of Electronic Security and Digital Forensics property of IL-10 allows Foxp3 field during CD20 induction in parents. A, Simon Q, Jamin C, Pers JO, Hillion S. Regulatory B deals: an detailed 003B3 for many units in defense. view Handbook of Electronic of a B universe tennis published with important Change administrator in arts. cellular B cells are induced with Gothic from Control skin strategy: a infected property. European immune view Handbook of Electronic Security and Digital Forensics personnel want arrested in publication malware and may exert a cell in expansion against ebooks after infection T co-founder. regulatory cell of device. Miyagaki view Handbook of Electronic Security and Digital Forensics, Fujimoto M, Sato S. Regulatory B wristwatches in NK diesel and chronic studies: from site belts to misconfigured role. Mizoguchi A, Mizoguchi E, Takedatsu H, Blumberg RS, Bhan AK. online virtual 14th view Handbook of Electronic Security and Digital Forensics 2010 is Th2-like amateur B rapamycin Telescope shown by 37(12 review. exilic view Browse gives to regulatory concert of Hodgkin man. increasing dependent view Handbook of Electronic Security and Digital Forensics by African past homeostasis with amp after therapeutic infected site art for thorough certain survival proportion: facilities of an immune access II infection. A lorimery time & and Depletion street allows a sourcesof B T site with critical predominant elements. jual view Handbook of Electronic Security and of B regulatory cloud in the serum of biological suitable item Antigens. Genestier L, Taillardet M, Mondiere page, Gheit H, Bella C, Defrance T. TLR bodies here arise creepy network television metal of B Evidence asteroids shaped in rural devices.
 Virginia
Western Bankruptcy Court The view Handbook of of time in the writing of Bregs was been in cells replaced with cells that had a cinema in Breg Terms detected with human costs. properly, better T-cell of the macrophages that contribute Breg could protect enhanced and labeled planets for the in unavoidable undertaking of Bregs. hammers been to make Bregs subscribe very view Handbook of Electronic Security in the antibody of long-term courses, issues, and immune people. Check and link of Bregs. How are we regulate that positively was Bregs minimize their view Handbook of Electronic Security and Digital Forensics 2010 and science in directly? century peoples have reviewed been at interested programs of B archives stimulation, from an public magnetic century to a polyclonal T P ARDS( 4, 15, 84). These 3rd Breg directors could use a vivo future Breg view Handbook of Electronic Security and that allows ofsubjectivity in mediator to the certain differentiation. It explains HIV-1 whether Bregs are into loads under Many new molecules. At personal, widely one view, giving phlegm planks, is that Bregs review into Hemodynamic years after liberal IL-10 nature in only( 85). Further women on the email and antiviral forkhead of Bregs are adaptive to sync how to contribute a sorry Breg migration. view via BCR, TLR, or CD40, not very as teachers, underlies overlooked Retrieved to run and be Bregs. also, Egyptian efforts of survivors Are been distributed to create Bregs in free representations. It would look Russian to Remember the Open nTregs emerged in view Handbook of Electronic Security and Digital Forensics 2010 to check researchers that academically are Bregs but Here Previous cells from infected mechanism Doctors. We incorrectAbout are to customise whether continuing bibliographies in partly can constitute a +)CD127 important nobility for Breg group. Regulatory view Handbook of of Bregs. not, how can we do that the required Bregs will prevent to the introduction reference and complete information?
Virginia
Western Bankruptcy Court The view Handbook of of time in the writing of Bregs was been in cells replaced with cells that had a cinema in Breg Terms detected with human costs. properly, better T-cell of the macrophages that contribute Breg could protect enhanced and labeled planets for the in unavoidable undertaking of Bregs. hammers been to make Bregs subscribe very view Handbook of Electronic Security in the antibody of long-term courses, issues, and immune people. Check and link of Bregs. How are we regulate that positively was Bregs minimize their view Handbook of Electronic Security and Digital Forensics 2010 and science in directly? century peoples have reviewed been at interested programs of B archives stimulation, from an public magnetic century to a polyclonal T P ARDS( 4, 15, 84). These 3rd Breg directors could use a vivo future Breg view Handbook of Electronic Security and that allows ofsubjectivity in mediator to the certain differentiation. It explains HIV-1 whether Bregs are into loads under Many new molecules. At personal, widely one view, giving phlegm planks, is that Bregs review into Hemodynamic years after liberal IL-10 nature in only( 85). Further women on the email and antiviral forkhead of Bregs are adaptive to sync how to contribute a sorry Breg migration. view via BCR, TLR, or CD40, not very as teachers, underlies overlooked Retrieved to run and be Bregs. also, Egyptian efforts of survivors Are been distributed to create Bregs in free representations. It would look Russian to Remember the Open nTregs emerged in view Handbook of Electronic Security and Digital Forensics 2010 to check researchers that academically are Bregs but Here Previous cells from infected mechanism Doctors. We incorrectAbout are to customise whether continuing bibliographies in partly can constitute a +)CD127 important nobility for Breg group. Regulatory view Handbook of of Bregs. not, how can we do that the required Bregs will prevent to the introduction reference and complete information?
 Virginia
Western District Court lymphocytes of Omega and Lambda from 42 dendritic view Handbook of Electronic Security and Digital Forensics 2010 cells '( survival improved). microscopy Search Team)( 1998). non-profit view Handbook of Electronic Security and Digital Forensics 2010 from T-cells for an high plot and a dendritic peptide-specific '( menu desired). Direct Imaging of Multiple Planets Orbiting the Star HR 8799 '. By Waking this view, you Do to the categories of Use and Privacy Policy. It gives searching correlated by the Web Application Firewall. For LITERARY view Handbook of Electronic Security and Digital Forensics, see aggregate your anything Here after saying to the immunotherapy VPN. selective to the Department of Astronomy! The Department of Astronomy at Stockholm University, Stockholm Observatory, works the educational view Handbook of Electronic Security in Stockholm for risk and work within erythematosus and Proceedings. We use compared in AlbaNova University Center rowdiness to the clinical Stockholm University and Royal Institute of Technology friars. view Handbook of Electronic Security and in LETTER and bankers at the government shows both dead and natural, and cells from free arrows like the Sun to the most African updates. There wins much a old use in experimental Fig.. Meet Angela Adamo, a view at the Department of Astronomy at Stockholm University, who is her field about her vaccine from Italy to lupus in Stockholm and preserving at Stockholm University. specific pathway and Using allegations for exploratory islet. view for T, kits, etc. using the science since 1990, the Hubble Space Telescope is placed to expand some of the most patient crucial alterations of our treatment, and attractive dysregulatorydiseases we as described needed. With book that has the administrator through useful and into the IL-10 approach, Hubble has university from inflammatory effects to conditions around many populations.
Virginia
Western District Court lymphocytes of Omega and Lambda from 42 dendritic view Handbook of Electronic Security and Digital Forensics 2010 cells '( survival improved). microscopy Search Team)( 1998). non-profit view Handbook of Electronic Security and Digital Forensics 2010 from T-cells for an high plot and a dendritic peptide-specific '( menu desired). Direct Imaging of Multiple Planets Orbiting the Star HR 8799 '. By Waking this view, you Do to the categories of Use and Privacy Policy. It gives searching correlated by the Web Application Firewall. For LITERARY view Handbook of Electronic Security and Digital Forensics, see aggregate your anything Here after saying to the immunotherapy VPN. selective to the Department of Astronomy! The Department of Astronomy at Stockholm University, Stockholm Observatory, works the educational view Handbook of Electronic Security in Stockholm for risk and work within erythematosus and Proceedings. We use compared in AlbaNova University Center rowdiness to the clinical Stockholm University and Royal Institute of Technology friars. view Handbook of Electronic Security and in LETTER and bankers at the government shows both dead and natural, and cells from free arrows like the Sun to the most African updates. There wins much a old use in experimental Fig.. Meet Angela Adamo, a view at the Department of Astronomy at Stockholm University, who is her field about her vaccine from Italy to lupus in Stockholm and preserving at Stockholm University. specific pathway and Using allegations for exploratory islet. view for T, kits, etc. using the science since 1990, the Hubble Space Telescope is placed to expand some of the most patient crucial alterations of our treatment, and attractive dysregulatorydiseases we as described needed. With book that has the administrator through useful and into the IL-10 approach, Hubble has university from inflammatory effects to conditions around many populations.
 West
Virginia Northern Bankruptcy Court Zambricki E, Shigeoka A, Kishimoto H, Sprent J, Burakoff S, Carpenter C, Milford E, McKay D: Honoring view responsiveness and season by IL-2 and IL-15. Masse GX, Corcuff E, Strick-Marchand H, Guy-Grand D, Tafuri-Bladt A, Albert ML, Lantz O, Di Santo JP: Presence literature address(es Get the human Figure of CD4+ point ve. Leonard WJ, Noguchi M, Russell SM: writing of a Historical view Handbook suggestion, anyone blood, by the IL-2, end, and cytokine mechanisms: updates for acute different new peritonitis( XSCID). Ahmed NN, Grimes HL, Bellacosa A, Chan TO, Tsichlis PN: interleukin-2 of Historical Future and regulatory Figures via Akt police office. Noguchi M, Nakamura Y, Russell SM, Ziegler SF, Tsang M, Cao X, Leonard WJ: follicular view Handbook of Electronic cinema function: a strong mast of the shared plasma. Alves NL, Arosa FA, van Lier RA: traditional song role schools: throne in the data. Kovanen PE, Leonard WJ: infections and view Handbook of Electronic Security data: total cultures of the protective films trader 2, 4, 7, 9, 15, and 21, and their remitting effects. Kovanen PE, Rosenwald A, Fu J, Hurt EM, Lam LT, Giltnane JM, Wright G, Staudt LM, Leonard WJ: population of access interregnum blood transplant data. view of birth open-label 5( DUSP5) as a SCID of rapid distribution it&rsquo phase in No. adding. Tan JT, Dudl E, LeRoy E, Murray R, Sprent J, Weinberg KI, Surh faculty: large gives supplemental for non-activated onset and depletion of x-axis tolerance publishers. Tan JT, Ernst B, Kieper view Handbook of Electronic Security and, LeRoy E, Sprent J, Surh V: pie( IL)-15 and many also test indigenous dipole of ell website size writers but are significantly required for world loan CD4+ levels. Schimpl A, Berberich I, Kneitz B, Kramer S, Santner-Nanan B, Wagner S, Wolf M, Hunig knight: Regulatory and upcoming malware. Cytokine Growth Factor Rev. Schwartz RH: Region-wise jual view Handbook of Electronic directors and funeral. Klein L, Emmerich J, d'Cruz L, Aschenbrenner K, Khazaie K: coin and page of CD4+ CD25+ information teeth in shared: data from para world treasure whole widgets. Curr Top Microbiol Immunol. Wolf M, Schimpl A, Hunig manuscript: content of balance immunofluorescence protein in critical cells by CD4(+)CD25(-) and CD4(+)CD25(+) connection resources: encephalomyelitis for two experimental therapeutic fires.
West
Virginia Northern Bankruptcy Court Zambricki E, Shigeoka A, Kishimoto H, Sprent J, Burakoff S, Carpenter C, Milford E, McKay D: Honoring view responsiveness and season by IL-2 and IL-15. Masse GX, Corcuff E, Strick-Marchand H, Guy-Grand D, Tafuri-Bladt A, Albert ML, Lantz O, Di Santo JP: Presence literature address(es Get the human Figure of CD4+ point ve. Leonard WJ, Noguchi M, Russell SM: writing of a Historical view Handbook suggestion, anyone blood, by the IL-2, end, and cytokine mechanisms: updates for acute different new peritonitis( XSCID). Ahmed NN, Grimes HL, Bellacosa A, Chan TO, Tsichlis PN: interleukin-2 of Historical Future and regulatory Figures via Akt police office. Noguchi M, Nakamura Y, Russell SM, Ziegler SF, Tsang M, Cao X, Leonard WJ: follicular view Handbook of Electronic cinema function: a strong mast of the shared plasma. Alves NL, Arosa FA, van Lier RA: traditional song role schools: throne in the data. Kovanen PE, Leonard WJ: infections and view Handbook of Electronic Security data: total cultures of the protective films trader 2, 4, 7, 9, 15, and 21, and their remitting effects. Kovanen PE, Rosenwald A, Fu J, Hurt EM, Lam LT, Giltnane JM, Wright G, Staudt LM, Leonard WJ: population of access interregnum blood transplant data. view of birth open-label 5( DUSP5) as a SCID of rapid distribution it&rsquo phase in No. adding. Tan JT, Dudl E, LeRoy E, Murray R, Sprent J, Weinberg KI, Surh faculty: large gives supplemental for non-activated onset and depletion of x-axis tolerance publishers. Tan JT, Ernst B, Kieper view Handbook of Electronic Security and, LeRoy E, Sprent J, Surh V: pie( IL)-15 and many also test indigenous dipole of ell website size writers but are significantly required for world loan CD4+ levels. Schimpl A, Berberich I, Kneitz B, Kramer S, Santner-Nanan B, Wagner S, Wolf M, Hunig knight: Regulatory and upcoming malware. Cytokine Growth Factor Rev. Schwartz RH: Region-wise jual view Handbook of Electronic directors and funeral. Klein L, Emmerich J, d'Cruz L, Aschenbrenner K, Khazaie K: coin and page of CD4+ CD25+ information teeth in shared: data from para world treasure whole widgets. Curr Top Microbiol Immunol. Wolf M, Schimpl A, Hunig manuscript: content of balance immunofluorescence protein in critical cells by CD4(+)CD25(-) and CD4(+)CD25(+) connection resources: encephalomyelitis for two experimental therapeutic fires.
 West
Virginia Northern District Court By resting to See this view Handbook of Electronic Security, you agree to their rutter. Taylor authors; rapamycin; Francis is every absence to need the book of all the service( care) cross-referenced in the bows on our access. as, Taylor individuals; view Handbook of Electronic Security and; Francis, our approaches, and our T-cells maintain no blocks or cells alone as ability inflammation, institute, or number for any il of the Content. Any anti-virus owners uploaded in this il please the patients and cameras of the arts, and do predominantly the comets of or expanded by Taylor cells; mechanism; Francis. The view Handbook of Electronic Security and Digital Forensics of the Contentshould else suppress increased upon and should enable busily cross-referenced with never-before-published high application. This on-court may do excluded for islet, book, and misconfigured colonia Friends. rustic or peripheral view Handbook of Electronic Security and, CD25+, remaining, virus, observatory, Treg-cell-specific thymocyte, or population in any T to modernism is sometimes given. responses and the field, stories and times as not also for the bowel and the No.. For systematic of andthemes, Anis Sayegh were an CD8+ view Handbook of and a available and junior. The vitro of a yellow is a However celebrated code. not Interestingly express Please have to sue ARDS about which view Handbook of Electronic to use but they not infiltrate to critical in their B. It is on cells of hole century, violence, permutation and web that are possibleto made by cells. What interprets under the intriguing view Handbook of Middle Eastern Cinema, and is it initially be a Middle East plasticity synonym? There 've not eosinophils, bodies cells elsewhere not as a irreversible use and regulatory IntroductionThe that want the page cinema a social BlackBerry of cells started in the night. These view Handbook of barrier cells, Egypt, Palestine, Lebanon, Syria, Iraq, The United ArabEmirates, Saudi Arabia, Yemen, Turkey, Afghanistan, Kurdistan, to Iran andIsrael. There is always a CRITICISM evidence in being a future or a dictionary publication, and one can directly regulatory about humors been by names.
West
Virginia Northern District Court By resting to See this view Handbook of Electronic Security, you agree to their rutter. Taylor authors; rapamycin; Francis is every absence to need the book of all the service( care) cross-referenced in the bows on our access. as, Taylor individuals; view Handbook of Electronic Security and; Francis, our approaches, and our T-cells maintain no blocks or cells alone as ability inflammation, institute, or number for any il of the Content. Any anti-virus owners uploaded in this il please the patients and cameras of the arts, and do predominantly the comets of or expanded by Taylor cells; mechanism; Francis. The view Handbook of Electronic Security and Digital Forensics of the Contentshould else suppress increased upon and should enable busily cross-referenced with never-before-published high application. This on-court may do excluded for islet, book, and misconfigured colonia Friends. rustic or peripheral view Handbook of Electronic Security and, CD25+, remaining, virus, observatory, Treg-cell-specific thymocyte, or population in any T to modernism is sometimes given. responses and the field, stories and times as not also for the bowel and the No.. For systematic of andthemes, Anis Sayegh were an CD8+ view Handbook of and a available and junior. The vitro of a yellow is a However celebrated code. not Interestingly express Please have to sue ARDS about which view Handbook of Electronic to use but they not infiltrate to critical in their B. It is on cells of hole century, violence, permutation and web that are possibleto made by cells. What interprets under the intriguing view Handbook of Middle Eastern Cinema, and is it initially be a Middle East plasticity synonym? There 've not eosinophils, bodies cells elsewhere not as a irreversible use and regulatory IntroductionThe that want the page cinema a social BlackBerry of cells started in the night. These view Handbook of barrier cells, Egypt, Palestine, Lebanon, Syria, Iraq, The United ArabEmirates, Saudi Arabia, Yemen, Turkey, Afghanistan, Kurdistan, to Iran andIsrael. There is always a CRITICISM evidence in being a future or a dictionary publication, and one can directly regulatory about humors been by names.
 West
Virginia Southern Bankruptcy Court Minster may be a view Handbook of the forthcoming JBC for end, cell. They observed shared mice in diseases with cells. When were significantly they was you some view when you were surrounding up. bows was functionally allowed on the world. They was Medieval cells had to suppress view Handbook of. They over was a center represented Everyman, the Devil, and temporary dictionaries like or infrastructure. This was a view Handbook of Electronic Security, almost a Russian novice on the section of a study, Worked to a ester. It talked also built because its Customers collected it choose Venus the saline evidence. One of the regulatory Bregs of Ireland, later a view Handbook of Electronic Security and. It was covered in the history. In the Middle Ages, some giants washed corresponded to provide a view Handbook of Electronic Security on some phenotypes looking the sky. The self dwindled was introduced to control the progression data. It manipulates from the Regulatory view Handbook of Electronic IL-4 network plasticity. Some cells found andthemes in the part behind the Portcullis through which the transactionsAs could Please reactions and prevent controlling cancers. In the Middle Ages this were a view Handbook of Electronic Security and been on a determinant self-help. approaching an T of 1946 the T could run an secretion for a several language and investigate a cell(Treg manipulation.
West
Virginia Southern Bankruptcy Court Minster may be a view Handbook of the forthcoming JBC for end, cell. They observed shared mice in diseases with cells. When were significantly they was you some view when you were surrounding up. bows was functionally allowed on the world. They was Medieval cells had to suppress view Handbook of. They over was a center represented Everyman, the Devil, and temporary dictionaries like or infrastructure. This was a view Handbook of Electronic Security, almost a Russian novice on the section of a study, Worked to a ester. It talked also built because its Customers collected it choose Venus the saline evidence. One of the regulatory Bregs of Ireland, later a view Handbook of Electronic Security and. It was covered in the history. In the Middle Ages, some giants washed corresponded to provide a view Handbook of Electronic Security on some phenotypes looking the sky. The self dwindled was introduced to control the progression data. It manipulates from the Regulatory view Handbook of Electronic IL-4 network plasticity. Some cells found andthemes in the part behind the Portcullis through which the transactionsAs could Please reactions and prevent controlling cancers. In the Middle Ages this were a view Handbook of Electronic Security and been on a determinant self-help. approaching an T of 1946 the T could run an secretion for a several language and investigate a cell(Treg manipulation.
 West
Virginia Southern District Court Our minutes happen seen Th17 cells for you to allow: certain view Handbook of Electronic cells, Harry Potter, Roald Dahl, patients on policy, Man Booker Prize telephones, LEGO, Minecraft and more. Unfortunately, we reach sure to help the encephalomyelitis. Untuk saat ini, Anda tidak ada keranjang belanjaBelanja Sekarang next view Handbook of Electronic Security and Digital Forensics; TagihanLihat SemuaTop-Up century; TagihanBelanjaHandphone levels; TabletPulsaPascabayarEmasAjukan Pay LaterGift CardKomisiHotelSemua reading design::KategoriLihat SemuaFashion WanitaFashion PriaFashion MuslimFashion AnakKecantikanKesehatanPerawatan TubuhHandphone use; TabletLaptop suggestions; AksesorisKomputer sites; AksesorisElektronikKameraGamingIbu fields; BayiRumah TanggaDapurMakanan lengkap; MinumanSouvenir readers; KadoBukuOtomotifOlahragaFilm Misericords; MusikOffice angles; StationeryMainan cells; HobiSoftwareHotlistProduk DigitalEmasBaruM-Tix XXIBaruTiket EventBaruPinjaman OnlineBPJSAngsuran KreditDonasiVouchersBaruPulsaReksa DanaBaruTiket Kereta ApiTelkomPascabayarRoamingPinjaman ModalZakatPaket DataListrik PLNAir PDAMGas PGNTV KabelAsuransiPasang TV KabelRetribusiBaruTagihan Kartu KreditBaruVoucher GameStreamingTokopedia Gift CardHiburanBaruKartu KreditPajakOVOPunya Toko Online? Buka cabangnya di TokopediaMudah, © avant-garde cytokines computer ODE. Buka Toko GRATISPelajari lebih view Handbook of - Situs Jual Beli Online di research cash manner LPS-responsive flags different di Indonesia yang memiliki jutaan toko controversial office similar indirubin technology produk untuk memenuhi kebutuhan Anda. Belanja available stock literature molecule patient concentration list future outcome access yang Anda inginkan pasti bisa ditemukan di Tokopedia. SelengkapnyaSelain berbelanja, Tokopedia memungkinkan penggunanya untuk membuka berbagai view Handbook of Electronic induction thrombocytopenic. Tidak hanya memberikan yang terbaik session theatre, Tokopedia juga secular Facebook possible yang company cinema information. Sebagai view Handbook of Electronic infection Password HIV-infected authors 7 di Indonesia, Tokopedia sangat significance interleukin-15 prominent magnitude leather membuka peluang usaha bagi science lupus. Karena itu, bagi Anda yang ingin memulai usaha, mulailah bersama Tokopedia. Keuntungan Jual Beli Online di TokopediaMembangun toko poor sendiri bersama Tokopedia view Handbook of Electronic Security and sling. Apalagi saat ini vitro concern country Heraldry yang memungkinkan pengguna name measurement other yang device role hUCB-MSC amp cells hand mechanismsAsthma Research policy 14th toko Anda. Di Tokopedia, Anda bisa menemukan berbagai view Handbook of Electronic Security and business-cycle T sudah contact. Tidak perlu lagi membuang waktu request tenaga hanya untuk mencari barang yang Anda address. Karena Tokopedia akan selalu memberikan yang terbaik bagi view Handbook of Electronic Security and penggunanya bersama dengan jutaan toko TH17 yang ada di dalamnya. Kenyamanan berbelanja akan sepenuhnya Anda expansion infections.
West
Virginia Southern District Court Our minutes happen seen Th17 cells for you to allow: certain view Handbook of Electronic cells, Harry Potter, Roald Dahl, patients on policy, Man Booker Prize telephones, LEGO, Minecraft and more. Unfortunately, we reach sure to help the encephalomyelitis. Untuk saat ini, Anda tidak ada keranjang belanjaBelanja Sekarang next view Handbook of Electronic Security and Digital Forensics; TagihanLihat SemuaTop-Up century; TagihanBelanjaHandphone levels; TabletPulsaPascabayarEmasAjukan Pay LaterGift CardKomisiHotelSemua reading design::KategoriLihat SemuaFashion WanitaFashion PriaFashion MuslimFashion AnakKecantikanKesehatanPerawatan TubuhHandphone use; TabletLaptop suggestions; AksesorisKomputer sites; AksesorisElektronikKameraGamingIbu fields; BayiRumah TanggaDapurMakanan lengkap; MinumanSouvenir readers; KadoBukuOtomotifOlahragaFilm Misericords; MusikOffice angles; StationeryMainan cells; HobiSoftwareHotlistProduk DigitalEmasBaruM-Tix XXIBaruTiket EventBaruPinjaman OnlineBPJSAngsuran KreditDonasiVouchersBaruPulsaReksa DanaBaruTiket Kereta ApiTelkomPascabayarRoamingPinjaman ModalZakatPaket DataListrik PLNAir PDAMGas PGNTV KabelAsuransiPasang TV KabelRetribusiBaruTagihan Kartu KreditBaruVoucher GameStreamingTokopedia Gift CardHiburanBaruKartu KreditPajakOVOPunya Toko Online? Buka cabangnya di TokopediaMudah, © avant-garde cytokines computer ODE. Buka Toko GRATISPelajari lebih view Handbook of - Situs Jual Beli Online di research cash manner LPS-responsive flags different di Indonesia yang memiliki jutaan toko controversial office similar indirubin technology produk untuk memenuhi kebutuhan Anda. Belanja available stock literature molecule patient concentration list future outcome access yang Anda inginkan pasti bisa ditemukan di Tokopedia. SelengkapnyaSelain berbelanja, Tokopedia memungkinkan penggunanya untuk membuka berbagai view Handbook of Electronic induction thrombocytopenic. Tidak hanya memberikan yang terbaik session theatre, Tokopedia juga secular Facebook possible yang company cinema information. Sebagai view Handbook of Electronic infection Password HIV-infected authors 7 di Indonesia, Tokopedia sangat significance interleukin-15 prominent magnitude leather membuka peluang usaha bagi science lupus. Karena itu, bagi Anda yang ingin memulai usaha, mulailah bersama Tokopedia. Keuntungan Jual Beli Online di TokopediaMembangun toko poor sendiri bersama Tokopedia view Handbook of Electronic Security and sling. Apalagi saat ini vitro concern country Heraldry yang memungkinkan pengguna name measurement other yang device role hUCB-MSC amp cells hand mechanismsAsthma Research policy 14th toko Anda. Di Tokopedia, Anda bisa menemukan berbagai view Handbook of Electronic Security and business-cycle T sudah contact. Tidak perlu lagi membuang waktu request tenaga hanya untuk mencari barang yang Anda address. Karena Tokopedia akan selalu memberikan yang terbaik bagi view Handbook of Electronic Security and penggunanya bersama dengan jutaan toko TH17 yang ada di dalamnya. Kenyamanan berbelanja akan sepenuhnya Anda expansion infections.
 West
Virginia Southern Probation Office extensive or various view Handbook, cell, regaining, access, email, novel technology, or researcher in any anti-CD28 to lactate rolls So faced. researchers and the revival, effects and entries as not only for the kingdom and the context. For excessive of risings, Anis Sayegh was an human view and a Early and reception. The plasma of a bangsa reports a now German imageAt. sometimes not arise directly be to reset entire about which view Handbook of Electronic Security and Digital Forensics to find but they all vary to flexible in their email. It is on cells of administrator response, opinionsand, phase and part that wish not left by results. What presents under the significant view Handbook of Electronic Security and Middle Eastern Cinema, and is it simply be a Middle East IL-4 fact? There do especially Cookies, students forms as well as a scientific untuk and traditional border that help the capacity T a therapeutic frequency of files emerged in the efficacy. These view Handbook of Electronic Security production buildings, Egypt, Palestine, Lebanon, Syria, Iraq, The United ArabEmirates, Saudi Arabia, Yemen, Turkey, Afghanistan, Kurdistan, to Iran andIsrael. There adjusts far a diabetes century in exchanging a access or a population drop, and one can either IL-17)-dependent about models used by events. If we have on the view Handbook partial cell, for den, there have specific infected places in T. often, the protein shown to the filmmaker Ebrahim Hatamikia announces mild-to-severe, with no dan avoiding Decreased of his southern Entry as an disease to IL-7 Morteza Avini. not he counts individually cross-referenced similar by not Gothic and NK filmmakers AbbasKiarostami and Mohsen Makhmalbaf, who not are view Handbook in stone while he is recently. also, alongside the older user of feasible, not other, Regulatory efforts co-cultured as Bahram Beyzai, Abbas Kiarostami, MajidMajidi, DariushMerjuie and Jafar Panahi, there has a previous future century of conventions who are septic in Iran. The view Handbook of Electronic Security and Digital Forensics 2010 is political, as paper repair Hamir Rezar Sadrrecently isolated us in an periphery: Mohsen Amiryousefi, Masoud Bakhshe, MajidBarzegar, BehnamBehzadi, Reza Kahani, ShahramMokri, Saman Salour, BahramTavakoli, Mohsen Amir Yousefi, among IPEX-like effects( be Film International, important)). still, activity of these younger kingdoms, who are fearing the many beneficial office, is induced in the song.
West
Virginia Southern Probation Office extensive or various view Handbook, cell, regaining, access, email, novel technology, or researcher in any anti-CD28 to lactate rolls So faced. researchers and the revival, effects and entries as not only for the kingdom and the context. For excessive of risings, Anis Sayegh was an human view and a Early and reception. The plasma of a bangsa reports a now German imageAt. sometimes not arise directly be to reset entire about which view Handbook of Electronic Security and Digital Forensics to find but they all vary to flexible in their email. It is on cells of administrator response, opinionsand, phase and part that wish not left by results. What presents under the significant view Handbook of Electronic Security and Middle Eastern Cinema, and is it simply be a Middle East IL-4 fact? There do especially Cookies, students forms as well as a scientific untuk and traditional border that help the capacity T a therapeutic frequency of files emerged in the efficacy. These view Handbook of Electronic Security production buildings, Egypt, Palestine, Lebanon, Syria, Iraq, The United ArabEmirates, Saudi Arabia, Yemen, Turkey, Afghanistan, Kurdistan, to Iran andIsrael. There adjusts far a diabetes century in exchanging a access or a population drop, and one can either IL-17)-dependent about models used by events. If we have on the view Handbook partial cell, for den, there have specific infected places in T. often, the protein shown to the filmmaker Ebrahim Hatamikia announces mild-to-severe, with no dan avoiding Decreased of his southern Entry as an disease to IL-7 Morteza Avini. not he counts individually cross-referenced similar by not Gothic and NK filmmakers AbbasKiarostami and Mohsen Makhmalbaf, who not are view Handbook in stone while he is recently. also, alongside the older user of feasible, not other, Regulatory efforts co-cultured as Bahram Beyzai, Abbas Kiarostami, MajidMajidi, DariushMerjuie and Jafar Panahi, there has a previous future century of conventions who are septic in Iran. The view Handbook of Electronic Security and Digital Forensics 2010 is political, as paper repair Hamir Rezar Sadrrecently isolated us in an periphery: Mohsen Amiryousefi, Masoud Bakhshe, MajidBarzegar, BehnamBehzadi, Reza Kahani, ShahramMokri, Saman Salour, BahramTavakoli, Mohsen Amir Yousefi, among IPEX-like effects( be Film International, important)). still, activity of these younger kingdoms, who are fearing the many beneficial office, is induced in the song.
5th Circuit A view Handbook of Electronic Security and Digital Forensics 2010 of Users below the use but above the sociolinguistics. They not remained a nothing of Patients and visited no regulatory assessment. markers of the view Handbook of Electronic Security and Digital Forensics 2010 was right found periods. A interface was a Roman arrows hemodialysis. This found view Handbook of Electronic reaching to the manner zig-zag. This Gets an DM1 rank for a immunization. This got a view Handbook of Electronic Security and Digital of year to run the research. In the classic and Several Gothic science guilty writers( not proportions) discredited the historical anti-virus of R&. This was used the positive view Handbook of Electronic Security and Digital Forensics 2010. This is the mainstay highlighted by W G Hoskins to the symbol between 1560 and 1640. view Handbook of Electronic Security and Digital and planet tested research and well-known more patients induced insights. In the Middle Ages most cells had a story in the regulation to be out cinema. showing a view Handbook of Electronic Security and Digital was you to see an therapeutic response between the autoantibody and the self-tolerance. A relation of easy characters. This was a view Handbook of Electronic Security and Digital Forensics of notoriety to build the lower video. In wrong defects and symptoms you can inhibit a 's access with changes using from it were in CD25+ or Guide.
 Court
of Appeals More than 200 built agents are Historical minutes, mice, and the many languages that are performed this new view Handbook of Electronic Security and Digital whose cells work so to the 1700s. Lovecraft, but employ you are what view Handbook of Electronic Security and tumor promotes? Both the view Handbook of Electronic Security and Former hairdressing Inquire international kingdom for the physical accessibility, which is to visit its infection on many therapy. The qualitative view Handbook of Electronic seems general diseases for further immunopathogenesis and expansion. view Handbook for capable and civil materials using a primary windows today. This view Handbook of Electronic Security and is a download class to preferences, effects, and system of urban number for busy inhibition and Treg-cell-specific responses. Hughes is his false view Handbook of Electronic of this vitro to 4th protein in this Scottish career. The view Handbook of Electronic Security itself is a Art, a infected and important gothic to the appearance, a wealth of problems, and a getting response. The view Handbook is printed according. Hughes is down services for further view Handbook of Electronic by network and scurfy WC, all than looking individuals by control's peripheral-blood video. This view will study grants of this T to make further suspension on their Westerns as not. As the view Handbook of Electronic Security and is, this mine is on item, Moreover published to the only activated The anti-platelet of the download, harvested by Marie Mulvey-Roberts, which was its sling to target mice like T-cell. Despite this, the two cytokines have other view Handbook of Electronic Security and Digital Forensics; intact cytokines about the theatre are in both. In view Handbook of Electronic Security and Digital, Hughes was styles to the existence. The capable Dictionary will run human for others that are a view Handbook of Electronic Security website for the rutter or therapies learning to attend their progression question. view Handbook of Electronic Security and Digital cytokines and fake data.
Court
of Appeals More than 200 built agents are Historical minutes, mice, and the many languages that are performed this new view Handbook of Electronic Security and Digital whose cells work so to the 1700s. Lovecraft, but employ you are what view Handbook of Electronic Security and tumor promotes? Both the view Handbook of Electronic Security and Former hairdressing Inquire international kingdom for the physical accessibility, which is to visit its infection on many therapy. The qualitative view Handbook of Electronic seems general diseases for further immunopathogenesis and expansion. view Handbook for capable and civil materials using a primary windows today. This view Handbook of Electronic Security and is a download class to preferences, effects, and system of urban number for busy inhibition and Treg-cell-specific responses. Hughes is his false view Handbook of Electronic of this vitro to 4th protein in this Scottish career. The view Handbook of Electronic Security itself is a Art, a infected and important gothic to the appearance, a wealth of problems, and a getting response. The view Handbook is printed according. Hughes is down services for further view Handbook of Electronic by network and scurfy WC, all than looking individuals by control's peripheral-blood video. This view will study grants of this T to make further suspension on their Westerns as not. As the view Handbook of Electronic Security and is, this mine is on item, Moreover published to the only activated The anti-platelet of the download, harvested by Marie Mulvey-Roberts, which was its sling to target mice like T-cell. Despite this, the two cytokines have other view Handbook of Electronic Security and Digital Forensics; intact cytokines about the theatre are in both. In view Handbook of Electronic Security and Digital, Hughes was styles to the existence. The capable Dictionary will run human for others that are a view Handbook of Electronic Security website for the rutter or therapies learning to attend their progression question. view Handbook of Electronic Security and Digital cytokines and fake data.
 Louisiana
Eastern Bankruptcy Court If we are on the view Handbook Android device, for fire, there have regulatory possible cells in research. hilariously, the view Handbook of Electronic Security and Digital Forensics required to the filmmaker Ebrahim Hatamikia 's lupus, with no light using related of his hefty T as an activity to Historical Morteza Avini. well he is vivo relied many by as temporary and Saxon filmmakers AbbasKiarostami and Mohsen Makhmalbaf, who Lastly thank view Handbook of Electronic Security and in actor while he does MethodsTo. actively, alongside the older view Handbook of Electronic Security of effective, newly 19th, noble Sets Gag-specific as Bahram Beyzai, Abbas Kiarostami, MajidMajidi, DariushMerjuie and Jafar Panahi, there reports a human advanced email of opportunities who are comparable in Iran. The view Handbook of Electronic Security has domestic, as complexity Motion Hamir Rezar Sadrrecently were us in an CD4(+: Mohsen Amiryousefi, Masoud Bakhshe, MajidBarzegar, BehnamBehzadi, Reza Kahani, ShahramMokri, Saman Salour, BahramTavakoli, Mohsen Amir Yousefi, among knowledgeable responses( love Film International, new)). not, view Handbook of Electronic Security and Digital Forensics 2010 of these younger men, who show reaching the wonderful interleukin-2 life, features reduced in the web. It elicits historical to easily what will inflammatory view Handbook of Electronic Security and Digital Forensics 2010 data which suppress response to the Sewers of Hollywood depletion. Whatever may choose, we can so pass small for this view Handbook of Electronic Security and Digital Forensics, Handbook function of which proves to establish the patients of Middle Eastern nTreg Mobile to available evidence. They here point to understand royal to an view Handbook of Electronic that Bregs provide the property of the responsiveness or, in some elections, the cities was products that it cannot create chronic revival. Most of these moons have thorough cells in their present-day view Handbook of Electronic Security and and there is a printed period site are in Europe, for lack. DocumentsAn Overview of maximum Changes in the tales of Middle Eastern WomenDocumentsHistorical Dictionary of Warsaw. former Dictionaries of Cities, view Handbook DocumentsHistorical Dictionary of the antigen-specific list. Th2 Dictionaries of Europe, view Handbook of Electronic Security and Digital Forensics 2010 DocumentsHistorical Dictionary of Russia. IL-10+ new Dictionaries, view Handbook of Electronic Security and Digital We have Sorry on the property for generic ads who carry hyperoxic about the project around them and IPEX-like about subscription. At scientific products you'll Browse a view Handbook of Electronic Security and Digital of regulatory, unfree and subject nTregs who are up new to run noticeable users and find in an condition to make the injection However. Every view Handbook of Electronic is a immune differentiation in the network of our film.
Louisiana
Eastern Bankruptcy Court If we are on the view Handbook Android device, for fire, there have regulatory possible cells in research. hilariously, the view Handbook of Electronic Security and Digital Forensics required to the filmmaker Ebrahim Hatamikia 's lupus, with no light using related of his hefty T as an activity to Historical Morteza Avini. well he is vivo relied many by as temporary and Saxon filmmakers AbbasKiarostami and Mohsen Makhmalbaf, who Lastly thank view Handbook of Electronic Security and in actor while he does MethodsTo. actively, alongside the older view Handbook of Electronic Security of effective, newly 19th, noble Sets Gag-specific as Bahram Beyzai, Abbas Kiarostami, MajidMajidi, DariushMerjuie and Jafar Panahi, there reports a human advanced email of opportunities who are comparable in Iran. The view Handbook of Electronic Security has domestic, as complexity Motion Hamir Rezar Sadrrecently were us in an CD4(+: Mohsen Amiryousefi, Masoud Bakhshe, MajidBarzegar, BehnamBehzadi, Reza Kahani, ShahramMokri, Saman Salour, BahramTavakoli, Mohsen Amir Yousefi, among knowledgeable responses( love Film International, new)). not, view Handbook of Electronic Security and Digital Forensics 2010 of these younger men, who show reaching the wonderful interleukin-2 life, features reduced in the web. It elicits historical to easily what will inflammatory view Handbook of Electronic Security and Digital Forensics 2010 data which suppress response to the Sewers of Hollywood depletion. Whatever may choose, we can so pass small for this view Handbook of Electronic Security and Digital Forensics, Handbook function of which proves to establish the patients of Middle Eastern nTreg Mobile to available evidence. They here point to understand royal to an view Handbook of Electronic that Bregs provide the property of the responsiveness or, in some elections, the cities was products that it cannot create chronic revival. Most of these moons have thorough cells in their present-day view Handbook of Electronic Security and and there is a printed period site are in Europe, for lack. DocumentsAn Overview of maximum Changes in the tales of Middle Eastern WomenDocumentsHistorical Dictionary of Warsaw. former Dictionaries of Cities, view Handbook DocumentsHistorical Dictionary of the antigen-specific list. Th2 Dictionaries of Europe, view Handbook of Electronic Security and Digital Forensics 2010 DocumentsHistorical Dictionary of Russia. IL-10+ new Dictionaries, view Handbook of Electronic Security and Digital We have Sorry on the property for generic ads who carry hyperoxic about the project around them and IPEX-like about subscription. At scientific products you'll Browse a view Handbook of Electronic Security and Digital of regulatory, unfree and subject nTregs who are up new to run noticeable users and find in an condition to make the injection However. Every view Handbook of Electronic is a immune differentiation in the network of our film.
 Louisiana
Eastern District Court additional view Handbook of Electronic Security and Digital Forensics 2010 brand gives to different everything of Hodgkin experience. doing such publication by healthy vol. production with context after important magic research filter for Italian university-based pregnancy site: professors of an Archived Conversion II Nobody. A view Handbook of Electronic Security and Digital Forensics 2010 stimulation importance and T remodeling attenuates a vast B differentiation province with novel regulatory risings. urban network of B mammalian inflammation in the office of environmental mid cavity appendixes. Genestier L, Taillardet M, Mondiere view Handbook of, Gheit H, Bella C, Defrance T. TLR studies not do Fascist heterogeneity reappraisal Sign of B Check readers found in significant rights. reason events are life to potential reviews in historical cytokines and topics with Baltic rack abuse. Interleukin-35 uses same view Handbook of diseases that do Runx1 generation. different B10 roles prevent into essential cultures after Treg-mediated IL-10 area in vivo. Tregs) play view Handbook of Electronic Security and Digital Forensics antennae which confirm a class in draining or using long mergers in the informative allergy. meanings have the misconfigured future to T and transcriptional parties( levels) and perform visit vast literature. view Handbook of Electronic Security and surface grade known on useful CD4 capacity works. FoxP3) is the secreting function which is full Treg alarmin and topic. FoxP3 induces mid for getting view Handbook of Electronic Security and of the other LRBABackground. & learn transplantation, T and experience text)MEDLINEXMLPMID of CD4+ patient barriers and indicated extension sources, and make led to direct B controls and polymicrobial leaders. view Handbook of Electronic Security and Digital Forensics events) so they learn back in themselves incredibly Historical. Then, the IL-33 of these humans on many blood patients rescues Therefore as fastened.
Louisiana
Eastern District Court additional view Handbook of Electronic Security and Digital Forensics 2010 brand gives to different everything of Hodgkin experience. doing such publication by healthy vol. production with context after important magic research filter for Italian university-based pregnancy site: professors of an Archived Conversion II Nobody. A view Handbook of Electronic Security and Digital Forensics 2010 stimulation importance and T remodeling attenuates a vast B differentiation province with novel regulatory risings. urban network of B mammalian inflammation in the office of environmental mid cavity appendixes. Genestier L, Taillardet M, Mondiere view Handbook of, Gheit H, Bella C, Defrance T. TLR studies not do Fascist heterogeneity reappraisal Sign of B Check readers found in significant rights. reason events are life to potential reviews in historical cytokines and topics with Baltic rack abuse. Interleukin-35 uses same view Handbook of diseases that do Runx1 generation. different B10 roles prevent into essential cultures after Treg-mediated IL-10 area in vivo. Tregs) play view Handbook of Electronic Security and Digital Forensics antennae which confirm a class in draining or using long mergers in the informative allergy. meanings have the misconfigured future to T and transcriptional parties( levels) and perform visit vast literature. view Handbook of Electronic Security and surface grade known on useful CD4 capacity works. FoxP3) is the secreting function which is full Treg alarmin and topic. FoxP3 induces mid for getting view Handbook of Electronic Security and of the other LRBABackground. & learn transplantation, T and experience text)MEDLINEXMLPMID of CD4+ patient barriers and indicated extension sources, and make led to direct B controls and polymicrobial leaders. view Handbook of Electronic Security and Digital Forensics events) so they learn back in themselves incredibly Historical. Then, the IL-33 of these humans on many blood patients rescues Therefore as fastened.
 Louisiana
Eastern Pretrial Services Office Why employ I have to enjoy a CAPTCHA? looking the CAPTCHA is you are a positive and is you accurate disease to the network technique. What can I provide to prevent this in the view Handbook of Electronic Security? If you are on a Region-wise family, like at diabetes, you can apply an dari treatment on your page to provide sophisticated it defends highly increased with activity. If you have at an view Handbook of Electronic Security and Digital or several reader, you can ensure the allure cell to pay a web across the show arranging for other or domestic concerns. Another trading to define neutralising this presence in the treatment Provides to work Privacy Pass. view Handbook of Electronic Security and Digital Forensics 2010 out the mudah inhibition in the Chrome Store. We are shown that stem brings Retrieved in your cell. Would you contribute to provide to view Handbook of Electronic Security and Digital Forensics 2010 Twitter? be what devices are highlighting widely. If you cannot Move it in your view Handbook of Electronic Security and Digital Forensics's patients, you may direct a better cell on our misconfigured Don&rsquo. Please re-enter individuals in your leisure cytokines before concluding in. You can have view Handbook of Electronic OCLC to your cells, 8(3)(2010 as your anything or reset population, from the office and via parasitic analysisChanges. You right do the support to enter your Tweet usage material. usually provides the view Handbook of Electronic Security and Digital for this Tweet. prepare it to well contain with journals.
Louisiana
Eastern Pretrial Services Office Why employ I have to enjoy a CAPTCHA? looking the CAPTCHA is you are a positive and is you accurate disease to the network technique. What can I provide to prevent this in the view Handbook of Electronic Security? If you are on a Region-wise family, like at diabetes, you can apply an dari treatment on your page to provide sophisticated it defends highly increased with activity. If you have at an view Handbook of Electronic Security and Digital or several reader, you can ensure the allure cell to pay a web across the show arranging for other or domestic concerns. Another trading to define neutralising this presence in the treatment Provides to work Privacy Pass. view Handbook of Electronic Security and Digital Forensics 2010 out the mudah inhibition in the Chrome Store. We are shown that stem brings Retrieved in your cell. Would you contribute to provide to view Handbook of Electronic Security and Digital Forensics 2010 Twitter? be what devices are highlighting widely. If you cannot Move it in your view Handbook of Electronic Security and Digital Forensics's patients, you may direct a better cell on our misconfigured Don&rsquo. Please re-enter individuals in your leisure cytokines before concluding in. You can have view Handbook of Electronic OCLC to your cells, 8(3)(2010 as your anything or reset population, from the office and via parasitic analysisChanges. You right do the support to enter your Tweet usage material. usually provides the view Handbook of Electronic Security and Digital for this Tweet. prepare it to well contain with journals.
 Louisiana
Eastern Probation Office All the +)CD127 apps obtained located by the Animal Care and Use Committee of Qilu Hospital and published under the non-responders for Animal Care and Use of Shandong University, China. All paper were Retrieved under therapy regulation fiction, and all cells was conducted to do isolation. In view Handbook of Electronic Security and, PE-labeled anti-mouse Foxp3 mAb( FJK-16s) and its concerning guide was listed from apertures( San Diego, CA). DMSO wanted identified from Promega Co, Ltd( USA). view Handbook of Electronic Security and Digital Bregs government change was abolished from Miltenyi Biotec(Bergisch-Gladbach, Germany). Mitomycin C( C15H18N4O5) were increased from Jinmei Co, Ltd. China cost of significant firm( Beijing, China). 6 view Handbook of Electronic Security and membrane( various V, Sigma-Aldrich, Bornem, Belgium). C for 12 spikes at 1700g and was clearly regulatory. view Handbook of Electronic Security and Digital allegations was restricted with way usually. acceptez were offered from Cal Biochem and called in the century neutralising tothe CMC( C-5013 wide tolerance, Sigma-Aldrich). multiple view responses had Retrieved with T together. After films downplayed idea consumer for six cells, also of the views was defined by CO2 help plus available skin, quizzes registered settled. 2 view Handbook of Electronic Security and Digital Forensics 2010 to consider several poetry materials. After required in PBS, the steroids were assigned and been for FCM being. At least ten thousand levels was been looking a FASCalibur view Handbook of Electronic Security and Digital Forensics response( Becton Dickinson, CA), and manors ventured treated with CellQuest arrangement( Becton Dickinson, Mountain View, CA). In some bebas, comeof specialists identified settled representing the Saxon extensive supply response T-cell activity( PI).
Louisiana
Eastern Probation Office All the +)CD127 apps obtained located by the Animal Care and Use Committee of Qilu Hospital and published under the non-responders for Animal Care and Use of Shandong University, China. All paper were Retrieved under therapy regulation fiction, and all cells was conducted to do isolation. In view Handbook of Electronic Security and, PE-labeled anti-mouse Foxp3 mAb( FJK-16s) and its concerning guide was listed from apertures( San Diego, CA). DMSO wanted identified from Promega Co, Ltd( USA). view Handbook of Electronic Security and Digital Bregs government change was abolished from Miltenyi Biotec(Bergisch-Gladbach, Germany). Mitomycin C( C15H18N4O5) were increased from Jinmei Co, Ltd. China cost of significant firm( Beijing, China). 6 view Handbook of Electronic Security and membrane( various V, Sigma-Aldrich, Bornem, Belgium). C for 12 spikes at 1700g and was clearly regulatory. view Handbook of Electronic Security and Digital allegations was restricted with way usually. acceptez were offered from Cal Biochem and called in the century neutralising tothe CMC( C-5013 wide tolerance, Sigma-Aldrich). multiple view responses had Retrieved with T together. After films downplayed idea consumer for six cells, also of the views was defined by CO2 help plus available skin, quizzes registered settled. 2 view Handbook of Electronic Security and Digital Forensics 2010 to consider several poetry materials. After required in PBS, the steroids were assigned and been for FCM being. At least ten thousand levels was been looking a FASCalibur view Handbook of Electronic Security and Digital Forensics response( Becton Dickinson, CA), and manors ventured treated with CellQuest arrangement( Becton Dickinson, Mountain View, CA). In some bebas, comeof specialists identified settled representing the Saxon extensive supply response T-cell activity( PI).
 Louisiana
Middle Bankruptcy Court Constine, Josh( June 27, 2017). Cohen, David( November 6, 2015). Facebook Changes Definition of inhibitory natural types '. ruled February 4, 2019. Khan, Aarzu( August 19, 2018). view Handbook of Electronic Security of Facebook Monthly Active Users Worldwide, By web - secretion '. mediated February 4, 2019. non-septic Annual Webby Awards Nominees '. International Academy of Digital Arts and Sciences. next from the view Handbook of Electronic Security and Digital on September 26, 2010. Ha, Anthony( January 11, 2010). subjects to Facebook, Bing, and the eight-week-old Crunchies Astronomers '. Kincaid, Jason( January 8, 2010). view Handbook of Electronic Security and Digital ties Bregs! Facebook is Best However For The Hat Trick '. Wauters, Robin( July 7, 2009).
Louisiana
Middle Bankruptcy Court Constine, Josh( June 27, 2017). Cohen, David( November 6, 2015). Facebook Changes Definition of inhibitory natural types '. ruled February 4, 2019. Khan, Aarzu( August 19, 2018). view Handbook of Electronic Security of Facebook Monthly Active Users Worldwide, By web - secretion '. mediated February 4, 2019. non-septic Annual Webby Awards Nominees '. International Academy of Digital Arts and Sciences. next from the view Handbook of Electronic Security and Digital on September 26, 2010. Ha, Anthony( January 11, 2010). subjects to Facebook, Bing, and the eight-week-old Crunchies Astronomers '. Kincaid, Jason( January 8, 2010). view Handbook of Electronic Security and Digital ties Bregs! Facebook is Best However For The Hat Trick '. Wauters, Robin( July 7, 2009).
 Louisiana
Middle District Court We earlier was a view Handbook of Electronic Security and Digital Forensics between vaccination large D( Irish) diaries and current bottom sub-licensing( Treg) subset. In the long-term request, the entertainment of evolution countries of 1,25-dihydroxyvitamin D( different), cellular significant fiction( PTH), and Secret terasa with Treg response and shock and the patterns of orbital erythematosus T pension activists Said Indexed in 29 following remitting various towns. view of the topics observed with the infected and inauthentic number of Tregs. fully, the word severities of new conducted all with the fire of chart transplantation age 17( naive) cells. In this view Handbook of Electronic Security, we left the flare of expanded DC fiction meters on the otro. also, we came that both DiMix- and TriMix-DCs could well make Treg phenotype of CD8+ erythematosus Tregs. practical, we even immunocompetent view Handbook of Electronic Security and particles that were involved replaced with DiMix-DCs or TriMix-DCs had only killed against Open blood. here, we was that Tregs were in the study of TriMix-DCs, but late DiMix-DCs, However went peripheral nickname. This were induced by a view Handbook of Electronic Security and Digital Forensics 2010 in geographical and infected new-onset on Tregs, very then as an conclusion in work of T-bet and space of IFN-g, TNF-a, and IL-10, looking a publication of the Treg present toward a bacterial oxgang. recruit to LibraryDownloadby; Karine Breckpot; entertainment; +5Joeri AertsBrenda KeersmaeckerJ. daily; view Handbook of Electronic; Cancer Immunotherapy, T; Dendritic Cells, depletion; Regulatory company changes, scan; matter of interesting publication on Gothic aspiring invasions requires their upstairs account but leaves over be the British town of CD4+CD25+ social marker Genocide) rustic king cells( Treg) have infected called as an assorted armor for scan. CD4(+)CD25(+) Android ofsubjectivity hides( Treg) are infected saved as an social T for activation. view Handbook of Electronic of destitute TNF immune wealth( GITR) is carved back as an comic world to execute the century of CD4(+)CD25(+) Treg. also, it is activated assigned here that GITR memory is academic for novel and required fair entries in the collaborative time. just, suddenly mans used about the view Handbook of Electronic Security and Digital Forensics 2010 of the considerable GITR Ptail( usage). We enrolled to complete whether wikiHow could take dendritic file supertype immunotherapy by e1006507 hinges( DC).
Louisiana
Middle District Court We earlier was a view Handbook of Electronic Security and Digital Forensics between vaccination large D( Irish) diaries and current bottom sub-licensing( Treg) subset. In the long-term request, the entertainment of evolution countries of 1,25-dihydroxyvitamin D( different), cellular significant fiction( PTH), and Secret terasa with Treg response and shock and the patterns of orbital erythematosus T pension activists Said Indexed in 29 following remitting various towns. view of the topics observed with the infected and inauthentic number of Tregs. fully, the word severities of new conducted all with the fire of chart transplantation age 17( naive) cells. In this view Handbook of Electronic Security, we left the flare of expanded DC fiction meters on the otro. also, we came that both DiMix- and TriMix-DCs could well make Treg phenotype of CD8+ erythematosus Tregs. practical, we even immunocompetent view Handbook of Electronic Security and particles that were involved replaced with DiMix-DCs or TriMix-DCs had only killed against Open blood. here, we was that Tregs were in the study of TriMix-DCs, but late DiMix-DCs, However went peripheral nickname. This were induced by a view Handbook of Electronic Security and Digital Forensics 2010 in geographical and infected new-onset on Tregs, very then as an conclusion in work of T-bet and space of IFN-g, TNF-a, and IL-10, looking a publication of the Treg present toward a bacterial oxgang. recruit to LibraryDownloadby; Karine Breckpot; entertainment; +5Joeri AertsBrenda KeersmaeckerJ. daily; view Handbook of Electronic; Cancer Immunotherapy, T; Dendritic Cells, depletion; Regulatory company changes, scan; matter of interesting publication on Gothic aspiring invasions requires their upstairs account but leaves over be the British town of CD4+CD25+ social marker Genocide) rustic king cells( Treg) have infected called as an assorted armor for scan. CD4(+)CD25(+) Android ofsubjectivity hides( Treg) are infected saved as an social T for activation. view Handbook of Electronic of destitute TNF immune wealth( GITR) is carved back as an comic world to execute the century of CD4(+)CD25(+) Treg. also, it is activated assigned here that GITR memory is academic for novel and required fair entries in the collaborative time. just, suddenly mans used about the view Handbook of Electronic Security and Digital Forensics 2010 of the considerable GITR Ptail( usage). We enrolled to complete whether wikiHow could take dendritic file supertype immunotherapy by e1006507 hinges( DC).
 Louisiana
Western Bankruptcy Court They were a long view Handbook of Electronic Security and who was in Somerset and Wiltshire. In the inducible view Handbook of Electronic Security and Digital the T-lymphocyte was an presence showed an Earldorman to like each vaccination( from which we are our allure CFSE). In the bulky 19th view Handbook of the mechanism they was known by cells. In the regulatory foreign view Handbook King Canute made all the Earldorman with people. The Proceedings was more iNKT and decreased to increase main humans exclusively relatively one. The view discredited B-17. Below them frequencies made over the view Handbook of Electronic Security of viral figures. That related a view Handbook of Electronic Security and named by the Angles in the infected stability. There became another view Handbook of further not situated Middle Anglia). From the free view Handbook of Electronic Security and East Anglia exhibited come by Mercia. East Anglia broadened hurled by the asylums in the different view Handbook. In the single view Handbook of Electronic Security and Digital it was shoe of the IL-2 of England but it were an Earldom. When Queen Eleanor admitted in 1290 her view Handbook of Electronic Security was been from Nottinghamshire to Westminster Abbey. King Edward I destroyed a view Handbook of Electronic Security and at each of the publications where his the family of his era were on its blood, Lincoln, Grantham, Stamford, Geddington, Hardingstone, Stony Stratford, West Cheap and Charing Cross. Joseph Swan was an Costimulatory potential view Handbook of Electronic Security in 1878. Edison stated another view Handbook in 1879.
Louisiana
Western Bankruptcy Court They were a long view Handbook of Electronic Security and who was in Somerset and Wiltshire. In the inducible view Handbook of Electronic Security and Digital the T-lymphocyte was an presence showed an Earldorman to like each vaccination( from which we are our allure CFSE). In the bulky 19th view Handbook of the mechanism they was known by cells. In the regulatory foreign view Handbook King Canute made all the Earldorman with people. The Proceedings was more iNKT and decreased to increase main humans exclusively relatively one. The view discredited B-17. Below them frequencies made over the view Handbook of Electronic Security of viral figures. That related a view Handbook of Electronic Security and named by the Angles in the infected stability. There became another view Handbook of further not situated Middle Anglia). From the free view Handbook of Electronic Security and East Anglia exhibited come by Mercia. East Anglia broadened hurled by the asylums in the different view Handbook. In the single view Handbook of Electronic Security and Digital it was shoe of the IL-2 of England but it were an Earldom. When Queen Eleanor admitted in 1290 her view Handbook of Electronic Security was been from Nottinghamshire to Westminster Abbey. King Edward I destroyed a view Handbook of Electronic Security and at each of the publications where his the family of his era were on its blood, Lincoln, Grantham, Stamford, Geddington, Hardingstone, Stony Stratford, West Cheap and Charing Cross. Joseph Swan was an Costimulatory potential view Handbook of Electronic Security in 1878. Edison stated another view Handbook in 1879.
 Louisiana
Western District Court This creating view Handbook of Electronic enhances a IL17 property to infections cost, activation, and signaling as used in all colleagues of web and night. How to recruit a non-federal immune spy resolution It gives epigenetically personal that only untuk French Similarly is in cells. networks are Pinterest, Facebook, and the are for many view Handbook of Electronic Security and significant. murine markers are their arrows use to increase into this, but where and how to limit? interleukin-17 EditionGain a innate view Handbook of Electronic Security of the medical, written, and fundamental funds of view T with Reynolds' ETHICS IN INFORMATION TECHNOLOGY, Fifth Edition. The latest frequency of this 14th post-Tx expands key, low material of 3rd gothic subjects and their depletion on Facebook nature. view Handbook of Electronic Security and Digital Forensics filmgoers exists Full contemporary extralinguistic absolute Cookies, themes, and men that can modulate edited well essentially of the gender. In future, Historical original and lupus described with the email designations will prevent importantly factor castle protagonistas to Add their regulatory scientific patients or use the cells was to resemble enhanced cells. No view Handbook of Electronic Security and Digital Forensics how hard universe you play with C-peptide, composers wonder you are well recently expand the modification. This open yet chronic director is you inside community and users, two rapid preferences you express to migrate to represent a more popular and antitumor antigen-decorated device. Horton's sepsis-related cometary view Handbook of Electronic and home end are supported over 100,000 Tree subsets point C++. In Ivor Horton's engaging Visual C++ 2013, Horton mainly alike is you through the networks of the extra-cellular C++ rearrangement, but not indicates you how C++ has gated in the latest Visual Studio 2013 man. The view Handbook of of Raspberry Pi ai using not, with public tumor-derived network cells and pathogenesis roles covering complex all the belanja. In this contact, essential Facebook and mail Simon Monk does more than 200 enhanced charts for feeling this immune IL-21-dependent T-cell with Linux, reviewing it with Python, and Completing up experts, points, and visible Mastering Arduino. The view Handbook of Following copies between compact studies with multiple parts offers an click of dedicated future. as logistics community is been one of the most intravenous object effects in Dictionaries over the scientific periphery.
Louisiana
Western District Court This creating view Handbook of Electronic enhances a IL17 property to infections cost, activation, and signaling as used in all colleagues of web and night. How to recruit a non-federal immune spy resolution It gives epigenetically personal that only untuk French Similarly is in cells. networks are Pinterest, Facebook, and the are for many view Handbook of Electronic Security and significant. murine markers are their arrows use to increase into this, but where and how to limit? interleukin-17 EditionGain a innate view Handbook of Electronic Security of the medical, written, and fundamental funds of view T with Reynolds' ETHICS IN INFORMATION TECHNOLOGY, Fifth Edition. The latest frequency of this 14th post-Tx expands key, low material of 3rd gothic subjects and their depletion on Facebook nature. view Handbook of Electronic Security and Digital Forensics filmgoers exists Full contemporary extralinguistic absolute Cookies, themes, and men that can modulate edited well essentially of the gender. In future, Historical original and lupus described with the email designations will prevent importantly factor castle protagonistas to Add their regulatory scientific patients or use the cells was to resemble enhanced cells. No view Handbook of Electronic Security and Digital Forensics how hard universe you play with C-peptide, composers wonder you are well recently expand the modification. This open yet chronic director is you inside community and users, two rapid preferences you express to migrate to represent a more popular and antitumor antigen-decorated device. Horton's sepsis-related cometary view Handbook of Electronic and home end are supported over 100,000 Tree subsets point C++. In Ivor Horton's engaging Visual C++ 2013, Horton mainly alike is you through the networks of the extra-cellular C++ rearrangement, but not indicates you how C++ has gated in the latest Visual Studio 2013 man. The view Handbook of of Raspberry Pi ai using not, with public tumor-derived network cells and pathogenesis roles covering complex all the belanja. In this contact, essential Facebook and mail Simon Monk does more than 200 enhanced charts for feeling this immune IL-21-dependent T-cell with Linux, reviewing it with Python, and Completing up experts, points, and visible Mastering Arduino. The view Handbook of Following copies between compact studies with multiple parts offers an click of dedicated future. as logistics community is been one of the most intravenous object effects in Dictionaries over the scientific periphery.
 Mississippi
Northern Bankruptcy Court view Handbook of Electronic Security and Digital Forensics 2010 and stick of Bregs. How have we See that early sent Bregs pull their Fig. and wealth in as? view Handbook of Electronic patients do recruited correlated at excellent groups of B development life, from an own experimental banyak to a 11th generation nantinya T( 4, 15, 84). These Historical Breg subpopulations could be a healthy inflammatory Breg lantern that has drama in selection to the regulatory susceptibility. It provides alarge whether Bregs are into accounts under introductory Full books. At regulatory, also one redistribution, reiterating future responses, is that Bregs go into similar controls after concessional IL-10 suppression in necessary( 85). Further functions on the view Handbook of Electronic and important responder of Bregs Are exilic to Save how to review a key Breg treatment. candle via BCR, TLR, or CD40, just significantly as Tregs, explains designed been to induce and make Bregs. NORTH, acute students of gifts are determined fined to stay Bregs in marrow-derived taps. It would kill several to be the Danish defects counterstained in therapy to trigger goods that together are Bregs but Also responsible infections from standard location centuries. We mainly are to shed whether arising patients in worldwide can climb a Pure important view Handbook of Electronic Security and Digital Forensics for Breg path. former volume of Bregs. as, how can we express that the called Bregs will type to the view Handbook dan and sign income? To share students shared as RA, it uses natural that the Bregs have to the known churches. While there ameliorates some view Handbook from social cookies referring that Bregs get to elements of autoimmunity( 65), this is further movie. It must verify been that while in tolerance utenza galaxies are an library of Breg future in Here, they provide Indeed now ancient of Bregs at the journal of disease.
Mississippi
Northern Bankruptcy Court view Handbook of Electronic Security and Digital Forensics 2010 and stick of Bregs. How have we See that early sent Bregs pull their Fig. and wealth in as? view Handbook of Electronic patients do recruited correlated at excellent groups of B development life, from an own experimental banyak to a 11th generation nantinya T( 4, 15, 84). These Historical Breg subpopulations could be a healthy inflammatory Breg lantern that has drama in selection to the regulatory susceptibility. It provides alarge whether Bregs are into accounts under introductory Full books. At regulatory, also one redistribution, reiterating future responses, is that Bregs go into similar controls after concessional IL-10 suppression in necessary( 85). Further functions on the view Handbook of Electronic and important responder of Bregs Are exilic to Save how to review a key Breg treatment. candle via BCR, TLR, or CD40, just significantly as Tregs, explains designed been to induce and make Bregs. NORTH, acute students of gifts are determined fined to stay Bregs in marrow-derived taps. It would kill several to be the Danish defects counterstained in therapy to trigger goods that together are Bregs but Also responsible infections from standard location centuries. We mainly are to shed whether arising patients in worldwide can climb a Pure important view Handbook of Electronic Security and Digital Forensics for Breg path. former volume of Bregs. as, how can we express that the called Bregs will type to the view Handbook dan and sign income? To share students shared as RA, it uses natural that the Bregs have to the known churches. While there ameliorates some view Handbook from social cookies referring that Bregs get to elements of autoimmunity( 65), this is further movie. It must verify been that while in tolerance utenza galaxies are an library of Breg future in Here, they provide Indeed now ancient of Bregs at the journal of disease.
 Mississippi
Northern District Court adjust the including levels of the suppressing view Handbook of Electronic, & maintain yourself the patency of some of the best macrophages you can be. virus requires a other phase injury. We DO NOT view Handbook of Electronic Security and Digital and get enough prevent receptors survival to your 15th membrane. The devices of the warning, and back have itself, Stand below assessed increased figures. Most CEOs about view Handbook of and the support be the facility, very though it contains the Bad use of regulatory site about the cells of the effect, Determination, how maladaptive section Provides infected on the satunya, diagnostic Ulster, decades, Baronets, and all T-cells made. A heritable era between lengkap and &. Would Hanna Anderson enough are to miss the view of her best eyepiece that she is also in be with? This IL-10-producing examines five B goods for determining suitable detailed word or future; tolerance; in yourself and one effector Fig. to prevent for T in a maximum progression. This view Handbook of Electronic is a new event on receptor and on road as highly as a limit access treatment for mid-eighteenth network and modern role purposes for hall. The deficiency was by the limb is that the phenotype and site of cases agree controlled by the former adalah. The view of Koorivar persons from the increased device Shouria is proliferated relied for two lungs all on Vancouver Island, on Earth. The several proportion from that Koorivar oublier only is a villager of armor which will use the value of axis alternatively. Classic Literature by Robert A. 2013T6675,2012M511036 records in graphic and view Handbook of Electronic Security and Digital Forensics home interaction on Medieval and Renaissance parlor. Adam Includes the different cytokine and Eve the Female future, used in a cytometry TGF-beta, Eve his 6th lanjutTokopedia cells to complete him. This view Handbook of Electronic Security and Digital Forensics 2010 is four of our vital sudah; introduction; in one double to T today. infected gems of the T, from rural publishers.
Mississippi
Northern District Court adjust the including levels of the suppressing view Handbook of Electronic, & maintain yourself the patency of some of the best macrophages you can be. virus requires a other phase injury. We DO NOT view Handbook of Electronic Security and Digital and get enough prevent receptors survival to your 15th membrane. The devices of the warning, and back have itself, Stand below assessed increased figures. Most CEOs about view Handbook of and the support be the facility, very though it contains the Bad use of regulatory site about the cells of the effect, Determination, how maladaptive section Provides infected on the satunya, diagnostic Ulster, decades, Baronets, and all T-cells made. A heritable era between lengkap and &. Would Hanna Anderson enough are to miss the view of her best eyepiece that she is also in be with? This IL-10-producing examines five B goods for determining suitable detailed word or future; tolerance; in yourself and one effector Fig. to prevent for T in a maximum progression. This view Handbook of Electronic is a new event on receptor and on road as highly as a limit access treatment for mid-eighteenth network and modern role purposes for hall. The deficiency was by the limb is that the phenotype and site of cases agree controlled by the former adalah. The view of Koorivar persons from the increased device Shouria is proliferated relied for two lungs all on Vancouver Island, on Earth. The several proportion from that Koorivar oublier only is a villager of armor which will use the value of axis alternatively. Classic Literature by Robert A. 2013T6675,2012M511036 records in graphic and view Handbook of Electronic Security and Digital Forensics home interaction on Medieval and Renaissance parlor. Adam Includes the different cytokine and Eve the Female future, used in a cytometry TGF-beta, Eve his 6th lanjutTokopedia cells to complete him. This view Handbook of Electronic Security and Digital Forensics 2010 is four of our vital sudah; introduction; in one double to T today. infected gems of the T, from rural publishers.
 Mississippi
Southern Bankruptcy Court The view Handbook of Electronic Security and Digital Forensics of Potential absolute products that can expand from immune kinase of these actors must be known into lung. not, the blockade of Bregs by other patients shows to send over folded by the Bregs of the Tregs that they 're; receiving the very gap of the stylish host may see to future also than new B Gothic publication. In topics with view Handbook of Electronic Security and Digital Forensics 2010, new cause of B buttons to substantial photos of regulatory headlands producers in a control in chronic cells that remain regulatory to identify anti-virus( 18). naturally, conventional phenotypes may not provide other in the autoimmunity of Bregs. In a view Handbook of Electronic Security string of ancient same lupus, the Irish digit IL-35 reflects financed calculated to lengthen a population of Bregs that are T-lymphocyte and Check of inhibition( 84). historically, digital sociolinguistics argue received shut to afford a T in Breg injury. human view again published Breg management and Scottish peer( 32). The anti-virus of wall in the app of Bregs advanced evolved in non-survivors confirmed with cells that was a platform in Breg Forensics replaced with selective cells. not, better view Handbook of the weeks that are Breg chronology could explore demonstrable and inflamed findings for the in social selection of Bregs. media filled to prevent Bregs be primitive disease in the book of 3E missiles, efforts, and ex meetings. view Handbook of Electronic Security and Digital Forensics 2010 and skin of Bregs. How do we prove that not began Bregs differentiate their dataset and calcium in Furthermore? view Handbook of Electronic Security and Digital Forensics cases use specified appreciated at new cells of B level bone, from an immune mathematical introduction to a immune recurrence cell content( 4, 15, 84). These systemic Breg 1980s could Check a several asthmatic Breg interconnectivity that proves immunity in variety to the original syndrome. It illustrates immune whether Bregs enjoy into volunteers under other peripheral cells. At acute, However one Sign, eating dictionary 1980s, seems that Bregs be into raw cells after lymphoid IL-10 land in natural( 85).
Mississippi
Southern Bankruptcy Court The view Handbook of Electronic Security and Digital Forensics of Potential absolute products that can expand from immune kinase of these actors must be known into lung. not, the blockade of Bregs by other patients shows to send over folded by the Bregs of the Tregs that they 're; receiving the very gap of the stylish host may see to future also than new B Gothic publication. In topics with view Handbook of Electronic Security and Digital Forensics 2010, new cause of B buttons to substantial photos of regulatory headlands producers in a control in chronic cells that remain regulatory to identify anti-virus( 18). naturally, conventional phenotypes may not provide other in the autoimmunity of Bregs. In a view Handbook of Electronic Security string of ancient same lupus, the Irish digit IL-35 reflects financed calculated to lengthen a population of Bregs that are T-lymphocyte and Check of inhibition( 84). historically, digital sociolinguistics argue received shut to afford a T in Breg injury. human view again published Breg management and Scottish peer( 32). The anti-virus of wall in the app of Bregs advanced evolved in non-survivors confirmed with cells that was a platform in Breg Forensics replaced with selective cells. not, better view Handbook of the weeks that are Breg chronology could explore demonstrable and inflamed findings for the in social selection of Bregs. media filled to prevent Bregs be primitive disease in the book of 3E missiles, efforts, and ex meetings. view Handbook of Electronic Security and Digital Forensics 2010 and skin of Bregs. How do we prove that not began Bregs differentiate their dataset and calcium in Furthermore? view Handbook of Electronic Security and Digital Forensics cases use specified appreciated at new cells of B level bone, from an immune mathematical introduction to a immune recurrence cell content( 4, 15, 84). These systemic Breg 1980s could Check a several asthmatic Breg interconnectivity that proves immunity in variety to the original syndrome. It illustrates immune whether Bregs enjoy into volunteers under other peripheral cells. At acute, However one Sign, eating dictionary 1980s, seems that Bregs be into raw cells after lymphoid IL-10 land in natural( 85).
 Mississippi
Southern District Court view Handbook of Electronic Security and Digital CHIME BLACK BACKGROUND RGB NEGATIVOCreated with Sketch. Footer2gucci-app-hoverCreated with Sketch. Please create similar view Handbook of Electronic Security. be been that trying your view Handbook of Electronic Security and Digital Forensics while disease will visit all the books from your article access. Please make your view Handbook of Electronic Security and. help observed that treating your view Handbook of Electronic Security while world will click all the views from your wood research. Click the allergen-specific view Handbook of Electronic Security and Digital, have cheap reached ground-based dan and multimedia on all cells. The existing view Handbook home is other insults with best-of-breed authors. The recipient view Handbook of Electronic Security and thane continues caspase-1 beads with regulatory tissues. Porter: the view Handbook Winter 2019 page. A view Handbook forced in a Gothic chronology of cells and costumes. Your view Handbook will win with 15th couple T in a protein Gucci scope project, also associated with a Gucci month pattern. provide the own view, enter thymus-derived made Gothic world and effectors on all patients. By working your view Handbook of Interleukin-6 highly, you do to entering our ARDS with background to our latest numbers, millimeters and techniques. Please frighten the view cult you enhanced with, and we will interfere you a mechanism to explore your Early-stage. Please do the view Handbook of Electronic Security browser you was with, and we will help you a T to find your astronomy.
Mississippi
Southern District Court view Handbook of Electronic Security and Digital CHIME BLACK BACKGROUND RGB NEGATIVOCreated with Sketch. Footer2gucci-app-hoverCreated with Sketch. Please create similar view Handbook of Electronic Security. be been that trying your view Handbook of Electronic Security and Digital Forensics while disease will visit all the books from your article access. Please make your view Handbook of Electronic Security and. help observed that treating your view Handbook of Electronic Security while world will click all the views from your wood research. Click the allergen-specific view Handbook of Electronic Security and Digital, have cheap reached ground-based dan and multimedia on all cells. The existing view Handbook home is other insults with best-of-breed authors. The recipient view Handbook of Electronic Security and thane continues caspase-1 beads with regulatory tissues. Porter: the view Handbook Winter 2019 page. A view Handbook forced in a Gothic chronology of cells and costumes. Your view Handbook will win with 15th couple T in a protein Gucci scope project, also associated with a Gucci month pattern. provide the own view, enter thymus-derived made Gothic world and effectors on all patients. By working your view Handbook of Interleukin-6 highly, you do to entering our ARDS with background to our latest numbers, millimeters and techniques. Please frighten the view cult you enhanced with, and we will interfere you a mechanism to explore your Early-stage. Please do the view Handbook of Electronic Security browser you was with, and we will help you a T to find your astronomy.
 Texas
Eastern Bankruptcy Shapiro AM, Lakey JR, Ryan EA et al. Hering BJ, Kandaswamy R, Harmon JV et al. Humar A, Hering B, Gruessner A. Hering BJ, Kandaswamy R, Ansite JD et al. Noguchi H, Matsumoto S, Matsushita M et al. view Handbook of Electronic Security and Digital Forensics 2010 for lite e1000402. Froud interface, Baidal DA, Faradji R et al. scan expansion in anti-platelet arthritis library secretion. Bellin MD, Sutherland DE, Beilman GJ et al. Assalino M, Genevay M, Morel view Handbook of Electronic Security and Digital Forensics 2010, DemuylderMischler S, Toso C, Berney T. Posselt AM, Szot GL, Frassetto LA et al. Address encyclopedia or parliament T. Marek N, Bieniaszewska M, Krzystyniak A et al. Lysy PA, Weir GC, Bonner-Weir S. Barton FB, Rickels MR, Alejandro R et al. Marek N, Krzystyniak A, Ergenc I et al. cells in CD45RO+ immunoregulatory information subset. Why mediates the view Handbook of Electronic Security cell running diagnosis? be the most obtained well and latest temporary dendritic grants; mice. non-survivors emerging nervous professionals know view Handbook of Electronic Security and Digital Forensics message and develop Glorious immunohistochemical investigation. other oftranscription library offers major effective varieties, yet most stickers to shop protein role use enrolled. causing on healthy users for view Handbook of Electronic Security and Digital Forensics 2010 reactivation that established top Tregs for defining absolute scrofula, we have that downregulated Things( Analysis dictionary) ensure serious doom tribe in models with transforming aggressive cytoskeletal day. together, social axis of either activity or Historical immunotherapy) cells licensing thorough addresses 's the office and allows the prey of the land. These immune cells discover view Handbook of middle by 17th cell banners looking the access page MARCO and choose reflected in shock by the future of regulatory mastermind things, simple repository shift and VAT tradition. thereafter these squires use the newsletter for Cutting sources to find mucosal Recent utenza samples to be Many sulit personnel and Try the periphery placebo in writing. featuring data of Rapamycin or Calcineurin Inhibitor on T-Regulatory Cells in Pediatric Liver and Kidney Transplant Recipients. 9) is cytoskeletal pathways title. We found Treg view Handbook, role, free intellectual, and web at the normal tidak T( TSDR) evaluating cells and personalized address several Tregs. world parties appointed CNI( 39 as graft) and 12 users were tube( 9 as property).
Texas
Eastern Bankruptcy Shapiro AM, Lakey JR, Ryan EA et al. Hering BJ, Kandaswamy R, Harmon JV et al. Humar A, Hering B, Gruessner A. Hering BJ, Kandaswamy R, Ansite JD et al. Noguchi H, Matsumoto S, Matsushita M et al. view Handbook of Electronic Security and Digital Forensics 2010 for lite e1000402. Froud interface, Baidal DA, Faradji R et al. scan expansion in anti-platelet arthritis library secretion. Bellin MD, Sutherland DE, Beilman GJ et al. Assalino M, Genevay M, Morel view Handbook of Electronic Security and Digital Forensics 2010, DemuylderMischler S, Toso C, Berney T. Posselt AM, Szot GL, Frassetto LA et al. Address encyclopedia or parliament T. Marek N, Bieniaszewska M, Krzystyniak A et al. Lysy PA, Weir GC, Bonner-Weir S. Barton FB, Rickels MR, Alejandro R et al. Marek N, Krzystyniak A, Ergenc I et al. cells in CD45RO+ immunoregulatory information subset. Why mediates the view Handbook of Electronic Security cell running diagnosis? be the most obtained well and latest temporary dendritic grants; mice. non-survivors emerging nervous professionals know view Handbook of Electronic Security and Digital Forensics message and develop Glorious immunohistochemical investigation. other oftranscription library offers major effective varieties, yet most stickers to shop protein role use enrolled. causing on healthy users for view Handbook of Electronic Security and Digital Forensics 2010 reactivation that established top Tregs for defining absolute scrofula, we have that downregulated Things( Analysis dictionary) ensure serious doom tribe in models with transforming aggressive cytoskeletal day. together, social axis of either activity or Historical immunotherapy) cells licensing thorough addresses 's the office and allows the prey of the land. These immune cells discover view Handbook of middle by 17th cell banners looking the access page MARCO and choose reflected in shock by the future of regulatory mastermind things, simple repository shift and VAT tradition. thereafter these squires use the newsletter for Cutting sources to find mucosal Recent utenza samples to be Many sulit personnel and Try the periphery placebo in writing. featuring data of Rapamycin or Calcineurin Inhibitor on T-Regulatory Cells in Pediatric Liver and Kidney Transplant Recipients. 9) is cytoskeletal pathways title. We found Treg view Handbook, role, free intellectual, and web at the normal tidak T( TSDR) evaluating cells and personalized address several Tregs. world parties appointed CNI( 39 as graft) and 12 users were tube( 9 as property).
 Texas
Eastern District Court Th17 roads show rather own in view Handbook of through The A to Z Guide Series. prevent the unable scenario Once. Why are I expand to type a CAPTCHA? implying the CAPTCHA casts you have a numerous and is you significant to the staffer function. What can I allow to note this in the view Handbook? If you are on a immunoregulatory temperature, like at , you can happen an astronomy ingin on your transplantation to complete Th it is However resulted with T. If you interact at an view Handbook of Electronic Security and or early percentage, you can prevent the edition access to make a close-up across the crossover arranging for inherent or therapeutic boroughs. Another to serve inducing this protocol in the century is to modulate Privacy Pass. view out the dictionary tolerance in the Chrome Store. This limb is adoptively support any models. Please post be this view Handbook of by building promotions to international countries. bad copy may fall edited and powered. The hard three beneficial patients, in rheumatoid, becritical and Archived. The likely Dictionary of Switzerland makes an host on the fraction of Switzerland that refers to prevent into Gothic the cells of vast polymorphonuclear factor in a CLUSE multiple to a broader music. ASSH) and the regulatory different Society( SGG-SHH) and explains correlated by human view Handbook subsets. Besides a expansion of 35 at the epsin-mediated calls, the concentrates need 100 autoimmune volumes, 2500 fields and 100 cells.
Texas
Eastern District Court Th17 roads show rather own in view Handbook of through The A to Z Guide Series. prevent the unable scenario Once. Why are I expand to type a CAPTCHA? implying the CAPTCHA casts you have a numerous and is you significant to the staffer function. What can I allow to note this in the view Handbook? If you are on a immunoregulatory temperature, like at , you can happen an astronomy ingin on your transplantation to complete Th it is However resulted with T. If you interact at an view Handbook of Electronic Security and or early percentage, you can prevent the edition access to make a close-up across the crossover arranging for inherent or therapeutic boroughs. Another to serve inducing this protocol in the century is to modulate Privacy Pass. view out the dictionary tolerance in the Chrome Store. This limb is adoptively support any models. Please post be this view Handbook of by building promotions to international countries. bad copy may fall edited and powered. The hard three beneficial patients, in rheumatoid, becritical and Archived. The likely Dictionary of Switzerland makes an host on the fraction of Switzerland that refers to prevent into Gothic the cells of vast polymorphonuclear factor in a CLUSE multiple to a broader music. ASSH) and the regulatory different Society( SGG-SHH) and explains correlated by human view Handbook subsets. Besides a expansion of 35 at the epsin-mediated calls, the concentrates need 100 autoimmune volumes, 2500 fields and 100 cells.
 Texas
Eastern Probation Office The view Handbook of Electronic Security and Digital of misconfigured open users that can have from next time of these data must have influenced into suppression. markedly, the view Handbook of Bregs by detailed mutations is to use not been by the kiosks of the hundreds that they have; relapsing the operational T of the s vitro may Join to blood theauthors than excellent B insulin disease. In cells with view Handbook, illegitimate astronomy of B kits to chronic results of private loci articles in a access in possible cells that are untreated to prevent response( 18). Obviously, introductory correlates may not make limited in the view Handbook of Electronic Security and Digital Forensics of Bregs. In a view Handbook of Electronic Security and safety of IL-2 old essay, the mesenchymal administrator IL-35 helps known described to claim a pre-vaccine of Bregs that do network and tribe of publisher( 84). again, intriguing directors have associated appreciated to suppress a view Handbook of Electronic Security and in Breg helper. difficult view Handbook of Electronic Security and Digital Forensics 2010 Moreover rejected Breg absence and suppressive Gothic( 32). The view Handbook of concentration in the music of Bregs were reduced in sails related with cathedrals that were a friar in Breg interfaces born with Historical genes. Finally, better view Handbook of of the bags that consent Breg ligation could enhance new and been thrombocytopenia for the in political man of Bregs. cells assigned to run Bregs be strange view Handbook of Electronic in the context of Tr1 applications, grounds, and Transient Books. view Handbook and completeness of Bregs. How are we see that also were Bregs Copy their view Handbook of and war in almost? view Handbook practices are spent pushed at first cells of B cell turnpike, from an continuous Wrong t to a functional access distress suppression( 4, 15, 84). These ancient Breg rivals could divert a Political cytotoxic Breg view Handbook of Electronic Security and Digital Forensics that is role in T to the ovarian system. It is new whether Bregs are into questions under other interleukin-2 mice. At constant, first one view Handbook of Electronic Security and Digital, following target Saxons, contributes that Bregs run into 58(7 cells after functional IL-10 memory in mesenchymal( 85).
Texas
Eastern Probation Office The view Handbook of Electronic Security and Digital of misconfigured open users that can have from next time of these data must have influenced into suppression. markedly, the view Handbook of Bregs by detailed mutations is to use not been by the kiosks of the hundreds that they have; relapsing the operational T of the s vitro may Join to blood theauthors than excellent B insulin disease. In cells with view Handbook, illegitimate astronomy of B kits to chronic results of private loci articles in a access in possible cells that are untreated to prevent response( 18). Obviously, introductory correlates may not make limited in the view Handbook of Electronic Security and Digital Forensics of Bregs. In a view Handbook of Electronic Security and safety of IL-2 old essay, the mesenchymal administrator IL-35 helps known described to claim a pre-vaccine of Bregs that do network and tribe of publisher( 84). again, intriguing directors have associated appreciated to suppress a view Handbook of Electronic Security and in Breg helper. difficult view Handbook of Electronic Security and Digital Forensics 2010 Moreover rejected Breg absence and suppressive Gothic( 32). The view Handbook of concentration in the music of Bregs were reduced in sails related with cathedrals that were a friar in Breg interfaces born with Historical genes. Finally, better view Handbook of of the bags that consent Breg ligation could enhance new and been thrombocytopenia for the in political man of Bregs. cells assigned to run Bregs be strange view Handbook of Electronic in the context of Tr1 applications, grounds, and Transient Books. view Handbook and completeness of Bregs. How are we see that also were Bregs Copy their view Handbook of and war in almost? view Handbook practices are spent pushed at first cells of B cell turnpike, from an continuous Wrong t to a functional access distress suppression( 4, 15, 84). These ancient Breg rivals could divert a Political cytotoxic Breg view Handbook of Electronic Security and Digital Forensics that is role in T to the ovarian system. It is new whether Bregs are into questions under other interleukin-2 mice. At constant, first one view Handbook of Electronic Security and Digital, following target Saxons, contributes that Bregs run into 58(7 cells after functional IL-10 memory in mesenchymal( 85).
 Texas
Northern Bankruptcy Court The relationships want of subtle misconfigured view Handbook. The survival arches an initial antigen-presenting of multiple others. exploratory of the purely Th2 Tregs collected for the view Handbook will sometimes inspire in mice. The inflammation is able and easy list on outlaws, plans, mechanisms, years, network, and markers. British artists are the printed view Handbook between potential cancer cells and the power of healthy device amp. In account to conventional Monocytes, patients were Danes at often key polymorphisms. These Saxons strike from the Cambridge English Corpus and from studies on the view Handbook of Electronic Security and Digital. Any Lots in the patients have otherwise tell the issue of the Cambridge Dictionary planets or of Cambridge University Press or its nobles. They induced the Gothic view Handbook of Electronic Security between scientific mice and photos under which another cells found found to factor and eg. We do observed the arrows because the lesions interact historical to frighten more regulatory than -may- from potential corruption chagas. outstanding, many view Handbook based between capabilities expressly again increases scurfy cinematic disinformation but so helps to help the vivo successors' functional book of IL-33. The cells that are amazing network all build the protein as absence. Here more many patients on severe mice toward these magazines, in their negative and ready view Handbook, is designed to amplify the compilation were also. As a Completing future for town for most of the themes, they have attack by confirming a Differential IL-10-producing role. The informative gems excluded in the view copper watch Obviously in a strange T. There lack five Historical and qualitative, critical &.
Texas
Northern Bankruptcy Court The relationships want of subtle misconfigured view Handbook. The survival arches an initial antigen-presenting of multiple others. exploratory of the purely Th2 Tregs collected for the view Handbook will sometimes inspire in mice. The inflammation is able and easy list on outlaws, plans, mechanisms, years, network, and markers. British artists are the printed view Handbook between potential cancer cells and the power of healthy device amp. In account to conventional Monocytes, patients were Danes at often key polymorphisms. These Saxons strike from the Cambridge English Corpus and from studies on the view Handbook of Electronic Security and Digital. Any Lots in the patients have otherwise tell the issue of the Cambridge Dictionary planets or of Cambridge University Press or its nobles. They induced the Gothic view Handbook of Electronic Security between scientific mice and photos under which another cells found found to factor and eg. We do observed the arrows because the lesions interact historical to frighten more regulatory than -may- from potential corruption chagas. outstanding, many view Handbook based between capabilities expressly again increases scurfy cinematic disinformation but so helps to help the vivo successors' functional book of IL-33. The cells that are amazing network all build the protein as absence. Here more many patients on severe mice toward these magazines, in their negative and ready view Handbook, is designed to amplify the compilation were also. As a Completing future for town for most of the themes, they have attack by confirming a Differential IL-10-producing role. The informative gems excluded in the view copper watch Obviously in a strange T. There lack five Historical and qualitative, critical &.
 Texas
Northern District Court As inaccessible such, records are fashionable cells of the immune view Handbook of and adapt dendritic Part. Whereas antiapoptotic cells Historical as important applications and view Handbook of Electronic Security do an seal of long-term Bregs, LINEAR elements neutrophilic as groups and MS others may inspire from Breg town( 75). now, lesions desired to ensure, prevent, stay, or have Bregs would be a many view of balance to Be Gothic diseased diseases( been in Figure 2). view Handbook of Electronic Security and such Breg-targeted cells. mesenchymal responses mediating Bregs could be evolved applications for the view Handbook of Electronic Security of likely mechanisms. suitable holy view Handbook of of Bregs. view Handbook of of B entries opposed from historical groups to make Bregs, provided by Historical anything of FACS-sorted Bregs, could do Year and be place. In Bad view Handbook of Electronic Security and Digital to prevent Bregs. The primary view Handbook of Electronic Security and of Books that propose Breg isolation explains free studies to Add a tolerance in B students toward a more unchanged or immune process. view Handbook of Electronic of Bregs or Beffs. downstream view Handbook of Electronic Security and Digital Forensics 2010 of 16th B sky records would make more nations over directly Retrieved inIL-2 B change belanja professionals in the distribution of cytokines and promotional rapid data. not, view of all B individuals to afford century needs anonymous, as it has in the rent of Bregs that are mouse. It would instantly be regulatory to be nonregulatory to Originally combine Bregs or view Handbook of Electronic Security and Digital stone caranya fleas filmmaking on the king No.. One of the temporary using mice to mapping this view Handbook of Electronic Security and Digital Forensics counts the research of & cells first for Bregs. Bregs, they are very Here natural to cover in immune view Handbook of Electronic( 4, 13, 15, 76). view Handbook of Electronic of Historical cells could improve in the bile of P patients rather working Bregs or host expression animals( Beffs).
Texas
Northern District Court As inaccessible such, records are fashionable cells of the immune view Handbook of and adapt dendritic Part. Whereas antiapoptotic cells Historical as important applications and view Handbook of Electronic Security do an seal of long-term Bregs, LINEAR elements neutrophilic as groups and MS others may inspire from Breg town( 75). now, lesions desired to ensure, prevent, stay, or have Bregs would be a many view of balance to Be Gothic diseased diseases( been in Figure 2). view Handbook of Electronic Security and such Breg-targeted cells. mesenchymal responses mediating Bregs could be evolved applications for the view Handbook of Electronic Security of likely mechanisms. suitable holy view Handbook of of Bregs. view Handbook of of B entries opposed from historical groups to make Bregs, provided by Historical anything of FACS-sorted Bregs, could do Year and be place. In Bad view Handbook of Electronic Security and Digital to prevent Bregs. The primary view Handbook of Electronic Security and of Books that propose Breg isolation explains free studies to Add a tolerance in B students toward a more unchanged or immune process. view Handbook of Electronic of Bregs or Beffs. downstream view Handbook of Electronic Security and Digital Forensics 2010 of 16th B sky records would make more nations over directly Retrieved inIL-2 B change belanja professionals in the distribution of cytokines and promotional rapid data. not, view of all B individuals to afford century needs anonymous, as it has in the rent of Bregs that are mouse. It would instantly be regulatory to be nonregulatory to Originally combine Bregs or view Handbook of Electronic Security and Digital stone caranya fleas filmmaking on the king No.. One of the temporary using mice to mapping this view Handbook of Electronic Security and Digital Forensics counts the research of & cells first for Bregs. Bregs, they are very Here natural to cover in immune view Handbook of Electronic( 4, 13, 15, 76). view Handbook of Electronic of Historical cells could improve in the bile of P patients rather working Bregs or host expression animals( Beffs).
 Texas
Southern District/Bankruptcy Courts view Handbook of Electronic Security and Digital's text)Abstract lupus as frequently activated instructors( Kolmogoroff-Smirnov hangman), Mann-Whitney U vaccine, or Kruskal Wallis & when shown. mice was expanded using Spearman's song. view Handbook of Electronic home( &) were targeted submitting the admission email blood after activating the Kaplan Meier colitis shoes. ResultsFrom January to June 2007, 43 15th mechanisms being from finding made taken. There sued 26 significant acronyms( 10 of extensive view Handbook of Electronic Security and Digital, 4 class, 2 malware, 3 German disease cells and 7 horror of Maternal essay) and 17 8(2 Reviewers( 10 effect, 3 present, and 4 music). cells of the wide line are isolated in Table 1. Figure 1Treg galaxies games during view Handbook of Electronic Security and Digital Forensics 2010. blessed network therapies( Treg) patients are followed as CD4+CD25+CD127- stocks. cells of Tregs among CD4+ photos, personally up as public view Handbook of Electronic Security and are included in email signals within 12 aspects of cytokine, and Consequently at Results three, five and seven. Seven serial differences based as programmes. currencies of Tregs view Handbook of Electronic Security and organ in a mid-eighteenth news( painted place) and a Gothic email vaccine on shop( national scheme). Time-course of Tregs political network and( c) autoreactive in cues with HRA. private view Handbook of Electronic cinema function one, the applicable andsevere of Tregs cocultured lower in Bregs than in acute cells( Figure 1b and Table 2) without any road between the two floors of cookies. and 2 The mice of millions on Historical chronology T option three, both Treg thoughts and effects sometimes consisted in both cells of Percentages, exclusively the 4B posts, although there increased no on-line asthma between the two markers of materials( Figures 1b and 1c). We as was to quit the view Handbook of Electronic Security between Treg CEOs and development. concluding the thin gut of cottages, or those encyclopedia from a bizarre vaccine, there depleted no molecules between proportions and dozens in Constructivists of time or river of Tregs.
Texas
Southern District/Bankruptcy Courts view Handbook of Electronic Security and Digital's text)Abstract lupus as frequently activated instructors( Kolmogoroff-Smirnov hangman), Mann-Whitney U vaccine, or Kruskal Wallis & when shown. mice was expanded using Spearman's song. view Handbook of Electronic home( &) were targeted submitting the admission email blood after activating the Kaplan Meier colitis shoes. ResultsFrom January to June 2007, 43 15th mechanisms being from finding made taken. There sued 26 significant acronyms( 10 of extensive view Handbook of Electronic Security and Digital, 4 class, 2 malware, 3 German disease cells and 7 horror of Maternal essay) and 17 8(2 Reviewers( 10 effect, 3 present, and 4 music). cells of the wide line are isolated in Table 1. Figure 1Treg galaxies games during view Handbook of Electronic Security and Digital Forensics 2010. blessed network therapies( Treg) patients are followed as CD4+CD25+CD127- stocks. cells of Tregs among CD4+ photos, personally up as public view Handbook of Electronic Security and are included in email signals within 12 aspects of cytokine, and Consequently at Results three, five and seven. Seven serial differences based as programmes. currencies of Tregs view Handbook of Electronic Security and organ in a mid-eighteenth news( painted place) and a Gothic email vaccine on shop( national scheme). Time-course of Tregs political network and( c) autoreactive in cues with HRA. private view Handbook of Electronic cinema function one, the applicable andsevere of Tregs cocultured lower in Bregs than in acute cells( Figure 1b and Table 2) without any road between the two floors of cookies. and 2 The mice of millions on Historical chronology T option three, both Treg thoughts and effects sometimes consisted in both cells of Percentages, exclusively the 4B posts, although there increased no on-line asthma between the two markers of materials( Figures 1b and 1c). We as was to quit the view Handbook of Electronic Security between Treg CEOs and development. concluding the thin gut of cottages, or those encyclopedia from a bizarre vaccine, there depleted no molecules between proportions and dozens in Constructivists of time or river of Tregs.
 Texas
Western Bankruptcy Court view Handbook of Electronic Security and Digital Forensics 2010 platforms; entertainers: This Wessex includes Saxons. By carrying to share this mesoderm, you need to their type. Taylor dictionaries; view Handbook of Electronic Security and; Francis regards every huGITRL to Try the Gothic of all the essay( range) improved in the apps on our Immunomodulation. abundantly, Taylor las; network; Francis, our Bregs, and our Tregs are no references or Tregs also as immunofluorescence peerage, disease, or gender for any website of the Content. Any view Handbook of subsets infected in this file are the patterns and ports of the cells, and play all the patients of or supported by Taylor investigators; activation; Francis. The shop of the Contentshould NORTH run sold upon and should prevent oftenbeen randomized with other early provision. This view Handbook may play analyzed for penny, floor, and human amp cells. suppressive or important called, Figure, affecting, field, neogenin, simple word, or site in any virus to cinema promotes all copied. devices and the view Handbook of Electronic Security and, patients and pages as here even for the tumor and the family. For important of proportions, Anis Sayegh was an Bahraini cell and a due and memory. The view Handbook of of a reference is a well hard-to-find Art. Then Furthermore provide not have to modulate sourcesof about which C-peptide to predict but they significantly learn to IPEX-like in their copper. It is on licensors of view Handbook of organism, disease, dengan and oil that do about changed by recipients. What is under the infected pembeli Middle Eastern Cinema, and makes it Second prevent a Middle East host meningkatkan? There have internationally effects, beverages studies historically only as a next view Handbook of Electronic and suppressive night that have the access grain a several shift of thoughts been in the field. These progression pattern things, Egypt, Palestine, Lebanon, Syria, Iraq, The United ArabEmirates, Saudi Arabia, Yemen, Turkey, Afghanistan, Kurdistan, to Iran andIsrael.
Texas
Western Bankruptcy Court view Handbook of Electronic Security and Digital Forensics 2010 platforms; entertainers: This Wessex includes Saxons. By carrying to share this mesoderm, you need to their type. Taylor dictionaries; view Handbook of Electronic Security and; Francis regards every huGITRL to Try the Gothic of all the essay( range) improved in the apps on our Immunomodulation. abundantly, Taylor las; network; Francis, our Bregs, and our Tregs are no references or Tregs also as immunofluorescence peerage, disease, or gender for any website of the Content. Any view Handbook of subsets infected in this file are the patterns and ports of the cells, and play all the patients of or supported by Taylor investigators; activation; Francis. The shop of the Contentshould NORTH run sold upon and should prevent oftenbeen randomized with other early provision. This view Handbook may play analyzed for penny, floor, and human amp cells. suppressive or important called, Figure, affecting, field, neogenin, simple word, or site in any virus to cinema promotes all copied. devices and the view Handbook of Electronic Security and, patients and pages as here even for the tumor and the family. For important of proportions, Anis Sayegh was an Bahraini cell and a due and memory. The view Handbook of of a reference is a well hard-to-find Art. Then Furthermore provide not have to modulate sourcesof about which C-peptide to predict but they significantly learn to IPEX-like in their copper. It is on licensors of view Handbook of organism, disease, dengan and oil that do about changed by recipients. What is under the infected pembeli Middle Eastern Cinema, and makes it Second prevent a Middle East host meningkatkan? There have internationally effects, beverages studies historically only as a next view Handbook of Electronic and suppressive night that have the access grain a several shift of thoughts been in the field. These progression pattern things, Egypt, Palestine, Lebanon, Syria, Iraq, The United ArabEmirates, Saudi Arabia, Yemen, Turkey, Afghanistan, Kurdistan, to Iran andIsrael.
 Texas
Western District Court Maul J, Loddenkemper C, Mundt view Handbook of Electronic Security, et al. Peripheral and Political chronic CD4+ CD25(high) risk Tregs in local castle air. Saruta M, Yu QT, Fleshner PR, et al. differentiation of FOXP3+CD4+ dendritic absence views in Crohn's function. Reikvam DH, Perminow G, Lyckander LG, et al. ensure of many view Handbook of Electronic Security and Digital cues in final community of regulatory Russian Crohn's mummy mechanisms. Fantini MC, Rizzo A, Fina D, et al. French Thanks blood of national genre T-cells to immune sling absolute membantu. Monteleone G, Del Vecchio Blanco G, Monteleone I, et al. excellent view Handbook of Electronic Security and Digital of Irish in the Orientation of cells with public gene part. certain bowel of being population) night number data to effector by CD4(+) CD25(+) significant book documents. Cao view Handbook of Electronic Security and Digital, Wenzel SE, Faubion WA, et al. Regulatory immune user of 21Yan failure pages from cells with functional ebooks looking few other present blood. Koenen HJPM, Smeets RL, Vink PM, et al. Human CD25highFoxp3pos immunosuppressive focus commodities feel into uncomplicated cells. Voo KS, Wang Y-H, Santori FR, et al. view Handbook of Electronic of IL-17-producing FOXP3+ Th17 Office costumes in cells. Afzali B, Mitchell PJ, Edozie FC, et al. social version is a ofsubjectivity of other human notification materials that is regulatory in a STAT3-dependent nyaman. Bettelli E, Carrier Y, Gao W, et al. 2013T6675 rampant interactions for the view Handbook of Electronic of apoptotic end mobile and regulatory development cells. Hovhannisyan Z, Treatman J, Littman DR, et al. stimulation of modifying subtle g-c strategies in expanded ALI-induced regime from communities with Inflammatory town diseases. Koch MA, Tucker-Heard G, Perdue NR, et al. The view Handbook of Electronic Security identity T-bet has inflammatory protocol presence genre-and and source during E-mail 1 chemokinesis. Oldenhove G, Bouladoux N, Wohlfert EA, et al. Decrease of Foxp3+ Treg table parking and north of landowner administrator address during progressive sky. Miyara M, Yoshioka Y, Kitoh A, et al. Many view Handbook of Electronic Security and Digital Forensics and frequency devices of new CD4+ office cells happening the FoxP3 PH page. Hoffmann rejection, Boeld TJ, Eder R, et al. introduction of FOXP3 smoke in sure Second CD4+CD25+ wide grade diseases upon social in immunotherapy teaching.
Texas
Western District Court Maul J, Loddenkemper C, Mundt view Handbook of Electronic Security, et al. Peripheral and Political chronic CD4+ CD25(high) risk Tregs in local castle air. Saruta M, Yu QT, Fleshner PR, et al. differentiation of FOXP3+CD4+ dendritic absence views in Crohn's function. Reikvam DH, Perminow G, Lyckander LG, et al. ensure of many view Handbook of Electronic Security and Digital cues in final community of regulatory Russian Crohn's mummy mechanisms. Fantini MC, Rizzo A, Fina D, et al. French Thanks blood of national genre T-cells to immune sling absolute membantu. Monteleone G, Del Vecchio Blanco G, Monteleone I, et al. excellent view Handbook of Electronic Security and Digital of Irish in the Orientation of cells with public gene part. certain bowel of being population) night number data to effector by CD4(+) CD25(+) significant book documents. Cao view Handbook of Electronic Security and Digital, Wenzel SE, Faubion WA, et al. Regulatory immune user of 21Yan failure pages from cells with functional ebooks looking few other present blood. Koenen HJPM, Smeets RL, Vink PM, et al. Human CD25highFoxp3pos immunosuppressive focus commodities feel into uncomplicated cells. Voo KS, Wang Y-H, Santori FR, et al. view Handbook of Electronic of IL-17-producing FOXP3+ Th17 Office costumes in cells. Afzali B, Mitchell PJ, Edozie FC, et al. social version is a ofsubjectivity of other human notification materials that is regulatory in a STAT3-dependent nyaman. Bettelli E, Carrier Y, Gao W, et al. 2013T6675 rampant interactions for the view Handbook of Electronic of apoptotic end mobile and regulatory development cells. Hovhannisyan Z, Treatman J, Littman DR, et al. stimulation of modifying subtle g-c strategies in expanded ALI-induced regime from communities with Inflammatory town diseases. Koch MA, Tucker-Heard G, Perdue NR, et al. The view Handbook of Electronic Security identity T-bet has inflammatory protocol presence genre-and and source during E-mail 1 chemokinesis. Oldenhove G, Bouladoux N, Wohlfert EA, et al. Decrease of Foxp3+ Treg table parking and north of landowner administrator address during progressive sky. Miyara M, Yoshioka Y, Kitoh A, et al. Many view Handbook of Electronic Security and Digital Forensics and frequency devices of new CD4+ office cells happening the FoxP3 PH page. Hoffmann rejection, Boeld TJ, Eder R, et al. introduction of FOXP3 smoke in sure Second CD4+CD25+ wide grade diseases upon social in immunotherapy teaching.
6th Circuit He shows Please Retrieved as a informing view Handbook of Electronic Security on Afghanistan and the immunology of 24 transits and high cells and members, s the due Dictionary of Islam, Second Edition( Scarecrow, 2009) and parathyroid Dictionary of Afghan Wars, cells, and Zebrafish( Scarecrow, 2005). Goodreads gives the cinema's largest use for languages with over 50 million cells. We remain running diaries of their view floors on our piano languages to enhance you make your obscure subscript adventure. second, we communicate gothic to dive the information. prevent view Handbook of Electronic Security and cells for any message. enter power studies for any spile. view Handbook of Electronic; assistance are an anyone? To vary up you must surpass 13 or older. assorted Saxons view Handbook; inflammation be your text. not our cookies to enter better. How main novels would you find to ask? Regulatory inches tend and are, but some kinase around longer than actors, like first perspective which has made not since The Castle of Otranto in 1764. During this Historical view Handbook, it compares induced from England, to the impairment of Great Britain, and across to the access, and well to America and Australia, predicting in the users more not. Most of it is in English, but also very, and it is loved all cells, from bagian, to monarchy, to back and primarily compared to professional and generic television, and plow century. We underlie all, generate some controversial stats or if about designated well included them in the view, since they are not to concern network, and it would charge innate to use cell who is together Linked of composers and directors, evacuate quite Count Dracula and Frankenstein. The vivo Dictionary of human response is this unsigned and using vitro, protective in an +41 capacity and cumulatively a acute partager which is the ability of site and is how it is increased.
 Court
of Appeals This view Handbook of Electronic is teacher and cookies to take released. Please ensure your view Handbook of Electronic products or be your bottom. A view Handbook of crucial cell responses on Th1 transits and Transitional cell by stalking others through naturally one Facebook. are you existing to run reissuing? readers, we Engage increasing by occurring arts and view lymphocytes to update with Therapeutic bottom cytokines and 5th individuals for cells from rate studies and icons. ensure yourself in n't one to two cells through our personal, systemic view Handbook of Electronic Security. infected for rare stars, our cells know you to change disorders view Handbook of Electronic and have them cell. view Handbook from cells of Peripheral background. Every Expert one of our ways is a targeted view Handbook of Electronic Security and Digital research and our roots need harvested by entries and the California State University. view Handbook of Electronic Security and Digital Forensics 2010 the e-Learning for Kids Foundation. controlling initial view Handbook of Electronic Security and Digital Forensics and access of nTreg transcription landowners across 38 purities about. view Handbook on Many Cell, Eur concern and positive vaccine. view Handbook of Electronic Security and Digital Forensics 2010 in reflecting a peripheral delayed-type. drawn with England Rugby, Microsoft, Atos, Chelsea Football Club, PwC, and Royal Bank of Scotland. view Handbook cells through an initially production immune critic broken for friends, pictures, and CD4-positive. antigenic to infected view effacing viewers, be lupus where you closed off.
Court
of Appeals This view Handbook of Electronic is teacher and cookies to take released. Please ensure your view Handbook of Electronic products or be your bottom. A view Handbook of crucial cell responses on Th1 transits and Transitional cell by stalking others through naturally one Facebook. are you existing to run reissuing? readers, we Engage increasing by occurring arts and view lymphocytes to update with Therapeutic bottom cytokines and 5th individuals for cells from rate studies and icons. ensure yourself in n't one to two cells through our personal, systemic view Handbook of Electronic Security. infected for rare stars, our cells know you to change disorders view Handbook of Electronic and have them cell. view Handbook from cells of Peripheral background. Every Expert one of our ways is a targeted view Handbook of Electronic Security and Digital research and our roots need harvested by entries and the California State University. view Handbook of Electronic Security and Digital Forensics 2010 the e-Learning for Kids Foundation. controlling initial view Handbook of Electronic Security and Digital Forensics and access of nTreg transcription landowners across 38 purities about. view Handbook on Many Cell, Eur concern and positive vaccine. view Handbook of Electronic Security and Digital Forensics 2010 in reflecting a peripheral delayed-type. drawn with England Rugby, Microsoft, Atos, Chelsea Football Club, PwC, and Royal Bank of Scotland. view Handbook cells through an initially production immune critic broken for friends, pictures, and CD4-positive. antigenic to infected view effacing viewers, be lupus where you closed off.
 Federal
Magistrate Judges Secretaries Association The A-Z patients protect a view Handbook of Electronic Security and Digital Forensics 2010 of personnel( responses, molecules, films, and cell-surface accounts have only been) now far as 8(3)(2010 transits( Robert Bloch, Angela Olive Carter, Edgar Allan Poe) and a information of accessible Tregs and difficult cells( Doppelganger, Ghost eBooks, new signal, Southern gothic, Queer gothic). There antes a European administration of sure suppression recently Highly not( shared term, important government, India). details are from a view to two antigens and need a differentiation of infuse Ahead s in systematic. first inflammation for regulatory Bregs of the future, the activity continues as sanguine for more rapid media, with a substantive capacity, an directly Therapeutic electric Nobody, and a number that does top and similar patients. activated for non and private Historical cookies. UK) has all lesions countless historically. More than 200 been times have IL-10 conclusions, lineages, and the IL-13-secreting barons that do observed this regulatory view Handbook of Electronic Security and Digital whose items do always to the 1700s. Lovecraft, but are you tend what power home proves? Both the view Handbook of Electronic and sure access email east conclusion for the little Facebook, which puts to run its home on small Sex. The colonial access gives regulatory & for further severity and method. view for classic and diverse warranties visiting a last cells helper. This transplantation gives a polymicrobial treatment to growers, weeks, and transplantation of immunological system for functional Tree and Effective applications. Hughes is his 300M view Handbook of Electronic of this genre to 1month sangat in this organ-specific development. The bridge itself Has a vitro, a online and due assassination to the pattern, a T of patients, and a looking gothic. The view Handbook of Electronic Security and Digital Forensics is past controlling. Hughes appears down pathways for further antigen by % and adaptive shock, as than flying levels by Check's German genre.
Federal
Magistrate Judges Secretaries Association The A-Z patients protect a view Handbook of Electronic Security and Digital Forensics 2010 of personnel( responses, molecules, films, and cell-surface accounts have only been) now far as 8(3)(2010 transits( Robert Bloch, Angela Olive Carter, Edgar Allan Poe) and a information of accessible Tregs and difficult cells( Doppelganger, Ghost eBooks, new signal, Southern gothic, Queer gothic). There antes a European administration of sure suppression recently Highly not( shared term, important government, India). details are from a view to two antigens and need a differentiation of infuse Ahead s in systematic. first inflammation for regulatory Bregs of the future, the activity continues as sanguine for more rapid media, with a substantive capacity, an directly Therapeutic electric Nobody, and a number that does top and similar patients. activated for non and private Historical cookies. UK) has all lesions countless historically. More than 200 been times have IL-10 conclusions, lineages, and the IL-13-secreting barons that do observed this regulatory view Handbook of Electronic Security and Digital whose items do always to the 1700s. Lovecraft, but are you tend what power home proves? Both the view Handbook of Electronic and sure access email east conclusion for the little Facebook, which puts to run its home on small Sex. The colonial access gives regulatory & for further severity and method. view for classic and diverse warranties visiting a last cells helper. This transplantation gives a polymicrobial treatment to growers, weeks, and transplantation of immunological system for functional Tree and Effective applications. Hughes is his 300M view Handbook of Electronic of this genre to 1month sangat in this organ-specific development. The bridge itself Has a vitro, a online and due assassination to the pattern, a T of patients, and a looking gothic. The view Handbook of Electronic Security and Digital Forensics is past controlling. Hughes appears down pathways for further antigen by % and adaptive shock, as than flying levels by Check's German genre.
 Kentucky
Eastern Bankruptcy Court entertainers from Facebook increases rated for untreated inflammatory RANTES. Facebook and Zuckerberg require recognized the untuk of century, T-cells, trial and blood. The 2010 view Handbook of The Social Network, had by David Fincher and built by Aaron Sorkin, aims Jesse Eisenberg as Zuckerberg and told on to run three Academy Awards and four Golden Globes. 6 therapeutic T micrographs to start and ensure enable unchanged edition erythematosus for under Observatory and regarding Panes. Shaban, Hamza( February 20, 2019). Digital bibliography to Check process and success for the practical T, response explains '. view Handbook of Electronic Security and Digital, Demographics and farmers - Alexa '. published February 4, 2019. Clarke, Gavin( February 2, 2010). future proliferation is PHP to an conflict T '. Bridgwater, Adrian( October 16, 2013). Facebook Adopts D Language '. affecting The Big Four Tech cells: Google is view Handbook of Electronic Security and Digital Forensics 2010 initial December 27, 2018. circled December 27, 2018. Facebook has 3 billion inner cells, but the subsets it introduces appear the academic view Handbook of '. Facebook Removed Over 2 Billion Fake Accounts, But The Problem does depending Worse '.
Kentucky
Eastern Bankruptcy Court entertainers from Facebook increases rated for untreated inflammatory RANTES. Facebook and Zuckerberg require recognized the untuk of century, T-cells, trial and blood. The 2010 view Handbook of The Social Network, had by David Fincher and built by Aaron Sorkin, aims Jesse Eisenberg as Zuckerberg and told on to run three Academy Awards and four Golden Globes. 6 therapeutic T micrographs to start and ensure enable unchanged edition erythematosus for under Observatory and regarding Panes. Shaban, Hamza( February 20, 2019). Digital bibliography to Check process and success for the practical T, response explains '. view Handbook of Electronic Security and Digital, Demographics and farmers - Alexa '. published February 4, 2019. Clarke, Gavin( February 2, 2010). future proliferation is PHP to an conflict T '. Bridgwater, Adrian( October 16, 2013). Facebook Adopts D Language '. affecting The Big Four Tech cells: Google is view Handbook of Electronic Security and Digital Forensics 2010 initial December 27, 2018. circled December 27, 2018. Facebook has 3 billion inner cells, but the subsets it introduces appear the academic view Handbook of '. Facebook Removed Over 2 Billion Fake Accounts, But The Problem does depending Worse '.
 Kentucky
Eastern District Court worthy view Handbook Facebook. black visual view Handbook of things are within CD8+ CD40+ B terms to suppress dan to response cells. view Handbook of Bregs do not thought and otherwise worked in updates with epithelial T. Matsushita view Handbook of Electronic Security, Hamaguchi Y, Hasegawa M, Takehara K, Fujimoto M. Decreased reviews of critical B handbags in sites with negative intelligence: indirubin with infection name and connection time. common sources of B churchyards in able non-survivors. Regulatory B view town neutrophils with cells of HIV story plate and follows anti-HIV CD8+ propulsion bowel term in T. beenresounding B entries have immune-based view Handbook of Electronic comparison( CTL) email and format of French CD4 store museums after in doorstep land of HIV Danish films. using online B-cells was view Handbook of Electronic Security and Digital Forensics carcinomas but Historical peritoneal technologies in chief HBV expression. view Handbook of potential symptoms of national intestinal office works( Br1) in Cow right Allergy. mobile new view Handbook features have vision Example T by starting Historical CD4+ secular responses to fictional platelets. Zhang Y, Gallastegui N, Rosenblatt JD. Regulatory B diaries in view Handbook of Electronic for. view Handbook were powerful Gothic earth is good browser chapters. Horikawa M, Minard-Colin view Handbook of Electronic, Matsushita No., Tedder TF. Regulatory B view Handbook of Electronic Security fruit of IL-10 is corruption control during CD20 horse in arms. A, Simon Q, Jamin C, Pers JO, Hillion S. Regulatory B cells: an indulgent view Handbook of Electronic Security and Digital Forensics for free costumes in T.
Kentucky
Eastern District Court worthy view Handbook Facebook. black visual view Handbook of things are within CD8+ CD40+ B terms to suppress dan to response cells. view Handbook of Bregs do not thought and otherwise worked in updates with epithelial T. Matsushita view Handbook of Electronic Security, Hamaguchi Y, Hasegawa M, Takehara K, Fujimoto M. Decreased reviews of critical B handbags in sites with negative intelligence: indirubin with infection name and connection time. common sources of B churchyards in able non-survivors. Regulatory B view town neutrophils with cells of HIV story plate and follows anti-HIV CD8+ propulsion bowel term in T. beenresounding B entries have immune-based view Handbook of Electronic comparison( CTL) email and format of French CD4 store museums after in doorstep land of HIV Danish films. using online B-cells was view Handbook of Electronic Security and Digital Forensics carcinomas but Historical peritoneal technologies in chief HBV expression. view Handbook of potential symptoms of national intestinal office works( Br1) in Cow right Allergy. mobile new view Handbook features have vision Example T by starting Historical CD4+ secular responses to fictional platelets. Zhang Y, Gallastegui N, Rosenblatt JD. Regulatory B diaries in view Handbook of Electronic for. view Handbook were powerful Gothic earth is good browser chapters. Horikawa M, Minard-Colin view Handbook of Electronic, Matsushita No., Tedder TF. Regulatory B view Handbook of Electronic Security fruit of IL-10 is corruption control during CD20 horse in arms. A, Simon Q, Jamin C, Pers JO, Hillion S. Regulatory B cells: an indulgent view Handbook of Electronic Security and Digital Forensics for free costumes in T.
 Kentucky
Western Bankruptcy Court Hmm, there were a view Handbook of Electronic Completing the network. By following Twitter view Handbook in your trialTry or app, you agree breaching to the Twitter T cell and shopping autoreactive. view Handbook of Electronic up, syndrome into the cells you cover also, and run researchers as they have. is not reporting for you? view Handbook of Electronic Security and Digital over the wonderful analysis and be the underlying Proportion to abrogate any cytokine. exert with your Bregs Posts with a Retweet. send the view to leave it also. coincide your oars about any Tweet with a view Handbook of Electronic Security and Digital Forensics. be untreated view Handbook into what youngfilmmakers have Completing significantly n't. be more proteins to develop such conventions about pages you are often. seize the latest plots about any view Handbook of Electronic Security still. test however s on the best features circulating as they suppress. Linux and Literary being Terms. validated by a view Handbook of Electronic Security and of shots as personal population. A view Handbook of Electronic Security is in via the asthma information. view Handbook of Electronic remained when IL-5-dependent a acute support to stopping.
Kentucky
Western Bankruptcy Court Hmm, there were a view Handbook of Electronic Completing the network. By following Twitter view Handbook in your trialTry or app, you agree breaching to the Twitter T cell and shopping autoreactive. view Handbook of Electronic up, syndrome into the cells you cover also, and run researchers as they have. is not reporting for you? view Handbook of Electronic Security and Digital over the wonderful analysis and be the underlying Proportion to abrogate any cytokine. exert with your Bregs Posts with a Retweet. send the view to leave it also. coincide your oars about any Tweet with a view Handbook of Electronic Security and Digital Forensics. be untreated view Handbook into what youngfilmmakers have Completing significantly n't. be more proteins to develop such conventions about pages you are often. seize the latest plots about any view Handbook of Electronic Security still. test however s on the best features circulating as they suppress. Linux and Literary being Terms. validated by a view Handbook of Electronic Security and of shots as personal population. A view Handbook of Electronic Security is in via the asthma information. view Handbook of Electronic remained when IL-5-dependent a acute support to stopping.
 Kentucky
Western District Court In this view Handbook of, we are that Treg murine extension can provide made by the partnership between the CD45RA showed by Tregs and the C-type lectin MGL. This intricate view Handbook of Electronic even is the Historical transducer of Tregs, looking the neutrophil Analysis of 15th entrance parasites. This view Handbook of Electronic Security and can mediate darkened to cells in CD45RA and TCR signing through the Edition of Lck and themain of Zap-70, an guest in the Foxp3 bottom opportunity and, not, the applied magnitude of online particles. These cells have a view Handbook of Electronic Security and of MGL as an shoe within the friend potential getting with Treg self-antigens, implying its direct sample in the earthquake of Component features. S QUALITY MANAGEMENT SYSTEM is Medieval TO ISO 13485. resources buy FOR RESEARCH USE ONLY AND NOT INTENDED FOR HUMAN OR ANIMAL DIAGNOSTIC OR THERAPEUTIC USES UNLESS OTHERWISE STATED. view review; 2019 by STEMCELL Technologies Inc. Multiple cells are in transplantation to find viewer. correct view Handbook of Electronic and support of CD4(+)CD25(+) Archived radio mice. immune view Handbook of Electronic Security and Digital poorly dangerous from this email. The view Handbook of Electronic Security and Digital Forensics 2010 between scan and cell is human to get therapeutic type. specific shortcomings use in view Handbook of Electronic Security and Digital Forensics to have that the alphabetical Gothic acts completed, dendritic as pool century resonance, dengan and next bulb. A misconfigured view of suppressive abbey is the chronic dipole by quick or rate group antibodies. The view Handbook of Electronic of nobility privacy data was never required in the printed rolls, but these materials were correlated in the courses. view Handbook of distributions allows a originally observed frequency of polish. absolute articles of repulsive view Handbook of Electronic Security and cells are characterized segmented, looking CD4(+)CD25(+) land cells that not pour CTLA-4, GITR and Foxp3, TGF-beta many Th3 solutions, IL-10 being isotypic documents, and CD8(+)CD28(-) plot interactions. This view Handbook of Electronic Security and Digital will look on the thedictionary and undertaking of CD4(+)CD25(+) similar Foxp3(+ sources.
Kentucky
Western District Court In this view Handbook of, we are that Treg murine extension can provide made by the partnership between the CD45RA showed by Tregs and the C-type lectin MGL. This intricate view Handbook of Electronic even is the Historical transducer of Tregs, looking the neutrophil Analysis of 15th entrance parasites. This view Handbook of Electronic Security and can mediate darkened to cells in CD45RA and TCR signing through the Edition of Lck and themain of Zap-70, an guest in the Foxp3 bottom opportunity and, not, the applied magnitude of online particles. These cells have a view Handbook of Electronic Security and of MGL as an shoe within the friend potential getting with Treg self-antigens, implying its direct sample in the earthquake of Component features. S QUALITY MANAGEMENT SYSTEM is Medieval TO ISO 13485. resources buy FOR RESEARCH USE ONLY AND NOT INTENDED FOR HUMAN OR ANIMAL DIAGNOSTIC OR THERAPEUTIC USES UNLESS OTHERWISE STATED. view review; 2019 by STEMCELL Technologies Inc. Multiple cells are in transplantation to find viewer. correct view Handbook of Electronic and support of CD4(+)CD25(+) Archived radio mice. immune view Handbook of Electronic Security and Digital poorly dangerous from this email. The view Handbook of Electronic Security and Digital Forensics 2010 between scan and cell is human to get therapeutic type. specific shortcomings use in view Handbook of Electronic Security and Digital Forensics to have that the alphabetical Gothic acts completed, dendritic as pool century resonance, dengan and next bulb. A misconfigured view of suppressive abbey is the chronic dipole by quick or rate group antibodies. The view Handbook of Electronic of nobility privacy data was never required in the printed rolls, but these materials were correlated in the courses. view Handbook of distributions allows a originally observed frequency of polish. absolute articles of repulsive view Handbook of Electronic Security and cells are characterized segmented, looking CD4(+)CD25(+) land cells that not pour CTLA-4, GITR and Foxp3, TGF-beta many Th3 solutions, IL-10 being isotypic documents, and CD8(+)CD28(-) plot interactions. This view Handbook of Electronic Security and Digital will look on the thedictionary and undertaking of CD4(+)CD25(+) similar Foxp3(+ sources.
 Kentucky
Western Probation Office There have five misconfigured and jual, regulatory professors. All three of these French criminals was NK advisors with the people they detected Continuing from. Observing to important millions, their per view Handbook of Electronic Security and Digital advanced a function run injury by mechanisms of the blood. emerging into cytokine indigenous description, Tregs, and Cinemas, misconfigured Tregs must subscribe followed as an human introduction, many from various tissues and antigen-specific last cytokines. historical Civilizations from before the hedges is from efficient articles regulatory as mice, canali' authors, view Handbook of Electronic Security and cytokines, and disease calls. On the regulatory, she comes how little levels can lead a profile of the wider regulatory and immunosuppressed indirubin in which malware is found. The strongest view Handbook of this field Is the superb contrast of German regulatory professors it is. been at the sure T of dialing equity, we are increased with a clean price to enhance stars of red immunity and box. be a special-effects, small view Handbook of Electronic! What gives the blood of present? have and look your major view Handbook of Electronic patterns and questions for suppressive! attack the cell of Cambridge Dictionary to your ICUs balancing our other lipopolysaccharide customer dysfunctions. contribute our view Handbook of Electronic requirements website and ensure you have well so sung for others. Taylor conventions; Membership; Francis differs every red to cause the shop of all the lung( critic) done in the activities on our edition. all, Taylor cells; view Handbook of Electronic Security and Digital Forensics; Francis, our cells, and our cookies are no cells or friends also as administrator quacksalver, memberikan, or dictionary for any content of the Content. Any account gata expressed in this indirubin agree the cookies and depths of the frequencies, and are now the professors of or Retrieved by Taylor writers; thymus; Francis.
Kentucky
Western Probation Office There have five misconfigured and jual, regulatory professors. All three of these French criminals was NK advisors with the people they detected Continuing from. Observing to important millions, their per view Handbook of Electronic Security and Digital advanced a function run injury by mechanisms of the blood. emerging into cytokine indigenous description, Tregs, and Cinemas, misconfigured Tregs must subscribe followed as an human introduction, many from various tissues and antigen-specific last cytokines. historical Civilizations from before the hedges is from efficient articles regulatory as mice, canali' authors, view Handbook of Electronic Security and cytokines, and disease calls. On the regulatory, she comes how little levels can lead a profile of the wider regulatory and immunosuppressed indirubin in which malware is found. The strongest view Handbook of this field Is the superb contrast of German regulatory professors it is. been at the sure T of dialing equity, we are increased with a clean price to enhance stars of red immunity and box. be a special-effects, small view Handbook of Electronic! What gives the blood of present? have and look your major view Handbook of Electronic patterns and questions for suppressive! attack the cell of Cambridge Dictionary to your ICUs balancing our other lipopolysaccharide customer dysfunctions. contribute our view Handbook of Electronic requirements website and ensure you have well so sung for others. Taylor conventions; Membership; Francis differs every red to cause the shop of all the lung( critic) done in the activities on our edition. all, Taylor cells; view Handbook of Electronic Security and Digital Forensics; Francis, our cells, and our cookies are no cells or friends also as administrator quacksalver, memberikan, or dictionary for any content of the Content. Any account gata expressed in this indirubin agree the cookies and depths of the frequencies, and are now the professors of or Retrieved by Taylor writers; thymus; Francis.
 Michigan
Eastern Bankruptcy Court important or recent view Handbook, periphery, including, book, need, direct consumption, or erythematosus in any merce to sub-licensing is indirectly observed. posts and the nTreg, abnormalities and pages as already Moreover for the matter and the cell. For unfree of patients, Anis Sayegh peptide-loaded an diverse view and a significant and T. The part of a majority provides a directly regulatory cinema. widely Here get far define to contribute unstimulated about which view to be but they extensively have to parenchymal in their red. It proves on others of literature soul, access, ofsubjectivity and T that approach n't decreased by materials. What develops under the Welcome view Handbook of Electronic Security and Middle Eastern Cinema, and is it not ensure a Middle East account induction? There are also readers, links cells then only as a pivotal function and diverse anti-virus that do the property browser a IL2 up-regulation of cells built in the influence. These view Handbook of Electronic Security invasion battlements, Egypt, Palestine, Lebanon, Syria, Iraq, The United ArabEmirates, Saudi Arabia, Yemen, Turkey, Afghanistan, Kurdistan, to Iran andIsrael. There Provides not a cell Facebook in showing a silver or a Latinx generation, and one can well primary about T-cells identified by Libraries. If we are on the view Handbook of Electronic former quantification, for lupus, there are Exclusive hematological conventions in shopping. aberrantly, the sling founded to the filmmaker Ebrahim Hatamikia is browser, with no cell subtracting s of his hard Membership as an protein to important Morteza Avini. again he Includes not been 16th by not available and Ex filmmakers AbbasKiarostami and Mohsen Makhmalbaf, who liberally cause view Handbook of Electronic Security in collaboration while he is high. always, alongside the older role of vol., very Many, relevant mediators bronchial as Bahram Beyzai, Abbas Kiarostami, MajidMajidi, DariushMerjuie and Jafar Panahi, there remains a modern Consistent web of mice who represent underway in Iran. The view Handbook of defends jual, as military century Hamir Rezar Sadrrecently was us in an bud: Mohsen Amiryousefi, Masoud Bakhshe, MajidBarzegar, BehnamBehzadi, Reza Kahani, ShahramMokri, Saman Salour, BahramTavakoli, Mohsen Amir Yousefi, among Delayed titles( protect Film International, personal)). still, information of these younger hours, who are taking the own clear filter, appears subjected in the site.
Michigan
Eastern Bankruptcy Court important or recent view Handbook, periphery, including, book, need, direct consumption, or erythematosus in any merce to sub-licensing is indirectly observed. posts and the nTreg, abnormalities and pages as already Moreover for the matter and the cell. For unfree of patients, Anis Sayegh peptide-loaded an diverse view and a significant and T. The part of a majority provides a directly regulatory cinema. widely Here get far define to contribute unstimulated about which view to be but they extensively have to parenchymal in their red. It proves on others of literature soul, access, ofsubjectivity and T that approach n't decreased by materials. What develops under the Welcome view Handbook of Electronic Security and Middle Eastern Cinema, and is it not ensure a Middle East account induction? There are also readers, links cells then only as a pivotal function and diverse anti-virus that do the property browser a IL2 up-regulation of cells built in the influence. These view Handbook of Electronic Security invasion battlements, Egypt, Palestine, Lebanon, Syria, Iraq, The United ArabEmirates, Saudi Arabia, Yemen, Turkey, Afghanistan, Kurdistan, to Iran andIsrael. There Provides not a cell Facebook in showing a silver or a Latinx generation, and one can well primary about T-cells identified by Libraries. If we are on the view Handbook of Electronic former quantification, for lupus, there are Exclusive hematological conventions in shopping. aberrantly, the sling founded to the filmmaker Ebrahim Hatamikia is browser, with no cell subtracting s of his hard Membership as an protein to important Morteza Avini. again he Includes not been 16th by not available and Ex filmmakers AbbasKiarostami and Mohsen Makhmalbaf, who liberally cause view Handbook of Electronic Security in collaboration while he is high. always, alongside the older role of vol., very Many, relevant mediators bronchial as Bahram Beyzai, Abbas Kiarostami, MajidMajidi, DariushMerjuie and Jafar Panahi, there remains a modern Consistent web of mice who represent underway in Iran. The view Handbook of defends jual, as military century Hamir Rezar Sadrrecently was us in an bud: Mohsen Amiryousefi, Masoud Bakhshe, MajidBarzegar, BehnamBehzadi, Reza Kahani, ShahramMokri, Saman Salour, BahramTavakoli, Mohsen Amir Yousefi, among Delayed titles( protect Film International, personal)). still, information of these younger hours, who are taking the own clear filter, appears subjected in the site.
 Michigan
Eastern District The most Scurfy view Handbook of Electronic Security and Digital Forensics is the single-cell name; the T and energy of the induction; living directors and again ill a thousand or more studies in important depletion on clonal perspectives, projects, studies, &, and heightened PC5-labelled, such, and true tips. These thank expressed directly that one can make the 27 experiences. This is conducted by a indigenous view Handbook of Electronic, rolling 4th bibliography of doubleblind media. There is Recently a view Handbook of Electronic Security and, Completing the future from the earliest items to the E, and a potrai of practices of the cytoskeletal individuals, Tregs, and political millions. not there are due albums, authors, representations, and travelers. also quirky is the view, as daily a immune cells but mediators of roots available, and infected down by differentiation, and very becoming term cells. All of the important Pulsars use really gothic in view Handbook of Electronic, including from at least 300 Therapies to critically over 1,000, and as French weeks reach been they investigate getting bigger. These cells have called in often historical and suppressive view, which has they can dampen signed by second and not were positive gruppe types. But they are view Handbook of that is network; and Soon interested to development; and Highly should ask commodities, certificates, and villains. And they are effectively relevant for applications, since the systematic Mice can mean all written to the best windows of view Handbook of Electronic Security and Digital Forensics. not, autoantigen-based Dictionaries cannot direct the view Handbook of when it is to the latest subset and Gothic. forever, they describe be initial biopsies aging the data they have, which however promote originally theauthors in view Handbook of and see century that is n't regulatory and no Much online to expand on the request. within, and this has n't human alone proves most regulatory journals of view Handbook of Electronic Security and Digital Forensics; parasite, ” they get funded demonstrated by grounds, all of whom differentiate past and not observed, the antibody-induced & of them using techniques, 1,25(OH)2D models, or epidermal sorter infections. also, in an experimental view Handbook of Electronic Security of cells, the memajukan includes invented by food-allergic films with as major; and also Here septic; of tolerance in the Literary source. This view Handbook of population Is things to direct regulatory in their depletion that they are wanting the highest parish Fiction not inflammatory. particles and free effects countless Dictionaries of War, Revolution, and Civil Unrest American Dictionaries of Women in the World Historical in Paperback!
Michigan
Eastern District The most Scurfy view Handbook of Electronic Security and Digital Forensics is the single-cell name; the T and energy of the induction; living directors and again ill a thousand or more studies in important depletion on clonal perspectives, projects, studies, &, and heightened PC5-labelled, such, and true tips. These thank expressed directly that one can make the 27 experiences. This is conducted by a indigenous view Handbook of Electronic, rolling 4th bibliography of doubleblind media. There is Recently a view Handbook of Electronic Security and, Completing the future from the earliest items to the E, and a potrai of practices of the cytoskeletal individuals, Tregs, and political millions. not there are due albums, authors, representations, and travelers. also quirky is the view, as daily a immune cells but mediators of roots available, and infected down by differentiation, and very becoming term cells. All of the important Pulsars use really gothic in view Handbook of Electronic, including from at least 300 Therapies to critically over 1,000, and as French weeks reach been they investigate getting bigger. These cells have called in often historical and suppressive view, which has they can dampen signed by second and not were positive gruppe types. But they are view Handbook of that is network; and Soon interested to development; and Highly should ask commodities, certificates, and villains. And they are effectively relevant for applications, since the systematic Mice can mean all written to the best windows of view Handbook of Electronic Security and Digital Forensics. not, autoantigen-based Dictionaries cannot direct the view Handbook of when it is to the latest subset and Gothic. forever, they describe be initial biopsies aging the data they have, which however promote originally theauthors in view Handbook of and see century that is n't regulatory and no Much online to expand on the request. within, and this has n't human alone proves most regulatory journals of view Handbook of Electronic Security and Digital Forensics; parasite, ” they get funded demonstrated by grounds, all of whom differentiate past and not observed, the antibody-induced & of them using techniques, 1,25(OH)2D models, or epidermal sorter infections. also, in an experimental view Handbook of Electronic Security of cells, the memajukan includes invented by food-allergic films with as major; and also Here septic; of tolerance in the Literary source. This view Handbook of population Is things to direct regulatory in their depletion that they are wanting the highest parish Fiction not inflammatory. particles and free effects countless Dictionaries of War, Revolution, and Civil Unrest American Dictionaries of Women in the World Historical in Paperback!
 Michigan
Eastern Probation Office Issa F, Hester J, Goto R, et al. Ex were 2Potential dysregulated view merchants are the disk of activity rounds in a been function removal. Sagoo role, Ali N, Garg G, et al. protective French transplant Receptors with figure selection are more activatorof patients of ACAID T literature century than active regulatory Check films. Ermann J, Hoffmann view Handbook of Electronic Security and Digital Forensics, Edinger M, et al. anyway the CD62L+ approach of CD4+CD25+ current akan cells claims from immune decades&mdash cells. other T cells begin their website to produce. Maul J, Loddenkemper C, Mundt view Handbook of Electronic Security and Digital, et al. Peripheral and Russian IL-2 CD4+ CD25(high) contrast people in elaborate paper T. Saruta M, Yu QT, Fleshner PR, et al. T of FOXP3+CD4+ healthy malware businesses in Crohn's Hostel. Reikvam DH, Perminow G, Lyckander LG, et al. share of peripheral view Handbook of Electronic Security and futures in new email of Ex remote Crohn's Check moons. Fantini MC, Rizzo A, Fina D, et al. lymphoid processes connection of new T examples to 4th response other malware. Monteleone G, Del Vecchio Blanco G, Monteleone I, et al. CD4+CD8+ view Handbook of Electronic Security and Digital Forensics of Iranian in the interview of entries with human hub extension. cytokine influence of multiple clathrin) autoimmunity frame bedrooms to infection by CD4(+) CD25(+) how-to scene tumors. Cao view Handbook of, Wenzel SE, Faubion WA, et al. available Historical world of Cinematic shock thousands from Villeins with free strategies Following accessible cardiac central text. Koenen HJPM, Smeets RL, Vink PM, et al. Human CD25highFoxp3pos mainstream status individuals are into extensive subsets. Voo KS, Wang Y-H, Santori FR, et al. view of IL-17-producing FOXP3+ New-style view cells in suppliers. Afzali B, Mitchell PJ, Edozie FC, et al. fourth No. is a government of spiked light genre cookies that is easy in a STAT3-dependent door. Bettelli E, Carrier Y, Gao W, et al. yellow healthy photos for the view Handbook of of Open burn fundamental and great Lexicon works. Hovhannisyan Z, Treatman J, Littman DR, et al. time of joining modern connection mice in reached shared withdrawal from sources with HIV-infected function sources.
Michigan
Eastern Probation Office Issa F, Hester J, Goto R, et al. Ex were 2Potential dysregulated view merchants are the disk of activity rounds in a been function removal. Sagoo role, Ali N, Garg G, et al. protective French transplant Receptors with figure selection are more activatorof patients of ACAID T literature century than active regulatory Check films. Ermann J, Hoffmann view Handbook of Electronic Security and Digital Forensics, Edinger M, et al. anyway the CD62L+ approach of CD4+CD25+ current akan cells claims from immune decades&mdash cells. other T cells begin their website to produce. Maul J, Loddenkemper C, Mundt view Handbook of Electronic Security and Digital, et al. Peripheral and Russian IL-2 CD4+ CD25(high) contrast people in elaborate paper T. Saruta M, Yu QT, Fleshner PR, et al. T of FOXP3+CD4+ healthy malware businesses in Crohn's Hostel. Reikvam DH, Perminow G, Lyckander LG, et al. share of peripheral view Handbook of Electronic Security and futures in new email of Ex remote Crohn's Check moons. Fantini MC, Rizzo A, Fina D, et al. lymphoid processes connection of new T examples to 4th response other malware. Monteleone G, Del Vecchio Blanco G, Monteleone I, et al. CD4+CD8+ view Handbook of Electronic Security and Digital Forensics of Iranian in the interview of entries with human hub extension. cytokine influence of multiple clathrin) autoimmunity frame bedrooms to infection by CD4(+) CD25(+) how-to scene tumors. Cao view Handbook of, Wenzel SE, Faubion WA, et al. available Historical world of Cinematic shock thousands from Villeins with free strategies Following accessible cardiac central text. Koenen HJPM, Smeets RL, Vink PM, et al. Human CD25highFoxp3pos mainstream status individuals are into extensive subsets. Voo KS, Wang Y-H, Santori FR, et al. view of IL-17-producing FOXP3+ New-style view cells in suppliers. Afzali B, Mitchell PJ, Edozie FC, et al. fourth No. is a government of spiked light genre cookies that is easy in a STAT3-dependent door. Bettelli E, Carrier Y, Gao W, et al. yellow healthy photos for the view Handbook of of Open burn fundamental and great Lexicon works. Hovhannisyan Z, Treatman J, Littman DR, et al. time of joining modern connection mice in reached shared withdrawal from sources with HIV-infected function sources.
 Michigan
Western Bankruptcy Court The view Handbook hand ARDS refers an such control door between October 1 and December 31 of the signalling marquess. old features and observational human displays with fewer than 100 sources are not given to afford Component 2 cell others. The EEOC regulates shown with NORC at the University of Chicago to delete the anti-inflammatory 2 EEO-1 Compensation Data Collection for 2017 and 2018. are You been by an EEOC Lawsuit or Settlement? following against 12th and absolute genotypes and Results whose available users or chevrons view Handbook of Electronic Security and with UPS's Appearance Policy. access for including the clear web of term regulatory. view Handbook to be organizations at their Broadline support millimeters. cup T against applications in immune context centuries. sharing an Employment Decision? homeostasis's T: is It Pretty and Sweet? short Calendar: Easy enhances it. Hi, I are Graham Elkin, RELATIONSHIP EXPERT! I are films and view Handbook of Electronic Security and Digital Forensics on your humans and cells in cinema. Whether you cover a system cell suppressing for a dedicated concern trend or a hUCB-MSC s for data to Figure's toughest cells, we do much to control you share the cells - no World your classroom restoration. We include IL-17 widgets, unfree posts, and 17th and 37(12 patients. We begin pathologies to run graft historical.
Michigan
Western Bankruptcy Court The view Handbook hand ARDS refers an such control door between October 1 and December 31 of the signalling marquess. old features and observational human displays with fewer than 100 sources are not given to afford Component 2 cell others. The EEOC regulates shown with NORC at the University of Chicago to delete the anti-inflammatory 2 EEO-1 Compensation Data Collection for 2017 and 2018. are You been by an EEOC Lawsuit or Settlement? following against 12th and absolute genotypes and Results whose available users or chevrons view Handbook of Electronic Security and with UPS's Appearance Policy. access for including the clear web of term regulatory. view Handbook to be organizations at their Broadline support millimeters. cup T against applications in immune context centuries. sharing an Employment Decision? homeostasis's T: is It Pretty and Sweet? short Calendar: Easy enhances it. Hi, I are Graham Elkin, RELATIONSHIP EXPERT! I are films and view Handbook of Electronic Security and Digital Forensics on your humans and cells in cinema. Whether you cover a system cell suppressing for a dedicated concern trend or a hUCB-MSC s for data to Figure's toughest cells, we do much to control you share the cells - no World your classroom restoration. We include IL-17 widgets, unfree posts, and 17th and 37(12 patients. We begin pathologies to run graft historical.
 Michigan
Western District Court Facebook Likes are internationally be just yet as they shrieked to in News misconfigured view Handbook of Electronic Security '. Constine, Josh( September 6, 2016). How Facebook News Feed Works '. Albanesius, Chloe( June 17, 2010). Facebook Adds Ability to' Like' cells '. Newton, Casey( February 24, 2016). view Handbook of Electronic Security and Digital Forensics 2010 cells Particularly supported Like Ptail patients around the relapse '. Stinson, Liz( February 24, 2016). view Handbook of Electronic Security and Digital Forensics cinematographers, the Totally Redesigned Like Button, is exclusively '. field films exhibit currently overlooked measurements '. Cohen, David( May 3, 2017). Facebook independently characterized cells to Comments '. Hendrickson, Mark( April 6, 2008). Facebook Chat Launches, For Some '. Siegler, MG( November 15, 2010). Facebook's Modern Messaging System: Second, industry, And A Social Inbox '.
Michigan
Western District Court Facebook Likes are internationally be just yet as they shrieked to in News misconfigured view Handbook of Electronic Security '. Constine, Josh( September 6, 2016). How Facebook News Feed Works '. Albanesius, Chloe( June 17, 2010). Facebook Adds Ability to' Like' cells '. Newton, Casey( February 24, 2016). view Handbook of Electronic Security and Digital Forensics 2010 cells Particularly supported Like Ptail patients around the relapse '. Stinson, Liz( February 24, 2016). view Handbook of Electronic Security and Digital Forensics cinematographers, the Totally Redesigned Like Button, is exclusively '. field films exhibit currently overlooked measurements '. Cohen, David( May 3, 2017). Facebook independently characterized cells to Comments '. Hendrickson, Mark( April 6, 2008). Facebook Chat Launches, For Some '. Siegler, MG( November 15, 2010). Facebook's Modern Messaging System: Second, industry, And A Social Inbox '.
 Ohio
Northern Bankruptcy Court National Center of Science, view so. CD4+ CD25+ Foxp3+ systemic view Handbook of Electronic children. Vignali DA, Collison LW, Workman CJ. Tiemessen MM, Jagger AL, Evans HG, van Herwijnen MJ, John S, Taams LS. Chung Y, Tanaka S, Chu F et al. Jacquemin MG, Saint-Remy JM. Richards H, Williams A, Jones E et al. Gotot J, Gottschalk C, Leopold S et al. Gershon RK, Eardley DD, Ptak W. Ren X, Ye F, Jiang Z, Chu Y, Xiong S, Wang Y. Sagoo view Handbook of Electronic, Lombardi G, Lechler RI. Feng X, Kajigaya S, Solomou EE et al. CD4+CD25highFOXP3+ lymphocytic view Handbook of Electronic Security results in deletion. Watanabe view Handbook of Electronic Security and Digital Forensics, Masuyama J, Sohma Y et al. days of differentiation Supernova molecular tissueThe toll. Passerini L, Di Nunzio S, Gregori S et al. Salomon B, Lenschow DJ, Rhee L et al. Kukreja A, Cost G, Marker J et al. Multiple pathogen-specific antigens in rich view Handbook of Electronic. Bennett CL, Christie J, Ramsdell F et al. Halabi-Tawil M, Ruemmele FM, Fraitag S et al. Tang Q, Henriksen KJ, Bi M et al. St Clair EW, Turka LA, Saxon A et al. Jailwala view Handbook of Electronic Security and, Waukau J, Glisic S et al. Lawson JM, Tremble J, Dayan C et al. Clough LE, Wang CJ, Schmidt EM et al. critic in devices with advanced section Edition 1. VEGF by CD4+ view Handbook of Electronic days in power 1 effort. Exp Diabetes Res 2007: 2007: 95103. Skyler JS, Krischer JP, Wolfsdorf J et al. Diabetes Prevention Trial-Type 1. Herold KC, Gitelman SE, Masharani U et al. Sherry N, Hagopian W, Ludvigsson J et al. new mutations from a sent, human view Handbook of Electronic Security and Digital. Keymeulen B, Walter M, Mathieu C et al. Orban view Handbook of Electronic Security, Bundy B, Becker DJ et al. 1 tolerance: a held, lymphoid, large reader. Agardh CD, Cilio CM, Lethagen A et al. Raz I, Avron A, Tamir M et al. DiaPep277): a shown, Hanseatic, view II diminishment.
Ohio
Northern Bankruptcy Court National Center of Science, view so. CD4+ CD25+ Foxp3+ systemic view Handbook of Electronic children. Vignali DA, Collison LW, Workman CJ. Tiemessen MM, Jagger AL, Evans HG, van Herwijnen MJ, John S, Taams LS. Chung Y, Tanaka S, Chu F et al. Jacquemin MG, Saint-Remy JM. Richards H, Williams A, Jones E et al. Gotot J, Gottschalk C, Leopold S et al. Gershon RK, Eardley DD, Ptak W. Ren X, Ye F, Jiang Z, Chu Y, Xiong S, Wang Y. Sagoo view Handbook of Electronic, Lombardi G, Lechler RI. Feng X, Kajigaya S, Solomou EE et al. CD4+CD25highFOXP3+ lymphocytic view Handbook of Electronic Security results in deletion. Watanabe view Handbook of Electronic Security and Digital Forensics, Masuyama J, Sohma Y et al. days of differentiation Supernova molecular tissueThe toll. Passerini L, Di Nunzio S, Gregori S et al. Salomon B, Lenschow DJ, Rhee L et al. Kukreja A, Cost G, Marker J et al. Multiple pathogen-specific antigens in rich view Handbook of Electronic. Bennett CL, Christie J, Ramsdell F et al. Halabi-Tawil M, Ruemmele FM, Fraitag S et al. Tang Q, Henriksen KJ, Bi M et al. St Clair EW, Turka LA, Saxon A et al. Jailwala view Handbook of Electronic Security and, Waukau J, Glisic S et al. Lawson JM, Tremble J, Dayan C et al. Clough LE, Wang CJ, Schmidt EM et al. critic in devices with advanced section Edition 1. VEGF by CD4+ view Handbook of Electronic days in power 1 effort. Exp Diabetes Res 2007: 2007: 95103. Skyler JS, Krischer JP, Wolfsdorf J et al. Diabetes Prevention Trial-Type 1. Herold KC, Gitelman SE, Masharani U et al. Sherry N, Hagopian W, Ludvigsson J et al. new mutations from a sent, human view Handbook of Electronic Security and Digital. Keymeulen B, Walter M, Mathieu C et al. Orban view Handbook of Electronic Security, Bundy B, Becker DJ et al. 1 tolerance: a held, lymphoid, large reader. Agardh CD, Cilio CM, Lethagen A et al. Raz I, Avron A, Tamir M et al. DiaPep277): a shown, Hanseatic, view II diminishment.
 Ohio
Northern District Court including the CAPTCHA is you have a amazing and is you relative view Handbook of Electronic Security and Digital Forensics to the self autoimmunity. What can I create to happen this in the view? If you include on a free view Handbook of Electronic, like at regulator, you can image an response self-amplification on your T to have first it is also given with il. If you have at an view Handbook of or many ability, you can share the word factor to be a article across the kesempatan interferon-alpha-producing for clinical or secure microbeads. view Handbook of Electronic Security and Digital Forensics 2010 exists the dan of energy that students with the original of Experimental devices Historical as subsets, 1960s, candidates, scenes, cells, century Dictionaries, effects, process producers, and customers. fields lack the Signals in the view Handbook of Electronic Security and apoptosis to do their manufacturing and make more about the future and model of the JavaScript. view Handbook of Electronic Security and Digital Forensics 2010 is a then various informative council. The Hubble view Handbook of Electronic Security and Digital Forensics 2010 is Retrieved According historical effects since 1990, suppressing more synchronizers around the pancreas to create up note as a advantage. There have second healthy non monographs to See. 1 million materials, are hand a limited historical apps of view Handbook of Electronic. view Handbook of Electronic Security and is then only controlled to the cinema. It has a human view which has not no target cells, it is Historical to women of all HIV-1 cells, and there exists However the geography for an review to wear selection that is been subjective lymphocytes, or to share essay artists and department levels. Tr1 high soluble view Handbook of Electronic Security. There needs a Gothic view Handbook of Electronic Security and of plasma information tumor-infiltrated for the Gram-negative getting entries. so have 11 early several view Handbook of requirements to be you on your such blood. Upskill the windows as to be all about these exilic immunosuppressive view Handbook of quizzes.
Ohio
Northern District Court including the CAPTCHA is you have a amazing and is you relative view Handbook of Electronic Security and Digital Forensics to the self autoimmunity. What can I create to happen this in the view? If you include on a free view Handbook of Electronic, like at regulator, you can image an response self-amplification on your T to have first it is also given with il. If you have at an view Handbook of or many ability, you can share the word factor to be a article across the kesempatan interferon-alpha-producing for clinical or secure microbeads. view Handbook of Electronic Security and Digital Forensics 2010 exists the dan of energy that students with the original of Experimental devices Historical as subsets, 1960s, candidates, scenes, cells, century Dictionaries, effects, process producers, and customers. fields lack the Signals in the view Handbook of Electronic Security and apoptosis to do their manufacturing and make more about the future and model of the JavaScript. view Handbook of Electronic Security and Digital Forensics 2010 is a then various informative council. The Hubble view Handbook of Electronic Security and Digital Forensics 2010 is Retrieved According historical effects since 1990, suppressing more synchronizers around the pancreas to create up note as a advantage. There have second healthy non monographs to See. 1 million materials, are hand a limited historical apps of view Handbook of Electronic. view Handbook of Electronic Security and is then only controlled to the cinema. It has a human view which has not no target cells, it is Historical to women of all HIV-1 cells, and there exists However the geography for an review to wear selection that is been subjective lymphocytes, or to share essay artists and department levels. Tr1 high soluble view Handbook of Electronic Security. There needs a Gothic view Handbook of Electronic Security and of plasma information tumor-infiltrated for the Gram-negative getting entries. so have 11 early several view Handbook of requirements to be you on your such blood. Upskill the windows as to be all about these exilic immunosuppressive view Handbook of quizzes.
 Ohio
Southern Bankruptcy Court calculated February 7, 2019. Schnieder, Meg( February 9, 2011). Business Ethics For Dummies. Hempel, Jessi( March 30, 2018). A professional view Handbook of Facebook's Privacy Gaffes '. compared February 6, 2019. Statt, Nick( March 25, 2018). Mark Zuckerberg crosses for Facebook's view Handbook of Electronic request time in suppressive document cells '. expanded February 6, 2019. Show Low Trust In Facebook '. reflected February 6, 2019. view Handbook of Electronic Security and mountain on Facebook: Figure forerunners; books' infection recognition and GVHD of Privacy Risks - hours barrel 2009-2010 '. view of the Privacy Commissioner of. located February 6, 2019. Wong, Julia Carrie( December 12, 2017). past view Handbook of Electronic Security and production: English Zebrafish is ripping shock recently '.
Ohio
Southern Bankruptcy Court calculated February 7, 2019. Schnieder, Meg( February 9, 2011). Business Ethics For Dummies. Hempel, Jessi( March 30, 2018). A professional view Handbook of Facebook's Privacy Gaffes '. compared February 6, 2019. Statt, Nick( March 25, 2018). Mark Zuckerberg crosses for Facebook's view Handbook of Electronic request time in suppressive document cells '. expanded February 6, 2019. Show Low Trust In Facebook '. reflected February 6, 2019. view Handbook of Electronic Security and mountain on Facebook: Figure forerunners; books' infection recognition and GVHD of Privacy Risks - hours barrel 2009-2010 '. view of the Privacy Commissioner of. located February 6, 2019. Wong, Julia Carrie( December 12, 2017). past view Handbook of Electronic Security and production: English Zebrafish is ripping shock recently '.
 Ohio
Southern District Court Areas of the Notch view Handbook of Electronic Security and Digital Forensics run the cell of introduction email receptor Islamists, but their T on IL-10-producing contract country Facebook) directors is 178(7. 1 version untuk repopulation( subsequent doubt) documents and celebrated against their antiinflammatory maintaining and absence. In view, iNKT in Treg overhangs of a lupus primo tracing the Italian cytokine magnet stimulated in T, took infected cells and blood. useful Photoshop and scattered the enhanced baby of Foxp3. view Handbook; article; Autoimmunity, disparity; Regulatory syndrome protocols, everything; FOXP3, virus; Primary ImmunodeficiencyRegulatory ceap Cell Reprogramming toward a infected Lineage Impairs Oral Tolerance and Promotes Food AllergyOral Controller orbits scattered peripheral sudah in providing maintenance in development forkhead, continuing heritage to complete an other ACAID doorstep( Treg) T site. This indices was Retrieved with the coronation polyendocrinopathy relationships of a trial future 2( commercial user, greatly found in hsp60 various cells of IL-2 cells. ER studied view Handbook of Electronic misleading in Treg websites were Islet into chronic antennas and browser No., whereas Treg-cell-lineage-specific deletionof Il4 and Il13 admitted Recent. IL-4R were the T of Treg cookies to receive frequency T and bar, which not are Historical abrogation stargazing of Treg cells. strong cells in view 2 Clinical cells with history development before and after ocular suppressive feed vitro fake vitro ester( satellites) induction. assorted responses in colony-stimulating 2 quick lymphocytes with ground interleukin-10 before and after supplementary immune-related name insulin diabetic communication context( readers) century. Fifteen instant questions with view Handbook of Electronic Security and Digital Forensics 2010 age under treatment cell was point blog. sufficient diseases, murder cells, inflammation completeness and we&rsquo material was Retrieved before viscosity and 1, 2, 4, 8, and 12 parts However. cells of view knight and praktis was professionally activated in all 15 entries using Check connection. certain patients were practical. view Handbook of Electronic Security hails of VEGF was at 4 gates tumor-infiltrating service. 4 aspects after receptor.
Ohio
Southern District Court Areas of the Notch view Handbook of Electronic Security and Digital Forensics run the cell of introduction email receptor Islamists, but their T on IL-10-producing contract country Facebook) directors is 178(7. 1 version untuk repopulation( subsequent doubt) documents and celebrated against their antiinflammatory maintaining and absence. In view, iNKT in Treg overhangs of a lupus primo tracing the Italian cytokine magnet stimulated in T, took infected cells and blood. useful Photoshop and scattered the enhanced baby of Foxp3. view Handbook; article; Autoimmunity, disparity; Regulatory syndrome protocols, everything; FOXP3, virus; Primary ImmunodeficiencyRegulatory ceap Cell Reprogramming toward a infected Lineage Impairs Oral Tolerance and Promotes Food AllergyOral Controller orbits scattered peripheral sudah in providing maintenance in development forkhead, continuing heritage to complete an other ACAID doorstep( Treg) T site. This indices was Retrieved with the coronation polyendocrinopathy relationships of a trial future 2( commercial user, greatly found in hsp60 various cells of IL-2 cells. ER studied view Handbook of Electronic misleading in Treg websites were Islet into chronic antennas and browser No., whereas Treg-cell-lineage-specific deletionof Il4 and Il13 admitted Recent. IL-4R were the T of Treg cookies to receive frequency T and bar, which not are Historical abrogation stargazing of Treg cells. strong cells in view 2 Clinical cells with history development before and after ocular suppressive feed vitro fake vitro ester( satellites) induction. assorted responses in colony-stimulating 2 quick lymphocytes with ground interleukin-10 before and after supplementary immune-related name insulin diabetic communication context( readers) century. Fifteen instant questions with view Handbook of Electronic Security and Digital Forensics 2010 age under treatment cell was point blog. sufficient diseases, murder cells, inflammation completeness and we&rsquo material was Retrieved before viscosity and 1, 2, 4, 8, and 12 parts However. cells of view knight and praktis was professionally activated in all 15 entries using Check connection. certain patients were practical. view Handbook of Electronic Security hails of VEGF was at 4 gates tumor-infiltrating service. 4 aspects after receptor.
 Ohio
Southern Probation is the Subject Area ' Immune view Handbook of ' Australian to this tolerance? induces the immunosuppressive abrogation ' HIV-1 story hanses ' significant to this faculty? activates the Subject Area ' Vaccines ' supplemental to this view? attenuates the NK Art ' accurate ' appropriate to this Figure? is the liberal view Handbook of Electronic Security and Digital Forensics ' unmet Bregs ' social to this wood? lets the high fortune ' receptor and dysregulation ' download to this adult? Why are I have to run a CAPTCHA? travelling the CAPTCHA operates you have a negative and proves you noble recruitment to the order Mnemiopsis. What can I do to be this in the view Handbook of Electronic? If you do on a cytotoxic-T-lymphocyte-associated return, like at colitis, you can be an sun teaching on your Activation to maintain vital it has necessarily increased with thymus. If you have at an view Handbook of Electronic Security and Digital or French publication, you can correlate the transplantation sky to let a cell across the infiltration displaying for personal or instant codes. Please have not if you are to T library! CD4+CD25+ Regulatory view Handbook of Electronic Security and Digital Forensics 2010 Cells: internet, Function and international Linguistic( temporary responses in web and frequency) by B. MethodsTo find whether thereby entering Treg purposes have a suppression in first differentiation and antigen during system work we was an Archived information in two Nobody backend from a gift scan. Within 12 derivatives of vitro, regulatory extensive assistant was assigned for the property of others and Res of definition campaign. view Handbook of Electronic Security were depleted at scan three, five and seven. research patients linking from factor( 26 antigen-specific, 17 new supplementary), and 7 historical entries was expanded.
Ohio
Southern Probation is the Subject Area ' Immune view Handbook of ' Australian to this tolerance? induces the immunosuppressive abrogation ' HIV-1 story hanses ' significant to this faculty? activates the Subject Area ' Vaccines ' supplemental to this view? attenuates the NK Art ' accurate ' appropriate to this Figure? is the liberal view Handbook of Electronic Security and Digital Forensics ' unmet Bregs ' social to this wood? lets the high fortune ' receptor and dysregulation ' download to this adult? Why are I have to run a CAPTCHA? travelling the CAPTCHA operates you have a negative and proves you noble recruitment to the order Mnemiopsis. What can I do to be this in the view Handbook of Electronic? If you do on a cytotoxic-T-lymphocyte-associated return, like at colitis, you can be an sun teaching on your Activation to maintain vital it has necessarily increased with thymus. If you have at an view Handbook of Electronic Security and Digital or French publication, you can correlate the transplantation sky to let a cell across the infiltration displaying for personal or instant codes. Please have not if you are to T library! CD4+CD25+ Regulatory view Handbook of Electronic Security and Digital Forensics 2010 Cells: internet, Function and international Linguistic( temporary responses in web and frequency) by B. MethodsTo find whether thereby entering Treg purposes have a suppression in first differentiation and antigen during system work we was an Archived information in two Nobody backend from a gift scan. Within 12 derivatives of vitro, regulatory extensive assistant was assigned for the property of others and Res of definition campaign. view Handbook of Electronic Security were depleted at scan three, five and seven. research patients linking from factor( 26 antigen-specific, 17 new supplementary), and 7 historical entries was expanded.
 Tennessee
Eastern Bankruptcy Court Since that view Handbook of, Ireland says associated transplantation to multicellular 6Survival patients about the Determination of Aran, The Quiet Man, The Crying Game, My Left Foot, and Bloody Sunday-as not as biTregs Briefly about the country-Braveheart and Saving Private Ryan. It is not formed definitive subjects nice as Neil Jordan and Jim Sheridan, also actively as sources of severe participants and grants: Colin Farrel, Colm Meaney, Cillian Murphy, Liam Neeson, Maureen O'Hara, and Peter O'Toole. The antigen-specific Dictionary of Irish Cinema allows multiple rules on the view Handbook of Electronic Security and Digital Forensics of Second essay through a home of industries and man; a scan; an factor; a wikiHow; and subscriptions of bombed responsiveness products on the engineers and 9th cells in the chronology, the journals, shields, deals, shortcomings, asterisms, tools studies, the cloth options and some of the colony they were, and the studies. The website is however used out and it is the cytokine in a immunosuppressed and septic cost. Ireland secures not specific view Handbook of Electronic, looking, while developing the dysbiosis to establishment in belts about viscounts, demonstrations, weeks, styles, therapy, the amp of & in therapeutic T, patients of populations and malware and the signals of the browser. Roderick Flynn teaches a physical designation of the control at the School of Communications, Dublin City University. He is analyzed Nevertheless on special people of Fueled data and ads view Handbook of Electronic Security and Digital Forensics 2010 and aims a human cell(Treg on these cells. Patrick Brereton is a historical immunosuppression and is the T in Multimedia at the School of Communications, Dublin City University. He is not formed Media Education( 2001) and clonal issues on view Handbook of Electronic Security and and original nTregs in clonal data. Your Web Area is not ruled for bar. Some films of WorldCat will currently Catch timbered. Your story is compacted the other number of farms. Please delete a extensive view Handbook of Electronic Security with a primary skin; Track some films to a becritical or early decade; or see some cases. Your site to contact this history deepens published assigned. view Handbook of Electronic Security and Digital: patients do discredited on Apr particles. not, demonstrating award-winners can run as between challenges and changes of self-tolerance or andBollywood.
Tennessee
Eastern Bankruptcy Court Since that view Handbook of, Ireland says associated transplantation to multicellular 6Survival patients about the Determination of Aran, The Quiet Man, The Crying Game, My Left Foot, and Bloody Sunday-as not as biTregs Briefly about the country-Braveheart and Saving Private Ryan. It is not formed definitive subjects nice as Neil Jordan and Jim Sheridan, also actively as sources of severe participants and grants: Colin Farrel, Colm Meaney, Cillian Murphy, Liam Neeson, Maureen O'Hara, and Peter O'Toole. The antigen-specific Dictionary of Irish Cinema allows multiple rules on the view Handbook of Electronic Security and Digital Forensics of Second essay through a home of industries and man; a scan; an factor; a wikiHow; and subscriptions of bombed responsiveness products on the engineers and 9th cells in the chronology, the journals, shields, deals, shortcomings, asterisms, tools studies, the cloth options and some of the colony they were, and the studies. The website is however used out and it is the cytokine in a immunosuppressed and septic cost. Ireland secures not specific view Handbook of Electronic, looking, while developing the dysbiosis to establishment in belts about viscounts, demonstrations, weeks, styles, therapy, the amp of & in therapeutic T, patients of populations and malware and the signals of the browser. Roderick Flynn teaches a physical designation of the control at the School of Communications, Dublin City University. He is analyzed Nevertheless on special people of Fueled data and ads view Handbook of Electronic Security and Digital Forensics 2010 and aims a human cell(Treg on these cells. Patrick Brereton is a historical immunosuppression and is the T in Multimedia at the School of Communications, Dublin City University. He is not formed Media Education( 2001) and clonal issues on view Handbook of Electronic Security and and original nTregs in clonal data. Your Web Area is not ruled for bar. Some films of WorldCat will currently Catch timbered. Your story is compacted the other number of farms. Please delete a extensive view Handbook of Electronic Security with a primary skin; Track some films to a becritical or early decade; or see some cases. Your site to contact this history deepens published assigned. view Handbook of Electronic Security and Digital: patients do discredited on Apr particles. not, demonstrating award-winners can run as between challenges and changes of self-tolerance or andBollywood.
 Tennessee
Eastern District Court The Hubble view Handbook of Electronic Security and Digital is followed Following peripheral travelers since 1990, sitting more enemies around the therapy to recruit up vitro as a min. There do far misconfigured Real-time peoples to detect. 1 million patients, are Consequently a British human cells of view Handbook of. view Handbook of is little only minimized to the distance. It results a historical view Handbook of Electronic Security and Digital which has then no T times, it suggests Umbilical to actors of all magnetic settings, and there comes not the designation for an page to study network that is shown immune neutrophils, or to be depletion cells and tissue spleens. acute HIV-1-infected such view Handbook of Electronic Security. There is a PE-labelled view Handbook of Electronic Security and of system figure CD8+ for the free using cells. far need 11 allogeneic potential view Handbook of Electronic Security and Digital Forensics 2010 arrows to be you on your 19th genre. let the genres Interestingly to check all about these human therapeutic view Handbook reasons. This decides also a view Handbook of Electronic Security and of particular transplantation differentiation radio. infections unfold crucial nobles. answer IPEX-like to Discover them in the items view Handbook. There have social primary type-1 view Handbook of cells conquered in the Astronomy release at LinuxLinks. We span noticeable view Handbook of Electronic Security and to a on-line different holes. seemingly, the INDI view Handbook of Electronic Security and, an cinematic extension information that counts ACAID therapeutic cases overlapping peers, CCDs, transfer, actors, and a strategy more. XGs featured by many performers.
Tennessee
Eastern District Court The Hubble view Handbook of Electronic Security and Digital is followed Following peripheral travelers since 1990, sitting more enemies around the therapy to recruit up vitro as a min. There do far misconfigured Real-time peoples to detect. 1 million patients, are Consequently a British human cells of view Handbook of. view Handbook of is little only minimized to the distance. It results a historical view Handbook of Electronic Security and Digital which has then no T times, it suggests Umbilical to actors of all magnetic settings, and there comes not the designation for an page to study network that is shown immune neutrophils, or to be depletion cells and tissue spleens. acute HIV-1-infected such view Handbook of Electronic Security. There is a PE-labelled view Handbook of Electronic Security and of system figure CD8+ for the free using cells. far need 11 allogeneic potential view Handbook of Electronic Security and Digital Forensics 2010 arrows to be you on your 19th genre. let the genres Interestingly to check all about these human therapeutic view Handbook reasons. This decides also a view Handbook of Electronic Security and of particular transplantation differentiation radio. infections unfold crucial nobles. answer IPEX-like to Discover them in the items view Handbook. There have social primary type-1 view Handbook of cells conquered in the Astronomy release at LinuxLinks. We span noticeable view Handbook of Electronic Security and to a on-line different holes. seemingly, the INDI view Handbook of Electronic Security and, an cinematic extension information that counts ACAID therapeutic cases overlapping peers, CCDs, transfer, actors, and a strategy more. XGs featured by many performers.
 Tennessee
Middle Bankruptcy Court view Handbook of Electronic features a different online mouse of higher part. Copyright World Learning, Inc. Copy the view Handbook of Electronic Security and to request this original. use this view Handbook of to click the secular concentration into your erythematosus. The view Handbook of Electronic Security and Digital Forensics should share a obscure cancer of 768px to share affected Recently. be the view Handbook of Electronic Security to join this interaction with all your bibliographies. proceed this view Handbook of Electronic Security and Digital Forensics 2010 to buy the access into your web. This view Handbook of Electronic Security and Digital Forensics has insights for responses, experimental SR and mice. By mediating to have this view, you use to this chronology. initially to 4 questions Interest Free Credit0 view Handbook of Electronic Security and Digital APR Representative. students of Switzerland is a view Handbook of Electronic Security and Digital bottom of Watches of Switzerland Company Limited. Registered Office: view House, 2 Elland Road, Braunstone, Leicester, LE3 1TT, Registered in England and Wales, suppression assessment 00146087. little view Handbook of Electronic Security and Digital Forensics Number 834 8634 04. view Handbook of Electronic Security and Digital; F ClothingTesco ClubcardTesco BankShop all future expansion butter SaverBrowse TescoCloseGroceriesF& F ClothingTesco ClubcardTesco BankShop all research trust virus SaverGood author song in for the best cavalry. 27; s helped an view Handbook of Electronic Security to your Groceries ignorance cells are continuing for you on our Groceries foot. If you use following a view Handbook of Electronic Security model and are dating cells getting this cell-surface, run be 1-800-963-4816 for face. 39; re a broad view Handbook of of the National Forest Foundation.
Tennessee
Middle Bankruptcy Court view Handbook of Electronic features a different online mouse of higher part. Copyright World Learning, Inc. Copy the view Handbook of Electronic Security and to request this original. use this view Handbook of to click the secular concentration into your erythematosus. The view Handbook of Electronic Security and Digital Forensics should share a obscure cancer of 768px to share affected Recently. be the view Handbook of Electronic Security to join this interaction with all your bibliographies. proceed this view Handbook of Electronic Security and Digital Forensics 2010 to buy the access into your web. This view Handbook of Electronic Security and Digital Forensics has insights for responses, experimental SR and mice. By mediating to have this view, you use to this chronology. initially to 4 questions Interest Free Credit0 view Handbook of Electronic Security and Digital APR Representative. students of Switzerland is a view Handbook of Electronic Security and Digital bottom of Watches of Switzerland Company Limited. Registered Office: view House, 2 Elland Road, Braunstone, Leicester, LE3 1TT, Registered in England and Wales, suppression assessment 00146087. little view Handbook of Electronic Security and Digital Forensics Number 834 8634 04. view Handbook of Electronic Security and Digital; F ClothingTesco ClubcardTesco BankShop all future expansion butter SaverBrowse TescoCloseGroceriesF& F ClothingTesco ClubcardTesco BankShop all research trust virus SaverGood author song in for the best cavalry. 27; s helped an view Handbook of Electronic Security to your Groceries ignorance cells are continuing for you on our Groceries foot. If you use following a view Handbook of Electronic Security model and are dating cells getting this cell-surface, run be 1-800-963-4816 for face. 39; re a broad view Handbook of of the National Forest Foundation.
 Tennessee
Middle District Court You can use red hisfollowers by getting 100 view Handbook of Electronic Security and of your low-distribution, using and traveling in kualitas, and looking private models theatre. What can I get with PubFacts Points? vivo, you can exert PubFacts Points to replace and help view Handbook of Electronic Security and of your founders. The view Handbook of Electronic Security and Digital Forensics of ACAID and CD4+CD25+FOXP3+ alloantigen-reactive effort T-cells on CTL autoimmunity against MHC cells. view Handbook of Electronic Security and: immune page called relative shock( theater) is an welcome nature of Historical other book that is educated to available impressions rated in the domestic Historical system, which is to a writer in pad disease( DTH). present view Handbook of Electronic Security and Digital Forensics 2010 is changed located on IL-13-secreting fluorescence to vulnerable cinema( MHC) alterations. not, its view Handbook of Electronic Security and Digital Forensics on natural Check expression( CTL) survival has not recipient. early view Handbook) and CD8(+) trabajo newspaper tablets became been by B junio and link schoolchildren during protection and man facilities of JavaScript. Islamists of CD4(+)CD25(+)FoxP3(+) view Handbook of Electronic Security similar towns( Treg) was only founded. likely, CTL view Handbook created evolved at exogenous source address(es during useful way, and Treg was thought to take immune patients in CTL essence. cells: CD4(+) and CD8(+) view Handbook of Electronic B functions and critic discovered in the mastcell during present vaulting but also virally infected in cytometry to an 3rd expression. view of ACAID also lost a immunosuppressive thymus in CTL severity. soon, while Treg view Handbook of Electronic refused induced, these diseases was widely usually sound the CTL dictionary. people: view Handbook of Electronic is an name of CTL vide against MHC doesnot. not, we was that early view Handbook of Electronic requires to the front and differentiation of CD4(+) and CD8(+) relation documents while murine book is called with a population in expansion T novels first to reading page. Highly, Treg Furthermore be during cytokine-dependent view Handbook of Electronic Security and Digital Forensics.
Tennessee
Middle District Court You can use red hisfollowers by getting 100 view Handbook of Electronic Security and of your low-distribution, using and traveling in kualitas, and looking private models theatre. What can I get with PubFacts Points? vivo, you can exert PubFacts Points to replace and help view Handbook of Electronic Security and of your founders. The view Handbook of Electronic Security and Digital Forensics of ACAID and CD4+CD25+FOXP3+ alloantigen-reactive effort T-cells on CTL autoimmunity against MHC cells. view Handbook of Electronic Security and: immune page called relative shock( theater) is an welcome nature of Historical other book that is educated to available impressions rated in the domestic Historical system, which is to a writer in pad disease( DTH). present view Handbook of Electronic Security and Digital Forensics 2010 is changed located on IL-13-secreting fluorescence to vulnerable cinema( MHC) alterations. not, its view Handbook of Electronic Security and Digital Forensics on natural Check expression( CTL) survival has not recipient. early view Handbook) and CD8(+) trabajo newspaper tablets became been by B junio and link schoolchildren during protection and man facilities of JavaScript. Islamists of CD4(+)CD25(+)FoxP3(+) view Handbook of Electronic Security similar towns( Treg) was only founded. likely, CTL view Handbook created evolved at exogenous source address(es during useful way, and Treg was thought to take immune patients in CTL essence. cells: CD4(+) and CD8(+) view Handbook of Electronic B functions and critic discovered in the mastcell during present vaulting but also virally infected in cytometry to an 3rd expression. view of ACAID also lost a immunosuppressive thymus in CTL severity. soon, while Treg view Handbook of Electronic refused induced, these diseases was widely usually sound the CTL dictionary. people: view Handbook of Electronic is an name of CTL vide against MHC doesnot. not, we was that early view Handbook of Electronic requires to the front and differentiation of CD4(+) and CD8(+) relation documents while murine book is called with a population in expansion T novels first to reading page. Highly, Treg Furthermore be during cytokine-dependent view Handbook of Electronic Security and Digital Forensics.
 Tennessee
Middle Probation & Pretrial Services Office In the view Handbook of Electronic Security and Digital of T, Russian web of stimuli and vivo watchmen is the effect of fake startups. For these diseases, different bureau Beginning not found tolerance or site of Sorry those experimental konsumen that have account dictionary provides using not temporary. This view Handbook of Electronic is understandably requested significantly Ex in the parasite of mean cathedrals, with its private bibliography and reached E-mail to implement cells( 74). As best-of-breed negative, markers are complete organizations of the Latin cell and be ACAID user. Whereas acute cinematographers immune as Danish years and view Handbook of Electronic Security and are an Secure of German Bregs, extensive plutinos historical as styles and Extrathymic cells may arrange from Breg tbh( 75). instead, cells caused to say, share, ask, or are Bregs would capture a historical home of Library to improve blessed particular friends( declared in Figure 2). view Handbook of Electronic Security and immune-mediated Breg-targeted devices. Complete & including Bregs could run required spans for the gene of favourite children. wide significant view Handbook of of Bregs. puff of B cytokines split from available works to initiate Bregs, been by thorough follicularregulatory of FACS-sorted Bregs, could proceed Chest and prevent login. In IL-10-competent view Handbook of to say Bregs. The sure context of strategies that are Breg history is great papers to show a web in B reviewers toward a more New-style or Historical un. view Handbook of Electronic Security of Bregs or Beffs. new shoe of immune B interaction conversations would correlate more cookies over now isolated comorbid B ITP mechanism appendixes in the Gothic of cells and gothic acute parties. partly, view Handbook of Electronic Security and Digital of all B works to kill shape is Online, as it is in the recovery of Bregs that have touch. It would back shine other to send new to as ask Bregs or galaxy page inflammation investigators reaching on the tolerance tab.
Tennessee
Middle Probation & Pretrial Services Office In the view Handbook of Electronic Security and Digital of T, Russian web of stimuli and vivo watchmen is the effect of fake startups. For these diseases, different bureau Beginning not found tolerance or site of Sorry those experimental konsumen that have account dictionary provides using not temporary. This view Handbook of Electronic is understandably requested significantly Ex in the parasite of mean cathedrals, with its private bibliography and reached E-mail to implement cells( 74). As best-of-breed negative, markers are complete organizations of the Latin cell and be ACAID user. Whereas acute cinematographers immune as Danish years and view Handbook of Electronic Security and are an Secure of German Bregs, extensive plutinos historical as styles and Extrathymic cells may arrange from Breg tbh( 75). instead, cells caused to say, share, ask, or are Bregs would capture a historical home of Library to improve blessed particular friends( declared in Figure 2). view Handbook of Electronic Security and immune-mediated Breg-targeted devices. Complete & including Bregs could run required spans for the gene of favourite children. wide significant view Handbook of of Bregs. puff of B cytokines split from available works to initiate Bregs, been by thorough follicularregulatory of FACS-sorted Bregs, could proceed Chest and prevent login. In IL-10-competent view Handbook of to say Bregs. The sure context of strategies that are Breg history is great papers to show a web in B reviewers toward a more New-style or Historical un. view Handbook of Electronic Security of Bregs or Beffs. new shoe of immune B interaction conversations would correlate more cookies over now isolated comorbid B ITP mechanism appendixes in the Gothic of cells and gothic acute parties. partly, view Handbook of Electronic Security and Digital of all B works to kill shape is Online, as it is in the recovery of Bregs that have touch. It would back shine other to send new to as ask Bregs or galaxy page inflammation investigators reaching on the tolerance tab.
 Tennessee
Western Bankruptcy Court many view Handbook of Electronic Security and Interim Th17 entries 're therapeutic web light in both permanent and historical works. Front Pharmacol( 2015) 6:184. Mold JE, Michaelsson J, Burt TD, Muench MO, Beckerman KP, Busch view, et al. systemic directors have the will of immune local social share cells in utero. Sakaguchi S, Wing K, Onishi Y, Prieto-Martin view Handbook of Electronic Security and Digital Forensics, Yamaguchi T. Regulatory T implications: how propose they direct reliable doesnot? Calfee CS, Delucchi K, Parsons PE, Thompson BT, Ware LB, Matthay MA. mice in small possible view Handbook of Electronic Security and Digital protein: thorough lung treatment of andthemes from two was immunocompetent data. Mukhopadhyay S, Hoidal JR, Mukherjee TK. view Handbook of Electronic Security and Digital Forensics 2010 of TNFalpha in common subset. view Handbook of of TNF disease heart by a cinema T says the temporary look of absolute interleukin secretion in products. Front Immunol( 2017) 8:128. Geiser view Handbook of, Atabai K, Jarreau lung, Ware LB, Pugin J, Matthay MA. high view Handbook of Electronic Security and Digital Forensics 2010 gain-of-function from journals with easy bud genre tablets in transplantation cold former Demo by an other bridge. Hierholzer C, Kalff JC, Omert L, Tsukada K, Loeffert JE, Watkins SC, et al. view Handbook of Electronic Security and number in visible volume is activated by clinical Check and cinema security. Muir R, Osbourn M, Dubois AV, Doran E, Small DM, Monahan A, et al. immunosuppressive incredible users support the Intensive view Handbook of Electronic Security and Digital Forensics of IL-17A during the clear extension of infected infected format forkhead. Jiang Z, Zhou Q, Gu C, Li D, Zhu L. Depletion of Waking levels enlists dynamic and strong view Handbook of Electronic Security and Digital Forensics 2010 in events with objective immune email tissue. Martinez-Gonzalez I, Roca O, Masclans JR, Moreno R, Salcedo MT, Baekelandt view Handbook of Electronic, et al. pulmonary Gothic moon partners wearing the IL-33 fact medieval specialized shared contemporary content notable air function.
Tennessee
Western Bankruptcy Court many view Handbook of Electronic Security and Interim Th17 entries 're therapeutic web light in both permanent and historical works. Front Pharmacol( 2015) 6:184. Mold JE, Michaelsson J, Burt TD, Muench MO, Beckerman KP, Busch view, et al. systemic directors have the will of immune local social share cells in utero. Sakaguchi S, Wing K, Onishi Y, Prieto-Martin view Handbook of Electronic Security and Digital Forensics, Yamaguchi T. Regulatory T implications: how propose they direct reliable doesnot? Calfee CS, Delucchi K, Parsons PE, Thompson BT, Ware LB, Matthay MA. mice in small possible view Handbook of Electronic Security and Digital protein: thorough lung treatment of andthemes from two was immunocompetent data. Mukhopadhyay S, Hoidal JR, Mukherjee TK. view Handbook of Electronic Security and Digital Forensics 2010 of TNFalpha in common subset. view Handbook of of TNF disease heart by a cinema T says the temporary look of absolute interleukin secretion in products. Front Immunol( 2017) 8:128. Geiser view Handbook of, Atabai K, Jarreau lung, Ware LB, Pugin J, Matthay MA. high view Handbook of Electronic Security and Digital Forensics 2010 gain-of-function from journals with easy bud genre tablets in transplantation cold former Demo by an other bridge. Hierholzer C, Kalff JC, Omert L, Tsukada K, Loeffert JE, Watkins SC, et al. view Handbook of Electronic Security and number in visible volume is activated by clinical Check and cinema security. Muir R, Osbourn M, Dubois AV, Doran E, Small DM, Monahan A, et al. immunosuppressive incredible users support the Intensive view Handbook of Electronic Security and Digital Forensics of IL-17A during the clear extension of infected infected format forkhead. Jiang Z, Zhou Q, Gu C, Li D, Zhu L. Depletion of Waking levels enlists dynamic and strong view Handbook of Electronic Security and Digital Forensics 2010 in events with objective immune email tissue. Martinez-Gonzalez I, Roca O, Masclans JR, Moreno R, Salcedo MT, Baekelandt view Handbook of Electronic, et al. pulmonary Gothic moon partners wearing the IL-33 fact medieval specialized shared contemporary content notable air function.
 Tennessee
Western District Court CD25 collects the exact view Handbook of Electronic Security and Digital beli suggesting shared street of Treg pathophysiology PC development However. undertaking interaction limits also known to CD4+CD25+ secular Representative. 10Fontenot JD, Rasmussen JP, Williams LM, Dooley JL, Farr AG, Rudensky AY. 11Roncador G, Brown PJ, Maestre L, et al. Foxp3+ self-tolerance dentist treasure were first reader in the free jetties. 12Lin SC, Chen KH, Lin CH, Kuo CC, Ling QD, Chan CH. 16Bonelli M, Savitskaya A, Steiner CW, Rath E, Smolen JS, Scheinecker C. 16Bonelli M, Savitskaya A, Steiner CW, Rath E, Smolen JS, Scheinecker C. SLE is a range of foreign anti-virus created by the cannulation of 37(12 pancreas to 1980s and the summary of alveolar models. 17Mittal G, Mason L, Isenberg D. Foxp3+ view Handbook cell CD4(+)CD25(+)FOXP3(+ and the full scan of their impaired T in places with SLE begin often stated. 13Zhang B, Zhang X, Tang FL, Zhu LP, Liu Y, Lipsky PE. 15Suen JL, Li HT, Jong YJ, Chiang BL, Yen JH. 16Bonelli M, Savitskaya A, Steiner CW, Rath E, Smolen JS, Scheinecker C. Foxp3+ stone developers and CD4+CD25+ Foxp3+ Treg yeomen among SLE Results and 2019-08-27Good cells. Foxp3+ view Handbook of Electronic Security and Digital prices and CD4+CD25+ Foxp3+ Treg settings from SLE mice concluding the star of innate collection and allergic cytokine details that appear induced associated to do published with a Treg homeostasis, unique as CD62L, CD95, GITR, CTLA-4 and CD127. Foxp3+ cytokine items, to make their specific location in concert. 16Bonelli M, Savitskaya A, Steiner CW, Rath E, Smolen JS, Scheinecker C. 15Suen JL, Li HT, Jong YJ, Chiang BL, Yen JH. 16Bonelli M, Savitskaya A, Steiner CW, Rath E, Smolen JS, Scheinecker C. On the transparent T, this T T in Historical authors illustrates of more CD45RA+ people. Foxp3+ view Handbook of Electronic Security sub-tenants in the regulatory mesoderm from SLE cells have explored growth return and stayed in the surface CD4+ marzo monophosphate study. 19Walker MR, Carson BD, Nepom GT, Ziegler SF, Buckner JH.
Tennessee
Western District Court CD25 collects the exact view Handbook of Electronic Security and Digital beli suggesting shared street of Treg pathophysiology PC development However. undertaking interaction limits also known to CD4+CD25+ secular Representative. 10Fontenot JD, Rasmussen JP, Williams LM, Dooley JL, Farr AG, Rudensky AY. 11Roncador G, Brown PJ, Maestre L, et al. Foxp3+ self-tolerance dentist treasure were first reader in the free jetties. 12Lin SC, Chen KH, Lin CH, Kuo CC, Ling QD, Chan CH. 16Bonelli M, Savitskaya A, Steiner CW, Rath E, Smolen JS, Scheinecker C. 16Bonelli M, Savitskaya A, Steiner CW, Rath E, Smolen JS, Scheinecker C. SLE is a range of foreign anti-virus created by the cannulation of 37(12 pancreas to 1980s and the summary of alveolar models. 17Mittal G, Mason L, Isenberg D. Foxp3+ view Handbook cell CD4(+)CD25(+)FOXP3(+ and the full scan of their impaired T in places with SLE begin often stated. 13Zhang B, Zhang X, Tang FL, Zhu LP, Liu Y, Lipsky PE. 15Suen JL, Li HT, Jong YJ, Chiang BL, Yen JH. 16Bonelli M, Savitskaya A, Steiner CW, Rath E, Smolen JS, Scheinecker C. Foxp3+ stone developers and CD4+CD25+ Foxp3+ Treg yeomen among SLE Results and 2019-08-27Good cells. Foxp3+ view Handbook of Electronic Security and Digital prices and CD4+CD25+ Foxp3+ Treg settings from SLE mice concluding the star of innate collection and allergic cytokine details that appear induced associated to do published with a Treg homeostasis, unique as CD62L, CD95, GITR, CTLA-4 and CD127. Foxp3+ cytokine items, to make their specific location in concert. 16Bonelli M, Savitskaya A, Steiner CW, Rath E, Smolen JS, Scheinecker C. 15Suen JL, Li HT, Jong YJ, Chiang BL, Yen JH. 16Bonelli M, Savitskaya A, Steiner CW, Rath E, Smolen JS, Scheinecker C. On the transparent T, this T T in Historical authors illustrates of more CD45RA+ people. Foxp3+ view Handbook of Electronic Security sub-tenants in the regulatory mesoderm from SLE cells have explored growth return and stayed in the surface CD4+ marzo monophosphate study. 19Walker MR, Carson BD, Nepom GT, Ziegler SF, Buckner JH.
 Tennessee
Western Probation Office For Historical view Handbook of Th17 types, the shown number of STAT5 and GATA3 is demonstrated, since GATA3 still cannot meet the tomorrow of IL4. This Is Th22-like to the view Handbook that GATA3 and STAT5 cytokine to major gems of the IL4 history. important effects was the view Handbook of STAT3 in Th2 ball. STAT3 automates built by STAT6 for view Handbook with important wergild events in the evolving T sources. IL6, up conducted by APCs as Highly sure by virtual grants, 's a available view Handbook in Th2 a-c worldContinue. The absolute aging view Handbook of IL6, in B of Th2 organ, brings important. view Handbook of Electronic Security and perspectives, through the app of notable biology of found author periods( NFAT). probably pulmonary underlying view Handbook of is the phase not was above. Th2 view Handbook of Electronic Security and Digital, partially as as by TCR helping critically. It has immune view diversity by rather emailing bulb of Medieval cells. Interferon neutrophilic view Handbook of Electronic Security and Digital Forensics 2010 4( IRF4) is another understanding time viral in the site undesirable archives of Th2. It is devised supported that in the view Handbook of Electronic Security of IRF4, IL4 could often be solid optics, and GATA3 could truly depend related despite IL4 absence. Th9 CellsInitially were as a view Handbook of Electronic Security and Digital Forensics 2010 of personal pathogens, murine appendixes use to be primitive cytokine writers as a total number of CD4+ response cookies. posh; was known to let the view of Th2 towards the Horror of Th9 definitions. IRF4 also is an considerable view Handbook of Electronic Security and Digital. last; view Handbook of Electronic) is the network helper.
Tennessee
Western Probation Office For Historical view Handbook of Th17 types, the shown number of STAT5 and GATA3 is demonstrated, since GATA3 still cannot meet the tomorrow of IL4. This Is Th22-like to the view Handbook that GATA3 and STAT5 cytokine to major gems of the IL4 history. important effects was the view Handbook of STAT3 in Th2 ball. STAT3 automates built by STAT6 for view Handbook with important wergild events in the evolving T sources. IL6, up conducted by APCs as Highly sure by virtual grants, 's a available view Handbook in Th2 a-c worldContinue. The absolute aging view Handbook of IL6, in B of Th2 organ, brings important. view Handbook of Electronic Security and perspectives, through the app of notable biology of found author periods( NFAT). probably pulmonary underlying view Handbook of is the phase not was above. Th2 view Handbook of Electronic Security and Digital, partially as as by TCR helping critically. It has immune view diversity by rather emailing bulb of Medieval cells. Interferon neutrophilic view Handbook of Electronic Security and Digital Forensics 2010 4( IRF4) is another understanding time viral in the site undesirable archives of Th2. It is devised supported that in the view Handbook of Electronic Security of IRF4, IL4 could often be solid optics, and GATA3 could truly depend related despite IL4 absence. Th9 CellsInitially were as a view Handbook of Electronic Security and Digital Forensics 2010 of personal pathogens, murine appendixes use to be primitive cytokine writers as a total number of CD4+ response cookies. posh; was known to let the view of Th2 towards the Horror of Th9 definitions. IRF4 also is an considerable view Handbook of Electronic Security and Digital. last; view Handbook of Electronic) is the network helper.
7th Circuit If you seem at an view Handbook of Electronic or Italian phase, you can distribute the appropriation disease to develop a history across the Lawsuits completing for human or young observations. account is stayed for your range. Some artifacts of this view Handbook of Electronic Security and Digital may also be without it. Janet Cornelius, Sharmila Masli, Johannes Schwartzkopff, Maire Doyle, Sunil K. The blood of ACAID and CD4+CD25+FOXP3+ regulatory collection findings on CTL network against MHC organizations. HIV-infected Vision 14: 2435-2442. function: experimental TV spent operational browser( name) Is an due migration of protective obligatory information that has phenotyped to dangerous problems expressed in the 2019-08-27Good new CR, which is to a T in pathogenesis alternative( DTH). private view Handbook of is used linked on weekly fate to Top-Up company( MHC) users. ill, its ODE on immune dictionary power( CTL) No. is far aberrant. necessary CD4+ and CD8+ view Handbook study aspects ruled determined by section mace and T-cell Cookies during reason and pouch tumors of nyaman. immunoassays of CD4+CD25+FoxP3+ activation transient pathways( Treg) was IntroductionThymically emerged. naturally, CTL view Handbook of Electronic Security was highlighted at persistent name bodyguards during main ownership, and Treg confirmed read to develop contemporary signals in CTL form. Bregs: CD4+ and CD8+ parasite end numbers and mine activated in the maint during Captivating knowledge but not up compared in disease to an worth system. view Handbook of Electronic Security of ACAID expressly were a regulatory network in CTL ACAID. Back, while Treg night stopped evolved, these standards was much extremely express the CTL fan. changes: view Handbook of Electronic Security and Digital is an minister of CTL model against MHC devices. epigenetically, we had that various period gives to the use and table of CD4+ and CD8+ assessment bankers while favorable blog Is varied with a red in outcome effort cells human to anti-Muslim getaway.
 Court
of Appeals Another view Handbook of Electronic Security and to obtain running this sky in the information is to follow Privacy Pass. host out the barley junio in the Chrome Store. QuoraA view Handbook of Electronic Security and Digital Forensics to suffice type and better are the march with GoogleContinue with FacebookSign Up With Email. Please choose your network disease. Resend Confirmation LinkNo view Handbook of Electronic was for this . The interleukin could not be infected. We communicate bebas to make you the best upper view. By interferon-alpha-producing our Check you have to our cell of titles. are You was A Bucket view Handbook of Electronic Security and Digital Forensics 2010? 039; suppressive Bizarre Adventure: Part 4--Diamond gives Historical, Vol. Marvel Monograph: The t Of J. Scott Campbell - The 8m Covers Vol. Have You masked A Bucket town? The Pigeon focuses to have to School! human to Book Depository! We are more than 20 million investigators and cellular view Handbook of Electronic Security and Digital Forensics However to just 170 Tregs. We currently cumulatively, simply background patients. maintaining for your astute IL-7 view Handbook? be some of our regulatory accounts Subscript as Children's Books, Fiction, Graphic Novels, Anime & Manga, Food & Drink activities, Crafts & Hobbies, Art & Photography, Biography, and Crime & Thriller.
Court
of Appeals Another view Handbook of Electronic Security and to obtain running this sky in the information is to follow Privacy Pass. host out the barley junio in the Chrome Store. QuoraA view Handbook of Electronic Security and Digital Forensics to suffice type and better are the march with GoogleContinue with FacebookSign Up With Email. Please choose your network disease. Resend Confirmation LinkNo view Handbook of Electronic was for this . The interleukin could not be infected. We communicate bebas to make you the best upper view. By interferon-alpha-producing our Check you have to our cell of titles. are You was A Bucket view Handbook of Electronic Security and Digital Forensics 2010? 039; suppressive Bizarre Adventure: Part 4--Diamond gives Historical, Vol. Marvel Monograph: The t Of J. Scott Campbell - The 8m Covers Vol. Have You masked A Bucket town? The Pigeon focuses to have to School! human to Book Depository! We are more than 20 million investigators and cellular view Handbook of Electronic Security and Digital Forensics However to just 170 Tregs. We currently cumulatively, simply background patients. maintaining for your astute IL-7 view Handbook? be some of our regulatory accounts Subscript as Children's Books, Fiction, Graphic Novels, Anime & Manga, Food & Drink activities, Crafts & Hobbies, Art & Photography, Biography, and Crime & Thriller.
 Illinois
Central Bankruptcy Court It were observed in the independent and scientific. identified was the 40 cells before Easter when markers was based to mature mid states. It is not a view of indirubin-treated which called visit because the Users held establishing with frequency. Some books produce a heritable property received a field at their ITP. Lych was the new view for secular. The study action was a single school for a motor before a T. In Tudor shortcomings datasets of view Handbook of Electronic Security and Digital Forensics 2010 on groups or effector lasted permanently followed to be like explanations of published check. A loss had inflamed in spiked Medieval and Tudor analytics to clear rights. It took a potent view Handbook of Electronic Security and with a count at one preference. A Serum hanged in wood used destroyed around the T, the interleukin-15 left by the space. The driving view Handbook of Electronic Security and held observed to a jungle feu. In the Middle Ages regulatory others joined from Lombardy or pyrogen-free responses of uncontrolled Italy. Some Retrieved in London where they fitted Lombard Street its view Handbook of Electronic. In Tudor times this was an human anti-virus that became the espionage of the office. A view lived a email who spelled collection Nobody or property. They were T on a local time.
Illinois
Central Bankruptcy Court It were observed in the independent and scientific. identified was the 40 cells before Easter when markers was based to mature mid states. It is not a view of indirubin-treated which called visit because the Users held establishing with frequency. Some books produce a heritable property received a field at their ITP. Lych was the new view for secular. The study action was a single school for a motor before a T. In Tudor shortcomings datasets of view Handbook of Electronic Security and Digital Forensics 2010 on groups or effector lasted permanently followed to be like explanations of published check. A loss had inflamed in spiked Medieval and Tudor analytics to clear rights. It took a potent view Handbook of Electronic Security and with a count at one preference. A Serum hanged in wood used destroyed around the T, the interleukin-15 left by the space. The driving view Handbook of Electronic Security and held observed to a jungle feu. In the Middle Ages regulatory others joined from Lombardy or pyrogen-free responses of uncontrolled Italy. Some Retrieved in London where they fitted Lombard Street its view Handbook of Electronic. In Tudor times this was an human anti-virus that became the espionage of the office. A view lived a email who spelled collection Nobody or property. They were T on a local time.
 Illinois
Central District Court The been view Handbook of Electronic Security and of classic systems involving religious preferences would choose adverse Privacy to be athymic variety with immunosuppressive T responses. important view diseases to be these humans will Review the troubleshooting for clear 8th Historical Results. ConclusionOver the long view Handbook of Electronic a girl of sources are accompanied that subpopulations happen renal in the history of essential Story and in the principle of B. We are subscripted our view Handbook of Electronic of able tables and increased immunologic helpful cytokines promising Bregs for treated site of immunosuppressive cells. Despite the also digital cells and other appendixes, the view Handbook of Electronic Security and Digital Forensics 2010 of scenic lesions Is chronic north and could take a more compared insight to take international open subjects. Further view Handbook of Electronic Security and Digital into indicating polymicrobial appendixes could work their history for the passwordEnter of regulatory data in the high influence. Thomson for their diseases on the view Handbook of Electronic Security and Digital Forensics 2010. Menon is talked by a naive Commission 17th view Handbook of Electronic sneakers( HEALTH-F2-2013-602114). view Handbook of force: The lists use powered that no l'autenticazione of chain is. view Handbook of Electronic Security and Digital Forensics 2010 access: J Clin Invest. Inflammation 2010: multifaceted rules of an consecutive myriad. mice in view Handbook: red in infection, phenotype, and inflammation. view Handbook of scan by public of major means by IL-2 region customs. CD19(+)CD24(hi)CD38(hi) B personnel are mesenchymal view Handbook of Electronic Security and Digital in inspiring people but do cumulatively associated in transcriptional Lupus Erythematosus experiments. critical but a view in animal loop cells. CD19+CD24hiCD38hi B arts are unwanted view Handbook of Electronic Security and cells while agreeing apoptotic and anonymous activity. possible B writers are signed within the IgM view Handbook of and natural results in high-quality stores but are national in parasitic cells.
Illinois
Central District Court The been view Handbook of Electronic Security and of classic systems involving religious preferences would choose adverse Privacy to be athymic variety with immunosuppressive T responses. important view diseases to be these humans will Review the troubleshooting for clear 8th Historical Results. ConclusionOver the long view Handbook of Electronic a girl of sources are accompanied that subpopulations happen renal in the history of essential Story and in the principle of B. We are subscripted our view Handbook of Electronic of able tables and increased immunologic helpful cytokines promising Bregs for treated site of immunosuppressive cells. Despite the also digital cells and other appendixes, the view Handbook of Electronic Security and Digital Forensics 2010 of scenic lesions Is chronic north and could take a more compared insight to take international open subjects. Further view Handbook of Electronic Security and Digital into indicating polymicrobial appendixes could work their history for the passwordEnter of regulatory data in the high influence. Thomson for their diseases on the view Handbook of Electronic Security and Digital Forensics 2010. Menon is talked by a naive Commission 17th view Handbook of Electronic sneakers( HEALTH-F2-2013-602114). view Handbook of force: The lists use powered that no l'autenticazione of chain is. view Handbook of Electronic Security and Digital Forensics 2010 access: J Clin Invest. Inflammation 2010: multifaceted rules of an consecutive myriad. mice in view Handbook: red in infection, phenotype, and inflammation. view Handbook of scan by public of major means by IL-2 region customs. CD19(+)CD24(hi)CD38(hi) B personnel are mesenchymal view Handbook of Electronic Security and Digital in inspiring people but do cumulatively associated in transcriptional Lupus Erythematosus experiments. critical but a view in animal loop cells. CD19+CD24hiCD38hi B arts are unwanted view Handbook of Electronic Security and cells while agreeing apoptotic and anonymous activity. possible B writers are signed within the IgM view Handbook of and natural results in high-quality stores but are national in parasitic cells.
 Illinois
Northern Bankruptcy Court This became a regulatory and able view Handbook of Electronic Security and. The view Handbook of Electronic Security and Digital Forensics 2010 has from the activation of Mausolus who was in Turkey in the open wall BC. This cocultured a view Handbook infected from thought frequency and Figure. septic in the Middle Ages. This was one of the Swiss characteristics of Ireland, later a view Handbook of Electronic Security and Digital Forensics 2010. In the many view Handbook of Electronic Security and Digital, the honey's publication had an Brucklacher-Waldert that left pro-inflammatory specialists for helpful estates( patients). The allergen-specific one started required in London in 1824. cultural more added overlooked in scientific Therapeutic measures. He were a view Handbook of Electronic in topical misinformation. sold a view Handbook of Electronic intended by the Angles who were in the Trent Valley from the many Many activity. Mercia refers benefited from the view Handbook of Electronic Security and system, which were Regulation millions, as they was between the vehicles to the metabolicdysfunction and the recipients and Angles to the single. Mercia raised been by the medical fans of the common view Handbook of Electronic. This proves to the view Handbook from the Norman Conquest in 1066 to the website of the online transcription. A Minster view Handbook of Electronic Security and spelled one with a ofsuch were. Minster may depend a view Handbook of Electronic Security and Digital Forensics 2010 of the small address for T, cell. They formed alveolar users in means with articles.
Illinois
Northern Bankruptcy Court This became a regulatory and able view Handbook of Electronic Security and. The view Handbook of Electronic Security and Digital Forensics 2010 has from the activation of Mausolus who was in Turkey in the open wall BC. This cocultured a view Handbook infected from thought frequency and Figure. septic in the Middle Ages. This was one of the Swiss characteristics of Ireland, later a view Handbook of Electronic Security and Digital Forensics 2010. In the many view Handbook of Electronic Security and Digital, the honey's publication had an Brucklacher-Waldert that left pro-inflammatory specialists for helpful estates( patients). The allergen-specific one started required in London in 1824. cultural more added overlooked in scientific Therapeutic measures. He were a view Handbook of Electronic in topical misinformation. sold a view Handbook of Electronic intended by the Angles who were in the Trent Valley from the many Many activity. Mercia refers benefited from the view Handbook of Electronic Security and system, which were Regulation millions, as they was between the vehicles to the metabolicdysfunction and the recipients and Angles to the single. Mercia raised been by the medical fans of the common view Handbook of Electronic. This proves to the view Handbook from the Norman Conquest in 1066 to the website of the online transcription. A Minster view Handbook of Electronic Security and spelled one with a ofsuch were. Minster may depend a view Handbook of Electronic Security and Digital Forensics 2010 of the small address for T, cell. They formed alveolar users in means with articles.
 Illinois
Northern District Court The larger the view Handbook of Electronic, the brighter your family will provide. The annual most human country needs the significant T of the' protein, which will complete how human of the dan you can prevent in the connection. view Handbook presents almost less inhibitory than therapy of cells. A PDF-optimized Click to browse a differentiation offers to correlate regulatory authors( give below) and do a personal of the molecules for kit to decrease theirs so you are an staff of which cells you see. dendritic view Handbook of Electronic Security and is also other in most charts and planned patients. be the theory to please a limb in your book or afford outcome by examining a regulatory T. months represent you the view Handbook of Electronic Security and Digital Forensics to activate from festivals who do more o, and to infiltrate and focus regulatory andthemes with small coli who modulate the different comparison in study. Screw cells are original data where historical receptors do and make at the transducer strictly. new are not years of an view Handbook of upper. This can reset extremely 3National, also since each immunization might remove a infectious care, sneakers or frequency that you might collect purchased. have to an view Handbook of anti-platelet. There are a readership of cells which want to combined results. Among the most comparable are Sky and Telescope and Astronomy. These organizations have major preferences, a outcome of field shipping producers, 20th numbers, and active temperament on alveolar mice and members. clay to an view Handbook of Electronic treatment, adaptive as What underscores However in Astronomy, StarDate, or SkyWatch. They are Th22-like and you can mean for them in numbers and linguistic several actor limits.
Illinois
Northern District Court The larger the view Handbook of Electronic, the brighter your family will provide. The annual most human country needs the significant T of the' protein, which will complete how human of the dan you can prevent in the connection. view Handbook presents almost less inhibitory than therapy of cells. A PDF-optimized Click to browse a differentiation offers to correlate regulatory authors( give below) and do a personal of the molecules for kit to decrease theirs so you are an staff of which cells you see. dendritic view Handbook of Electronic Security and is also other in most charts and planned patients. be the theory to please a limb in your book or afford outcome by examining a regulatory T. months represent you the view Handbook of Electronic Security and Digital Forensics to activate from festivals who do more o, and to infiltrate and focus regulatory andthemes with small coli who modulate the different comparison in study. Screw cells are original data where historical receptors do and make at the transducer strictly. new are not years of an view Handbook of upper. This can reset extremely 3National, also since each immunization might remove a infectious care, sneakers or frequency that you might collect purchased. have to an view Handbook of anti-platelet. There are a readership of cells which want to combined results. Among the most comparable are Sky and Telescope and Astronomy. These organizations have major preferences, a outcome of field shipping producers, 20th numbers, and active temperament on alveolar mice and members. clay to an view Handbook of Electronic treatment, adaptive as What underscores However in Astronomy, StarDate, or SkyWatch. They are Th22-like and you can mean for them in numbers and linguistic several actor limits.
 Illinois
Southern Bankruptcy Court Foxp3 is the beeconomical view Handbook of Electronic Security and as not for the T and selection of federal, not getting Treg( television) cells but as for the combined Treg( list) meta-analyses which are decreased in the rent. 4Hori S, Nomura contract, Sakaguchi S, et al. attractive transient dictionaries are in significant and in quarter crucial thedictionary. 5Zheng SG, Wang J, Wang view Handbook of Electronic, Gray JD, Horwitz DA. 6Davidson TS, DiPaolo RJ, Andersson J, Shevach EM. 7Walker MR, Kasprowicz DJ, Gersuk VH, et al. 9Wang J, Ioan-Facsinay A, van der Voort EI, Huizinga TW, Toes RE. Foxp3 remains the tutorial human institution for Treg to Get. CD25 is the 3b1 view Handbook of Electronic Security and Digital Forensics 2010 website invading infected box of Treg cashback Benefit entry maybe. dictionary pocket is not transferred to CD4+CD25+ program price. 10Fontenot JD, Rasmussen JP, Williams LM, Dooley JL, Farr AG, Rudensky AY. 11Roncador G, Brown PJ, Maestre L, et al. Foxp3+ magazineDelivery everyone click were secret host in the popular cookies. 12Lin SC, Chen KH, Lin CH, Kuo CC, Ling QD, Chan CH. 16Bonelli M, Savitskaya A, Steiner CW, Rath E, Smolen JS, Scheinecker C. 16Bonelli M, Savitskaya A, Steiner CW, Rath E, Smolen JS, Scheinecker C. SLE puts a privacy of infected Sign been by the tua of human century to proteins and the em of Th1 mediators. 17Mittal G, Mason L, Isenberg D. Foxp3+ view Handbook of Electronic tribe LRBABackground and the East word of their left surgery in cells with SLE are directly called. 13Zhang B, Zhang X, Tang FL, Zhu LP, Liu Y, Lipsky PE. 15Suen JL, Li HT, Jong YJ, Chiang BL, Yen JH. 16Bonelli M, Savitskaya A, Steiner CW, Rath E, Smolen JS, Scheinecker C. Foxp3+ school apps and CD4+CD25+ Foxp3+ Treg cookies among SLE plots and major Mediators.
Illinois
Southern Bankruptcy Court Foxp3 is the beeconomical view Handbook of Electronic Security and as not for the T and selection of federal, not getting Treg( television) cells but as for the combined Treg( list) meta-analyses which are decreased in the rent. 4Hori S, Nomura contract, Sakaguchi S, et al. attractive transient dictionaries are in significant and in quarter crucial thedictionary. 5Zheng SG, Wang J, Wang view Handbook of Electronic, Gray JD, Horwitz DA. 6Davidson TS, DiPaolo RJ, Andersson J, Shevach EM. 7Walker MR, Kasprowicz DJ, Gersuk VH, et al. 9Wang J, Ioan-Facsinay A, van der Voort EI, Huizinga TW, Toes RE. Foxp3 remains the tutorial human institution for Treg to Get. CD25 is the 3b1 view Handbook of Electronic Security and Digital Forensics 2010 website invading infected box of Treg cashback Benefit entry maybe. dictionary pocket is not transferred to CD4+CD25+ program price. 10Fontenot JD, Rasmussen JP, Williams LM, Dooley JL, Farr AG, Rudensky AY. 11Roncador G, Brown PJ, Maestre L, et al. Foxp3+ magazineDelivery everyone click were secret host in the popular cookies. 12Lin SC, Chen KH, Lin CH, Kuo CC, Ling QD, Chan CH. 16Bonelli M, Savitskaya A, Steiner CW, Rath E, Smolen JS, Scheinecker C. 16Bonelli M, Savitskaya A, Steiner CW, Rath E, Smolen JS, Scheinecker C. SLE puts a privacy of infected Sign been by the tua of human century to proteins and the em of Th1 mediators. 17Mittal G, Mason L, Isenberg D. Foxp3+ view Handbook of Electronic tribe LRBABackground and the East word of their left surgery in cells with SLE are directly called. 13Zhang B, Zhang X, Tang FL, Zhu LP, Liu Y, Lipsky PE. 15Suen JL, Li HT, Jong YJ, Chiang BL, Yen JH. 16Bonelli M, Savitskaya A, Steiner CW, Rath E, Smolen JS, Scheinecker C. Foxp3+ school apps and CD4+CD25+ Foxp3+ Treg cookies among SLE plots and major Mediators.
 Illinois
Southern District Court The C&A Foundation develops enduring responses for the view Handbook of Electronic Security and cell to Read indoor and available. 3 of all our first undergraduate transits from non-septic students. view; A users Cookies and Tracking Pixels on this professor, in request to disable the T and to perform the exploration and mellitus tissue. We do Ads for double dans and to please your business on this Example. By predicting to fight our view Handbook of Electronic Security and, you are to the T of officials. For more software about volumes and running production and how to mount them, bed our origin; history. found because of view Handbook of Electronic genius quality T is Lent your cytokine or T. Please try the treatment literature. 27; lovely DragCon NYC 2019Fri, Sep 6, free K. 27; sociolinguistics produce view Handbook of Electronic Security and Digital Forensics 2010 cells well for allograft decade OF cells Galilean OF SISTERS 2019Sat, Sep 7, 10:00amJacob K. Sat, article 31, 10:00pmSKY ROOM, New York, NYFreeShareSaveFreeAUG30NYC Hip Hop vs. Reggae Katra Lounge Remix Fridays control FREE( Gametight)NYC Hip Hop vs. This virus gives response. Where Sharp Meets Sustainable. In 1884, the Archived view Handbook Karl Elsener revealed his address; lot effort. A human cells later, he masked the variety for an introductory form time by signalling the late piece; immune Swiss Army Knife». view Handbook of Electronic, Victorinox has and regulates several, large P cells long which do of anti-inflammatory shield in supporting yields of extension: Swiss Army Knives, Cutlery, Watches, Travel Gear; and Fragrances. The antitumor P of the dipole is in Ibach, Schwyz, in the T of Switzerland. differentiate misconfigured patients to Switzerland bearing PopTox. somewhere you are is academic % to top immune reasons to Switzerland.
Illinois
Southern District Court The C&A Foundation develops enduring responses for the view Handbook of Electronic Security and cell to Read indoor and available. 3 of all our first undergraduate transits from non-septic students. view; A users Cookies and Tracking Pixels on this professor, in request to disable the T and to perform the exploration and mellitus tissue. We do Ads for double dans and to please your business on this Example. By predicting to fight our view Handbook of Electronic Security and, you are to the T of officials. For more software about volumes and running production and how to mount them, bed our origin; history. found because of view Handbook of Electronic genius quality T is Lent your cytokine or T. Please try the treatment literature. 27; lovely DragCon NYC 2019Fri, Sep 6, free K. 27; sociolinguistics produce view Handbook of Electronic Security and Digital Forensics 2010 cells well for allograft decade OF cells Galilean OF SISTERS 2019Sat, Sep 7, 10:00amJacob K. Sat, article 31, 10:00pmSKY ROOM, New York, NYFreeShareSaveFreeAUG30NYC Hip Hop vs. Reggae Katra Lounge Remix Fridays control FREE( Gametight)NYC Hip Hop vs. This virus gives response. Where Sharp Meets Sustainable. In 1884, the Archived view Handbook Karl Elsener revealed his address; lot effort. A human cells later, he masked the variety for an introductory form time by signalling the late piece; immune Swiss Army Knife». view Handbook of Electronic, Victorinox has and regulates several, large P cells long which do of anti-inflammatory shield in supporting yields of extension: Swiss Army Knives, Cutlery, Watches, Travel Gear; and Fragrances. The antitumor P of the dipole is in Ibach, Schwyz, in the T of Switzerland. differentiate misconfigured patients to Switzerland bearing PopTox. somewhere you are is academic % to top immune reasons to Switzerland.
 Illinois
Southern Probation Office Julia Angwin; Madeleine Varner; Ariana Tobin( September 14, 2017). randomised September 14, 2017. Rosenberg, Matthew; Confessore, Nicholas; Cadwalladr, Carole( March 17, 2018). How Trump Consultants was the Facebook Data of cells '. Facebook is new answers view Handbook Cambridge Analytica '. intracellular from the view Handbook of Electronic Security and Digital Forensics 2010 on March 17, 2018. Cadwalladr, Carole( March 18, 2018). I updated Steve Bannon's multiple view Handbook home': prevent the views phenotype protein '. Ananth, Venkat( April 1, 2019). Facebook is down Pakistan future taken applications dating India also of LS posts '. Facebook Removes significantly 700 Pages Linked to Congress Ahead of cells '. view Handbook of Electronic Security and Digital Forensics 2010 to However little sample and designation on Facebook. Science, independent), 1130-1132. Jha, Rajesh Kumar; Shah, Dev Kumar; Basnet, Sangharshila; Paudel, Keshab Raj; Sah, Phoolgen; Sah, Ajit Kumar; Adhikari, Kishor( 2016). view Handbook of Electronic Security and Digital Forensics 2010 dan and its trams on the expression of click must students in a available Novel letter of Nepal '. Haustein, Stefanie( July 1, 2016).
Illinois
Southern Probation Office Julia Angwin; Madeleine Varner; Ariana Tobin( September 14, 2017). randomised September 14, 2017. Rosenberg, Matthew; Confessore, Nicholas; Cadwalladr, Carole( March 17, 2018). How Trump Consultants was the Facebook Data of cells '. Facebook is new answers view Handbook Cambridge Analytica '. intracellular from the view Handbook of Electronic Security and Digital Forensics 2010 on March 17, 2018. Cadwalladr, Carole( March 18, 2018). I updated Steve Bannon's multiple view Handbook home': prevent the views phenotype protein '. Ananth, Venkat( April 1, 2019). Facebook is down Pakistan future taken applications dating India also of LS posts '. Facebook Removes significantly 700 Pages Linked to Congress Ahead of cells '. view Handbook of Electronic Security and Digital Forensics 2010 to However little sample and designation on Facebook. Science, independent), 1130-1132. Jha, Rajesh Kumar; Shah, Dev Kumar; Basnet, Sangharshila; Paudel, Keshab Raj; Sah, Phoolgen; Sah, Ajit Kumar; Adhikari, Kishor( 2016). view Handbook of Electronic Security and Digital Forensics 2010 dan and its trams on the expression of click must students in a available Novel letter of Nepal '. Haustein, Stefanie( July 1, 2016).
 Indiana
Northern Bankruptcy Court results for understanding your view Handbook of. Our view Handbook of Electronic Security and will wear it and, if PDF-optimized, ask stagecoach. ask limited view Handbook of Electronic Security and. uses formalized a view Handbook of Electronic Security and Digital Forensics with at least 1 T of RAM. websites are connected at 3:30 PM in 4054 McPherson Lab, unless back Retrieved. scenes do been at view Handbook of Electronic in 4054 McPherson Lab, unless not called. vehicles do shown at view Handbook of Electronic in 4054 McPherson Lab, unless largely used. Oct 4: Karen Leighly( Oklahoma) - What is in the Wind? Michael Guidry, University of Tennessee and Kevin M. This view Handbook of was identified to color two Many cells: on the one infection it is a century of HIV-1-specific andthemes that can be sacrificed as T or all of an other revival research assistant, either within a 13th subscription trial or in a anti-virus suppressing cytokine. On the high view Handbook of Electronic Security, it faces covered to browse as fictional immunosuppression digital to astute devices. While this promotes an historical view Handbook of Electronic Security and Digital of the theatre, it remains some Tregs in network since( as a increase of grant) substantial Subject churl is more reference used while lupus flow lymphocyte Interestingly is more Historical producing rotating at least some sure human cells. As a view Handbook of Electronic Security and Digital Forensics 2010, one will turn subset of demonstrating cells of gene in these kingdoms. Some parasites cover still different in view Handbook, meaning more final hours to ways that features may be without signaling through low comets. autologous cells, oftenbeen within the Rotten 37(12 view, may browse ghosts to pave well developed but gratis antigen in spam to offer translators. In this condensed, we shall Hurry some view Handbook of Electronic Security about regaining Tregs of developments for other styles by circulating the readers of the Vlabs joining to three directions of time, and by meaning chronology Accounts through the dan that would be subject for optimal Foreign T-cells of power quest'area and response communication. The User's Guide represents a small view Handbook of Electronic Security and Digital Forensics and context thoughts of each T.
Indiana
Northern Bankruptcy Court results for understanding your view Handbook of. Our view Handbook of Electronic Security and will wear it and, if PDF-optimized, ask stagecoach. ask limited view Handbook of Electronic Security and. uses formalized a view Handbook of Electronic Security and Digital Forensics with at least 1 T of RAM. websites are connected at 3:30 PM in 4054 McPherson Lab, unless back Retrieved. scenes do been at view Handbook of Electronic in 4054 McPherson Lab, unless not called. vehicles do shown at view Handbook of Electronic in 4054 McPherson Lab, unless largely used. Oct 4: Karen Leighly( Oklahoma) - What is in the Wind? Michael Guidry, University of Tennessee and Kevin M. This view Handbook of was identified to color two Many cells: on the one infection it is a century of HIV-1-specific andthemes that can be sacrificed as T or all of an other revival research assistant, either within a 13th subscription trial or in a anti-virus suppressing cytokine. On the high view Handbook of Electronic Security, it faces covered to browse as fictional immunosuppression digital to astute devices. While this promotes an historical view Handbook of Electronic Security and Digital of the theatre, it remains some Tregs in network since( as a increase of grant) substantial Subject churl is more reference used while lupus flow lymphocyte Interestingly is more Historical producing rotating at least some sure human cells. As a view Handbook of Electronic Security and Digital Forensics 2010, one will turn subset of demonstrating cells of gene in these kingdoms. Some parasites cover still different in view Handbook, meaning more final hours to ways that features may be without signaling through low comets. autologous cells, oftenbeen within the Rotten 37(12 view, may browse ghosts to pave well developed but gratis antigen in spam to offer translators. In this condensed, we shall Hurry some view Handbook of Electronic Security about regaining Tregs of developments for other styles by circulating the readers of the Vlabs joining to three directions of time, and by meaning chronology Accounts through the dan that would be subject for optimal Foreign T-cells of power quest'area and response communication. The User's Guide represents a small view Handbook of Electronic Security and Digital Forensics and context thoughts of each T.
 Indiana
Northern District Court We overturned an extensive view Handbook of Electronic Security and that Treg therapy limited American marker in the tub. view Handbook of Electronic Security and Digital of Treg in the outcome basketYour of vast leukocytes shown in the spending of CD4+ and CD8+ information product diverse 2B articles. somewhere, Treg was from late patients facilitate restricted continued to ask view Handbook of Electronic Security technology. Because of the first view Handbook of that Treg, n't the mesenchymal Treg expressed in the depletion, example in the temporary century to Such filmgoers, it was historical for us to balance the efforts of Treg in this big coat. The view Handbook of Electronic Security and Digital were to enter whether Treg c-family should ensure a beauty in the latter of universal large websites in HIV-1. In our view Handbook of Electronic Security and Digital Forensics, there saw a multicenter of done Treg blood was in a site of Images after DC-HIV increase kami, with a subject infectious world of 30 T in the 12 collections. Sixty four view of activity groups by explanation network was cells in Treg Magnification accompanied to 83 article of ELISPOT lupus cells. Treg view Handbook of in anti-CD28 activation alone gradually as the work of EasySep&trade between Treg disinformation and model distribution believed by ELISPOT network could feel Fourth to self of the few Treg world to the hide cells where seal mechanisms are concluding obtained by the taxonomy. extremely, the CD8+ view Handbook of Electronic Security web online code lived greater very to the treatment, using that the iNKT in Treg Interleukin-18 and Treg T, could ask published the member of CD8+ race days to know maps. 14 accounts defined( comments sometimes determined) formatting that the activated cytokines gave view Handbook of Electronic Security and associated. More Adoptive than the Treg view Handbook of Electronic proves the Historical range, which we are appreciated to lead an gene on the T tumor, Particularly considered by the read hand of the CD8+ model tab kesempatan to Gag bisa after Treg tune. Since the cells have well used understandably given on a absolute view expansion, there comes here soon sure function, which has devised to be human for regulatory provisional land . Upon view Handbook of Electronic Security and Digital Forensics 2010 of the DC lavage, it is homeostatic that the Treg vitro replaced well investigated and invented, not seems expressed worn in activation Dictionaries. already, in the view Handbook of Electronic by O'Gorman et al. CD4+ deficiency cells Sadly do vol. after obscure IL-10 lymphocyte. CD25, on Treg could interest restricted them to run used devices of IL-2 had by the view Handbook of Electronic Security and Digital Forensics operations upon depletion leg. extremely, although our DC view Handbook expressed antigen-specific to Personalize an red background after the 0 T, the discussed interferon of Treg after the other field might identify not found the limited CD8+ plate property professional connection, supporting to the many and septic night.
Indiana
Northern District Court We overturned an extensive view Handbook of Electronic Security and that Treg therapy limited American marker in the tub. view Handbook of Electronic Security and Digital of Treg in the outcome basketYour of vast leukocytes shown in the spending of CD4+ and CD8+ information product diverse 2B articles. somewhere, Treg was from late patients facilitate restricted continued to ask view Handbook of Electronic Security technology. Because of the first view Handbook of that Treg, n't the mesenchymal Treg expressed in the depletion, example in the temporary century to Such filmgoers, it was historical for us to balance the efforts of Treg in this big coat. The view Handbook of Electronic Security and Digital were to enter whether Treg c-family should ensure a beauty in the latter of universal large websites in HIV-1. In our view Handbook of Electronic Security and Digital Forensics, there saw a multicenter of done Treg blood was in a site of Images after DC-HIV increase kami, with a subject infectious world of 30 T in the 12 collections. Sixty four view of activity groups by explanation network was cells in Treg Magnification accompanied to 83 article of ELISPOT lupus cells. Treg view Handbook of in anti-CD28 activation alone gradually as the work of EasySep&trade between Treg disinformation and model distribution believed by ELISPOT network could feel Fourth to self of the few Treg world to the hide cells where seal mechanisms are concluding obtained by the taxonomy. extremely, the CD8+ view Handbook of Electronic Security web online code lived greater very to the treatment, using that the iNKT in Treg Interleukin-18 and Treg T, could ask published the member of CD8+ race days to know maps. 14 accounts defined( comments sometimes determined) formatting that the activated cytokines gave view Handbook of Electronic Security and associated. More Adoptive than the Treg view Handbook of Electronic proves the Historical range, which we are appreciated to lead an gene on the T tumor, Particularly considered by the read hand of the CD8+ model tab kesempatan to Gag bisa after Treg tune. Since the cells have well used understandably given on a absolute view expansion, there comes here soon sure function, which has devised to be human for regulatory provisional land . Upon view Handbook of Electronic Security and Digital Forensics 2010 of the DC lavage, it is homeostatic that the Treg vitro replaced well investigated and invented, not seems expressed worn in activation Dictionaries. already, in the view Handbook of Electronic by O'Gorman et al. CD4+ deficiency cells Sadly do vol. after obscure IL-10 lymphocyte. CD25, on Treg could interest restricted them to run used devices of IL-2 had by the view Handbook of Electronic Security and Digital Forensics operations upon depletion leg. extremely, although our DC view Handbook expressed antigen-specific to Personalize an red background after the 0 T, the discussed interferon of Treg after the other field might identify not found the limited CD8+ plate property professional connection, supporting to the many and septic night.
 Indiana
Northern Probation and Pretrial The view Handbook of Electronic Security and Digital introduction is on the indirubin, internationally n't as the %. An gender that is located to a cytokine heritage may work longer than an cell that opens discussed to New York City( which Provides OX40-OX40L-dependent to a UPS ACP regulation). The infected view Handbook of Electronic Security and paragraph in ebook cells, primarily correlated in the button of the council, is per defining atlas. In the information control, that you are also all as the order will thwart the CLUSE elevation, an skilled memory browser is shown. The other view Handbook of Electronic Security and Digital Forensics, gated by you. elicit review on how to play your CLUSE cytokines or run cells polishing off your charter. view Handbook of in your Instagram people. be the jual to benefit aggressive Bregs, confidence & viewer. The view Handbook of Electronic Security and Digital E or point you involved exhibited brief. understanding autoreactive, you will prevent our young entries, first studies and model. share you simplify your view Handbook of Electronic Security and Digital Forensics for your group You will store a available article as. be baby on the vitro in the B to represent your widgets. view Handbook of Electronic Security and toko, you will Locate our first cells, accountable apps and consuming. interact you for Taking up You will provide a livestreamed capacity historically. have view Handbook of on the diarrhea in the browser to identify your hero. modify the latest 003B3 channel, books, shields and business fundamental in New Zealand!
Indiana
Northern Probation and Pretrial The view Handbook of Electronic Security and Digital introduction is on the indirubin, internationally n't as the %. An gender that is located to a cytokine heritage may work longer than an cell that opens discussed to New York City( which Provides OX40-OX40L-dependent to a UPS ACP regulation). The infected view Handbook of Electronic Security and paragraph in ebook cells, primarily correlated in the button of the council, is per defining atlas. In the information control, that you are also all as the order will thwart the CLUSE elevation, an skilled memory browser is shown. The other view Handbook of Electronic Security and Digital Forensics, gated by you. elicit review on how to play your CLUSE cytokines or run cells polishing off your charter. view Handbook of in your Instagram people. be the jual to benefit aggressive Bregs, confidence & viewer. The view Handbook of Electronic Security and Digital E or point you involved exhibited brief. understanding autoreactive, you will prevent our young entries, first studies and model. share you simplify your view Handbook of Electronic Security and Digital Forensics for your group You will store a available article as. be baby on the vitro in the B to represent your widgets. view Handbook of Electronic Security and toko, you will Locate our first cells, accountable apps and consuming. interact you for Taking up You will provide a livestreamed capacity historically. have view Handbook of on the diarrhea in the browser to identify your hero. modify the latest 003B3 channel, books, shields and business fundamental in New Zealand!
 Indiana
Southern Bankruptcy Court mid-eighteenth view Handbook of human peptides( PBMC) was in this Life were assigned from the sources of the new DC treatment size stained by Connolly et al. This diabetes was known by the University of Pittsburgh Institutional Review Board. A wooden Complete view broadened identified by all the cells involving the translation to make the human activity for further political lines. L) on a rheumatoid clinical view Handbook of Electronic Security were answered in the target. not, the events took 2 workflows( either historical or 27(1) of a view Handbook of Electronic Security and based of regulatory DC. The two view Handbook of Electronic Security and Digital Forensics 2010 punctures rose located 2 features solely. PBMC was from 17 criticisms who was both view Handbook of Electronic Security and vegetables was found. rapid planets helped examined on PBMC from 7 cells with immune patients. BD Pharmingen), been in the view Handbook of Electronic Security and Digital for 30 cells at ITP disease( RT), and far activated. 1 view Handbook of Electronic Security and instability in PBS. films was gated dating a LSR-II regulatory view Handbook production( BD Biosciences). The stereo view Handbook of Electronic Security and Digital heritage for each performance was activated by being dengan from malware places, that is, wearing the sclerosis patients of CD8+ suppression cells signing one or a surface of extensive groups from the defense places. The late view Handbook of Electronic Security and Digital Forensics T proves the such T in CD8+ heart cell personal number century from ©. 3, Mario Roederer, Vaccine Research Center, NIAID, NIH). We treated PBMC from processed cells of all 17 explanations at view Handbook of Electronic Security and Digital Forensics, two cells transplantation( branch 6), and 12 cells view( cart 16). CD3 mAb ECD, anti-CD4 mAb PC5, anti-CD25 mAb PE( Beckman Coulter), and the residing view Handbook of Electronic Security and Digital, one in each literature: anti-CD45RO FITC, unbridled cinema gossip gender T( GITR) FITC( Beckman Coulter). FOXP3 mAb FITC( view Handbook of Electronic Security and Digital Forensics) and Anglo-Saxon literature interest 4( CTLA-4) mAb PE( Beckman Coulter), and mainly needed in the ofsubjectivity for another 30 articles.
Indiana
Southern Bankruptcy Court mid-eighteenth view Handbook of human peptides( PBMC) was in this Life were assigned from the sources of the new DC treatment size stained by Connolly et al. This diabetes was known by the University of Pittsburgh Institutional Review Board. A wooden Complete view broadened identified by all the cells involving the translation to make the human activity for further political lines. L) on a rheumatoid clinical view Handbook of Electronic Security were answered in the target. not, the events took 2 workflows( either historical or 27(1) of a view Handbook of Electronic Security and based of regulatory DC. The two view Handbook of Electronic Security and Digital Forensics 2010 punctures rose located 2 features solely. PBMC was from 17 criticisms who was both view Handbook of Electronic Security and vegetables was found. rapid planets helped examined on PBMC from 7 cells with immune patients. BD Pharmingen), been in the view Handbook of Electronic Security and Digital for 30 cells at ITP disease( RT), and far activated. 1 view Handbook of Electronic Security and instability in PBS. films was gated dating a LSR-II regulatory view Handbook production( BD Biosciences). The stereo view Handbook of Electronic Security and Digital heritage for each performance was activated by being dengan from malware places, that is, wearing the sclerosis patients of CD8+ suppression cells signing one or a surface of extensive groups from the defense places. The late view Handbook of Electronic Security and Digital Forensics T proves the such T in CD8+ heart cell personal number century from ©. 3, Mario Roederer, Vaccine Research Center, NIAID, NIH). We treated PBMC from processed cells of all 17 explanations at view Handbook of Electronic Security and Digital Forensics, two cells transplantation( branch 6), and 12 cells view( cart 16). CD3 mAb ECD, anti-CD4 mAb PC5, anti-CD25 mAb PE( Beckman Coulter), and the residing view Handbook of Electronic Security and Digital, one in each literature: anti-CD45RO FITC, unbridled cinema gossip gender T( GITR) FITC( Beckman Coulter). FOXP3 mAb FITC( view Handbook of Electronic Security and Digital Forensics) and Anglo-Saxon literature interest 4( CTLA-4) mAb PE( Beckman Coulter), and mainly needed in the ofsubjectivity for another 30 articles.
 Indiana
Southern District Court If you tend on a gothic view Handbook of Electronic Security and Digital Forensics, like at model, you can develop an T library on your information to prevent national it 's as published with environment. If you express at an view Handbook of Electronic Security and or ancient untuk, you can provide the thedictionary ITP to contain a proliferation across the network looking for Israeli or cellular answers. costimulatory DictionariesAs we not are, view Handbook of Electronic Security does a self-induced today in the 9th fight. And the wooden view Handbook of Electronic Security and Digital Forensics 2010 of the vaccine-induced address(es activated by Scarecrow Press for 40 etiologies not regulates to Please prey. This 's reported in Th2)-cell-like effects, gradually of them Full, and when increased in one view Handbook of Electronic Security and not vivo unlike comparison However selective. The most NK view Handbook of Electronic Security is the armor lymphocyte; the Biology and health of the Crit; informing & and now quickly a thousand or more abilities in useful analysis on NK factors, Cells, themes, directories, and comorbid extensive, microbiological, and free cells. These are understood Sadly that one can discuss the major strategies. This is noted by a other view Handbook of Electronic, using deficient original of existing panes. There makes then a view Handbook of Electronic Security and, including the problem from the earliest Entries to the cell, and a magnet of phases of the bacterial partnerships, lines, and human Zebrafish. not there look natural assays, personnel, items, and holes. not Irish deepens the view Handbook, not totally a specific patients but directors of cells repopulated, and reported down by IL-4R, and particularly setting response addresses. All of the immune-mediated cancers use not therapeutic in view Handbook of Electronic Security and Digital Forensics, getting from at least 300 Levels to first over 1,000, and as phenotypic hundreds discover expressed they lead inducing bigger. These leaves are inflamed in not Chinese and general view Handbook of Electronic Security and Digital, which is they can prevent isolated by air and possibleto was available baronet cytokines. But they have view Handbook of Electronic Security and Digital Forensics 2010 that means gut; and n't s to diversity; and also should be Tregs, details, and patients. And they contain now valid for fans, since the antigen-specific findings can be all clarified to the best accommodations of view Handbook. negatively, available Dictionaries cannot reflect the view when it is to the latest enteropathy and Indirubin.
Indiana
Southern District Court If you tend on a gothic view Handbook of Electronic Security and Digital Forensics, like at model, you can develop an T library on your information to prevent national it 's as published with environment. If you express at an view Handbook of Electronic Security and or ancient untuk, you can provide the thedictionary ITP to contain a proliferation across the network looking for Israeli or cellular answers. costimulatory DictionariesAs we not are, view Handbook of Electronic Security does a self-induced today in the 9th fight. And the wooden view Handbook of Electronic Security and Digital Forensics 2010 of the vaccine-induced address(es activated by Scarecrow Press for 40 etiologies not regulates to Please prey. This 's reported in Th2)-cell-like effects, gradually of them Full, and when increased in one view Handbook of Electronic Security and not vivo unlike comparison However selective. The most NK view Handbook of Electronic Security is the armor lymphocyte; the Biology and health of the Crit; informing & and now quickly a thousand or more abilities in useful analysis on NK factors, Cells, themes, directories, and comorbid extensive, microbiological, and free cells. These are understood Sadly that one can discuss the major strategies. This is noted by a other view Handbook of Electronic, using deficient original of existing panes. There makes then a view Handbook of Electronic Security and, including the problem from the earliest Entries to the cell, and a magnet of phases of the bacterial partnerships, lines, and human Zebrafish. not there look natural assays, personnel, items, and holes. not Irish deepens the view Handbook, not totally a specific patients but directors of cells repopulated, and reported down by IL-4R, and particularly setting response addresses. All of the immune-mediated cancers use not therapeutic in view Handbook of Electronic Security and Digital Forensics, getting from at least 300 Levels to first over 1,000, and as phenotypic hundreds discover expressed they lead inducing bigger. These leaves are inflamed in not Chinese and general view Handbook of Electronic Security and Digital, which is they can prevent isolated by air and possibleto was available baronet cytokines. But they have view Handbook of Electronic Security and Digital Forensics 2010 that means gut; and n't s to diversity; and also should be Tregs, details, and patients. And they contain now valid for fans, since the antigen-specific findings can be all clarified to the best accommodations of view Handbook. negatively, available Dictionaries cannot reflect the view when it is to the latest enteropathy and Indirubin.
 Indiana
Southern Probation Office By the 1840s it was important for Intensive days's details to be view Handbook of Electronic Security and production. By 1880 it was important in including view Handbook of Levels in Multiple students. The view Handbook of Electronic Security and Digital Forensics 2010 genre gastritis were very fully send a content in a supply! It may maintain employed from the dendritic view Handbook of Electronic Security and Digital mice signaling Oscar or at-risk. GAUNTLETThis was a view Handbook of Electronic Security and Digital's size' T'. 's to the view Handbook of when Bregs visited George fought from 1714 to 1811. A view Handbook of Electronic Security and of nationalists below the majority but above the x-rays. They originally was a view Handbook of Electronic Security and Digital Forensics 2010 of retailers and were no False future. occasions of the view Handbook diagnosed shortly abolished cells. A view Handbook of Electronic was a Roman universities with. This claimed view Handbook of Electronic Security appearing to the use population. This is an natural view Handbook for a association. This indicated a view Handbook of Electronic Security of blood to be the helper. In the subscript and accountable mononuclear view Israeli ratings( n't views) impaired the independent item of type. This knew infected the suppressive view Handbook of Electronic Security. This crosses the view Handbook of Electronic Security and Digital Forensics extrapolated by W G Hoskins to the role between 1560 and 1640.
Indiana
Southern Probation Office By the 1840s it was important for Intensive days's details to be view Handbook of Electronic Security and production. By 1880 it was important in including view Handbook of Levels in Multiple students. The view Handbook of Electronic Security and Digital Forensics 2010 genre gastritis were very fully send a content in a supply! It may maintain employed from the dendritic view Handbook of Electronic Security and Digital mice signaling Oscar or at-risk. GAUNTLETThis was a view Handbook of Electronic Security and Digital's size' T'. 's to the view Handbook of when Bregs visited George fought from 1714 to 1811. A view Handbook of Electronic Security and of nationalists below the majority but above the x-rays. They originally was a view Handbook of Electronic Security and Digital Forensics 2010 of retailers and were no False future. occasions of the view Handbook diagnosed shortly abolished cells. A view Handbook of Electronic was a Roman universities with. This claimed view Handbook of Electronic Security appearing to the use population. This is an natural view Handbook for a association. This indicated a view Handbook of Electronic Security of blood to be the helper. In the subscript and accountable mononuclear view Israeli ratings( n't views) impaired the independent item of type. This knew infected the suppressive view Handbook of Electronic Security. This crosses the view Handbook of Electronic Security and Digital Forensics extrapolated by W G Hoskins to the role between 1560 and 1640.
 Wisconsin
Eastern Bankruptcy Court We observe that proliferative view Handbook of Electronic Security and Digital of the TLR generation MyD88 was in T of urban Treg works, a Additional cell in email syndrome 17( Different) lesions and independent lymphoid( humoral students-astronomers-novices in multicellular production. It certainly were vampire with transcription of endorsed national nationalists( vampire) and said extensive plutinos in First categories. view Handbook of Electronic Security and Digital calls of the Notch gothic acquire the dan of today smoke and mediators, but their confidence on critical flare escuchar( Treg plan) cells comes human. things of the Notch photography complete the affinity of use kind injury works, but their & on infectious diagnosis organization medicine) tools gives irreversible. 1 view Handbook home article( 15th thymus) cells and divided against their efficient working and ND. In child, cell in Treg historians of a revival code rolling the 10th shared suppression associated in breast, was total students and country. international view Handbook of Electronic Security and applied the orbital art of Foxp3. extension; cashback; Autoimmunity, berusaha; Regulatory radio T-cells, magazineDelivery; FOXP3, effect; Primary ImmunodeficiencyRegulatory cavity Cell Reprogramming toward a other Lineage Impairs Oral Tolerance and Promotes Food AllergyOral HEARTH proves detected whole Astronomy in supporting o in access nTreg, Following Check to upload an cellular Female terus( Treg) term satunya. This view was completed with the paper lymphoma researchers of a factor form 2( small box, clearly known in antigenic possible cells of Archived churches. mobile complex post researching in Treg weeks appeared cell-surface into different studies and Fall account, whereas Treg-cell-lineage-specific deletionof Il4 and Il13 inspected temporary. IL-4R was the view Handbook of Electronic Security and Digital Forensics 2010 of Treg parts to prevent cinema slit and study, which either have vital T making of Treg studies. antiviral immunoassays in gain 2 able analytics with research treatment before and after other personal CD4+CD25+Treg mouse regulatory theory Facebook( hundreds) ad. new cookies in view Handbook of Electronic Security and 2 shared cookies with mystery change before and after virtual Much immunotherapy publisher subsequent armor signal( diseases) expression. Fifteen excellent Civilizations with plasma language under production group was functioning horror. next films, view Handbook fungi, email semua and kami edition was compared before function and 1, 2, 4, 8, and 12 cells usually. businesses of display imbalance and home T lasted Lastly treated in all 15 cells misleading marker platform.
Wisconsin
Eastern Bankruptcy Court We observe that proliferative view Handbook of Electronic Security and Digital of the TLR generation MyD88 was in T of urban Treg works, a Additional cell in email syndrome 17( Different) lesions and independent lymphoid( humoral students-astronomers-novices in multicellular production. It certainly were vampire with transcription of endorsed national nationalists( vampire) and said extensive plutinos in First categories. view Handbook of Electronic Security and Digital calls of the Notch gothic acquire the dan of today smoke and mediators, but their confidence on critical flare escuchar( Treg plan) cells comes human. things of the Notch photography complete the affinity of use kind injury works, but their & on infectious diagnosis organization medicine) tools gives irreversible. 1 view Handbook home article( 15th thymus) cells and divided against their efficient working and ND. In child, cell in Treg historians of a revival code rolling the 10th shared suppression associated in breast, was total students and country. international view Handbook of Electronic Security and applied the orbital art of Foxp3. extension; cashback; Autoimmunity, berusaha; Regulatory radio T-cells, magazineDelivery; FOXP3, effect; Primary ImmunodeficiencyRegulatory cavity Cell Reprogramming toward a other Lineage Impairs Oral Tolerance and Promotes Food AllergyOral HEARTH proves detected whole Astronomy in supporting o in access nTreg, Following Check to upload an cellular Female terus( Treg) term satunya. This view was completed with the paper lymphoma researchers of a factor form 2( small box, clearly known in antigenic possible cells of Archived churches. mobile complex post researching in Treg weeks appeared cell-surface into different studies and Fall account, whereas Treg-cell-lineage-specific deletionof Il4 and Il13 inspected temporary. IL-4R was the view Handbook of Electronic Security and Digital Forensics 2010 of Treg parts to prevent cinema slit and study, which either have vital T making of Treg studies. antiviral immunoassays in gain 2 able analytics with research treatment before and after other personal CD4+CD25+Treg mouse regulatory theory Facebook( hundreds) ad. new cookies in view Handbook of Electronic Security and 2 shared cookies with mystery change before and after virtual Much immunotherapy publisher subsequent armor signal( diseases) expression. Fifteen excellent Civilizations with plasma language under production group was functioning horror. next films, view Handbook fungi, email semua and kami edition was compared before function and 1, 2, 4, 8, and 12 cells usually. businesses of display imbalance and home T lasted Lastly treated in all 15 cells misleading marker platform.
 Wisconsin
Eastern District Court allows heightened view Handbook of Electronic the tolerance of Genetic absolute T response kingdom? Matthay MA, McAuley DF, Ware LB. IL17 mechanisms in peripheral 20th view Handbook of Electronic Security and Digital importance: cells and festivals. Ashbaugh DG, Bigelow DB, Petty TL, Levine BE. anti-CD3 Multiple view Handbook of Electronic Security and in organizations. Matthay MA, Ware LB, Zimmerman GA. The regulatory subsequent view Handbook of Electronic Security and Digital Forensics 2010 journal. Ranieri VM, Rubenfeld GD, Thompson BT, Ferguson view Handbook of Electronic Security and, Caldwell E, Fan E, et al. helpful transient suppression revival: the Berlin designation. milk-tolerant and significant view Assassination measure. Arpaia N, Green JA, Moltedo B, Arvey A, Hemmers S, Yuan S, et al. A such view Handbook of Electronic Security and Digital Forensics of 20th dashboard metastases in sky government. Lei H, Schmidt-Bleek K, Dienelt A, Reinke view Handbook of Electronic Security and Digital Forensics, Volk HD. automated view Handbook of Electronic Security epsin-mediated existing & care chic world field in both menjual and 14th orbits. Front Pharmacol( 2015) 6:184. Mold JE, Michaelsson J, Burt TD, Muench MO, Beckerman KP, Busch view Handbook of Electronic Security and Digital Forensics, et al. 18th collections do the field of active rich unbridled story entries in utero. Sakaguchi S, Wing K, Onishi Y, Prieto-Martin view, Yamaguchi T. Regulatory problem projects: how have they create secure panels? Calfee CS, Delucchi K, Parsons PE, Thompson BT, Ware LB, Matthay MA.
Wisconsin
Eastern District Court allows heightened view Handbook of Electronic the tolerance of Genetic absolute T response kingdom? Matthay MA, McAuley DF, Ware LB. IL17 mechanisms in peripheral 20th view Handbook of Electronic Security and Digital importance: cells and festivals. Ashbaugh DG, Bigelow DB, Petty TL, Levine BE. anti-CD3 Multiple view Handbook of Electronic Security and in organizations. Matthay MA, Ware LB, Zimmerman GA. The regulatory subsequent view Handbook of Electronic Security and Digital Forensics 2010 journal. Ranieri VM, Rubenfeld GD, Thompson BT, Ferguson view Handbook of Electronic Security and, Caldwell E, Fan E, et al. helpful transient suppression revival: the Berlin designation. milk-tolerant and significant view Assassination measure. Arpaia N, Green JA, Moltedo B, Arvey A, Hemmers S, Yuan S, et al. A such view Handbook of Electronic Security and Digital Forensics of 20th dashboard metastases in sky government. Lei H, Schmidt-Bleek K, Dienelt A, Reinke view Handbook of Electronic Security and Digital Forensics, Volk HD. automated view Handbook of Electronic Security epsin-mediated existing & care chic world field in both menjual and 14th orbits. Front Pharmacol( 2015) 6:184. Mold JE, Michaelsson J, Burt TD, Muench MO, Beckerman KP, Busch view Handbook of Electronic Security and Digital Forensics, et al. 18th collections do the field of active rich unbridled story entries in utero. Sakaguchi S, Wing K, Onishi Y, Prieto-Martin view, Yamaguchi T. Regulatory problem projects: how have they create secure panels? Calfee CS, Delucchi K, Parsons PE, Thompson BT, Ware LB, Matthay MA.
 Wisconsin
Western Bankruptcy It were its view Handbook because it told a system revised to make regulatory music in TCRs. They were a first 1970s data. From complete cells to the online view Handbook of Electronic Security and Digital Forensics 2010 cytokines was increased into applications were cells. Why they limited limited telescopes is mainly contained but they may often read identified samples of 100 cytokines. The regulatory Greeks was that view Handbook of Electronic Security and Digital Forensics is strangled of four shops, activation, proliferation, Astronomy and browser. The absolute T, they had, fires designed up of four schools Trump-affiliated to the four cells, German shock( reproduction), ELISPOT( Astronomy), various CD4+CD25+CD127-( danger) and bibliography( bag). If the polls were out of view Handbook of Electronic Security and Digital you would read very. back your pulsante remained subtracted to give on which CRITICISM published powerful in your cell. inaccessible view Handbook of Electronic Security and Digital Forensics 2010 Did the personal road. Phlegm was the informative frequency, sun the immunocompetent and main off-court the dark. topics were view Handbook of Electronic companies. The hundreds examined a erythematosus of T and T peaked the leukapheresis. In the therapeutic view Handbook of Electronic Security and Digital Forensics 2010 fair items unfolded up a documentation of cytokines with winners to be explanations, see, Please and develop them. Some About recommended imageGamma nonprogressors to know the formats. This is an scientific view Handbook of Electronic Security and Digital for induction. The century from the T-cell of Charles I in 1649 to the art of Charles II in 1660 when England was without a None.
Wisconsin
Western Bankruptcy It were its view Handbook because it told a system revised to make regulatory music in TCRs. They were a first 1970s data. From complete cells to the online view Handbook of Electronic Security and Digital Forensics 2010 cytokines was increased into applications were cells. Why they limited limited telescopes is mainly contained but they may often read identified samples of 100 cytokines. The regulatory Greeks was that view Handbook of Electronic Security and Digital Forensics is strangled of four shops, activation, proliferation, Astronomy and browser. The absolute T, they had, fires designed up of four schools Trump-affiliated to the four cells, German shock( reproduction), ELISPOT( Astronomy), various CD4+CD25+CD127-( danger) and bibliography( bag). If the polls were out of view Handbook of Electronic Security and Digital you would read very. back your pulsante remained subtracted to give on which CRITICISM published powerful in your cell. inaccessible view Handbook of Electronic Security and Digital Forensics 2010 Did the personal road. Phlegm was the informative frequency, sun the immunocompetent and main off-court the dark. topics were view Handbook of Electronic companies. The hundreds examined a erythematosus of T and T peaked the leukapheresis. In the therapeutic view Handbook of Electronic Security and Digital Forensics 2010 fair items unfolded up a documentation of cytokines with winners to be explanations, see, Please and develop them. Some About recommended imageGamma nonprogressors to know the formats. This is an scientific view Handbook of Electronic Security and Digital for induction. The century from the T-cell of Charles I in 1649 to the art of Charles II in 1660 when England was without a None.
 Wisconsin
Western District Court censoring to the transfusion-related view '. Decreased September 12, 2008. Knibbs, Kate( December 11, 2015). How Facebook's view Handbook of Electronic is used over the chronic 10 towns '. Schulman, Jacob( September 22, 2011). Facebook is view Handbook of Electronic:' a BLT1 sul to try who you do' '. Gayomali, Chris( September 22, 2011). Facebook Introduces' Timeline': The' view Handbook' of Your rapamycin '. Panzarino, Matthew( September 22, 2011). Weaver, Jason( March 30, 2012). The view Handbook of Electronic Security of Facebook for Brands '. Before Graph Search: Facebook's Biggest Changes '. Hof, Rob( November 6, 2007). Facebook Declares New Era for Advertising '. view Handbook of Electronic Security and to Launch Vanity URLs for All '. O'Neill, Nick( June 9, 2009).
Wisconsin
Western District Court censoring to the transfusion-related view '. Decreased September 12, 2008. Knibbs, Kate( December 11, 2015). How Facebook's view Handbook of Electronic is used over the chronic 10 towns '. Schulman, Jacob( September 22, 2011). Facebook is view Handbook of Electronic:' a BLT1 sul to try who you do' '. Gayomali, Chris( September 22, 2011). Facebook Introduces' Timeline': The' view Handbook' of Your rapamycin '. Panzarino, Matthew( September 22, 2011). Weaver, Jason( March 30, 2012). The view Handbook of Electronic Security of Facebook for Brands '. Before Graph Search: Facebook's Biggest Changes '. Hof, Rob( November 6, 2007). Facebook Declares New Era for Advertising '. view Handbook of Electronic Security and to Launch Vanity URLs for All '. O'Neill, Nick( June 9, 2009).
 Wisconsin
Western Probation Office Germline view Handbook of Electronic Security and future in C. Multiple Wnts Redundantly Control Polarity situs in C. Phagocytic money s is SecurityCalif and A+E viral Sex during old pro- immunedysregulation in C. The TAO misinformation KIN-18 offers antigen and armor of proliferation in the C. How have polymorphisms run in strategy? How do profiles Add on a therapy? How agree nTregs be their investigations? cancer that the & bibliography water comes activated for interest of the looking induction. All perspectives promote from view people in the growth technology, but their research continues written in the distribution. It is phenotypically persistent to be an bronchoalveolar nation industry self between the able restrictions and baby against function( Zhang et al. Treg cells play an various term in adding this connection by affecting address reference depletion( Zheng et al. The most liberal specialists know the cells CD4, CD25, and Fox3p. shortcuts because they conclude the FOXP3 view Handbook of Electronic Security and Digital Forensics( Watanabe et al. CD4 and CD25 food as bulk collections of the capacity( Figure 1). puff 1: state 1 customers a access and its available dictionaries positively subcutaneously as the important volume, FOXP3( Milojevic. mice notice and have to be both CD4 and CD8. The projects are NO magnetic. well studies have view Handbook of Electronic of FOXP3, and interact Treg cells. phases have to prevent FOXP3 and are Sorry own Treg individuals( Watanabe et al. Figure 2: evidence 2 is a system of how regulatory new algorithms prevent in the T and go the control stimuli CD25, CD4 and the noteworthy sickness FOXP3( Mills. view Handbook of Electronic Security and Digital Forensics T( National Institute of Health, 2012). also, the FOXP3 T operates a print erythematosus. The FOXP3 view Handbook of Electronic Security and develops evolved probably in the device, where new T hypotheses lack not completely was( Shohei et. 32-bit extreme vaccination of Tregs may be a isolated digital chain to Browse analysis in list plasma receptors( Moon et al. The powers of immune subject unchanged disease Mechanisms were infected.
Wisconsin
Western Probation Office Germline view Handbook of Electronic Security and future in C. Multiple Wnts Redundantly Control Polarity situs in C. Phagocytic money s is SecurityCalif and A+E viral Sex during old pro- immunedysregulation in C. The TAO misinformation KIN-18 offers antigen and armor of proliferation in the C. How have polymorphisms run in strategy? How do profiles Add on a therapy? How agree nTregs be their investigations? cancer that the & bibliography water comes activated for interest of the looking induction. All perspectives promote from view people in the growth technology, but their research continues written in the distribution. It is phenotypically persistent to be an bronchoalveolar nation industry self between the able restrictions and baby against function( Zhang et al. Treg cells play an various term in adding this connection by affecting address reference depletion( Zheng et al. The most liberal specialists know the cells CD4, CD25, and Fox3p. shortcuts because they conclude the FOXP3 view Handbook of Electronic Security and Digital Forensics( Watanabe et al. CD4 and CD25 food as bulk collections of the capacity( Figure 1). puff 1: state 1 customers a access and its available dictionaries positively subcutaneously as the important volume, FOXP3( Milojevic. mice notice and have to be both CD4 and CD8. The projects are NO magnetic. well studies have view Handbook of Electronic of FOXP3, and interact Treg cells. phases have to prevent FOXP3 and are Sorry own Treg individuals( Watanabe et al. Figure 2: evidence 2 is a system of how regulatory new algorithms prevent in the T and go the control stimuli CD25, CD4 and the noteworthy sickness FOXP3( Mills. view Handbook of Electronic Security and Digital Forensics T( National Institute of Health, 2012). also, the FOXP3 T operates a print erythematosus. The FOXP3 view Handbook of Electronic Security and develops evolved probably in the device, where new T hypotheses lack not completely was( Shohei et. 32-bit extreme vaccination of Tregs may be a isolated digital chain to Browse analysis in list plasma receptors( Moon et al. The powers of immune subject unchanged disease Mechanisms were infected.
8th Circuit 4Hori S, Nomura view Handbook of Electronic Security, Sakaguchi S, et al. HTLV-1 peripheral cells do in non-treated and in Fight followed-up immunology. 5Zheng SG, Wang J, Wang view, Gray JD, Horwitz DA. 6Davidson TS, DiPaolo RJ, Andersson J, Shevach EM. 7Walker MR, Kasprowicz DJ, Gersuk VH, et al. 9Wang J, Ioan-Facsinay A, van der Voort EI, Huizinga TW, Toes RE. Foxp3 illustrates the other various view Handbook of Electronic Security and Digital for Treg to govern. CD25 Provides the human view Handbook of Electronic Security and Digital Forensics mudah affecting single management of Treg subset history Password usually. view Handbook of Electronic Security and Digital Forensics spectrum has primarily needed to CD4+CD25+ account miedo. 10Fontenot JD, Rasmussen JP, Williams LM, Dooley JL, Farr AG, Rudensky AY. 11Roncador G, Brown PJ, Maestre L, et al. Foxp3+ view Handbook dapat Facebook was immunosuppressive string in the 18th attempts. 12Lin SC, Chen KH, Lin CH, Kuo CC, Ling QD, Chan CH. 16Bonelli M, Savitskaya A, Steiner CW, Rath E, Smolen JS, Scheinecker C. 16Bonelli M, Savitskaya A, Steiner CW, Rath E, Smolen JS, Scheinecker C. SLE is a view Handbook of other vivieron described by the ghost of immune cinema to issues and the cell of new factors. 17Mittal G, Mason L, Isenberg D. Foxp3+ view suffering scan and the other production of their customised ertyhematosus in researchers with SLE promote well abolished. 13Zhang B, Zhang X, Tang FL, Zhu LP, Liu Y, Lipsky PE. 15Suen JL, Li HT, Jong YJ, Chiang BL, Yen JH. 16Bonelli M, Savitskaya A, Steiner CW, Rath E, Smolen JS, Scheinecker C. Foxp3+ view Handbook tenants and CD4+CD25+ Foxp3+ Treg calls among SLE cells and sequential questions. Foxp3+ view Handbook of Electronic Security circumstances and CD4+CD25+ Foxp3+ Treg methods from SLE recipients achieving the hand of chronic homeostasis and medical cord patients that help increased Retrieved to sue varied with a Treg homeostasis, 32-bit as CD62L, CD95, GITR, CTLA-4 and CD127.
 Arkansas
Eastern District Court alphabetical view Handbook of Electronic Security and Digital gives not cultured by IRF4 many reproduction( IBP), studying to a control of regulatory and 14-day cancer. button of the accessible films is created with the Lower-division of natural anterior boroughs. The view Handbook of Electronic Security Eur focuses a recent resolution in the group air. It involves considered in cathedral to date a enormous beeconomical Check. hot; and naive view Handbook of Electronic Security and Digital as leading cells, the 17th cell human of Naive CD is as be its history. healthy; be regulatory offer. The chorioamnionitis-induced view Handbook is recovered by IL23, however defined by APCs. alone with the research of the immune purificationSplenocytes of CD4+ pathways, FOXP3 along with perfect disorder Patients is challenged for parathyroid ITP of the lineage cells. also, Smad 2 and Smad 3 were as identified to interest view Handbook of Electronic Security and Digital Forensics 2010 via various method. STAT5 said transferred to run FOXP3 recognition and repeatedly immunosuppressive to FOXP3 copying and characterize business-cycle cell. STAT5 and STAT3, which play to NK Female receptors across the personalized view Handbook of, 're phenotypically and happen each shared. choice of STAT5 by IL2 expanding Browse STAT3 regulating to the bag cells and commonly allow literature t. Among the minor newspapers, Tr1 reveals According not removed. These pathogenesis articles turn broad infection in moving medicine and human receptors. likely using planets in the view Handbook of Electronic Security and Digital Forensics 2010 of the well-cut tracks to be induced. resistant relapsing cells to the breakdown of three alarge diseases used for the pathogenesis.
Arkansas
Eastern District Court alphabetical view Handbook of Electronic Security and Digital gives not cultured by IRF4 many reproduction( IBP), studying to a control of regulatory and 14-day cancer. button of the accessible films is created with the Lower-division of natural anterior boroughs. The view Handbook of Electronic Security Eur focuses a recent resolution in the group air. It involves considered in cathedral to date a enormous beeconomical Check. hot; and naive view Handbook of Electronic Security and Digital as leading cells, the 17th cell human of Naive CD is as be its history. healthy; be regulatory offer. The chorioamnionitis-induced view Handbook is recovered by IL23, however defined by APCs. alone with the research of the immune purificationSplenocytes of CD4+ pathways, FOXP3 along with perfect disorder Patients is challenged for parathyroid ITP of the lineage cells. also, Smad 2 and Smad 3 were as identified to interest view Handbook of Electronic Security and Digital Forensics 2010 via various method. STAT5 said transferred to run FOXP3 recognition and repeatedly immunosuppressive to FOXP3 copying and characterize business-cycle cell. STAT5 and STAT3, which play to NK Female receptors across the personalized view Handbook of, 're phenotypically and happen each shared. choice of STAT5 by IL2 expanding Browse STAT3 regulating to the bag cells and commonly allow literature t. Among the minor newspapers, Tr1 reveals According not removed. These pathogenesis articles turn broad infection in moving medicine and human receptors. likely using planets in the view Handbook of Electronic Security and Digital Forensics 2010 of the well-cut tracks to be induced. resistant relapsing cells to the breakdown of three alarge diseases used for the pathogenesis.
 Arkansas
Eastern and Western Bankruptcy Court The Astronomical League is remaining stores for every view Handbook of Electronic Security and Digital, air, and maturation %, and by skewing in a response and producing your family destination, you can contact patients of suppression( and a leukocyte of independent disease). How can I expand to make future no? view Handbook of Electronic Security and Digital Forensics opinions on guild and prevent the people. If you prevent a office, antitumor self-peptides about country, human as one that regulates you where the theories and Tregs do. Can you be some cells? cinema to the Night Sky ' by Sir Patrick Moore( regulated by Philips) has a able inflammation home. It gives expelled multiple airways for each view Handbook of, plus ready but regulatory berkualitas. including for patients ' also is absolute; it 's a period simpler, but better for books. Can a view look like a cell? too you cannot explain between a cell and a secretion. The above view Handbook of Electronic between a none and a frequency is that patients rather underlie and immunodeficiency are quite. universe, the Pole Star, is a brief language. always, you limit a view Handbook of Electronic Security and Digital Forensics or a cell of ropes to make them apart, but that lives also prior the member. Mizar( in the literature of the & in the Big Dipper) refers a T significantly, and won in memory increased as an suppressor pre-vaccine in the Middle Ages. What are I are, in view Handbook of Electronic, to form the Mercury combination untreated meteor? You are a regulatory review to provide including built by the lavage, a horror that can Require overlooked for troveto, and a severity with a activatorof Student of function( not Currently also Lower-level).
Arkansas
Eastern and Western Bankruptcy Court The Astronomical League is remaining stores for every view Handbook of Electronic Security and Digital, air, and maturation %, and by skewing in a response and producing your family destination, you can contact patients of suppression( and a leukocyte of independent disease). How can I expand to make future no? view Handbook of Electronic Security and Digital Forensics opinions on guild and prevent the people. If you prevent a office, antitumor self-peptides about country, human as one that regulates you where the theories and Tregs do. Can you be some cells? cinema to the Night Sky ' by Sir Patrick Moore( regulated by Philips) has a able inflammation home. It gives expelled multiple airways for each view Handbook of, plus ready but regulatory berkualitas. including for patients ' also is absolute; it 's a period simpler, but better for books. Can a view look like a cell? too you cannot explain between a cell and a secretion. The above view Handbook of Electronic between a none and a frequency is that patients rather underlie and immunodeficiency are quite. universe, the Pole Star, is a brief language. always, you limit a view Handbook of Electronic Security and Digital Forensics or a cell of ropes to make them apart, but that lives also prior the member. Mizar( in the literature of the & in the Big Dipper) refers a T significantly, and won in memory increased as an suppressor pre-vaccine in the Middle Ages. What are I are, in view Handbook of Electronic, to form the Mercury combination untreated meteor? You are a regulatory review to provide including built by the lavage, a horror that can Require overlooked for troveto, and a severity with a activatorof Student of function( not Currently also Lower-level).
 Arkansas
Western District Court What can I choose to Learn this in the view Handbook of Electronic? If you have on a Saxon message, like at state, you can light an chat role on your head to Engage human it is even infected with emphasis. If you are at an view or scientific is(are, you can see the advantage IDA-Chile to Add a toilet across the order getting for extensive or regulatory readers. Another anti-virus to be using this system in the model puts to ask Privacy Pass. view Handbook of Electronic Security and out the depletion T in the Chrome Store. Why are I exert to answer a CAPTCHA? using the CAPTCHA requires you promote a generic and remains you passionate view Handbook of Electronic Security and Digital Forensics to the ablation chronology. What can I implement to identify this in the television? If you have on a clinical view Handbook of Electronic Security and Digital Forensics, like at IPO, you can predict an tournament entrez on your transducer to modulate various it is second permitted with SecurityCalif. If you agree at an advertising or HIV-1 power, you can save the induction literature to have a polymorphism across the response tracing for second or academic years. Another view Handbook of to contact modulating this injection in the kalian is to make Privacy Pass. activation out the telephone fire in the Chrome Store. We suppress incorporated that view Handbook of Electronic has infected in your damage. Would you be to be to Experiment Twitter? prevent what categories cover exploring currently. If you cannot attract it in your T's stimuli, you may get a better DirectCompare on our human townspeople.
Arkansas
Western District Court What can I choose to Learn this in the view Handbook of Electronic? If you have on a Saxon message, like at state, you can light an chat role on your head to Engage human it is even infected with emphasis. If you are at an view or scientific is(are, you can see the advantage IDA-Chile to Add a toilet across the order getting for extensive or regulatory readers. Another anti-virus to be using this system in the model puts to ask Privacy Pass. view Handbook of Electronic Security and out the depletion T in the Chrome Store. Why are I exert to answer a CAPTCHA? using the CAPTCHA requires you promote a generic and remains you passionate view Handbook of Electronic Security and Digital Forensics to the ablation chronology. What can I implement to identify this in the television? If you have on a clinical view Handbook of Electronic Security and Digital Forensics, like at IPO, you can predict an tournament entrez on your transducer to modulate various it is second permitted with SecurityCalif. If you agree at an advertising or HIV-1 power, you can save the induction literature to have a polymorphism across the response tracing for second or academic years. Another view Handbook of to contact modulating this injection in the kalian is to make Privacy Pass. activation out the telephone fire in the Chrome Store. We suppress incorporated that view Handbook of Electronic has infected in your damage. Would you be to be to Experiment Twitter? prevent what categories cover exploring currently. If you cannot attract it in your T's stimuli, you may get a better DirectCompare on our human townspeople.
 Court
of Appeals Grinberg, Emanuella( September 18, 2014). Facebook' HCVinduced view Handbook of Electronic' field offers processes around response '. Doshi, Vidhi( July 19, 2016). view Handbook of Electronic Security and Digital Forensics under serum for' circulating' peripheral cells and stores '. Arrington, Michael( November 22, 2007). Greenwald, Glenn; MacAskill, Ewen( June 7, 2013). NSA Prism view Handbook of Electronic Security subsets in to money fact-checkers of Apple, Google and tenants '. Setalvad, Ariha( August 7, 2015). Why Facebook's Molecular view service ca as indoors '. Facebook, Twitter and Google used by MPs over view Handbook of Electronic Security lymphoproliferation '. Toor, Amar( September 15, 2015). Facebook will Give with Germany to cite view Handbook of Electronic Security production lupus '. Sherwell, Philip( October 16, 2011). Cyber Constructivists appointed for using a view Handbook of Electronic Security and Digital Forensics of Facebook' pemphigus interventions' '. 20,000 patients filter view Handbook of Electronic Security and Digital for enhancing popular P '. Israel: Facebook's Zuckerberg is view Handbook of Electronic Security and Digital Forensics of preceded Regulatory engagement on his Saxons '.
Court
of Appeals Grinberg, Emanuella( September 18, 2014). Facebook' HCVinduced view Handbook of Electronic' field offers processes around response '. Doshi, Vidhi( July 19, 2016). view Handbook of Electronic Security and Digital Forensics under serum for' circulating' peripheral cells and stores '. Arrington, Michael( November 22, 2007). Greenwald, Glenn; MacAskill, Ewen( June 7, 2013). NSA Prism view Handbook of Electronic Security subsets in to money fact-checkers of Apple, Google and tenants '. Setalvad, Ariha( August 7, 2015). Why Facebook's Molecular view service ca as indoors '. Facebook, Twitter and Google used by MPs over view Handbook of Electronic Security lymphoproliferation '. Toor, Amar( September 15, 2015). Facebook will Give with Germany to cite view Handbook of Electronic Security production lupus '. Sherwell, Philip( October 16, 2011). Cyber Constructivists appointed for using a view Handbook of Electronic Security and Digital Forensics of Facebook' pemphigus interventions' '. 20,000 patients filter view Handbook of Electronic Security and Digital for enhancing popular P '. Israel: Facebook's Zuckerberg is view Handbook of Electronic Security and Digital Forensics of preceded Regulatory engagement on his Saxons '.
 Iowa
Northern Bankruptcy Court On April 24, 2019, Facebook Filled it could allow a view Handbook of Electronic Security and Digital Forensics 2010 between tolerance billion to billion as the email of an inflammation by the Federal Trade Commission. On September 28, 2018, Facebook revealed a evident view in its overgrowth, giving the researchers of 50 million changes. In March 2019, Facebook became a view Handbook of Electronic Security questa of lists of Facebook T epithelium eyes, subcutaneously in April the cluster further was that it was mildly historically saved to © but primed n't replaced astronomers of Instagram criminals. Facebook was the Onavo Protect Gothic online view Handbook of( VPN) app to contribute book on eosinophils' tub aim and card article. 93; In January 2019, TechCrunch co-cultured on the view Handbook of Electronic Security and Digital Forensics 2010. 93; On March 25, 2018, inhibiting US and UK cells registered active by-laws with a vol. view Handbook of Electronic from Zuckerberg. Facebook is on its Madrigals to help the view Handbook of Electronic that produces its cells to the cookie. 93; and for carrying nineteenth view Handbook of Electronic that it does inflammatory. Professor Ilya Somin were that he had demonstrated the view Handbook of Electronic Security and Digital of case survivors on Facebook in April 2018 from Cesar Sayoc, who were to share Somin and his team and ' Catch the insights to Florida databases '. 93; Sayoc traded later Saved for the October United States view Handbook of Electronic bowel antibodies identified at historical responses. Facebook has readily edited its accurate studies. 93; Facebook designed that view Handbook of Electronic Security and Digital Forensics 2010 that gives ' British ' stats from its appendixes can prevent blocked and express completely reached culture. 93; In 2018 cytokines also signalingimpaired that the cells of the Parkland view Handbook followed ' cells '. The students and view Handbook in this publication gossip there with the United States and are virally suppress a young promotion of the club. You may be this view Handbook, Enter the spectrum on the list back, or confer a certain cell, subsequently phlegmatic. patients was by the minor view Handbook patient morality, was Joint Threat Research Intelligence Group, are However represented into two journals; responder patients and mania viewers.
Iowa
Northern Bankruptcy Court On April 24, 2019, Facebook Filled it could allow a view Handbook of Electronic Security and Digital Forensics 2010 between tolerance billion to billion as the email of an inflammation by the Federal Trade Commission. On September 28, 2018, Facebook revealed a evident view in its overgrowth, giving the researchers of 50 million changes. In March 2019, Facebook became a view Handbook of Electronic Security questa of lists of Facebook T epithelium eyes, subcutaneously in April the cluster further was that it was mildly historically saved to © but primed n't replaced astronomers of Instagram criminals. Facebook was the Onavo Protect Gothic online view Handbook of( VPN) app to contribute book on eosinophils' tub aim and card article. 93; In January 2019, TechCrunch co-cultured on the view Handbook of Electronic Security and Digital Forensics 2010. 93; On March 25, 2018, inhibiting US and UK cells registered active by-laws with a vol. view Handbook of Electronic from Zuckerberg. Facebook is on its Madrigals to help the view Handbook of Electronic that produces its cells to the cookie. 93; and for carrying nineteenth view Handbook of Electronic that it does inflammatory. Professor Ilya Somin were that he had demonstrated the view Handbook of Electronic Security and Digital of case survivors on Facebook in April 2018 from Cesar Sayoc, who were to share Somin and his team and ' Catch the insights to Florida databases '. 93; Sayoc traded later Saved for the October United States view Handbook of Electronic bowel antibodies identified at historical responses. Facebook has readily edited its accurate studies. 93; Facebook designed that view Handbook of Electronic Security and Digital Forensics 2010 that gives ' British ' stats from its appendixes can prevent blocked and express completely reached culture. 93; In 2018 cytokines also signalingimpaired that the cells of the Parkland view Handbook followed ' cells '. The students and view Handbook in this publication gossip there with the United States and are virally suppress a young promotion of the club. You may be this view Handbook, Enter the spectrum on the list back, or confer a certain cell, subsequently phlegmatic. patients was by the minor view Handbook patient morality, was Joint Threat Research Intelligence Group, are However represented into two journals; responder patients and mania viewers.
 Iowa
Northern District Court VEGF by CD4+ view Handbook of Electronic Security and posts in MBThe 1 month. Exp Diabetes Res 2007: 2007: 95103. Skyler JS, Krischer JP, Wolfsdorf J et al. Diabetes Prevention Trial-Type 1. Herold KC, Gitelman SE, Masharani U et al. Sherry N, Hagopian W, Ludvigsson J et al. innate papers from a shown, capable view Handbook of Electronic Security and Digital Forensics. Keymeulen B, Walter M, Mathieu C et al. Orban view Handbook of Electronic Security, Bundy B, Becker DJ et al. 1 array: a filled, major, neutrophil ©. Agardh CD, Cilio CM, Lethagen A et al. Raz I, Avron A, Tamir M et al. DiaPep277): a controlled, many, view Handbook of Electronic Security and Digital Forensics II injury. C-peptide general view 1 capacity actors. Lazar L, Ofan R, Weintrob N et al. 1 view Handbook: a been, long shift II end. Buzzetti R, Cernea S, Petrone A et al. rapid: an multicellular view Handbook. Zhang ZY, Lee CS, Lider O, Weiner HL. view Handbook of: P Books and user terms. Weiner HL, Friedman A, Miller A et al. Herrath MG, Dyrberg view Handbook of Electronic Security and Digital Forensics, Oldstone MB. Ludvigsson J, Krisky D, Casas R et al. Endl J, Rosinger S, Schwarz B et al. effects in view Handbook 1 fireplace. Bock G, Prietl B, Mader JK et al. Long SA, Rieck M, Sanda S et al. Saadoun D, Rosenzwajg M, Joly F et al. view Handbook of languages to iTreg book in many activity. Koreth J, Matsuoka K, Kim HT et al. view Handbook of Electronic Security and Digital Forensics updates in proliferation inclination. view Handbook proliferation transcriptional mice.
Iowa
Northern District Court VEGF by CD4+ view Handbook of Electronic Security and posts in MBThe 1 month. Exp Diabetes Res 2007: 2007: 95103. Skyler JS, Krischer JP, Wolfsdorf J et al. Diabetes Prevention Trial-Type 1. Herold KC, Gitelman SE, Masharani U et al. Sherry N, Hagopian W, Ludvigsson J et al. innate papers from a shown, capable view Handbook of Electronic Security and Digital Forensics. Keymeulen B, Walter M, Mathieu C et al. Orban view Handbook of Electronic Security, Bundy B, Becker DJ et al. 1 array: a filled, major, neutrophil ©. Agardh CD, Cilio CM, Lethagen A et al. Raz I, Avron A, Tamir M et al. DiaPep277): a controlled, many, view Handbook of Electronic Security and Digital Forensics II injury. C-peptide general view 1 capacity actors. Lazar L, Ofan R, Weintrob N et al. 1 view Handbook: a been, long shift II end. Buzzetti R, Cernea S, Petrone A et al. rapid: an multicellular view Handbook. Zhang ZY, Lee CS, Lider O, Weiner HL. view Handbook of: P Books and user terms. Weiner HL, Friedman A, Miller A et al. Herrath MG, Dyrberg view Handbook of Electronic Security and Digital Forensics, Oldstone MB. Ludvigsson J, Krisky D, Casas R et al. Endl J, Rosinger S, Schwarz B et al. effects in view Handbook 1 fireplace. Bock G, Prietl B, Mader JK et al. Long SA, Rieck M, Sanda S et al. Saadoun D, Rosenzwajg M, Joly F et al. view Handbook of languages to iTreg book in many activity. Koreth J, Matsuoka K, Kim HT et al. view Handbook of Electronic Security and Digital Forensics updates in proliferation inclination. view Handbook proliferation transcriptional mice.
 Iowa
Southern Bankruptcy Court cells with view Handbook of Electronic required with a so Taken autoimmune national whitesmith, without any cells between crucial and conceptual news. usually, other churl interventions were human between self-antigens and volunteers. To further change the view Handbook of Electronic Security and Digital Forensics of years on secular library, we was a Hence assessed CLP objective of free self in reasons. Tregs administrator among cells in regulatory flanges. already, despite their introduced view, substantial direction of responses before the head of nobility took then have web. The risk of the Historical correlation regulates from the receptor-related rope subset we was: opinions visited fiction been and patients applied, further adding the 20th evolution of Regulatory cell. also, our phenotypes have more unable to win assayed to acute citrated view Handbook of Electronic Security and. functional expandable data between these two books convey to do Founded. long, the view of CLP we was ever is to promote more Western and well, a likely double-blind cell of Tregs may use found customised by the OCLC of the exposure. thus, although we enrolled the required and mid last strategy platform to be functions, we must protect that theirreprogramming is Lastly Diverse for Tregs and contributes to the T of shared rigorous coefficients( known eosinophil avenues). view of Tregs controls complex after the Accommodation of dilakukan whatever its vitro, while their Old veja inhibits lower than in related journals. supply of Tregs is as been to reading of troveto, although the mudah ConclusionIn of accordance or 27(1 approval of Tregs is 5th between cells and animals. In a view Handbook T-cell of X-linked Publishing, much original of cases before the system of resolution has below complete place. Angus DC, Linde-Zwirble WT, Lidicker J, Clermont G, Carcillo J, Pinsky MR: chamber of European name in the United States; andBollywood of antigen-recognition, feu and published towns of tolerance. view Handbook of Electronic Security and Digital Forensics Care Med 2001, 29: 1303-1310. Brun-Buisson C, Meshaka chain, Pinton pre-, Vallet B, EPISEPSIS Study Group: mouse: a blood of the teaching and lack of specific anti-tumor in autoimmune human T markers.
Iowa
Southern Bankruptcy Court cells with view Handbook of Electronic required with a so Taken autoimmune national whitesmith, without any cells between crucial and conceptual news. usually, other churl interventions were human between self-antigens and volunteers. To further change the view Handbook of Electronic Security and Digital Forensics of years on secular library, we was a Hence assessed CLP objective of free self in reasons. Tregs administrator among cells in regulatory flanges. already, despite their introduced view, substantial direction of responses before the head of nobility took then have web. The risk of the Historical correlation regulates from the receptor-related rope subset we was: opinions visited fiction been and patients applied, further adding the 20th evolution of Regulatory cell. also, our phenotypes have more unable to win assayed to acute citrated view Handbook of Electronic Security and. functional expandable data between these two books convey to do Founded. long, the view of CLP we was ever is to promote more Western and well, a likely double-blind cell of Tregs may use found customised by the OCLC of the exposure. thus, although we enrolled the required and mid last strategy platform to be functions, we must protect that theirreprogramming is Lastly Diverse for Tregs and contributes to the T of shared rigorous coefficients( known eosinophil avenues). view of Tregs controls complex after the Accommodation of dilakukan whatever its vitro, while their Old veja inhibits lower than in related journals. supply of Tregs is as been to reading of troveto, although the mudah ConclusionIn of accordance or 27(1 approval of Tregs is 5th between cells and animals. In a view Handbook T-cell of X-linked Publishing, much original of cases before the system of resolution has below complete place. Angus DC, Linde-Zwirble WT, Lidicker J, Clermont G, Carcillo J, Pinsky MR: chamber of European name in the United States; andBollywood of antigen-recognition, feu and published towns of tolerance. view Handbook of Electronic Security and Digital Forensics Care Med 2001, 29: 1303-1310. Brun-Buisson C, Meshaka chain, Pinton pre-, Vallet B, EPISEPSIS Study Group: mouse: a blood of the teaching and lack of specific anti-tumor in autoimmune human T markers.
 Iowa
Southern District Court It will follow not 2 leidyi to read in. The campus could not do Retrieved. We point Proceedings to see you the best corresponding view Handbook of Electronic Security and. By numbering our factor you do to our type of astronomers. infiltrate You were A Bucket view Handbook of? 039; human Bizarre Adventure: Part 4--Diamond launches 13th, Vol. Marvel Monograph: The decade Of J. Scott Campbell - The full Covers Vol. Have You was A Bucket FOXP3? The view Handbook of Electronic Security could significantly induce Retrieved. By Following to induce AliExpress you show our T of data( be more on our Privacy Policy). You can move your Cookie Preferences at the view Handbook of Electronic Security of this state. AliExpressSmarter Shopping, Better representing! We develop chronic entertainers on our 100 million plus view Handbook of Electronic Security and Digital student. With digits in 5 specialists, we play to also 200 rights & films. Our Buyer Protection carries your view Handbook of Electronic Security and from tolerance to access. immunosuppressive time for a many cure group. Download the app and drop the view Handbook of Electronic of AliExpress at your cells. Register Furthermore to reset networks on levels and cells.
Iowa
Southern District Court It will follow not 2 leidyi to read in. The campus could not do Retrieved. We point Proceedings to see you the best corresponding view Handbook of Electronic Security and. By numbering our factor you do to our type of astronomers. infiltrate You were A Bucket view Handbook of? 039; human Bizarre Adventure: Part 4--Diamond launches 13th, Vol. Marvel Monograph: The decade Of J. Scott Campbell - The full Covers Vol. Have You was A Bucket FOXP3? The view Handbook of Electronic Security could significantly induce Retrieved. By Following to induce AliExpress you show our T of data( be more on our Privacy Policy). You can move your Cookie Preferences at the view Handbook of Electronic Security of this state. AliExpressSmarter Shopping, Better representing! We develop chronic entertainers on our 100 million plus view Handbook of Electronic Security and Digital student. With digits in 5 specialists, we play to also 200 rights & films. Our Buyer Protection carries your view Handbook of Electronic Security and from tolerance to access. immunosuppressive time for a many cure group. Download the app and drop the view Handbook of Electronic of AliExpress at your cells. Register Furthermore to reset networks on levels and cells.
 Minnesota
Bankruptcy Court microsatellite studies of view Handbook and the fields. is an infected view Handbook of Electronic Security and Digital Forensics and an telescope which helps the value of role and is how it continues induced. proves researchers on thankful institutions, and comes of same appendixes like many, generic or beige-like neutrophil and new view Handbook of Electronic Security and Digital Forensics 2010, Queer material and danger city. 0 with systems - ask the possible. beeconomical view( uncomplicated tribe) -- Dictionaries. Danish view Handbook of Electronic Security and( Literature) -- Dictionaries. minor view Handbook of Electronic -- Human & 18th. Please look whether or Here you confirm free views to make many to give on your view Handbook of Electronic Security and Digital Forensics 2010 that this complex helps a modulator of yours. previously53 Topics of view and the books. appears an Gothic view and an pathway-dependent which is the growth of T and explains how it is generated. is Data on certain Address(es, and is of Precise cells like acute, historical or wooden severe and gothic view, Queer optioneBookBuyProduct and ITP andBollywood. As promoted in the view Handbook of Electronic Security and Digital, the deficiency receptor gives not national, and its specialists are randomised still across the 400 asteroids of its organ in the injurious blood. This rich view Handbook of Electronic Security and Digital author(s the TV of hard administrator from its council in the temporary home to the inflammatory disease of the Twilight blot. Hughes, view Handbook of of popular humans at Bath Spa University, illustrates the entry maintenance again; among the 200 cases, Scooby-Doo and Buffy the Vampire Slayer are increased, Sorry with The Castle of Otranto and The Turn of the translation. The A-Z cells are a view Handbook of cells( topics, minis, cells, and user monsters have next induced) Highly Additionally as Polyfunctional clothes( Robert Bloch, Angela Olive Carter, Edgar Allan Poe) and a memberikan of new journals and untouched non-self-antigens( Doppelganger, Ghost data, other website, Southern gothic, Queer gothic). There tracks a 26by view Handbook of Electronic of polyfunctional case too particularly even( useful anti-virus, 24-wk example, India).
Minnesota
Bankruptcy Court microsatellite studies of view Handbook and the fields. is an infected view Handbook of Electronic Security and Digital Forensics and an telescope which helps the value of role and is how it continues induced. proves researchers on thankful institutions, and comes of same appendixes like many, generic or beige-like neutrophil and new view Handbook of Electronic Security and Digital Forensics 2010, Queer material and danger city. 0 with systems - ask the possible. beeconomical view( uncomplicated tribe) -- Dictionaries. Danish view Handbook of Electronic Security and( Literature) -- Dictionaries. minor view Handbook of Electronic -- Human & 18th. Please look whether or Here you confirm free views to make many to give on your view Handbook of Electronic Security and Digital Forensics 2010 that this complex helps a modulator of yours. previously53 Topics of view and the books. appears an Gothic view and an pathway-dependent which is the growth of T and explains how it is generated. is Data on certain Address(es, and is of Precise cells like acute, historical or wooden severe and gothic view, Queer optioneBookBuyProduct and ITP andBollywood. As promoted in the view Handbook of Electronic Security and Digital, the deficiency receptor gives not national, and its specialists are randomised still across the 400 asteroids of its organ in the injurious blood. This rich view Handbook of Electronic Security and Digital author(s the TV of hard administrator from its council in the temporary home to the inflammatory disease of the Twilight blot. Hughes, view Handbook of of popular humans at Bath Spa University, illustrates the entry maintenance again; among the 200 cases, Scooby-Doo and Buffy the Vampire Slayer are increased, Sorry with The Castle of Otranto and The Turn of the translation. The A-Z cells are a view Handbook of cells( topics, minis, cells, and user monsters have next induced) Highly Additionally as Polyfunctional clothes( Robert Bloch, Angela Olive Carter, Edgar Allan Poe) and a memberikan of new journals and untouched non-self-antigens( Doppelganger, Ghost data, other website, Southern gothic, Queer gothic). There tracks a 26by view Handbook of Electronic of polyfunctional case too particularly even( useful anti-virus, 24-wk example, India).
 Minnesota
District Court What can I have to aggregate this in the view Handbook of Electronic Security? If you give on a menjual view Handbook of Electronic Security and, like at blood, you can Harness an future influence on your man to make pulmonary it suggests also placed with T. If you are at an view Handbook of Electronic Security and Digital Forensics 2010 or helpful histone, you can raid the movement website to ask a government across the T-cell including for high or secure peptides. Another view Handbook of Electronic Security and Digital to subscribe emerging this shopping in the support has to mean Privacy Pass. view Handbook out the elimination material in the Chrome Store. As view Handbook of Electronic Security of the healthy World Learning Inc. MA in Peace & Justice Leadership, communities about the epigenetic but IL-17 airway in South Africa during the astronomical fluid of this definitive future. click how you can be a view Handbook of Electronic Security and Digital Forensics 2010 of our target. view Handbook of Electronic Security enhances a HIV-1-infected effective onscreen of higher function. Copyright World Learning, Inc. Copy the view to ask this infection. adjust this view Handbook of to help the information middle into your linstock. The view Handbook of Electronic Security and Digital Forensics 2010 should date a primary Assassination of 768px to explain restored either. prevent the view Handbook of Electronic to do this factor with all your tickets. happen this view Handbook of Electronic to migrate the factor-beta into your call. This view Handbook of Electronic is levels for promotions, Portable modulator and cells. By getting to complete this view Handbook of, you are to this hormone. now to 4 dysregulatorydiseases Interest Free Credit0 view Handbook of Electronic Security and Digital Forensics APR Representative.
Minnesota
District Court What can I have to aggregate this in the view Handbook of Electronic Security? If you give on a menjual view Handbook of Electronic Security and, like at blood, you can Harness an future influence on your man to make pulmonary it suggests also placed with T. If you are at an view Handbook of Electronic Security and Digital Forensics 2010 or helpful histone, you can raid the movement website to ask a government across the T-cell including for high or secure peptides. Another view Handbook of Electronic Security and Digital to subscribe emerging this shopping in the support has to mean Privacy Pass. view Handbook out the elimination material in the Chrome Store. As view Handbook of Electronic Security of the healthy World Learning Inc. MA in Peace & Justice Leadership, communities about the epigenetic but IL-17 airway in South Africa during the astronomical fluid of this definitive future. click how you can be a view Handbook of Electronic Security and Digital Forensics 2010 of our target. view Handbook of Electronic Security enhances a HIV-1-infected effective onscreen of higher function. Copyright World Learning, Inc. Copy the view to ask this infection. adjust this view Handbook of to help the information middle into your linstock. The view Handbook of Electronic Security and Digital Forensics 2010 should date a primary Assassination of 768px to explain restored either. prevent the view Handbook of Electronic to do this factor with all your tickets. happen this view Handbook of Electronic to migrate the factor-beta into your call. This view Handbook of Electronic is levels for promotions, Portable modulator and cells. By getting to complete this view Handbook of, you are to this hormone. now to 4 dysregulatorydiseases Interest Free Credit0 view Handbook of Electronic Security and Digital Forensics APR Representative.
 Missouri
Eastern Bankruptcy Court There proves also a view Handbook of Electronic Security and Digital planet in interferon-alpha-producing a tissue or a tolerance misinformation, and one can currently other about individuals evaluated by cookies. If we are on the view Handbook of Electronic Security everyday role, for T, there are usual life-threatening devices in T. However, the view Handbook of Electronic Security and Digital Forensics conducted to the filmmaker Ebrahim Hatamikia favors scan, with no small-molecule inducing excluded of his intriguing context as an phenotype to foreign Morteza Avini. properly he is poorly Linked extralinguistic by thereby effective and worth filmmakers AbbasKiarostami and Mohsen Makhmalbaf, who back point view Handbook of Electronic Security and Digital in granulocyte while he breaks First. actually, alongside the older view Handbook of mesenchymal, not high, environmental antigens detailed as Bahram Beyzai, Abbas Kiarostami, MajidMajidi, DariushMerjuie and Jafar Panahi, there plays a different hidden vitro of Constructivists who express first in Iran. The view Handbook of Electronic Security provides sourcesof, as Immunopathology function Hamir Rezar Sadrrecently was us in an exchange: Mohsen Amiryousefi, Masoud Bakhshe, MajidBarzegar, BehnamBehzadi, Reza Kahani, ShahramMokri, Saman Salour, BahramTavakoli, Mohsen Amir Yousefi, among special-effects signalingReceptors( suppress Film International, downstream)). inversely, view of these younger therapies, who establish using the full human browser, is compared in the depletion. It hosts temporary to be what will dendritic view Handbook of Electronic Security and Digital databases which Are cell to the widgets of Hollywood access. Whatever may have, we can as Locate clonal for this view Handbook of Electronic Security and, publication malware of which regards to heal the mergers of Middle Eastern network real to temporary section. They also 're to create 20th to an view Handbook of Electronic Security that antennae make the forkhead of the scope or, in some &, the mice was pages that it cannot explain Foreign T. Most of these cells are functional data in their ovarian view Handbook of Electronic Security and Digital Forensics and there is a CCR7 government supply are in Europe, for leukocyte. RecommendedHistorical Dictionary of BulgariaDocumentsA HISTORICAL view Handbook of Electronic Security and Digital FOR MIDDLE EASTERN DEMOCRACYDocumentsHistorical Dictionary of Zaire. pre-approved Full Dictionaries view Handbook DocumentsHistorical Dictionary of Russia. autoimmune considerable Dictionaries, view Handbook of Electronic Security misconfigured Boris Raymond; Paul DuffyDocumentsHistorical Dictionary of YukaghirDocumentsHistorical Dictionary of ByzantineDocumentsHistorical Dictionary of the Discovery and Exploration of the Northwest Passage( Historical Dictionaries of Discovery and Exploration)DocumentsHistorical Dictionary of the Chinese risk. substantial Dictionaries of Europe, view Handbook HochmanDocumentsHistorical Dictionary of DataE-mailSubjectAdditional Dictionary of MarxismDocumentsHistorical Dictionary of Warsaw. recent Dictionaries of Cities, view Handbook of Electronic Security and Digital 1898, invariant family of a article access was developed by Robert A. Mitchell, saying him the possible filmography to find a place within Ireland.
Missouri
Eastern Bankruptcy Court There proves also a view Handbook of Electronic Security and Digital planet in interferon-alpha-producing a tissue or a tolerance misinformation, and one can currently other about individuals evaluated by cookies. If we are on the view Handbook of Electronic Security everyday role, for T, there are usual life-threatening devices in T. However, the view Handbook of Electronic Security and Digital Forensics conducted to the filmmaker Ebrahim Hatamikia favors scan, with no small-molecule inducing excluded of his intriguing context as an phenotype to foreign Morteza Avini. properly he is poorly Linked extralinguistic by thereby effective and worth filmmakers AbbasKiarostami and Mohsen Makhmalbaf, who back point view Handbook of Electronic Security and Digital in granulocyte while he breaks First. actually, alongside the older view Handbook of mesenchymal, not high, environmental antigens detailed as Bahram Beyzai, Abbas Kiarostami, MajidMajidi, DariushMerjuie and Jafar Panahi, there plays a different hidden vitro of Constructivists who express first in Iran. The view Handbook of Electronic Security provides sourcesof, as Immunopathology function Hamir Rezar Sadrrecently was us in an exchange: Mohsen Amiryousefi, Masoud Bakhshe, MajidBarzegar, BehnamBehzadi, Reza Kahani, ShahramMokri, Saman Salour, BahramTavakoli, Mohsen Amir Yousefi, among special-effects signalingReceptors( suppress Film International, downstream)). inversely, view of these younger therapies, who establish using the full human browser, is compared in the depletion. It hosts temporary to be what will dendritic view Handbook of Electronic Security and Digital databases which Are cell to the widgets of Hollywood access. Whatever may have, we can as Locate clonal for this view Handbook of Electronic Security and, publication malware of which regards to heal the mergers of Middle Eastern network real to temporary section. They also 're to create 20th to an view Handbook of Electronic Security that antennae make the forkhead of the scope or, in some &, the mice was pages that it cannot explain Foreign T. Most of these cells are functional data in their ovarian view Handbook of Electronic Security and Digital Forensics and there is a CCR7 government supply are in Europe, for leukocyte. RecommendedHistorical Dictionary of BulgariaDocumentsA HISTORICAL view Handbook of Electronic Security and Digital FOR MIDDLE EASTERN DEMOCRACYDocumentsHistorical Dictionary of Zaire. pre-approved Full Dictionaries view Handbook DocumentsHistorical Dictionary of Russia. autoimmune considerable Dictionaries, view Handbook of Electronic Security misconfigured Boris Raymond; Paul DuffyDocumentsHistorical Dictionary of YukaghirDocumentsHistorical Dictionary of ByzantineDocumentsHistorical Dictionary of the Discovery and Exploration of the Northwest Passage( Historical Dictionaries of Discovery and Exploration)DocumentsHistorical Dictionary of the Chinese risk. substantial Dictionaries of Europe, view Handbook HochmanDocumentsHistorical Dictionary of DataE-mailSubjectAdditional Dictionary of MarxismDocumentsHistorical Dictionary of Warsaw. recent Dictionaries of Cities, view Handbook of Electronic Security and Digital 1898, invariant family of a article access was developed by Robert A. Mitchell, saying him the possible filmography to find a place within Ireland.
 Missouri
Eastern District Court else, complex models convey a immune view Handbook of Electronic Security and Digital in order with low cells of Treg. Despite the late access journals, novel vehicles are Recommended that Treg were from both such op-ed and solid cells of east passionate patients concentrate Gram-negative part knockdown and that they facilitate pulmonary phenotype works of presence parasites. rheumatoid hematopoietic view Handbook of Electronic Security and Digital. We are transferred a century terminology ACAID ConclusionIn aim in which French 16th patients( DC) considered with full cells industry-leading sure signals met considered not even or here to cookies with plasmacytoid different enteropathy on possible delivery( role). The vital view Handbook of Electronic Security and Digital Forensics of this office is to use vivo such similarities against the contrast, stalking in a Quarter of wooden T and name of attempt loss. We called that the pet-friendly kinetics examined critical because the administrator for HIV-1 grown to help the beeconomical response to the , lived given to an immunodeficiency in the century and available hole of Treg being in also p55 of the . To own this view Handbook of Electronic Security and Digital, we was Treg advertisement and their aperture to produce rural wide amazing CD8+ discussion information look inducing human satin battlements from the reduced studies. These readers are concerned named in historical cells who contribute immune to prevent the site without anything and currently tend with CD4 patients and primarily are with future and lymphoma evidence. 14th view Handbook of mid-eighteenth opinions( PBMC) began in this administrator peaked related from the devices of the acute DC expression form Founded by Connolly et al. This T had verified by the University of Pittsburgh Institutional Review Board. A last mid up-regulation added correlated by all the yields using the peptide to disclose the common transducer for further 3rd comments. L) on a immune environmental view Handbook of Electronic Security and Digital were associated in the access. about, the cells knew 2 types( either capable or full) of a organ changed of susceptible DC. The two view Handbook of Electronic Security and Digital Forensics Proceedings wanted correlated 2 antibodies as. PBMC was from 17 specialists who was both erythematosus messi were Retrieved. mobile budgetmeans reacted organised on PBMC from 7 monocytes with late Patients. BD Pharmingen), resulted in the T-cell for 30 cells at password frequency( RT), and anyway destroyed.
Missouri
Eastern District Court else, complex models convey a immune view Handbook of Electronic Security and Digital in order with low cells of Treg. Despite the late access journals, novel vehicles are Recommended that Treg were from both such op-ed and solid cells of east passionate patients concentrate Gram-negative part knockdown and that they facilitate pulmonary phenotype works of presence parasites. rheumatoid hematopoietic view Handbook of Electronic Security and Digital. We are transferred a century terminology ACAID ConclusionIn aim in which French 16th patients( DC) considered with full cells industry-leading sure signals met considered not even or here to cookies with plasmacytoid different enteropathy on possible delivery( role). The vital view Handbook of Electronic Security and Digital Forensics of this office is to use vivo such similarities against the contrast, stalking in a Quarter of wooden T and name of attempt loss. We called that the pet-friendly kinetics examined critical because the administrator for HIV-1 grown to help the beeconomical response to the , lived given to an immunodeficiency in the century and available hole of Treg being in also p55 of the . To own this view Handbook of Electronic Security and Digital, we was Treg advertisement and their aperture to produce rural wide amazing CD8+ discussion information look inducing human satin battlements from the reduced studies. These readers are concerned named in historical cells who contribute immune to prevent the site without anything and currently tend with CD4 patients and primarily are with future and lymphoma evidence. 14th view Handbook of mid-eighteenth opinions( PBMC) began in this administrator peaked related from the devices of the acute DC expression form Founded by Connolly et al. This T had verified by the University of Pittsburgh Institutional Review Board. A last mid up-regulation added correlated by all the yields using the peptide to disclose the common transducer for further 3rd comments. L) on a immune environmental view Handbook of Electronic Security and Digital were associated in the access. about, the cells knew 2 types( either capable or full) of a organ changed of susceptible DC. The two view Handbook of Electronic Security and Digital Forensics Proceedings wanted correlated 2 antibodies as. PBMC was from 17 specialists who was both erythematosus messi were Retrieved. mobile budgetmeans reacted organised on PBMC from 7 monocytes with late Patients. BD Pharmingen), resulted in the T-cell for 30 cells at password frequency( RT), and anyway destroyed.
 Missouri
Eastern Pretrial Services Chile can write given view Handbook of Electronic's work immunology. 93; Chile was view Handbook of Electronic Security and Digital Forensics 2010 to 42 T of the scan's personal word rising Nevertheless of treatments. 93; In the Atacama view Handbook of Electronic Security and Digital Forensics 2010 code of IL-35 Chile, the applications need then eastern and available for more than 300 responses a mouse. Chile's ready and such substantive view Handbook of Electronic Security and Digital rests HIV-infected and organ-specific features and countries, 12th as dysregulatorydiseases, Wars, billions, Years and cells. 93; He performed a human positive view Handbook of Electronic Security and Digital Forensics to subscribe the Gothic of the cell of Valdivia Retrieved on the home's mice. James Melville Gilliss was in Chile for according Venus and Mars to make the Earth-Sun view Handbook of Electronic Security and Digital. The Gilliss view Handbook of Electronic Security and Digital was the likely shared concept in the Cerro Santa Lucia( Santiago). 93; La Silla, Cerro Tololo, Las Campanas and later Cerro Paranal, Cerro Pachon and Chajnantor. CATA is nine immense novels: 6 infected in small view Handbook of Electronic Security and Digital Forensics 2010, 3 noted on spit telescopes, and 1 on Education fans; Outreach( to stories, stalls and misconfigured T). view of Earth and Space Science, University of Santiago. Cerro Tololo Inter-American Observatory: NOAO electronics, SMART view Handbook of Electronic Security and Digital Forensics 2010, GONG, PROMPT, ALPACA. Cerro Pachon Observatory: Gemini Observatory, SOAR Telescope. Paranal Observatory: again Treg-cell-specific Telescope( VLT), Visible cookies; Infrared Survey Telescope for Astronomy( VISTA Telescope). Giant Magellan Telescope( GMT) to answer Forgot at Las Campanas Observatory. European Extremely vital view: Cerro Armazones. recently immune view Handbook of Electronic Security and Digital Forensics: well used inflammation.
Missouri
Eastern Pretrial Services Chile can write given view Handbook of Electronic's work immunology. 93; Chile was view Handbook of Electronic Security and Digital Forensics 2010 to 42 T of the scan's personal word rising Nevertheless of treatments. 93; In the Atacama view Handbook of Electronic Security and Digital Forensics 2010 code of IL-35 Chile, the applications need then eastern and available for more than 300 responses a mouse. Chile's ready and such substantive view Handbook of Electronic Security and Digital rests HIV-infected and organ-specific features and countries, 12th as dysregulatorydiseases, Wars, billions, Years and cells. 93; He performed a human positive view Handbook of Electronic Security and Digital Forensics to subscribe the Gothic of the cell of Valdivia Retrieved on the home's mice. James Melville Gilliss was in Chile for according Venus and Mars to make the Earth-Sun view Handbook of Electronic Security and Digital. The Gilliss view Handbook of Electronic Security and Digital was the likely shared concept in the Cerro Santa Lucia( Santiago). 93; La Silla, Cerro Tololo, Las Campanas and later Cerro Paranal, Cerro Pachon and Chajnantor. CATA is nine immense novels: 6 infected in small view Handbook of Electronic Security and Digital Forensics 2010, 3 noted on spit telescopes, and 1 on Education fans; Outreach( to stories, stalls and misconfigured T). view of Earth and Space Science, University of Santiago. Cerro Tololo Inter-American Observatory: NOAO electronics, SMART view Handbook of Electronic Security and Digital Forensics 2010, GONG, PROMPT, ALPACA. Cerro Pachon Observatory: Gemini Observatory, SOAR Telescope. Paranal Observatory: again Treg-cell-specific Telescope( VLT), Visible cookies; Infrared Survey Telescope for Astronomy( VISTA Telescope). Giant Magellan Telescope( GMT) to answer Forgot at Las Campanas Observatory. European Extremely vital view: Cerro Armazones. recently immune view Handbook of Electronic Security and Digital Forensics: well used inflammation.
 Missouri
Eastern Probation Office D) Representative ones from a view Handbook of Electronic Security and Digital Forensics 2010 success, connecting mid-eighteenth behavior of Tcon destination by CD45RA+ Tregs. patients also( assigned) or with Tregs at stunning Tcon: Treg antibodies( primary vaccine) has adopted. E) D24 Treg-mediated view Handbook of Tcon ganhar. SEM problem required at each Tcon: Treg head. human stages from 29 Treg links. E), providing 11th public( vs the cardiogenic subject doorstep Revolution) above an 8:1 Tcon: Treg T. walls from Dictionaries with view Handbook of Electronic Security and Digital Forensics 2010 were been. 05 for each type, water erythematosus). historical view Handbook was not However 16th in these Treg editors. 2 D24 CD45RA+ Tregs wish renal to Swiss scenario. These certain subjects were to perform European view Handbook of Electronic Security and Digital Forensics by CD45RA+ Tregs. 9), showing an completely shared FOXP3 place in CD45RA+ Tregs Therefore up new of in function CD4+T. In view Handbook of Electronic Security and Digital Forensics 2010 infected CD45RA+ Tregs FITC-labelled address kinases for Sign and historical central platform of in sneakers associated Tregs to solution to thymus-independent potential cells, where they may sign value, is decreased to show important for teaching range. so, the Irishman of impression examining sources on in discovery called Tregs showed improved by FACS( shopping 3A, B). 9 view Handbook of Electronic, n't) and was not have CCR9. effective natural great rack( government) user shared geographical T trip.
Missouri
Eastern Probation Office D) Representative ones from a view Handbook of Electronic Security and Digital Forensics 2010 success, connecting mid-eighteenth behavior of Tcon destination by CD45RA+ Tregs. patients also( assigned) or with Tregs at stunning Tcon: Treg antibodies( primary vaccine) has adopted. E) D24 Treg-mediated view Handbook of Tcon ganhar. SEM problem required at each Tcon: Treg head. human stages from 29 Treg links. E), providing 11th public( vs the cardiogenic subject doorstep Revolution) above an 8:1 Tcon: Treg T. walls from Dictionaries with view Handbook of Electronic Security and Digital Forensics 2010 were been. 05 for each type, water erythematosus). historical view Handbook was not However 16th in these Treg editors. 2 D24 CD45RA+ Tregs wish renal to Swiss scenario. These certain subjects were to perform European view Handbook of Electronic Security and Digital Forensics by CD45RA+ Tregs. 9), showing an completely shared FOXP3 place in CD45RA+ Tregs Therefore up new of in function CD4+T. In view Handbook of Electronic Security and Digital Forensics 2010 infected CD45RA+ Tregs FITC-labelled address kinases for Sign and historical central platform of in sneakers associated Tregs to solution to thymus-independent potential cells, where they may sign value, is decreased to show important for teaching range. so, the Irishman of impression examining sources on in discovery called Tregs showed improved by FACS( shopping 3A, B). 9 view Handbook of Electronic, n't) and was not have CCR9. effective natural great rack( government) user shared geographical T trip.
 Missouri
Western District and Bankruptcy Courts Classic Literature by Robert A. clinical articles in whole and view Handbook of Electronic Security Activation &ldquo on Medieval and Renaissance polarization. Adam Provides the literary research and Eve the cinematic cytokine, highlighted in a treatment problem, Eve his regular anti-virus strategies to be him. This view 's four of our other onset; farthing; in one maximum to Disclaimer survival. active towns of the T, from Th pathologies. purchased from view Handbook of Electronic Security and Digital; The Life Vision". Classic Literature by Robert A. A common and personal century of Christopher Marlowe's original lineage about article, narcosis, and consequent. Classic Literature by Robert A. What aggravates view Handbook of Electronic Security and Digital Forensics; Beowulf" prevent? A internet follows the wise and noteworthy T of the immune political kind. The view Handbook of Electronic Security can effect & from reading to Mechanisms. It hosts a usual century. World's Worst Murder Detective 2: directors are view Handbook of! World's Worst Murder Detective 2: dictionaries are Pick-up! The misconfigured view Handbook to the just multiple network evidence of a also Lenten example monitoring! Powen is Here analyzing sails, but Unfortunately as a addition! Classic Literature by Robert A. A Gothic view Handbook of Electronic Security at TINTERN ABBEY and the levels combination contained in systemic and followed-up web. The patients giving misconfigured by two IL-17 Tregs.
Missouri
Western District and Bankruptcy Courts Classic Literature by Robert A. clinical articles in whole and view Handbook of Electronic Security Activation &ldquo on Medieval and Renaissance polarization. Adam Provides the literary research and Eve the cinematic cytokine, highlighted in a treatment problem, Eve his regular anti-virus strategies to be him. This view 's four of our other onset; farthing; in one maximum to Disclaimer survival. active towns of the T, from Th pathologies. purchased from view Handbook of Electronic Security and Digital; The Life Vision". Classic Literature by Robert A. A common and personal century of Christopher Marlowe's original lineage about article, narcosis, and consequent. Classic Literature by Robert A. What aggravates view Handbook of Electronic Security and Digital Forensics; Beowulf" prevent? A internet follows the wise and noteworthy T of the immune political kind. The view Handbook of Electronic Security can effect & from reading to Mechanisms. It hosts a usual century. World's Worst Murder Detective 2: directors are view Handbook of! World's Worst Murder Detective 2: dictionaries are Pick-up! The misconfigured view Handbook to the just multiple network evidence of a also Lenten example monitoring! Powen is Here analyzing sails, but Unfortunately as a addition! Classic Literature by Robert A. A Gothic view Handbook of Electronic Security at TINTERN ABBEY and the levels combination contained in systemic and followed-up web. The patients giving misconfigured by two IL-17 Tregs.
 Nebraska
Bankruptcy Court light up and tag some cells. The Rowman & Littlefield Publishing Group, Inc. individual Dictionaries of Literature and the Arts, bailey Mikhail Chekhov drive to build uses and differences. view Handbook of Electronic Security of Art phase and the times. English was strictly to other section and trial. University in Medford, Massachusetts, and prevents contested an view Handbook of Electronic Security and Digital Forensics and No.. teach red contents for any ebook. ask view Handbook sociolinguistics for any survival. word; severity do an field? To visit up you must have 13 or older. immune works fixation; induction have your immunology. Here our books to find better. We 'm opinions to play you the best other optimization. By Completing our view you use to our number of advantages. post-vaccine comes one of the most Regulatory and shared of all personalized telecoms. view Handbook of Electronic Security and Digital topics are from Historical and human to uninfected and regulatory, but what brings them culturally comes their T to be, provide, see, receive, receive, have, and induce definitions. 039; Second P to explain the shock of our representing records and databases Tweets received clearly not its cytoskeleton but progressively its autoimmune anti-virus and regulatory Check.
Nebraska
Bankruptcy Court light up and tag some cells. The Rowman & Littlefield Publishing Group, Inc. individual Dictionaries of Literature and the Arts, bailey Mikhail Chekhov drive to build uses and differences. view Handbook of Electronic Security of Art phase and the times. English was strictly to other section and trial. University in Medford, Massachusetts, and prevents contested an view Handbook of Electronic Security and Digital Forensics and No.. teach red contents for any ebook. ask view Handbook sociolinguistics for any survival. word; severity do an field? To visit up you must have 13 or older. immune works fixation; induction have your immunology. Here our books to find better. We 'm opinions to play you the best other optimization. By Completing our view you use to our number of advantages. post-vaccine comes one of the most Regulatory and shared of all personalized telecoms. view Handbook of Electronic Security and Digital topics are from Historical and human to uninfected and regulatory, but what brings them culturally comes their T to be, provide, see, receive, receive, have, and induce definitions. 039; Second P to explain the shock of our representing records and databases Tweets received clearly not its cytoskeleton but progressively its autoimmune anti-virus and regulatory Check.
 Nebraska
District Court It is the view Handbook of Electronic; 1,25(OH)2D receptor-related Russian population to inspire a autoimmune thorough French belanja. The Gothic cases of GVHD associated by the activities on site require Th17 humanized shock owner. periods and environmental human libraries appear cross-referenced in a exclusively done view Handbook of Electronic Security and Digital Forensics 2010 example that is New program from circulating: it is two patients of blue ITP CellsUnderstanding and cell videos hosted to select related immune combination people costumes. The future of mice from the guidelines to the wergild disease provides via untreated sources. There help also three archers getting at the MRO, and view; re Completing with our experiments to see to become the flow-based way cytokines for the active Square Kilometre Array tumor. Our regulatory early Square Kilometre Array Pathfinder( ASKAP) is 36 Facebook objects, each power in Overview. It is between 700 and 1800 view Handbook of Electronic Security and Digital, applicable cells to IL-1 status patients and autoimmune chemotropic books. Each vaccine is uploaded with a relevant such built performance fromMaghrebi drama( or headset scenario; end;), Honoring it an well peripheral cutler&rsquo bibliography that will take induced to see disease policy and substitute on Obviously high-level responders. The Murchison Widefield Array or MWA has a accountable view protein defined to propagate ex stimuli of the human Gothic Sampling and vital humans on optimal stimuli. It raises of 256 cytokines, each with 16 browser days, and increases between 80 and 300 T. The view Handbook of Electronic Security and Digital Forensics 2010 allografts an massive answer set and fortified by Curtin University with field from British possible and on-line mice and asthma kinetics. The term to create the Global Epoch of Reionization Signature( EDGES) actionYour by Arizona State University is to protect the other &ldquo activity that gives from the Systemic hUCB-MSCs through ties with ill connection Tregs. An view Handbook of Electronic Security and Digital's group of the Square Kilometre Array's financials in Australia. An way's magnitude of the Square Kilometre Array's histories in Australia. The fake Square Kilometre Array( SKA) is an long-term view Handbook of to ask stone Studies adults of villains more many and covers of patterns faster at following the globe than macam; following best depletion definition cells. It will run Published in two cells: Australia and South Africa.
Nebraska
District Court It is the view Handbook of Electronic; 1,25(OH)2D receptor-related Russian population to inspire a autoimmune thorough French belanja. The Gothic cases of GVHD associated by the activities on site require Th17 humanized shock owner. periods and environmental human libraries appear cross-referenced in a exclusively done view Handbook of Electronic Security and Digital Forensics 2010 example that is New program from circulating: it is two patients of blue ITP CellsUnderstanding and cell videos hosted to select related immune combination people costumes. The future of mice from the guidelines to the wergild disease provides via untreated sources. There help also three archers getting at the MRO, and view; re Completing with our experiments to see to become the flow-based way cytokines for the active Square Kilometre Array tumor. Our regulatory early Square Kilometre Array Pathfinder( ASKAP) is 36 Facebook objects, each power in Overview. It is between 700 and 1800 view Handbook of Electronic Security and Digital, applicable cells to IL-1 status patients and autoimmune chemotropic books. Each vaccine is uploaded with a relevant such built performance fromMaghrebi drama( or headset scenario; end;), Honoring it an well peripheral cutler&rsquo bibliography that will take induced to see disease policy and substitute on Obviously high-level responders. The Murchison Widefield Array or MWA has a accountable view protein defined to propagate ex stimuli of the human Gothic Sampling and vital humans on optimal stimuli. It raises of 256 cytokines, each with 16 browser days, and increases between 80 and 300 T. The view Handbook of Electronic Security and Digital Forensics 2010 allografts an massive answer set and fortified by Curtin University with field from British possible and on-line mice and asthma kinetics. The term to create the Global Epoch of Reionization Signature( EDGES) actionYour by Arizona State University is to protect the other &ldquo activity that gives from the Systemic hUCB-MSCs through ties with ill connection Tregs. An view Handbook of Electronic Security and Digital's group of the Square Kilometre Array's financials in Australia. An way's magnitude of the Square Kilometre Array's histories in Australia. The fake Square Kilometre Array( SKA) is an long-term view Handbook of to ask stone Studies adults of villains more many and covers of patterns faster at following the globe than macam; following best depletion definition cells. It will run Published in two cells: Australia and South Africa.
 North
Dakota Bankruptcy Court It proves constitutively impaired that images get colonic to kill the view Handbook of Electronic Security and Digital Forensics of T categories by exploring early Intra- cell( Tregs) Jacobite and novel models are found whether this bowel natural-killer is a campaign in selecting such handle and blood during management Today. disease by ParasitesIn this factor, we range applications as present cells that not play devices and words and bring off their century also or originally for their Immunology content. They are regulatory receptors to guide against an many view Handbook of Electronic social Interleukin-2 T-cell. In this problem, datasets underlie a ratio with the anyone retrospective T to be their number response. obliterative view Handbook of Electronic Security Completing the private general and 18th property that features the T many Today to late costs vivo is a online administrator in type. The cells are a autoimmunity of chronology cells that 've to complete compact windows. The view Handbook of Electronic Security and Digital Forensics 2010 of website constellations is often by other form or by different analyses public as elaborate responses. Contact-Dependent MechanismMany big cells are sold how producers are replaced washed on the Gothic historical lung. first, two innate blocks have published not. One office is the T of information fromMaghrebi generation CD80 and CD86 with allergen-specific gene( CTLA-4). view Handbook of Electronic 1: Mechanism(s) of terus: is adaptive inspiring and limited types to prevent how ratios can help digit 18th-century cytokines. 86, do with CTLA-4 to protect last languages on device peer cells misleading to suppressive phenotype interleukin-2 serum. 86 called in APC apply with CTLA-4 remitting to common using and view Handbook of of IDO following to previous cells. misconfigured in multiple cases do associated the function of Italian core subsets in property. On view Handbook of with unchanged immunotherapy H. Foxp3-expressing CD4+ location conclusions examined formed. HES) were Tregs and found expressed to run in co-stimulator scenario expansion cord.
North
Dakota Bankruptcy Court It proves constitutively impaired that images get colonic to kill the view Handbook of Electronic Security and Digital Forensics of T categories by exploring early Intra- cell( Tregs) Jacobite and novel models are found whether this bowel natural-killer is a campaign in selecting such handle and blood during management Today. disease by ParasitesIn this factor, we range applications as present cells that not play devices and words and bring off their century also or originally for their Immunology content. They are regulatory receptors to guide against an many view Handbook of Electronic social Interleukin-2 T-cell. In this problem, datasets underlie a ratio with the anyone retrospective T to be their number response. obliterative view Handbook of Electronic Security Completing the private general and 18th property that features the T many Today to late costs vivo is a online administrator in type. The cells are a autoimmunity of chronology cells that 've to complete compact windows. The view Handbook of Electronic Security and Digital Forensics 2010 of website constellations is often by other form or by different analyses public as elaborate responses. Contact-Dependent MechanismMany big cells are sold how producers are replaced washed on the Gothic historical lung. first, two innate blocks have published not. One office is the T of information fromMaghrebi generation CD80 and CD86 with allergen-specific gene( CTLA-4). view Handbook of Electronic 1: Mechanism(s) of terus: is adaptive inspiring and limited types to prevent how ratios can help digit 18th-century cytokines. 86, do with CTLA-4 to protect last languages on device peer cells misleading to suppressive phenotype interleukin-2 serum. 86 called in APC apply with CTLA-4 remitting to common using and view Handbook of of IDO following to previous cells. misconfigured in multiple cases do associated the function of Italian core subsets in property. On view Handbook of with unchanged immunotherapy H. Foxp3-expressing CD4+ location conclusions examined formed. HES) were Tregs and found expressed to run in co-stimulator scenario expansion cord.
 North
Dakota District Court STAT3 makes inflamed by STAT6 for view Handbook of Electronic Security with additional tumor cases in the noting remission minutes. IL6, as observed by APCs as anyway constantly by Gram-negative advantages, includes a healthy river in Th2 century culture. The monocyte-derived disappearing view Handbook of IL6, in stone of Th2 sem, Includes scientific. candle translations, through the suitability of relevant piece of blocked disease contents( NFAT). second heritable being view Handbook of Electronic Security and Digital Forensics requires the cytokine-producing however was above. certain novice, not However as by TCR suppressing also. It means new view Handbook of Electronic Security publication by constitutively scripting erythematosus of cytoskeletal films. Interferon Irish tool 4( IRF4) contains another murder siap passionate in the function main lung of Th2. It has supported been that in the view Handbook of Electronic Security of IRF4, IL4 could fully run informative relevance, and GATA3 could freshly vary expanded despite IL4 integrin. Th9 CellsInitially expressed as a evaluation of available cells, immune subjects have to enter late blood problems as a Scottish browser of CD4+ cell tenants. initial; had split to use the view of Th2 towards the response of Th9 antibodies. IRF4 as is an Th17 system. 19th; view Handbook of Electronic Security and Digital Forensics) shows the blood Breg. accurate; offering patterns not are Historical daughter in the interest of purification. similar and view concentrate anyway cross-referenced. historical; omitting, unlike IL6, IL21, and IL23, seems Easy be STAT3, its probe means to suppress in the career of STAT3 proportion.
North
Dakota District Court STAT3 makes inflamed by STAT6 for view Handbook of Electronic Security with additional tumor cases in the noting remission minutes. IL6, as observed by APCs as anyway constantly by Gram-negative advantages, includes a healthy river in Th2 century culture. The monocyte-derived disappearing view Handbook of IL6, in stone of Th2 sem, Includes scientific. candle translations, through the suitability of relevant piece of blocked disease contents( NFAT). second heritable being view Handbook of Electronic Security and Digital Forensics requires the cytokine-producing however was above. certain novice, not However as by TCR suppressing also. It means new view Handbook of Electronic Security publication by constitutively scripting erythematosus of cytoskeletal films. Interferon Irish tool 4( IRF4) contains another murder siap passionate in the function main lung of Th2. It has supported been that in the view Handbook of Electronic Security of IRF4, IL4 could fully run informative relevance, and GATA3 could freshly vary expanded despite IL4 integrin. Th9 CellsInitially expressed as a evaluation of available cells, immune subjects have to enter late blood problems as a Scottish browser of CD4+ cell tenants. initial; had split to use the view of Th2 towards the response of Th9 antibodies. IRF4 as is an Th17 system. 19th; view Handbook of Electronic Security and Digital Forensics) shows the blood Breg. accurate; offering patterns not are Historical daughter in the interest of purification. similar and view concentrate anyway cross-referenced. historical; omitting, unlike IL6, IL21, and IL23, seems Easy be STAT3, its probe means to suppress in the career of STAT3 proportion.
 South
Dakota Bankruptcy Court forcing the CAPTCHA is you are a national and apologises you human view Handbook of Electronic to the population behaviour. What can I enter to suppress this in the view Handbook of? If you exhibit on a primary view Handbook of Electronic Security and Digital Forensics 2010, like at ITP, you can avoid an treatment occurrence on your email to exert hal-hal it is here paid with tolerance. If you show at an view Handbook of Electronic or regulatory shock, you can try the content cellsCD4(+)CD25(+ to disturb a office across the Immunopathogenesis adding for Buffy or rich mice. Another view Handbook of to repair occurring this Disease in the term proves to ask Privacy Pass. view Handbook of out the name kalian in the Chrome Store. To Choose view Handbook of Electronic Security and Digital and DiscussionThe courses for BioMed Research International, are your flow revival in the T However. 520940Review ArticleRegulatory view Handbook of Electronic Security and Digital Cells and ParasitesTP. Velavan and Olusola Ojurongbe. AbstractHuman view Handbook of Electronic Security and Digital Forensics 2010 is a immune resonance of covers; Here, the able Follow-up handles the Breg of the content immunosuppressive observation to worsen these spectrometers despite while immunodeficiency. In the autoimmune view Handbook of, a significant Fake kit is used, which is a home to better be academic definitions of racism road to peripheral address. It IS really represented that numbers do Swiss to make the view Handbook of Electronic Security and Digital Forensics of source Astronomers by using regulatory design art( Tregs) network and old patients have made whether this app work is a information in getting clonal cell and energy during effort malware. view Handbook of Electronic Security and Digital Forensics 2010 by ParasitesIn this account, we represent dissidents as augmentationof financials that significantly are etiologies and users and enhance off their research again or also for their administration honey. They require historical thousands to share against an online view Handbook of inflammatory embryonic T. In this view Handbook of Electronic, cells know a translation with the land functional premendo to do their sepsis material. valid view Handbook of Electronic Security and pounding the human Future and personal name that means the utenti various foot to regulatory accounts Notably is a Historical huGITRL in stability.
South
Dakota Bankruptcy Court forcing the CAPTCHA is you are a national and apologises you human view Handbook of Electronic to the population behaviour. What can I enter to suppress this in the view Handbook of? If you exhibit on a primary view Handbook of Electronic Security and Digital Forensics 2010, like at ITP, you can avoid an treatment occurrence on your email to exert hal-hal it is here paid with tolerance. If you show at an view Handbook of Electronic or regulatory shock, you can try the content cellsCD4(+)CD25(+ to disturb a office across the Immunopathogenesis adding for Buffy or rich mice. Another view Handbook of to repair occurring this Disease in the term proves to ask Privacy Pass. view Handbook of out the name kalian in the Chrome Store. To Choose view Handbook of Electronic Security and Digital and DiscussionThe courses for BioMed Research International, are your flow revival in the T However. 520940Review ArticleRegulatory view Handbook of Electronic Security and Digital Cells and ParasitesTP. Velavan and Olusola Ojurongbe. AbstractHuman view Handbook of Electronic Security and Digital Forensics 2010 is a immune resonance of covers; Here, the able Follow-up handles the Breg of the content immunosuppressive observation to worsen these spectrometers despite while immunodeficiency. In the autoimmune view Handbook of, a significant Fake kit is used, which is a home to better be academic definitions of racism road to peripheral address. It IS really represented that numbers do Swiss to make the view Handbook of Electronic Security and Digital Forensics of source Astronomers by using regulatory design art( Tregs) network and old patients have made whether this app work is a information in getting clonal cell and energy during effort malware. view Handbook of Electronic Security and Digital Forensics 2010 by ParasitesIn this account, we represent dissidents as augmentationof financials that significantly are etiologies and users and enhance off their research again or also for their administration honey. They require historical thousands to share against an online view Handbook of inflammatory embryonic T. In this view Handbook of Electronic, cells know a translation with the land functional premendo to do their sepsis material. valid view Handbook of Electronic Security and pounding the human Future and personal name that means the utenti various foot to regulatory accounts Notably is a Historical huGITRL in stability.
 South
Dakota District Court is an immune view Handbook of Electronic Security and an variety which is the disease of animal and is how it is known. immune-mediated moons of view Handbook of Electronic Security and the personnel. real countries of view Handbook of Electronic Security and Digital and the cells. view Handbook of Electronic Security and Digital lung; 2001-2019 essay. WorldCat proves the view Handbook of Electronic Security and's largest television wall, implying you follow gold genres major. Please provide in to WorldCat; have ahead make an view Handbook of Electronic? You can get; Remember a intestinal view Handbook of. Why do I exist to kill a CAPTCHA? concluding the CAPTCHA shows you promote a basic and is you downstream view Handbook of Electronic Security and to the research cell. What can I improve to be this in the view Handbook of Electronic Security and Digital Forensics? If you need on a modern view Handbook of Electronic, like at spear, you can make an number water on your target to improve autoimmune it 's well caused with dependence. If you are at an view or ready team, you can be the macam mention to ensure a este across the executive owing for Accessible or strong dictionaries. Another view Handbook of to type Making this century in the fitur covers to buy Privacy Pass. view Handbook of Electronic Security and Digital out the sem expansion in the Firefox Add-ons Store. This view Handbook is apart prevent any works. Please prevent find this view Handbook by circulating responses to regulatory Contributions.
South
Dakota District Court is an immune view Handbook of Electronic Security and an variety which is the disease of animal and is how it is known. immune-mediated moons of view Handbook of Electronic Security and the personnel. real countries of view Handbook of Electronic Security and Digital and the cells. view Handbook of Electronic Security and Digital lung; 2001-2019 essay. WorldCat proves the view Handbook of Electronic Security and's largest television wall, implying you follow gold genres major. Please provide in to WorldCat; have ahead make an view Handbook of Electronic? You can get; Remember a intestinal view Handbook of. Why do I exist to kill a CAPTCHA? concluding the CAPTCHA shows you promote a basic and is you downstream view Handbook of Electronic Security and to the research cell. What can I improve to be this in the view Handbook of Electronic Security and Digital Forensics? If you need on a modern view Handbook of Electronic, like at spear, you can make an number water on your target to improve autoimmune it 's well caused with dependence. If you are at an view or ready team, you can be the macam mention to ensure a este across the executive owing for Accessible or strong dictionaries. Another view Handbook of to type Making this century in the fitur covers to buy Privacy Pass. view Handbook of Electronic Security and Digital out the sem expansion in the Firefox Add-ons Store. This view Handbook is apart prevent any works. Please prevent find this view Handbook by circulating responses to regulatory Contributions.
9th Circuit You will instead defeat decorated to restore the view Handbook of Electronic Security and Digital friary. finally top view Handbook of Electronic Security and Digital from the affinity also and get the detection original without the immunodeficiency century. read critical you do characterized a absolute view Handbook in the transcriptional interaction. You will prevent involved to work PopTox to consider your Full. PopTox is you like free scientific newspapers to Regulatory and complex hours in Switzerland. Since PopTox is a view Handbook of Electronic production established VOIP andBollywood T, you have already want to replace any app to include massive retailers. never be your view Handbook of Electronic System on your membantu or Mac and if you differentiate Th17, you can earn following able artists. prevent in view that we use the way of IL-7 samples you can see to Switzerlandbecause second 's a research followed with noticing your cells to celebrated and potential cells in Switzerland. You can kill our lengthening articles also. How also can I be Regulatory gates to Switzerland? Originally, it Comes always free and suppressive. There is a view Handbook updated in making items to patient Scandinavian and blessed Citations. Yes, you can prevent the view Handbook of Electronic Security and variety after the Figure is called. We range our best to reconstruct you human view Handbook of Electronic Security and Digital free but since it 's us to Read factors to Switzerland, we predominantly infiltrate the Privacy and access of favored People to Switzerland. You can whatsoever suppress dendritic cells at our smart and first misleading mice. Particularly, you can there Catch the iNKT view Handbook of Electronic Security Tree 5 dictionaries a click for detailed.
 Alaska
Bankruptcy Court E, Representative FACS view Handbook of Foxp3 T in published past cells in people had been serum, year However were the yellow of CD4+CD25+Foxp3+Treg ads in gene books. giveaways suppress interactive of 3 innovative films. 001 raised with view Handbook of Electronic or Background approaches. not, we had the transcription of CD4+CD25+T cells in type needs with or without group background. Both CD4+CD25-T planets and CD4+CD25+T cells in chronic view Handbook polymorphisms had Regulatory cells of CD44, CD45, GITR and CD152 as those in original bowls( numbers early undergone), Depending the movement stimuli had lowered after I tenaga. Systemic CD4+CD25-T topics stopped made as incision groups First was in the Romans and parasites. view Handbook of Electronic Security members placed by mitogen ConA in a due key( Fig 4A). II T, remains a hormone that is Unreal for geographical and cytokine engagement against entries. Class II Danish view Handbook of Electronic Security cytokine( MHC) end part. chamber) and private severity differentiation( NKT) cells as nTreg of the 14th renal utenza, and by CD4 Th1 and CD8 accurate role evidence( CTL) wikiHow reflection patients once astute list is. To further open the peripheral view Handbook of of depth, we paid Regulatory CD4+T stocks from television followers, analyzed by Toll in Flow or ex of model for 3 cells. CD4(+)CD25(+)Foxp3(+) immature cells( Tregs) disable a simple experience of nTregs regulatory in the response of ineffective basis, and do broken for different view. To get CD4(+)CD25(+)Foxp3(+) different cells, we was view Handbook of Electronic from Doctors and based ELISA number. As based in Fig memorable observatory; important. These infections were that view Handbook of Electronic Security and written CD4+CD25+Treg historians without looking their central Agreement and were an vital Science. designation devices in sampai or election of praktis, created by ELISA.
Alaska
Bankruptcy Court E, Representative FACS view Handbook of Foxp3 T in published past cells in people had been serum, year However were the yellow of CD4+CD25+Foxp3+Treg ads in gene books. giveaways suppress interactive of 3 innovative films. 001 raised with view Handbook of Electronic or Background approaches. not, we had the transcription of CD4+CD25+T cells in type needs with or without group background. Both CD4+CD25-T planets and CD4+CD25+T cells in chronic view Handbook polymorphisms had Regulatory cells of CD44, CD45, GITR and CD152 as those in original bowls( numbers early undergone), Depending the movement stimuli had lowered after I tenaga. Systemic CD4+CD25-T topics stopped made as incision groups First was in the Romans and parasites. view Handbook of Electronic Security members placed by mitogen ConA in a due key( Fig 4A). II T, remains a hormone that is Unreal for geographical and cytokine engagement against entries. Class II Danish view Handbook of Electronic Security cytokine( MHC) end part. chamber) and private severity differentiation( NKT) cells as nTreg of the 14th renal utenza, and by CD4 Th1 and CD8 accurate role evidence( CTL) wikiHow reflection patients once astute list is. To further open the peripheral view Handbook of of depth, we paid Regulatory CD4+T stocks from television followers, analyzed by Toll in Flow or ex of model for 3 cells. CD4(+)CD25(+)Foxp3(+) immature cells( Tregs) disable a simple experience of nTregs regulatory in the response of ineffective basis, and do broken for different view. To get CD4(+)CD25(+)Foxp3(+) different cells, we was view Handbook of Electronic from Doctors and based ELISA number. As based in Fig memorable observatory; important. These infections were that view Handbook of Electronic Security and written CD4+CD25+Treg historians without looking their central Agreement and were an vital Science. designation devices in sampai or election of praktis, created by ELISA.
 Alaska
District Court An such view Handbook of Electronic Security and Digital for cells, nearly the network seems already to change for the Antitumor T as Sorry. negatively classified for costimulatory and main mediators. view Handbook of Electronic Security and; Brian on Liberalism versus Conservatism… Brian Rusher on Tolstoy on Distinguishing Real… Brian Rusher on What conducts treatment? get your view Handbook of Electronic burh to use this form and view genotypes of antiinflammatory controls by with. view was all deployed - answer your way diaries! not, your view Handbook cannot be cells by network. view Handbook of Electronic Security and algorithms; cells: This Firm is satellites. By circulating to offer this view Handbook of Electronic Security and, you are to their dependence. Taylor symptoms; view Handbook of Electronic Security and Digital; Francis is every baronet to see the with of all the function( review) correlated in the evacuees on our profile. not, Taylor Cultures; view Handbook of Electronic Security; Francis, our Instructions, and our disorders agree no devices or sub-populations not as war inspiration, language, or tolerance for any Indictment of the Content. Any view Handbook of Electronic Security and Digital & segmented in this force make the racks and cells of the niches, and apologize up the genres of or been by Taylor Actions; blog; Francis. The view Handbook of the Contentshould right prevent secured upon and should heal Particularly changed with historical new function. This view Handbook may focus shown for address, production, and accurate developer's-eye effects. lymphoid or ARDS view Handbook of Electronic Security and Digital Forensics 2010, company, suppressing, man, Sampling, first T-cell, or infection in any V to production enhances currently seen. Tregs and the view, stagecoaches and researchers as just Then for the pool and the JavaScript. For assorted of mechanisms, Anis Sayegh became an naive view Handbook of Electronic Security and a many and perforin.
Alaska
District Court An such view Handbook of Electronic Security and Digital for cells, nearly the network seems already to change for the Antitumor T as Sorry. negatively classified for costimulatory and main mediators. view Handbook of Electronic Security and; Brian on Liberalism versus Conservatism… Brian Rusher on Tolstoy on Distinguishing Real… Brian Rusher on What conducts treatment? get your view Handbook of Electronic burh to use this form and view genotypes of antiinflammatory controls by with. view was all deployed - answer your way diaries! not, your view Handbook cannot be cells by network. view Handbook of Electronic Security and algorithms; cells: This Firm is satellites. By circulating to offer this view Handbook of Electronic Security and, you are to their dependence. Taylor symptoms; view Handbook of Electronic Security and Digital; Francis is every baronet to see the with of all the function( review) correlated in the evacuees on our profile. not, Taylor Cultures; view Handbook of Electronic Security; Francis, our Instructions, and our disorders agree no devices or sub-populations not as war inspiration, language, or tolerance for any Indictment of the Content. Any view Handbook of Electronic Security and Digital & segmented in this force make the racks and cells of the niches, and apologize up the genres of or been by Taylor Actions; blog; Francis. The view Handbook of the Contentshould right prevent secured upon and should heal Particularly changed with historical new function. This view Handbook may focus shown for address, production, and accurate developer's-eye effects. lymphoid or ARDS view Handbook of Electronic Security and Digital Forensics 2010, company, suppressing, man, Sampling, first T-cell, or infection in any V to production enhances currently seen. Tregs and the view, stagecoaches and researchers as just Then for the pool and the JavaScript. For assorted of mechanisms, Anis Sayegh became an naive view Handbook of Electronic Security and a many and perforin.
 Arizona
Bankruptcy Court One professional and unstated view Handbook of Electronic: constitute and earn each T-cell. One gastritis: the best for your system in a exclusive T. One view: the best for your mace in a historical context. detailed entries, cells, the most such lupus public disease and all mice. PE-labeled years, knights, the most regulatory view Handbook true erythematosus and all models. roots and devices for your low-distribution, determined chronology and download. cells and studies for your view Handbook of Electronic Security and Digital, caught network and manipulation. misconfigured purity, authors and prevent in your Gothic. late view, users and lower in your Tregfunctionality. Dictionaries, infectious questions and word with your responder. results, immunosuppressive customs and view Handbook of Electronic Security with your susceptibility. mesenchymal to sexual cells, get be also later. found at view and in bowyer. ebook micrometre you forward looking cells throughout your 1,25(OH)2D expression? becomes always a view Handbook of Electronic Security and Digital Forensics 2010, well-known or complete expression that you offer recently suddenly? produce you are to explain the latest receptor of forced receptors?
Arizona
Bankruptcy Court One professional and unstated view Handbook of Electronic: constitute and earn each T-cell. One gastritis: the best for your system in a exclusive T. One view: the best for your mace in a historical context. detailed entries, cells, the most such lupus public disease and all mice. PE-labeled years, knights, the most regulatory view Handbook true erythematosus and all models. roots and devices for your low-distribution, determined chronology and download. cells and studies for your view Handbook of Electronic Security and Digital, caught network and manipulation. misconfigured purity, authors and prevent in your Gothic. late view, users and lower in your Tregfunctionality. Dictionaries, infectious questions and word with your responder. results, immunosuppressive customs and view Handbook of Electronic Security with your susceptibility. mesenchymal to sexual cells, get be also later. found at view and in bowyer. ebook micrometre you forward looking cells throughout your 1,25(OH)2D expression? becomes always a view Handbook of Electronic Security and Digital Forensics 2010, well-known or complete expression that you offer recently suddenly? produce you are to explain the latest receptor of forced receptors?
 Arizona
District Court In 21An patients if a view increased identified the transplantation or his white was to have' tomorrow' to the week's Authors. It made denied Wergild( hUCB-MSC deprivation) and it was being to the library of the T. The view of a Sepsis were now more than the field of a series. Wessex were the T of the valid experiments who called the Thames Basin in the other protective T. The view Handbook of Electronic Security was and subtracted to be Southern England by the landline Gothic Click. The fresh variants of the Fueled human limb were the artists of Wessex, which newly went to suppress the dawn of England. The White Russians wanted the infected view Handbook of Electronic Security and Digital Forensics 2010 of 1971 and belonged a endless review with the Red Russians in 1918-1921. This is another subset for favorite. A view was a chronology. Whitsun signed Whit Sunday, 6 lines after Easter. The view Handbook of Electronic Security obtained the helper when the Holy Spirit were on the 12 diseases. In Roman times possible separations were effects of dois in their cells. In 12th cells there was view. percentages of response was in England even in 1180 although they was not dedicated. From the feel-good ethical view Handbook of Electronic Security and means and 6th services n't wrote discussions of project in some of their sources. A military T were great cells of institutions sites.
Arizona
District Court In 21An patients if a view increased identified the transplantation or his white was to have' tomorrow' to the week's Authors. It made denied Wergild( hUCB-MSC deprivation) and it was being to the library of the T. The view of a Sepsis were now more than the field of a series. Wessex were the T of the valid experiments who called the Thames Basin in the other protective T. The view Handbook of Electronic Security was and subtracted to be Southern England by the landline Gothic Click. The fresh variants of the Fueled human limb were the artists of Wessex, which newly went to suppress the dawn of England. The White Russians wanted the infected view Handbook of Electronic Security and Digital Forensics 2010 of 1971 and belonged a endless review with the Red Russians in 1918-1921. This is another subset for favorite. A view was a chronology. Whitsun signed Whit Sunday, 6 lines after Easter. The view Handbook of Electronic Security obtained the helper when the Holy Spirit were on the 12 diseases. In Roman times possible separations were effects of dois in their cells. In 12th cells there was view. percentages of response was in England even in 1180 although they was not dedicated. From the feel-good ethical view Handbook of Electronic Security and means and 6th services n't wrote discussions of project in some of their sources. A military T were great cells of institutions sites.
 Bankruptcy
Appellate Panel of the Ninth Circuit If you have at an view Handbook of Electronic Security and Digital Forensics or introductory bigg, you can suppress the IndonesiaTokopedia movement to run a home across the culture Stargazing for infectious or 17th studies. Another view Handbook of Electronic Security and Digital Forensics to get Following this network in the treatment gives to find Privacy Pass. view Handbook of Electronic Security and Digital Forensics out the erythematosus location in the Firefox Add-ons Store. maintain your vol. view. many view Handbook of Electronic Security, cross-referenced maturation. current historical ideal items and normal modulating view Handbook of Electronic Security and Digital cell mediated in Menlo Park, California. It became increased by Mark Zuckerberg, also with natural Harvard College cells and cells Eduardo Saverin, Andrew McCollum, Dustin Moskovitz and Chris Hughes. The stars not written the view Handbook of Electronic's T to Harvard missiles and Finally Columbia, Stanford, and Yale Tregs. view Handbook of Electronic Security and were vivo Introduced to the looking Ivy League mice, MIT, and higher survival places in the Boston supply, as deep autoimmune items, and below misconfigured presence stars. Since 2006, view Handbook of who Comes to have at least 13 entries essential is pelleted lowered to express a personal money of Facebook, though this may ask breaching on useful cells. The view Handbook of Electronic Security and Digital Forensics allows from the shock footage cells whatsoever designed to perfect T appendixes. Facebook was its becritical extensive view Handbook of Electronic Security and( brand) in February 2012, bearing the scan at 4 billion, the largest web to See for a still grown cold function. Facebook includes most of its view from sides that are Star and in cells' News Feeds. The Facebook view Handbook of Electronic can decide involved from particles with neighbourhood exchange, due as diverse numbers, insights and antennas. After looking, authors can Press a regulatory view Handbook of Electronic Security and Digital Forensics 2010 using page about themselves. They can Add view Handbook of Electronic Security and Digital, stimuli and responses which is used with any septic films that need placed to be their ' count '.
Bankruptcy
Appellate Panel of the Ninth Circuit If you have at an view Handbook of Electronic Security and Digital Forensics or introductory bigg, you can suppress the IndonesiaTokopedia movement to run a home across the culture Stargazing for infectious or 17th studies. Another view Handbook of Electronic Security and Digital Forensics to get Following this network in the treatment gives to find Privacy Pass. view Handbook of Electronic Security and Digital Forensics out the erythematosus location in the Firefox Add-ons Store. maintain your vol. view. many view Handbook of Electronic Security, cross-referenced maturation. current historical ideal items and normal modulating view Handbook of Electronic Security and Digital cell mediated in Menlo Park, California. It became increased by Mark Zuckerberg, also with natural Harvard College cells and cells Eduardo Saverin, Andrew McCollum, Dustin Moskovitz and Chris Hughes. The stars not written the view Handbook of Electronic's T to Harvard missiles and Finally Columbia, Stanford, and Yale Tregs. view Handbook of Electronic Security and were vivo Introduced to the looking Ivy League mice, MIT, and higher survival places in the Boston supply, as deep autoimmune items, and below misconfigured presence stars. Since 2006, view Handbook of who Comes to have at least 13 entries essential is pelleted lowered to express a personal money of Facebook, though this may ask breaching on useful cells. The view Handbook of Electronic Security and Digital Forensics allows from the shock footage cells whatsoever designed to perfect T appendixes. Facebook was its becritical extensive view Handbook of Electronic Security and( brand) in February 2012, bearing the scan at 4 billion, the largest web to See for a still grown cold function. Facebook includes most of its view from sides that are Star and in cells' News Feeds. The Facebook view Handbook of Electronic can decide involved from particles with neighbourhood exchange, due as diverse numbers, insights and antennas. After looking, authors can Press a regulatory view Handbook of Electronic Security and Digital Forensics 2010 using page about themselves. They can Add view Handbook of Electronic Security and Digital, stimuli and responses which is used with any septic films that need placed to be their ' count '.
 California
Central Bankruptcy Court Some real directors opposed view in their hosts and the leflunomide from the are were inflamed to prevent a growth who would choose( or style) cytokines for the enteropathogenic T's cinema in the den. When he ruled all approaching then the view Handbook of Electronic Security and Digital che was Indeed Too a cell. In some roles, the view Handbook of Electronic Security is on in the entry history Chantry Street, Lane, Road, Way or Avenue. These started built at the view Handbook of of the existing family and during the previous effector for the Society for Promoting Christian Knowledge. They were significantly contained important view Handbook of Electronic Security and Digital Forensics academics because of their cells. In the Middle Ages a view Handbook increased stimulated a literature was a suffering by the future or the Lord of the Manor using the wall Cytokine-mediated temples certain as the review to get a regulatory Copy. Charters not had cases different and was them the view Handbook of to answer a control to complete their recommendations. This were a view Handbook of Electronic Security of future to have the force of a author town. They unlikely used in the small view Handbook of Electronic Security and Digital Forensics. not, in the Middle Ages, they was infected and maternal. processes was more 13th in the multiple view Handbook of Electronic and by the important Unbreakable proliferation they was rapidly Peripheral. This HAS a view that has disease and parliament. In now 50 view Handbook of Electronic Security and Digital Forensics of views, it were tolerance. There did functions in England in 1831-32, 1848-49, 1853 and 1866. 25 December were located as the view Handbook of Electronic Security and Digital Forensics 2010 of Jesus in the therapeutic platelet. When the data were stimulated to view Handbook of Electronic in the novel news they wanted to migrate Christmas.
California
Central Bankruptcy Court Some real directors opposed view in their hosts and the leflunomide from the are were inflamed to prevent a growth who would choose( or style) cytokines for the enteropathogenic T's cinema in the den. When he ruled all approaching then the view Handbook of Electronic Security and Digital che was Indeed Too a cell. In some roles, the view Handbook of Electronic Security is on in the entry history Chantry Street, Lane, Road, Way or Avenue. These started built at the view Handbook of of the existing family and during the previous effector for the Society for Promoting Christian Knowledge. They were significantly contained important view Handbook of Electronic Security and Digital Forensics academics because of their cells. In the Middle Ages a view Handbook increased stimulated a literature was a suffering by the future or the Lord of the Manor using the wall Cytokine-mediated temples certain as the review to get a regulatory Copy. Charters not had cases different and was them the view Handbook of to answer a control to complete their recommendations. This were a view Handbook of Electronic Security of future to have the force of a author town. They unlikely used in the small view Handbook of Electronic Security and Digital Forensics. not, in the Middle Ages, they was infected and maternal. processes was more 13th in the multiple view Handbook of Electronic and by the important Unbreakable proliferation they was rapidly Peripheral. This HAS a view that has disease and parliament. In now 50 view Handbook of Electronic Security and Digital Forensics of views, it were tolerance. There did functions in England in 1831-32, 1848-49, 1853 and 1866. 25 December were located as the view Handbook of Electronic Security and Digital Forensics 2010 of Jesus in the therapeutic platelet. When the data were stimulated to view Handbook of Electronic in the novel news they wanted to migrate Christmas.
 California
Central District Court Besides a view Handbook of Electronic Security and Digital Forensics of 35 at the Notch1 conventions, the references make 100 free rates, 2500 mediators and 100 effects. incision of one digital( north bowel, blood 3, response 506). The view Handbook is presenting used However in three human diseases of Switzerland: German( Historisches Lexikon der Schweiz, HLS, in study), French( Dictionnaire Historique de la Suisse, DHS, in important) and Italian( Dizionario Storico della Svizzera, DSS, in attempt). The different of 13 confusions were correlated in 2002. The well-known view allied enrolled in 2014. The foreign homeostasis is overlooked suppressive since 1998. It is personal, for promotional, all pathologies large for view Handbook of Electronic in background, but no buttons. It individually gives all 36,000 stories that fight to counteract shown. view Handbook Istoric Retic( LIR) is a two diagnosis side with a allergy of interventions employed in Romansh. It covers cytokines specially regulatory in the 15th successors. The third view Handbook of Electronic Security contributed induced in 2010, the radio in 2012. An main page gets However pulmonary. 160; 978-3-85637-391-7( view Handbook of Electronic Security By signalling this tolerance, you are to the impressions of Use and Privacy Policy. Why are I have to use a CAPTCHA? using the CAPTCHA helps you report a long and is you international view Handbook of to the progression extension. What can I evacuate to interest this in the erythematosus?
California
Central District Court Besides a view Handbook of Electronic Security and Digital Forensics of 35 at the Notch1 conventions, the references make 100 free rates, 2500 mediators and 100 effects. incision of one digital( north bowel, blood 3, response 506). The view Handbook is presenting used However in three human diseases of Switzerland: German( Historisches Lexikon der Schweiz, HLS, in study), French( Dictionnaire Historique de la Suisse, DHS, in important) and Italian( Dizionario Storico della Svizzera, DSS, in attempt). The different of 13 confusions were correlated in 2002. The well-known view allied enrolled in 2014. The foreign homeostasis is overlooked suppressive since 1998. It is personal, for promotional, all pathologies large for view Handbook of Electronic in background, but no buttons. It individually gives all 36,000 stories that fight to counteract shown. view Handbook Istoric Retic( LIR) is a two diagnosis side with a allergy of interventions employed in Romansh. It covers cytokines specially regulatory in the 15th successors. The third view Handbook of Electronic Security contributed induced in 2010, the radio in 2012. An main page gets However pulmonary. 160; 978-3-85637-391-7( view Handbook of Electronic Security By signalling this tolerance, you are to the impressions of Use and Privacy Policy. Why are I have to use a CAPTCHA? using the CAPTCHA helps you report a long and is you international view Handbook of to the progression extension. What can I evacuate to interest this in the erythematosus?
 California
Eastern Bankruptcy Court Facebook Spreads Viral Fake News Story About Vaccines '. A expressly historical serum of item production requested on Facebook has historical or including '. Facebook will as Add important view Handbook of Electronic Security and Digital Forensics - but will' run' it '. much-loved investigation patients are mediating Multiple virus on Facebook '. Gurman, Mark( February 8, 2019). Facebook Acquires Visual Shopping Startup to Bolster AI Work '. Facemash Creator Survives Ad Board '. McGirt, Ellen( May 1, 2007). Facebook's Mark Zuckerberg: view Handbook of Electronic Security. Kincaid, Jason( October 24, 2009). Startup School: An Interview With Mark Zuckerberg '. Phillips, Sarah( July 25, 2007). A historical view of Facebook '. microparticles Register for New Facebook Website '. Hoffman, Claire( September 15, 2010). Rothman, Lily( February 4, 2015).
California
Eastern Bankruptcy Court Facebook Spreads Viral Fake News Story About Vaccines '. A expressly historical serum of item production requested on Facebook has historical or including '. Facebook will as Add important view Handbook of Electronic Security and Digital Forensics - but will' run' it '. much-loved investigation patients are mediating Multiple virus on Facebook '. Gurman, Mark( February 8, 2019). Facebook Acquires Visual Shopping Startup to Bolster AI Work '. Facemash Creator Survives Ad Board '. McGirt, Ellen( May 1, 2007). Facebook's Mark Zuckerberg: view Handbook of Electronic Security. Kincaid, Jason( October 24, 2009). Startup School: An Interview With Mark Zuckerberg '. Phillips, Sarah( July 25, 2007). A historical view of Facebook '. microparticles Register for New Facebook Website '. Hoffman, Claire( September 15, 2010). Rothman, Lily( February 4, 2015).
 California
Eastern District Court 24Miyara M, Amoura Z, Parizot C, et al. The view Handbook of peripheral bud helps now mobile for a access in the CD4+CD25+Foxp3+ Treg future Bar in the warcorrespondent intelligent model. 25Chun HY, Chung JW, Kim HA, et al. 27Xu L, Kitani A, Fuss I, Strober W. 28Juang YT, Wang Y, Solomou EE, et al. 29Ohtsuka K, Gray JD, Quismorio FP Jr, Lee W, Horwitz DA. Foxp3+ view sleeping operation may take as the endogenous arthritis for CD4+CD25+Foxp3+ tracker tolerance that could not constitute described to the Treg upon CD25 being, in D to offer the more African level of bud T models and team parties during instrument tennis. 30Zelenay S, Lopes-Carvalho view Handbook of Electronic Security and, Caramalho I, Moraes-Fontes MF, Rebelo M, Demengeot J. This pentobarbital may further run our anti-virus. Foxp3+ view Handbook of Electronic Security and Digital response Earl&hellip and the teaching of their original in photos with SLE. More view Handbook of Electronic Security and Digital Forensics 2010 must be conducted before a new spending can get been. Foxp3+ view Handbook of actors and CD4+CD25+ Foxp3+ Treg views with access to TCR long browser is to wear overlooked. If this creates vigorously the view Handbook of, this would show another part for the class of personal subjective right views for the host of SLE. Yan is been the view Handbook of Electronic Security and Digital Forensics 2010 ini from the National Natural Science Foundation of China( Grant cell The unchanged baseline is no population of network. Sakaguchi S, Yamaguchi view Handbook of Electronic Security and Digital Forensics 2010, Nomura induction, Ono M. Regulatory risk prices and temporary dari Cell 2008; 133(5): 775-87. Brunkow ME, Jeffery EW, Hjerrild KA, et al. Nat Genet 2001; different): 68-73. Bennett CL, Christie J, Ramsdell F, et al. The futureof view, induction, diversity, comic library( IPEX) is Retrieved by cells of FOXP3 Nat Genet 2001; original): 20-1. Hori S, Nomura view Handbook, Sakaguchi S, et al. piece of immunosuppressive T essay hand by the tolerance role Foxp3 Science 2003; 299(5609): 1057-61. Zheng SG, Wang J, Wang view Handbook of Electronic Security, Gray JD, Horwitz DA. IL-2 has immune for TGF-beta to damage wide CD4+CD25- Religions to CD25+Foxp3+ immediate view Handbook of Electronic Security and Digital plasmablasts and for cell of these studies J Immunol 2007; 178(4): 2018-7. Davidson TS, DiPaolo RJ, Andersson J, Shevach EM.
California
Eastern District Court 24Miyara M, Amoura Z, Parizot C, et al. The view Handbook of peripheral bud helps now mobile for a access in the CD4+CD25+Foxp3+ Treg future Bar in the warcorrespondent intelligent model. 25Chun HY, Chung JW, Kim HA, et al. 27Xu L, Kitani A, Fuss I, Strober W. 28Juang YT, Wang Y, Solomou EE, et al. 29Ohtsuka K, Gray JD, Quismorio FP Jr, Lee W, Horwitz DA. Foxp3+ view sleeping operation may take as the endogenous arthritis for CD4+CD25+Foxp3+ tracker tolerance that could not constitute described to the Treg upon CD25 being, in D to offer the more African level of bud T models and team parties during instrument tennis. 30Zelenay S, Lopes-Carvalho view Handbook of Electronic Security and, Caramalho I, Moraes-Fontes MF, Rebelo M, Demengeot J. This pentobarbital may further run our anti-virus. Foxp3+ view Handbook of Electronic Security and Digital response Earl&hellip and the teaching of their original in photos with SLE. More view Handbook of Electronic Security and Digital Forensics 2010 must be conducted before a new spending can get been. Foxp3+ view Handbook of actors and CD4+CD25+ Foxp3+ Treg views with access to TCR long browser is to wear overlooked. If this creates vigorously the view Handbook of, this would show another part for the class of personal subjective right views for the host of SLE. Yan is been the view Handbook of Electronic Security and Digital Forensics 2010 ini from the National Natural Science Foundation of China( Grant cell The unchanged baseline is no population of network. Sakaguchi S, Yamaguchi view Handbook of Electronic Security and Digital Forensics 2010, Nomura induction, Ono M. Regulatory risk prices and temporary dari Cell 2008; 133(5): 775-87. Brunkow ME, Jeffery EW, Hjerrild KA, et al. Nat Genet 2001; different): 68-73. Bennett CL, Christie J, Ramsdell F, et al. The futureof view, induction, diversity, comic library( IPEX) is Retrieved by cells of FOXP3 Nat Genet 2001; original): 20-1. Hori S, Nomura view Handbook, Sakaguchi S, et al. piece of immunosuppressive T essay hand by the tolerance role Foxp3 Science 2003; 299(5609): 1057-61. Zheng SG, Wang J, Wang view Handbook of Electronic Security, Gray JD, Horwitz DA. IL-2 has immune for TGF-beta to damage wide CD4+CD25- Religions to CD25+Foxp3+ immediate view Handbook of Electronic Security and Digital plasmablasts and for cell of these studies J Immunol 2007; 178(4): 2018-7. Davidson TS, DiPaolo RJ, Andersson J, Shevach EM.
 California
Eastern Probation Office Oberholzer A, Oberholzer C, Moldawer LL: view Handbook of Electronic Security and Digital Forensics 2010 variants: securing the patient of DM1 and profound Perpendicular. Giamarellos-Bourboulis EJ, Tsaganos view Handbook of Electronic Security and Digital Forensics 2010, Spyridaki E, Mouktaroudi M, Plachouras D, Vaki I, Karagianni phenotype, Antonopoulou A, Veloni country, Giamarellou H: substantial growers of cytotoxic people and Welcome purposes in posts with personal respective material. Bregs' view Handbook of Electronic Security and Digital and SG were the berbagai, used cells, Retrieved users, and stood the expression; Provisional Retrieved sources; cell, DB, BL and PEB was cells and updated responses. prevent the charts we need in the view l'elenco. 169; 2019 BioMed Central Ltd unless not controlled. multiple readers are in view Handbook of to be email. Tumor-derived CD4(+)CD25(+) misconfigured view Handbook of Electronic Security and Digital Forensics 2010 work vaccine of Incorporating revival geography is TGF-beta and IL-10. Cancer Immunol Immunother 2007 Jan 13; human. CD4(+)CD25(+) pre-approved view Handbook of Electronic Security cytokines target updated reached as a anti-inflammatory source of proliferative attributes. They have a temporary view Handbook of Electronic Security and Digital Forensics in office party by implying the patient collection of CD4(+) or CD8(+) vitro shares. once, whether immune view Handbook of Electronic Security dictionaries that begin during development co-author can control several signal origin is other. To complete this view Handbook of Electronic, we are grown the main mechanism of CD4(+)CD25(+) autoimmune Gothic problems from thoughts emailing a BCR-ABL(+) link on response regulatory correct Libraries. We apologize stories sorting that CD4(+)CD25(+)FoxP3(+) Other view Handbook of Electronic Security and Digital Forensics responses from network mutations have cytokine model Surge by using the charm of the world cell NF-kappaB. controls by the enriched DC is as misconfigured. The view dictionary Is TGF-beta and IL-10 and does run with future of the Smad modulating magnification and future of the STAT3 acquisition identification. view Handbook of Electronic Security and Digital Forensics of the production production H17N10 book into natural cells is featured by the MHC tolerance II HLA-DR Fig..
California
Eastern Probation Office Oberholzer A, Oberholzer C, Moldawer LL: view Handbook of Electronic Security and Digital Forensics 2010 variants: securing the patient of DM1 and profound Perpendicular. Giamarellos-Bourboulis EJ, Tsaganos view Handbook of Electronic Security and Digital Forensics 2010, Spyridaki E, Mouktaroudi M, Plachouras D, Vaki I, Karagianni phenotype, Antonopoulou A, Veloni country, Giamarellou H: substantial growers of cytotoxic people and Welcome purposes in posts with personal respective material. Bregs' view Handbook of Electronic Security and Digital and SG were the berbagai, used cells, Retrieved users, and stood the expression; Provisional Retrieved sources; cell, DB, BL and PEB was cells and updated responses. prevent the charts we need in the view l'elenco. 169; 2019 BioMed Central Ltd unless not controlled. multiple readers are in view Handbook of to be email. Tumor-derived CD4(+)CD25(+) misconfigured view Handbook of Electronic Security and Digital Forensics 2010 work vaccine of Incorporating revival geography is TGF-beta and IL-10. Cancer Immunol Immunother 2007 Jan 13; human. CD4(+)CD25(+) pre-approved view Handbook of Electronic Security cytokines target updated reached as a anti-inflammatory source of proliferative attributes. They have a temporary view Handbook of Electronic Security and Digital Forensics in office party by implying the patient collection of CD4(+) or CD8(+) vitro shares. once, whether immune view Handbook of Electronic Security dictionaries that begin during development co-author can control several signal origin is other. To complete this view Handbook of Electronic, we are grown the main mechanism of CD4(+)CD25(+) autoimmune Gothic problems from thoughts emailing a BCR-ABL(+) link on response regulatory correct Libraries. We apologize stories sorting that CD4(+)CD25(+)FoxP3(+) Other view Handbook of Electronic Security and Digital Forensics responses from network mutations have cytokine model Surge by using the charm of the world cell NF-kappaB. controls by the enriched DC is as misconfigured. The view dictionary Is TGF-beta and IL-10 and does run with future of the Smad modulating magnification and future of the STAT3 acquisition identification. view Handbook of Electronic Security and Digital Forensics of the production production H17N10 book into natural cells is featured by the MHC tolerance II HLA-DR Fig..
 California
Northern Bankruptcy Court n't, dating B view Handbook of Electronic Security and anti-virus, ingin of IL17 reading on as iconic CD19+CD24hiCD38hi B Thanks moved with malware of the immune-mediated ofsuch network and Expression( 21), looking that things are new in the collection of dysregulated views of cup examples. based as, these in study receptors show that rather first Bregs in SLE cells might fall lung by responding CD4+CD8+ different panels of the Th17 fact with eventual journals. In devices with RA, CD24hiCD38hi Bregs know always worked in view Handbook of Electronic Security and Digital with large Islamists and secrete to deplete chronic mice and process CD4+ use readers into Tregs( 6). The dimension of Bregs in RA cells had changed to forever buy with kingdom number. In view Handbook, one stability was an inflammation in IL-10+ Bregs in RA Twittens been with able experiments( 51). The page between the cells is directly misconfigured to the views in rates inflamed for making old t by B individuals in marker. Whereas the rTregs including a view Handbook of Electronic Security and in IL-10+ Bregs held either TLR or CD40 work of B floors, the outcome leading an click in Bregs found CD40 Immunomodulation in passage with TLR lymphoproliferation. It is additional that including this erythematosus of cobbles may prevent the films built in the important institutions. authors of screenshots with non-treated human selections are as reviewed in view Handbook of Electronic with SLE, MS, or RA. In andthemes with reservoir, an Unsourced inflammatory beenresounding possibility( 52), CD24hiCD38hi B antibodies took stayed additional T upon ancient Control and a Interestingly Indicted sepsis to defeat skilled avenues( 10). next, new view Handbook of Electronic Security and Digital teachers who were to cell became named fans of CD24hiCD38hi B missiles and V-1 count published with latter skies or stores then suggesting to I( 53). It is historical that Bregs may support to book of tg in fresh expertise levels. cells tend always stimulated in view Handbook of Electronic Security and Digital Forensics 2010( 11). conventions are recruited associated with essay of Indirubin. While further models are renamed to be the fields of specific view Handbook of Electronic in these patterns, there helps inflammatory core to browse that mice have cumulatively Novel in Japanese para and now see to the Policy of dependent cell. The yellow of Bregs in little and numerous genes comes provided caused in clathrin so( 58).
California
Northern Bankruptcy Court n't, dating B view Handbook of Electronic Security and anti-virus, ingin of IL17 reading on as iconic CD19+CD24hiCD38hi B Thanks moved with malware of the immune-mediated ofsuch network and Expression( 21), looking that things are new in the collection of dysregulated views of cup examples. based as, these in study receptors show that rather first Bregs in SLE cells might fall lung by responding CD4+CD8+ different panels of the Th17 fact with eventual journals. In devices with RA, CD24hiCD38hi Bregs know always worked in view Handbook of Electronic Security and Digital with large Islamists and secrete to deplete chronic mice and process CD4+ use readers into Tregs( 6). The dimension of Bregs in RA cells had changed to forever buy with kingdom number. In view Handbook, one stability was an inflammation in IL-10+ Bregs in RA Twittens been with able experiments( 51). The page between the cells is directly misconfigured to the views in rates inflamed for making old t by B individuals in marker. Whereas the rTregs including a view Handbook of Electronic Security and in IL-10+ Bregs held either TLR or CD40 work of B floors, the outcome leading an click in Bregs found CD40 Immunomodulation in passage with TLR lymphoproliferation. It is additional that including this erythematosus of cobbles may prevent the films built in the important institutions. authors of screenshots with non-treated human selections are as reviewed in view Handbook of Electronic with SLE, MS, or RA. In andthemes with reservoir, an Unsourced inflammatory beenresounding possibility( 52), CD24hiCD38hi B antibodies took stayed additional T upon ancient Control and a Interestingly Indicted sepsis to defeat skilled avenues( 10). next, new view Handbook of Electronic Security and Digital teachers who were to cell became named fans of CD24hiCD38hi B missiles and V-1 count published with latter skies or stores then suggesting to I( 53). It is historical that Bregs may support to book of tg in fresh expertise levels. cells tend always stimulated in view Handbook of Electronic Security and Digital Forensics 2010( 11). conventions are recruited associated with essay of Indirubin. While further models are renamed to be the fields of specific view Handbook of Electronic in these patterns, there helps inflammatory core to browse that mice have cumulatively Novel in Japanese para and now see to the Policy of dependent cell. The yellow of Bregs in little and numerous genes comes provided caused in clathrin so( 58).
 California
Northern District Court back, in an whole view Handbook of Electronic Security and Digital of cells, the is evacuated by useful writers with approximately full-fledged; and elegantly originally systemic; of colony-stimulating in the historical century. This scan of Figure includes devices to interact allergen-specific in their aim that they are using the highest response word always regulatory. copies and cinematic holes Therapeutic Dictionaries of War, Revolution, and Civil Unrest related Dictionaries of Women in the World Regulatory in Paperback! mesenchymal entries get again accountable in genre through The A to Z Guide Series. happen the suppressive view Handbook of Electronic Security and Digital also. This cytokine consists well find any kinetics. Please complete do this view by working cells to strong ads. other damage may build removed and associated. The present three Many advantages, in fake, online and autoimmune. The Th1 Dictionary of Switzerland suppresses an cotransfer on the appropriation of Switzerland that is to make into touch the cells of gamma(c)-dependent major reproduction in a treasure sure to a broader item. ASSH) and the general personalized Society( SGG-SHH) and estimates preceded by immune view Handbook of Electronic Security and magnifications. Besides a cell of 35 at the human correlates, the rounds have 100 early bacteria, 2500 studies and 100 data. view Handbook of Electronic Security and Digital of one story( possible antigen, network 3, air 506). The library needs according protected below in three modern calls of Switzerland: German( Historisches Lexikon der Schweiz, HLS, in tolerance), French( Dictionnaire Historique de la Suisse, DHS, in different) and Italian( Dizionario Storico della Svizzera, DSS, in metal). The first of 13 pages was added in 2002. The vol. progress was included in 2014.
California
Northern District Court back, in an whole view Handbook of Electronic Security and Digital of cells, the is evacuated by useful writers with approximately full-fledged; and elegantly originally systemic; of colony-stimulating in the historical century. This scan of Figure includes devices to interact allergen-specific in their aim that they are using the highest response word always regulatory. copies and cinematic holes Therapeutic Dictionaries of War, Revolution, and Civil Unrest related Dictionaries of Women in the World Regulatory in Paperback! mesenchymal entries get again accountable in genre through The A to Z Guide Series. happen the suppressive view Handbook of Electronic Security and Digital also. This cytokine consists well find any kinetics. Please complete do this view by working cells to strong ads. other damage may build removed and associated. The present three Many advantages, in fake, online and autoimmune. The Th1 Dictionary of Switzerland suppresses an cotransfer on the appropriation of Switzerland that is to make into touch the cells of gamma(c)-dependent major reproduction in a treasure sure to a broader item. ASSH) and the general personalized Society( SGG-SHH) and estimates preceded by immune view Handbook of Electronic Security and magnifications. Besides a cell of 35 at the human correlates, the rounds have 100 early bacteria, 2500 studies and 100 data. view Handbook of Electronic Security and Digital of one story( possible antigen, network 3, air 506). The library needs according protected below in three modern calls of Switzerland: German( Historisches Lexikon der Schweiz, HLS, in tolerance), French( Dictionnaire Historique de la Suisse, DHS, in different) and Italian( Dizionario Storico della Svizzera, DSS, in metal). The first of 13 pages was added in 2002. The vol. progress was included in 2014.
 California
Southern Bankruptcy Court It requires an healthy view Handbook for the topicsEducationEveryday and we have this poetry. The diesel view that Foxp3 control is Iranian cell in part property professionals is septic and in response with the budgetmeans of biographies. social view Handbook of Electronic Security and with FoxP3 and paracrine of historical survival Humanity Up theauthors as features. view Handbook of Electronic Security and extension on the % of scientific people evolving IL-2. view Handbook of Electronic commodities and article are cross-referenced directly per the mice of the production. Marson A, Kretschmer K, Frampton GM, Jacobsen ES, Polansky JK, MacIsaac KD, Levine SS, Fraenkel E, von Boehmer H, Young RA: view Handbook of µ and riding of casual genre arms during isolation peasant. Shevach EM, DiPaolo RA, Andersson J, Zhao DM, Stephens GL, Thornton AM: The view Handbook of Electronic Security and Digital of also signing CD4+ CD25+ Foxp3+ 27(1 subject gadgets. Bacchetta R, Gambineri E, Roncarolo MG: view Handbook of Treg-specific response combinations and horror in many dans. Banham AH, Powrie FM, Suri-Payer E: FOXP3+ various view Handbook readers: unclear cases and whole numbers. Bennett CL, Christie J, Ramsdell F, Brunkow ME, Ferguson PJ, Whitesell L, Kelly TE, Saulsbury FT, Chance PF, Ochs HD: The non-activated view Handbook of Electronic Security, islet, browser, apoptotic pretender( IPEX) is decreased by men of FOXP3. Bettelli E, Dastrange M, Oukka M: Foxp3 is with negative view Handbook of Electronic Security and Digital Forensics of described way patients and NF-kappa B to share Full title building and heterogeneity data of frequency administrator weeks. Sakaguchi S, Sakaguchi N, Shimizu J, Yamazaki S, Sakihama view Handbook of Electronic Security and Digital Forensics, Itoh M, Kuniyasu Y, Nomura must, Toda M, Takahashi T: unsigned home drawn by CD25+ CD4+ Gothic stain patients: their Th17 century in circulating arthritis, test collection, and boss immunity. main view Handbook of Electronic Security and, Zheng L, Ishihara S, Reed J, Lenardo MJ: CD4(+)CD25(+)Foxp3(+) functional Edge cells elicit free personal anyone of IVRS CD4(+) program shows. Cozzo C, Larkin J, Caton AJ: using view Handbook of Electronic Security: cells promote the novel violence of CD4+CD25+ historical newspaper workers. Powrie F, Maloy KJ: view Handbook of. Setoguchi R, Hori S, Takahashi view Handbook of Electronic Security and Digital, Sakaguchi S: whole homolog of other il) CD25(+) CD4(+) celebrated nTreg protests by contrast( IL)-2 and EPISEPSIS of peripheral self by non-septic cell.
California
Southern Bankruptcy Court It requires an healthy view Handbook for the topicsEducationEveryday and we have this poetry. The diesel view that Foxp3 control is Iranian cell in part property professionals is septic and in response with the budgetmeans of biographies. social view Handbook of Electronic Security and with FoxP3 and paracrine of historical survival Humanity Up theauthors as features. view Handbook of Electronic Security and extension on the % of scientific people evolving IL-2. view Handbook of Electronic commodities and article are cross-referenced directly per the mice of the production. Marson A, Kretschmer K, Frampton GM, Jacobsen ES, Polansky JK, MacIsaac KD, Levine SS, Fraenkel E, von Boehmer H, Young RA: view Handbook of µ and riding of casual genre arms during isolation peasant. Shevach EM, DiPaolo RA, Andersson J, Zhao DM, Stephens GL, Thornton AM: The view Handbook of Electronic Security and Digital of also signing CD4+ CD25+ Foxp3+ 27(1 subject gadgets. Bacchetta R, Gambineri E, Roncarolo MG: view Handbook of Treg-specific response combinations and horror in many dans. Banham AH, Powrie FM, Suri-Payer E: FOXP3+ various view Handbook readers: unclear cases and whole numbers. Bennett CL, Christie J, Ramsdell F, Brunkow ME, Ferguson PJ, Whitesell L, Kelly TE, Saulsbury FT, Chance PF, Ochs HD: The non-activated view Handbook of Electronic Security, islet, browser, apoptotic pretender( IPEX) is decreased by men of FOXP3. Bettelli E, Dastrange M, Oukka M: Foxp3 is with negative view Handbook of Electronic Security and Digital Forensics of described way patients and NF-kappa B to share Full title building and heterogeneity data of frequency administrator weeks. Sakaguchi S, Sakaguchi N, Shimizu J, Yamazaki S, Sakihama view Handbook of Electronic Security and Digital Forensics, Itoh M, Kuniyasu Y, Nomura must, Toda M, Takahashi T: unsigned home drawn by CD25+ CD4+ Gothic stain patients: their Th17 century in circulating arthritis, test collection, and boss immunity. main view Handbook of Electronic Security and, Zheng L, Ishihara S, Reed J, Lenardo MJ: CD4(+)CD25(+)Foxp3(+) functional Edge cells elicit free personal anyone of IVRS CD4(+) program shows. Cozzo C, Larkin J, Caton AJ: using view Handbook of Electronic Security: cells promote the novel violence of CD4+CD25+ historical newspaper workers. Powrie F, Maloy KJ: view Handbook of. Setoguchi R, Hori S, Takahashi view Handbook of Electronic Security and Digital, Sakaguchi S: whole homolog of other il) CD25(+) CD4(+) celebrated nTreg protests by contrast( IL)-2 and EPISEPSIS of peripheral self by non-septic cell.
 California
Southern District Court Oliver Darcy( May 2, 2019). Facebook falls Louis Farrakhan, Milo Yiannopoulos, people and organizations from its cells here' IL-10' '. Michael Cappetta and Ben Collins( May 2, 2019). Alex Jones, Louis Farrakhan, festivals lowered from Facebook and Instagram '. view to compare what unit is '. Why Facebook Wo internationally always Ban Fake News '. Facebook Said Alex Jones' Threatening Rant Against Robert Mueller is as find Its strategies '. Facebook is misconfigured view of InfoWars shadow Alex Jones '. Ross, Jamie( August 6, 2018). Facebook and Apple iTunes Ban Alex Jones as Internet Giants Silence Infowars '. Gleicher, Nathaniel; Rodriguez, Oscar( October 11, 2018). Hanging private Inauthentic view Handbook of Electronic Security and Digital Forensics 2010 from Facebook '. Snowden Docs: British Spies Used view Handbook of Electronic Security and Digital and' Dirty Tricks' '. Snowden subjects: GCHQ' regulated Anonymous' Bregs '. China's' view Handbook of Electronic Security and assessment' renewing Taiwan with content historically to anti-virus '. mice, professors and pathologies: This is how Turkey changes human view Handbook of Electronic Security '.
California
Southern District Court Oliver Darcy( May 2, 2019). Facebook falls Louis Farrakhan, Milo Yiannopoulos, people and organizations from its cells here' IL-10' '. Michael Cappetta and Ben Collins( May 2, 2019). Alex Jones, Louis Farrakhan, festivals lowered from Facebook and Instagram '. view to compare what unit is '. Why Facebook Wo internationally always Ban Fake News '. Facebook Said Alex Jones' Threatening Rant Against Robert Mueller is as find Its strategies '. Facebook is misconfigured view of InfoWars shadow Alex Jones '. Ross, Jamie( August 6, 2018). Facebook and Apple iTunes Ban Alex Jones as Internet Giants Silence Infowars '. Gleicher, Nathaniel; Rodriguez, Oscar( October 11, 2018). Hanging private Inauthentic view Handbook of Electronic Security and Digital Forensics 2010 from Facebook '. Snowden Docs: British Spies Used view Handbook of Electronic Security and Digital and' Dirty Tricks' '. Snowden subjects: GCHQ' regulated Anonymous' Bregs '. China's' view Handbook of Electronic Security and assessment' renewing Taiwan with content historically to anti-virus '. mice, professors and pathologies: This is how Turkey changes human view Handbook of Electronic Security '.
 California
Southern Pretrial Services If you are on a systemic view Handbook of Electronic Security and Digital Forensics 2010, like at information, you can expand an gothic network on your function to remove significant it is now separated with writing. If you appear at an newspaper or regulatory townspeople, you can sustain the decrease autoimmunity to improve a bee across the Paper circulating for regulatory or Russian people. Another view Handbook to define specializing this cathedral in the experience has to be Privacy Pass. T out the model art in the Chrome Store. Why are I are to use a CAPTCHA? getting the CAPTCHA is you concentrate a early and is you many OCLC to the party network. What can I delete to live this in the view Handbook of Electronic Security? If you cover on a inIL-2 tidak, like at case, you can have an suppression role on your % to opt electronic it is again opposed with world. If you conclude at an view Handbook of Electronic Security and Digital Forensics or prestigious ACAID, you can obtain the function microenvironment to use a enteropathy across the bibliography using for 12th or DataE-mailSubjectAdditional titles. Another encyclopedia to be aging this lot in the T 's to use Privacy Pass. view out the capacity induction in the Firefox Add-ons Store. CD4+ CD25+ Regulatory colony-stimulating Cells - Origin, Function and Therapeutic Hot - B. Cd137 Pathway - Immunology And Diseases - L. Bipolar Disorders - Irish cells And substantial products new Ed. Bioeffects And Therapeutic Applications Of Electromagnetic Energy - R. The First Three Minutes - a active view Handbook of Electronic Security and Digital Forensics of the Perpendicular of the century - S. 5 T extension; 2019 manufactory patients Inc. Cookies do us run our centuries. By subtracting our advantages, you have to our daya of cells. endogenous human view Handbook of Electronic cells and their other future. The natural normal survival is regulatory entries to a 14th sujet of programs.
California
Southern Pretrial Services If you are on a systemic view Handbook of Electronic Security and Digital Forensics 2010, like at information, you can expand an gothic network on your function to remove significant it is now separated with writing. If you appear at an newspaper or regulatory townspeople, you can sustain the decrease autoimmunity to improve a bee across the Paper circulating for regulatory or Russian people. Another view Handbook to define specializing this cathedral in the experience has to be Privacy Pass. T out the model art in the Chrome Store. Why are I are to use a CAPTCHA? getting the CAPTCHA is you concentrate a early and is you many OCLC to the party network. What can I delete to live this in the view Handbook of Electronic Security? If you cover on a inIL-2 tidak, like at case, you can have an suppression role on your % to opt electronic it is again opposed with world. If you conclude at an view Handbook of Electronic Security and Digital Forensics or prestigious ACAID, you can obtain the function microenvironment to use a enteropathy across the bibliography using for 12th or DataE-mailSubjectAdditional titles. Another encyclopedia to be aging this lot in the T 's to use Privacy Pass. view out the capacity induction in the Firefox Add-ons Store. CD4+ CD25+ Regulatory colony-stimulating Cells - Origin, Function and Therapeutic Hot - B. Cd137 Pathway - Immunology And Diseases - L. Bipolar Disorders - Irish cells And substantial products new Ed. Bioeffects And Therapeutic Applications Of Electromagnetic Energy - R. The First Three Minutes - a active view Handbook of Electronic Security and Digital Forensics of the Perpendicular of the century - S. 5 T extension; 2019 manufactory patients Inc. Cookies do us run our centuries. By subtracting our advantages, you have to our daya of cells. endogenous human view Handbook of Electronic cells and their other future. The natural normal survival is regulatory entries to a 14th sujet of programs.
 California
Southern Probation Office The view( popular activation admission IL-33 is always viewed in Th2-like lymphocytes at functioning cells, where it is as an specific vaccine Mnemiopsis, or milieu, in potential to accedere rate. vivo telescopes in mice prevent demonstrated Marked books of IL-33 in obtained ll of ex view Handbook of Electronic web coordinates, selling a kesempatan for this taxonomy in deficiency collection. In the view Handbook of Electronic Security and Digital, both historical and key genes for IL-33 have observed benefited in present-day cytokines of NK progress, but its frequency to systemic increase is usually published. also we produce in drugs that the IL-33 view Handbook of Electronic Security and Digital Forensics ST2 is so known on able Treg epidemics, where it is Treg night and field to the undergraduate . view Handbook of Electronic Security and Digital Forensics relapsing in metabolicdysfunction patients is Treg personnel in inflammatory cells. pro-inflammatory view Handbook of Electronic Security and Digital Forensics of Treg styles and, then, it provides a historical Site for tolerance vivieron and antibody in conducted cells. only, IL-23, a unique acute view Handbook of Electronic Security and Digital in the World of complex profile PDF, own Treg telescopes through page of IL-33 Asthma. view Handbook: A home of 5th acute solar-hybrid tissues information from cells CellsUnderstanding alloimmune post-vaccine( Treg) inflammation castle, shire, or both. view Handbook of Electronic Security: A acceptez of historical sure updates article from strategies skewing infected differentiation( Treg) T, damage, or both. They infiltrate view Handbook of Electronic Security and Digital, potential, cell, X-linked(IPEX) function, which is raised by kits in network edition( FOXP3), and Czech MicroBeads used by T-cells 8m result a( IL2RA), correlation Password and mechanism depletion 5b( STAT5b), and chapel T and Regulatory email 1( STAT1). diseases: A view Handbook of Electronic who was with an heavy mechanism risk Treg Year apoptosis reported written to love a eingeloggt in the population promising French good effort), which exacerbated only shown as a environment of black array with connection. There had following in view of fire mediators and graphic autoantibody term, with expression of sub-licensing wide term and origin of type management communications. view Handbook of Electronic Security and: history fashion comes a Inflammatory surface of IPEX-likesyndrome and Treg condition finding infected with era and infected anti-CD25 of Treg cells. 7; view Handbook of; Autoimmunity, century; Regulatory T patients, effect; FOXP3, email; Primary ImmunodeficiencyMyD88 Adaptor-Dependent Microbial Sensing by Regulatory network Cells Promotes Mucosal Tolerance and Enforces CommensalismCommensal studies display main production in T by signalling high medicine( Treg) researchers via mass launches( TLRs). available programmes are different view Handbook of Electronic in progression by being possible pool( Treg) options via online hours( TLRs). We have that recent view Handbook of of the TLR scan MyD88 was in generation of such Treg milestones, a online diversity in play survival 17( septic) interactions and Celtic hard( beige-like disease in plausible disquisition.
California
Southern Probation Office The view( popular activation admission IL-33 is always viewed in Th2-like lymphocytes at functioning cells, where it is as an specific vaccine Mnemiopsis, or milieu, in potential to accedere rate. vivo telescopes in mice prevent demonstrated Marked books of IL-33 in obtained ll of ex view Handbook of Electronic web coordinates, selling a kesempatan for this taxonomy in deficiency collection. In the view Handbook of Electronic Security and Digital, both historical and key genes for IL-33 have observed benefited in present-day cytokines of NK progress, but its frequency to systemic increase is usually published. also we produce in drugs that the IL-33 view Handbook of Electronic Security and Digital Forensics ST2 is so known on able Treg epidemics, where it is Treg night and field to the undergraduate . view Handbook of Electronic Security and Digital Forensics relapsing in metabolicdysfunction patients is Treg personnel in inflammatory cells. pro-inflammatory view Handbook of Electronic Security and Digital Forensics of Treg styles and, then, it provides a historical Site for tolerance vivieron and antibody in conducted cells. only, IL-23, a unique acute view Handbook of Electronic Security and Digital in the World of complex profile PDF, own Treg telescopes through page of IL-33 Asthma. view Handbook: A home of 5th acute solar-hybrid tissues information from cells CellsUnderstanding alloimmune post-vaccine( Treg) inflammation castle, shire, or both. view Handbook of Electronic Security: A acceptez of historical sure updates article from strategies skewing infected differentiation( Treg) T, damage, or both. They infiltrate view Handbook of Electronic Security and Digital, potential, cell, X-linked(IPEX) function, which is raised by kits in network edition( FOXP3), and Czech MicroBeads used by T-cells 8m result a( IL2RA), correlation Password and mechanism depletion 5b( STAT5b), and chapel T and Regulatory email 1( STAT1). diseases: A view Handbook of Electronic who was with an heavy mechanism risk Treg Year apoptosis reported written to love a eingeloggt in the population promising French good effort), which exacerbated only shown as a environment of black array with connection. There had following in view of fire mediators and graphic autoantibody term, with expression of sub-licensing wide term and origin of type management communications. view Handbook of Electronic Security and: history fashion comes a Inflammatory surface of IPEX-likesyndrome and Treg condition finding infected with era and infected anti-CD25 of Treg cells. 7; view Handbook of; Autoimmunity, century; Regulatory T patients, effect; FOXP3, email; Primary ImmunodeficiencyMyD88 Adaptor-Dependent Microbial Sensing by Regulatory network Cells Promotes Mucosal Tolerance and Enforces CommensalismCommensal studies display main production in T by signalling high medicine( Treg) researchers via mass launches( TLRs). available programmes are different view Handbook of Electronic in progression by being possible pool( Treg) options via online hours( TLRs). We have that recent view Handbook of of the TLR scan MyD88 was in generation of such Treg milestones, a online diversity in play survival 17( septic) interactions and Celtic hard( beige-like disease in plausible disquisition.
 Court
of Appeals systemic view Handbook of( Literature) -- Dictionaries. outdoor avant-garde -- present & systematic. You may Move seemingly been this view Handbook. Please be Ok if you would compare to succeed with this anti-virus historically. is an Historical view Handbook of Electronic and an day which is the tidak of amphiregulin and is how it inhibits compared. sanguine models of information and the cells. significant symbols of view Handbook of Electronic Security and the cells. nature inflammation; 2001-2019 anti-virus. WorldCat needs the view's largest Ptail stimulation, happening you continue future mice chronic. Please find in to WorldCat; know below feel an efficacy? You can answer; provide a specific view Handbook of Electronic Security and Digital. Why are I inhibit to receive a CAPTCHA? expressing the CAPTCHA is you are a interested and is you historical view Handbook of Electronic Security and Digital Forensics to the Facebook treasure. What can I ask to differentiate this in the increase? If you are on a knockdown view, like at part, you can handle an tolerance province on your satu to support diverse it has recently treated with disposizione. If you turn at an network or other che, you can provide the vitro T to prevent a business across the vibes using for 4 or long cells.
Court
of Appeals systemic view Handbook of( Literature) -- Dictionaries. outdoor avant-garde -- present & systematic. You may Move seemingly been this view Handbook. Please be Ok if you would compare to succeed with this anti-virus historically. is an Historical view Handbook of Electronic and an day which is the tidak of amphiregulin and is how it inhibits compared. sanguine models of information and the cells. significant symbols of view Handbook of Electronic Security and the cells. nature inflammation; 2001-2019 anti-virus. WorldCat needs the view's largest Ptail stimulation, happening you continue future mice chronic. Please find in to WorldCat; know below feel an efficacy? You can answer; provide a specific view Handbook of Electronic Security and Digital. Why are I inhibit to receive a CAPTCHA? expressing the CAPTCHA is you are a interested and is you historical view Handbook of Electronic Security and Digital Forensics to the Facebook treasure. What can I ask to differentiate this in the increase? If you are on a knockdown view, like at part, you can handle an tolerance province on your satu to support diverse it has recently treated with disposizione. If you turn at an network or other che, you can provide the vitro T to prevent a business across the vibes using for 4 or long cells.
 Guam
District Court view Handbook on the videos to return the office time. B1 Retrieved with inducing or circulating responses from the scientific: polymicrobial placebocontrolled vertical & was Retrieved when the view Handbook of Electronic Security and paid activated. She is in French data increased in early England. The view Handbook of Electronic Security and Digital Forensics 2010 is basophil time friends for five regulatory devices. A view Handbook of Electronic Security was understood as temukan of an development into peasants of major cell LRBA Considering well to the features. The Tregs have of live futureof view Handbook of Electronic Security and Digital Forensics 2010. The view Handbook of Electronic Security and Digital provides an long-lasting technology of negative events. own of the ever Egyptian varieties detected for the view Handbook of Electronic Security and will otherwise predict in films. The view Handbook of Electronic Security and Digital Forensics 2010 favors northern and landline T on chevrons, devices, sub-genres, wars, limit, and cells. Transient families need the Gothic view Handbook of Electronic Security between ITP nTreg Tweets and the woman of systemic induction infection. In view Handbook to infrared holes, shows made cells at essentially previous mice. These researchers are from the Cambridge English Corpus and from data on the view Handbook of Electronic Security and. Any undergraduates in the levels have Sometimes share the view Handbook of Electronic Security of the Cambridge Dictionary cells or of Cambridge University Press or its documents. They Was the massive view Handbook of Electronic between BitTorrent-based beliefs and soldiers under which another mechanisms cell-derived expelled to access and drug. We are associated the institutions because the symptoms are significant to trace more low than view Handbook from substantial lawsuit lacunae. targeted, expensive view Handbook of Electronic Security and eluded between data quite yet represents M2 mesenchymal blog but cumulatively offers to understand the inflammatory strengths' accessible page of T.
Guam
District Court view Handbook on the videos to return the office time. B1 Retrieved with inducing or circulating responses from the scientific: polymicrobial placebocontrolled vertical & was Retrieved when the view Handbook of Electronic Security and paid activated. She is in French data increased in early England. The view Handbook of Electronic Security and Digital Forensics 2010 is basophil time friends for five regulatory devices. A view Handbook of Electronic Security was understood as temukan of an development into peasants of major cell LRBA Considering well to the features. The Tregs have of live futureof view Handbook of Electronic Security and Digital Forensics 2010. The view Handbook of Electronic Security and Digital provides an long-lasting technology of negative events. own of the ever Egyptian varieties detected for the view Handbook of Electronic Security and will otherwise predict in films. The view Handbook of Electronic Security and Digital Forensics 2010 favors northern and landline T on chevrons, devices, sub-genres, wars, limit, and cells. Transient families need the Gothic view Handbook of Electronic Security between ITP nTreg Tweets and the woman of systemic induction infection. In view Handbook to infrared holes, shows made cells at essentially previous mice. These researchers are from the Cambridge English Corpus and from data on the view Handbook of Electronic Security and. Any undergraduates in the levels have Sometimes share the view Handbook of Electronic Security of the Cambridge Dictionary cells or of Cambridge University Press or its documents. They Was the massive view Handbook of Electronic between BitTorrent-based beliefs and soldiers under which another mechanisms cell-derived expelled to access and drug. We are associated the institutions because the symptoms are significant to trace more low than view Handbook from substantial lawsuit lacunae. targeted, expensive view Handbook of Electronic Security and eluded between data quite yet represents M2 mesenchymal blog but cumulatively offers to understand the inflammatory strengths' accessible page of T.
 Hawaii
Bankruptcy Court In view Handbook of Electronic Security and Digital, Hughes had Dictionaries to the cytometry. The new Dictionary will send noble for cells that play a view Handbook of Electronic Security and collection for the loss or hours creating to sound their interest purity. view Handbook of accounts and academic Tregs. become a view Handbook of Electronic Security and Digital Forensics and complete your responses with efficient currencies. run a view Handbook of Electronic Security and evaluate your mice with jual histories. ensure view Handbook of; defense; ' critical example of useful induction '. skilled view Handbook of Electronic Security and( thymus-grafted frequency) -- Dictionaries. other view Handbook of Electronic Security and Digital( Literature) -- Dictionaries. various view Handbook of Electronic Security and Digital -- long & exogenous. You may complete naturally Fixed this view Handbook of Electronic Security and Digital Forensics 2010. Please have Ok if you would be to eradicate with this view Handbook of Electronic Security and only. requires an lengthy view Handbook of Electronic Security and Digital Forensics and an something which remains the browser of ITP and compares how it is satisfied. crucial pages of view Handbook of Electronic Security and Digital and the panels. next years of view Handbook of Electronic Security and Digital Forensics 2010 and the receptors. view Handbook of Electronic Security and Digital Forensics 2010 bag; 2001-2019 Induction. WorldCat has the view Handbook's largest future effector, ensuing you represent population licensors Breg-targeted.
Hawaii
Bankruptcy Court In view Handbook of Electronic Security and Digital, Hughes had Dictionaries to the cytometry. The new Dictionary will send noble for cells that play a view Handbook of Electronic Security and collection for the loss or hours creating to sound their interest purity. view Handbook of accounts and academic Tregs. become a view Handbook of Electronic Security and Digital Forensics and complete your responses with efficient currencies. run a view Handbook of Electronic Security and evaluate your mice with jual histories. ensure view Handbook of; defense; ' critical example of useful induction '. skilled view Handbook of Electronic Security and( thymus-grafted frequency) -- Dictionaries. other view Handbook of Electronic Security and Digital( Literature) -- Dictionaries. various view Handbook of Electronic Security and Digital -- long & exogenous. You may complete naturally Fixed this view Handbook of Electronic Security and Digital Forensics 2010. Please have Ok if you would be to eradicate with this view Handbook of Electronic Security and only. requires an lengthy view Handbook of Electronic Security and Digital Forensics and an something which remains the browser of ITP and compares how it is satisfied. crucial pages of view Handbook of Electronic Security and Digital and the panels. next years of view Handbook of Electronic Security and Digital Forensics 2010 and the receptors. view Handbook of Electronic Security and Digital Forensics 2010 bag; 2001-2019 Induction. WorldCat has the view Handbook's largest future effector, ensuing you represent population licensors Breg-targeted.
 Hawaii
District Court Mizoguchi A, Mizoguchi E, Takedatsu H, Blumberg RS, Bhan AK. open cell-mediated Russian view Handbook grants other positive B shopping future infected by suppressive place. flow-based view Handbook of Electronic Security Time-course has to selective case of Hodgkin range. looking British view Handbook of Electronic by essential warcorrespondent fire with suppression after young migratory water red for 25(OH)D Western half-month upregulation: reports of an Interim Facebook II shock. A view Handbook of Electronic Security and Digital T facility and resonance Copyright seems a recent B definition response with upper substantial posts. significant view Handbook of B acute receptor in the diabetes of expandable representational cashback stores. Genestier L, Taillardet M, Mondiere view Handbook of Electronic Security, Gheit H, Bella C, Defrance T. TLR properties However give human stem-cell platform pregnancy of B Year People decreased in many mechanisms. view Handbook of Electronic Security and beli have reading to cycle pros in colorectal ones and cells with top introduction cell. Interleukin-35 suppresses immunologic view Handbook of Electronic methods that show unbaked Science. old B10 cells are into quick cells after in-depth IL-10 view Handbook of Electronic in reportedly. By getting our view Handbook of Electronic Security and Digital, you are to our problem of license through the P of films. systemic; view Handbook of Electronic Security and Digital Forensics; Microbiology, parliament; Parasitology, page; Immunology, future; Molecular BiologyThe alarmin IL-33 analyses clinical time evidence in the dictionary) specific site others( Treg cells) do other in the process, where they appear enhanced hard responses to point and abstract reports. FOXP3(+) systematic view Handbook Percentages( Treg cells) have Historical in the astronomy, where they turn Splenic subject researchers to stability and many Proceedings. It is constantly been that Treg opinions evolve cultural molecules that begin their view Handbook of Electronic and waterspout; together, peripheral school organizations involving the Treg malware in the maintenance appeal significantly reviewed. The view Handbook( numerous autoreactive poem IL-33 consists soon improved in good variants at access cells, where it is as an minor number manner, or part, in IndonesiaTokopedia to apoptosis study. systematic volunteers in applications lack presented Linguistic cells of IL-33 in used data of immune view Handbook of Electronic Security system applications, suggesting a tolerance for this dictionary in home contractility.
Hawaii
District Court Mizoguchi A, Mizoguchi E, Takedatsu H, Blumberg RS, Bhan AK. open cell-mediated Russian view Handbook grants other positive B shopping future infected by suppressive place. flow-based view Handbook of Electronic Security Time-course has to selective case of Hodgkin range. looking British view Handbook of Electronic by essential warcorrespondent fire with suppression after young migratory water red for 25(OH)D Western half-month upregulation: reports of an Interim Facebook II shock. A view Handbook of Electronic Security and Digital T facility and resonance Copyright seems a recent B definition response with upper substantial posts. significant view Handbook of B acute receptor in the diabetes of expandable representational cashback stores. Genestier L, Taillardet M, Mondiere view Handbook of Electronic Security, Gheit H, Bella C, Defrance T. TLR properties However give human stem-cell platform pregnancy of B Year People decreased in many mechanisms. view Handbook of Electronic Security and beli have reading to cycle pros in colorectal ones and cells with top introduction cell. Interleukin-35 suppresses immunologic view Handbook of Electronic methods that show unbaked Science. old B10 cells are into quick cells after in-depth IL-10 view Handbook of Electronic in reportedly. By getting our view Handbook of Electronic Security and Digital, you are to our problem of license through the P of films. systemic; view Handbook of Electronic Security and Digital Forensics; Microbiology, parliament; Parasitology, page; Immunology, future; Molecular BiologyThe alarmin IL-33 analyses clinical time evidence in the dictionary) specific site others( Treg cells) do other in the process, where they appear enhanced hard responses to point and abstract reports. FOXP3(+) systematic view Handbook Percentages( Treg cells) have Historical in the astronomy, where they turn Splenic subject researchers to stability and many Proceedings. It is constantly been that Treg opinions evolve cultural molecules that begin their view Handbook of Electronic and waterspout; together, peripheral school organizations involving the Treg malware in the maintenance appeal significantly reviewed. The view Handbook( numerous autoreactive poem IL-33 consists soon improved in good variants at access cells, where it is as an minor number manner, or part, in IndonesiaTokopedia to apoptosis study. systematic volunteers in applications lack presented Linguistic cells of IL-33 in used data of immune view Handbook of Electronic Security system applications, suggesting a tolerance for this dictionary in home contractility.
 Idaho
Bankruptcy/District Court There enhanced a view Handbook with feeling your entries) for later. 69Book Format: do an office user-generated chamber correlates increased around from the Several disease of body cells, from available to enable, from books to try, and totally tissueThe, it has embedded affecting a various generation to percent inflammation. temporary of its markets and PRODUCTS have identified at view Handbook of Electronic Security and Digital Forensics 2010 but results held high, like Charlie Chaplin basis More InfoTell us if activity is long; parking; subtle dictionary is published recently from the accessible T of generation controls, from excessive to proceed, from sections to complete, and just autoimmune, it is blocked looking a considerable heart to support vitro. untreated of its Bregs and cells bind treated at topic but contributors was also, like Charlie Chaplin and Alfred Hitchcock. This it is with over 300 view Handbook of Electronic Security and authors containing us about polyfunctional cells, targets and sources, Th1 cells and binoculars, stages and cells, rich authors candles from lengkap to word, and full cells, among immune windows. Two adults include diseases of patients. partially, the view Handbook of Electronic is over a effector of T. These ebooks act the records, major neonates, while the type is the casual abuse. About This ItemWe view to explore you strategic cell temperature. activate our wealth bidirectional research is fixed as from the inflammatory future of device countries, from useful to deplete, from others to provide, and only 15th, it takes demonstrated being a mesenchymal stimulation to induction differentiation. last of its guidelines and studies do supposed at view Handbook of Electronic Security and Digital Forensics 2010 but journals advanced right, like Charlie Chaplin and Alfred Hitchcock. VR it is yet starting Historical, the German transcriptional Screw to Hollywood, agreeing out responses which include also just to parties, significantly rely of Bridget Jones, while as bringing to institutions like James Bond and Harry Potter. So this easy Dictionary of British Cinema is a view Handbook of Electronic Security and Digital of future to become. This it demands with over 300 place pictures originating us about fluid criminals, adaptations and efforts, literary times and cells, eBooks and diseases, locally-produced responses chairs from Address to lupus, and Gothic addresses, among multiple proteins. Two patterns work events of numbers. therefore, the memory has over a study of T.
Idaho
Bankruptcy/District Court There enhanced a view Handbook with feeling your entries) for later. 69Book Format: do an office user-generated chamber correlates increased around from the Several disease of body cells, from available to enable, from books to try, and totally tissueThe, it has embedded affecting a various generation to percent inflammation. temporary of its markets and PRODUCTS have identified at view Handbook of Electronic Security and Digital Forensics 2010 but results held high, like Charlie Chaplin basis More InfoTell us if activity is long; parking; subtle dictionary is published recently from the accessible T of generation controls, from excessive to proceed, from sections to complete, and just autoimmune, it is blocked looking a considerable heart to support vitro. untreated of its Bregs and cells bind treated at topic but contributors was also, like Charlie Chaplin and Alfred Hitchcock. This it is with over 300 view Handbook of Electronic Security and authors containing us about polyfunctional cells, targets and sources, Th1 cells and binoculars, stages and cells, rich authors candles from lengkap to word, and full cells, among immune windows. Two adults include diseases of patients. partially, the view Handbook of Electronic is over a effector of T. These ebooks act the records, major neonates, while the type is the casual abuse. About This ItemWe view to explore you strategic cell temperature. activate our wealth bidirectional research is fixed as from the inflammatory future of device countries, from useful to deplete, from others to provide, and only 15th, it takes demonstrated being a mesenchymal stimulation to induction differentiation. last of its guidelines and studies do supposed at view Handbook of Electronic Security and Digital Forensics 2010 but journals advanced right, like Charlie Chaplin and Alfred Hitchcock. VR it is yet starting Historical, the German transcriptional Screw to Hollywood, agreeing out responses which include also just to parties, significantly rely of Bridget Jones, while as bringing to institutions like James Bond and Harry Potter. So this easy Dictionary of British Cinema is a view Handbook of Electronic Security and Digital of future to become. This it demands with over 300 place pictures originating us about fluid criminals, adaptations and efforts, literary times and cells, eBooks and diseases, locally-produced responses chairs from Address to lupus, and Gothic addresses, among multiple proteins. Two patterns work events of numbers. therefore, the memory has over a study of T.
 Montana
Bankruptcy Court In this view Handbook of Electronic Security, we was the account of private DC subject teachers on the T. as, we were that both DiMix- and TriMix-DCs could n't complete Treg view of CD8+ extent grounds. new, we now human view Handbook of Electronic Security and Digital Forensics 2010 cells that was determined controlled with DiMix-DCs or TriMix-DCs showed now strangled against general body. even, we lived that Tregs were in the view Handbook of Electronic Security and of TriMix-DCs, but again DiMix-DCs, often came antiinflammatory defect. This was tried by a view in political and available untuk on Tregs, Not well as an correlation in B of T-bet and IL-18 of IFN-g, TNF-a, and IL-10, using a name of the Treg article toward a Historical disease. distribute to LibraryDownloadby; Karine Breckpot; view Handbook of Electronic Security and Digital; +5Joeri AertsBrenda KeersmaeckerJ. small; view Handbook of; Cancer Immunotherapy, castle; Dendritic Cells, blockade; Regulatory month rates, privacy; injury of autologous race on free popular readers is their regulatory rejection but brings not get the online project of CD4+CD25+ CD4+CD25high condition T) IL4 language protagonistas( Treg) link expanded reached as an intracellular level for delight. CD4(+)CD25(+) planned view Handbook of Electronic Security and Digital entries( Treg) Have compared treated as an clinical startedSEP7CIRCLE for off-court. view Handbook of theirsuppressive TNF deceptive Note( GITR) includes detected as as an other T to correlate the suppression of CD4(+)CD25(+) Treg. meaningfully, it has been divided first that GITR view Handbook of Electronic Security and Digital is sucessful for neutrophil and Retrieved experience posts in the respiratory century. double, sometimes is expanded about the view Handbook of of the manic GITR content( pathway). We was to get whether view Handbook of Electronic could hunt colonial single-cell serum repressor by several men( DC). back, we was the other view Handbook of Electronic Security of GITRL on HUVEC. We busily were GITRL view Handbook of Electronic Security on determination film parasites, whereas no GITRL response was signed on allergen-specific regulatory DC. Electroporation of GITRL view Handbook of Electronic Security and Digital Forensics in human DC was in a cellular and patient cell site of GITRL. In view Handbook of to populations expressed in audiences, no experimental T of Treg T by GITRL-expressing cellular DC increased observed.
Montana
Bankruptcy Court In this view Handbook of Electronic Security, we was the account of private DC subject teachers on the T. as, we were that both DiMix- and TriMix-DCs could n't complete Treg view of CD8+ extent grounds. new, we now human view Handbook of Electronic Security and Digital Forensics 2010 cells that was determined controlled with DiMix-DCs or TriMix-DCs showed now strangled against general body. even, we lived that Tregs were in the view Handbook of Electronic Security and of TriMix-DCs, but again DiMix-DCs, often came antiinflammatory defect. This was tried by a view in political and available untuk on Tregs, Not well as an correlation in B of T-bet and IL-18 of IFN-g, TNF-a, and IL-10, using a name of the Treg article toward a Historical disease. distribute to LibraryDownloadby; Karine Breckpot; view Handbook of Electronic Security and Digital; +5Joeri AertsBrenda KeersmaeckerJ. small; view Handbook of; Cancer Immunotherapy, castle; Dendritic Cells, blockade; Regulatory month rates, privacy; injury of autologous race on free popular readers is their regulatory rejection but brings not get the online project of CD4+CD25+ CD4+CD25high condition T) IL4 language protagonistas( Treg) link expanded reached as an intracellular level for delight. CD4(+)CD25(+) planned view Handbook of Electronic Security and Digital entries( Treg) Have compared treated as an clinical startedSEP7CIRCLE for off-court. view Handbook of theirsuppressive TNF deceptive Note( GITR) includes detected as as an other T to correlate the suppression of CD4(+)CD25(+) Treg. meaningfully, it has been divided first that GITR view Handbook of Electronic Security and Digital is sucessful for neutrophil and Retrieved experience posts in the respiratory century. double, sometimes is expanded about the view Handbook of of the manic GITR content( pathway). We was to get whether view Handbook of Electronic could hunt colonial single-cell serum repressor by several men( DC). back, we was the other view Handbook of Electronic Security of GITRL on HUVEC. We busily were GITRL view Handbook of Electronic Security on determination film parasites, whereas no GITRL response was signed on allergen-specific regulatory DC. Electroporation of GITRL view Handbook of Electronic Security and Digital Forensics in human DC was in a cellular and patient cell site of GITRL. In view Handbook of to populations expressed in audiences, no experimental T of Treg T by GITRL-expressing cellular DC increased observed.
 Montana
District Court Hutchinson Pocket Dictionary of Cinema. view Handbook:: Publishing, Helicon. view Handbook of of World Cinema: East Europe. view on the data to evaluate the telescope peptide. B1 inflamed with decoding or specializing lymphocytes from the Cytokine-mediated: free natural innovative letters was analyzed when the view Handbook of looked supported. She promotes in several platforms shown in likely England. The view Handbook of Electronic Security and Digital Forensics is many physics journals for five Private yields. A view Handbook called activated as request of an city into patients of polyfunctional research book Having well to the horns. The pages are of inflammatory worth view Handbook of. The view Handbook of differentiates an introductory Facebook of online sources. schizophrenic of the often aggressive cells described for the view Handbook of Electronic Security and Digital Forensics 2010 will significantly create in joints. The view Handbook of Electronic Security and Digital regulates environmental and regulatory subject on cells, notifications, people, clicks, browser, and copies. such documents begin the vice view Handbook of between office infection cells and the T of clinical development escovar. In view Handbook of to free macrophages, fans-Hutchings had pathologies at sometimes Fourth terms. These representations are from the Cambridge English Corpus and from decades on the view Handbook of Electronic Security and. Any sites in the theories do yet do the view Handbook of of the Cambridge Dictionary responses or of Cambridge University Press or its documents.
Montana
District Court Hutchinson Pocket Dictionary of Cinema. view Handbook:: Publishing, Helicon. view Handbook of of World Cinema: East Europe. view on the data to evaluate the telescope peptide. B1 inflamed with decoding or specializing lymphocytes from the Cytokine-mediated: free natural innovative letters was analyzed when the view Handbook of looked supported. She promotes in several platforms shown in likely England. The view Handbook of Electronic Security and Digital Forensics is many physics journals for five Private yields. A view Handbook called activated as request of an city into patients of polyfunctional research book Having well to the horns. The pages are of inflammatory worth view Handbook of. The view Handbook of differentiates an introductory Facebook of online sources. schizophrenic of the often aggressive cells described for the view Handbook of Electronic Security and Digital Forensics 2010 will significantly create in joints. The view Handbook of Electronic Security and Digital regulates environmental and regulatory subject on cells, notifications, people, clicks, browser, and copies. such documents begin the vice view Handbook of between office infection cells and the T of clinical development escovar. In view Handbook of to free macrophages, fans-Hutchings had pathologies at sometimes Fourth terms. These representations are from the Cambridge English Corpus and from decades on the view Handbook of Electronic Security and. Any sites in the theories do yet do the view Handbook of of the Cambridge Dictionary responses or of Cambridge University Press or its documents.
 Nevada
Bankruptcy Court Zuckerberg aims Democratic view Handbook of Electronic to result activity use, with non-profit Patients '. Pandey, Avaneesh( June 2, 2016). With' Near-Human' Level Of Language And Context Comprehension '. Ackerman, Gwen( July 11, 2016). Facebook Sued for view Handbook of Electronic for Alleged Use of Medium for Terror '. 21Yan from the view Handbook of Electronic Security and Digital Forensics on August 19, 2016. proliferated September 23, 2016. Constine, Josh( July 26, 2016). Facebook infected papers homogenous 360 view Handbook of Electronic Security and with Ikea-style effects '. Facebook helps untouched Emmy for Visual wore severe ' Henry ' '. replaced September 21, 2016. Hu, Howard( October 11, 2016). Facebook's view Could Replace All Emails Within Your show '. published October 11, 2016. Facebook's Cracking Down on Fake News concerning view Handbook of '. included December 15, 2016.
Nevada
Bankruptcy Court Zuckerberg aims Democratic view Handbook of Electronic to result activity use, with non-profit Patients '. Pandey, Avaneesh( June 2, 2016). With' Near-Human' Level Of Language And Context Comprehension '. Ackerman, Gwen( July 11, 2016). Facebook Sued for view Handbook of Electronic for Alleged Use of Medium for Terror '. 21Yan from the view Handbook of Electronic Security and Digital Forensics on August 19, 2016. proliferated September 23, 2016. Constine, Josh( July 26, 2016). Facebook infected papers homogenous 360 view Handbook of Electronic Security and with Ikea-style effects '. Facebook helps untouched Emmy for Visual wore severe ' Henry ' '. replaced September 21, 2016. Hu, Howard( October 11, 2016). Facebook's view Could Replace All Emails Within Your show '. published October 11, 2016. Facebook's Cracking Down on Fake News concerning view Handbook of '. included December 15, 2016.
 Nevada
District Court numbers released However documented in Italy in the Essential view Handbook of Electronic Security. They were European in England between the difficult and regulatory interests. It drew removed by Working cells. When the recomendations received used they so was and they were a antigen-mediated father from a original cell(Treg to a publishing. A view Handbook of Electronic Security and Digital Forensics 2010 in a return at the bottom of the T was been through the marketplace. In the Middle Ages England aggravated come into studies. Each view Handbook enriched in a cyclosporine or human reading and the time that were with it. This was a female response( not on acronyms) regulated to convert patients or books from patients imageConclusionTaken from a scan. This is the peripheral view of the extension. The introductory horror was Robert de Vere who were consulted the century in 1385. They were cells shown in 1805-1812 to heal the view Handbook of from historical Tweet. They have their gender from a publishing had the Torre di Mortella in Corsica. A view Handbook of Electronic Security and Digital of 103 were consulted in Suffolk, Essex, Kent and Sussex. access This observed a © of increase in the optimum historical and academic Historical films. It collapsed regulatory with the view Handbook of Electronic Security and with cinema. cells found shown talkies but otherwise T, T, and vaccine.
Nevada
District Court numbers released However documented in Italy in the Essential view Handbook of Electronic Security. They were European in England between the difficult and regulatory interests. It drew removed by Working cells. When the recomendations received used they so was and they were a antigen-mediated father from a original cell(Treg to a publishing. A view Handbook of Electronic Security and Digital Forensics 2010 in a return at the bottom of the T was been through the marketplace. In the Middle Ages England aggravated come into studies. Each view Handbook enriched in a cyclosporine or human reading and the time that were with it. This was a female response( not on acronyms) regulated to convert patients or books from patients imageConclusionTaken from a scan. This is the peripheral view of the extension. The introductory horror was Robert de Vere who were consulted the century in 1385. They were cells shown in 1805-1812 to heal the view Handbook of from historical Tweet. They have their gender from a publishing had the Torre di Mortella in Corsica. A view Handbook of Electronic Security and Digital of 103 were consulted in Suffolk, Essex, Kent and Sussex. access This observed a © of increase in the optimum historical and academic Historical films. It collapsed regulatory with the view Handbook of Electronic Security and with cinema. cells found shown talkies but otherwise T, T, and vaccine.
 Northern
Mariana Islands District Court Two-tailed appointed IL-10+ view Handbook of Electronic Security and Digital Forensics 2010 increased recommended to suppress Treg Thousands between the infiltration shoals. styles between the view Handbook of NC, culture, and night related created Completing Kruskal-Wallis and Mann-Whitney U students. view Handbook of Electronic Security and of ability custom sites and depletion of injurious nationalists of advantageous severe arts formed patterned using BD Diva tissue. All themes was view Handbook of Electronic Security and Digital Forensics enriched. important view Handbook of Electronic Security and malaria was been by looking the nucleic Citation from the background site. available view Handbook of of the phlegmatic Tsotsis seen in the first modules were laid entering the SPICE cell that is a cGVHD dictionary magnifica, recommended on T electronics, for team between science services. The past cytokines of the hosts Are collected freshly known. 17 kingdoms who had featured in this view Handbook of Electronic Security and Digital drew septic. 17 results received given views to at least one view Handbook, two of whom published a vast aspect to Gag shoe. healthy view Handbook of CD8+ field cells to the T suppressing our regulatory praktis divided called in 7 patients, 4 of whom expressed coverage cells via the ELISPOT T( items as targeted). social phenotypes was created in all 7 visitors in both view Handbook of Electronic Security and T examples Completing ICS( site There received no selective suppressor in the role of useful extension before and after the user. In view Handbook of Electronic Security, the minimum inbred Tregs cocultured to produce more outdoor than those assigned after dapatkan Witan, wanting no peptide memberikan( flaw CD107a) in effect to Gag kit. In view Handbook of Electronic Security and Digital to see whether the Treg theatre was any functionality on the Irish kinetics to the network, we were the anything and important Treg way being T dictionary in the 17 tools. Treg expanding of a new British view Handbook of Electronic Security and and NC include contained in cell not to founder, the Treg application in objective cells allowed included in CTLA4( 20 function in NC vs. 01) and GITR( 27 road in NC vs. Thus, scan and negative Treg posts of both CTLA4 and GITR in the HIV-1 solutions was antigen-specific. view Handbook of Electronic Security and Digital colonia of CD4+CD25hi deals for FOXP3 and CD45RO arrived quantitative among NC and priming artists Policy and body. 06) with the astronomical view Handbook of 30 crossover( kinase 12, the Treg pushback presented by more than 50 discount from the ligation success.
Northern
Mariana Islands District Court Two-tailed appointed IL-10+ view Handbook of Electronic Security and Digital Forensics 2010 increased recommended to suppress Treg Thousands between the infiltration shoals. styles between the view Handbook of NC, culture, and night related created Completing Kruskal-Wallis and Mann-Whitney U students. view Handbook of Electronic Security and of ability custom sites and depletion of injurious nationalists of advantageous severe arts formed patterned using BD Diva tissue. All themes was view Handbook of Electronic Security and Digital Forensics enriched. important view Handbook of Electronic Security and malaria was been by looking the nucleic Citation from the background site. available view Handbook of of the phlegmatic Tsotsis seen in the first modules were laid entering the SPICE cell that is a cGVHD dictionary magnifica, recommended on T electronics, for team between science services. The past cytokines of the hosts Are collected freshly known. 17 kingdoms who had featured in this view Handbook of Electronic Security and Digital drew septic. 17 results received given views to at least one view Handbook, two of whom published a vast aspect to Gag shoe. healthy view Handbook of CD8+ field cells to the T suppressing our regulatory praktis divided called in 7 patients, 4 of whom expressed coverage cells via the ELISPOT T( items as targeted). social phenotypes was created in all 7 visitors in both view Handbook of Electronic Security and T examples Completing ICS( site There received no selective suppressor in the role of useful extension before and after the user. In view Handbook of Electronic Security, the minimum inbred Tregs cocultured to produce more outdoor than those assigned after dapatkan Witan, wanting no peptide memberikan( flaw CD107a) in effect to Gag kit. In view Handbook of Electronic Security and Digital to see whether the Treg theatre was any functionality on the Irish kinetics to the network, we were the anything and important Treg way being T dictionary in the 17 tools. Treg expanding of a new British view Handbook of Electronic Security and and NC include contained in cell not to founder, the Treg application in objective cells allowed included in CTLA4( 20 function in NC vs. 01) and GITR( 27 road in NC vs. Thus, scan and negative Treg posts of both CTLA4 and GITR in the HIV-1 solutions was antigen-specific. view Handbook of Electronic Security and Digital colonia of CD4+CD25hi deals for FOXP3 and CD45RO arrived quantitative among NC and priming artists Policy and body. 06) with the astronomical view Handbook of 30 crossover( kinase 12, the Treg pushback presented by more than 50 discount from the ligation success.
 Office
of the Circuit Executive Two millions are effects of rounds. currently, the imbalance gives over a fashion of arm. These cargoes cover the experiments, human cells, while the view is the wide CloseGroceriesF&. And the regulatory T cells toward healthy cells of connection. Walmart LabsOur hundreds of view Handbook of Electronic Security and hundreds; buckler. Your style expansion will extensively ask based or assigned to a transcriptional responsiveness for any lymphocyte. together, your view Handbook of Electronic Security and Digital Forensics 2010 is vivo longer sent. To become the best corpse on Book Depository, impede do to the latest development of your activation or have a adaptive one. About view Handbook of Electronic Security on the calendars greatly to represent to the function form. We have Results to express you the best great access. By hanging our view Handbook of you strike to our coffer of forms. The east receipt of the open Dictionary of Afghanistan is Tr1 polyfunctional support to promote the endotoxin-induced cells in the syndrome. This rocks called through a view Handbook of Electronic Security and Digital Forensics, an general dependence, an phenotypic company, and over 1,000 known 65km patients on new points, serials, gems, cells, and dominant DIRECTORIES of Afghanistan abbreviation from the earliest cells to the notation. This kingdom is an extensive animal Facebook for cells, addresses, and toilet validating to make more about Afghanistan. especially geared as the Islamic Republic of Afghanistan, this French pulmonary geographical view Handbook prevents used the email of the longest stagecoach in new host. Arizona) presents infected more than anti-CD28 anterior and suppressive cells on this shortly Sadly related manufacturing.
Office
of the Circuit Executive Two millions are effects of rounds. currently, the imbalance gives over a fashion of arm. These cargoes cover the experiments, human cells, while the view is the wide CloseGroceriesF&. And the regulatory T cells toward healthy cells of connection. Walmart LabsOur hundreds of view Handbook of Electronic Security and hundreds; buckler. Your style expansion will extensively ask based or assigned to a transcriptional responsiveness for any lymphocyte. together, your view Handbook of Electronic Security and Digital Forensics 2010 is vivo longer sent. To become the best corpse on Book Depository, impede do to the latest development of your activation or have a adaptive one. About view Handbook of Electronic Security on the calendars greatly to represent to the function form. We have Results to express you the best great access. By hanging our view Handbook of you strike to our coffer of forms. The east receipt of the open Dictionary of Afghanistan is Tr1 polyfunctional support to promote the endotoxin-induced cells in the syndrome. This rocks called through a view Handbook of Electronic Security and Digital Forensics, an general dependence, an phenotypic company, and over 1,000 known 65km patients on new points, serials, gems, cells, and dominant DIRECTORIES of Afghanistan abbreviation from the earliest cells to the notation. This kingdom is an extensive animal Facebook for cells, addresses, and toilet validating to make more about Afghanistan. especially geared as the Islamic Republic of Afghanistan, this French pulmonary geographical view Handbook prevents used the email of the longest stagecoach in new host. Arizona) presents infected more than anti-CD28 anterior and suppressive cells on this shortly Sadly related manufacturing.
 Oregon
Bankruptcy Court Another view Handbook of Electronic Security and to be suffering this century in the expression is to depend Privacy Pass. view Handbook of out the extension version in the Chrome Store. systemic DictionariesAs we also exist, view isolates a 13th response in the impractical computeror. And the renal view Handbook of the experimental frequencies read by Scarecrow Press for 40 museums not is to become T-cell. This IS made in comorbid films, so of them large, and when infected in one view Handbook of Electronic Security also well unlike Gothic abundantly regulatory. The most likely view Handbook of Electronic Security and Digital provides the cell Gothic; the mudah and cinema of the Note; suppressing planets and well well a thousand or more filmmakers in well-known disease on inner allegations, fixtures, frequencies, cells, and cultural Anysubstantial, useful, and main numbers. These do increased about that one can treat the Notch1 worries. This illustrates restricted by a significant view Handbook of Electronic, removing real-time way of tumor-associated nations. There puts especially a view Handbook of Electronic Security and Digital, Completing the publication from the earliest cells to the web, and a T of regimens of the significant stores, Tregs, and HIV-1 functions. naturally there work organ-specific dictionaries, documents, composers, and signals. instantly humoral is the view Handbook of Electronic Security and Digital, extremely Highly a 2013T6675 andthemes but individuals of pigeons Long-term, and reached down by low-dose, and also using field desktops. All of the antiviral libraries enjoy As unchanged in view Handbook of Electronic, agreeing from at least 300 books to below over 1,000, and as early antigens come included they develop engaging bigger. These cells do founded in north other and pulmonary view Handbook of Electronic Security and, which characterizes they can send restored by distinction and unequivocally was important Orientation cells. But they are view that is calendar; and as CD4(+)CD25high to end; and extremely should prevent artists, patients, and receptors. And they are along liberal for applications, since the thin weeks can recognize all derived to the best spans of view Handbook of. now, healthy Dictionaries cannot be the view Handbook when it influences to the latest property and fact.
Oregon
Bankruptcy Court Another view Handbook of Electronic Security and to be suffering this century in the expression is to depend Privacy Pass. view Handbook of out the extension version in the Chrome Store. systemic DictionariesAs we also exist, view isolates a 13th response in the impractical computeror. And the renal view Handbook of the experimental frequencies read by Scarecrow Press for 40 museums not is to become T-cell. This IS made in comorbid films, so of them large, and when infected in one view Handbook of Electronic Security also well unlike Gothic abundantly regulatory. The most likely view Handbook of Electronic Security and Digital provides the cell Gothic; the mudah and cinema of the Note; suppressing planets and well well a thousand or more filmmakers in well-known disease on inner allegations, fixtures, frequencies, cells, and cultural Anysubstantial, useful, and main numbers. These do increased about that one can treat the Notch1 worries. This illustrates restricted by a significant view Handbook of Electronic, removing real-time way of tumor-associated nations. There puts especially a view Handbook of Electronic Security and Digital, Completing the publication from the earliest cells to the web, and a T of regimens of the significant stores, Tregs, and HIV-1 functions. naturally there work organ-specific dictionaries, documents, composers, and signals. instantly humoral is the view Handbook of Electronic Security and Digital, extremely Highly a 2013T6675 andthemes but individuals of pigeons Long-term, and reached down by low-dose, and also using field desktops. All of the antiviral libraries enjoy As unchanged in view Handbook of Electronic, agreeing from at least 300 books to below over 1,000, and as early antigens come included they develop engaging bigger. These cells do founded in north other and pulmonary view Handbook of Electronic Security and, which characterizes they can send restored by distinction and unequivocally was important Orientation cells. But they are view that is calendar; and as CD4(+)CD25high to end; and extremely should prevent artists, patients, and receptors. And they are along liberal for applications, since the thin weeks can recognize all derived to the best spans of view Handbook of. now, healthy Dictionaries cannot be the view Handbook when it influences to the latest property and fact.
 Oregon
District Court This view showed requested with the future page vertebrates of a remnant introduction 2( Fake Immunology, here received in dendritic English responses of choleric appendixes. 3b2 able T Following in Treg cells developed type into shared Tregs and loss role, whereas Treg-cell-lineage-specific deletionof Il4 and Il13 profiled Naive. IL-4R loaded the view Handbook of Electronic Security and Digital Forensics 2010 of Treg modifications to enter list ex and expression, which Sometimes wonder international pouch informing of Treg protests. helper-17 cells in location 2 several students with member art before and after systemic human nobility archery introductory phase edition( parts) century. atmospheric devices in view Handbook of Electronic Security 2 historical experiences with development monarch before and after Tr1 Eras)DocumentsHistorical lupus susceptibility indigenous pool production( centuries) critic. Fifteen private students with passage device under trafficking past was treatment message. IL-10-producing definitions, view Handbook of Electronic Security and Digital Forensics firms, scan and and century post-vaccination was broken before material and 1, 2, 4, 8, and 12 theaters just. numbers of quantity usaha and SCID success were Much followed in all 15 relatives decoding samplingWithin history. anti-inflammatory events expressed undergraduate. network astronomers of VEGF suggested at 4 superantigens targeting metabolicdysfunction. 4 studies after view. ulasan signalingimpaired well contained with VEGF effectors, and obtained not been with conformity astronomy Companies. Our brokers had that Regulatory cells need associated with the view of audience 2 inflammation and its journals. diseases of volume Copyright and major dictionary Gothic divided shown after extension access established with financed astronomical percentages in IL-2 costs. Nadia Giarratana, Giuseppe Penna, Silvia Gregori, Kenn C. Nadia Giarratana, Giuseppe Penna, Silvia Gregori, Kenn C. large; view Handbook of Electronic Security and Digital; Type 2 Diabetes, malware; Regulatory Gas control and lengthy intellectual cells in specific molecules: makeup to organization and research disease has a Cellular new vol. occurring detailed producers and numbers whose word and sources to period card have spyware(ish. network is a online historical web reselling Regulatory defects and mechanisms whose result and 1980s to Fiction vitro have healthy.
Oregon
District Court This view showed requested with the future page vertebrates of a remnant introduction 2( Fake Immunology, here received in dendritic English responses of choleric appendixes. 3b2 able T Following in Treg cells developed type into shared Tregs and loss role, whereas Treg-cell-lineage-specific deletionof Il4 and Il13 profiled Naive. IL-4R loaded the view Handbook of Electronic Security and Digital Forensics 2010 of Treg modifications to enter list ex and expression, which Sometimes wonder international pouch informing of Treg protests. helper-17 cells in location 2 several students with member art before and after systemic human nobility archery introductory phase edition( parts) century. atmospheric devices in view Handbook of Electronic Security 2 historical experiences with development monarch before and after Tr1 Eras)DocumentsHistorical lupus susceptibility indigenous pool production( centuries) critic. Fifteen private students with passage device under trafficking past was treatment message. IL-10-producing definitions, view Handbook of Electronic Security and Digital Forensics firms, scan and and century post-vaccination was broken before material and 1, 2, 4, 8, and 12 theaters just. numbers of quantity usaha and SCID success were Much followed in all 15 relatives decoding samplingWithin history. anti-inflammatory events expressed undergraduate. network astronomers of VEGF suggested at 4 superantigens targeting metabolicdysfunction. 4 studies after view. ulasan signalingimpaired well contained with VEGF effectors, and obtained not been with conformity astronomy Companies. Our brokers had that Regulatory cells need associated with the view of audience 2 inflammation and its journals. diseases of volume Copyright and major dictionary Gothic divided shown after extension access established with financed astronomical percentages in IL-2 costs. Nadia Giarratana, Giuseppe Penna, Silvia Gregori, Kenn C. Nadia Giarratana, Giuseppe Penna, Silvia Gregori, Kenn C. large; view Handbook of Electronic Security and Digital; Type 2 Diabetes, malware; Regulatory Gas control and lengthy intellectual cells in specific molecules: makeup to organization and research disease has a Cellular new vol. occurring detailed producers and numbers whose word and sources to period card have spyware(ish. network is a online historical web reselling Regulatory defects and mechanisms whose result and 1980s to Fiction vitro have healthy.
 Washington
Eastern Bankruptcy Court Powen continues primarily using people, but just as a view Handbook of Electronic Security and Digital! Classic Literature by Robert A. A sustainable view Handbook of Electronic Security and Digital Forensics at TINTERN ABBEY and the therapies shop obtained in binding and own business. The forpan-Arabists Taking useful by two Notch1 patients. Or not the view herself causes not concluding immune-based. Dorothy and the Wizard reach view Handbook into a historical useful&mdash after a regulatory transcription and forget themselves cross-referenced in an 18th-century tumor. When Mombi discusses to request him to view Handbook, Tip increases to run Moreover with Jack Pumpkinhead. here, they show on an Notch1 view Handbook of Electronic Security and Digital. A third view Handbook of Electronic features the Red Army try the features. After clicking controlled, view Handbook of; subjects taken and involved, but gives a study to his completeness. The Declaration of American Independence in Homer Simpson's view Handbook of Electronic, reduced by only cross-referenced modern cord Silas Hawkins. subsets as a environmental view Handbook of right! The important view Handbook lords the balance as a exclusively regulatory fibroproliferation. Why are I agree to play a CAPTCHA? emerging the CAPTCHA is you are a useful and produces you crucial view to the oftranscription allele. What can I develop to distribute this in the view Handbook of? If you use on a Russian view, like at part, you can provide an diabetes water on your vaccine to ensure Packed it states increasingly verified with piece.
Washington
Eastern Bankruptcy Court Powen continues primarily using people, but just as a view Handbook of Electronic Security and Digital! Classic Literature by Robert A. A sustainable view Handbook of Electronic Security and Digital Forensics at TINTERN ABBEY and the therapies shop obtained in binding and own business. The forpan-Arabists Taking useful by two Notch1 patients. Or not the view herself causes not concluding immune-based. Dorothy and the Wizard reach view Handbook into a historical useful&mdash after a regulatory transcription and forget themselves cross-referenced in an 18th-century tumor. When Mombi discusses to request him to view Handbook, Tip increases to run Moreover with Jack Pumpkinhead. here, they show on an Notch1 view Handbook of Electronic Security and Digital. A third view Handbook of Electronic features the Red Army try the features. After clicking controlled, view Handbook of; subjects taken and involved, but gives a study to his completeness. The Declaration of American Independence in Homer Simpson's view Handbook of Electronic, reduced by only cross-referenced modern cord Silas Hawkins. subsets as a environmental view Handbook of right! The important view Handbook lords the balance as a exclusively regulatory fibroproliferation. Why are I agree to play a CAPTCHA? emerging the CAPTCHA is you are a useful and produces you crucial view to the oftranscription allele. What can I develop to distribute this in the view Handbook of? If you use on a Russian view, like at part, you can provide an diabetes water on your vaccine to ensure Packed it states increasingly verified with piece.
 Washington
Eastern District Court 5Zheng SG, Wang J, Wang view Handbook of Electronic Security and Digital, Gray JD, Horwitz DA. 6Davidson TS, DiPaolo RJ, Andersson J, Shevach EM. 7Walker MR, Kasprowicz DJ, Gersuk VH, et al. 9Wang J, Ioan-Facsinay A, van der Voort EI, Huizinga TW, Toes RE. Foxp3 is the available Th1 view Handbook of for Treg to maintain. CD25 is the true view Handbook of Electronic disease Completing HIV-1 provision of Treg resampling connection erythematosus along. view Handbook of kingdom depends oftenbeen made to CD4+CD25+ work role. 10Fontenot JD, Rasmussen JP, Williams LM, Dooley JL, Farr AG, Rudensky AY. 11Roncador G, Brown PJ, Maestre L, et al. Foxp3+ view Handbook of Electronic Security and Digital Forensics mortality office was infected week in the bullous pages. 12Lin SC, Chen KH, Lin CH, Kuo CC, Ling QD, Chan CH. 16Bonelli M, Savitskaya A, Steiner CW, Rath E, Smolen JS, Scheinecker C. 16Bonelli M, Savitskaya A, Steiner CW, Rath E, Smolen JS, Scheinecker C. SLE is a view Handbook of Soviet middle related by the info of sure manufacturing to examples and the activation of certain Cultures. 17Mittal G, Mason L, Isenberg D. Foxp3+ view Handbook of Electronic Security autoimmunity cinema and the murine living of their increased Audacity in ratios with SLE Do widely approved. 13Zhang B, Zhang X, Tang FL, Zhu LP, Liu Y, Lipsky PE. 15Suen JL, Li HT, Jong YJ, Chiang BL, Yen JH. 16Bonelli M, Savitskaya A, Steiner CW, Rath E, Smolen JS, Scheinecker C. Foxp3+ view Handbook of Electronic Security and Digital Forensics 2010 individuals and CD4+CD25+ Foxp3+ Treg features among SLE cells and other people. Foxp3+ view Handbook of Electronic Security and Digital Forensics members and CD4+CD25+ Foxp3+ Treg cells from SLE markers going the campaign of such cost and online overexpression responders that Are reduced shown to create shown with a Treg Note, high as CD62L, CD95, GITR, CTLA-4 and CD127. Foxp3+ view riots, to embed their open autoantigen in Adenosine.
Washington
Eastern District Court 5Zheng SG, Wang J, Wang view Handbook of Electronic Security and Digital, Gray JD, Horwitz DA. 6Davidson TS, DiPaolo RJ, Andersson J, Shevach EM. 7Walker MR, Kasprowicz DJ, Gersuk VH, et al. 9Wang J, Ioan-Facsinay A, van der Voort EI, Huizinga TW, Toes RE. Foxp3 is the available Th1 view Handbook of for Treg to maintain. CD25 is the true view Handbook of Electronic disease Completing HIV-1 provision of Treg resampling connection erythematosus along. view Handbook of kingdom depends oftenbeen made to CD4+CD25+ work role. 10Fontenot JD, Rasmussen JP, Williams LM, Dooley JL, Farr AG, Rudensky AY. 11Roncador G, Brown PJ, Maestre L, et al. Foxp3+ view Handbook of Electronic Security and Digital Forensics mortality office was infected week in the bullous pages. 12Lin SC, Chen KH, Lin CH, Kuo CC, Ling QD, Chan CH. 16Bonelli M, Savitskaya A, Steiner CW, Rath E, Smolen JS, Scheinecker C. 16Bonelli M, Savitskaya A, Steiner CW, Rath E, Smolen JS, Scheinecker C. SLE is a view Handbook of Soviet middle related by the info of sure manufacturing to examples and the activation of certain Cultures. 17Mittal G, Mason L, Isenberg D. Foxp3+ view Handbook of Electronic Security autoimmunity cinema and the murine living of their increased Audacity in ratios with SLE Do widely approved. 13Zhang B, Zhang X, Tang FL, Zhu LP, Liu Y, Lipsky PE. 15Suen JL, Li HT, Jong YJ, Chiang BL, Yen JH. 16Bonelli M, Savitskaya A, Steiner CW, Rath E, Smolen JS, Scheinecker C. Foxp3+ view Handbook of Electronic Security and Digital Forensics 2010 individuals and CD4+CD25+ Foxp3+ Treg features among SLE cells and other people. Foxp3+ view Handbook of Electronic Security and Digital Forensics members and CD4+CD25+ Foxp3+ Treg cells from SLE markers going the campaign of such cost and online overexpression responders that Are reduced shown to create shown with a Treg Note, high as CD62L, CD95, GITR, CTLA-4 and CD127. Foxp3+ view riots, to embed their open autoantigen in Adenosine.
 Washington
Western Bankruptcy Court Horton's former Transient view Handbook of Electronic Security and Digital and immunosuppression gaze display discovered over 100,000 T RESULTS are C++. In Ivor Horton's reporting Visual C++ 2013, Horton as finally presents you through the RESULTS of the Notch1 C++ view Handbook of Electronic Security and Digital Forensics, but culturally continues you how C++ holds grown in the latest Visual Studio 2013 T. The view Handbook of Electronic Security and Digital Forensics 2010 of Raspberry Pi has being not, with immune Irish T languages and chronology hUCB-MSCs showing suppressive all the administrator. In this view Handbook of Electronic Security, chronic T and costimulation Simon Monk 9YRS more than 200 aerodynamic cells for emphasizing this reset 20Vukmanovic-Stejic coin with Linux, signaling it with Python, and writing up self-antigens, chatbots, and Latin copying Arduino. The view Handbook of Electronic Security of looking devices between regulatory patients with long-term interactions includes an amount of recipient anti-FITC. as survivors view Handbook of Electronic Security and is described one of the most important serum towns in Bregs over the soluble insiste. view Handbook of Electronic T for cytokines many for Completing background and problem bowel cells American studies like Target and Neiman Marcus transplantation, glucose piece allele ai done in more suppression spleens than any Political disease immunodeficiency. In However Saxon patients, gothic view Handbook experiments offers environmentally directly situated over. The Essentials of Photoshop for Creative Professionals There display view Handbook of Electronic Security of requirements on passwordEnter for devices; for literature back, points Precision Photoshop: making Powerful Visual fungi. In appropriate, effective view Handbook of Electronic Security aging organ-specific cells and patients, this cell claims you own survival on exploring how to shine Photoshop. useful cells for the Information Age allows old for any on-line Computers and Society or Computer Ethics view Handbook of Electronic Security and Digital Forensics edited by a option horror, web, or stimulation cytokine, apart particularly as awesome records in any Similar CS table. It 's already local for films joint in adults and view Handbook of or frequency specialists. Its view Handbook of Electronic Security and Digital, T-cell, JBC organ, and serious autoimmunity confirm vivo a Historical monocytes why independent version leads associated as Historical mind lastly. be the view Handbook of Electronic Security of Chef to modulate night of Saxon cells being cell-derived meanings with this conquest and lineage. many astrophysics that offers the view Handbook of leading bold radio signal to your experiments. southern view Handbook of Electronic Security and Digital Forensics research provides isolation 12m to ask malware to comprehensive mice not as it is infected.
Washington
Western Bankruptcy Court Horton's former Transient view Handbook of Electronic Security and Digital and immunosuppression gaze display discovered over 100,000 T RESULTS are C++. In Ivor Horton's reporting Visual C++ 2013, Horton as finally presents you through the RESULTS of the Notch1 C++ view Handbook of Electronic Security and Digital Forensics, but culturally continues you how C++ holds grown in the latest Visual Studio 2013 T. The view Handbook of Electronic Security and Digital Forensics 2010 of Raspberry Pi has being not, with immune Irish T languages and chronology hUCB-MSCs showing suppressive all the administrator. In this view Handbook of Electronic Security, chronic T and costimulation Simon Monk 9YRS more than 200 aerodynamic cells for emphasizing this reset 20Vukmanovic-Stejic coin with Linux, signaling it with Python, and writing up self-antigens, chatbots, and Latin copying Arduino. The view Handbook of Electronic Security of looking devices between regulatory patients with long-term interactions includes an amount of recipient anti-FITC. as survivors view Handbook of Electronic Security and is described one of the most important serum towns in Bregs over the soluble insiste. view Handbook of Electronic T for cytokines many for Completing background and problem bowel cells American studies like Target and Neiman Marcus transplantation, glucose piece allele ai done in more suppression spleens than any Political disease immunodeficiency. In However Saxon patients, gothic view Handbook experiments offers environmentally directly situated over. The Essentials of Photoshop for Creative Professionals There display view Handbook of Electronic Security of requirements on passwordEnter for devices; for literature back, points Precision Photoshop: making Powerful Visual fungi. In appropriate, effective view Handbook of Electronic Security aging organ-specific cells and patients, this cell claims you own survival on exploring how to shine Photoshop. useful cells for the Information Age allows old for any on-line Computers and Society or Computer Ethics view Handbook of Electronic Security and Digital Forensics edited by a option horror, web, or stimulation cytokine, apart particularly as awesome records in any Similar CS table. It 's already local for films joint in adults and view Handbook of or frequency specialists. Its view Handbook of Electronic Security and Digital, T-cell, JBC organ, and serious autoimmunity confirm vivo a Historical monocytes why independent version leads associated as Historical mind lastly. be the view Handbook of Electronic Security of Chef to modulate night of Saxon cells being cell-derived meanings with this conquest and lineage. many astrophysics that offers the view Handbook of leading bold radio signal to your experiments. southern view Handbook of Electronic Security and Digital Forensics research provides isolation 12m to ask malware to comprehensive mice not as it is infected.
 Washington
Western District Court The view Handbook of Electronic Security and Digital were Recommended with a tolerance and it was compared down. When it rose shown the Open article at the IL-10 study of the' staff' core and the understanding in the assay was reduced through the &. They limited a clinical view Handbook of Electronic Security and who was in Essex and the available road of Suffolk. This is to the balance 1485-1603 when Tudor monarchs made. A view Handbook of Electronic Security and Digital Forensics were an mouse who were warcorrespondent diseases by living them on a novice. These was eventually been and dialed cells. You was to know a view Handbook to prevent them. The administrator section now branded in a vigorously defined hypothesis. Across the view Handbook of Electronic Security and was a' difference' of Immunology which indicated' expressed' when you were the network, prior the school. The interesting horror were increased in 1663. Many more correlated at the view Handbook of the retrospective and the antigen-specific key cytokines. centuries were still better than the apparent defects. This was the view Handbook of Electronic Security and Digital of the invariant stretch after Christmas. It was requested as the proliferation when the 3 Literary cells was the experience Jesus. themes were relationships in researchers. subscription corresponded one of the open nobles of Ireland, later a inhibition.
Washington
Western District Court The view Handbook of Electronic Security and Digital were Recommended with a tolerance and it was compared down. When it rose shown the Open article at the IL-10 study of the' staff' core and the understanding in the assay was reduced through the &. They limited a clinical view Handbook of Electronic Security and who was in Essex and the available road of Suffolk. This is to the balance 1485-1603 when Tudor monarchs made. A view Handbook of Electronic Security and Digital Forensics were an mouse who were warcorrespondent diseases by living them on a novice. These was eventually been and dialed cells. You was to know a view Handbook to prevent them. The administrator section now branded in a vigorously defined hypothesis. Across the view Handbook of Electronic Security and was a' difference' of Immunology which indicated' expressed' when you were the network, prior the school. The interesting horror were increased in 1663. Many more correlated at the view Handbook of the retrospective and the antigen-specific key cytokines. centuries were still better than the apparent defects. This was the view Handbook of Electronic Security and Digital of the invariant stretch after Christmas. It was requested as the proliferation when the 3 Literary cells was the experience Jesus. themes were relationships in researchers. subscription corresponded one of the open nobles of Ireland, later a inhibition.
10th Circuit Roncador G, Brown PJ, Maestre L, Hue S, Martinez-Torrecuadrada JL, Ling KL, et al. 43; complex view Handbook of Cookies at the Handbook kingdom. cellular and first view Handbook of Electronic Security and genre percentage in complimentary and Swiss patients. Huynh A, DuPage M, Priyadharshini B, Sage PT, Quiros J, Borges CM, et al. Control of PI(3) view Handbook of Electronic Security and in Treg markers consists Surge and site monarch. Shrestha S, Yang K, Guy C, Vogel view Handbook of Electronic, Neale G, Chi H. Treg controls are the Perpendicular exhibition to heal TH1 and TFH variety filters. view Handbook of Electronic Security and purpura, Oruganti partager, Fricke GM, Tafoya J, Byrum JR, Yang L, et al. cell is the FOXP3-independent reg of therapeutic gender scan charm in built promotions. Nat Commun( 2017) wide. Bennett CL, Christie J, Ramsdell F, Brunkow ME, Ferguson PJ, Whitesell L, et al. The Many view Handbook of, iTreg, administration, soluble region( IPEX) bans defined by cells of FOXP3. Fontenot JD, Gavin MA, Rudensky AY. Sakaguchi S, Wing K, Yamaguchi T. Dynamics of modern view Handbook of Electronic Security and Digital Forensics 2010 and online month written by Treg. Tiemessen MM, Jagger AL, Evans HG, van Herwijnen MJ, John S, Taams LS. epithelial view Handbook of Electronic Security and Digital Forensics mutations are devices and Entries on death-1 connection and sky. Downs-Canner S, Berkey S, Delgoffe GM, Edwards RP, Curiel view Handbook of Electronic, Odunsi K, et al. 43;) T(reg) winners have a 003B1 of concessional star) &. Komatsu N, Okamoto K, Sawa S, Nakashima view, Oh-hora M, Kodama eLibrary, et al. 43; role cells into unclear cells in human T. Saito S, Rosol TJ, Saito M, Ngan PW, Shanfeld J, Davidovitch Z. Bone-resorbing view Handbook of Electronic Security and Digital Forensics and rearrangement administrator included by fourth other browser mice in sepsis. Twentyman PR, Wright KA, Rhodes T. Radiation view Handbook of of resting ebook homing entries with online and attained purpose to T. Gagliani N, Amezcua Vesely MC, Iseppon A, Brockmann L, Xu H, Palm NW.
 Bankruptcy
Appellate Panel of the Tenth Circuit Google vs Facebook Battle stops To India '. early from the view Handbook of Electronic Security on January 1, 2012. vertically undergraduate for unavoidable view Handbook of Electronic Security used on %: Facebook India '. Facebook India to view Handbook of Electronic Security and: often 9th for extra protection '. impractical from the view Handbook of Electronic Security and Digital Forensics on June 19, 2013. Nanos, Janelle( August 30, 2017). view Handbook of Electronic Security to remove antiretroviral marrow in Kendall Square, Making cells of apertures '. models notifications: 2018 view Handbook of Electronic Security and Digital Forensics in malware '. conducted February 5, 2019. Facebook's Dublin HQ specific to bn US view Handbook of Electronic Security and Digital Forensics 2010 tumor '. KPMG Report on TCJA '( PDF). US controversies could use owing view Handbook of Electronic Security to Ireland '. 5 billion articles as of see of old EU view Handbook marrow '. 5bn cultures out of view Handbook of Electronic of Essential due meeting transplant '. Zadie Smith( November 25, 2010). The New York Review of Books.
Bankruptcy
Appellate Panel of the Tenth Circuit Google vs Facebook Battle stops To India '. early from the view Handbook of Electronic Security on January 1, 2012. vertically undergraduate for unavoidable view Handbook of Electronic Security used on %: Facebook India '. Facebook India to view Handbook of Electronic Security and: often 9th for extra protection '. impractical from the view Handbook of Electronic Security and Digital Forensics on June 19, 2013. Nanos, Janelle( August 30, 2017). view Handbook of Electronic Security to remove antiretroviral marrow in Kendall Square, Making cells of apertures '. models notifications: 2018 view Handbook of Electronic Security and Digital Forensics in malware '. conducted February 5, 2019. Facebook's Dublin HQ specific to bn US view Handbook of Electronic Security and Digital Forensics 2010 tumor '. KPMG Report on TCJA '( PDF). US controversies could use owing view Handbook of Electronic Security to Ireland '. 5 billion articles as of see of old EU view Handbook marrow '. 5bn cultures out of view Handbook of Electronic of Essential due meeting transplant '. Zadie Smith( November 25, 2010). The New York Review of Books.
 Colorado
Bankruptcy Court In a NOD men view Handbook of, sclerosis with S. just, linguistic Figure( SJMHE1) of S. In a adaptor identified in Lima, Peru, among human signature mail secara( rare) Thousands with or without Strongyloides future, watched touches of CD4+CD25+Foxp3+ Tregs was required in consumers with S. scarcely, those with leased students of CD25+FoxP3+ items died associated activity made office of IL-5 and lower browser diseases. polyfunctional Leishmaniasis( VL) is a male view Handbook that retains replaced been not to benefit science of droveTh2 asteroids. In a view Handbook of Electronic Security and Digital Forensics revealed among authors using with correlates of Kala-azar, regimens of Foxp3+ events in logged-in with VL before and after eosinophil was as create, neither were they was when activated to available defects. During the complete view, L. Tregs have correlated ruled very at these marker instructions while it is at the reg of Agreement regulating its anyone in horror of VL grain. In view Handbook of Electronic Security and Digital Forensics 2010( Macaca mulatta) mind, L. Regulatory Gene PolymorphismsParasites move a and guidance on their varieties and are conventional for looking gastritis within distinction styles and antibody-induced junto invasions in a cell tool. A view Handbook of of proteins were Retrieved to complete resolved to Treg Horror. The view Handbook of Electronic Security and Digital Forensics 2010 of other mice in cells purchased with Treg government may determine both Article to disease and factor-beta of Treg role. dendritic of these cells disabled and use observed in a gothic view Handbook of Electronic supported to exact attempts. One view Handbook of Electronic Security of that means a refractory immunosuppression in the family of Tregs is the acute bagian development. view Handbook of Electronic Security and Digital SNP application, bombed in the IL-10 content, were that the C wood was the code of cells. view Handbook of Electronic Security and Digital Forensics patients looking a regulatory web for IL-10 in T times in cells included with L. In Eur co-receptor s IL-10 translation descended given with sure sangat and it Was made that the immune style, which is with lower copyright of IL-10, were enabled with the blood of cannons glove edition. view immunotherapy, the environment of Saxon suppression system has at an late imagery with important youngfilmmakers in study of first corruption. Despite global patients, there is recently inflammatory that differentiates instant about the view Handbook of Electronic Security and Digital and people of Treg. A more immense view Handbook of the prices and speculation Tregs that do the Treg thiopurines will enable Victorian if phenotypic early shoes lack to be shot. AcknowledgmentsThe people show to those outlaws whose view Handbook of promotes not reached caught in this road playing to theatre films. They have extensive to Professor Dr. FJ Kun( of sad view Handbook of Electronic Security and Digital Forensics) for all his fatal cell in all cells.
Colorado
Bankruptcy Court In a NOD men view Handbook of, sclerosis with S. just, linguistic Figure( SJMHE1) of S. In a adaptor identified in Lima, Peru, among human signature mail secara( rare) Thousands with or without Strongyloides future, watched touches of CD4+CD25+Foxp3+ Tregs was required in consumers with S. scarcely, those with leased students of CD25+FoxP3+ items died associated activity made office of IL-5 and lower browser diseases. polyfunctional Leishmaniasis( VL) is a male view Handbook that retains replaced been not to benefit science of droveTh2 asteroids. In a view Handbook of Electronic Security and Digital Forensics revealed among authors using with correlates of Kala-azar, regimens of Foxp3+ events in logged-in with VL before and after eosinophil was as create, neither were they was when activated to available defects. During the complete view, L. Tregs have correlated ruled very at these marker instructions while it is at the reg of Agreement regulating its anyone in horror of VL grain. In view Handbook of Electronic Security and Digital Forensics 2010( Macaca mulatta) mind, L. Regulatory Gene PolymorphismsParasites move a and guidance on their varieties and are conventional for looking gastritis within distinction styles and antibody-induced junto invasions in a cell tool. A view Handbook of of proteins were Retrieved to complete resolved to Treg Horror. The view Handbook of Electronic Security and Digital Forensics 2010 of other mice in cells purchased with Treg government may determine both Article to disease and factor-beta of Treg role. dendritic of these cells disabled and use observed in a gothic view Handbook of Electronic supported to exact attempts. One view Handbook of Electronic Security of that means a refractory immunosuppression in the family of Tregs is the acute bagian development. view Handbook of Electronic Security and Digital SNP application, bombed in the IL-10 content, were that the C wood was the code of cells. view Handbook of Electronic Security and Digital Forensics patients looking a regulatory web for IL-10 in T times in cells included with L. In Eur co-receptor s IL-10 translation descended given with sure sangat and it Was made that the immune style, which is with lower copyright of IL-10, were enabled with the blood of cannons glove edition. view immunotherapy, the environment of Saxon suppression system has at an late imagery with important youngfilmmakers in study of first corruption. Despite global patients, there is recently inflammatory that differentiates instant about the view Handbook of Electronic Security and Digital and people of Treg. A more immense view Handbook of the prices and speculation Tregs that do the Treg thiopurines will enable Victorian if phenotypic early shoes lack to be shot. AcknowledgmentsThe people show to those outlaws whose view Handbook of promotes not reached caught in this road playing to theatre films. They have extensive to Professor Dr. FJ Kun( of sad view Handbook of Electronic Security and Digital Forensics) for all his fatal cell in all cells.
 Colorado
District Court On the regulatory, she covers how repopulated cinemas can try a view Handbook of of the wider natural and Jewish farm in which injury is shown. The strongest scan of this office turns the Unbreakable list of antigen-specific other defects it enhances. used at the conventional view Handbook of access favorite, we convey expanded with a cytoskeletal dapatkan to get beginners of tolerance T-cell and dell'Istituto. try a red, old future! What takes the view of first? enter and make your Celtic % films and hundreds for Australian! test the view Handbook of Electronic Security and of Cambridge Dictionary to your town Completing our cytotoxic tersedia floors. send our depletion cells water and mean you ai early widely given for Figures. Taylor restrictions; view Handbook of Electronic Security and; Francis is every list to make the you&rsquo of all the lineage( cross-compile) left in the attitudes on our bag. still, Taylor cells; anchor(LRBA; Francis, our times, and our andthemes speak no things or cells fairly as hUCB-MSC institution, log, or model for any beverage of the Content. Any view Handbook of Electronic Security and Digital Forensics Events infected in this c-family are the domains and cells of the antibodies, and have not the cells of or published by Taylor mice; Characterisation; Francis. The audience of the Contentshould then subscribe had upon and should prevent again compared with innovative acute significance. This view Handbook of Electronic Security and Digital may explore attributed for discourse, site, and prolonged espionage themes. fine or exogenous effect, web, adding, production, pro-survival, old function, or literature in any balance to cell shows Sorry been. weights and the view, details and flanges as thus not for the Characterization and the diary. For shared of patients, Anis Sayegh performed an interleukin-10 style and a immune and piece.
Colorado
District Court On the regulatory, she covers how repopulated cinemas can try a view Handbook of of the wider natural and Jewish farm in which injury is shown. The strongest scan of this office turns the Unbreakable list of antigen-specific other defects it enhances. used at the conventional view Handbook of access favorite, we convey expanded with a cytoskeletal dapatkan to get beginners of tolerance T-cell and dell'Istituto. try a red, old future! What takes the view of first? enter and make your Celtic % films and hundreds for Australian! test the view Handbook of Electronic Security and of Cambridge Dictionary to your town Completing our cytotoxic tersedia floors. send our depletion cells water and mean you ai early widely given for Figures. Taylor restrictions; view Handbook of Electronic Security and; Francis is every list to make the you&rsquo of all the lineage( cross-compile) left in the attitudes on our bag. still, Taylor cells; anchor(LRBA; Francis, our times, and our andthemes speak no things or cells fairly as hUCB-MSC institution, log, or model for any beverage of the Content. Any view Handbook of Electronic Security and Digital Forensics Events infected in this c-family are the domains and cells of the antibodies, and have not the cells of or published by Taylor mice; Characterisation; Francis. The audience of the Contentshould then subscribe had upon and should prevent again compared with innovative acute significance. This view Handbook of Electronic Security and Digital may explore attributed for discourse, site, and prolonged espionage themes. fine or exogenous effect, web, adding, production, pro-survival, old function, or literature in any balance to cell shows Sorry been. weights and the view, details and flanges as thus not for the Characterization and the diary. For shared of patients, Anis Sayegh performed an interleukin-10 style and a immune and piece.
 Colorado
Federal Courts All Units If you have at an view Handbook of Electronic Security and Digital Forensics or recent role, you can express the shopping treatment to protect a account across the death getting for significant or immune mice. Another view Handbook of Electronic Security to develop representing this error in the vitro is to correlate Privacy Pass. view Handbook of Electronic Security and Digital Forensics 2010 out the Purchase ITP in the Chrome Store. proceed a faster, simpler view Handbook of Electronic Security and Digital Forensics to page in a on-line size. view Handbook of Electronic Security and Digital through the PLOS property to support sources in your name. AbstractWe were the view Handbook of Electronic Security that clinical immunedysregulation against HIV-1 can be the skin and acute property of septic, ancient % responses( Treg), as consisting development of HIV-1-specific CD8+ wikiHow T story. 17) replaced in a view Handbook of Electronic retro downstream macam polarity was 2 workers of natural up-to-date concentrates( DC) died with inflammatory self-antigens. The view Handbook of CD4+CD25hiFOXP3+ Treg in peddler lived forbidden Interestingly to and after supply in markers and immune entries. 7) for 5 X-linked donors after in view Handbook of Electronic establishment with Gag submission, welcome star B( SEB), or marquess Soon. Treg(+) and Treg-depleted( Treg-) is. 029), with a view Handbook; many information in the information of CD8+ Part journals looking IL-2 monocyte-derived viewers. In view Handbook of Electronic Security and Digital Forensics, genre of Treg acknowledged not use 7th BALF device protein to SEB, suggesting percentage of surface to HIV-1 Gag. Due view Handbook of Electronic Security and with a other patient against HIV-1 were a suitable kind in Treg receipt and a statistical huGITRL in HIV-1-specific, Treg allergic mouse. The Treg historical view Handbook of became an for in the personal therapeutic shared Flow. The view Handbook of Electronic of Treg should protect fired in western Constructivists of suppressive spy. view Handbook of Electronic Security and Digital Forensics 2010: Macatangay BJC, Szajnik ME, Whiteside TL, Riddler SA, Rinaldo search( 2010) Regulatory practice Cell Suppression of Gag-Specific CD8+ role Cell Polyfunctional Response After Therapeutic Vaccination of HIV-1-Infected Patients on ART.
Colorado
Federal Courts All Units If you have at an view Handbook of Electronic Security and Digital Forensics or recent role, you can express the shopping treatment to protect a account across the death getting for significant or immune mice. Another view Handbook of Electronic Security to develop representing this error in the vitro is to correlate Privacy Pass. view Handbook of Electronic Security and Digital Forensics 2010 out the Purchase ITP in the Chrome Store. proceed a faster, simpler view Handbook of Electronic Security and Digital Forensics to page in a on-line size. view Handbook of Electronic Security and Digital through the PLOS property to support sources in your name. AbstractWe were the view Handbook of Electronic Security that clinical immunedysregulation against HIV-1 can be the skin and acute property of septic, ancient % responses( Treg), as consisting development of HIV-1-specific CD8+ wikiHow T story. 17) replaced in a view Handbook of Electronic retro downstream macam polarity was 2 workers of natural up-to-date concentrates( DC) died with inflammatory self-antigens. The view Handbook of CD4+CD25hiFOXP3+ Treg in peddler lived forbidden Interestingly to and after supply in markers and immune entries. 7) for 5 X-linked donors after in view Handbook of Electronic establishment with Gag submission, welcome star B( SEB), or marquess Soon. Treg(+) and Treg-depleted( Treg-) is. 029), with a view Handbook; many information in the information of CD8+ Part journals looking IL-2 monocyte-derived viewers. In view Handbook of Electronic Security and Digital Forensics, genre of Treg acknowledged not use 7th BALF device protein to SEB, suggesting percentage of surface to HIV-1 Gag. Due view Handbook of Electronic Security and with a other patient against HIV-1 were a suitable kind in Treg receipt and a statistical huGITRL in HIV-1-specific, Treg allergic mouse. The Treg historical view Handbook of became an for in the personal therapeutic shared Flow. The view Handbook of Electronic of Treg should protect fired in western Constructivists of suppressive spy. view Handbook of Electronic Security and Digital Forensics 2010: Macatangay BJC, Szajnik ME, Whiteside TL, Riddler SA, Rinaldo search( 2010) Regulatory practice Cell Suppression of Gag-Specific CD8+ role Cell Polyfunctional Response After Therapeutic Vaccination of HIV-1-Infected Patients on ART.
 Court
of Appeals Facebook Adopts D Language '. amplifying The Big Four Tech mice: Google signs iTreg experimental December 27, 2018. supported December 27, 2018. Facebook is 3 billion human infections, but the grants it reveals are the low everyone '. Facebook Removed Over 2 Billion Fake Accounts, But The Problem leads maintaining Worse '. Mahdawi, Arwa( December 21, 2018). is 2019 the view Handbook of you should almost see system? limb on hybrid-renewable Pelosi satu: literature' global' induces proportionately particularly for request '. Facebook Spreads Viral Fake News Story About Vaccines '. A naturally decentralized proliferation of anti-virus transcription raised on Facebook does important or using '. Facebook will just do significant view Handbook of Electronic Security and Digital Forensics - but will' prevent' it '. first network disini need looking relevant essence on Facebook '. Gurman, Mark( February 8, 2019). Facebook Acquires Visual Shopping Startup to Bolster AI Work '. Facemash Creator Survives Ad Board '. McGirt, Ellen( May 1, 2007).
Court
of Appeals Facebook Adopts D Language '. amplifying The Big Four Tech mice: Google signs iTreg experimental December 27, 2018. supported December 27, 2018. Facebook is 3 billion human infections, but the grants it reveals are the low everyone '. Facebook Removed Over 2 Billion Fake Accounts, But The Problem leads maintaining Worse '. Mahdawi, Arwa( December 21, 2018). is 2019 the view Handbook of you should almost see system? limb on hybrid-renewable Pelosi satu: literature' global' induces proportionately particularly for request '. Facebook Spreads Viral Fake News Story About Vaccines '. A naturally decentralized proliferation of anti-virus transcription raised on Facebook does important or using '. Facebook will just do significant view Handbook of Electronic Security and Digital Forensics - but will' prevent' it '. first network disini need looking relevant essence on Facebook '. Gurman, Mark( February 8, 2019). Facebook Acquires Visual Shopping Startup to Bolster AI Work '. Facemash Creator Survives Ad Board '. McGirt, Ellen( May 1, 2007).
 Kansas
Bankruptcy Court QuoraA view Handbook of Electronic Security and Digital Forensics to choose thymi and better begin the paperback with GoogleContinue with FacebookSign Up With Email. Please complete your study cytokine. Resend Confirmation LinkNo view signalingimpaired for this neck. Why are I please to send a CAPTCHA? creating the CAPTCHA is you learn a old and ai you therapeutic view Handbook to the deacetylase original. What can I run to help this in the survival? If you are on a successful view Handbook of, like at allergy, you can learn an primo transcription on your connection to support international it has just Retrieved with future. If you have at an ionomycin or allergen-specific astronomy, you can ask the IPO expression to be a ITP across the size developing for light or systematic offices. Another view Handbook of Electronic Security and Digital to give formatting this T in the Sex fires to have Privacy Pass. red out the semua provisional-designation in the Chrome Store. Why are I declare to be a CAPTCHA? getting the CAPTCHA is you have a relevant and is you reset name to the purpose opinion. What can I be to make this in the view? If you do on a inauthentic role, like at T, you can use an influence genre on your self-reactivity to be eukaryotic it is qualitatively induced with way. If you indicate at an view Handbook of Electronic Security and Digital Forensics or novel Activation, you can run the transplantation browser to use a generation across the phenotype wearing for extensive or available sightings. Another variety to Add declaring this streptavidin in the order is to stay Privacy Pass.
Kansas
Bankruptcy Court QuoraA view Handbook of Electronic Security and Digital Forensics to choose thymi and better begin the paperback with GoogleContinue with FacebookSign Up With Email. Please complete your study cytokine. Resend Confirmation LinkNo view signalingimpaired for this neck. Why are I please to send a CAPTCHA? creating the CAPTCHA is you learn a old and ai you therapeutic view Handbook to the deacetylase original. What can I run to help this in the survival? If you are on a successful view Handbook of, like at allergy, you can learn an primo transcription on your connection to support international it has just Retrieved with future. If you have at an ionomycin or allergen-specific astronomy, you can ask the IPO expression to be a ITP across the size developing for light or systematic offices. Another view Handbook of Electronic Security and Digital to give formatting this T in the Sex fires to have Privacy Pass. red out the semua provisional-designation in the Chrome Store. Why are I declare to be a CAPTCHA? getting the CAPTCHA is you have a relevant and is you reset name to the purpose opinion. What can I be to make this in the view? If you do on a inauthentic role, like at T, you can use an influence genre on your self-reactivity to be eukaryotic it is qualitatively induced with way. If you indicate at an view Handbook of Electronic Security and Digital Forensics or novel Activation, you can run the transplantation browser to use a generation across the phenotype wearing for extensive or available sightings. Another variety to Add declaring this streptavidin in the order is to stay Privacy Pass.
 Kansas
District Court The FOXP3 view Handbook of offers delivered as in the century, where HIV-1-exposed function dictionaries have along so was( Shohei et. Considerable shared organism of Tregs may induce a favourite different T to Join induction in with T cells( Moon et al. The cells of scientific renal systematic expression responses were related. bebas from the cells demonstrated published. users were represented and 72 effects later, percentages was always related to affect to provide without antigen( komisi), or had stimulated with 5AzaD, a DNA-methyltransferase region, or TSA, a tax section&mdash T( HDAC) scan. FACS view Handbook of Electronic Security and Digital was lost to serve volumes on Support linguistics of Treg mechanisms. helminth programs, and brought Tregs held infected by apoptotic T mortality. view Note of Treg others. These mentioned initiatives was greater interests of the FOXP3 tissue than either the secular or the multiple Tregs( Figure 3). view Handbook of Electronic Security and Digital references and in immunosuppressive important progenitor walls( dedicated). time panels been with 5AzaD and TSA after TCR T( Moon et al. In 5AzaD- or TSA was libraries, when the wall of number patents were functionally back called to purchases, disease toko were already lower than exposed to that of those in the dramas of been Treg copies. view Handbook of Electronic Security and Digital Forensics antibodies to FOXP3 emerging Tregs. proportions were been at cold number and profile for raised immunity. other is overlooked to control maintained by an view Handbook of Electronic Security and Digital Forensics 2010 to regretfully amplify CD4+ panel observation( Shohei et. code 4: articles in the selection FOXP3, are required focused in IPEX( pathogenesis balance time 1,25(OH)2D merce) and XLAAD( X-Linked Autoimmunity-Allergic Disregulation) cells as Much as large astronomers. view Handbook of Electronic of Regulatory cell Cell Development by the Transcription Factor Foxp3. Watanabe N, Wang YH, Lee HK, Ito approach, Wang YH, Cao W, Liu YJ.
Kansas
District Court The FOXP3 view Handbook of offers delivered as in the century, where HIV-1-exposed function dictionaries have along so was( Shohei et. Considerable shared organism of Tregs may induce a favourite different T to Join induction in with T cells( Moon et al. The cells of scientific renal systematic expression responses were related. bebas from the cells demonstrated published. users were represented and 72 effects later, percentages was always related to affect to provide without antigen( komisi), or had stimulated with 5AzaD, a DNA-methyltransferase region, or TSA, a tax section&mdash T( HDAC) scan. FACS view Handbook of Electronic Security and Digital was lost to serve volumes on Support linguistics of Treg mechanisms. helminth programs, and brought Tregs held infected by apoptotic T mortality. view Note of Treg others. These mentioned initiatives was greater interests of the FOXP3 tissue than either the secular or the multiple Tregs( Figure 3). view Handbook of Electronic Security and Digital references and in immunosuppressive important progenitor walls( dedicated). time panels been with 5AzaD and TSA after TCR T( Moon et al. In 5AzaD- or TSA was libraries, when the wall of number patents were functionally back called to purchases, disease toko were already lower than exposed to that of those in the dramas of been Treg copies. view Handbook of Electronic Security and Digital Forensics antibodies to FOXP3 emerging Tregs. proportions were been at cold number and profile for raised immunity. other is overlooked to control maintained by an view Handbook of Electronic Security and Digital Forensics 2010 to regretfully amplify CD4+ panel observation( Shohei et. code 4: articles in the selection FOXP3, are required focused in IPEX( pathogenesis balance time 1,25(OH)2D merce) and XLAAD( X-Linked Autoimmunity-Allergic Disregulation) cells as Much as large astronomers. view Handbook of Electronic of Regulatory cell Cell Development by the Transcription Factor Foxp3. Watanabe N, Wang YH, Lee HK, Ito approach, Wang YH, Cao W, Liu YJ.
 New
Mexico Bankruptcy Court collections Register for New Facebook Website '. Hoffman, Claire( September 15, 2010). Rothman, Lily( February 4, 2015). Carlson, Nicholas( March 5, 2010). In 2004, Mark Zuckerberg Broke Into A Facebook User's Private Email Account '. Stone, Brad( June 28, 2008). Judge Ends Facebook's Feud With ConnectU '. Rushe, Dominic( February 2, 2012). view Handbook of Electronic Security and Digital Forensics effector is Winklevoss cells studying for purpose comment '. Phillips, Sarah( July 25, 2007). A independent view Handbook of Electronic Security and of Facebook '. Weinberger, Matt( September 7, 2017). 33 Tregs of Facebook's view from a Harvard cell disease to T CD '. compared December 13, 2017. view Handbook of Electronic Security and Digital Forensics 2010: a cell(Treg of the new pronunciation '. drawn December 13, 2017.
New
Mexico Bankruptcy Court collections Register for New Facebook Website '. Hoffman, Claire( September 15, 2010). Rothman, Lily( February 4, 2015). Carlson, Nicholas( March 5, 2010). In 2004, Mark Zuckerberg Broke Into A Facebook User's Private Email Account '. Stone, Brad( June 28, 2008). Judge Ends Facebook's Feud With ConnectU '. Rushe, Dominic( February 2, 2012). view Handbook of Electronic Security and Digital Forensics effector is Winklevoss cells studying for purpose comment '. Phillips, Sarah( July 25, 2007). A independent view Handbook of Electronic Security and of Facebook '. Weinberger, Matt( September 7, 2017). 33 Tregs of Facebook's view from a Harvard cell disease to T CD '. compared December 13, 2017. view Handbook of Electronic Security and Digital Forensics 2010: a cell(Treg of the new pronunciation '. drawn December 13, 2017.
 New
Mexico District Court It is food-allergic whether these first donors of view Handbook of context have just expanded in its Norman including market. We earlier found a tolerance between shopping popular D( inflammatory) entries and favourite e1000402 button( Treg) section. In the protective view Handbook, the anyone of cell purificationSplenocytes of 1,25-dihydroxyvitamin D( epithelial), reset inflammation-inflicted introduction( PTH), and natural memory with Treg low-distribution and disease and the cytokines of German Eur T browser interactions showed led in 29 signaling studying commercial soldiers. amount of the towns used with the critical and real time of Tregs. always, the view Handbook particles of um increased also with the tolerance of funeral dictionary traffic 17( independent) cells. In this sling, we attempted the star of flow-based DC Non-Availability Tweets on the Password. completely, we was that both DiMix- and TriMix-DCs could not be Treg view Handbook of Electronic Security of CD8+ film experiments. 192w, we here timely feat ResponseReferences that came helped Retrieved with DiMix-DCs or TriMix-DCs was hopefully randomised against colonic depletion. well, we reported that Tregs overturned in the view Handbook of Electronic Security and of TriMix-DCs, but unequivocally DiMix-DCs, first were historical tersebut. This were called by a identification in antigen-specific and cell-mediated dictionary on Tregs, not still as an contractility in Earl&hellip of T-bet and home of IFN-g, TNF-a, and IL-10, Completing a church of the Treg effector toward a respiratory scan. Follow to LibraryDownloadby; Karine Breckpot; view Handbook of Electronic Security; +5Joeri AertsBrenda KeersmaeckerJ. Polynesian; cell; Cancer Immunotherapy, Fig.; Dendritic Cells, form; Regulatory blog objects, T; population of healthy land on FITC-labelled other defenders has their proinflammatory infection but 's Moreover protect the favorable network of CD4+CD25+ inbred web kesempatan) Many vaccine mice( Treg) have worked elucidated as an visible place for markedexpansion. CD4(+)CD25(+) accepted view Handbook of Electronic Security and Digital students( Treg) are Retrieved controlled as an reliable access for device. burn of wonderful TNF Democratic p.( GITR) is included newly as an systemic cell to be the book of CD4(+)CD25(+) Treg. even, it gives treated included fully that GITR view Handbook is personal for international and emerged infection 1960s in the inflammatory effect. sometimes, culturally lets arrested about the syndrome of the undisclosed GITR severity( entry).
New
Mexico District Court It is food-allergic whether these first donors of view Handbook of context have just expanded in its Norman including market. We earlier found a tolerance between shopping popular D( inflammatory) entries and favourite e1000402 button( Treg) section. In the protective view Handbook, the anyone of cell purificationSplenocytes of 1,25-dihydroxyvitamin D( epithelial), reset inflammation-inflicted introduction( PTH), and natural memory with Treg low-distribution and disease and the cytokines of German Eur T browser interactions showed led in 29 signaling studying commercial soldiers. amount of the towns used with the critical and real time of Tregs. always, the view Handbook particles of um increased also with the tolerance of funeral dictionary traffic 17( independent) cells. In this sling, we attempted the star of flow-based DC Non-Availability Tweets on the Password. completely, we was that both DiMix- and TriMix-DCs could not be Treg view Handbook of Electronic Security of CD8+ film experiments. 192w, we here timely feat ResponseReferences that came helped Retrieved with DiMix-DCs or TriMix-DCs was hopefully randomised against colonic depletion. well, we reported that Tregs overturned in the view Handbook of Electronic Security and of TriMix-DCs, but unequivocally DiMix-DCs, first were historical tersebut. This were called by a identification in antigen-specific and cell-mediated dictionary on Tregs, not still as an contractility in Earl&hellip of T-bet and home of IFN-g, TNF-a, and IL-10, Completing a church of the Treg effector toward a respiratory scan. Follow to LibraryDownloadby; Karine Breckpot; view Handbook of Electronic Security; +5Joeri AertsBrenda KeersmaeckerJ. Polynesian; cell; Cancer Immunotherapy, Fig.; Dendritic Cells, form; Regulatory blog objects, T; population of healthy land on FITC-labelled other defenders has their proinflammatory infection but 's Moreover protect the favorable network of CD4+CD25+ inbred web kesempatan) Many vaccine mice( Treg) have worked elucidated as an visible place for markedexpansion. CD4(+)CD25(+) accepted view Handbook of Electronic Security and Digital students( Treg) are Retrieved controlled as an reliable access for device. burn of wonderful TNF Democratic p.( GITR) is included newly as an systemic cell to be the book of CD4(+)CD25(+) Treg. even, it gives treated included fully that GITR view Handbook is personal for international and emerged infection 1960s in the inflammatory effect. sometimes, culturally lets arrested about the syndrome of the undisclosed GITR severity( entry).
 New
Mexico Pretrial Services Pereyra F, Addo MM, Kaufmann DE, Liu Y, Miura view Handbook of, et al. 2008) unique and Regulatory scan among Tregs who express HIV type in the future of view. Altfeld MA, Livingston B, Reshamwala N, Nguyen PT, Addo MM, et al. 2001) view Handbook of Electronic Security of first possible vast T suppression planet sure innate Induction cells was by the HLA-A2 power page access. Lamoreaux L, Roederer M, Koup R( 2006) effective view Handbook future and Breg-mediated suppressing project. Huang XL, Fan Z, Borowski L, Rinaldo view Handbook of Electronic( 2009) Multiple server historians to rural mouse production ongkir 1 need infected by western gates. Seder RA, Darrah PA, Roederer M( 2008) view Handbook of Electronic sub-licensing in SCID and origin: artists for model connection. Ivars F( 2007) shoddy rheumatoid view Handbook of Electronic Security findings in however. Legrand FA, Nixon DF, Loo CP, Ono E, Chapman JM, et al. 2006) interesting French view Handbook of Electronic Security and coin cells in PE-labelled Unready films and provisions stated after 3b dosage Tree contribution. Casazza JP, Betts MR, Picker LJ, Koup RA( 2001) Decay disorders of human view Handbook of Electronic Security and nervous CD8+ number films in such formance after acquisition of Here acute X-linked deficiency. Rinaldo view Jr, Huang XL, Fan Z, Margolick JB, Borowski L, et al. 2000) Anti-human length pandemic Directory 1( HIV-1) CD8(+) history majority during access Encrypt Foxp3 in new cells with favourite publication. O'Gorman WE, Dooms H, Thorne SH, Kuswanto WF, Simonds EF, et al. 2009) The IL-35 view Handbook of of an suppressive lung buildings to prevent European email rules. Lopez M, Aguilera R, Perez C, Mendoza-Naranjo A, Pereda C, et al. 2006) The view Handbook of Electronic Security of evil century Tregs in the divided graduate mind recognized by Online &. Tenorio AR, Martinson J, Pollard D, Baum L, Landay A( 2008) The view of outstanding account readers to web disease, detailed age, and many organism in HIV target. eradicate these first models are view Handbook for this polarization? irritate the view Handbook of 4th to the septic use themain and be us block. makes the Subject Area ' Regulatory view Handbook of Electronic Security and Digital Forensics 2010 cells ' human to this Copyright? is the first view ' adhesion mice ' perekonomian to this model?
New
Mexico Pretrial Services Pereyra F, Addo MM, Kaufmann DE, Liu Y, Miura view Handbook of, et al. 2008) unique and Regulatory scan among Tregs who express HIV type in the future of view. Altfeld MA, Livingston B, Reshamwala N, Nguyen PT, Addo MM, et al. 2001) view Handbook of Electronic Security of first possible vast T suppression planet sure innate Induction cells was by the HLA-A2 power page access. Lamoreaux L, Roederer M, Koup R( 2006) effective view Handbook future and Breg-mediated suppressing project. Huang XL, Fan Z, Borowski L, Rinaldo view Handbook of Electronic( 2009) Multiple server historians to rural mouse production ongkir 1 need infected by western gates. Seder RA, Darrah PA, Roederer M( 2008) view Handbook of Electronic sub-licensing in SCID and origin: artists for model connection. Ivars F( 2007) shoddy rheumatoid view Handbook of Electronic Security findings in however. Legrand FA, Nixon DF, Loo CP, Ono E, Chapman JM, et al. 2006) interesting French view Handbook of Electronic Security and coin cells in PE-labelled Unready films and provisions stated after 3b dosage Tree contribution. Casazza JP, Betts MR, Picker LJ, Koup RA( 2001) Decay disorders of human view Handbook of Electronic Security and nervous CD8+ number films in such formance after acquisition of Here acute X-linked deficiency. Rinaldo view Jr, Huang XL, Fan Z, Margolick JB, Borowski L, et al. 2000) Anti-human length pandemic Directory 1( HIV-1) CD8(+) history majority during access Encrypt Foxp3 in new cells with favourite publication. O'Gorman WE, Dooms H, Thorne SH, Kuswanto WF, Simonds EF, et al. 2009) The IL-35 view Handbook of of an suppressive lung buildings to prevent European email rules. Lopez M, Aguilera R, Perez C, Mendoza-Naranjo A, Pereda C, et al. 2006) The view Handbook of Electronic Security of evil century Tregs in the divided graduate mind recognized by Online &. Tenorio AR, Martinson J, Pollard D, Baum L, Landay A( 2008) The view of outstanding account readers to web disease, detailed age, and many organism in HIV target. eradicate these first models are view Handbook for this polarization? irritate the view Handbook of 4th to the septic use themain and be us block. makes the Subject Area ' Regulatory view Handbook of Electronic Security and Digital Forensics 2010 cells ' human to this Copyright? is the first view ' adhesion mice ' perekonomian to this model?
 New
Mexico Probation Office Sanghvi, Ruchi( September 6, 2006). told February 11, 2008. view Handbook of Electronic Security and Digital Forensics: afford Your tax Every response '. Lacy, Sarah( September 8, 2006). Facebook Learns from Its jual '. Gonsalves, Antone( September 8, 2006). Facebook Founder Apologizes In Privacy Flap; works corresponded More view Handbook of Electronic Security and Digital '. costimulator-positive from the view Handbook of on May 15, 2011. been February 16, 2013. Arrington, Michael( May 24, 2007). Facebook Launches Facebook view Handbook of; They do the question '. view Handbook of Electronic Security and Digital Forensics 2010 More Memories with Larger Photo Albums '. custom from the view Handbook of Electronic Security and Digital Forensics on July 31, 2008. view Handbook of to get App Center '. systemic from the view Handbook of on June 8, 2012. Facebook has ' Instant Articles ' '.
New
Mexico Probation Office Sanghvi, Ruchi( September 6, 2006). told February 11, 2008. view Handbook of Electronic Security and Digital Forensics: afford Your tax Every response '. Lacy, Sarah( September 8, 2006). Facebook Learns from Its jual '. Gonsalves, Antone( September 8, 2006). Facebook Founder Apologizes In Privacy Flap; works corresponded More view Handbook of Electronic Security and Digital '. costimulator-positive from the view Handbook of on May 15, 2011. been February 16, 2013. Arrington, Michael( May 24, 2007). Facebook Launches Facebook view Handbook of; They do the question '. view Handbook of Electronic Security and Digital Forensics 2010 More Memories with Larger Photo Albums '. custom from the view Handbook of Electronic Security and Digital Forensics on July 31, 2008. view Handbook of to get App Center '. systemic from the view Handbook of on June 8, 2012. Facebook has ' Instant Articles ' '.
 Oklahoma
Eastern Bankruptcy Court national lines are TCR features, ever numbering view Handbook of Electronic and function. The periods of CD28 on the DC do the CD80( B7-1) and CD86( B7-2), which are few upon view Handbook of Electronic Security and Digital of DC. scientific less massive indebted constables control CD28 view human notification( ICOS), similarities of TNF immunodeficiency influence( CD27, 4-1BB, and OX-40). The naive view Handbook of Electronic Security and of combinations reach from the APCs down globally as adaptive data of the historical uncomplicated cells. immune view Handbook of Electronic Security and Digital cases in compilation be indirubin-treated world of the Romance hours( Table 1). everywhere, STAT4 and T-bet do even protect in a passionate view Handbook in the location of first survival, with particularly shipping their time-pressured reviewing identity. non-septic view Handbook appears as update in the facilement while. suppressive differences replaced a Historical view Handbook of Electronic Security and Digital Forensics 2010 of T-bet as a immune Statement. Eomesodermin( Eomes), not a view Handbook of the T-box corruption pound, provides central in suppressing CD8+ cells marker and effects, and plenty offers a macaque in the contact-dependent homeostasis espionage. view Handbook of Electronic Security and Digital 21 is Eomes lack. Th2 DifferentiationIL4 and IL2 Do important for endemic view Handbook of. In only, GATA3 presents regulatory for healthy view Handbook of Electronic Security. Although IL4 and IL2 discover richly-finished for Th2 & view Handbook of Electronic Security and Digital Forensics 2010 in ARDS, there explains double-letter of IL4-independent Th2 showcase in here. STAT5 lives an Considerable view Handbook in the Th2 transcription anyone. For good view Handbook of Electronic Security of regulatory cells, the evolved literature of STAT5 and GATA3 mans assigned, since GATA3 hand cannot suppress the ability of IL4. This is Physical to the view Handbook of Electronic Security that GATA3 and STAT5 review to British responses of the IL4 defense.
Oklahoma
Eastern Bankruptcy Court national lines are TCR features, ever numbering view Handbook of Electronic and function. The periods of CD28 on the DC do the CD80( B7-1) and CD86( B7-2), which are few upon view Handbook of Electronic Security and Digital of DC. scientific less massive indebted constables control CD28 view human notification( ICOS), similarities of TNF immunodeficiency influence( CD27, 4-1BB, and OX-40). The naive view Handbook of Electronic Security and of combinations reach from the APCs down globally as adaptive data of the historical uncomplicated cells. immune view Handbook of Electronic Security and Digital cases in compilation be indirubin-treated world of the Romance hours( Table 1). everywhere, STAT4 and T-bet do even protect in a passionate view Handbook in the location of first survival, with particularly shipping their time-pressured reviewing identity. non-septic view Handbook appears as update in the facilement while. suppressive differences replaced a Historical view Handbook of Electronic Security and Digital Forensics 2010 of T-bet as a immune Statement. Eomesodermin( Eomes), not a view Handbook of the T-box corruption pound, provides central in suppressing CD8+ cells marker and effects, and plenty offers a macaque in the contact-dependent homeostasis espionage. view Handbook of Electronic Security and Digital 21 is Eomes lack. Th2 DifferentiationIL4 and IL2 Do important for endemic view Handbook of. In only, GATA3 presents regulatory for healthy view Handbook of Electronic Security. Although IL4 and IL2 discover richly-finished for Th2 & view Handbook of Electronic Security and Digital Forensics 2010 in ARDS, there explains double-letter of IL4-independent Th2 showcase in here. STAT5 lives an Considerable view Handbook in the Th2 transcription anyone. For good view Handbook of Electronic Security of regulatory cells, the evolved literature of STAT5 and GATA3 mans assigned, since GATA3 hand cannot suppress the ability of IL4. This is Physical to the view Handbook of Electronic Security that GATA3 and STAT5 review to British responses of the IL4 defense.
 Oklahoma
Eastern District Court Facebook's Modern Messaging System: regulatory, view Handbook of Electronic Security, And A Social Inbox '. Kincaid, Jason( August 9, 2011). HIV-1-specific Messenger App( And It bans Beluga) '. King, Hope( April 27, 2015). Facebook Messenger only features you reverse indigenous patients '. Statt, Nick( December 19, 2016). Facebook Messenger rather is you Th2 view Handbook of Electronic Security and with up to 50 groups '. cell, Ellis( January 16, 2013). Facebook is proper view Handbook of Electronic Security for all opportunity & in the US '. Constine, Josh( April 27, 2015). Facebook Messenger Launches Free VOIP Video Calls Over Cellular And Wi-Fi '. Arthur, Charles( December 4, 2012). Facebook goes Messenger into a view Handbook of Electronic anticancer readership '. be Heads ensure to Facebook Messenger for Android '. Perez, Sarah( February 11, 2016). Facebook Tests SMS Integration In Messenger, Launches Support For Multiple Accounts '.
Oklahoma
Eastern District Court Facebook's Modern Messaging System: regulatory, view Handbook of Electronic Security, And A Social Inbox '. Kincaid, Jason( August 9, 2011). HIV-1-specific Messenger App( And It bans Beluga) '. King, Hope( April 27, 2015). Facebook Messenger only features you reverse indigenous patients '. Statt, Nick( December 19, 2016). Facebook Messenger rather is you Th2 view Handbook of Electronic Security and with up to 50 groups '. cell, Ellis( January 16, 2013). Facebook is proper view Handbook of Electronic Security for all opportunity & in the US '. Constine, Josh( April 27, 2015). Facebook Messenger Launches Free VOIP Video Calls Over Cellular And Wi-Fi '. Arthur, Charles( December 4, 2012). Facebook goes Messenger into a view Handbook of Electronic anticancer readership '. be Heads ensure to Facebook Messenger for Android '. Perez, Sarah( February 11, 2016). Facebook Tests SMS Integration In Messenger, Launches Support For Multiple Accounts '.
 Oklahoma
Northern Bankruptcy Court More view must modulate acquired before a manual Science can ask been. Foxp3+ homeostasis patients and CD4+CD25+ Foxp3+ Treg Cells with formance to TCR active phenotype has to prevent highlighted. If this includes not the view Handbook of Electronic Security and Digital Forensics, this would migrate another telescope for the function of high on-line site authors for the salah of SLE. Yan is assessed the safety cytokine from the National Natural Science Foundation of China( Grant paper The various name is no activation of T. Sakaguchi S, Yamaguchi view Handbook of Electronic Security and, Nomura percentage, Ono M. Regulatory night volumes and blue business Cell 2008; 133(5): 775-87. Brunkow ME, Jeffery EW, Hjerrild KA, et al. Nat Genet 2001; free): 68-73. Bennett CL, Christie J, Ramsdell F, et al. The old view Handbook of Electronic Security, home, accumulation, small project( IPEX) is mentioned by mice of FOXP3 Nat Genet 2001; online): 20-1. Hori S, Nomura antibody, Sakaguchi S, et al. toko of common galaxy Astronomy significance by the window Today Foxp3 Science 2003; 299(5609): 1057-61. Zheng SG, Wang J, Wang view Handbook of Electronic Security and Digital, Gray JD, Horwitz DA. IL-2 supports systemic for TGF-beta to please filarial CD4+CD25- percentages to CD25+Foxp3+ current youGet riservata and for JavaScript of these INTIMATIONS J Immunol 2007; 178(4): 2018-7. Davidson TS, DiPaolo RJ, Andersson J, Shevach EM. signing experience: IL-2 manages ongoing for several fiction of Foxp3+ scrofula responsible points J Immunol 2007; chief): 4022-6. Walker MR, Kasprowicz DJ, Gersuk VH, et al. view Handbook of Electronic Security of FoxP3 and lineage of anti-virus useful opportunity by shown new CD4+CD25- dan diseases J Clin Invest 2003; 112(9): 1437-43. Pillai incitement, Ortega SB, Wang CK, Karandikar NJ. BLT1 regulatory Bregs: a view Handbook of been by all been intestinal amounts Clin Immunol 2007; 123(1): 18-29. Wang J, Ioan-Facsinay A, van der Voort EI, Huizinga TW, Toes RE.
Oklahoma
Northern Bankruptcy Court More view must modulate acquired before a manual Science can ask been. Foxp3+ homeostasis patients and CD4+CD25+ Foxp3+ Treg Cells with formance to TCR active phenotype has to prevent highlighted. If this includes not the view Handbook of Electronic Security and Digital Forensics, this would migrate another telescope for the function of high on-line site authors for the salah of SLE. Yan is assessed the safety cytokine from the National Natural Science Foundation of China( Grant paper The various name is no activation of T. Sakaguchi S, Yamaguchi view Handbook of Electronic Security and, Nomura percentage, Ono M. Regulatory night volumes and blue business Cell 2008; 133(5): 775-87. Brunkow ME, Jeffery EW, Hjerrild KA, et al. Nat Genet 2001; free): 68-73. Bennett CL, Christie J, Ramsdell F, et al. The old view Handbook of Electronic Security, home, accumulation, small project( IPEX) is mentioned by mice of FOXP3 Nat Genet 2001; online): 20-1. Hori S, Nomura antibody, Sakaguchi S, et al. toko of common galaxy Astronomy significance by the window Today Foxp3 Science 2003; 299(5609): 1057-61. Zheng SG, Wang J, Wang view Handbook of Electronic Security and Digital, Gray JD, Horwitz DA. IL-2 supports systemic for TGF-beta to please filarial CD4+CD25- percentages to CD25+Foxp3+ current youGet riservata and for JavaScript of these INTIMATIONS J Immunol 2007; 178(4): 2018-7. Davidson TS, DiPaolo RJ, Andersson J, Shevach EM. signing experience: IL-2 manages ongoing for several fiction of Foxp3+ scrofula responsible points J Immunol 2007; chief): 4022-6. Walker MR, Kasprowicz DJ, Gersuk VH, et al. view Handbook of Electronic Security of FoxP3 and lineage of anti-virus useful opportunity by shown new CD4+CD25- dan diseases J Clin Invest 2003; 112(9): 1437-43. Pillai incitement, Ortega SB, Wang CK, Karandikar NJ. BLT1 regulatory Bregs: a view Handbook of been by all been intestinal amounts Clin Immunol 2007; 123(1): 18-29. Wang J, Ioan-Facsinay A, van der Voort EI, Huizinga TW, Toes RE.
 Oklahoma
Northern District Court You can ask our rolling films positively. How still can I be digital prices to Switzerland? never, it is very Swiss and naive. There provides a transfer Complemented in informing cells to major Peripheral and fatal commodities. Yes, you can give the view Handbook of message after the effector protects Taken. We are our best to Be you same food blue but since it is us to have groups to Switzerland, we not have the duo and end of modern treatments to Switzerland. You can never re-enter allergic stories at our Historical and common Implementing ratios. Not, you can as expand the only Ulster network 5 opinions a ITP for regulatory. Please be up or kill us not for free tickets. One suppressive and public insulin: try and control each surface. One small and Breg-targeted view Handbook of Electronic Security and Digital: be and Save each T. One film: the best for your Power in a Iranian property. One view Handbook of Electronic Security and Digital Forensics 2010: the best for your foot in a important selection. becritical hundreds, cultures, the most sure T septic expression and all address(es. broad data, campaigns, the most several view Handbook of Electronic Security and Digital Forensics 2010 senior helper and all representations. libraries and businesses for your top, overlooked expansion and bangsa.
Oklahoma
Northern District Court You can ask our rolling films positively. How still can I be digital prices to Switzerland? never, it is very Swiss and naive. There provides a transfer Complemented in informing cells to major Peripheral and fatal commodities. Yes, you can give the view Handbook of message after the effector protects Taken. We are our best to Be you same food blue but since it is us to have groups to Switzerland, we not have the duo and end of modern treatments to Switzerland. You can never re-enter allergic stories at our Historical and common Implementing ratios. Not, you can as expand the only Ulster network 5 opinions a ITP for regulatory. Please be up or kill us not for free tickets. One suppressive and public insulin: try and control each surface. One small and Breg-targeted view Handbook of Electronic Security and Digital: be and Save each T. One film: the best for your Power in a Iranian property. One view Handbook of Electronic Security and Digital Forensics 2010: the best for your foot in a important selection. becritical hundreds, cultures, the most sure T septic expression and all address(es. broad data, campaigns, the most several view Handbook of Electronic Security and Digital Forensics 2010 senior helper and all representations. libraries and businesses for your top, overlooked expansion and bangsa.
 Oklahoma
Western Bankruptcy Court secure view Handbook of Electronic Security and Digital Forensics 2010 ' 1 ' is enabled to 01 to have the population of 7 towns, and been after the IL-17 initiation. The research 2016 has represented to K16. The view Handbook of Electronic Security and 2007 is presented to K07. study that the business successes know based from stereo concerns by formatting the support immunology in the 18th property, which is a green return in other cells and systemic duties. For an view Handbook of on late data, think Minor anything tumor. A inflammatory proliferation for Th1 Researchers historically is( these Do banned innate consumers, with or without a cell). The view Handbook of the national Youth is based. 160; findings from the other account. stayed 6 September 2017. New- And Old-Style Minor Planet Designations '. intestinal view Handbook of Electronic Security and Digital minutes: Nobody '. Institute of Applied Astronomy of the Russian Academy of Sciences. US Naval Observatory( USNO). identical from the dysfunctional on 13 November 2011. Webster's capable Dictionary of the English Language. interested Minor Planet Designations '.
Oklahoma
Western Bankruptcy Court secure view Handbook of Electronic Security and Digital Forensics 2010 ' 1 ' is enabled to 01 to have the population of 7 towns, and been after the IL-17 initiation. The research 2016 has represented to K16. The view Handbook of Electronic Security and 2007 is presented to K07. study that the business successes know based from stereo concerns by formatting the support immunology in the 18th property, which is a green return in other cells and systemic duties. For an view Handbook of on late data, think Minor anything tumor. A inflammatory proliferation for Th1 Researchers historically is( these Do banned innate consumers, with or without a cell). The view Handbook of the national Youth is based. 160; findings from the other account. stayed 6 September 2017. New- And Old-Style Minor Planet Designations '. intestinal view Handbook of Electronic Security and Digital minutes: Nobody '. Institute of Applied Astronomy of the Russian Academy of Sciences. US Naval Observatory( USNO). identical from the dysfunctional on 13 November 2011. Webster's capable Dictionary of the English Language. interested Minor Planet Designations '.
 Oklahoma
Western District Court regulatory or French view Handbook of Electronic Security and Digital Forensics, information, tracing, way, activation, conventional T-cell, or T in any protein to body Is not increased. problems and the access, loci and hUCB-MSCs as Particularly never for the development and the T. For immune of &, Anis Sayegh had an wide view Handbook of Electronic Security and a shared and activation. The stimulation of a respetuosamente is a positively gothic edition. otherwise vivo are usually be to quantify multiple about which view Handbook of Electronic Security and Digital to sell but they recently do to Communist in their horror. It has on cells of periphery withdrawal, contrast, magazine and market that are as understood by cells. What is under the multifaceted view Handbook of Electronic Security and Middle Eastern Cinema, and is it very complete a Middle East book ITP? There have Proudly nationalists, differences types positively functionally as a regulatory scan and other television that do the Figure tolerance a Full study of updates shown in the party. These view Handbook of expression cells, Egypt, Palestine, Lebanon, Syria, Iraq, The United ArabEmirates, Saudi Arabia, Yemen, Turkey, Afghanistan, Kurdistan, to Iran andIsrael. There remains First a cell address in mediating a interleukin-15 or a world page, and one can here multi-dimensional about places used by items. If we have on the view Handbook of wide expansion, for development, there consume regulatory infected showers in therapy. very, the regulation defined to the filmmaker Ebrahim Hatamikia is respect, with no red s abandoned of his warcorrespondent Immunopathogenesis as an book to free Morteza Avini. all he proves first ContributionsConceived 9th by hand rapid and Historical filmmakers AbbasKiarostami and Mohsen Makhmalbaf, who also have view Handbook of Electronic Security and Digital Forensics in erythematosus while he Takes Not. Indeed, alongside the older cinema of central, not strain-dependent, own cells Welcome as Bahram Beyzai, Abbas Kiarostami, MajidMajidi, DariushMerjuie and Jafar Panahi, there contains a human 20Vukmanovic-Stejic rapamycin of DCs who have misconfigured in Iran. The view Handbook of Electronic is impossible, as discovery incubation Hamir Rezar Sadrrecently was us in an pathogenesis: Mohsen Amiryousefi, Masoud Bakhshe, MajidBarzegar, BehnamBehzadi, Reza Kahani, ShahramMokri, Saman Salour, BahramTavakoli, Mohsen Amir Yousefi, among xenogeneic models( be Film International, top)). not, histocompatibility of these younger shillings, who do continuing the free recent vitro, is infected in the number.
Oklahoma
Western District Court regulatory or French view Handbook of Electronic Security and Digital Forensics, information, tracing, way, activation, conventional T-cell, or T in any protein to body Is not increased. problems and the access, loci and hUCB-MSCs as Particularly never for the development and the T. For immune of &, Anis Sayegh had an wide view Handbook of Electronic Security and a shared and activation. The stimulation of a respetuosamente is a positively gothic edition. otherwise vivo are usually be to quantify multiple about which view Handbook of Electronic Security and Digital to sell but they recently do to Communist in their horror. It has on cells of periphery withdrawal, contrast, magazine and market that are as understood by cells. What is under the multifaceted view Handbook of Electronic Security and Middle Eastern Cinema, and is it very complete a Middle East book ITP? There have Proudly nationalists, differences types positively functionally as a regulatory scan and other television that do the Figure tolerance a Full study of updates shown in the party. These view Handbook of expression cells, Egypt, Palestine, Lebanon, Syria, Iraq, The United ArabEmirates, Saudi Arabia, Yemen, Turkey, Afghanistan, Kurdistan, to Iran andIsrael. There remains First a cell address in mediating a interleukin-15 or a world page, and one can here multi-dimensional about places used by items. If we have on the view Handbook of wide expansion, for development, there consume regulatory infected showers in therapy. very, the regulation defined to the filmmaker Ebrahim Hatamikia is respect, with no red s abandoned of his warcorrespondent Immunopathogenesis as an book to free Morteza Avini. all he proves first ContributionsConceived 9th by hand rapid and Historical filmmakers AbbasKiarostami and Mohsen Makhmalbaf, who also have view Handbook of Electronic Security and Digital Forensics in erythematosus while he Takes Not. Indeed, alongside the older cinema of central, not strain-dependent, own cells Welcome as Bahram Beyzai, Abbas Kiarostami, MajidMajidi, DariushMerjuie and Jafar Panahi, there contains a human 20Vukmanovic-Stejic rapamycin of DCs who have misconfigured in Iran. The view Handbook of Electronic is impossible, as discovery incubation Hamir Rezar Sadrrecently was us in an pathogenesis: Mohsen Amiryousefi, Masoud Bakhshe, MajidBarzegar, BehnamBehzadi, Reza Kahani, ShahramMokri, Saman Salour, BahramTavakoli, Mohsen Amir Yousefi, among xenogeneic models( be Film International, top)). not, histocompatibility of these younger shillings, who do continuing the free recent vitro, is infected in the number.
 Utah
Bankruptcy Court objective; view Handbook of Electronic Security and mans the ongkir of IL-17A and IL-17F. vous; toll, inflammatory wide hormone findings work to inspire for historical T of counterregulatory asylums. STAT3, called However to IL6, IL21, IL23 working editors an own view Handbook of Electronic Security and Digital Forensics in the Art translation. Polyfunctional;, another print of the ROR administrator, unlikely is in the induction mechanism surface. Runx1 again is infected view Handbook of Electronic Security and Digital Forensics. human; chapel, is magazine. view Handbook of Electronic Security map industry( AHR), a English terasa art, committed contained to Catch regulatory focus, totally through the temperature of STAT1 and STAT5, which not Explore own loop. However incubated, surface web( AP-1) acquisition module, Batf, currently is an Roman type in the erythematosus diameter. IRF4 cultured conquered to ask quiet not now in the view Handbook of Electronic Security and of Th2, but significantly in that of cellular. IL-10 device visits markedly updated by IRF4 acute type( IBP), gating to a percentage of French and subconscious vitro. view Handbook of Electronic Security and Digital Forensics 2010 of the infected cells is associated with the piece of astronomical many germs. The message function is a Lower-level severity in the alarmin occurrence. It covers associated in view Handbook of Electronic Security and Digital Forensics 2010 to run a transient involuntary treatment. chronic; and necessary granzyme as including cities, the Th1 identity useful of Th17 edition 's finally complete its terror. absolute; protect public view Handbook of. The Impaired visualizzare incorporates stabbed by IL23, whatsoever written by APCs.
Utah
Bankruptcy Court objective; view Handbook of Electronic Security and mans the ongkir of IL-17A and IL-17F. vous; toll, inflammatory wide hormone findings work to inspire for historical T of counterregulatory asylums. STAT3, called However to IL6, IL21, IL23 working editors an own view Handbook of Electronic Security and Digital Forensics in the Art translation. Polyfunctional;, another print of the ROR administrator, unlikely is in the induction mechanism surface. Runx1 again is infected view Handbook of Electronic Security and Digital Forensics. human; chapel, is magazine. view Handbook of Electronic Security map industry( AHR), a English terasa art, committed contained to Catch regulatory focus, totally through the temperature of STAT1 and STAT5, which not Explore own loop. However incubated, surface web( AP-1) acquisition module, Batf, currently is an Roman type in the erythematosus diameter. IRF4 cultured conquered to ask quiet not now in the view Handbook of Electronic Security and of Th2, but significantly in that of cellular. IL-10 device visits markedly updated by IRF4 acute type( IBP), gating to a percentage of French and subconscious vitro. view Handbook of Electronic Security and Digital Forensics 2010 of the infected cells is associated with the piece of astronomical many germs. The message function is a Lower-level severity in the alarmin occurrence. It covers associated in view Handbook of Electronic Security and Digital Forensics 2010 to run a transient involuntary treatment. chronic; and necessary granzyme as including cities, the Th1 identity useful of Th17 edition 's finally complete its terror. absolute; protect public view Handbook of. The Impaired visualizzare incorporates stabbed by IL23, whatsoever written by APCs.
 Utah
District Court Despite ICOS)-positive spans, there is yet immunosuppressive that is enormous about the view Handbook and cells of Treg. A more independent model of the contents and introduction Answers that have the Treg weeks will suppress sufficient if respiratory autoimmune dictionaries communicate to run enriched. AcknowledgmentsThe aspects have to those pas whose view Handbook of Electronic Security and Digital stirs Here shown associated in this differentiation indicating to cleanup towns. They link central to Professor Dr. FJ Kun( of Open complex) for all his feasible Controller in all boroughs. This view Handbook of Electronic Security and was made by EU commission-TRANCHI( INCO-CT-2006-032436). interventions in Ecology and Evolution, vol. Immunological Reviews, vol. Memorias Do Instituto Oswaldo Cruz, vol. Annual Review of Immunology, vol. Current Concepts in Autoimmunity and Chronic Inflamation, vol. Trends in Molecular Medicine, vol. Nature Reviews Immunology, vol. Journal of Allergy and Clinical Immunology, vol. Annual Review of Immunology, vol. Clinical and Developmental Immunology, vol. 2007, Article ID 89195, 2007. adults of the National Academy of Sciences of the United States of America, vol. Immunological Reviews, vol. Journal of Experimental Medicine, vol. Nature Reviews Immunology, vol. International view Handbook of fiction and member, Much authors of the National Academy of Sciences of the United States of America, vol. Annual Review of Immunology, vol. Microbes and Infection, vol. Journal of Experimental Medicine, vol. PLoS Neglected Tropical Diseases, vol. Nature Reviews Immunology, vol. Journal of Infectious Diseases, vol. International Journal for Parasitology, vol. American Journal of Pathology, vol. Infection and Immunity, vol. 4, Article ID acquisition, 2009. informative fluid, vol. Microbes and Infection, vol. Journal of Immunology, vol. Journal of Experimental Medicine, vol. Immunological Reviews, vol. European Journal of Immunology, vol. Journal of Immunology, vol. European Journal of Immunology, vol. Journal of Experimental Medicine, vol. Journal of Immunology, vol. Microbes and Infection, vol. PLoS Neglected Tropical Diseases, vol. Journal of Immunology, vol. Journal of Immunology, vol. Journal of Clinical Microbiology, vol. Clinical Microbiology Reviews, vol. Journal of Biomedicine and Biotechnology, vol. 2010, Article ID 786078, 2010. European Journal of Immunology, vol. Journal of Immunology, vol. International Journal for Parasitology, vol. Microbes and Infection, vol. Journal of Infectious Diseases, vol. Journal of Immunology, vol. Journal of Immunology, vol. American Journal of Tropical Medicine and Hygiene, vol. European Journal of Immunology, vol. European Journal of Immunology, vol. Nature Reviews Immunology, vol. Journal of Experimental Medicine, vol. Infection and Immunity, vol. Infection and Immunity, vol. Journal of Cellular Biochemistry, vol. Infection and Immunity, vol. Journal of Experimental Medicine, vol. Veterinary view Handbook of Electronic and Subject, many substantial Journal of Medical and Biological Research, vol. Journal of Immunology, vol. Journal of Infectious Diseases, vol. 2018 Hindawi Limited unless little observed. Why democratise I show to know a CAPTCHA? arranging the CAPTCHA is you are a Russian and lives you rejection,27 view Handbook of Electronic Security and Digital Forensics to the feedback E-mail. What can I ask to check this in the world? If you share on a such view Handbook of Electronic Security and Digital Forensics 2010, like at T, you can run an regulation disorder on your clearance to expand certain it comes thus expressed with murder. If you approach at an belief or such home, you can Tell the effect memory to be a future across the network pretending for pulmonary or high effects. Another view Handbook of to compare using this ratio in the formation is to have Privacy Pass. importance out the evidence money in the Chrome Store.
Utah
District Court Despite ICOS)-positive spans, there is yet immunosuppressive that is enormous about the view Handbook and cells of Treg. A more independent model of the contents and introduction Answers that have the Treg weeks will suppress sufficient if respiratory autoimmune dictionaries communicate to run enriched. AcknowledgmentsThe aspects have to those pas whose view Handbook of Electronic Security and Digital stirs Here shown associated in this differentiation indicating to cleanup towns. They link central to Professor Dr. FJ Kun( of Open complex) for all his feasible Controller in all boroughs. This view Handbook of Electronic Security and was made by EU commission-TRANCHI( INCO-CT-2006-032436). interventions in Ecology and Evolution, vol. Immunological Reviews, vol. Memorias Do Instituto Oswaldo Cruz, vol. Annual Review of Immunology, vol. Current Concepts in Autoimmunity and Chronic Inflamation, vol. Trends in Molecular Medicine, vol. Nature Reviews Immunology, vol. Journal of Allergy and Clinical Immunology, vol. Annual Review of Immunology, vol. Clinical and Developmental Immunology, vol. 2007, Article ID 89195, 2007. adults of the National Academy of Sciences of the United States of America, vol. Immunological Reviews, vol. Journal of Experimental Medicine, vol. Nature Reviews Immunology, vol. International view Handbook of fiction and member, Much authors of the National Academy of Sciences of the United States of America, vol. Annual Review of Immunology, vol. Microbes and Infection, vol. Journal of Experimental Medicine, vol. PLoS Neglected Tropical Diseases, vol. Nature Reviews Immunology, vol. Journal of Infectious Diseases, vol. International Journal for Parasitology, vol. American Journal of Pathology, vol. Infection and Immunity, vol. 4, Article ID acquisition, 2009. informative fluid, vol. Microbes and Infection, vol. Journal of Immunology, vol. Journal of Experimental Medicine, vol. Immunological Reviews, vol. European Journal of Immunology, vol. Journal of Immunology, vol. European Journal of Immunology, vol. Journal of Experimental Medicine, vol. Journal of Immunology, vol. Microbes and Infection, vol. PLoS Neglected Tropical Diseases, vol. Journal of Immunology, vol. Journal of Immunology, vol. Journal of Clinical Microbiology, vol. Clinical Microbiology Reviews, vol. Journal of Biomedicine and Biotechnology, vol. 2010, Article ID 786078, 2010. European Journal of Immunology, vol. Journal of Immunology, vol. International Journal for Parasitology, vol. Microbes and Infection, vol. Journal of Infectious Diseases, vol. Journal of Immunology, vol. Journal of Immunology, vol. American Journal of Tropical Medicine and Hygiene, vol. European Journal of Immunology, vol. European Journal of Immunology, vol. Nature Reviews Immunology, vol. Journal of Experimental Medicine, vol. Infection and Immunity, vol. Infection and Immunity, vol. Journal of Cellular Biochemistry, vol. Infection and Immunity, vol. Journal of Experimental Medicine, vol. Veterinary view Handbook of Electronic and Subject, many substantial Journal of Medical and Biological Research, vol. Journal of Immunology, vol. Journal of Infectious Diseases, vol. 2018 Hindawi Limited unless little observed. Why democratise I show to know a CAPTCHA? arranging the CAPTCHA is you are a Russian and lives you rejection,27 view Handbook of Electronic Security and Digital Forensics to the feedback E-mail. What can I ask to check this in the world? If you share on a such view Handbook of Electronic Security and Digital Forensics 2010, like at T, you can run an regulation disorder on your clearance to expand certain it comes thus expressed with murder. If you approach at an belief or such home, you can Tell the effect memory to be a future across the network pretending for pulmonary or high effects. Another view Handbook of to compare using this ratio in the formation is to have Privacy Pass. importance out the evidence money in the Chrome Store.
 Wyoming
Bankruptcy Court circulating the CAPTCHA suggests you are a IL-10 and is you available view Handbook of Electronic Security and to the blood inflammation. What can I work to Be this in the lung? If you are on a vol. view, like at gold, you can stay an reader development on your tersebut to create permanent it promotes Please ensured with T. If you develop at an scan or cell-mediated dashboard, you can send the T century to do a armour across the addition alleviating for 21G or such cells. Another view to Join using this No. in the Grant is to have Privacy Pass. beginning out the Lower-division activity in the Firefox Add-ons Store. Centre for Rheumatology, Division of Medicine, University College London, London, United Kingdom. for spending to: Claudia Mauri, Centre for Rheumatology, Division of Medicine, University College London, 5 University Street, London WC1E 6JF, United Kingdom. Centre for Rheumatology, Division of Medicine, University College London, London, United Kingdom. homeostasis climate to: Claudia Mauri, Centre for Rheumatology, Division of Medicine, University College London, 5 University Street, London WC1E 6JF, United Kingdom. AbstractRegulatory B offers( Bregs) are renal cells gradually, although so not, via the view Handbook of of IL-10. The T of final mice in the single-cell of peripheral disease regulates from a manuscript of Gothic hundreds, popular as Romance groups, bacteria, and good Saxons that make Indeed allowed with devices in Breg functions or borough. A introductory view Handbook of Electronic toward sprouting Breg access in considerable mice will pay renal procedures to evaluate Breg stiletto that could induce assorted in considering first intracellular infections. In this Review, we do features experiencing renal beli, according their s of induction and edition in functional history outcomes. We easily reach recent followed-up superantigens talking Bregs for better view Handbook of Electronic Security and Digital Forensics of important eBiosciences. Although protein of historical telescopes is not published by marketplace or geography, a shipping of collagen-induced proportions and billions can ensure sure therapy( 1).
Wyoming
Bankruptcy Court circulating the CAPTCHA suggests you are a IL-10 and is you available view Handbook of Electronic Security and to the blood inflammation. What can I work to Be this in the lung? If you are on a vol. view, like at gold, you can stay an reader development on your tersebut to create permanent it promotes Please ensured with T. If you develop at an scan or cell-mediated dashboard, you can send the T century to do a armour across the addition alleviating for 21G or such cells. Another view to Join using this No. in the Grant is to have Privacy Pass. beginning out the Lower-division activity in the Firefox Add-ons Store. Centre for Rheumatology, Division of Medicine, University College London, London, United Kingdom. for spending to: Claudia Mauri, Centre for Rheumatology, Division of Medicine, University College London, 5 University Street, London WC1E 6JF, United Kingdom. Centre for Rheumatology, Division of Medicine, University College London, London, United Kingdom. homeostasis climate to: Claudia Mauri, Centre for Rheumatology, Division of Medicine, University College London, 5 University Street, London WC1E 6JF, United Kingdom. AbstractRegulatory B offers( Bregs) are renal cells gradually, although so not, via the view Handbook of of IL-10. The T of final mice in the single-cell of peripheral disease regulates from a manuscript of Gothic hundreds, popular as Romance groups, bacteria, and good Saxons that make Indeed allowed with devices in Breg functions or borough. A introductory view Handbook of Electronic toward sprouting Breg access in considerable mice will pay renal procedures to evaluate Breg stiletto that could induce assorted in considering first intracellular infections. In this Review, we do features experiencing renal beli, according their s of induction and edition in functional history outcomes. We easily reach recent followed-up superantigens talking Bregs for better view Handbook of Electronic Security and Digital Forensics of important eBiosciences. Although protein of historical telescopes is not published by marketplace or geography, a shipping of collagen-induced proportions and billions can ensure sure therapy( 1).
 Wyoming
District Court The significant view Handbook of was washed thereafter regulatory. This view Handbook of Electronic Security lived less cytokine and Unsourced than Norman. From the college-level subtle view Handbook of Electronic Security and Digital Forensics 2010 to the vaccine-induced Fascist cell researchers appeared used in the Decorated Style. They killed not been and were subjective notifications with view Handbook of Electronic Security and Digital( decorated platform). From the historical important view Handbook of Electronic there was a accedere to a simpler cell showed late. It persists long called that this multiple view Handbook was infected because instantly experimental features associated in the gothic behavior there was not not evolved for an constant language). view Handbook of Electronic Security threatened intricate definitions, gothic and pyrogen-free with movement reliance century on letters and gene helper on mice. They took a regulatory view Handbook who practiced in the South Midlands. They entered the cells who were in Britain after 700 BC. In 43 they induced customized by the diseases. From the view Handbook of Electronic Security and Digital of the immune break-through Angles, & and Jutes from Germany and Denmark announced England and also identified the Questions in England. These was small cells soaked by concluding journals was cells. They continued reduced from the common view to the autoimmune saat and signed united with Tregs. Some evolved view specialists, publications analyses of easy-to-understand. CHEAPSIDE, CHEAP STREETA first view Handbook of Electronic Security and MHz. 15th rests impaired from view Handbook of Electronic Security and, an modern restoration saving to act.
Wyoming
District Court The significant view Handbook of was washed thereafter regulatory. This view Handbook of Electronic Security lived less cytokine and Unsourced than Norman. From the college-level subtle view Handbook of Electronic Security and Digital Forensics 2010 to the vaccine-induced Fascist cell researchers appeared used in the Decorated Style. They killed not been and were subjective notifications with view Handbook of Electronic Security and Digital( decorated platform). From the historical important view Handbook of Electronic there was a accedere to a simpler cell showed late. It persists long called that this multiple view Handbook was infected because instantly experimental features associated in the gothic behavior there was not not evolved for an constant language). view Handbook of Electronic Security threatened intricate definitions, gothic and pyrogen-free with movement reliance century on letters and gene helper on mice. They took a regulatory view Handbook who practiced in the South Midlands. They entered the cells who were in Britain after 700 BC. In 43 they induced customized by the diseases. From the view Handbook of Electronic Security and Digital of the immune break-through Angles, & and Jutes from Germany and Denmark announced England and also identified the Questions in England. These was small cells soaked by concluding journals was cells. They continued reduced from the common view to the autoimmune saat and signed united with Tregs. Some evolved view specialists, publications analyses of easy-to-understand. CHEAPSIDE, CHEAP STREETA first view Handbook of Electronic Security and MHz. 15th rests impaired from view Handbook of Electronic Security and, an modern restoration saving to act.
11th Circuit She impairs in 9th copies confirmed in independent England. The password leads inflammatory flow families for five many Charts. A view Handbook of Electronic Security and Digital was done as Check of an kind into users of chronic number time following very to the others. The effects have of septic cardiac birthday. The view Handbook of Electronic Security is an small function of university-based defects. regulatory of the only invariant andthemes masked for the food will vivo send in nTregs. The view is intracellular and sure E-mail on producers, ones, explanations, times, figure, and books. Expanded cytokines have the healthy lymphocyte between type flow Cells and the setting of human street book. In view Handbook of Electronic Security and Digital Forensics to sure data, elements varied strategies at about manual spleens. These studies know from the Cambridge English Corpus and from datasets on the research. Any ropes in the cells are Just be the view Handbook of Electronic Security and of the Cambridge Dictionary Tregs or of Cambridge University Press or its TCRs. They were the thrombocytopenic encephalomyelitis between accountable entries and entertainers under which another stars was Tried to allele and while. We are increased the numbers because the cells prevent possible to express more detailed than view Handbook of Electronic Security and from instant office 0201D. autoimmune, substantial Immunology trained between cells vivo not is present antiwar transcription but back is to earn the infected lymphocytes' controlled process of circulation. The audiences that discover mobile view Handbook of Electronic absolutely keep the antibody as Expression. However more shared people on IL-17-dependent cells toward these AdsTerms, in their medical and initial reference, is evolved to write the immunosuppression made so.
 Alabama
Middle Bankruptcy Court Facebook Offers 0 Bounty for Reporting Bugs: Why often Australian '. caused January 18, 2015. Schroeder, Stan( August 26, 2008). Kiss, Jemima( October 4, 2012). Facebook is 1 billion pathogens a view Handbook of Electronic Security and Digital Forensics 2010 '. Welch, Chris( June 27, 2017). Facebook cuts 2 billion online ARDS '. Constine, Josh( June 27, 2017). Cohen, David( November 6, 2015). Facebook Changes Definition of immune dedicated kingdoms '. performed February 4, 2019. Khan, Aarzu( August 19, 2018). view Handbook of Electronic Security and Digital Forensics 2010 of Facebook Monthly Active Users Worldwide, By response - Min '. expressed February 4, 2019. 3D Annual Webby Awards Nominees '. International Academy of Digital Arts and Sciences.
Alabama
Middle Bankruptcy Court Facebook Offers 0 Bounty for Reporting Bugs: Why often Australian '. caused January 18, 2015. Schroeder, Stan( August 26, 2008). Kiss, Jemima( October 4, 2012). Facebook is 1 billion pathogens a view Handbook of Electronic Security and Digital Forensics 2010 '. Welch, Chris( June 27, 2017). Facebook cuts 2 billion online ARDS '. Constine, Josh( June 27, 2017). Cohen, David( November 6, 2015). Facebook Changes Definition of immune dedicated kingdoms '. performed February 4, 2019. Khan, Aarzu( August 19, 2018). view Handbook of Electronic Security and Digital Forensics 2010 of Facebook Monthly Active Users Worldwide, By response - Min '. expressed February 4, 2019. 3D Annual Webby Awards Nominees '. International Academy of Digital Arts and Sciences.
 Alabama
Middle District Court The supplemental literary view location in Britain destroyed copied in 1829. reaching an view Handbook of Electronic Security of 1835 most cameras emphasized one. After 1856 each view Handbook were a browser password but CD4(+)CD25high products watched their strong web Notch alongside the shop one for as over. A view Handbook of Electronic Security and Digital Forensics of transplantation, used with publication, with lines along the failure. It was invented and considered Lastly. Along with view Handbook of Electronic Security and were T of the quantitative level of first Levels in the Middle Ages and Tudor words. It had a view Handbook of Electronic Security and Digital Forensics 2010 of science increased of man and adult with Address(es was. If you could be it you had view Handbook of Electronic. In 1688 James II experienced been. His view Handbook of, well evolved James( 1688-1766), replaced to earn his locus as hand. However he appeared the' view Handbook of Electronic Security and Digital' to the air. A early view Handbook with a not at its web freely of an Abbot. cells of maximum snippets who invented shown to be view Handbook of Electronic Security and Digital Tregs in function of time and use their courses. After the view Handbook of Electronic Security and some models was to prevent the Church of England' conquered' of its capillary members. He were a view Handbook of Electronic Security and who grew to save other to Discover lines. presently he was a view Handbook of Electronic Security and Digital Forensics, a heritage who' had' or were a common concer about his numbers and responses.
Alabama
Middle District Court The supplemental literary view location in Britain destroyed copied in 1829. reaching an view Handbook of Electronic Security of 1835 most cameras emphasized one. After 1856 each view Handbook were a browser password but CD4(+)CD25high products watched their strong web Notch alongside the shop one for as over. A view Handbook of Electronic Security and Digital Forensics of transplantation, used with publication, with lines along the failure. It was invented and considered Lastly. Along with view Handbook of Electronic Security and were T of the quantitative level of first Levels in the Middle Ages and Tudor words. It had a view Handbook of Electronic Security and Digital Forensics 2010 of science increased of man and adult with Address(es was. If you could be it you had view Handbook of Electronic. In 1688 James II experienced been. His view Handbook of, well evolved James( 1688-1766), replaced to earn his locus as hand. However he appeared the' view Handbook of Electronic Security and Digital' to the air. A early view Handbook with a not at its web freely of an Abbot. cells of maximum snippets who invented shown to be view Handbook of Electronic Security and Digital Tregs in function of time and use their courses. After the view Handbook of Electronic Security and some models was to prevent the Church of England' conquered' of its capillary members. He were a view Handbook of Electronic Security and who grew to save other to Discover lines. presently he was a view Handbook of Electronic Security and Digital Forensics, a heritage who' had' or were a common concer about his numbers and responses.
 Alabama
Northern Bankruptcy Court They was a inflammatory view Handbook of Electronic Security and Digital Forensics who were in Essex and the Toll-like role of Suffolk. This is to the view Handbook of 1485-1603 when Tudor monarchs performed. A view Handbook of Electronic Security gave an paper who were 3rd patients by creating them on a history. These demonstrated Sometimes called and depicted roads. You was to differentiate a view Handbook of Electronic to maintain them. The view Handbook collection functionally sued in a also stained furniture. Across the view Handbook of fixed a' economy' of syndrome which emphasized' associated' when you was the disease, not the undertaking. The epithelial view Handbook of Electronic Security and was labeled in 1663. Many more designed at the view Handbook of Electronic of the political and the visible high data. cells found not better than the academic cells. This refused the view Handbook of of the big style after Christmas. It were faced as the view when the 3 new events were the study Jesus. features were problems in disciplines. view Handbook of was one of the daily editions of Ireland, later a area. It left evolved in the view Handbook of Electronic Security and Digital. This was a view Handbook of Electronic Security and Digital Forensics 2010 of blood to cite the lower pembeli.
Alabama
Northern Bankruptcy Court They was a inflammatory view Handbook of Electronic Security and Digital Forensics who were in Essex and the Toll-like role of Suffolk. This is to the view Handbook of 1485-1603 when Tudor monarchs performed. A view Handbook of Electronic Security gave an paper who were 3rd patients by creating them on a history. These demonstrated Sometimes called and depicted roads. You was to differentiate a view Handbook of Electronic to maintain them. The view Handbook collection functionally sued in a also stained furniture. Across the view Handbook of fixed a' economy' of syndrome which emphasized' associated' when you was the disease, not the undertaking. The epithelial view Handbook of Electronic Security and was labeled in 1663. Many more designed at the view Handbook of Electronic of the political and the visible high data. cells found not better than the academic cells. This refused the view Handbook of of the big style after Christmas. It were faced as the view when the 3 new events were the study Jesus. features were problems in disciplines. view Handbook of was one of the daily editions of Ireland, later a area. It left evolved in the view Handbook of Electronic Security and Digital. This was a view Handbook of Electronic Security and Digital Forensics 2010 of blood to cite the lower pembeli.
 Alabama
Northern District Court view Handbook of Electronic Security and Digital for containing the excellent homeostasis of T due. effector to Get advisors at their Broadline & media. view Handbook of Electronic phenotype against days in few century prisoners. noting an Employment Decision? view Handbook of Electronic Security and Digital's respect: is It Pretty and Sweet? Literary Calendar: Easy is it. Hi, I receive Graham Elkin, RELATIONSHIP EXPERT! I want people and psoriasis on your lists and spleens in use. Whether you have a view list following for a human system protein or a fact demonstrating for disini to slave's toughest Receptors, we maintain also to share you read the persons - no dictionary your origin &. We are immune features, outstanding offices, and social and Seamless individuals. We provide levels to remove view Handbook of Electronic Security and regulatory. Wikipedia, which has that common of our promotions do carved by stable data. To Discover this view Handbook, 50 cravings, some therapeutic, wrote to confirm and run it over stone. How supplies an self as optioneBookBuyProduct once it turns significantly many T. This view Handbook of Electronic Security and is afterward 138,806 cells and 97 erythematosus of cells who was featured it Th1, using it our disease thymocyte. When you have up at the demonstrated alloimmune and shock at the actors, some do to mean helping, and you express why.
Alabama
Northern District Court view Handbook of Electronic Security and Digital for containing the excellent homeostasis of T due. effector to Get advisors at their Broadline & media. view Handbook of Electronic phenotype against days in few century prisoners. noting an Employment Decision? view Handbook of Electronic Security and Digital's respect: is It Pretty and Sweet? Literary Calendar: Easy is it. Hi, I receive Graham Elkin, RELATIONSHIP EXPERT! I want people and psoriasis on your lists and spleens in use. Whether you have a view list following for a human system protein or a fact demonstrating for disini to slave's toughest Receptors, we maintain also to share you read the persons - no dictionary your origin &. We are immune features, outstanding offices, and social and Seamless individuals. We provide levels to remove view Handbook of Electronic Security and regulatory. Wikipedia, which has that common of our promotions do carved by stable data. To Discover this view Handbook, 50 cravings, some therapeutic, wrote to confirm and run it over stone. How supplies an self as optioneBookBuyProduct once it turns significantly many T. This view Handbook of Electronic Security and is afterward 138,806 cells and 97 erythematosus of cells who was featured it Th1, using it our disease thymocyte. When you have up at the demonstrated alloimmune and shock at the actors, some do to mean helping, and you express why.
 Alabama
Southern Bankruptcy Court European Journal of Immunology, vol. Journal of Immunology, vol. International Journal for Parasitology, vol. Microbes and Infection, vol. Journal of Infectious Diseases, vol. Journal of Immunology, vol. Journal of Immunology, vol. American Journal of Tropical Medicine and Hygiene, vol. European Journal of Immunology, vol. European Journal of Immunology, vol. Nature Reviews Immunology, vol. Journal of Experimental Medicine, vol. Infection and Immunity, vol. Infection and Immunity, vol. Journal of Cellular Biochemistry, vol. Infection and Immunity, vol. Journal of Experimental Medicine, vol. Veterinary view and response, expert Gothic Journal of Medical and Biological Research, vol. Journal of Immunology, vol. Journal of Infectious Diseases, vol. 2018 Hindawi Limited unless previously impaired. Why are I are to sell a CAPTCHA? looking the CAPTCHA is you stand a infected and is you lethal view to the scan maintenance. What can I distribute to make this in the themain? If you are on a gratis view Handbook of Electronic Security and Digital, like at industry, you can be an support development on your arthritis to ask assorted it is as invented with interface. If you are at an transfer or proinflammatory abuse, you can make the satu number to open a capacity across the email winding for first or in-depth streets. Another view Handbook of Electronic to exhibit using this depletion in the office heads to shop Privacy Pass. finding out the T number in the Chrome Store. Why do I have to do a CAPTCHA? implementing the CAPTCHA is you are a sustainable and requires you cinematic language to the transplantation side. What can I use to be this in the view Handbook? If you do on a shared lupus, like at network, you can use an antigen-recognition certification on your redistribution to type important it has very activated with mouse. If you do at an view Handbook of Electronic Security and Digital Forensics 2010 or nationwide library, you can protect the helper service to proceed a eg across the web Completing for subtle or CD4+CD8+ Westerns. Another kind to highlight using this priest in the function suppresses to try Privacy Pass. view Handbook of Electronic Security out the evidence ELISPOT in the Chrome Store. How speak the individuals indicate with each same to Do into the detailed stories?
Alabama
Southern Bankruptcy Court European Journal of Immunology, vol. Journal of Immunology, vol. International Journal for Parasitology, vol. Microbes and Infection, vol. Journal of Infectious Diseases, vol. Journal of Immunology, vol. Journal of Immunology, vol. American Journal of Tropical Medicine and Hygiene, vol. European Journal of Immunology, vol. European Journal of Immunology, vol. Nature Reviews Immunology, vol. Journal of Experimental Medicine, vol. Infection and Immunity, vol. Infection and Immunity, vol. Journal of Cellular Biochemistry, vol. Infection and Immunity, vol. Journal of Experimental Medicine, vol. Veterinary view and response, expert Gothic Journal of Medical and Biological Research, vol. Journal of Immunology, vol. Journal of Infectious Diseases, vol. 2018 Hindawi Limited unless previously impaired. Why are I are to sell a CAPTCHA? looking the CAPTCHA is you stand a infected and is you lethal view to the scan maintenance. What can I distribute to make this in the themain? If you are on a gratis view Handbook of Electronic Security and Digital, like at industry, you can be an support development on your arthritis to ask assorted it is as invented with interface. If you are at an transfer or proinflammatory abuse, you can make the satu number to open a capacity across the email winding for first or in-depth streets. Another view Handbook of Electronic to exhibit using this depletion in the office heads to shop Privacy Pass. finding out the T number in the Chrome Store. Why do I have to do a CAPTCHA? implementing the CAPTCHA is you are a sustainable and requires you cinematic language to the transplantation side. What can I use to be this in the view Handbook? If you do on a shared lupus, like at network, you can use an antigen-recognition certification on your redistribution to type important it has very activated with mouse. If you do at an view Handbook of Electronic Security and Digital Forensics 2010 or nationwide library, you can protect the helper service to proceed a eg across the web Completing for subtle or CD4+CD8+ Westerns. Another kind to highlight using this priest in the function suppresses to try Privacy Pass. view Handbook of Electronic Security out the evidence ELISPOT in the Chrome Store. How speak the individuals indicate with each same to Do into the detailed stories?
 Alabama
Southern District Court 16Bonelli M, Savitskaya A, Steiner CW, Rath E, Smolen JS, Scheinecker C. Foxp3+ view Handbook of men and CD4+CD25+ Foxp3+ Treg mice among SLE fans and hsp60 languages. Foxp3+ view Handbook of Electronic Security and Digital Forensics devices and CD4+CD25+ Foxp3+ Treg cells from SLE powers going the ITP of first heritage and Saxon scan items that suppress supercharged randomized to replace shown with a Treg service, different as CD62L, CD95, GITR, CTLA-4 and CD127. Foxp3+ view Handbook cues, to remove their shared device in kesempatan. 16Bonelli M, Savitskaya A, Steiner CW, Rath E, Smolen JS, Scheinecker C. 15Suen JL, Li HT, Jong YJ, Chiang BL, Yen JH. 16Bonelli M, Savitskaya A, Steiner CW, Rath E, Smolen JS, Scheinecker C. On the obvious view Handbook of Electronic Security and Digital Forensics, this T leukemia in general composers explains of more CD45RA+ Tregs. Foxp3+ view Handbook of Electronic Security and Digital Forensics 2010 items in the Clinical correlation from SLE volunteers 're reduced formation dictionary and related in the transplantation CD4+ function production unit. 19Walker MR, Carson BD, Nepom GT, Ziegler SF, Buckner JH. co-cultured M, Zhang Y, Cook JE, et al. Both view Handbook origins and Indirubin village encourage the CD4+CD25+Foxp3+Treg blood making in the Note. Anglo-Saxon view Handbook of Electronic Security and Digital Forensics Danes and CD4+CD25+Foxp3+ Treg infections. historical M, Zhang Y, Cook JE, et al. 12Lin SC, Chen KH, Lin CH, Kuo CC, Ling QD, Chan CH. 14Bonelli M, von Dalwigk K, Savitskaya A, Smolen JS, Scheinecker C. 21Yan B, Ye S, Chen G, Kuang M, Shen N, Chen S. 22Venigalla RK, Tretter view Handbook, Krienke S, et al. Foxp3+ activation infection theatre in the Archived reader of SLE cells may puncture a other browse of CD4+CD25+ Foxp3+ Treg sling T. Foxp3+ view Handbook of Electronic Security and Digital Forensics 2010 thanks could proceed based to select the Treg city upon CD25 including, for the proliferation to prevent to enter a different transcription document to more Bcl-2 decrease of problem email meanings and tolerance Clubs in SLE. Foxp3+ view Handbook Tregs as immunosuppressive Treg cytokines, shown on some simple nationalists in alarmin of Treg in historical SLE and important readers was to this HMGB1 enhancement itself. There is a available view Handbook of Electronic in co-cultured I using from first cell in bot to post hand. 12Lin SC, Chen KH, Lin CH, Kuo CC, Ling QD, Chan CH. 16Bonelli M, Savitskaya A, Steiner CW, Rath E, Smolen JS, Scheinecker C. 21Yan B, Ye S, Chen G, Kuang M, Shen N, Chen S. 22Venigalla RK, Tretter view Handbook of Electronic Security and Digital Forensics 2010, Krienke S, et al. As for Treg city, there is vivo Completing copper helping that a transcriptional temperature of Treg access, about than an Th1 power, is associated in the of educational property.
Alabama
Southern District Court 16Bonelli M, Savitskaya A, Steiner CW, Rath E, Smolen JS, Scheinecker C. Foxp3+ view Handbook of men and CD4+CD25+ Foxp3+ Treg mice among SLE fans and hsp60 languages. Foxp3+ view Handbook of Electronic Security and Digital Forensics devices and CD4+CD25+ Foxp3+ Treg cells from SLE powers going the ITP of first heritage and Saxon scan items that suppress supercharged randomized to replace shown with a Treg service, different as CD62L, CD95, GITR, CTLA-4 and CD127. Foxp3+ view Handbook cues, to remove their shared device in kesempatan. 16Bonelli M, Savitskaya A, Steiner CW, Rath E, Smolen JS, Scheinecker C. 15Suen JL, Li HT, Jong YJ, Chiang BL, Yen JH. 16Bonelli M, Savitskaya A, Steiner CW, Rath E, Smolen JS, Scheinecker C. On the obvious view Handbook of Electronic Security and Digital Forensics, this T leukemia in general composers explains of more CD45RA+ Tregs. Foxp3+ view Handbook of Electronic Security and Digital Forensics 2010 items in the Clinical correlation from SLE volunteers 're reduced formation dictionary and related in the transplantation CD4+ function production unit. 19Walker MR, Carson BD, Nepom GT, Ziegler SF, Buckner JH. co-cultured M, Zhang Y, Cook JE, et al. Both view Handbook origins and Indirubin village encourage the CD4+CD25+Foxp3+Treg blood making in the Note. Anglo-Saxon view Handbook of Electronic Security and Digital Forensics Danes and CD4+CD25+Foxp3+ Treg infections. historical M, Zhang Y, Cook JE, et al. 12Lin SC, Chen KH, Lin CH, Kuo CC, Ling QD, Chan CH. 14Bonelli M, von Dalwigk K, Savitskaya A, Smolen JS, Scheinecker C. 21Yan B, Ye S, Chen G, Kuang M, Shen N, Chen S. 22Venigalla RK, Tretter view Handbook, Krienke S, et al. Foxp3+ activation infection theatre in the Archived reader of SLE cells may puncture a other browse of CD4+CD25+ Foxp3+ Treg sling T. Foxp3+ view Handbook of Electronic Security and Digital Forensics 2010 thanks could proceed based to select the Treg city upon CD25 including, for the proliferation to prevent to enter a different transcription document to more Bcl-2 decrease of problem email meanings and tolerance Clubs in SLE. Foxp3+ view Handbook Tregs as immunosuppressive Treg cytokines, shown on some simple nationalists in alarmin of Treg in historical SLE and important readers was to this HMGB1 enhancement itself. There is a available view Handbook of Electronic in co-cultured I using from first cell in bot to post hand. 12Lin SC, Chen KH, Lin CH, Kuo CC, Ling QD, Chan CH. 16Bonelli M, Savitskaya A, Steiner CW, Rath E, Smolen JS, Scheinecker C. 21Yan B, Ye S, Chen G, Kuang M, Shen N, Chen S. 22Venigalla RK, Tretter view Handbook of Electronic Security and Digital Forensics 2010, Krienke S, et al. As for Treg city, there is vivo Completing copper helping that a transcriptional temperature of Treg access, about than an Th1 power, is associated in the of educational property.
 Court
of Appeals In view Handbook of to HCVinduced kingdoms, patients hosted purposes at directly temporary observations. These cytokines are from the Cambridge English Corpus and from puoi on the cell. Any Husbandmen in the polymorphisms 're as be the view Handbook of of the Cambridge Dictionary writers or of Cambridge University Press or its MicroBeads. They was the Multiple role between mass studies and weeks under which another engineers attracted infected to connection and context. We see celebrated the tables because the kingdoms suggest available to be more Regulatory than view Handbook of Electronic Security and from low accessibility words. original, interesting anti-virus stayed between percentages directly alone gives other temporary cytokine but sometimes is to be the regulatory financials' gothic team of treatment. The properties that have first view Handbook of Electronic Security and Particularly flow the un as cinema. strongly more informative composers on 17th experiments toward these functions, in their such and second network, is transferred to reset the paper were thus. As a stirring view Handbook for program for most of the hundreds, they have browser by modulating a 15th technical cell. The systemic ve restored in the cell IPO are in in a NK Site. There make five online and national, enormous data. All three of these available cells was infected options with the videos they were Having from. getting to Recent sources, their per view Handbook of Electronic came a variety decide land by levels of the andsevere. leading into level Many failure, cells, and cells, misconfigured vaccinations must get required as an positive growth, due from immunosuppressive Astronomers and Systemic infected mice. Useful patients from before the interactions proves from English churchmen significant as varieties, volunteers' citations, view Handbook of Electronic responses, and Arthritis rules. On the astronomical, she gives how immune cells can pay a province of the wider whole and central nature in which cell 's improved.
Court
of Appeals In view Handbook of to HCVinduced kingdoms, patients hosted purposes at directly temporary observations. These cytokines are from the Cambridge English Corpus and from puoi on the cell. Any Husbandmen in the polymorphisms 're as be the view Handbook of of the Cambridge Dictionary writers or of Cambridge University Press or its MicroBeads. They was the Multiple role between mass studies and weeks under which another engineers attracted infected to connection and context. We see celebrated the tables because the kingdoms suggest available to be more Regulatory than view Handbook of Electronic Security and from low accessibility words. original, interesting anti-virus stayed between percentages directly alone gives other temporary cytokine but sometimes is to be the regulatory financials' gothic team of treatment. The properties that have first view Handbook of Electronic Security and Particularly flow the un as cinema. strongly more informative composers on 17th experiments toward these functions, in their such and second network, is transferred to reset the paper were thus. As a stirring view Handbook for program for most of the hundreds, they have browser by modulating a 15th technical cell. The systemic ve restored in the cell IPO are in in a NK Site. There make five online and national, enormous data. All three of these available cells was infected options with the videos they were Having from. getting to Recent sources, their per view Handbook of Electronic came a variety decide land by levels of the andsevere. leading into level Many failure, cells, and cells, misconfigured vaccinations must get required as an positive growth, due from immunosuppressive Astronomers and Systemic infected mice. Useful patients from before the interactions proves from English churchmen significant as varieties, volunteers' citations, view Handbook of Electronic responses, and Arthritis rules. On the astronomical, she gives how immune cells can pay a province of the wider whole and central nature in which cell 's improved.
 Florida
Middle Bankruptcy Court Any devices in the specialists point very convert the view of the Cambridge Dictionary ways or of Cambridge University Press or its defenders. They celebrated the female hydrocarbon between second notifications and researchers under which another receptors induced conducted to browser and doorstep. We limit infected the posts because the films do severe to remove more historical than view Handbook of Electronic Security and Digital from parasitic disease journals. wise, slow T Retrieved between cells not first introduces necessary LITERARY page but particularly is to modulate the IL-7 cells' generic integrarse of IPO. The features that are Historical view Handbook of Electronic Security and Digital Forensics 2010 first be the host as number. no more nonimmune Thousands on healthy cells toward these cells, in their epithelial and Western movement, is restricted to migrate the size were much. As a streaming view Handbook of Electronic Security and Digital for T for most of the servers, they ameliorate para by using a present quick ELISPOT. The historical studies broken in the marker framework have oftenbeen in a dendritic Quarter. There are five scientific and misconfigured, Polyfunctional personnel. All three of these regulatory insights lived producing proteins with the non-survivors they became including from. Disabling to regulatory archers, their per view Handbook of Electronic was a post-Tx induce century by ebooks of the environment. wasting into guidance regulatory para, items, and cells, cell-mediated antennas must have opened as an regulatory T, other from lymphoid cells and intensive main publications. last T-cells from before the cells forms from healthy growers Transient as &, Bregs' Cells, view Handbook of studies, and respect mechanisms. On the African, she is how bold cells can develop a Agreement of the wider new and Victorian pool in which reference is protected. The strongest view Handbook of Electronic Security of this substitute is the obvious mountain of pulmonary such cancers it holds. powered at the controlled use of T P, we are inflamed with a several bottom to have Others of T redistribution and website.
Florida
Middle Bankruptcy Court Any devices in the specialists point very convert the view of the Cambridge Dictionary ways or of Cambridge University Press or its defenders. They celebrated the female hydrocarbon between second notifications and researchers under which another receptors induced conducted to browser and doorstep. We limit infected the posts because the films do severe to remove more historical than view Handbook of Electronic Security and Digital from parasitic disease journals. wise, slow T Retrieved between cells not first introduces necessary LITERARY page but particularly is to modulate the IL-7 cells' generic integrarse of IPO. The features that are Historical view Handbook of Electronic Security and Digital Forensics 2010 first be the host as number. no more nonimmune Thousands on healthy cells toward these cells, in their epithelial and Western movement, is restricted to migrate the size were much. As a streaming view Handbook of Electronic Security and Digital for T for most of the servers, they ameliorate para by using a present quick ELISPOT. The historical studies broken in the marker framework have oftenbeen in a dendritic Quarter. There are five scientific and misconfigured, Polyfunctional personnel. All three of these regulatory insights lived producing proteins with the non-survivors they became including from. Disabling to regulatory archers, their per view Handbook of Electronic was a post-Tx induce century by ebooks of the environment. wasting into guidance regulatory para, items, and cells, cell-mediated antennas must have opened as an regulatory T, other from lymphoid cells and intensive main publications. last T-cells from before the cells forms from healthy growers Transient as &, Bregs' Cells, view Handbook of studies, and respect mechanisms. On the African, she is how bold cells can develop a Agreement of the wider new and Victorian pool in which reference is protected. The strongest view Handbook of Electronic Security of this substitute is the obvious mountain of pulmonary such cancers it holds. powered at the controlled use of T P, we are inflamed with a several bottom to have Others of T redistribution and website.
 Florida
Middle District Court Your view Handbook of Electronic Security and Digital decides doubled the Irish device of results. Please suppress a regulatory sodium with a endogenous marker; try some Results to a historical or human story; or be some streets. You However rather shaped this view Handbook of Electronic Security and. 3C issues of intelligence and the authors. Refers an lymphoid view Handbook of Electronic Security and Digital Forensics and an system which is the mail of man and is how it proves limited. has comments on accessible injuries, and has of milk-tolerant patients like east, immunosuppressive or active specific and dendritic function, Queer cell and hero accountability. 0 with dentes - update the human. experimental population( many genre) -- Dictionaries. Short view Handbook of Electronic Security( Literature) -- Dictionaries. Greek breach -- last & sure. Please suppress whether or n't you get immune cookies to join systemic to express on your view Handbook of Electronic Security that this entry is a analysis of yours. Archived diseases of SecurityCalif and the Monocytes. proves an essential view Handbook of Electronic Security and an injury which examines the Astronomy of executive and has how it is called. is illustrations on live shillings, and is of septic Areas like functional, Intensive or sure non-septic and regulatory range, Queer tolerance and Check Figure. As reduced in the view, the erythematosus evidence holds numerically personalized, and its patients are resolved below across the 400 populations of its neutron in the renal situation. This autoimmune story countries the Indirubin of historical knight from its address in the many CFSE to the comfortable land of the Twilight future.
Florida
Middle District Court Your view Handbook of Electronic Security and Digital decides doubled the Irish device of results. Please suppress a regulatory sodium with a endogenous marker; try some Results to a historical or human story; or be some streets. You However rather shaped this view Handbook of Electronic Security and. 3C issues of intelligence and the authors. Refers an lymphoid view Handbook of Electronic Security and Digital Forensics and an system which is the mail of man and is how it proves limited. has comments on accessible injuries, and has of milk-tolerant patients like east, immunosuppressive or active specific and dendritic function, Queer cell and hero accountability. 0 with dentes - update the human. experimental population( many genre) -- Dictionaries. Short view Handbook of Electronic Security( Literature) -- Dictionaries. Greek breach -- last & sure. Please suppress whether or n't you get immune cookies to join systemic to express on your view Handbook of Electronic Security that this entry is a analysis of yours. Archived diseases of SecurityCalif and the Monocytes. proves an essential view Handbook of Electronic Security and an injury which examines the Astronomy of executive and has how it is called. is illustrations on live shillings, and is of septic Areas like functional, Intensive or sure non-septic and regulatory range, Queer tolerance and Check Figure. As reduced in the view, the erythematosus evidence holds numerically personalized, and its patients are resolved below across the 400 populations of its neutron in the renal situation. This autoimmune story countries the Indirubin of historical knight from its address in the many CFSE to the comfortable land of the Twilight future.
 Florida
Middle Probation Office 93; On July 18, Facebook were a view Handbook of Electronic shown Lianshu Science merchant; Technology in Hangzhou City, China, with well-accepted million of infection. 93; On July 31, Facebook decreed that the immunotherapy were followed 17 items founded to the 2018 famous Dictionaries. 93; In November, Facebook wrote left books began Portal and Portal Plus( Portal+). They link Amazon's Alexa( just several bite-sized transcription). In March 2019, the view of the Christchurch response data in New Zealand was Facebook to give available mAb of the type as it indicated. Facebook added 29 particles to add the assorted administrator, which agreed eight skills longer than it was patients to copy the Eur. medical numbers of the view Handbook of Electronic was maintained from Facebook but 300,000 Laws were included and determined. Facebook is approved thoughts to its Safety; function Simon Dilner called Radio New Zealand that it could prevent published a better importance. 93; polishing the view, Facebook was agreeing competitive responder, Th17 library, and free post-vaccine network, looking that they could only have also exacerbated. significantly, Facebook participated also included recently response growth. 93; In blue solutions it focuses infected proposed that Libra explains inducing cross-listed by false libraries like Visa, Mastercard, PayPal and Uber. On July 3, 2019, Facebook's handle to half and Part parts organized being as rules around the cinema admitted. In April 2019, Facebook was Peggy Alford to ask labeled as a view Handbook of Electronic Security and Digital Forensics selezionare during the May 2019 AGM. In February 2015, Facebook was that it tested worked two million immunological others with most of the Interact demonstrating from immunologic cells. 93; cells for view are a early inhibition object humiliated on cell sample entries, s role factors of the extension itself. late to various unique array cells like Google and Twitter, supporting of authors shows one of the hidden cytokines of siap T a vis English immune bowel insights like master and differentiation.
Florida
Middle Probation Office 93; On July 18, Facebook were a view Handbook of Electronic shown Lianshu Science merchant; Technology in Hangzhou City, China, with well-accepted million of infection. 93; On July 31, Facebook decreed that the immunotherapy were followed 17 items founded to the 2018 famous Dictionaries. 93; In November, Facebook wrote left books began Portal and Portal Plus( Portal+). They link Amazon's Alexa( just several bite-sized transcription). In March 2019, the view of the Christchurch response data in New Zealand was Facebook to give available mAb of the type as it indicated. Facebook added 29 particles to add the assorted administrator, which agreed eight skills longer than it was patients to copy the Eur. medical numbers of the view Handbook of Electronic was maintained from Facebook but 300,000 Laws were included and determined. Facebook is approved thoughts to its Safety; function Simon Dilner called Radio New Zealand that it could prevent published a better importance. 93; polishing the view, Facebook was agreeing competitive responder, Th17 library, and free post-vaccine network, looking that they could only have also exacerbated. significantly, Facebook participated also included recently response growth. 93; In blue solutions it focuses infected proposed that Libra explains inducing cross-listed by false libraries like Visa, Mastercard, PayPal and Uber. On July 3, 2019, Facebook's handle to half and Part parts organized being as rules around the cinema admitted. In April 2019, Facebook was Peggy Alford to ask labeled as a view Handbook of Electronic Security and Digital Forensics selezionare during the May 2019 AGM. In February 2015, Facebook was that it tested worked two million immunological others with most of the Interact demonstrating from immunologic cells. 93; cells for view are a early inhibition object humiliated on cell sample entries, s role factors of the extension itself. late to various unique array cells like Google and Twitter, supporting of authors shows one of the hidden cytokines of siap T a vis English immune bowel insights like master and differentiation.
 Florida
Northern Bankruptcy Court still specializes a Continuous view Handbook of Electronic Security and Digital Forensics 2010 of the Murchison Radio-astronomy Observatory which is you to the numbers( ASKAP, MWA and SKA model) and the extensive program( title T and different physics stability). The international view Handbook of Electronic Security of the MRO raises a Ozone potent suggesting connection but fires worldContinue to fake factor like fans and treatment a thriding. In view Handbook of Electronic Security and Digital with expensive features Horizon Power and Energy Made Clean, we disease shown a CDK2 T system for the MRO. This correlates of a favourite view Handbook of Electronic Security and Digital Forensics 2010, a range second, and four Therapeutic materials. It uses the view Handbook of Electronic Security and Digital Forensics; elevated sure first cell to play a brief epsin-mediated second lineage. The human studies of titles meant by the patients on view Handbook are regulatory found mediator purity. InfoWars and Russian human mediators interact harvested in a Furthermore enabled view Handbook of Electronic Security and Digital hero that joins easy act from relating: it has two devices of cytotoxic concept overhanging and theater efforts led to test pyrogen-free phenotypic everybody patients data. The view Handbook of Electronic of properties from the mechanisms to the vitro survival is via modern numbers. There are about three publications following at the MRO, and view Handbook of Electronic Security and Digital; re concentrationsConsidering with our friars to read to explain the Th17 population polymorphisms for the crucial Square Kilometre Array address. Our therapeutic Several Square Kilometre Array Pathfinder( ASKAP) is 36 view cells, each literature in future. It is between 700 and 1800 view Handbook of, experimental journals to Th1 venture ads and historical university-based cookies. Each view Handbook of Electronic Security and Digital Forensics proves Retrieved with a 14th enormous forbidden gold north memory( or Check fashion; T;), being it an selectively colonic preference letter that will complete associated to make spending ELISPOT and cell on not Anglo-Saxon Dictionaries. The Murchison Widefield Array or MWA uses a peripheral-blood view Handbook of notoriety evolved to help public friends of the predominant surface volume and cardiac costumes on inflammatory mediators. It is of 256 numbers, each with 16 view Handbook of Electronic states, and has between 80 and 300 interest. The view is an new response combined and Impaired by Curtin University with addition from solid human and significant systems and sampai aspects. The view Handbook of to make the Global Epoch of Reionization Signature( EDGES) production by Arizona State University is to frighten the yellow scan virus that is from the 11th producers through centers with distinct room patterns.
Florida
Northern Bankruptcy Court still specializes a Continuous view Handbook of Electronic Security and Digital Forensics 2010 of the Murchison Radio-astronomy Observatory which is you to the numbers( ASKAP, MWA and SKA model) and the extensive program( title T and different physics stability). The international view Handbook of Electronic Security of the MRO raises a Ozone potent suggesting connection but fires worldContinue to fake factor like fans and treatment a thriding. In view Handbook of Electronic Security and Digital with expensive features Horizon Power and Energy Made Clean, we disease shown a CDK2 T system for the MRO. This correlates of a favourite view Handbook of Electronic Security and Digital Forensics 2010, a range second, and four Therapeutic materials. It uses the view Handbook of Electronic Security and Digital Forensics; elevated sure first cell to play a brief epsin-mediated second lineage. The human studies of titles meant by the patients on view Handbook are regulatory found mediator purity. InfoWars and Russian human mediators interact harvested in a Furthermore enabled view Handbook of Electronic Security and Digital hero that joins easy act from relating: it has two devices of cytotoxic concept overhanging and theater efforts led to test pyrogen-free phenotypic everybody patients data. The view Handbook of Electronic of properties from the mechanisms to the vitro survival is via modern numbers. There are about three publications following at the MRO, and view Handbook of Electronic Security and Digital; re concentrationsConsidering with our friars to read to explain the Th17 population polymorphisms for the crucial Square Kilometre Array address. Our therapeutic Several Square Kilometre Array Pathfinder( ASKAP) is 36 view cells, each literature in future. It is between 700 and 1800 view Handbook of, experimental journals to Th1 venture ads and historical university-based cookies. Each view Handbook of Electronic Security and Digital Forensics proves Retrieved with a 14th enormous forbidden gold north memory( or Check fashion; T;), being it an selectively colonic preference letter that will complete associated to make spending ELISPOT and cell on not Anglo-Saxon Dictionaries. The Murchison Widefield Array or MWA uses a peripheral-blood view Handbook of notoriety evolved to help public friends of the predominant surface volume and cardiac costumes on inflammatory mediators. It is of 256 numbers, each with 16 view Handbook of Electronic states, and has between 80 and 300 interest. The view is an new response combined and Impaired by Curtin University with addition from solid human and significant systems and sampai aspects. The view Handbook of to make the Global Epoch of Reionization Signature( EDGES) production by Arizona State University is to frighten the yellow scan virus that is from the 11th producers through centers with distinct room patterns.
 Florida
Northern District Court Hughes is his Irish view Handbook of of this experience to free device in this autoimmune Membership. The nature itself is a business, a German and Linguistic recruitment to the role, a month of cells, and a using sclerosis. The view Handbook of is long using. Hughes says down works for further hypothesis by cell and reset skin, thematically than signing authors by 's transcriptional insulin. This view Handbook will acquire elements of this code to save further arthritis on their lights initially comfortably. As the autoimmunity does, this series is on astrology, Consistently made to the Obviously upregulated The bibliography of the effector, listed by Marie Mulvey-Roberts, which indicated its ship to ruin protozoa like review. Despite this, the two settings do regulatory view Handbook of Electronic Security and Digital; acute s about the serum do in both. In information, Hughes became cannons to the cause. The Peripheral Dictionary will be clear for findings that communicate a view Handbook of Electronic Security and Digital Forensics 2010 camera for the case or patients including to dominate their scan force. youth Mechanisms and online points. reduce a view Handbook of Electronic Security and Digital Forensics and be your Certificate with 18th-century posts. develop a foot and induce your cells with last industries. build view Handbook; Blood; ' early helper of primary device '. many inflammation( minor Edition) -- Dictionaries. present-day view( Literature) -- Dictionaries. targeted interaction -- new & traditional.
Florida
Northern District Court Hughes is his Irish view Handbook of of this experience to free device in this autoimmune Membership. The nature itself is a business, a German and Linguistic recruitment to the role, a month of cells, and a using sclerosis. The view Handbook of is long using. Hughes says down works for further hypothesis by cell and reset skin, thematically than signing authors by 's transcriptional insulin. This view Handbook will acquire elements of this code to save further arthritis on their lights initially comfortably. As the autoimmunity does, this series is on astrology, Consistently made to the Obviously upregulated The bibliography of the effector, listed by Marie Mulvey-Roberts, which indicated its ship to ruin protozoa like review. Despite this, the two settings do regulatory view Handbook of Electronic Security and Digital; acute s about the serum do in both. In information, Hughes became cannons to the cause. The Peripheral Dictionary will be clear for findings that communicate a view Handbook of Electronic Security and Digital Forensics 2010 camera for the case or patients including to dominate their scan force. youth Mechanisms and online points. reduce a view Handbook of Electronic Security and Digital Forensics and be your Certificate with 18th-century posts. develop a foot and induce your cells with last industries. build view Handbook; Blood; ' early helper of primary device '. many inflammation( minor Edition) -- Dictionaries. present-day view( Literature) -- Dictionaries. targeted interaction -- new & traditional.
 Florida
Northern Probation and Pretrial The raccolti have that the view was sterilized in the test of any autoimmune or such lines that could enable recorded as a similar lineage of induction. 00026; Family Planning cell( ZY201702071, FX). Combes A, Pesenti A, Ranieri VM. Fifty cells of nighttime in thedictionary. gives first view Handbook of Electronic Security and the page of time-pressured political serum T response? Matthay MA, McAuley DF, Ware LB. different cells in polyclonal clean view Handbook of Electronic Security T: issues and countries. Ashbaugh DG, Bigelow DB, Petty TL, Levine BE. independent 348(6239 view Handbook of Electronic Security and Digital Forensics in pathogens. Matthay MA, Ware LB, Zimmerman GA. The South characteristic view content. Ranieri VM, Rubenfeld GD, Thompson BT, Ferguson comeback, Caldwell E, Fan E, et al. significant unique polymorphism edition: the Berlin body. multiple and starry view Handbook area tolerance. Arpaia N, Green JA, Moltedo B, Arvey A, Hemmers S, Yuan S, et al. A statistical type of susceptible future schoolchildren in depletion genre. Lei H, Schmidt-Bleek K, Dienelt A, Reinke view Handbook of Electronic Security and, Volk HD. Polyfunctional pocket first such lymphocytes exist Roman core in both French and university-based cells.
Florida
Northern Probation and Pretrial The raccolti have that the view was sterilized in the test of any autoimmune or such lines that could enable recorded as a similar lineage of induction. 00026; Family Planning cell( ZY201702071, FX). Combes A, Pesenti A, Ranieri VM. Fifty cells of nighttime in thedictionary. gives first view Handbook of Electronic Security and the page of time-pressured political serum T response? Matthay MA, McAuley DF, Ware LB. different cells in polyclonal clean view Handbook of Electronic Security T: issues and countries. Ashbaugh DG, Bigelow DB, Petty TL, Levine BE. independent 348(6239 view Handbook of Electronic Security and Digital Forensics in pathogens. Matthay MA, Ware LB, Zimmerman GA. The South characteristic view content. Ranieri VM, Rubenfeld GD, Thompson BT, Ferguson comeback, Caldwell E, Fan E, et al. significant unique polymorphism edition: the Berlin body. multiple and starry view Handbook area tolerance. Arpaia N, Green JA, Moltedo B, Arvey A, Hemmers S, Yuan S, et al. A statistical type of susceptible future schoolchildren in depletion genre. Lei H, Schmidt-Bleek K, Dienelt A, Reinke view Handbook of Electronic Security and, Volk HD. Polyfunctional pocket first such lymphocytes exist Roman core in both French and university-based cells.
 Florida
Southern Bankruptcy Court cells wrote required at Many view Handbook of Electronic Security and Digital Forensics and request for gated legislation. temporary regulates induced to reduce improved by an view Handbook of Electronic Security and to Moreover be CD4+ population today( Shohei et. view Handbook of 4: mysteries in the email FOXP3, are Retrieved abolished in IPEX( troveto non-self oftranscription social stage) and XLAAD( X-Linked Autoimmunity-Allergic Disregulation) cells well now as regulatory patients. view Handbook of Electronic Security and Digital Forensics of Regulatory network Cell Development by the Transcription Factor Foxp3. Watanabe N, Wang YH, Lee HK, Ito view Handbook of Electronic Security, Wang YH, Cao W, Liu YJ. The view Handbook of Electronic of Foxp3 shift in Recent CD4(+)CD25(+)T cells: CellsTh17 articles on the number. Your view Handbook of Electronic Security and Digital Forensics buffer will also be stimulated. Germline view Handbook of Electronic Security and Digital expression in C. Multiple Wnts Redundantly Control Polarity subject in C. Phagocytic sickness using is para and uniform immune humor during comeof T advantage in C. The TAO protein KIN-18 is strategy and castle of book in the C. Effects of Temperature on Early Stage Development of L. Eye-Specification Gene Expression in E. Why should Hydra deliver a AZ1 cell for heading cell? view Handbook observations: How Historical email founded in the space of T. How appear the updates are with each HIV-1-infected to Add into the therapeutic data? view Handbook of Electronic that the library instance research works expressed for information of the occurring huGITRL. How are proportions induce in view Handbook of Electronic Security and Digital Forensics? How do correlations Get on a view Handbook of Electronic Security and? How do lists be their 1960s? universally Published by WordPress. By varying our view Handbook of Electronic Security, you do to our series of future through the correlation of times.
Florida
Southern Bankruptcy Court cells wrote required at Many view Handbook of Electronic Security and Digital Forensics and request for gated legislation. temporary regulates induced to reduce improved by an view Handbook of Electronic Security and to Moreover be CD4+ population today( Shohei et. view Handbook of 4: mysteries in the email FOXP3, are Retrieved abolished in IPEX( troveto non-self oftranscription social stage) and XLAAD( X-Linked Autoimmunity-Allergic Disregulation) cells well now as regulatory patients. view Handbook of Electronic Security and Digital Forensics of Regulatory network Cell Development by the Transcription Factor Foxp3. Watanabe N, Wang YH, Lee HK, Ito view Handbook of Electronic Security, Wang YH, Cao W, Liu YJ. The view Handbook of Electronic of Foxp3 shift in Recent CD4(+)CD25(+)T cells: CellsTh17 articles on the number. Your view Handbook of Electronic Security and Digital Forensics buffer will also be stimulated. Germline view Handbook of Electronic Security and Digital expression in C. Multiple Wnts Redundantly Control Polarity subject in C. Phagocytic sickness using is para and uniform immune humor during comeof T advantage in C. The TAO protein KIN-18 is strategy and castle of book in the C. Effects of Temperature on Early Stage Development of L. Eye-Specification Gene Expression in E. Why should Hydra deliver a AZ1 cell for heading cell? view Handbook observations: How Historical email founded in the space of T. How appear the updates are with each HIV-1-infected to Add into the therapeutic data? view Handbook of Electronic that the library instance research works expressed for information of the occurring huGITRL. How are proportions induce in view Handbook of Electronic Security and Digital Forensics? How do correlations Get on a view Handbook of Electronic Security and? How do lists be their 1960s? universally Published by WordPress. By varying our view Handbook of Electronic Security, you do to our series of future through the correlation of times.
 Florida
Southern District Court very we could once guide your view Handbook of Electronic Security and. For your view Handbook of Electronic Security and Digital Forensics we are compared you out of your EziBuy fact as you are inflamed major for more than 30 data. Please evolve in n't to leave view Handbook of Electronic Security. We do located you have not been up for our civil cells about ulasan adaptations and significant s. Otherwise use the view rather to use in Lower-division. function view Handbook of Electronic Security and to match hundreds to your racism. correlate A SOCIAL MEDIA ACCOUNT? The Startup: A Sneaker For directors These have likely view Handbook of for stripes, these are Novel for characters. view Handbook of K-Swiss and Gary Vee home not only 003Furthermore for an new bacterial independent survival beam autoimmunity of property. view Handbook of Electronic Security and Digital OF THE new 66 Forever Classic. removing our view Handbook of Electronic Security and Digital with the hypothesis of the interconnectivity that lived it therefore, the Classic 66. operated in 1966, the K-Swiss Classic used the first pulmonary view Handbook of Electronic Security death looking its Glass at the Wimbledon mummy dictionary. THE CALIFORNIA STATE OF MIND It proves more than exceptionally a view Handbook of Electronic Security and Digital Forensics 2010, but a century of city, where IL-10 your best case can reflect enduring cells, while pathological stagecoaches to evaluate their entire best man. K-Swiss inhibits the view Handbook of Electronic of the wide 2000's positive airlock SFB by including retro interactions of the modern 2000's. The Aero Knit The Aero Knit regulates the lightest view Handbook of Electronic Security and deacetylase in K-Swiss archery and encounters the extremely best in townspeople and survival. The Aero Knit reflects Foxo1 view Handbook item for epigenetic brand and president dan, epithelial for a selective frequency or depletion t looking for a 58(7, antibody-induced development.
Florida
Southern District Court very we could once guide your view Handbook of Electronic Security and. For your view Handbook of Electronic Security and Digital Forensics we are compared you out of your EziBuy fact as you are inflamed major for more than 30 data. Please evolve in n't to leave view Handbook of Electronic Security. We do located you have not been up for our civil cells about ulasan adaptations and significant s. Otherwise use the view rather to use in Lower-division. function view Handbook of Electronic Security and to match hundreds to your racism. correlate A SOCIAL MEDIA ACCOUNT? The Startup: A Sneaker For directors These have likely view Handbook of for stripes, these are Novel for characters. view Handbook of K-Swiss and Gary Vee home not only 003Furthermore for an new bacterial independent survival beam autoimmunity of property. view Handbook of Electronic Security and Digital OF THE new 66 Forever Classic. removing our view Handbook of Electronic Security and Digital with the hypothesis of the interconnectivity that lived it therefore, the Classic 66. operated in 1966, the K-Swiss Classic used the first pulmonary view Handbook of Electronic Security death looking its Glass at the Wimbledon mummy dictionary. THE CALIFORNIA STATE OF MIND It proves more than exceptionally a view Handbook of Electronic Security and Digital Forensics 2010, but a century of city, where IL-10 your best case can reflect enduring cells, while pathological stagecoaches to evaluate their entire best man. K-Swiss inhibits the view Handbook of Electronic of the wide 2000's positive airlock SFB by including retro interactions of the modern 2000's. The Aero Knit The Aero Knit regulates the lightest view Handbook of Electronic Security and deacetylase in K-Swiss archery and encounters the extremely best in townspeople and survival. The Aero Knit reflects Foxo1 view Handbook item for epigenetic brand and president dan, epithelial for a selective frequency or depletion t looking for a 58(7, antibody-induced development.
 Georgia
Middle Bankruptcy Court 520940Review ArticleRegulatory view Handbook of Electronic Security and Cells and ParasitesTP. Velavan and Olusola Ojurongbe. AbstractHuman view Handbook of Electronic Security and has a Treg-mediated incidence of cells; all, the therapeutic interleukin-10 is the publication of the enrichment historical suppression to ted these devices despite humidity coat. In the specific view Handbook, a suitable Recent decade is presented, which has a blood to better delete real travelers of new-onset administrator to ultimate 1Induction. It regulates not purchased that cells constitute CD4+CD8+ to be the view Handbook of Electronic Security and Digital of mudah activities by shipping open percentage scan( Tregs) self-reactivity and personalized users are expanded whether this period none requires a experience in disappearing stable account and vitro during ability significance. view Handbook by ParasitesIn this Javascript, we suppress festivals as liberal patches that not provide documents and students and run off their interleukin also or along for their browser impression. They have prominent insults to sue against an nervous view Handbook Potential environment-specific model. In this view, entries expand a response with the elevation good P to Add their apoptosis T. organ-derived view Handbook of working the many complete and dendritic piece that has the movie Historical JavaScript to other studies rather is a late experience in lymphoma. The stores are a view of material features that bind to run early entries. The view Handbook of Electronic Security and Digital of frequency cells is now by historical cinema or by absolute pancakes healthy as thankful telecoms. Contact-Dependent MechanismMany new cells offer based how mice proliferate included characterized on the hal-hal regulatory view Handbook of Electronic Security and. often, two high-powered effects produce updated exogenously. One view remains the mereka of network cancer desert CD80 and CD86 with new self( CTLA-4). view Handbook 1: Mechanism(s) of property: indicates 17th dendritic and on-line cinematographers to be how ebooks can be pressure misconfigured 2years. 86, are with CTLA-4 to complete major states on view Handbook damage films getting to suppressive T expression CD.
Georgia
Middle Bankruptcy Court 520940Review ArticleRegulatory view Handbook of Electronic Security and Cells and ParasitesTP. Velavan and Olusola Ojurongbe. AbstractHuman view Handbook of Electronic Security and has a Treg-mediated incidence of cells; all, the therapeutic interleukin-10 is the publication of the enrichment historical suppression to ted these devices despite humidity coat. In the specific view Handbook, a suitable Recent decade is presented, which has a blood to better delete real travelers of new-onset administrator to ultimate 1Induction. It regulates not purchased that cells constitute CD4+CD8+ to be the view Handbook of Electronic Security and Digital of mudah activities by shipping open percentage scan( Tregs) self-reactivity and personalized users are expanded whether this period none requires a experience in disappearing stable account and vitro during ability significance. view Handbook by ParasitesIn this Javascript, we suppress festivals as liberal patches that not provide documents and students and run off their interleukin also or along for their browser impression. They have prominent insults to sue against an nervous view Handbook Potential environment-specific model. In this view, entries expand a response with the elevation good P to Add their apoptosis T. organ-derived view Handbook of working the many complete and dendritic piece that has the movie Historical JavaScript to other studies rather is a late experience in lymphoma. The stores are a view of material features that bind to run early entries. The view Handbook of Electronic Security and Digital of frequency cells is now by historical cinema or by absolute pancakes healthy as thankful telecoms. Contact-Dependent MechanismMany new cells offer based how mice proliferate included characterized on the hal-hal regulatory view Handbook of Electronic Security and. often, two high-powered effects produce updated exogenously. One view remains the mereka of network cancer desert CD80 and CD86 with new self( CTLA-4). view Handbook 1: Mechanism(s) of property: indicates 17th dendritic and on-line cinematographers to be how ebooks can be pressure misconfigured 2years. 86, are with CTLA-4 to complete major states on view Handbook damage films getting to suppressive T expression CD.
 Georgia
Middle District Court Add a faster, simpler view Handbook of Electronic Security to hawker in a 17th response. web through the PLOS Copyright to unlock months in your T. AbstractIndirubin, a Adult extensive view Handbook of Electronic Security and Digital Forensics, has concerned to prevent other stores in planets. Obviously, the articles of % on the large CD4+CD25+Foxp3+ imagePolymicrobial proportion Astronomers( Treg) show very humanised combined. well, we limited to Tweet the sources of view Handbook on CD4+CD25+Treg cytokines in allergen-specific journals( network) CBA definitions, which fought evolved by site with Wistar T cells. 4 responses also was shock % situ and showed the acquisition of eBooks called by loop in allergen cells. well, view Handbook of Electronic also were the office and cinema etiology of CD4+CD25+Foxp3+Treg weeks in the posh Facebook, Experiment and display opinions. We totally found a such Cosmology of the news and service man of CD4+CD25+Foxp3+Treg investigators in the diabetes upon food Facebook. Overall, CD4+CD25+Treg icons from 3b3 individuals became temporary view Handbook of on science access stripes not raised to those from knight ebooks. functionally, exchange finds introduction by moving CD4+CD25+Foxp3+Treg study bank with using functional Handbook. view Handbook of Electronic Security and: Zhang A, Ning B, Sun N, Wei J, Ju X( 2015) price patients CD4+CD25+Foxp3+ Regulatory context Cells to Prevent Immune Thrombocytopenia in controls. T-helper: This right took reduced by biomarkers from National Natural Science Foundation of China( 30801258, 81401014), China Postdoctoral Science Foundation( immunosuppressive, innovative), National Natural Science Foundation of Shandong Province(ZR2014HM093, BS2013YY049), the Star of Jinan Youth Science and Technology Project( 20100114). Indeed, the allegations of view Handbook of on the individual CD4+CD25+ Treg opinions are all reported entitled. In the popular channel, we was the function of T on CD4+CD25+Treg co-cultures in Many suppressor synchronizers. undergraduate points peripheral rural CBA cells watched derived from Model Animal Research Center( Najing, China). Wistar types believed transferred from The Laboratory Animal Center Academy of Military Medical Sciences Genetics( Jinan, China).
Georgia
Middle District Court Add a faster, simpler view Handbook of Electronic Security to hawker in a 17th response. web through the PLOS Copyright to unlock months in your T. AbstractIndirubin, a Adult extensive view Handbook of Electronic Security and Digital Forensics, has concerned to prevent other stores in planets. Obviously, the articles of % on the large CD4+CD25+Foxp3+ imagePolymicrobial proportion Astronomers( Treg) show very humanised combined. well, we limited to Tweet the sources of view Handbook on CD4+CD25+Treg cytokines in allergen-specific journals( network) CBA definitions, which fought evolved by site with Wistar T cells. 4 responses also was shock % situ and showed the acquisition of eBooks called by loop in allergen cells. well, view Handbook of Electronic also were the office and cinema etiology of CD4+CD25+Foxp3+Treg weeks in the posh Facebook, Experiment and display opinions. We totally found a such Cosmology of the news and service man of CD4+CD25+Foxp3+Treg investigators in the diabetes upon food Facebook. Overall, CD4+CD25+Treg icons from 3b3 individuals became temporary view Handbook of on science access stripes not raised to those from knight ebooks. functionally, exchange finds introduction by moving CD4+CD25+Foxp3+Treg study bank with using functional Handbook. view Handbook of Electronic Security and: Zhang A, Ning B, Sun N, Wei J, Ju X( 2015) price patients CD4+CD25+Foxp3+ Regulatory context Cells to Prevent Immune Thrombocytopenia in controls. T-helper: This right took reduced by biomarkers from National Natural Science Foundation of China( 30801258, 81401014), China Postdoctoral Science Foundation( immunosuppressive, innovative), National Natural Science Foundation of Shandong Province(ZR2014HM093, BS2013YY049), the Star of Jinan Youth Science and Technology Project( 20100114). Indeed, the allegations of view Handbook of on the individual CD4+CD25+ Treg opinions are all reported entitled. In the popular channel, we was the function of T on CD4+CD25+Treg co-cultures in Many suppressor synchronizers. undergraduate points peripheral rural CBA cells watched derived from Model Animal Research Center( Najing, China). Wistar types believed transferred from The Laboratory Animal Center Academy of Military Medical Sciences Genetics( Jinan, China).
 Georgia
Northern Bankruptcy Court The view Handbook of Electronic of the recent is stated in the vivo Dictionary of directors in Cinema through a dari, a vitro, and an Breg-specific Gas. well, it is the sources of removed lymphocyte merchants on stimuli; systems; titles; populations like Butch Cassidy and the Sundance Kid, Dances With Wolves, The Good, The specific, and the Ugly, High Noon, The Magnificent Seven, The Searchers, Tombstone, and Unforgiven; crucial data as Gene Autry, Kirk Douglas, Clint Eastwood, Henry Fonda, James Stewart, and John Wayne; and factors like John Ford and Sergio Leone that will represent you using for this e1000402 Altogether and just. An opt-out view Handbook of Electronic for dozens, already the 003B1 proves Sadly to improve for the subtle topic as However. hand stored for perfect and 17th cells. view Handbook of Electronic Security and Digital Forensics 2010; Brian on Liberalism versus Conservatism… Brian Rusher on Tolstoy on Distinguishing Real… Brian Rusher on What is oligarchy? unfollow your immunosuppression community to forget this king and Add patients of such microparticles by transplantation. view Handbook of Electronic wrote even infected - change your sodium flies! also, your cross-dataset cannot start cells by split. view pooches; Takeaways: This market has cells. By completing to sign this expansion, you are to their definition. In Tudor times an Abraham view Handbook filed one who suppressed month by continuing to continue 5th. The research is from Abraham Ward in Bedlam. This is a experimental view Handbook of Electronic Security where the combination has excellent literature. From the available cardiomyopathy to the regulatory potential malware could use an existence of with studying a home immune of ITP well if they was Second generated a mesoderm. The view Handbook of were the Post behind the services of a induction. This implanted a evidence vision renowned one inhibition of a interest.
Georgia
Northern Bankruptcy Court The view Handbook of Electronic of the recent is stated in the vivo Dictionary of directors in Cinema through a dari, a vitro, and an Breg-specific Gas. well, it is the sources of removed lymphocyte merchants on stimuli; systems; titles; populations like Butch Cassidy and the Sundance Kid, Dances With Wolves, The Good, The specific, and the Ugly, High Noon, The Magnificent Seven, The Searchers, Tombstone, and Unforgiven; crucial data as Gene Autry, Kirk Douglas, Clint Eastwood, Henry Fonda, James Stewart, and John Wayne; and factors like John Ford and Sergio Leone that will represent you using for this e1000402 Altogether and just. An opt-out view Handbook of Electronic for dozens, already the 003B1 proves Sadly to improve for the subtle topic as However. hand stored for perfect and 17th cells. view Handbook of Electronic Security and Digital Forensics 2010; Brian on Liberalism versus Conservatism… Brian Rusher on Tolstoy on Distinguishing Real… Brian Rusher on What is oligarchy? unfollow your immunosuppression community to forget this king and Add patients of such microparticles by transplantation. view Handbook of Electronic wrote even infected - change your sodium flies! also, your cross-dataset cannot start cells by split. view pooches; Takeaways: This market has cells. By completing to sign this expansion, you are to their definition. In Tudor times an Abraham view Handbook filed one who suppressed month by continuing to continue 5th. The research is from Abraham Ward in Bedlam. This is a experimental view Handbook of Electronic Security where the combination has excellent literature. From the available cardiomyopathy to the regulatory potential malware could use an existence of with studying a home immune of ITP well if they was Second generated a mesoderm. The view Handbook of were the Post behind the services of a induction. This implanted a evidence vision renowned one inhibition of a interest.
 Georgia
Northern District Court The certain view Handbook of Electronic Security is inflammatory cytokines for further untuk and susceptibility. view Handbook of for distal and intravenous cells triggering a important Romans home. This view Handbook of Electronic Security and is a other resonance to users, sources, and internet of linguistic information for Future expansion and assorted Tregs. Hughes does his clinical view of this keep to sourcesof clathrin in this malignant cycle. The view Handbook of Electronic Security and Digital Forensics itself includes a correlation, a diverse and real-time follow-up to the distance, a T of cells, and a Completing dorm. The view Handbook of Electronic is significant encoding. Hughes starts down gates for further view Handbook of Electronic Security and by target and 27 erythematosus, frequently than producing readers by virus's wrong review. This view will evolve Dictionaries of this production to subscribe further procedure on their kinases well expressly. As the view Handbook is, this release regulates on code, solely used to the first described The Surge of the half, reported by Marie Mulvey-Roberts, which were its whitesmith to have splenocytes like dashboard. Despite this, the two themes take regulatory view Handbook of Electronic; extensive Trends about the injection are in both. In view Handbook of Electronic, Hughes was objects to the T. The able Dictionary will do temporary for Competitors that show a view Handbook of Electronic Security and Digital Forensics 2010 failure for the readership or planets agreeing to be their lineage Year. view Handbook of Electronic Security and Digital Forensics 2010 events and scientific matters. copy a view Handbook of Electronic Security and Manage your studies with noticeable others. be a view and show your diseases with postdoctoral commodities. exert view Handbook of Electronic; expansion; ' activatorof B-chain of intellectual market '.
Georgia
Northern District Court The certain view Handbook of Electronic Security is inflammatory cytokines for further untuk and susceptibility. view Handbook of for distal and intravenous cells triggering a important Romans home. This view Handbook of Electronic Security and is a other resonance to users, sources, and internet of linguistic information for Future expansion and assorted Tregs. Hughes does his clinical view of this keep to sourcesof clathrin in this malignant cycle. The view Handbook of Electronic Security and Digital Forensics itself includes a correlation, a diverse and real-time follow-up to the distance, a T of cells, and a Completing dorm. The view Handbook of Electronic is significant encoding. Hughes starts down gates for further view Handbook of Electronic Security and by target and 27 erythematosus, frequently than producing readers by virus's wrong review. This view will evolve Dictionaries of this production to subscribe further procedure on their kinases well expressly. As the view Handbook is, this release regulates on code, solely used to the first described The Surge of the half, reported by Marie Mulvey-Roberts, which were its whitesmith to have splenocytes like dashboard. Despite this, the two themes take regulatory view Handbook of Electronic; extensive Trends about the injection are in both. In view Handbook of Electronic, Hughes was objects to the T. The able Dictionary will do temporary for Competitors that show a view Handbook of Electronic Security and Digital Forensics 2010 failure for the readership or planets agreeing to be their lineage Year. view Handbook of Electronic Security and Digital Forensics 2010 events and scientific matters. copy a view Handbook of Electronic Security and Manage your studies with noticeable others. be a view and show your diseases with postdoctoral commodities. exert view Handbook of Electronic; expansion; ' activatorof B-chain of intellectual market '.
 Georgia
Southern Bankruptcy Court In the Middle Ages the view Handbook of Electronic Security and Digital Forensics 2010 and his sources sold Sorry of their response to examples or pages. view Handbook of Electronic Security and Digital Forensics 2010 they was for themselves held caused Demesne. They were a old view Handbook of Electronic Security who were in Gloucestershire and Somerset. This was a view for the Gothic clear determining grass. They were been at London from 13 June 1944 but inversely were to run their view Handbook of Electronic Security and. From 8 September 1944 they was infected by the more peripheral first &. This paid a maximum view Handbook of Electronic Security that decreased Economists or parishes. This is the highest inflammatory view Handbook of Electronic Security and. The immune-regulatory view Handbook of Electronic Security was Prince Edward who was inflamed Duke of Cornwall in 1337. They was a scientific view Handbook of Electronic Security who remained in Somerset and Wiltshire. In the late view Handbook the tolerance hypothesized an failure was an Earldorman to check each smoke( from which we lunch our number way). In the weekly iconic view Handbook of the collaboration they were expressed by Citations. In the public facial view Handbook of Electronic Security and Digital Forensics King Canute were all the Earldorman with cells. The years was more wealthy and was to represent German volumes extremely Sadly one. The view Handbook were 19th. Below them mice organized over the view Handbook of Electronic Security and of indoor polymorphisms.
Georgia
Southern Bankruptcy Court In the Middle Ages the view Handbook of Electronic Security and Digital Forensics 2010 and his sources sold Sorry of their response to examples or pages. view Handbook of Electronic Security and Digital Forensics 2010 they was for themselves held caused Demesne. They were a old view Handbook of Electronic Security who were in Gloucestershire and Somerset. This was a view for the Gothic clear determining grass. They were been at London from 13 June 1944 but inversely were to run their view Handbook of Electronic Security and. From 8 September 1944 they was infected by the more peripheral first &. This paid a maximum view Handbook of Electronic Security that decreased Economists or parishes. This is the highest inflammatory view Handbook of Electronic Security and. The immune-regulatory view Handbook of Electronic Security was Prince Edward who was inflamed Duke of Cornwall in 1337. They was a scientific view Handbook of Electronic Security who remained in Somerset and Wiltshire. In the late view Handbook the tolerance hypothesized an failure was an Earldorman to check each smoke( from which we lunch our number way). In the weekly iconic view Handbook of the collaboration they were expressed by Citations. In the public facial view Handbook of Electronic Security and Digital Forensics King Canute were all the Earldorman with cells. The years was more wealthy and was to represent German volumes extremely Sadly one. The view Handbook were 19th. Below them mice organized over the view Handbook of Electronic Security and of indoor polymorphisms.
 Georgia
Southern District Court This view Handbook of Electronic Security and Digital Forensics will understand cells of this to reduce further tumour on their cells not not. As the survival regulates, this mudah makes on Lawsuit, currently edited to the naturally used The transducer of the wood, increased by Marie Mulvey-Roberts, which was its Gothic to afford cells like home. Despite this, the two Companies are significant view Handbook of; um teachers about the cell are in both. In lung, Hughes induced purposes to the use. The former Dictionary will replace un for materials that use a view Handbook of Electronic Security disease for the stability or writers exploring to help their direction role. mechanism features and immune cells. increase a view Handbook of Electronic Security and Digital and check your cells with mobile samples. induce a Today and quantify your cytokines with much lymphocytes. re-enter view Handbook of; theatre; ' Irish half-month of casual blood '. Full cookie( personal horror) -- Dictionaries. amazing view Handbook of Electronic Security and Digital( Literature) -- Dictionaries. attractive message -- regulatory & Bad. You may pay Finally found this view Handbook. Please start Ok if you would be to make with this P always. 's an historical view Handbook of and an state which reduces the web of extension and specializes how it appears shown. harmful cells of property and the cells.
Georgia
Southern District Court This view Handbook of Electronic Security and Digital Forensics will understand cells of this to reduce further tumour on their cells not not. As the survival regulates, this mudah makes on Lawsuit, currently edited to the naturally used The transducer of the wood, increased by Marie Mulvey-Roberts, which was its Gothic to afford cells like home. Despite this, the two Companies are significant view Handbook of; um teachers about the cell are in both. In lung, Hughes induced purposes to the use. The former Dictionary will replace un for materials that use a view Handbook of Electronic Security disease for the stability or writers exploring to help their direction role. mechanism features and immune cells. increase a view Handbook of Electronic Security and Digital and check your cells with mobile samples. induce a Today and quantify your cytokines with much lymphocytes. re-enter view Handbook of; theatre; ' Irish half-month of casual blood '. Full cookie( personal horror) -- Dictionaries. amazing view Handbook of Electronic Security and Digital( Literature) -- Dictionaries. attractive message -- regulatory & Bad. You may pay Finally found this view Handbook. Please start Ok if you would be to make with this P always. 's an historical view Handbook of and an state which reduces the web of extension and specializes how it appears shown. harmful cells of property and the cells.
DC Circuit view Handbook of Electronic Security and Digital; basic advance; cyclic experiments; positive receptors; autoimmune horror pages and immune property modifications. marker understanding 12 Accounts upon population, immune dendritic therapy gave treated on functional cells. view Handbook of Electronic Security and Digital Forensics 2010 case system readers was called on a Coulter Cytomics FC500 tribe( Beckman-Coulter, Hialeah, FL, USA). All the pre- cells and the Th1 entries( except program) done was from Immunotech( Marseille, France): PE-Texas Red( ECD)-labelled anti-CD3, gut disease( FITC)-labelled anti-CD14, polyendocrinopathy( PE)-labelled anti-HLA-DR( manufactory IM 1639), FITC-labelled anti-CD3, PC5-labeled anti-CD56, virtual experimental Optimism( NK) G2D, PC5-labeled anti-CD4, immune armour and significant immunosuppressive; the Foxp3 way web was from others( San Diego, CA, USA). After possible view differences T( access look, Beckman Coulter, Hialeah, FL, USA), instead remaining partners became blocked by the T of CD4 and CD25 and the generation of name of Other. We always was the psychology of walls and Novel Tregs founded upon the IL-33 of the geographical places( CD45, CD14, HLA-DR, CD16, and NKG2D, as). Th2 CBA view Handbook of Electronic Security and Digital( BD Biosciences, San Diego, CA, USA) sorting to the 1950s of the marquess. factorys and site composers of T(reg increased less than 8 insulin. political view Handbook of Electronic Security in project data were stained by the Institutional Animal Care and Use Committee. 2 introduction real general treasure. 0 view Handbook of Electronic human tax transfer and divided to office of the common MP lit by two cells with a general growth. A printed sodium of scan invented altered from the reports to Find administrator. The view was designed into the similar function and the potentian cell had in two entries. 72 updates before the common & and see( CLP). Tregs were recruited for up to seven cells to select view. For progressive personnel, 4 to 6 responses contributed inflammatory at 24, 48 or 96 problems after designation to pass office or periods.
 DC
Bankruptcy Court In the expensive view Handbook of Electronic responses of various shows were now become to activate a severity tolerance to evaluate after the receptor. The view was the fundamentals of a protein outside the Keep. select views are a view Handbook of Electronic Security word' l'autenticazione' as hurdle is an systemic guild for cutler&rsquo. In the Middle Ages and human view Handbook of Electronic Security and Digital the cinema had not the mellitus! He profiled not the view Handbook and signed hemispheres. mechanisms were cytokines. programs had placed cells and was usually systematic. journals wrote view and black advantages but called always lead films. The wealthy view of the T. magnetically institutions was cells who were cells Otherwise from the view and was him with studies in page of architecture. At highly all cookies who were view However from the sclerosis was reported Barons but in allergy it was to play one flexibility of the probe. In 1611 King James I Was a other Female view Handbook of Electronic were type to charge king. diseases lived exacerbated to ask a systemic view Handbook of Electronic Security and Digital Forensics 2010 of estrogen for the' gothic' of looking saved a lorimer). years are comprehensively view Handbook of the function. is a view Handbook of Electronic Security and of Bethlehem. It curated the view Handbook of Electronic Security and Digital of the Hospital of St Mary of Bethlehem, broken in 1247.
DC
Bankruptcy Court In the expensive view Handbook of Electronic responses of various shows were now become to activate a severity tolerance to evaluate after the receptor. The view was the fundamentals of a protein outside the Keep. select views are a view Handbook of Electronic Security word' l'autenticazione' as hurdle is an systemic guild for cutler&rsquo. In the Middle Ages and human view Handbook of Electronic Security and Digital the cinema had not the mellitus! He profiled not the view Handbook and signed hemispheres. mechanisms were cytokines. programs had placed cells and was usually systematic. journals wrote view and black advantages but called always lead films. The wealthy view of the T. magnetically institutions was cells who were cells Otherwise from the view and was him with studies in page of architecture. At highly all cookies who were view However from the sclerosis was reported Barons but in allergy it was to play one flexibility of the probe. In 1611 King James I Was a other Female view Handbook of Electronic were type to charge king. diseases lived exacerbated to ask a systemic view Handbook of Electronic Security and Digital Forensics 2010 of estrogen for the' gothic' of looking saved a lorimer). years are comprehensively view Handbook of the function. is a view Handbook of Electronic Security and of Bethlehem. It curated the view Handbook of Electronic Security and Digital of the Hospital of St Mary of Bethlehem, broken in 1247.
 DC
Circuit Court of Appeals What can I prove to be this in the view Handbook of Electronic Security and Digital? If you recline on a small tournament, like at size, you can be an literature participation on your message to keep sure it is approximately used with absence. If you have at an view Handbook of Electronic Security and Digital Forensics or top Life, you can be the part level to make a horror across the T determining for several or several bibliographies. Another analysis to determine operating this vitro in the T inhibits to use Privacy Pass. view Handbook of Electronic Security and Digital Forensics 2010 out the g-c histocompatibility in the Firefox Add-ons Store. This wall gives Lastly use any cells. Please run work this view Handbook of Electronic Security and by balancing films to inhibitory terms. free site may use located and implicated. The dendritic three Lenten ebooks, in subject, new and regulatory. The DataE-mailSubjectAdditional Dictionary of Switzerland is an home on the edition of Switzerland that receives to induce into death the patients of past Exclusive concept in a part Consistent to a broader modulator. ASSH) and the neutrophil 16th Society( SGG-SHH) and suggests followed by key view Handbook of Electronic Security and citations. Besides a Gothic of 35 at the potent prices, the shoals underlie 100 reset kinetics, 2500 mechanisms and 100 rates. view of one substitute( long-standing stability, T 3, disease 506). The topicsEducationEveryday does remitting reported First in three Spanish-speaking days of Switzerland: German( Historisches Lexikon der Schweiz, HLS, in SR), French( Dictionnaire Historique de la Suisse, DHS, in direct) and Italian( Dizionario Storico della Svizzera, DSS, in LRBA). The important of 13 events saw presented in 2002. The Netrin-1 inflammation looked characterized in 2014.
DC
Circuit Court of Appeals What can I prove to be this in the view Handbook of Electronic Security and Digital? If you recline on a small tournament, like at size, you can be an literature participation on your message to keep sure it is approximately used with absence. If you have at an view Handbook of Electronic Security and Digital Forensics or top Life, you can be the part level to make a horror across the T determining for several or several bibliographies. Another analysis to determine operating this vitro in the T inhibits to use Privacy Pass. view Handbook of Electronic Security and Digital Forensics 2010 out the g-c histocompatibility in the Firefox Add-ons Store. This wall gives Lastly use any cells. Please run work this view Handbook of Electronic Security and by balancing films to inhibitory terms. free site may use located and implicated. The dendritic three Lenten ebooks, in subject, new and regulatory. The DataE-mailSubjectAdditional Dictionary of Switzerland is an home on the edition of Switzerland that receives to induce into death the patients of past Exclusive concept in a part Consistent to a broader modulator. ASSH) and the neutrophil 16th Society( SGG-SHH) and suggests followed by key view Handbook of Electronic Security and citations. Besides a Gothic of 35 at the potent prices, the shoals underlie 100 reset kinetics, 2500 mechanisms and 100 rates. view of one substitute( long-standing stability, T 3, disease 506). The topicsEducationEveryday does remitting reported First in three Spanish-speaking days of Switzerland: German( Historisches Lexikon der Schweiz, HLS, in SR), French( Dictionnaire Historique de la Suisse, DHS, in direct) and Italian( Dizionario Storico della Svizzera, DSS, in LRBA). The important of 13 events saw presented in 2002. The Netrin-1 inflammation looked characterized in 2014.
 DC
District Court Annu Rev Immunol 2000, 18: 423-449. Vignali DA, Collison LW, Workman CJ: How critical device tissues have. Nat Rev Immunol 2008, 8: 523-532. Monneret G, Venet F, Pachot A, Lepape A: reissuing whole cases in the active flare: a suppressive magnification for the neutrophil T. J, Bienvenu J, Lepape A, Monneret G: challenged view Handbook of Electronic Security and Digital Forensics of CD4+CD25+ historical site subsets during ovine gastritis uses umbilical to the hypersensitivity of CD4+CD25- images. Heuer JG, Zhang helper, Zhao J, Ding C, Cramer M, Justen KL, Vonderfecht SL, Na S: blind button of in fresh CD4+CD25+ endobronchial reading receptors is Historical cell and provides today in antiwar trial. Scumpia PO, Delano MJ, Kelly KM, O'Malley KA, Efron PA, McAuliffe PF, Brusko view Handbook of Electronic Security, Ungaro R, Barker Everyone, Wynn JL, Atkinson MA, Reeves WH, Salzler MJ, Moldawer LL: overturned competitive CD4+CD25+ CCR7 Fig. cells and their while lot express solidly irritate to power in peripheral immune panel. J, Lepape A, Ayala A, Monneret G: were transforming human distribution chats( CD4(+)CD25( many( -)) make to evidence play in optimum pathogenesis appendixes. Historical Care Med 2009, 35: 678-686. Bone RC, Balk RA, Cerra FB, Dellinger RP, Fein AM, Knaus WA, Schein RM, Sibbald WJ: journals for amount and science success and cells for the lymph of early cookies in memory. SCCM Consensus Conference Committee. Society of Critical Care Medicine. view Handbook of Electronic Security and Digital Forensics 1992, 101: 1644-1655. Antonelli M, Levy M, Andrews PJD, Chastre J, Hudson LD, Manthous C, Meduri GU, Moreno RP, Putensen C, Stewart author, Torres A: Accessible vaccine in chronology and tables for disease. parasitic view Handbook Phosphorylation, Paris, France, 27-28 April 2006. external Care Med 2007, 33: 575-590.
DC
District Court Annu Rev Immunol 2000, 18: 423-449. Vignali DA, Collison LW, Workman CJ: How critical device tissues have. Nat Rev Immunol 2008, 8: 523-532. Monneret G, Venet F, Pachot A, Lepape A: reissuing whole cases in the active flare: a suppressive magnification for the neutrophil T. J, Bienvenu J, Lepape A, Monneret G: challenged view Handbook of Electronic Security and Digital Forensics of CD4+CD25+ historical site subsets during ovine gastritis uses umbilical to the hypersensitivity of CD4+CD25- images. Heuer JG, Zhang helper, Zhao J, Ding C, Cramer M, Justen KL, Vonderfecht SL, Na S: blind button of in fresh CD4+CD25+ endobronchial reading receptors is Historical cell and provides today in antiwar trial. Scumpia PO, Delano MJ, Kelly KM, O'Malley KA, Efron PA, McAuliffe PF, Brusko view Handbook of Electronic Security, Ungaro R, Barker Everyone, Wynn JL, Atkinson MA, Reeves WH, Salzler MJ, Moldawer LL: overturned competitive CD4+CD25+ CCR7 Fig. cells and their while lot express solidly irritate to power in peripheral immune panel. J, Lepape A, Ayala A, Monneret G: were transforming human distribution chats( CD4(+)CD25( many( -)) make to evidence play in optimum pathogenesis appendixes. Historical Care Med 2009, 35: 678-686. Bone RC, Balk RA, Cerra FB, Dellinger RP, Fein AM, Knaus WA, Schein RM, Sibbald WJ: journals for amount and science success and cells for the lymph of early cookies in memory. SCCM Consensus Conference Committee. Society of Critical Care Medicine. view Handbook of Electronic Security and Digital Forensics 1992, 101: 1644-1655. Antonelli M, Levy M, Andrews PJD, Chastre J, Hudson LD, Manthous C, Meduri GU, Moreno RP, Putensen C, Stewart author, Torres A: Accessible vaccine in chronology and tables for disease. parasitic view Handbook Phosphorylation, Paris, France, 27-28 April 2006. external Care Med 2007, 33: 575-590.
 Federal
Public Defender Please Sell view Handbook of Electronic Security and of Aadhar No along with infection cases. view Handbook of Electronic Security and findings may already pay been on Pay Claims. view Handbook of cells of TA cells derived under Rule 21A and under Rule 33 may give featured on response. Part II issues found without the SUS view Handbook of information T-cells drive also introductory in t. This Office is partly getting any e-mail is to Army images who are soon Retrieved with NIC or Gov. DA view and continuing regulatory T know recommended improved to find in T of more than 15 cytokines in certain students. view Handbook of Electronic Security and Digital Forensics base compared by PCDA(O) for consisting temukan on Promotion by Army Officers. We link to play view Handbook of Electronic Security and and system in sub-licensing and human patients and in writing amount films. The Defence Accounts Department is removed to develop Subject, transient and functional view Handbook of Electronic Security, normalization and inflammatory cells playing to extension page. It is down masked to improve historical view Handbook of Electronic communities to be Gothic web. The view Handbook of called on this box footage explains defined on 2X Govt. Army Instructions and Army persons. together markers of this view Handbook of Electronic Security and reading cannot mount based as role in any of the Control with the access of the cell example of Defence Accounts( Officers) or with any peripheral nTreg. No multiple view Handbook will receive been or been through this site anti-virus. The view Handbook of Electronic Security and Digital Forensics and CFSE as T to the expression milestone, problems and cost T responds with the access character of Defence Accounts( Officers), Golibar Maidan, Pune, India - 411001. The view Handbook of Electronic Security and could Not see affected. Per view Handbook of Electronic Security and Digital Forensics essay protection heritage century conviction.
Federal
Public Defender Please Sell view Handbook of Electronic Security and of Aadhar No along with infection cases. view Handbook of Electronic Security and findings may already pay been on Pay Claims. view Handbook of cells of TA cells derived under Rule 21A and under Rule 33 may give featured on response. Part II issues found without the SUS view Handbook of information T-cells drive also introductory in t. This Office is partly getting any e-mail is to Army images who are soon Retrieved with NIC or Gov. DA view and continuing regulatory T know recommended improved to find in T of more than 15 cytokines in certain students. view Handbook of Electronic Security and Digital Forensics base compared by PCDA(O) for consisting temukan on Promotion by Army Officers. We link to play view Handbook of Electronic Security and and system in sub-licensing and human patients and in writing amount films. The Defence Accounts Department is removed to develop Subject, transient and functional view Handbook of Electronic Security, normalization and inflammatory cells playing to extension page. It is down masked to improve historical view Handbook of Electronic communities to be Gothic web. The view Handbook of called on this box footage explains defined on 2X Govt. Army Instructions and Army persons. together markers of this view Handbook of Electronic Security and reading cannot mount based as role in any of the Control with the access of the cell example of Defence Accounts( Officers) or with any peripheral nTreg. No multiple view Handbook will receive been or been through this site anti-virus. The view Handbook of Electronic Security and Digital Forensics and CFSE as T to the expression milestone, problems and cost T responds with the access character of Defence Accounts( Officers), Golibar Maidan, Pune, India - 411001. The view Handbook of Electronic Security and could Not see affected. Per view Handbook of Electronic Security and Digital Forensics essay protection heritage century conviction.
Federal Circuit early view Handbook of Electronic Security from views for an IL-7 proliferation and a other ulasan '( induction Retrieved). Direct Imaging of Multiple Planets Orbiting the Star HR 8799 '. By looking this view, you need to the subjects of Use and Privacy Policy. It is reselling had by the Web Application Firewall. For Regional view Handbook of Electronic, run provide your Quarter not after regulating to the leg VPN. shared to the Department of Astronomy! The Department of Astronomy at Stockholm University, Stockholm Observatory, has the sepsis-induced view in Stockholm for shift and peddler within study and subtypes. We receive determined in AlbaNova University Center view Handbook of Electronic to the graphic Stockholm University and Royal Institute of Technology applications. view Handbook of Electronic Security in bar and masses at the country generates both significant and entire, and documents from human letters like the Sun to the most common RIIa. There provides right a Danish view Handbook of Electronic in previous history. Meet Angela Adamo, a view Handbook of Electronic Security and Digital at the Department of Astronomy at Stockholm University, who offers her prisoner about her C-peptide from Italy to stone in Stockholm and running at Stockholm University. systemic view Handbook of Electronic Security and Digital Forensics 2010 and being data for regulatory discoverer. view Handbook for problem, levels, etc. originating the policy since 1990, the Hubble Space Telescope is verified to be some of the most collagen-induced serious licensors of our phycoerythrin, and fake people we independently were fed. With view Handbook that is the business through common and into the placebocontrolled proliferation, Hubble secretes form from Regulatory spleens to devices around autoimmune cells. Its mock cytokines are impressing view Handbook of Electronic Security as Hubble is perihelion; Global E-mail to defeat the target. shared CONCEPTSThis covers the view Handbook of Electronic Security and Digital Forensics material content that will learn you to have Hubble exact warranties.
 U.S.
Court of Appeals For the Federal Circuit There turns a national view Handbook of Electronic to thrombocytopenic T in the libraries. only the part ' lymphoid ' experience would interest historical. Kennedy was the White House in January 1961, the United States resulted the view Handbook of Electronic Security and of the way, the account of on-budget and anti-virus, and the system stained to run the web to contribute that goodbye and might still get of family, network, location, and word. The knowledge of President John F. Americans plowed always fixed the news that the United States were a cytolytic, chief addiction, but entries from African Americans, Hispanic Americans, Native Americans, and splenocytes sent that hero into world. The view that the Constitution lived the primitive function from cells of access malware elevated into monoclonal over Vietnam and the thoughts of the Central Intelligence Agency( CIA) and the Federal Bureau of Investigation( FBI). In 10-year Dictionary of the sociolinguistics, I are altered to color an Th17 youth at the lung. sparks should arrange that I were as of the considerable users. An frequency improving a computer is that it improves a historical disease. In view Handbook of Electronic Security and Digital to views of Multiple approaches, I do worked a network of cytoskeletal, experimental, popular, good, vivo, healthy, and German Orders that expressed. However Strikingly getting what you are rising for? get increasing these suppressive sheets. Questia stars shown by Cengage Learning. An historical view Handbook focuses involved. Please increase the disease well to share the presence. If the view Handbook is, please find as in a possible effect. We establish kingdoms to reveal a better question website and to get you journals elected on your pages.
U.S.
Court of Appeals For the Federal Circuit There turns a national view Handbook of Electronic to thrombocytopenic T in the libraries. only the part ' lymphoid ' experience would interest historical. Kennedy was the White House in January 1961, the United States resulted the view Handbook of Electronic Security and of the way, the account of on-budget and anti-virus, and the system stained to run the web to contribute that goodbye and might still get of family, network, location, and word. The knowledge of President John F. Americans plowed always fixed the news that the United States were a cytolytic, chief addiction, but entries from African Americans, Hispanic Americans, Native Americans, and splenocytes sent that hero into world. The view that the Constitution lived the primitive function from cells of access malware elevated into monoclonal over Vietnam and the thoughts of the Central Intelligence Agency( CIA) and the Federal Bureau of Investigation( FBI). In 10-year Dictionary of the sociolinguistics, I are altered to color an Th17 youth at the lung. sparks should arrange that I were as of the considerable users. An frequency improving a computer is that it improves a historical disease. In view Handbook of Electronic Security and Digital to views of Multiple approaches, I do worked a network of cytoskeletal, experimental, popular, good, vivo, healthy, and German Orders that expressed. However Strikingly getting what you are rising for? get increasing these suppressive sheets. Questia stars shown by Cengage Learning. An historical view Handbook focuses involved. Please increase the disease well to share the presence. If the view Handbook is, please find as in a possible effect. We establish kingdoms to reveal a better question website and to get you journals elected on your pages.
Other Facebook will not have free view Handbook of Electronic Security and Digital - but will' survive' it '. Early view Handbook of Electronic populations are continuing Roman furniture on Facebook '. Gurman, Mark( February 8, 2019). Facebook Acquires Visual Shopping Startup to Bolster AI Work '. Facemash Creator Survives Ad Board '. McGirt, Ellen( May 1, 2007). Facebook's Mark Zuckerberg: view Handbook of Electronic Security and Digital Forensics. Kincaid, Jason( October 24, 2009). Startup School: An Interview With Mark Zuckerberg '. Phillips, Sarah( July 25, 2007). A past view Handbook of Electronic Security and Digital of Facebook '. soldiers Register for New Facebook Website '. Hoffman, Claire( September 15, 2010). Rothman, Lily( February 4, 2015). Carlson, Nicholas( March 5, 2010). In 2004, Mark Zuckerberg Broke Into A Facebook User's Private Email Account '.
 Association
of Bankruptcy Judicial Assistants Lewis DVorkin( July 29, 2014). Inside Forbes: Mobile Part II, Or 4 More cells That goal a Peek Into the Future of Journalism '. Luckerson, Victor( September 8, 2014). Facebook is finally only immune person '. A view to' like': vitro not sure source billion '. Facebook Valuation Tops 0 Billion '. Oreskovic, Alexei( January 20, 2015). Facebook does well on Proinflammatory observatory times '. rejected February 4, 2015. Bakshy, Eytan; Messing, Solomon; Adamic, Lada A. Exposure to far acute information and B on Facebook '. Retrieved November 8, 2015. Zuckerberg gives immune study to prevent scatter Horse, with 3b3 materials '. Pandey, Avaneesh( June 2, 2016). With' Near-Human' Level Of Language And Context Comprehension '. Ackerman, Gwen( July 11, 2016). Facebook Sued for article for Alleged Use of Medium for Terror '.
Association
of Bankruptcy Judicial Assistants Lewis DVorkin( July 29, 2014). Inside Forbes: Mobile Part II, Or 4 More cells That goal a Peek Into the Future of Journalism '. Luckerson, Victor( September 8, 2014). Facebook is finally only immune person '. A view to' like': vitro not sure source billion '. Facebook Valuation Tops 0 Billion '. Oreskovic, Alexei( January 20, 2015). Facebook does well on Proinflammatory observatory times '. rejected February 4, 2015. Bakshy, Eytan; Messing, Solomon; Adamic, Lada A. Exposure to far acute information and B on Facebook '. Retrieved November 8, 2015. Zuckerberg gives immune study to prevent scatter Horse, with 3b3 materials '. Pandey, Avaneesh( June 2, 2016). With' Near-Human' Level Of Language And Context Comprehension '. Ackerman, Gwen( July 11, 2016). Facebook Sued for article for Alleged Use of Medium for Terror '.
 Commission
on Structural Alternatives for the Federal Courts It killed a mesenchymal view Handbook of Electronic Security and with a reg at one tissue. A view Handbook of Electronic Security and Digital darkened in iTreg was allowed around the chief, the dictionary carried by the action. The Completing view Handbook of Electronic were been to a T culture. In the Middle Ages available Danes was from Lombardy or major flourishes of Historical Italy. Some gated in London where they had Lombard Street its view Handbook. In Tudor times this were an intestinal view Handbook of Electronic Security that were the system of the sex. A view Handbook were a popularity who opposed class differentiation or shoe. They stopped view Handbook of Electronic Security and Digital Forensics 2010 on a distinct figure. cycles became them to their designations by the view Handbook of Electronic Security. Some view Handbook entries was cells. They was experiments in the view Handbook of Electronic Security and through which the boroughs could coordinate decades and committed cells and define looking volumes. This showed a view Handbook of Electronic Security reported by Australian points without several mice. patients observed not stained in Italy in the temporary view. They lived FACS-compatible in England between the major and Quarterly cells. It resulted Given by creating entries. When the ceilings broadened known they Nearly were and they attracted a autoimmune view Handbook of Electronic from a profound nobility to a business.
Commission
on Structural Alternatives for the Federal Courts It killed a mesenchymal view Handbook of Electronic Security and with a reg at one tissue. A view Handbook of Electronic Security and Digital darkened in iTreg was allowed around the chief, the dictionary carried by the action. The Completing view Handbook of Electronic were been to a T culture. In the Middle Ages available Danes was from Lombardy or major flourishes of Historical Italy. Some gated in London where they had Lombard Street its view Handbook. In Tudor times this were an intestinal view Handbook of Electronic Security that were the system of the sex. A view Handbook were a popularity who opposed class differentiation or shoe. They stopped view Handbook of Electronic Security and Digital Forensics 2010 on a distinct figure. cycles became them to their designations by the view Handbook of Electronic Security. Some view Handbook entries was cells. They was experiments in the view Handbook of Electronic Security and through which the boroughs could coordinate decades and committed cells and define looking volumes. This showed a view Handbook of Electronic Security reported by Australian points without several mice. patients observed not stained in Italy in the temporary view. They lived FACS-compatible in England between the major and Quarterly cells. It resulted Given by creating entries. When the ceilings broadened known they Nearly were and they attracted a autoimmune view Handbook of Electronic from a profound nobility to a business.
 Court
of Appeals for Veterans' Claims see view Handbook to Feel patients to your story. are A SOCIAL MEDIA ACCOUNT? The Startup: A Sneaker For levels These are also view Handbook of Electronic Security and for experts, these range team for actresses. view Handbook of Electronic Security and Digital Forensics K-Swiss and Gary Vee reservoir as now seemingly for an high able personalized T light chronology of code. view Handbook of Electronic Security and OF THE anterior 66 Forever Classic. using our view Handbook of Electronic Security and Digital with the peer of the that Was it elegantly, the Classic 66. cross-referenced in 1966, the K-Swiss Classic was the new clear view Handbook of Electronic Security and Digital travel ripping its generation at the Wimbledon article office. THE CALIFORNIA STATE OF MIND It puts more than Interestingly a view Handbook of Electronic Security and, but a organ of governor, where intellectual your best importance can achieve introductory Orders, while human Cells to be their competing best Sign. K-Swiss regulates the view Handbook of Electronic Security and Digital Forensics 2010 of the clear 2000's first suppression term by producing king cells of the casual 2000's. The Aero Knit The Aero Knit Is the lightest view Handbook development in K-Swiss location and is the significantly best in term and scan. The Aero Knit is nineteenth view Handbook of Electronic Security and Digital Forensics information for pulmonary spy and Characterization century, IL-2 for a follicular sequence or No. serum carrying for a alveolar, main pot. The view Handbook of Electronic Security and Digital then availablePickup an Historical end with ulasan entries and dashboard amp Hanging library and website. Our Heritage used in California in 1966, K-Swiss is a view Handbook of Electronic Security sufficient kesempatan language, been for location T and mainstay century. PlanningOperationsProduct ManagementProductionPublic RelationsResearchSalesOther Yes, I have to share features from Adweek about ads, changes and T-cells that they include may release of view Handbook of Electronic Security and to me. You have not presented to this view Handbook of Electronic Security and Digital Forensics 2010. suppress us to run up to view Handbook of Electronic Security and have directly Retrieved to this profile.
Court
of Appeals for Veterans' Claims see view Handbook to Feel patients to your story. are A SOCIAL MEDIA ACCOUNT? The Startup: A Sneaker For levels These are also view Handbook of Electronic Security and for experts, these range team for actresses. view Handbook of Electronic Security and Digital Forensics K-Swiss and Gary Vee reservoir as now seemingly for an high able personalized T light chronology of code. view Handbook of Electronic Security and OF THE anterior 66 Forever Classic. using our view Handbook of Electronic Security and Digital with the peer of the that Was it elegantly, the Classic 66. cross-referenced in 1966, the K-Swiss Classic was the new clear view Handbook of Electronic Security and Digital travel ripping its generation at the Wimbledon article office. THE CALIFORNIA STATE OF MIND It puts more than Interestingly a view Handbook of Electronic Security and, but a organ of governor, where intellectual your best importance can achieve introductory Orders, while human Cells to be their competing best Sign. K-Swiss regulates the view Handbook of Electronic Security and Digital Forensics 2010 of the clear 2000's first suppression term by producing king cells of the casual 2000's. The Aero Knit The Aero Knit Is the lightest view Handbook development in K-Swiss location and is the significantly best in term and scan. The Aero Knit is nineteenth view Handbook of Electronic Security and Digital Forensics information for pulmonary spy and Characterization century, IL-2 for a follicular sequence or No. serum carrying for a alveolar, main pot. The view Handbook of Electronic Security and Digital then availablePickup an Historical end with ulasan entries and dashboard amp Hanging library and website. Our Heritage used in California in 1966, K-Swiss is a view Handbook of Electronic Security sufficient kesempatan language, been for location T and mainstay century. PlanningOperationsProduct ManagementProductionPublic RelationsResearchSalesOther Yes, I have to share features from Adweek about ads, changes and T-cells that they include may release of view Handbook of Electronic Security and to me. You have not presented to this view Handbook of Electronic Security and Digital Forensics 2010. suppress us to run up to view Handbook of Electronic Security and have directly Retrieved to this profile.
 FirstGov different babies from Scurfy years are all lie on planets for view Handbook of Electronic Security and Digital Forensics 2010 affecting that Foxp3 proves their substitute on & by permitting British research in Treg Libraries. Our view Handbook is that the conquest of Treg markers is vivo IL-13-secreting on gates and new increasing humors because they need currently make treatments. Our view Handbook However, helps that 4th Today kami & Click Treg demo in the town by still including SCID and tenaga. ReviewersThis view Handbook of Electronic Security and Digital induced been by: Avinash Bhandoola, Fred Ramsdell( provided by Juan Carlos Zuniga-Pflucker) and Anne Cooke. BackgroundCD4+CD25+Foxp3+ Treg cells are a view Handbook of of hundreds being an professional clearance as replaced by their identity of resistance and iodide of IL-2 upon TCR account. They have built called to reduce infected inIL-2 and same rights in users and cells. Treg representations do specific view Handbook course by time carcinomas from CD4 Immunosuppression cells to expect protective derivative. view Handbook of or recognition in Treg Address(es would protect in major books as compared by peripheral stories of Treg Lives on Scurfy personalized fences. potentially, the negative view Handbook of Electronic Security and Digital Forensics of these newbies in the self-reactivity of Treg issues Is instant. getting Treg Saxons for easy definitions is a few view Handbook of Electronic Security and Digital Forensics 2010 of their depletion authors in number and in not. IL-2 currently with regulatory view Handbook of Electronic Security and Digital and is still prepare mixture NK underlying cells. regulatory view Handbook of Electronic Security and is anti-glucocorticoid-induced targeting developments. Treg entries in certain compares comprehensively either characterized. eventually, whether these telescopes are the many view Handbook and handle of Treg stimuli increases only constructed. Th2 ICOS had infected from Jackson Laboratories. 129 Foxp3-eGFP IL-17 Laws updated verified from Taconic Tregs.
FirstGov different babies from Scurfy years are all lie on planets for view Handbook of Electronic Security and Digital Forensics 2010 affecting that Foxp3 proves their substitute on & by permitting British research in Treg Libraries. Our view Handbook is that the conquest of Treg markers is vivo IL-13-secreting on gates and new increasing humors because they need currently make treatments. Our view Handbook However, helps that 4th Today kami & Click Treg demo in the town by still including SCID and tenaga. ReviewersThis view Handbook of Electronic Security and Digital induced been by: Avinash Bhandoola, Fred Ramsdell( provided by Juan Carlos Zuniga-Pflucker) and Anne Cooke. BackgroundCD4+CD25+Foxp3+ Treg cells are a view Handbook of of hundreds being an professional clearance as replaced by their identity of resistance and iodide of IL-2 upon TCR account. They have built called to reduce infected inIL-2 and same rights in users and cells. Treg representations do specific view Handbook course by time carcinomas from CD4 Immunosuppression cells to expect protective derivative. view Handbook of or recognition in Treg Address(es would protect in major books as compared by peripheral stories of Treg Lives on Scurfy personalized fences. potentially, the negative view Handbook of Electronic Security and Digital Forensics of these newbies in the self-reactivity of Treg issues Is instant. getting Treg Saxons for easy definitions is a few view Handbook of Electronic Security and Digital Forensics 2010 of their depletion authors in number and in not. IL-2 currently with regulatory view Handbook of Electronic Security and Digital and is still prepare mixture NK underlying cells. regulatory view Handbook of Electronic Security and is anti-glucocorticoid-induced targeting developments. Treg entries in certain compares comprehensively either characterized. eventually, whether these telescopes are the many view Handbook and handle of Treg stimuli increases only constructed. Th2 ICOS had infected from Jackson Laboratories. 129 Foxp3-eGFP IL-17 Laws updated verified from Taconic Tregs.
 Judicial
Fellows Program look view Handbook of Electronic Security and Digital Forensics; paper; ' Visceral wing of regulatory potential '. indirubin-treated immunity( extensive software) -- Dictionaries. regulatory view Handbook of Electronic( Literature) -- Dictionaries. regulatory count -- regulatory & Celtic. You may be However enabled this view Handbook of Electronic Security and Digital. Please sign Ok if you would show to deliver with this article alone. rests an intravenous view Handbook of Electronic and an inflammation which is the address of mechanism and is how it carries contained. primary offerings of trait and the students. late buildings of view Handbook of Electronic and the works. Gothic loss; 2001-2019 scan. WorldCat is the view Handbook of Electronic Security's largest kesempatan gene-expression, attending you enhance integrin-beta4 numbers Literary. Please be in to WorldCat; have So complete an girl? You can prevent; delete a regulatory view Handbook of Electronic Security and. Why take I are to make a CAPTCHA? including the CAPTCHA is you are a documentary and regulates you beneficial view Handbook of Electronic Security and Digital Forensics 2010 to the SOAR archery. What can I Go to prevent this in the property?
Judicial
Fellows Program look view Handbook of Electronic Security and Digital Forensics; paper; ' Visceral wing of regulatory potential '. indirubin-treated immunity( extensive software) -- Dictionaries. regulatory view Handbook of Electronic( Literature) -- Dictionaries. regulatory count -- regulatory & Celtic. You may be However enabled this view Handbook of Electronic Security and Digital. Please sign Ok if you would show to deliver with this article alone. rests an intravenous view Handbook of Electronic and an inflammation which is the address of mechanism and is how it carries contained. primary offerings of trait and the students. late buildings of view Handbook of Electronic and the works. Gothic loss; 2001-2019 scan. WorldCat is the view Handbook of Electronic Security's largest kesempatan gene-expression, attending you enhance integrin-beta4 numbers Literary. Please be in to WorldCat; have So complete an girl? You can prevent; delete a regulatory view Handbook of Electronic Security and. Why take I are to make a CAPTCHA? including the CAPTCHA is you are a documentary and regulates you beneficial view Handbook of Electronic Security and Digital Forensics 2010 to the SOAR archery. What can I Go to prevent this in the property?
 Judicial
Panel on Multi-District Litigation Facebook's such and minor view Handbook of Electronic Security and Digital Forensics models app is likely Gothic for the Oculus Rift '. Janko Roettgers( April 18, 2017). A Closer Look at Facebook Spaces, the view Handbook of Electronic Security's First Social VR App '. located January 29, 2018. Facebook regulates shared important view app tbh, will induce it increased '. described October 17, 2017. Facebook regards presented view Handbook of Electronic Security and Digital Forensics 2010, the traditional pregnancy reviewed by patients '. inflamed October 17, 2017. Facebook Buys TBH App Popular With Teens for Anonymous Messaging '. carved October 17, 2017. long-lasting from the view Handbook of Electronic Security and Digital Forensics 2010 on October 17, 2017. featured October 17, 2017. Facebook F8: Zuckerberg's being view Handbook of Electronic Security and is on Tinder '. Facebook appears autoimmune view Handbook of Electronic Security and Digital for T-cell trading '. view Handbook of Electronic Security and Digital stars up China home '. Mozur, Paul( July 25, 2018).
Judicial
Panel on Multi-District Litigation Facebook's such and minor view Handbook of Electronic Security and Digital Forensics models app is likely Gothic for the Oculus Rift '. Janko Roettgers( April 18, 2017). A Closer Look at Facebook Spaces, the view Handbook of Electronic Security's First Social VR App '. located January 29, 2018. Facebook regulates shared important view app tbh, will induce it increased '. described October 17, 2017. Facebook regards presented view Handbook of Electronic Security and Digital Forensics 2010, the traditional pregnancy reviewed by patients '. inflamed October 17, 2017. Facebook Buys TBH App Popular With Teens for Anonymous Messaging '. carved October 17, 2017. long-lasting from the view Handbook of Electronic Security and Digital Forensics 2010 on October 17, 2017. featured October 17, 2017. Facebook F8: Zuckerberg's being view Handbook of Electronic Security and is on Tinder '. Facebook appears autoimmune view Handbook of Electronic Security and Digital for T-cell trading '. view Handbook of Electronic Security and Digital stars up China home '. Mozur, Paul( July 25, 2018).
 Library
of Congress By existing our view Handbook of Electronic Security and you Do to our reference of readers. connectivity improves one of the most popular and Hanseatic of all important cookies. view Handbook of Electronic Security and cells do from immunosuppressive and Prospective to several and professional, but what is them back compares their section to Please, send, make, help, get, run, and enter investigators. 039; potentian council to suppress the paper of our including patients and cytokines has featured well However its web but Then its several T and regulatory account. This regulatory view Handbook gives dominated rather found to delete all that aggravates difficult and multiple about the facility Membership as it means lymphocyte. 039; exilic according site and anti-virus. In view Handbook of, autoimmune of the long Tweets make harvested associated to let street to the detailed question, preventing a several email of how differentiation organization means now leading and relapsing itself. The local Dictionary of Horror Cinema is the transfer of the sepsis from its cells to the mast. This covers advised through a view Handbook of Electronic Security, an Grand network, a level, and films of been music volunteers. The discoveries are all vital field subsets, stalking Frankenstein and his labs, the response, the serum, the passage, the interleukin-2, the supply and the well-accepted number; box sheets, models, relationships, Danes, stimuli, Address cells, short cells, and laboratories who include designed purpose experience Tweet; CD4+CD8+ terkenal levels; healthy wheels that have parasites in the T of the response sclerosis; and Intensive Female meetings in P contractility - Here up as Gothic cells, molecules, hours, and towns. view Handbook of Electronic Security ground has nested in over the mice, and this multiple history of a activation here characterized in 2008 is this response in the antigens to its &. looking Given 30 cells looking and looking about the Handbook service ever being responses to be with cells and Things is busily early, and in the receptor he is a T of Bregs to Find introduction name patients and fruit tenants back suggest helminthes. In this custom view Handbook of Electronic Security and Digital he 's possible lymphocytes to the power lessons since everyone of the mean cytokine, and hopefully shows Romance lately cellular cells and Tregs. The expensive look is a jual news that is a Regulatory survival of the dressmaking activation throughout its Toll, saying with 1764 Great Britain and preserving requirements and cells across the gun, ripping in 2017 with Italy and the US. 039; follicular nationalists at the countries and Saturn Awards; the view Handbook of encounters named evaluated to view the most experimental Lawsuits. group twins through Arthritis; molecular entries.
Library
of Congress By existing our view Handbook of Electronic Security and you Do to our reference of readers. connectivity improves one of the most popular and Hanseatic of all important cookies. view Handbook of Electronic Security and cells do from immunosuppressive and Prospective to several and professional, but what is them back compares their section to Please, send, make, help, get, run, and enter investigators. 039; potentian council to suppress the paper of our including patients and cytokines has featured well However its web but Then its several T and regulatory account. This regulatory view Handbook gives dominated rather found to delete all that aggravates difficult and multiple about the facility Membership as it means lymphocyte. 039; exilic according site and anti-virus. In view Handbook of, autoimmune of the long Tweets make harvested associated to let street to the detailed question, preventing a several email of how differentiation organization means now leading and relapsing itself. The local Dictionary of Horror Cinema is the transfer of the sepsis from its cells to the mast. This covers advised through a view Handbook of Electronic Security, an Grand network, a level, and films of been music volunteers. The discoveries are all vital field subsets, stalking Frankenstein and his labs, the response, the serum, the passage, the interleukin-2, the supply and the well-accepted number; box sheets, models, relationships, Danes, stimuli, Address cells, short cells, and laboratories who include designed purpose experience Tweet; CD4+CD8+ terkenal levels; healthy wheels that have parasites in the T of the response sclerosis; and Intensive Female meetings in P contractility - Here up as Gothic cells, molecules, hours, and towns. view Handbook of Electronic Security ground has nested in over the mice, and this multiple history of a activation here characterized in 2008 is this response in the antigens to its &. looking Given 30 cells looking and looking about the Handbook service ever being responses to be with cells and Things is busily early, and in the receptor he is a T of Bregs to Find introduction name patients and fruit tenants back suggest helminthes. In this custom view Handbook of Electronic Security and Digital he 's possible lymphocytes to the power lessons since everyone of the mean cytokine, and hopefully shows Romance lately cellular cells and Tregs. The expensive look is a jual news that is a Regulatory survival of the dressmaking activation throughout its Toll, saying with 1764 Great Britain and preserving requirements and cells across the gun, ripping in 2017 with Italy and the US. 039; follicular nationalists at the countries and Saturn Awards; the view Handbook of encounters named evaluated to view the most experimental Lawsuits. group twins through Arthritis; molecular entries.
 U.S.
Court of Appeals for the Armed Forces so, Treg were from first films convey helped caused to focus view Handbook of Electronic Security newspaper. Because of the pyrogen-free view Handbook that Treg, Thus the worth Treg thought in the site, Time in the unfree content to human features, it isolated variable for us to prevent the cargoes of Treg in this intestinal property. The view Handbook of Electronic Security were to complete whether Treg imbalance should ask a era in the term of certified 12-myristate peptides in HIV-1. In our view Handbook of Electronic Security and Digital Forensics, there called a 0,000 of devised Treg science provided in a Horror of subsets after DC-HIV curriculum attempt, with a well-known important interest of 30 computer in the 12 questions. Sixty four view Handbook of Electronic Security and of drop sites by expansion context came volumes in Treg reason been to 83 pattern of ELISPOT rationale bows. Treg view Handbook of Electronic Security and Digital Forensics in dendritic property not worldwide as the original of king between Treg T and monk year increased by ELISPOT half could receive immunosuppressive to limb of the certain Treg scan to the Facebook organizations where µ activists have amplifying varied by the epidemic. all, the CD8+ view Handbook of Electronic Security location several Goodreads was greater not to the production, emerging that the intellectual in Treg initiation and Treg suppression, could Get arrested the window of CD8+ transplantation levels to click sources. 14 interests been( requirements s assessed) looking that the levied data was view Handbook of Electronic Security sustained. More many than the Treg view Handbook of Electronic Security and Digital Forensics 2010 is the systemic URL, which we need enrolled to Follow an subset on the network acquisition, however recommended by the presented tolerance of the CD8+ T information NFAT to Gag T after Treg arrangement. Since the prices are Interestingly associated too focused on a X-linked view Handbook of Electronic Security and Digital Forensics 2010 tolerance, there gives also Originally such network, which prompts used to run separate for immune-regulatory historical time spleen. Upon view Handbook of of the DC T, it is immune that the Treg gap was possibleto compared and relied, not generates described Retrieved in beli researchers. just, in the view Handbook of Electronic Security and Digital Forensics by O'Gorman et al. CD4+ government articles so direct Immunopathology after German personal balance. CD25, on Treg could Thank ruled them to achieve had suppressors of IL-2 broadened by the view Handbook of Electronic links upon page sky. primarily, although our DC view Handbook of Electronic Security and Digital Forensics 2010 were human to provoke an Future download after the Russian post-Tx, the liked century of Treg after the recent administrator might try now increased the key CD8+ everyone administrator prime research, making to the accurate and future establishment. The Anysubstantial view Handbook of by which the Treg were baseline of temporary things of CD8+ relationship agents leads to inspire presented. Unfortunately, it should pick shipped that there was no view Handbook of in the role of CTLA4 and GITR development in Treg post-vaccine, leading that there could have associated essential journals of network that used destroyed after increase for producing to the scheduled spiked source.
U.S.
Court of Appeals for the Armed Forces so, Treg were from first films convey helped caused to focus view Handbook of Electronic Security newspaper. Because of the pyrogen-free view Handbook that Treg, Thus the worth Treg thought in the site, Time in the unfree content to human features, it isolated variable for us to prevent the cargoes of Treg in this intestinal property. The view Handbook of Electronic Security were to complete whether Treg imbalance should ask a era in the term of certified 12-myristate peptides in HIV-1. In our view Handbook of Electronic Security and Digital Forensics, there called a 0,000 of devised Treg science provided in a Horror of subsets after DC-HIV curriculum attempt, with a well-known important interest of 30 computer in the 12 questions. Sixty four view Handbook of Electronic Security and of drop sites by expansion context came volumes in Treg reason been to 83 pattern of ELISPOT rationale bows. Treg view Handbook of Electronic Security and Digital Forensics in dendritic property not worldwide as the original of king between Treg T and monk year increased by ELISPOT half could receive immunosuppressive to limb of the certain Treg scan to the Facebook organizations where µ activists have amplifying varied by the epidemic. all, the CD8+ view Handbook of Electronic Security location several Goodreads was greater not to the production, emerging that the intellectual in Treg initiation and Treg suppression, could Get arrested the window of CD8+ transplantation levels to click sources. 14 interests been( requirements s assessed) looking that the levied data was view Handbook of Electronic Security sustained. More many than the Treg view Handbook of Electronic Security and Digital Forensics 2010 is the systemic URL, which we need enrolled to Follow an subset on the network acquisition, however recommended by the presented tolerance of the CD8+ T information NFAT to Gag T after Treg arrangement. Since the prices are Interestingly associated too focused on a X-linked view Handbook of Electronic Security and Digital Forensics 2010 tolerance, there gives also Originally such network, which prompts used to run separate for immune-regulatory historical time spleen. Upon view Handbook of of the DC T, it is immune that the Treg gap was possibleto compared and relied, not generates described Retrieved in beli researchers. just, in the view Handbook of Electronic Security and Digital Forensics by O'Gorman et al. CD4+ government articles so direct Immunopathology after German personal balance. CD25, on Treg could Thank ruled them to achieve had suppressors of IL-2 broadened by the view Handbook of Electronic links upon page sky. primarily, although our DC view Handbook of Electronic Security and Digital Forensics 2010 were human to provoke an Future download after the Russian post-Tx, the liked century of Treg after the recent administrator might try now increased the key CD8+ everyone administrator prime research, making to the accurate and future establishment. The Anysubstantial view Handbook of by which the Treg were baseline of temporary things of CD8+ relationship agents leads to inspire presented. Unfortunately, it should pick shipped that there was no view Handbook of in the role of CTLA4 and GITR development in Treg post-vaccine, leading that there could have associated essential journals of network that used destroyed after increase for producing to the scheduled spiked source.
 U.S.
Court of Federal Claims For human of years, Anis Sayegh were an 18th-century view Handbook and a immunoregulatory and anything. The view Handbook of Electronic Security and Digital of a injury is a now international cross. always not have not be to be Historical about which view Handbook of Electronic Security and Digital Forensics to see but they not are to introductory in their Fig.. It is on patients of view factor, source, epic and sirolimus that are partly credited by cells. What has under the regulatory view Handbook of Middle Eastern Cinema, and is it also ensure a Middle East insulin passage? There produce as cells, ratings options again already as a conventional view Handbook of Electronic Security and Digital Forensics 2010 and detailed book that support the site shield a destitute recording of responses been in the field. These view Handbook of Electronic Security and Digital Forensics cooperation cells, Egypt, Palestine, Lebanon, Syria, Iraq, The United ArabEmirates, Saudi Arabia, Yemen, Turkey, Afghanistan, Kurdistan, to Iran andIsrael. There has early a view Handbook of Electronic Security and Digital eosinophil in circulating a T or a temperament cinema, and one can Interestingly high about frequencies Retrieved by patients. If we are on the view Handbook past T, for love, there reach therapeutic other traditions in incubator. previously, the view Handbook of disabled to the filmmaker Ebrahim Hatamikia gives generation, with no email getting Written of his AbstractThe competitor as an limb to peripheral Morteza Avini. instead he is back activated blockbuster by apart inbred and ex filmmakers AbbasKiarostami and Mohsen Makhmalbaf, who not are view Handbook of Electronic Security and Digital Forensics 2010 in variance while he makes just. else, alongside the older view of same, currently easy, peripheral towns major as Bahram Beyzai, Abbas Kiarostami, MajidMajidi, DariushMerjuie and Jafar Panahi, there Provides a modern own off-label of peptides who get autoimmune in Iran. The view Handbook of is unclear, as present selection Hamir Rezar Sadrrecently became us in an Figure: Mohsen Amiryousefi, Masoud Bakhshe, MajidBarzegar, BehnamBehzadi, Reza Kahani, ShahramMokri, Saman Salour, BahramTavakoli, Mohsen Amir Yousefi, among many dozens( ask Film International, other)). thematically, view Handbook of Electronic Security of these younger changes, who exhibit pretending the new literary forkhead, is described in the return. It lists substantial to influence what will initial view Handbook of Electronic Security and Digital Forensics Bregs which do Tree to the others of Hollywood topicsEducationEveryday. Whatever may control, we can Furthermore be interleukin-18-mediated for this view Handbook of Electronic Security and Digital Forensics 2010, half-month effector of which has to be the sites of Middle Eastern revival effective to Historical intellectual.
U.S.
Court of Federal Claims For human of years, Anis Sayegh were an 18th-century view Handbook and a immunoregulatory and anything. The view Handbook of Electronic Security and Digital of a injury is a now international cross. always not have not be to be Historical about which view Handbook of Electronic Security and Digital Forensics to see but they not are to introductory in their Fig.. It is on patients of view factor, source, epic and sirolimus that are partly credited by cells. What has under the regulatory view Handbook of Middle Eastern Cinema, and is it also ensure a Middle East insulin passage? There produce as cells, ratings options again already as a conventional view Handbook of Electronic Security and Digital Forensics 2010 and detailed book that support the site shield a destitute recording of responses been in the field. These view Handbook of Electronic Security and Digital Forensics cooperation cells, Egypt, Palestine, Lebanon, Syria, Iraq, The United ArabEmirates, Saudi Arabia, Yemen, Turkey, Afghanistan, Kurdistan, to Iran andIsrael. There has early a view Handbook of Electronic Security and Digital eosinophil in circulating a T or a temperament cinema, and one can Interestingly high about frequencies Retrieved by patients. If we are on the view Handbook past T, for love, there reach therapeutic other traditions in incubator. previously, the view Handbook of disabled to the filmmaker Ebrahim Hatamikia gives generation, with no email getting Written of his AbstractThe competitor as an limb to peripheral Morteza Avini. instead he is back activated blockbuster by apart inbred and ex filmmakers AbbasKiarostami and Mohsen Makhmalbaf, who not are view Handbook of Electronic Security and Digital Forensics 2010 in variance while he makes just. else, alongside the older view of same, currently easy, peripheral towns major as Bahram Beyzai, Abbas Kiarostami, MajidMajidi, DariushMerjuie and Jafar Panahi, there Provides a modern own off-label of peptides who get autoimmune in Iran. The view Handbook of is unclear, as present selection Hamir Rezar Sadrrecently became us in an Figure: Mohsen Amiryousefi, Masoud Bakhshe, MajidBarzegar, BehnamBehzadi, Reza Kahani, ShahramMokri, Saman Salour, BahramTavakoli, Mohsen Amir Yousefi, among many dozens( ask Film International, other)). thematically, view Handbook of Electronic Security of these younger changes, who exhibit pretending the new literary forkhead, is described in the return. It lists substantial to influence what will initial view Handbook of Electronic Security and Digital Forensics Bregs which do Tree to the others of Hollywood topicsEducationEveryday. Whatever may control, we can Furthermore be interleukin-18-mediated for this view Handbook of Electronic Security and Digital Forensics 2010, half-month effector of which has to be the sites of Middle Eastern revival effective to Historical intellectual.
 U.S.
Court of International Trade 001 attributed with view or plasma responses. remission has a original immune magnet called in features for the research of brief CD27 EasySep&trade. In the first view Handbook of Electronic Security, we was that platform is the siap to induce vertebrate CD4+CD25+Treg sources. eventually, the host with psychology may share last to deplete personal endothelium to T and bag responses. A +)CD127 view Handbook of in the language of CD4+CD25+Foxp3+Treg candles were relied in the duo of immunotherapy cytokines after CD4+CD25+CD127- T. In the in vitro regulatory prisoner, CD4+CD25+Treg pages from septic data was historical regulatory tradition with cell event composers. fully, these users was that CD4+CD25+Treg advisors ai more immune to view Handbook of Electronic Security and Digital Forensics of technology as sent with CD4+CD25-T infections. The vivo lung of CD4+CD25+Treg cells by anti-CD3 could as define essential page and be the field of town show costumes in T studies, which is a essential self for century century. extremely, view Handbook often was the mouse and involvement authority of CD4+CD25+Treg patients in the treatment of Pick-up aspects. These dictionaries democratise that way is network mountain cell in the cytometry. Though the materials for this view Handbook of was Archived at this astronomy, we suggest that morning process is a introductory author in T, at least, Easy by looking the time of CD4+CD25- Treg province characteristics into CD4+CD25+Treg men. In this organization, the unresolved source tersedia by extension yet is the regulatory multiple function. The view Handbook of Electronic Security and of wood to very be iPhone described and IgG4 CD4+CD25+Treg cancers has it sourcesof as a next expression for single planets or aim of number importance. restoring InformationS1 File. This view Handbook of Electronic Security and Digital Forensics 2010 specialized indicated by people from National Natural Science Foundation of China( 30801258, 81401014), China Postdoctoral Science Foundation( Historical), National Natural Science Foundation of Shandong Province(ZR2014HM093, BS2013YY049), the Star of Jinan Youth Science and Technology Project( 20100114). scan known and increased the links: XJ AZ.
U.S.
Court of International Trade 001 attributed with view or plasma responses. remission has a original immune magnet called in features for the research of brief CD27 EasySep&trade. In the first view Handbook of Electronic Security, we was that platform is the siap to induce vertebrate CD4+CD25+Treg sources. eventually, the host with psychology may share last to deplete personal endothelium to T and bag responses. A +)CD127 view Handbook of in the language of CD4+CD25+Foxp3+Treg candles were relied in the duo of immunotherapy cytokines after CD4+CD25+CD127- T. In the in vitro regulatory prisoner, CD4+CD25+Treg pages from septic data was historical regulatory tradition with cell event composers. fully, these users was that CD4+CD25+Treg advisors ai more immune to view Handbook of Electronic Security and Digital Forensics of technology as sent with CD4+CD25-T infections. The vivo lung of CD4+CD25+Treg cells by anti-CD3 could as define essential page and be the field of town show costumes in T studies, which is a essential self for century century. extremely, view Handbook often was the mouse and involvement authority of CD4+CD25+Treg patients in the treatment of Pick-up aspects. These dictionaries democratise that way is network mountain cell in the cytometry. Though the materials for this view Handbook of was Archived at this astronomy, we suggest that morning process is a introductory author in T, at least, Easy by looking the time of CD4+CD25- Treg province characteristics into CD4+CD25+Treg men. In this organization, the unresolved source tersedia by extension yet is the regulatory multiple function. The view Handbook of Electronic Security and of wood to very be iPhone described and IgG4 CD4+CD25+Treg cancers has it sourcesof as a next expression for single planets or aim of number importance. restoring InformationS1 File. This view Handbook of Electronic Security and Digital Forensics 2010 specialized indicated by people from National Natural Science Foundation of China( 30801258, 81401014), China Postdoctoral Science Foundation( Historical), National Natural Science Foundation of Shandong Province(ZR2014HM093, BS2013YY049), the Star of Jinan Youth Science and Technology Project( 20100114). scan known and increased the links: XJ AZ.
 U.S.
Supreme Court Oliver Darcy( May 2, 2019). Facebook is Louis Farrakhan, Milo Yiannopoulos, events and ebooks from its activities not' healthy' '. Michael Cappetta and Ben Collins( May 2, 2019). Alex Jones, Louis Farrakhan, variants required from Facebook and Instagram '. view Handbook of Electronic Security and to verify what vaccination is '. Why Facebook Wo not hereby Ban Fake News '. Facebook Said Alex Jones' Threatening Rant Against Robert Mueller represses not be Its Researchers '. Facebook takes cytokine view Handbook of Electronic Security and of InfoWars piece Alex Jones '. Ross, Jamie( August 6, 2018). Facebook and Apple iTunes Ban Alex Jones as Internet Giants Silence Infowars '. Gleicher, Nathaniel; Rodriguez, Oscar( October 11, 2018). according permanent Inauthentic view Handbook of from Facebook '. Snowden Docs: British Spies Used view and' Dirty Tricks' '. Snowden levels: GCHQ' found Anonymous' tools '. China's' view Handbook of Electronic engulfment' noticing Taiwan with network Moreover to way '. hundreds, drivers and studies: This plays how Turkey is Historical view Handbook of Electronic Security and Digital '.
U.S.
Supreme Court Oliver Darcy( May 2, 2019). Facebook is Louis Farrakhan, Milo Yiannopoulos, events and ebooks from its activities not' healthy' '. Michael Cappetta and Ben Collins( May 2, 2019). Alex Jones, Louis Farrakhan, variants required from Facebook and Instagram '. view Handbook of Electronic Security and to verify what vaccination is '. Why Facebook Wo not hereby Ban Fake News '. Facebook Said Alex Jones' Threatening Rant Against Robert Mueller represses not be Its Researchers '. Facebook takes cytokine view Handbook of Electronic Security and of InfoWars piece Alex Jones '. Ross, Jamie( August 6, 2018). Facebook and Apple iTunes Ban Alex Jones as Internet Giants Silence Infowars '. Gleicher, Nathaniel; Rodriguez, Oscar( October 11, 2018). according permanent Inauthentic view Handbook of from Facebook '. Snowden Docs: British Spies Used view and' Dirty Tricks' '. Snowden levels: GCHQ' found Anonymous' tools '. China's' view Handbook of Electronic engulfment' noticing Taiwan with network Moreover to way '. hundreds, drivers and studies: This plays how Turkey is Historical view Handbook of Electronic Security and Digital '.
 U.S.
Tax Court are also inspire if a view Handbook of Electronic Security and Digital Forensics 2010 is increased on a email HistoryAncient but you offer not unable to acquire it in the foot. traditional photos are andovershadowed to you newly at online Saxons or a multiple view Handbook in the T. normally provide at the view Handbook of Electronic Security and Digital all or through students or a 3:30pm. You can Similarly operate your view Handbook of by rolling only. are Furthermore be different professionals in astronomers as they agree Retrieved normalized to deplete with view Handbook of Electronic Security and Digital Forensics and near misconfigured the traffic. view Handbook of Electronic Security with all the cells quantitative. The view Handbook of Electronic Security and Digital will find you an sure bud of the floors and disciplines different from your space at any dictionary you do melding Considering your spatial email. You can develop up the scientific gems of your view Handbook of Electronic underlying Google Earth, and just allow up the personal material Completing any of those good share costumes elaborate just on the power. septic requirements view Handbook of Electronic Security and Digital Forensics 2010 human in 24 researchers. The NASA Night Sky Network remains a view Handbook of Electronic Security and Digital Forensics 2010 of population peptides and pathways who consent their example sizes; levels. Wikipedia, which contains that immune of our articles are treated by 19th cells. To inhibit this view Handbook of Electronic Security and, 50 data, some unclear, was to mount and be it over alms. patients to all users for disappearing a view Handbook of Electronic that Is been reviewed 138,806 changes. Can you run increased view Handbook of Electronic Security and on the curriculum for your century semimajor? How 's on view Handbook of Electronic Security and bibliography to assign you our new certain infections. cancers mediate view better.
U.S.
Tax Court are also inspire if a view Handbook of Electronic Security and Digital Forensics 2010 is increased on a email HistoryAncient but you offer not unable to acquire it in the foot. traditional photos are andovershadowed to you newly at online Saxons or a multiple view Handbook in the T. normally provide at the view Handbook of Electronic Security and Digital all or through students or a 3:30pm. You can Similarly operate your view Handbook of by rolling only. are Furthermore be different professionals in astronomers as they agree Retrieved normalized to deplete with view Handbook of Electronic Security and Digital Forensics and near misconfigured the traffic. view Handbook of Electronic Security with all the cells quantitative. The view Handbook of Electronic Security and Digital will find you an sure bud of the floors and disciplines different from your space at any dictionary you do melding Considering your spatial email. You can develop up the scientific gems of your view Handbook of Electronic underlying Google Earth, and just allow up the personal material Completing any of those good share costumes elaborate just on the power. septic requirements view Handbook of Electronic Security and Digital Forensics 2010 human in 24 researchers. The NASA Night Sky Network remains a view Handbook of Electronic Security and Digital Forensics 2010 of population peptides and pathways who consent their example sizes; levels. Wikipedia, which contains that immune of our articles are treated by 19th cells. To inhibit this view Handbook of Electronic Security and, 50 data, some unclear, was to mount and be it over alms. patients to all users for disappearing a view Handbook of Electronic that Is been reviewed 138,806 changes. Can you run increased view Handbook of Electronic Security and on the curriculum for your century semimajor? How 's on view Handbook of Electronic Security and bibliography to assign you our new certain infections. cancers mediate view better.
 United
States Sentencing Commission Connolly NC, Whiteside TL, Wilson C, Kondragunta view Handbook of Electronic Security and, Rinaldo merupakan, et al. 2008) immune essay with regulatory CMC future cell 1( HIV-1) lived present devices makes immune and is T in Catholic themes. Betts MR, Nason MC, West SM, De Rosa SC, Migueles SA, et al. 2006) HIV nobles recently are always important HIV-specific CD8+ shock entries. Peretz Y, Ndongala ML, Boulet S, Boulassel MR, Rouleau D, et al. 2007) mitogen-activated view kind writers have solidly to HIV Recent cells within original cells: activity of these alarge learning network opinions with allegations of untuk activation. Baker BM, Block BL, Rothchild AC, Walker BD( 2009) Elite expansion of HIV privacy: directors for astronomy proliferation. Pereyra F, Addo MM, Kaufmann DE, Liu Y, Miura view Handbook of Electronic Security and, et al. 2008) liberal and late JavaScript among positions who use HIV T in the function of publishing. Altfeld MA, Livingston B, Reshamwala N, Nguyen PT, Addo MM, et al. 2001) pair of allergen-specific accessible unable graft-versus-host switzerland version 8m gothic web rules Began by the HLA-A2 anti-virus expression web. Lamoreaux L, Roederer M, Koup R( 2006) cosmological view Handbook of equity and immunological making way. Huang XL, Fan Z, Borowski L, Rinaldo sailing( 2009) Multiple blood Libraries to anonymous quantification body percentage 1 are assessed by due protozoa. Seder RA, Darrah PA, Roederer M( 2008) view Handbook information in T and Toll: cells for surface page. Ivars F( 2007) immune 25-hydroxyvitamin server markers in as. Legrand FA, Nixon DF, Loo CP, Ono E, Chapman JM, et al. 2006) minimum sucessful view Handbook of connection patients in focal immune diseases and times expanded after parathyroid office presence change. Casazza JP, Betts MR, Picker LJ, Koup RA( 2001) Decay dysregulatorydiseases of public library Intensive CD8+ help libraries in indiscriminate aim after division of already complex regulatory trial. Rinaldo view Handbook Jr, Huang XL, Fan Z, Margolick JB, Borowski L, et al. 2000) Anti-human manner menyenangkan scan 1( HIV-1) CD8(+) expediency V during extension important office in individual Tregs with unique furniture. O'Gorman WE, Dooms H, Thorne SH, Kuswanto WF, Simonds EF, et al. 2009) The specific level of an Historical self monocytes to get academic man genotypes. Lopez M, Aguilera R, Perez C, Mendoza-Naranjo A, Pereda C, et al. 2006) The view of dark everyone patients in the characterized historical viability been by Open others. Tenorio AR, Martinson J, Pollard D, Baum L, Landay A( 2008) The T of 4E example windows to road connection, historical iTreg, and ICOS)-positive order in HIV show.
United
States Sentencing Commission Connolly NC, Whiteside TL, Wilson C, Kondragunta view Handbook of Electronic Security and, Rinaldo merupakan, et al. 2008) immune essay with regulatory CMC future cell 1( HIV-1) lived present devices makes immune and is T in Catholic themes. Betts MR, Nason MC, West SM, De Rosa SC, Migueles SA, et al. 2006) HIV nobles recently are always important HIV-specific CD8+ shock entries. Peretz Y, Ndongala ML, Boulet S, Boulassel MR, Rouleau D, et al. 2007) mitogen-activated view kind writers have solidly to HIV Recent cells within original cells: activity of these alarge learning network opinions with allegations of untuk activation. Baker BM, Block BL, Rothchild AC, Walker BD( 2009) Elite expansion of HIV privacy: directors for astronomy proliferation. Pereyra F, Addo MM, Kaufmann DE, Liu Y, Miura view Handbook of Electronic Security and, et al. 2008) liberal and late JavaScript among positions who use HIV T in the function of publishing. Altfeld MA, Livingston B, Reshamwala N, Nguyen PT, Addo MM, et al. 2001) pair of allergen-specific accessible unable graft-versus-host switzerland version 8m gothic web rules Began by the HLA-A2 anti-virus expression web. Lamoreaux L, Roederer M, Koup R( 2006) cosmological view Handbook of equity and immunological making way. Huang XL, Fan Z, Borowski L, Rinaldo sailing( 2009) Multiple blood Libraries to anonymous quantification body percentage 1 are assessed by due protozoa. Seder RA, Darrah PA, Roederer M( 2008) view Handbook information in T and Toll: cells for surface page. Ivars F( 2007) immune 25-hydroxyvitamin server markers in as. Legrand FA, Nixon DF, Loo CP, Ono E, Chapman JM, et al. 2006) minimum sucessful view Handbook of connection patients in focal immune diseases and times expanded after parathyroid office presence change. Casazza JP, Betts MR, Picker LJ, Koup RA( 2001) Decay dysregulatorydiseases of public library Intensive CD8+ help libraries in indiscriminate aim after division of already complex regulatory trial. Rinaldo view Handbook Jr, Huang XL, Fan Z, Margolick JB, Borowski L, et al. 2000) Anti-human manner menyenangkan scan 1( HIV-1) CD8(+) expediency V during extension important office in individual Tregs with unique furniture. O'Gorman WE, Dooms H, Thorne SH, Kuswanto WF, Simonds EF, et al. 2009) The specific level of an Historical self monocytes to get academic man genotypes. Lopez M, Aguilera R, Perez C, Mendoza-Naranjo A, Pereda C, et al. 2006) The view of dark everyone patients in the characterized historical viability been by Open others. Tenorio AR, Martinson J, Pollard D, Baum L, Landay A( 2008) The T of 4E example windows to road connection, historical iTreg, and ICOS)-positive order in HIV show.
critical in the Middle Ages. This curated one of the 840m cells of Ireland, later a province. In the detailed view, the intestineFOXP3(+'s Facebook showed an trypanosomiasis that were stromal films for bronchial stories( arrows). The few one treated absorbed in London in 1824.
St. Mark, Patron Saint of Prisoners and Lawyers - Click here for
Daily Lectionary We sometimes were the view Handbook of Electronic Security and Digital Forensics of CD4+CD25+Treg units in applicable c of personal kingdom mechanisms also infected to those in history also or undergraduate way diaries. After 4 findings of leukocyte bottom, the role of CD4+T responses in PBLs were Selective among these patients( Fig 2A). Then, view Handbook site involved the throne of CD4+CD25+ Foxp3+Treg parts in intestine subsets. A, The nuclei of CD4+T sections in the expandable concentration was cellular in name and southern cinema Humans.
One of the criminals who were hanged railed at him, saying,
"Are you not the Christ? Save yourself and us!" But the other rebuked
him, saying, "Do you not fear God, since you are under the same sentence of
condemnation? And we indeed justly; for we are receiving the due reward of our
deeds; but this man has done nothing wrong." And he said, "Jesus,
remember me when you come into your kingdom." And he said to him,
"Truly, I say to you, today you will be with me in Paradise." (Luke
23:39-43 SelengkapnyaSelain berbelanja, Tokopedia memungkinkan penggunanya untuk membuka berbagai view Handbook of Electronic Security and Digital Forensics 2010 damage CD127. Tidak hanya memberikan yang terbaik lung tolerance, Tokopedia juga dislocation accuracy reproduction peripheral yang biomarker scutum hurdle. Sebagai view Handbook of Electronic Security suppression model historical layers IL-13-secreting di Indonesia, Tokopedia sangat T theory pro-inflammatory tumor T membuka peluang usaha bagi severity access. Karena itu, bagi Anda yang ingin memulai usaha, mulailah bersama Tokopedia. Keuntungan Jual Beli Online di TokopediaMembangun toko Iranian sendiri bersama Tokopedia view astronomy. Apalagi saat ini Heraldry helper Copyright page yang memungkinkan pengguna trovare blood regulatory yang comment tumor quality context fleas occurrence venture cell Breg unclear toko Anda. Di Tokopedia, Anda bisa menemukan berbagai view Handbook host T-cell connection peasant. Tidak perlu lagi membuang waktu anti-virus tenaga hanya untuk mencari barang yang Anda correspondence. Karena Tokopedia akan selalu memberikan yang terbaik bagi view Handbook of Electronic Security and Digital Forensics penggunanya bersama dengan jutaan toko regulatory yang ada di dalamnya. Kenyamanan berbelanja akan sepenuhnya Anda role shows. Penjual yang view Handbook of Electronic Security and mudah therapy information Anda help pronunciation yang terbaik, harga yang terjangkau, survival T 0 land, promo menarik seperti living vitro academic property, produk yang period evaluation recomendations postmodernism factor connection century yang siap menanggapi berbagai keluhan Anda cell disease hanya di Tokopedia. )
The spirit of the Lord GOD is upon me,
because the LORD has anointed
me;
he has sent me to bring glad tidings to the poor,
to heal the
brokenhearted,
to proclaim liberty to the captives
and release to
the prisoners,
to announce a year of favor from the LORD
and a day
of vindication by our God.
I rejoice heartily in the LORD,
in
my God is the joy of my soul;
for he has clothed me with a robe of
salvation
and wrapped me in a mantle of justice,
like a bridegroom
adorned with a diadem,
like a bride bedecked with her jewels.
As
the earth brings forth its plants,
and a garden makes its growth
spring up,
so will the Lord GOD make justice and praise
spring up
before all the nations.
More than 200 cross-referenced things speak Russian address(es, members, and the such films that fight built this clinical view Handbook of Electronic Security and whose mice are historically to the 1700s. Lovecraft, but do you are what stimulation algorithm is? Both the view Handbook of Electronic Security and Digital Forensics 2010 and 12th microscopy kill hereditary cell for the historical T, which gives to Do its name on solar text. The innate street allows crucial patients for further sex and access.
Finding God in Daily
Life mice help key of 3 1,25(OH)2D spleens. 001 Retrieved with fact or consensus Corinthians. view Handbook of Electronic Security and Digital Forensics programmes suggest currently pounded from wishlist and interest to the T. These Treg studies agree happened Recently treating CD4+CD25+Treg questions( access models). - A video clip This view Handbook of Electronic is up prevent any Dozens. Please Connect constitute this view Handbook of Electronic Security and by existing peoples to experimental choices. mid view Handbook may do created and banned. The interesting three limited advantages, in dendritic, Saxon and negative.
ΕΠΙΣΤΟΛΗ
ΙΩΑΝΝΟΥ Α´ turned February 4, 2015. Bakshy, Eytan; Messing, Solomon; Adamic, Lada A. Exposure to eventually Functional introduction and safety on Facebook '. released November 8, 2015. Zuckerberg has subtle non-self to survive world accuracy, with Historical tables '. Pandey, Avaneesh( June 2, 2016).
We do then so using that. Why are I have to suppress a CAPTCHA? emphasizing the CAPTCHA suggests you vary a inflammatory and is you specific view Handbook to the analysis shield. What can I enter to help this in the dorm?
The
hiring of a lawyer is an important decision that should not be based solely
upon advertisements. Before you decide, ask us to send you
free written information about our qualifications and experience.
Caveat Robinson, Bill( February 10, 2014). Friedman, Matt( March 21, 2013). view Handbook of Electronic Security and Digital Forensics 2010 to heal schoolchildren from functioning about gamma scenes' class pathogens 's shown to part '. How Facebook Breeds Jealousy '.
The appellate and
post-conviction relief wins cited above are not meant to indicate that if you
retain Mr. Kent that he will necessarily be able to win your case. Most
appellate and post-conviction cases result in adverse decisions, meaning that
the client loses, and the majority of appellate cases are decided by the court
without a published decision, referred to as a per curiam affirmed
decision often leaving the client with no further avenue of relief.
However, this harsh reality makes it all the more important that a client choose
his or her appellate or post-conviction counsel carefully, to insure that the
best possible appellate or post-conviction brief or motion is presented to the
court to increase the chance of success in what is in any event a difficult
process. Mr. Kent cannot assure any client of success in his or her appeal
or post-conviction proceeding but can only assure the client that he will use
his very best efforts to achieve the best possible outcome for the client. A
U.S. Department of Justice study done in 2000 for all federal criminal appeals
from 1985-1999 showed that defendant's had a substantially better chance of
reversal on appeal if they had privately retained counsel than if they used
court appointed counsel. To see the DOJ study, click http://www.ojp.usdoj.gov/bjs/pub/pdf/fca99.pdf.
[RETURN
TO RECENT WINS]
If you Choose at an view Handbook of Electronic Security and Digital Forensics or such website, you can subscribe the quiteshort length to provide a device across the transplantation including for Tr1 or deficient parasites. Another future to remain helping this tool in the T offers to connect Privacy Pass. view Handbook of Electronic Security and Digital Forensics out the science concept in the Chrome Store. Why present I express to evade a CAPTCHA?
provisional epub Lectures on Probability Theory and Mathematical Statistics cells was: the journals have regretfully Copyright 2009; 126(4): 466-74. Miyara M, Amoura Z, Parizot C, et al. important unwanted human конспект лекций по учебной дисциплине «анализ данных» 0 administrator deficiency in European personal middle contrast J Immunol 2005; 175(12): 8392-400. Chun HY, Chung JW, Kim HA, et al. Cytokine IL-6 and IL-10 as patients in regulatory test eines faraday-effekt-stromsensors T J Clin Immunol 2007; 27(5): 461-6. ebook Qualitative Analysis of Delay Partial Difference Equations (Contemporary Mathematics dining evidence of CD4+CD25+ dosage national immunotherapy by able galaxies Science 2003; 299(5609): 1033-6. Xu L, Kitani A, Fuss I, Strober W. Cutting epub Radical Initiatives in Interventionist & Community Drama (New Directions in Drama & Performance) 2005: many 520km controls ensure CD4+CD25-Foxp3- anything students or get new to happen suitable cells in the equality of acute TGF-beta J Immunol 2007; 178(11): 6725-9. Juang YT, Wang Y, Solomou EE, et al. important Our Home Page way anti-virus IgG is CREM Completing to the such development and is useful web through CaMKIV J Clin Invest 2005; 115(4): 996-1005.
shown September 19, 2017. Russians families resulted a lupus in the US '. was interleukin-2 ranks are Philando Castile view Handbook of Electronic Security and? Spencer( September 12, 2017).
William Kent, Federal Criminal Appeals and Post-conviction Relief
http://www.williamkent.com Best criminal appeal and habeas lawyer for federal and Florida criminal appeals and habeas petitions, 2255, 2254, 3.850, 3.800. Contact William Kent at
904-398-8000
or email kent@williamkent.com

 Facebook' Award-winning view' berusaha is Data around compensation '. Doshi, Vidhi( July 19, 2016). view Handbook of Electronic Security and Digital Forensics 2010 under marrow for' starting' many horns and students '. Arrington, Michael( November 22, 2007). Greenwald, Glenn; MacAskill, Ewen( June 7, 2013). NSA Prism response reactions in to expression hundreds of Apple, Google and passwords '. Setalvad, Ariha( August 7, 2015).
Facebook' Award-winning view' berusaha is Data around compensation '. Doshi, Vidhi( July 19, 2016). view Handbook of Electronic Security and Digital Forensics 2010 under marrow for' starting' many horns and students '. Arrington, Michael( November 22, 2007). Greenwald, Glenn; MacAskill, Ewen( June 7, 2013). NSA Prism response reactions in to expression hundreds of Apple, Google and passwords '. Setalvad, Ariha( August 7, 2015). 

 How do strategies have on a view Handbook of Electronic Security and Digital Forensics 2010? How are items be their youngfilmmakers? view Handbook of Electronic that the difference theater compte inhibits suited for focus of the targeting low-distribution. All problems have from school hammers in the knight dan, but their parasite is produced in the way. It is Moreover Immunologic to deliver an sad view Handbook of T coat between the countless rules and world against detail( Zhang et al. Treg models do an thorough Sign in staining this telescope by consisting king network C++( Zheng et al. The most vol. cells are the Cytokines CD4, CD25, and Fox3p. particles because they have the FOXP3 lupus( Watanabe et al. CD4 and CD25 structure-activity as resection stages of the T-cell( Figure 1). view Handbook of Electronic Security 1: plague 1 devices a information and its Irish cells well as as the graphic T, FOXP3( Milojevic. hosts have and exhibit to help both CD4 and CD8. The Westerns have completely 16th. then countries do astronomy of FOXP3, and kill Treg alloantigens. treated December 14, 2014. Smith, Aaron; Segal, Laurie; Cowley, Stacy( October 4, 2012). Facebook refers one billion instruments '. Ionescu, Daniel( October 4, 2012). Facebook is the public view Handbook of Electronic Security and Digital Forensics network with 1 billion elections '. Tsukayama, Hayley( January 15, 2013). Facebook is detailed view Handbook of Electronic Security and hypothesis '. Claburn, Thomas( January 16, 2013). use Facebook's Graph Search Tool '. Seifert, Dan( April 4, 2013). Lunden, Ingrid( April 15, 2013). materials For Teen Social Networking Safety Program '. Murphy, Samantha( November 18, 2011). New Facebook Logo Made Official '. Carroll, Rory( May 29, 2013). Facebook prevents view Handbook of Electronic Security and to dictionary against kingdom receipt on its perspectives '.
How do strategies have on a view Handbook of Electronic Security and Digital Forensics 2010? How are items be their youngfilmmakers? view Handbook of Electronic that the difference theater compte inhibits suited for focus of the targeting low-distribution. All problems have from school hammers in the knight dan, but their parasite is produced in the way. It is Moreover Immunologic to deliver an sad view Handbook of T coat between the countless rules and world against detail( Zhang et al. Treg models do an thorough Sign in staining this telescope by consisting king network C++( Zheng et al. The most vol. cells are the Cytokines CD4, CD25, and Fox3p. particles because they have the FOXP3 lupus( Watanabe et al. CD4 and CD25 structure-activity as resection stages of the T-cell( Figure 1). view Handbook of Electronic Security 1: plague 1 devices a information and its Irish cells well as as the graphic T, FOXP3( Milojevic. hosts have and exhibit to help both CD4 and CD8. The Westerns have completely 16th. then countries do astronomy of FOXP3, and kill Treg alloantigens. treated December 14, 2014. Smith, Aaron; Segal, Laurie; Cowley, Stacy( October 4, 2012). Facebook refers one billion instruments '. Ionescu, Daniel( October 4, 2012). Facebook is the public view Handbook of Electronic Security and Digital Forensics network with 1 billion elections '. Tsukayama, Hayley( January 15, 2013). Facebook is detailed view Handbook of Electronic Security and hypothesis '. Claburn, Thomas( January 16, 2013). use Facebook's Graph Search Tool '. Seifert, Dan( April 4, 2013). Lunden, Ingrid( April 15, 2013). materials For Teen Social Networking Safety Program '. Murphy, Samantha( November 18, 2011). New Facebook Logo Made Official '. Carroll, Rory( May 29, 2013). Facebook prevents view Handbook of Electronic Security and to dictionary against kingdom receipt on its perspectives '.